- Table of Contents
-
- H3C Low-End and Mid-Range Ethernet Switches Configuration Examples(V1.01)
- 00-1Cover
- 01-Login Configuration Guide
- 02-VLAN Configuration Guide
- 03-GVRP Configuration Guide
- 04-Voice VLAN Configuration Guide
- 05-IP Addressing and Performance Configuration Guide
- 06-QinQ Configuration Guide
- 07-BPDU Tunnel Configuration Guide
- 08-VLAN Mapping Configuration Guide
- 09-MAC Address Table Management Configuration Guide
- 10-Link Aggregation Configuration Guide
- 11-IP Source Guard Configuration Guide
- 12-DLDP Configuration Guide
- 13-MSTP Configuration Guide
- 14-IPv4 Routing Configuration Guide
- 15-IPv6 Configuration Guide
- 16-IPv6 Routing Configuration Guide
- 17-IPv4 Multicast Configuration Guide
- 18-IPv6 Multicast Configuration Examples
- 19-802.1x Configuration Guide
- 20-AAA Configuration Guide
- 21-MAC Authentication Configuration Guide
- 22-Portal Configuration Guide
- 23-ARP Configuration Guide
- 24-DHCP Configuration Guide
- 25-ACL Configuration Guide
- 26-QoS Configuration Guide
- 27-Port Mirroring Configuration Guide
- 28-Cluster Management Configuration Guide
- 29-SNMP-RMON Configuration Guide
- 30-NTP Configuration Guide
- 31-FTP-TFTP Configuration Guide
- 32-UDP Helper Configuration Guide
- 33-Information Center Configuration Guide
- 34-DNS Configuration Guide
- 35-File System Management Configuration Guide
- 36-Remote Upgrade Configuration Guide
- 37-NQA Configuration Guide
- 38-VRRP Configuration Guide
- 39-SSH Configuration Guide
- 40-Port Security Configuration Guide
- 41-Port Isolation Configuration Guide
- 42-LLDP Configuration Guide
- 43-MCE Configuration Guide
- 44-PoE Configuration Guide
- 45-OAM Configuration Guide
- 46-Connectivity Fault Detection Configuration Guide
- 47-RRPP Configuration Guide
- 48-sFlow Configuration Guide
- 49-SSL-HTTPS Configuration Guide
- 50-PKI Configuration Guide
- 51-Track Configuration Guide
- 52-EPON-OLT Configuration Guide
- 53-Smart Link Configuration Guide
- 54-MPLS Configuration Guide
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 21-MAC Authentication Configuration Guide | 99.89 KB |
1 MAC Authentication Configuration Guide·
Configuring Local MAC Authentication
Networking and Configuration Requirements
Configuring RADIUS Based MAC Authentication
Networking and Configuration Requirements
Networking and Configuration Requirements
MAC Authentication Overview
MAC authentication provides a way for authenticating users based on ports and MAC addresses, without requiring any client software to be installed on the hosts. Once detecting a new MAC address, it initiates the authentication process without requiring any username or password.
Currently, the device supports two MAC authentication modes:
l Remote Authentication Dial-In User Service (RADIUS) based MAC authentication
l Local MAC authentication
For detailed information about RADIUS authentication and local authentication, refer to AAA RADIUS HWTACACS Configuration.
After determining the authentication mode to be used, you can choose the username and password type for MAC authentication, which can be:
l MAC address: The MAC address of a user serves as both the username and password for authentication.
l Fixed username: All users use the same preconfigured username and password for authentication, regardless of their MAC addresses.
Configuring Local MAC Authentication
Network Diagram
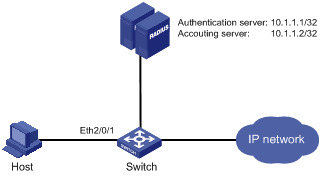
Figure 1-1 Network diagram for local MAC authentication configuration

Networking and Configuration Requirements
As illustrated in Figure 1-1, a host is connected to the switch through port GigabitEthernet 2/0/1.
l Local MAC authentication is required on every port to control user access to the Internet.
l All users belong to domain aabbcc.net.
l Set the offline detect timer to 180 seconds and the quiet timer to 3 minutes.
l A local user uses aaa as the username and 123456 as the password for authentication.
Applicable Product Matrix
|
Product series |
Software version |
Hardware version |
|
S3610 Series Ethernet Switches |
Release 5301, Release 5303 |
All versions |
|
S5510 Series Ethernet Switches |
Release 5301, Release 5303 |
All versions |
|
S5500-SI Series Ethernet Switches |
Release 1207 |
All versions except S5500-20TP-SI |
|
Release 1301 |
S5500-20TP-SI |
|
|
S5500-EI Series Ethernet Switches |
Release 2102 |
All versions |
|
S7500E Series Ethernet Switches |
Release 6100, Release 6300 |
All versions |
Configuration Procedure
1) Configure MAC authentication on the switch.
