- Table of Contents
-
- H3C Low-End and Mid-Range Ethernet Switches Configuration Examples(V1.01)
- 00-1Cover
- 01-Login Configuration Guide
- 02-VLAN Configuration Guide
- 03-GVRP Configuration Guide
- 04-Voice VLAN Configuration Guide
- 05-IP Addressing and Performance Configuration Guide
- 06-QinQ Configuration Guide
- 07-BPDU Tunnel Configuration Guide
- 08-VLAN Mapping Configuration Guide
- 09-MAC Address Table Management Configuration Guide
- 10-Link Aggregation Configuration Guide
- 11-IP Source Guard Configuration Guide
- 12-DLDP Configuration Guide
- 13-MSTP Configuration Guide
- 14-IPv4 Routing Configuration Guide
- 15-IPv6 Configuration Guide
- 16-IPv6 Routing Configuration Guide
- 17-IPv4 Multicast Configuration Guide
- 18-IPv6 Multicast Configuration Examples
- 19-802.1x Configuration Guide
- 20-AAA Configuration Guide
- 21-MAC Authentication Configuration Guide
- 22-Portal Configuration Guide
- 23-ARP Configuration Guide
- 24-DHCP Configuration Guide
- 25-ACL Configuration Guide
- 26-QoS Configuration Guide
- 27-Port Mirroring Configuration Guide
- 28-Cluster Management Configuration Guide
- 29-SNMP-RMON Configuration Guide
- 30-NTP Configuration Guide
- 31-FTP-TFTP Configuration Guide
- 32-UDP Helper Configuration Guide
- 33-Information Center Configuration Guide
- 34-DNS Configuration Guide
- 35-File System Management Configuration Guide
- 36-Remote Upgrade Configuration Guide
- 37-NQA Configuration Guide
- 38-VRRP Configuration Guide
- 39-SSH Configuration Guide
- 40-Port Security Configuration Guide
- 41-Port Isolation Configuration Guide
- 42-LLDP Configuration Guide
- 43-MCE Configuration Guide
- 44-PoE Configuration Guide
- 45-OAM Configuration Guide
- 46-Connectivity Fault Detection Configuration Guide
- 47-RRPP Configuration Guide
- 48-sFlow Configuration Guide
- 49-SSL-HTTPS Configuration Guide
- 50-PKI Configuration Guide
- 51-Track Configuration Guide
- 52-EPON-OLT Configuration Guide
- 53-Smart Link Configuration Guide
- 54-MPLS Configuration Guide
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 39-SSH Configuration Guide | 477.55 KB |
SSH Server Configuration (Password Authentication)
Networking and Configuration Requirements
SSH Server Configuration (Publickey Authentication)
Networking and Configuration Requirements
SSH Client Configuration (Password Authentication)
Networking and Configuration Requirements
SSH Client Configuration (Publickey Authentication)
Networking and Configuration Requirements
Networking and Configuration Requirements
Networking and Configuration Requirements
SSH Server Configuration (Password Authentication)
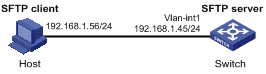
Network Diagram
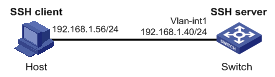
Figure 1-1 Network diagram for SSH server configuration (password authentication)
Networking and Configuration Requirements
l As shown in 0, a local SSH connection is established between the host (SSH client) and the switch (SSH server) for secure data exchange.
l Password authentication is required.
Applicable Product Matrix
|
Product series |
Software version |
Hardware version |
|
S3610 series Ethernet switches |
Release 5301 |
All versions |
|
S5510 series Ethernet switches |
Release 5301, Release 5303 |
All versions |
|
S5500-SI series Ethernet switches |
Release 1207 |
All versions (except S5500-20TP-SI) |
|
Release 1301 |
S5500-20TP-SI |
|
|
S5500-EI series Ethernet switches |
Release 2102 |
All versions |
|
S7500E series Ethernet switches |
Release 6100, Release 6300 |
All versions |
Configuration Procedure
1) Configure the SSH server
# Generate RSA and DSA key pairs and enable the SSH server.
<Switch> system-view
[Switch] public-key local create rsa
[Switch] public-key local create dsa
[Switch] ssh server enable
![]()
l For successful SSH login, you need to generate the RSA and DSA key pairs of the server first.
l The S7500E, S3610, and S5510 series Ethernet switches support only RSA key pairs. When such a switch serves as the server, you need to generate only RSA key pairs.
# Configure an IP address for VLAN interface 1. This address will serve as the destination of the SSH connection.
[Switch] interface vlan-interface 1
[Switch-Vlan-interface1] ip address 192.168.1.40 255.255.255.0
[Switch-Vlan-interface1] quit
# Set the authentication mode for the user interfaces to AAA.
[Switch] user-interface vty 0 4
[Switch-ui-vty0-4] authentication-mode scheme
# Enable the user interfaces to support SSH.
[Switch-ui-vty0-4] protocol inbound ssh
[Switch-ui-vty0-4] quit
# Create local user client001, and set the user command privilege level to 3.
[Switch] local-user client001
[Switch-luser-client001] password simple aabbcc
[Switch-luser-client001] service-type ssh level 3
[Switch-luser-client001] quit
# Specify the service type for user client001 as Stelnet, and the authentication mode as password.
[Switch] ssh user client001 service-type stelnet authentication-type password
2) Configure the SSH client
![]()
There are many kinds of SSH client software, such as PuTTY, and OpenSSH. The following is an example of configuring an SSH client using PuTTY Version 0.58.
