- Table of Contents
-
- 03-CLI configuration examples (AC+fit AP)
- 01-HTTPS Login Configuration Examples
- 02-SSH Configuration Examples
- 03-License Management Configuration Examples
- 04-IPv6 URL Redirection Configuration Examples
- 05-AP Association with the AC at Layer 2 Configuration Examples
- 06-AP Association with the AC at Layer 2 (IPv6) Configuration Examples
- 07-Auto AP Configuration Examples
- 08-AP Association with the AC at Layer 3 Configuration Examples
- 09-AP Association with the AC at Layer 3 (IPv6) Configuration Examples
- 10-WEP Encryption Configuration Examples
- 11-PSK Encryption Configuration Examples
- 12-WPA3-SAE PSK Encryption Configuration Examples
- 13-WLAN Access (IPv6) Configuration Examples
- 14-Policy-Based Forwarding with Dual Gateways Configuration Examples
- 15-Scheduled Configuration Deployment by AP Group Configuration Examples
- 16-Inter-AC Roaming with Static Client VLAN Allocation Configuration Examples
- 17-Service Template and Radio Binding Configuration Examples
- 18-Scheduled WLAN Access Services Configuration Examples
- 19-Local Portal Authentication Configuration Examples
- 20-HTTPS-Based Local Portal Authentication Configuration Examples
- 21-Remote Portal Authentication Configuration Examples
- 22-Local Portal Authentication through LDAP Server Configuration Examples
- 23-Local Portal Authentication and SSID-based Authentication Page Pushing Configuration Examples
- 24-Local Portal MAC-Trigger Authentication Configuration Examples
- 25-Portal MAC-Trigger Authentication Configuration Examples
- 26-Local Forwarding Mode and Local Portal MAC-Trigger Authentication Configuration Examples
- 27-Local Portal Authentication (IPv6) Configuration Examples
- 28-Local Portal Authentication through LDAP Server (IPv6) Configuration Examples
- 29-Remote Portal Authentication (IPv6) Configuration Examples
- 30-Portal MAC-Trigger Authentication (IPv6) Configuration Example
- 31-Remote Portal Authentication with User Profile Authorization Configuration Examples
- 32-Portal Fail-Permit Configuration Examples
- 33-Local MAC Authentication Configuration Examples
- 34-MAC Authentication and PSK Authentication Configuration Examples
- 35-Remote MAC and Portal Authentication and Transparent Authentication Configuration Examples
- 36-Remote AP and Remote Portal MAC-Trigger Authentication Configuration Examples
- 37-MAC Authentication with Guest VLAN Assignment Configuration Examples
- 38-MAC Authentication with Guest VLAN Assignment (IPv6) Configuration Examples
- 39-Local MAC-Then-802.1X Authentication Configuration Examples
- 40-Local 802.1X Authentication Configuration Examples
- 41-Local RADIUS-Based 802.1X Authentication in EAP Relay Mode Configuration Examples
- 42-Remote 802.1X Authentication Configuration Examples
- 43-Remote 802.1X Authentication (IPv6) Configuration Examples
- 44-Remote 802.1X Authentication in WPA3-Enterprise Mode Configuration Examples
- 45-802.1X Authentication with ACL Assignment Through IMC Server Configuration Examples
- 46-802.1X Authentication with User Profile Assignment Through IMC Server Configuration Examples
- 47-EAD Authentication Configuration Examples
- 48-EAD Authentication (IPv6) Configuration Examples
- 49-Local Forwarding Mode and Local Portal Authentication Configuration Examples
- 50-Local Forwarding Mode Direct Portal Authentication Configuration Examples
- 51-Local Forwarding Mode Direct Portal Authentication (IPv6) Configuration Examples
- 52-Local Forwarding Configuration Examples
- 53-Remote AP Configuration Examples
- 54-WIPS Configuration Examples
- 55-WIPS Countermeasures Against All SSIDs Configuration Examples
- 56-IP Source Guard (IPv4) Configuration Examples
- 57-IP Source Guard (IPv6) Configuration Examples
- 58-IRF Setup with Members Directly Connected Configuration Examples
- 59-IRF Setup with Members Not Directly Connected Configuration Examples
- 60-IRF Setup with Members in One Chassis Configuration Examples
- 61-IRF Setup with Members in Different Chassis Configuration Examples
- 62-Dual-Link Backup Configuration Examples
- 63-Remote 802.1X Auth on AC Hierarchy Network with Dual-Link Central AC Backup Configuration Examples
- 64-Remote Portal Auth on AC Hierarchy Network with Dual-Link Central AC Backup Configuration Examples