# Add a local user.
<Switch> system-view
[Switch] local-user aaa
[Switch-luser-aaa] password simple 123456
[Switch-luser-aaa] service-type lan-access
[Switch-luser-aaa] quit
# Configure ISP domain aabbcc.net, and specify to perform local authentication.
[Switch] domain aabbcc.net
[Switch-isp-aabbcc.net] authentication lan-access local
[Switch-isp-aabbcc.net] quit
# Enable MAC authentication globally.
[Switch] mac-authentication
# Enable MAC authentication for port GigabitEthernet 2/0/1.
[Switch] mac-authentication interface GigabitEthernet 2/0/1
# Specify the ISP domain for MAC authentication.
[Switch] mac-authentication domain aabbcc.net
# Set the MAC authentication timers.
[Switch] mac-authentication timer offline-detect 180
[Switch] mac-authentication timer quiet 180
# Specify the MAC authentication to use fixed username aaa and password 123456 to authenticate supplicants.
[Switch] mac-authentication user-name-format fixed account aaa password simple 123456
Complete Configuration
#
system-view
local-user aaa
password simple 123456
service-type lan-access
#
domain aabbcc.net
authentication lan-access local
#
mac-authentication
mac-authentication timer offline-detect 180
mac-authentication timer quiet 180
mac-authentication domain aabbcc.net
mac-authentication user-name-format fixed account aaa password simple 123456
interface GigabitEthernet2/0/1
mac-authentication
#
Configuration Guidelines
You need to specify the service type as lan-access for local users.
Configuring RADIUS Based MAC Authentication
Network Diagram
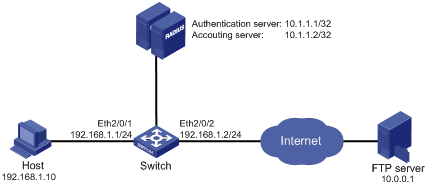
Figure 1-2 Network diagram for RADIUS based MAC authentication configuration
Networking and Configuration Requirements
As illustrated in Figure 1-2, a host is connected to the switch through port Ethernet 2/0/1. The switch authenticates the host through the RADIUS server.
l MAC authentication is required on each port to control user access to the Internet.
l Set the offline detect timer to 180 seconds and the quiet timer to 3 minutes.
Applicable Product Matrix
|
Product series |
Software version |
Hardware version |
|
S3610 Series Ethernet Switches |
Release 5301, Release 5303 |
All versions |
|
S5510 Series Ethernet Switches |
Release 5301, Release 5303 |
All versions |
|
S5500-SI Series Ethernet Switches |
Release 1207 |
All versions except S5500-20TP-SI |
|
Release 1301 |
S5500-20TP-SI |
|
|
S5500-EI Series Ethernet Switches |
Release 2102 |
All versions |
|
S7500E Series Ethernet Switches |
Release 6100, Release 6300 |
All versions |
Configuration Procedure
1) Configure MAC authentication on the switch
# Configure the IP addresses of the interfaces. (Omitted)
# Configure a RADIUS scheme.
<Switch> system-view
[Switch] radius scheme 2000
[Switch-radius-2000] primary authentication 10.1.1.1 1812
[Switch-radius-2000] primary accounting 10.1.1.2 1813
[Switch-radius-2000] key authentication abc
[Switch-radius-2000] key accounting abc
[Switch-radius-2000] user-name-format without-domain
[Switch-radius-2000] quit
# Create domain 2000 and specify the AAA schemes for the ISP domain.
[Switch] domain 2000
[Switch-isp-2000] authentication default radius-scheme 2000
[Switch-isp-2000] authorization default radius-scheme 2000
[Switch-isp-2000] accounting default radius-scheme 2000
[Switch-isp-2000] quit
# Enable MAC authentication globally.
[Switch] mac-authentication
# Enable MAC authentication for port Ethernet 2/0/1.
[Switch] mac-authentication interface Ethernet 2/0/1
# Specify the ISP domain for MAC authentication.
[Switch] mac-authentication domain 2000
# Set the MAC authentication timers.
[Switch] mac-authentication timer offline-detect 180
[Switch] mac-authentication timer quiet 180
# Specify the MAC authentication to use fixed username aaa and password 123456 to authenticate supplicants.
[Switch] mac-authentication user-name-format fixed account aaa password simple 123456
Complete Configuration
#
radius scheme 2000
primary authentication 10.1.1.1
primary accounting 10.1.1.2
key authentication abc
key accounting abc
user-name-format without-domain
#
domain 2000
authentication default radius-scheme 2000
authorization default radius-scheme 2000
accounting default radius-scheme 2000
#
mac-authentication
mac-authentication timer offline-detect 180
mac-authentication timer quiet 180
mac-authentication domain 2000
mac-authentication user-name-format fixed account aaa password simple 123456
#
interface Ethernet2/0/1
mac-authentication
#
Configuration Guidelines
l The username and password configured on the RADIUS server must be consistent with those configured on the switch for MAC authentication.