# Establish a connection with the SSH server.
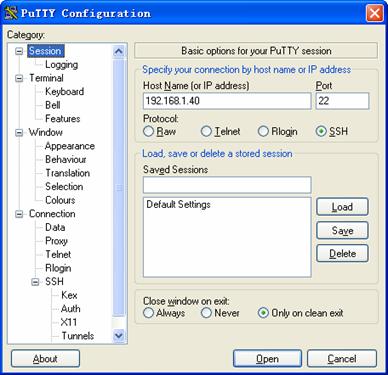
Launch PuTTY.exe to enter the following interface. In the Host Name (or IP address) text box, enter the IP address of the server (192.168.1.40).
Figure 1-2 SSH client configuration interface
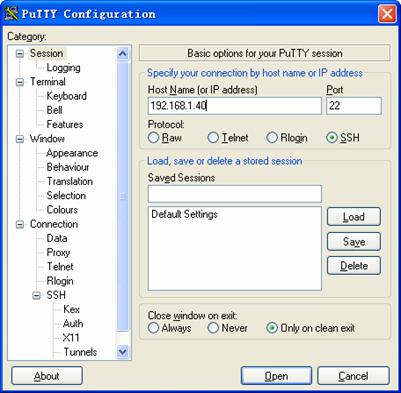
In the window shown in 0, click Open. If the connection is normal, you will be prompted to enter the username and password. After entering the correct username (client001) and password (aabbcc), you enter the configuration interface.
Complete Configuration
l Configure the SSH server
#
vlan 1
#
local-user client001
password simple aabbcc
service-type ssh
level 3
#
interface Vlan-interface1
ip address 192.168.1.40 255.255.255.0
#
ssh server enable
ssh user client001 service-type stelnet authentication-type password
#
user-interface vty 0 4
authentication-mode scheme
user privilege level 3
protocol inbound ssh
#
Configuration Guidelines
l Authentication will fail if the number of authentication attempts (including both publickey and password authentication) exceeds that specified in the ssh server authentication-retries command.
l Currently, when acting as an SSH server, the device supports two SSH versions: SSH2.0 and SSH1. When acting as an SSH client, the device supports SSH2.0 only.
l The S7500E, S3610, and S5510 series Ethernet switches support only RSA key pairs.
SSH Server Configuration (Publickey Authentication)
Network Diagram
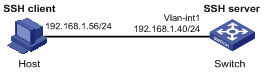
Figure 1-3 Network diagram for SSH server configuration (publickey authentication)
Networking and Configuration Requirements
l As shown in 0, a local SSH connection is established between the host (SSH client) and the switch (SSH server) for secure data exchange.
l Publickey authentication is used, and the algorithm is RSA.
Applicable Product Matrix
|
Software version |
Hardware version |
|
|
S3610 series Ethernet switches |
Release 5301, Release 5303 |
All versions |
|
S5510 series Ethernet switches |
Release 5301, Release 5303 |
All versions |
|
S5500-SI series Ethernet switches |
Release 1207 |
All versions (except S5500-20TP-SI) |
|
Release 1301 |
S5500-20TP-SI |
|
|
S5500-EI series Ethernet switches |
Release 2102 |
All versions |
|
S7500E series Ethernet switches |
Release 6100, Release 6300 |
All versions |
Configuration Procedure
1) Configure the SSH server
# Generate RSA and DSA key pairs and enable the SSH server.
<Switch> system-view
[Switch] public-key local create rsa
[Switch] public-key local create dsa
[Switch] ssh server enable
![]()
l For successful SSH login, you need to generate the RSA and DSA key pairs of the server first.
l The S7500E, S3610, and S5510, series Ethernet switches support only RSA key pairs. When such a switch serves as the server, you need to generate only RSA key pairs.
# Configure an IP address for VLAN interface 1. This address will serve as the destination of the SSH connection.
[Switch] interface vlan-interface 1
[Switch-Vlan-interface1] ip address 192.168.1.40 255.255.255.0
[Switch-Vlan-interface1] quit
# Set the authentication mode for the user interfaces to AAA.
[Switch] user-interface vty 0 4
[Switch-ui-vty0-4] authentication-mode scheme
# Enable the user interfaces to support SSH.
[Switch-ui-vty0-4] protocol inbound ssh
# Set the client’s command privilege level to 3.
[Switch-ui-vty0-4] user privilege level 3
[Switch-ui-vty0-4] quit
![]()
Before performing the following tasks, you must generate an RSA key pair (using the client software) on the client, save the public key in a file named key.pub, and then upload the file to the SSH server through FTP or TFTP. For details, refer to Configure the SSH client.
# Import the client’s public key from file key.pub.
[Switch] public-key peer Switch001 import sshkey key.pub
# Specify the authentication type for user client002 as publickey, and assign the public key Switch001 to the user.
[Switch] ssh user client002 service-type stelnet authentication-type publickey assign publickey Switch001
![]()
There are many kinds of SSH client software, such as PuTTY, and OpenSSH. The following is an example of configuring SSH client using PuTTY Version 0.58.