- 65-OAuth-Based Portal MAC-Trigger Auth on Local-Forwarding Dual-Link Backup Configuration Examples
- 66-Dual-Link Backup OAuth-Based Portal Auth in Local Forwarding Configuration Examples
- 67-Dual-Link Backup Remote Portal MAC-Trigger Auth in Local Forwarding Configuration Examples
- 68-Dual-Link Backup Remote Portal and Transparent MAC Auth in Local Forwarding Configuration Examples
- 69-Dual-Link Backup Remote Portal Auth in Local Forwarding Configuration Examples
- 70-Dual-Link Backup Remote Portal and MAC Auth in Centralized Forward Configuration Examples
- 71-Dual-Link Backup Remote Portal Auth in Centralized Forwarding Configuration Examples
- 72-Dual-Link Backup Lightweight Portal Auth in Centralized Forwarding Configuration Examples
- 73-Dual-Link Backup OAuth-Based Portal Auth in Centralized Forwarding Configuration Examples
- 74-Dual-Link Backup Remote Portal MAC-Trigger Auth in Centralized Forwarding Configuration Examples
- 75-Remote 802.1X Auth on a Dual-Link AC Backup Network Configuration Examples
- 76-Remote MAC Auth on a Dual-Link AC Backup Network Configuration Examples
- 77-Remote 802.1X Authentication on an AC Hierarchy Network Configuration Examples
- 78-Remote 802.1X Authentication Configuration Examples
- 79-WLAN Probe Configuration Examples
- 80-Multicast Optimization Configuration Examples
- 81-Client Rate Limiting Configuration Examples
- 82-Inter-AC Roaming Configuration Examples
- 83-Inter-AC Roaming (IPv6) Configuration Examples
- 84-WLAN Load Balancing Configuration Examples
- 85-Static Blacklist Configuration Examples
- 86-Client Quantity Control Configuration Examples
- 87-AP License Synchronization Configuration Examples
- 88-iBeacon Management Configuration Examples
- 89-Mesh Link Establishment Between a Fit AP and a Fat AP Configuration Examples
- 90-Mesh Link Establishment Between Fit APs Configuration Examples
- 91-Auto-DFS and Auto-TPC Configuration Examples
- 92-AP Image Downloading Configuration Examples
- 93-Dual-Uplink Interfaces Configuration Guide
- 94-Internal-to-External Access Through NAT Configuration Examples
- 95-Layer 2 Static Aggregation Configuration Examples
- 96-Layer 2 Multicast Configuration Examples
- 97-Static VLAN Allocation Configuration Examples
- 98-URL Redirection Configuration Examples
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 75-Remote 802.1X Auth on a Dual-Link AC Backup Network Configuration Examples | 248.47 KB |
|
|
|
H3C Access Controllers |
|
Comware 7 Remote 802.1X Authentication on a Dual-Link AC Backup Network |
|
Configuration Examples |
|
|
Copyright © 2022 New H3C Technologies Co., Ltd. All rights reserved.
No part of this manual may be reproduced or transmitted in any form or by any means without prior written consent of New H3C Technologies Co., Ltd.
Except for the trademarks of New H3C Technologies Co., Ltd., any trademarks that may be mentioned in this document are the property of their respective owners.
The information in this document is subject to change without notice.
Contents
General restrictions and guidelines
Example: Configuring remote 802.1X authentication on a dual-link AC backup network
Introduction
The following information provides an example of configuring remote 802.1X authentication for clients on a dual-link AC backup network.
Prerequisites
The following information applies to Comware 7-based access controllers and access points. Procedures and information in the examples might be slightly different depending on the software or hardware version of the access controllers and access points.
The configuration examples were created and verified in a lab environment, and all the devices were started with the factory default configuration. When you are working on a live network, make sure you understand the potential impact of every command on your network.
The following information is provided based on the assumption that you have basic knowledge of WLAN access, WLAN user security, WLAN user access authentication, 802.1X, AAA, and WLAN high availability features.
General restrictions and guidelines
Make sure the master and backup ACs have the same RADIUS, service template, and radio settings.
Make sure the master and backup ACs use the same version of software.