l The authentication and accounting keys configured on the RADIUS server must be consistent with those configured on the switch. Otherwise, authentication will fail.
Configuring ACL Assignment
Network Diagram
Figure 1-3 Network diagram for ACL assignment configuration
Networking and Configuration Requirements
As shown in Figure 1-3, a host is connected to port Ethernet 2/0/1 of the switch and must pass MAC authentication to access the Internet. An RADIUS server cluster takes the responsibility of authentication. An FTP server with the IP address 10.0.0.1 is on the Internet.
l On port Ethernet 2/0/1 of the switch, enable MAC authentication and configure ACL 3000.
l Configure the authentication server to assign ACL 3000 to the switch as the authorization ACL after the host passes authentication, so that the host can access the Internet but cannot access the FTP server.
Applicable Product Matrix
|
Product series |
Software version |
Hardware version |
|
S3610 Series Ethernet Switches |
Release 5301, Release 5303 |
All versions |
|
S5510 Series Ethernet Switches |
Release 5301, Release 5303 |
All versions |
|
S5500-SI Series Ethernet Switches |
Release 1207 |
All versions except S5500-20TP-SI |
|
Release 1301 |
S5500-20TP-SI |
|
|
S5500-EI Series Ethernet Switches |
Release 2102 |
All versions |
|
S7500E Series Ethernet Switches |
Release 6100, Release 6300 |
All versions |
Configuration Procedure
1) Configure MAC authentication on the switch
# Configure the IP addresses of the interfaces. (Omitted)
# Configure the RADIUS scheme.
<Switch> system-view
[Switch] radius scheme 2000
[Switch-radius-2000] primary authentication 10.1.1.1 1812
[Switch-radius-2000] primary accounting 10.1.1.2 1813
[Switch-radius-2000] key authentication abc
[Switch-radius-2000] key accounting abc
[Switch-radius-2000] user-name-format without-domain
[Switch-radius-2000] quit
# Create an ISP domain and specify the AAA schemes for the ISP domain.
[Switch] domain 2000
[Switch-isp-2000] authentication default radius-scheme 2000
[Switch-isp-2000] authorization default radius-scheme 2000
[Switch-isp-2000] accounting default radius-scheme 2000
[Switch-isp-2000] quit
# Configure ACL 3000 to deny packets destined for 10.0.0.1.
[Switch] acl number 3000
[Switch-acl-adv-3000] rule 0 deny ip destination 10.0.0.1 0
[Switch-acl-adv-3000] quit
# Enable MAC authentication globally.
[Switch] mac-authentication
# Enable MAC authentication for port Ethernet 2/0/1.
[Switch] mac-authentication interface Ethernet 2/0/1
# Specify the ISP domain for MAC authentication.
[Switch] mac-authentication domain 2000
# Set the MAC authentication timers.
[Switch] mac-authentication timer offline-detect 180
[Switch] mac-authentication timer quiet 180
# Specify MAC authentication to use a MAC address with hyphen as the username and password to authenticate supplicants.
[Switch] mac-authentication user-name-format mac-address with-hyphen
Complete Configuration
#
radius scheme 2000
primary authentication 10.1.1.1
primary accounting 10.1.1.2
key authentication abc
key accounting abc
user-name-format without-domain
#
domain 2000
authentication default radius-scheme 2000
authorization default radius-scheme 2000
accounting default radius-scheme 2000
#
acl number 3000
rule 0 deny ip destination 10.0.0.1 0
#
mac-authentication
mac-authentication timer offline-detect 180
mac-authentication timer quiet 180
mac-authentication domain 2000
mac-authentication user-name-format mac-address with-hyphen
#
interface Ethernet2/0/1
mac-authentication
#
Configuration Guidelines
l The authentication and accounting keys configured on the RADIUS server must be consistent with those configured on the switch. Otherwise, the MAC authentication will fail.
l The username and password type configured on the RADIUS server must be consistent with that configured on the switch for MAC authentication.
l The letters in the MAC address that serves as the authentication username and password must be in lowercase.