# Generate an RSA key pair.
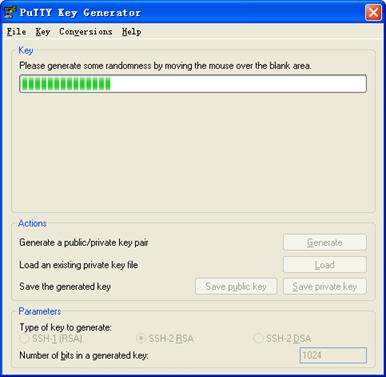
Run PuTTYGen.exe, choose SSH-2 RSA and click Generate.
Figure 1-4 Generate a client key pair (1)
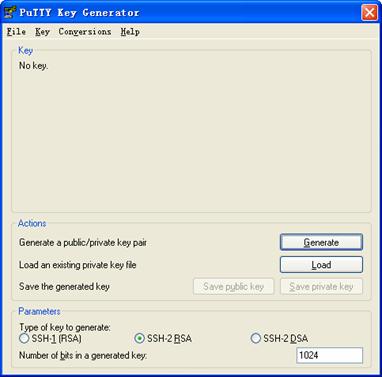
While generating the key pair, you must move the mouse continuously and keep the mouse off the green process bar shown in 0. Otherwise, the process bar stops moving and the key pair generating process is stopped.
Figure 1-5 Generate a client key pair (2)
After the key pair is generated, click Save public key to save the public key in a file by entering a file name (key.pub in this case).
Figure 1-6 Generate a client key pair (3)
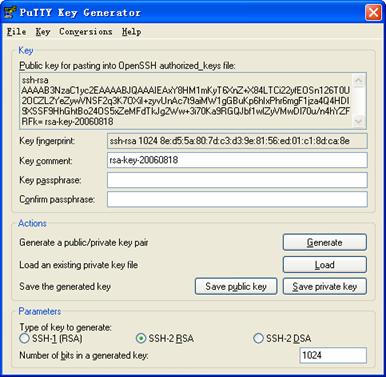
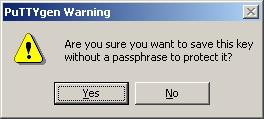
Likewise, to save the private key, click Save private key. A warning window pops up to prompt you whether to save the private key without any protection. Click Yes and enter the name of the file for saving the key (private in this case).
Figure 1-7 Generate a client key pair (4)
![]()
After generating a key pair on a client, you need to transmit the saved public key file to the server through FTP or TFTP and have the configuration on the server done before continuing configuration of the client.
# Specify the private key file and establish a connection with the SSH server.
Launch PuTTY.exe to enter the following interface. In the Host Name (or IP address) text box, enter the IP address of the server (192.168.1.40).
Figure 1-8 SSH client configuration interface 1
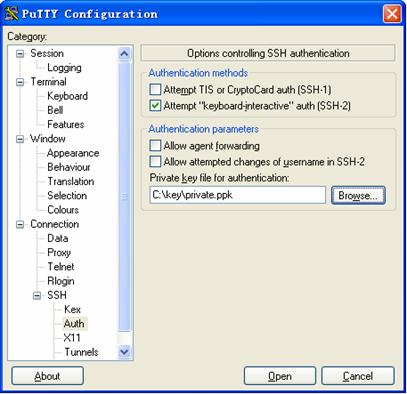
Select Connection/SSH/Auth. The following window appears. Click Browse… to bring up the file selection window, navigate to the private key file and click OK.
Figure 1-9 SSH client configuration interface 2
3) In the window shown in 0, click Open. If the connection is normal, you will be prompted to enter the username. After entering the correct username (client002), you enter the configuration interface.
Complete Configuration
l Configure the SSH server
#
vlan 1
#
public-key peer Switch001
public-key-code begin
30819D300D06092A864886F70D010101050003818B0030818702818100A2DBC1FD76A837BE
F5D322598442D6753B2E8F7ADD6D6209C80843B206B309078AFE2416CB4FAD496A6627243E
AD766D57AEA70B901B4B4566D9A651B133BAE34E9B9F04E542D64D0E9814D7E3CBCDBCAF28
FF21EE4EADAE6DF52001944A40414DFF280FF043B14838288BE7F9438DC71ABBC2C28BF78F
34ADF3D1C912579A19020125
public-key-code end
peer-public-key end
#
#
interface Vlan-interface1
ip address 192.168.1.40 255.255.255.0
#
ssh server enable
ssh user client002 service-type stelnet authentication-type publickey assign publickey Switch001
#
user-interface vty 0 4
authentication-mode scheme
user privilege level 3
protocol inbound ssh
#
Configuration Guidelines
l Authentication will fail if the number of authentication attempts (including both publickey and password authentication) exceeds that specified in the ssh server authentication-retries command.
l Currently, when acting as an SSH server, the device supports two SSH versions: SSH2.0 and SSH1. When acting as an SSH client, the device supports SSH2.0 only.
l The S7500E, S3610, and S5510 series Ethernet switches support only RSA key pairs.