Example: Configuring remote 802.1X authentication on a dual-link AC backup network
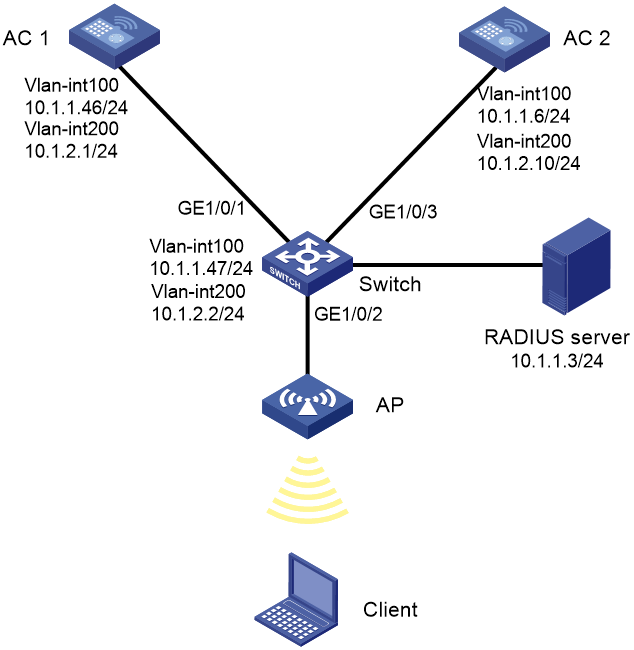
Network configuration
· The AP is attached to a switch dual-homed to AC 1 (the master AC) and AC 2 (the backup AC).
· The switch acts as a DHCP server to assign IP addresses to the AP and the client.
· The network deploys a RADIUS server that runs IMC for 802.1X authentication.
Configure the devices to meet the following requirements:
· The ACs operate in active/standby mode to provide centralized forwarding. When AC 1 fails, the AP associates with AC 2. When AC 1 recovers, the AP re-associates with AC 1.
· The ACs act as the authenticator and use the RADIUS server to perform authentication, authorization, and accounting for the client.
· The client accesses the wireless network through VLAN 200 and performs RADIUS-based 802.1X authentication.
· Open system authentication is used to authenticate the client at the data link layer. This is the default authentication method.
· The 802.1X AKM mode is used to secure data transmission between the client and the AP.
· The cipher suite used for frame encryption is CCMP.
Restrictions and guidelines
When you configure remote 802.1X authentication on a dual-link AC backup network, follow these restrictions and guidelines:
· Use the serial ID labeled on the AP's rear panel to specify an AP.
· For the IMC server to dynamically change client authorization information or forcibly disconnect a client, enable the RADIUS session-control feature on the ACs.
· To avoid dynamic authorization failures, configure the RADIUS Dynamic Authorization Extensions Server (DAS) feature.
Procedures
Configuring AC 1
1. Configure interfaces on the AC:
# Create VLAN 100 and VLAN-interface 100, and assign an IP address to the VLAN interface. The AC will use this IP address to establish the master CAPWAP control and data tunnels with the AP.
<AC1> system-view
[AC1] vlan 100
[AC1-vlan100] quit
[AC1] interface vlan-interface 100
[AC1-Vlan-interface100] ip address 10.1.1.46 24
[AC1-Vlan-interface100] quit
# Create VLAN 200 and VLAN-interface 200, and assign an IP address to the VLAN interface. VLAN 200 will be used for client access.
[AC1] vlan 200
[AC1-vlan200] quit
[AC1] interface vlan-interface 200
[AC1-Vlan-interface200] ip address 10.1.2.1 24
[AC1-Vlan-interface200] quit
# Configure GigabitEthernet 1/0/1 (the port connected to the switch) as a trunk port, and assign the port to VLANs 100 and 200.