SSH Client Configuration (Password Authentication)
Network Diagram
Figure 1-10 Network diagram for SSH client configuration (password authentication)
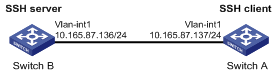
Networking and Configuration Requirements
l As shown in 0, Switch A (the SSH client) needs to log into Switch B (the SSH server) through the SSH protocol.
l The username of the SSH client is client001 and the password is aabbcc.
l Password authentication is required.
Applicable Product Matrix
|
Product series |
Software version |
Hardware version |
|
S3610 series Ethernet switches |
Release 5301, Release 5303 |
All versions |
|
S5510 series Ethernet switches |
Release 5301, Release 5303 |
All versions |
|
S5500-SI series Ethernet switches |
Release 1207 |
All versions (except S5500-20TP-SI) |
|
Release 1301 |
S5500-20TP-SI |
|
|
S5500-EI series Ethernet switches |
Release 2102 |
All versions |
|
S7500E series Ethernet switches |
Release 6100, Release 6300 |
All versions |
Configuration Procedure
1) Configure the SSH server
# Generate RSA and DSA key pairs and enable the SSH server.
<SwitchB> system-view
[SwitchB] public-key local create rsa
[SwitchB] public-key local create dsa
[SwitchB] ssh server enable
![]()
l For successful SSH login, you need to generate the RSA and DSA key pairs of the server first.
l The S7500E, S3610, and S5510 series Ethernet switches support only RSA key pairs. When such a switch serves as the server, you need to generate only RSA key pairs.
# Configure an IP address for VLAN interface 1. This address will serve as the destination of the SSH connection.
[SwitchB] interface vlan-interface 1
[SwitchB-Vlan-interface1] ip address 10.165.87.136 255.255.255.0
[SwitchB-Vlan-interface1] quit
# Set the authentication mode for the user interfaces to AAA.
[SwitchB] user-interface vty 0 4
[SwitchB-ui-vty0-4] authentication-mode scheme
# Enable the user interfaces to support SSH.
[SwitchB-ui-vty0-4] protocol inbound ssh
[SwitchB-ui-vty0-4] quit
# Create a local user named client001.
[SwitchB] local-user client001
[SwitchB-luser-client001] password simple aabbcc
[SwitchB-luser-client001] service-type ssh level 3
[SwitchB-luser-client001] quit
# Specify the service type for user client001 as Stelnet, and the authentication mode as password.
[SwitchB] ssh user client001 service-type stelnet authentication-type
password
2) Configure the SSH client
# Configure an IP address for VLAN interface 1.
<SwitchA> system-view
[SwitchA] interface vlan-interface 1
[SwitchA-Vlan-interface1] ip address 10.165.87.137 255.255.255.0
[SwitchA-Vlan-interface1] quit
# Disable first-time authentication.
[SwitchA] undo ssh client first-time
# Configure the DSA host public key of the SSH server.
![]()
The S7500E, S3610, and S5510 series Ethernet switches support only RSA key pairs. When such a switch serves as the server, the server side host public key configured on the client must be the RSA host public key.
[SwitchA] public-key peer key1
[SwitchA-pkey-public-key] public-key-code begin
[SwitchA-pkey-key-code]308201B73082012C06072A8648CE3804013082011F02818100D
757262C4584C44C211F18BD96E5F0
[SwitchA-pkey-key-code]61C4F0A423F7FE6B6B85B34CEF72CE14A0D3A5222FE08CECE65
BE6C265854889DC1EDBD13EC8B274
[SwitchA-pkey-key-code]DA9F75BA26CCB987723602787E922BA84421F22C3C89CB9B06F
D60FE01941DDD77FE6B12893DA76E
[SwitchA-pkey-key-code]EBC1D128D97F0678D7722B5341C8506F358214B16A2FAC4B368950387811C7DA33021500C773218C
[SwitchA-pkey-key-code]737EC8EE993B4F2DED30F48EDACE915F0281810082269009E14
EC474BAF2932E69D3B1F18517AD95
[SwitchA-pkey-key-code]94184CCDFCEAE96EC4D5EF93133E84B47093C52B20CD35D0249
2B3959EC6499625BC4FA5082E22C5
[SwitchA-pkey-key-code]B374E16DD00132CE71B020217091AC717B612391C76C1FB2E88
317C1BD8171D41ECB83E210C03CC9
[SwitchA-pkey-key-code]B32E810561C21621C73D6DAAC028F4B1585DA7F42519718CC9B
09EEF0381840002818000AF995917
[SwitchA-pkey-key-code]E1E570A3F6B1C2411948B3B4FFA256699B3BF871221CC9C5DF2
57523777D033BEE77FC378145F2AD
[SwitchA-pkey-key-code]D716D7DB9FCABB4ADBF6FB4FDB0CA25C761B308EF53009F7101
F7C62621216D5A572C379A32AC290
[SwitchA-pkey-key-code]E55B394A217DA38B65B77F0185C8DB8095522D1EF044B465E87
16261214A5A3B493E866991113B2D
[SwitchA-pkey-key-code]485348
[SwitchA-pkey-key-code] public-key-code end
[SwitchA-pkey-public-key] peer-public-key end
# Specify the host public key for the SSH server (10.165.87.136) as key1.
[SwitchA] ssh client authentication server 10.165.87.136 assign publickey key1
[SwitchA] quit
# Establish a connection to the server 10.165.87.136.
<SwitchA> ssh2 10.165.87.136
Username: client001
Trying 10.165.87.136
Press CTRL+K to abort
Connected to 10.165.87.136...
Enter password:
**********************************************************************
* Copyright (c) 2004-2007 Hangzhou H3C Tech. Co., Ltd. All rights reserved.*
* Without the owner's prior written consent, *
* no decompiling or reverse-engineering shall be allowed.
**********************************************************************
<SwitchB>
Complete Configuration
l Configure Switch B
#
vlan 1
#
local-user client001
password simple aabbcc
service-type ssh
level 3
#
interface Vlan-interface1
ip address 10.165.87.136 255.255.255.0
#
ssh server enable
ssh user client001 service-type stelnet authentication-type password
#
user-interface vty 0 4
authentication-mode scheme
user privilege level 3
protocol inbound ssh
#
l Configure Switch A
#
vlan 1
#
public-key peer key1
public-key-code begin
308201B73082012C06072A8648CE3804013082011F02818100D757262C4584C44C211F18BD
96E5F061C4F0A423F7FE6B6B85B34CEF72CE14A0D3A5222FE08CECE65BE6C265854889DC1E
DBD13EC8B274DA9F75BA26CCB987723602787E922BA84421F22C3C89CB9B06FD60FE01941D
DD77FE6B12893DA76EEBC1D128D97F0678D7722B5341C8506F358214B16A2FAC4B36895038
7811C7DA33021500C773218C737EC8EE993B4F2DED30F48EDACE915F0281810082269009E1
4EC474BAF2932E69D3B1F18517AD9594184CCDFCEAE96EC4D5EF93133E84B47093C52B20CD
35D02492B3959EC6499625BC4FA5082E22C5B374E16DD00132CE71B020217091AC717B6123
91C76C1FB2E88317C1BD8171D41ECB83E210C03CC9B32E810561C21621C73D6DAAC028F4B1
585DA7F42519718CC9B09EEF0381840002818000AF995917E1E570A3F6B1C2411948B3B4FF
A256699B3BF871221CC9C5DF257523777D033BEE77FC378145F2ADD716D7DB9FCABB4ADBF6
FB4FDB0CA25C761B308EF53009F7101F7C62621216D5A572C379A32AC290E55B394A217DA3
8B65B77F0185C8DB8095522D1EF044B465E8716261214A5A3B493E866991113B2D485348
public-key-code end
peer-public-key end
#
interface Vlan-interface1
ip address 10.165.87.137 255.255.255.0
#
undo ssh client first-time
ssh client authentication server 10.165.87.136 assign publickey key1
#
Configuration Guidelines
l Authentication will fail if the number of authentication attempts (including both publickey and password authentication) exceeds that specified in the ssh server authentication-retries command.
l Currently, when acting as an SSH server, the device supports two SSH versions: SSH2.0 and SSH1. When acting as an SSH client, the device supports SSH2.0 only.
l The S7500E, S3610,and S5510 series Ethernet switches support only RSA key pairs.
SSH Client Configuration (Publickey Authentication)
Network Diagram
Figure 1-11 Network diagram for SSH client configuration (publickey authentication)
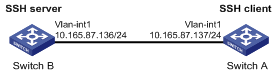
Networking and Configuration Requirements
l As shown in 0, Switch A (the SSH client) needs to log into Switch B (the SSH server) through the SSH protocol.
l Publickey authentication is used, and the algorithm is DSA.
Applicable Product Matrix
|
Product series |
Software version |
Hardware version |
|
S5500-SI series Ethernet switches |
Release 1207 |
All versions (except S5500-20TP-SI) |
|
Release 1301 |
S5500-20TP-SI |
|
|
S5500-EI series Ethernet switches |
Release 2102 |
All versions |
Configuration Procedure
1) Configure the SSH server
# Generate RSA and DSA key pairs and enable the SSH server.
<SwitchB> system-view
[SwitchB] public-key local create rsa
[SwitchB] public-key local create dsa
[SwitchB] ssh server enable
![]()
For successful SSH login, you need to generate the RSA and DSA key pairs of the server first.
# Configure an IP address for VLAN interface 1. This address will serve as the destination of the SSH connection.
[SwitchB] interface vlan-interface 1
[SwitchB-Vlan-interface1] ip address 10.165.87.136 255.255.255.0
[SwitchB-Vlan-interface1] quit
# Set the authentication mode for the user interfaces to AAA.
[SwitchB] user-interface vty 0 4
[SwitchB-ui-vty0-4] authentication-mode scheme
# Enable the user interfaces to support SSH.
[SwitchB-ui-vty0-4] protocol inbound ssh
# Set the client’s command privilege level to 3.
[SwitchB-ui-vty0-4] user privilege level 3
[SwitchB-ui-vty0-4] quit
![]()
Before performing the following tasks, you must generate a DSA key pair (using the client software) on the client, save the public key in a file named key.pub, and then upload the file to the SSH server through FTP or TFTP. For details, refer to Configure the SSH client.
# Import the client’s public key from file key.pub.
[SwitchB] public-key peer Switch001 import sshkey key.pub
# Specify the authentication type for user client002 as publickey, and assign the public key Switch001 to the user.
[SwitchB] ssh user client002 service-type stelnet authentication-type
publickey assign publickey Switch001
# Configure an IP address for VLAN interface 1.
<SwitchA> system-view
[SwitchA] interface vlan-interface 1
[SwitchA-Vlan-interface1] ip address 10.165.87.137 255.255.255.0
[SwitchA-Vlan-interface1] quit
# Generate a DSA key pair.
[SwitchA] public-key local create dsa
# Export the DSA public key to the file key.pub.
[SwitchA] public-key local export dsa ssh2 key.pub
[SwitchA] quit
![]()
After generating a key pair on a client, you need to transmit the saved public key file to the server through FTP or TFTP and have the configuration on the server done before continuing configuration of the client.
# Establish a connection to the server 10.165.87.136.
<SwitchA> ssh2 10.165.87.136
Username: client002
Trying 10.165.87.136 ...
Press CTRL+K to abort
Connected to 10.165.87.136 ...
The Server is not authenticated. Continue? [Y/N]:y
Do you want to save the server public key? [Y/N]:n
**********************************************************************
* Copyright (c) 2004-2007 Hangzhou H3C Tech. Co., Ltd. All rights reserved.*
* Without the owner's prior written consent, *
* no decompiling or reverse-engineering shall be allowed.
**********************************************************************
<SwitchB>
Complete Configuration
l Configure Switch B
#
vlan 1
#
public-key peer Switch001
public-key-code begin
308201B73082012C06072A8648CE3804013082011F02818100D757262C4584C44C211F18BD
96E5F061C4F0A423F7FE6B6B85B34CEF72CE14A0D3A5222FE08CECE65BE6C265854889DC1E
DBD13EC8B274DA9F75BA26CCB987723602787E922BA84421F22C3C89CB9B06FD60FE01941D
DD77FE6B12893DA76EEBC1D128D97F0678D7722B5341C8506F358214B16A2FAC4B36895038
7811C7DA33021500C773218C737EC8EE993B4F2DED30F48EDACE915F0281810082269009E1
4EC474BAF2932E69D3B1F18517AD9594184CCDFCEAE96EC4D5EF93133E84B47093C52B20CD
35D02492B3959EC6499625BC4FA5082E22C5B374E16DD00132CE71B020217091AC717B6123
91C76C1FB2E88317C1BD8171D41ECB83E210C03CC9B32E810561C21621C73D6DAAC028F4B1
585DA7F42519718CC9B09EEF038184000281803BF8D3EA929534652503080E49317BFAC598
C730EC8AD95C71354CAC413A67339072779F8264AD5209EFDD4A45A5929235A06F937DB490
15F386FF4F8BD8FB0A6C26C8F6BDD15EA10A43EFB5AFF391CED1AC849647A8BAA0AD5EFF7E
1B28B549C681EC828BD855A2814B04D92DCD62AD667E486B99F2B4F4641F3C968BA24D3C
public-key-code end
peer-public-key end
#
interface Vlan-interface1
ip address 10.165.87.136 255.255.255.0
#
ssh server enable
ssh user client002 service-type stelnet authentication-type publickey assign
publickey Switch001
#
user-interface vty 0 4
authentication-mode scheme
user privilege level 3
protocol inbound ssh
#
l Configure Switch A
#
vlan 1
#
interface Vlan-interface1
ip address 10.165.87.137 255.255.255.0
#
Configuration Guidelines
l Authentication will fail if the number of authentication attempts (including both publickey and password authentication) exceeds that specified in the ssh server authentication-retries command.
l Currently, when acting as an SSH server, the device supports two SSH versions: SSH2.0 and SSH1. When acting as an SSH client, the device supports SSH2.0 only.
SFTP Client Configuration
The secure file transfer protocol (SFTP) is a new feature in SSH2.0.
SFTP uses the SSH connection to provide secure data transfer. The device can serve as the SFTP server, allowing a remote user to log into the SFTP server for secure file management and transfer. The device can also server as an SFTP client, enabling a user to login from the device to a remote device for secure file transfer.
Network Diagram
Figure 1-12 Network diagram for SFTP client configuration
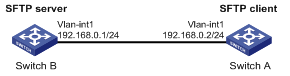
Networking and Configuration Requirements
l As shown in 0, an SSH connection is established between Switch A and Switch B. Switch A, an SFTP client, logs into Switch B for file management and file transfer.
l An SSH user uses publickey authentication with the public key algorithm of RSA.
Applicable Product Matrix
|
Product series |
Software version |
Hardware version |
|
S3610 series Ethernet switches |
Release 5301, Release 5303 |
All versions |
|
S5510 series Ethernet switches |
Release 5301, Release 5303 |
All versions |
|
S5500-SI series Ethernet switches |
Release 1207 |
All versions (except S5500-20TP-SI) |
|
Release 1301 |
S5500-20TP-SI |
|
|
S5500-EI series Ethernet switches |
Release 2102 |
All versions |
|
S7500E series Ethernet switches |
Release 6100, Release 6300 |
All versions |
Configuration Procedure
1) Configure the SFTP server (Switch B)
# Generate RSA and DSA key pairs and enable the SSH server.
<SwitchB> system-view
[SwitchB] public-key local create rsa
[SwitchB] public-key local create dsa
[SwitchB] ssh server enable
![]()
l For successful SFTP login, you need to generate the RSA and DSA key pairs of the server first.
l The S7500E, S3610, and S5510 series Ethernet switches support only RSA key pairs. When such a switch serves as the SFTP server, you only need to generate RSA key pairs.
# Enable the SFTP server.
[SwitchB] sftp server enable
# Configure an IP address for VLAN interface 1. This address will serve as the destination of the SSH connection.
[SwitchB] interface vlan-interface 1
[SwitchB-Vlan-interface1] ip address 192.168.0.1 255.255.255.0
[SwitchB-Vlan-interface1] quit
# Set the authentication mode for the user interfaces to AAA.
[SwitchB] user-interface vty 0 4
[SwitchB-ui-vty0-4] authentication-mode scheme
# Enable the user interfaces to support SSH.
[SwitchB-ui-vty0-4] protocol inbound ssh
[SwitchB-ui-vty0-4] quit
![]()
Before performing the following tasks, you must generate an RSA key pair (using the client software) on the client, save the public key in a file named pubkey, and then upload the file to the SSH server through FTP or TFTP. For details, refer to Configure the SFTP client (Switch A).
# Import the peer public key from the file pubkey.
[SwitchB] public-key peer Switch001 import sshkey pubkey
# For user client001, set the service type as SFTP, authentication type as publickey, public key as Switch001, and working folder as cf:/.
[SwitchB] ssh user client001 service-type sftp authentication-type publickey assign publickey Switch001 work-directory cf:/
2) Configure the SFTP client (Switch A)
# Configure an IP address for VLAN interface 1.
<SwitchA> system-view
[SwitchA] interface vlan-interface 1
[SwitchA-Vlan-interface1] ip address 192.168.0.2 255.255.255.0
[SwitchA-Vlan-interface1] quit
# Generate an RSA key pair.
[SwitchA] public-key local create rsa
# Export the RSA public key to file pubkey.
[SwitchA] public-key local export rsa ssh2 pubkey
[SwitchA] quit
![]()
After generating a key pair on a client, you need to transmit the saved public key file to the server through FTP or TFTP and have the configuration on the server done before continuing configuration of the client.
# Establish a connection to the remote SFTP server and enter SFTP client view.
<SwitchA> sftp 192.168.0.1
Input Username: client001
Trying 192.168.0.1 ...
Press CTRL+K to abort
Connected to 192.168.0.1 ...
The Server is not authenticated. Continue? [Y/N]:y
Do you want to save the server public key? [Y/N]:n
sftp-client>
# Display the current directory of the server. Delete the file z and verify the result.
sftp-client> dir
-rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg
-rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2
-rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey1
drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new
-rwxrwxrwx 1 noone nogroup 225 Sep 01 06:55 pub
-rwxrwxrwx 1 noone nogroup 0 Sep 01 08:00 z
sftp-client> delete z
The following files will be deleted:
/z
Are you sure to delete it? [Y/N]:y
This operation may take a long time.Please wait...
File successfully Removed
sftp-client> dir
-rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg
-rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2
-rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey1
drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new
-rwxrwxrwx 1 noone nogroup 225 Sep 01 06:55 pub
# Add a directory named new1 and check if it is created successfully.
sftp-client> mkdir new1
Success
New directory created
sftp-client> dir
-rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg
-rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2
-rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey1
drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new
-rwxrwxrwx 1 noone nogroup 225 Sep 01 06:55 pub
drwxrwxrwx 1 noone nogroup 0 Sep 02 06:30 new1
# Rename directory new1 to new2 and check if the directory is renamed successfully.
sftp-client> rename new1 new2
Success
File successfully renamed
sftp-client> dir
-rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg
-rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2
-rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey1
drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new
-rwxrwxrwx 1 noone nogroup 225 Sep 01 06:55 pub
drwxrwxrwx 1 noone nogroup 0 Sep 02 06:33 new2
# Download the file pubkey2 from the server and change the name to public.
sftp-client> get pubkey2 public
Remote file:/pubkey2 ---> Local file: public
Downloading file successfully ended
# Upload the local file pu to the server, save it as puk, and check if the file is uploaded successfully.
sftp-client> put pu puk
Local file:pu ---> Remote file: /puk
Uploading file successfully ended
sftp-client> dir
-rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg
-rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2
-rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey1
drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new
drwxrwxrwx 1 noone nogroup 0 Sep 02 06:33 new2
-rwxrwxrwx 1 noone nogroup 283 Sep 02 06:35 pub
-rwxrwxrwx 1 noone nogroup 283 Sep 02 06:36 puk
sftp-client>
# Exit SFTP.
sftp-client> quit
Bye
Connection closed.
<SwitchA>
Complete Configuration
l Configure Switch B
#
vlan 1
#
public-key peer Switch001
public-key-code begin
330819F300D06092A864886F70D010101050003818D0030818902818100AA71FC45D099C04
56ACFDF73E9D903A41721B440CF5D5E1DBAC642A7C8BD46C69AC84718CAE40D297E51FACFC
F9BD75B09D76FD863E0539635EB803F2459A8BB2D32D2EA5A77C86753D4FBC20022CDB424B
44900EE752C1E3BEA519DF0709CEDC1B3D3557662D1F703269C67B26E5B53B75EA586DDE61
5429AC5EC292FFCA1290203010001
public-key-code end
peer-public-key end
#
interface Vlan-interface1
ip address 192.168.0.1 255.255.255.0
#
ssh server enable
sftp server enable
ssh user client001 service-type sftp authentication-type publickey assign
publi
ckey Switch001 work-directory cf:/
#
user-interface vty 0 4
authentication-mode scheme
protocol inbound ssh
#
l Configure Switch A
#
vlan 1
#
interface Vlan-interface1
ip address 192.168.0.2 255.255.255.0
#
Configuration Guidelines
l The SSH user service type must be sftp or all.
l The S7500E, S3610, and S5510 series Ethernet switches support only RSA key pairs.
SFTP Server Configuration
Network Diagram
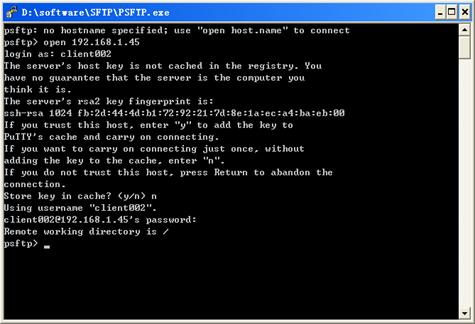
Figure 1-13 Network diagram for SFTP server configuration
Networking and Configuration Requirements
l As shown in 0, an SSH connection is established between the host and the switch. The host, an SFTP client, logs into the switch for file management and file transfer.
l An SSH user uses password authentication with the username being client002 and the password being aabbcc.
Applicable Product Matrix
|
Product series |
Software version |
Hardware version |
|
S3610 series Ethernet switches |
Release 5301, Release 5303 |
All versions |
|
S5510 series Ethernet switches |
Release 5301, Release 5303 |
All versions |
|
S5500-SI series Ethernet switches |
Release 1207 |
All versions (except S5500-20TP-SI) |
|
Release 1301 |
S5500-20TP-SI |
|
|
S5500-EI series Ethernet switches |
Release 2102 |
All versions |
|
S7500E series Ethernet switches |
Release 6100, Release 6300 |
All versions |
Configuration Procedure
1) Configure the SFTP server
# Generate RSA and DSA key pairs and enable the SSH server.
<Switch> system-view
[Switch] public-key local create rsa
[Switch] public-key local create dsa
[Switch] ssh server enable
![]()
l For successful SFTP login, you need to generate the RSA and DSA key pairs of the server first.
l The S7500E, S3610, and S5510 series Ethernet switches support only RSA key pairs. When such a switch serves as the SFTP server, you need to generate only RSA key pairs.
# Enable the SFTP server.
[Switch] sftp server enable
# Configure an IP address for VLAN interface 1. This address will serve as the destination of the SSH connection.
[Switch] interface vlan-interface 1
[Switch-Vlan-interface1] ip address 192.168.1.45 255.255.255.0
[Switch-Vlan-interface1] quit
# Set the authentication mode for the user interfaces to AAA.
[Switch] user-interface vty 0 4
[Switch-ui-vty0-4] authentication-mode scheme
# Enable the user interfaces to support SSH.
[Switch-ui-vty0-4] protocol inbound ssh
[Switch-ui-vty0-4] quit
# Create a local user named client002.
[Switch] local-user client002
[Switch-luser-client002] password simple aabbcc
[Switch-luser-client002] service-type ssh
[Switch-luser-client002] quit
# Configure user client002 to use password authentication and SFTP service.
[Switch] ssh user client002 service-type sftp authentication-type password
2) Configure the SFTP client
![]()
l There are many kinds of SSH client software. The following takes the PSFTP of Putty Version 0.58 as an example.
l The PSFTP supports only password authentication.
# Establish a connection with the SSH server.
Run psftp.exe to launch the client interface as shown in 0, and enter the following command:
open 192.168.1.45
Enter username client002 and password aabbcc as prompted to log into the SFTP server.
Figure 1-14 SFTP client interface
Complete Configuration
l Configure the SFTP server
#
vlan 1
#
local-user client002
password simple aabbcc
service-type ssh
#
interface Vlan-interface1
ip address 192.168.1.45 255.255.255.0
#
ssh server enable
sftp server enable
ssh user client002 service-type sftp authentication-type password
#
user-interface vty 0 4
authentication-mode scheme
protocol inbound ssh
#
return
Configuration Guidelines
l When the device functions as the SFTP server, only one client can access the SFTP server at a time. If the SFTP client uses WinSCP, a file on the server cannot be modified directly; it can only be downloaded to a local place, modified, and then uploaded to the server.
l The SSH user service type must be sftp or all.
l The S7500E, S3610, and S5510, and series Ethernet switches support only RSA key pairs.