[AC1] interface gigabitethernet1/0/1
[AC1-GigabitEthernet1/0/1] port link-type trunk
[AC1-GigabitEthernet1/0/1] port trunk permit vlan 100 200
[AC1-GigabitEthernet1/0/1] quit
2. Configure RADIUS-based 802.1X authentication:
# Create RADIUS scheme radius1 and enter its view.
[AC1] radius scheme radius1
# Specify the IP addresses of the primary authentication and accounting RADIUS servers.
[AC1-radius-radius1] primary authentication 10.1.1.3
[AC1-radius-radius1] primary accounting 10.1.1.3
# Specify the shared keys for RADIUS authentication and accounting.
[AC1-radius-radius1] key authentication simple 12345
[AC1-radius-radius1] key accounting simple 12345
# Specify IP address 10.1.2.1 as the source IP address for outgoing RADIUS packets.
[AC1-radius-radius1] nas-ip 10.1.2.1
[AC1-radius-radius1] quit
# Create ISP domain dom1 and enter its view.
[AC1] domain dom1
# Configure the ISP domain to use RADIUS scheme radius1 for 802.1X user authentication, authorization, and accounting.
[AC1-isp-dom1] authentication lan-access radius-scheme radius1
[AC1-isp-dom1] authorization lan-access radius-scheme radius1
[AC1-isp-dom1] accounting lan-access radius-scheme radius1
[AC1-isp-dom1] quit
# Enable RADIUS session-control.
[AC1] radius session-control enable
# Enable RADIUS DAS and enter its view.
[AC1] radius dynamic-author server
# Specify the RADIUS server at 10.1.1.3 as a DAC and set the shared key to 12345 in plain text for authenticating DAE packets from the RADIUS server.
[AC1-radius-da-server] client ip 10.1.1.3 key simple 12345
[AC1-radius-da-server] quit
# Configure EAP relay as the method for the AC to exchange packets with the RADIUS server.
[AC1] dot1x authentication-method eap
3. Configure a manual AP:
# Create manual AP office and specify the AP model and serial ID.
[AC1] wlan ap office model WA5320
[AC1-wlan-ap-office] serial-id 219801A0YD8166E00012
# Set the AP connection priority to 7.
[AC1-wlan-ap-office] priority 7
# Specify AC 2 as a backup AC to AC 1.
[AC1-wlan-ap-office] backup-ac ip 10.1.1.6
# Enable master CAPWAP tunnel preemption.
[AC1-wlan-ap-office] wlan tunnel-preempt enable
[AC1-wlan-ap-office] quit
4. Configure a service template:
# Create service template service and enter its view.
[AC1] wlan service-template service
# Set the SSID to service.
[AC1-wlan-st-service] ssid service
# Assign clients coming online through the service template to VLAN 200.
[AC1-wlan-st-service] vlan 200
# Set the AKM mode to 802.1X.
[AC1-wlan-st-service] akm mode dot1x
# Specify the CCMP cipher suite and enable the RSN IE in beacon and probe responses.
[AC1-wlan-st-service] cipher-suite ccmp
[AC1-wlan-st-service] security-ie rsn
# Set the access authentication mode to 802.1X authentication.
[AC1-wlan-st-service] client-security authentication-mode dot1x
# Specify ISP domain dom1 as the 802.1X authentication domain.
[AC1-wlan-st-service] dot1x domain dom1
# Enable the service template.
[AC1-wlan-st-service] service-template enable
[AC1-wlan-st-service] quit
5. Configure a radio and bind service template service to the radio:
# Enter the view of AP office.
[AC1] wlan ap office
# Enter the view of radio 1, and bind service template service to radio 1.
[AC1-wlan-ap-office] radio 1
[AC1-wlan-ap-office-radio-1] service-template service
# Enable radio 1.
[AC1-wlan-ap-office-radio-1] radio enable
[AC1-wlan-ap-office-radio-1] quit
[AC1-wlan-ap-office] quit
Configuring AC 2
1. Configure interfaces on the AC:
# Create VLAN 100 and VLAN-interface 100, and assign an IP address to the VLAN interface. The AC will use this IP address to establish the backup CAPWAP control and data tunnels with the AP.
<AC2> system-view
[AC2] vlan 100
[AC2-vlan100] quit
[AC2] interface vlan-interface 100
[AC2-Vlan-interface100] ip address 10.1.1.6 24
[AC2-Vlan-interface100] quit
# Create VLAN 200 and VLAN-interface 200, and assign an IP address to the VLAN interface. VLAN 200 will be used for client access.
[AC2] vlan 200
[AC2-vlan200] quit
[AC2] interface vlan-interface 200
[AC2-Vlan-interface200] ip address 10.1.2.10 24
[AC2-Vlan-interface200] quit
# Configure GigabitEthernet 1/0/1 (the port connected to the switch) as a trunk port, and assign the port to VLANs 100 and 200.
[AC2] interface gigabitethernet1/0/1
[AC2-GigabitEthernet1/0/1] port link-type trunk
[AC2-GigabitEthernet1/0/1] port trunk permit vlan 100 200
[AC2-GigabitEthernet1/0/1] quit
2. Configure RADIUS-based 802.1X authentication:
# Create RADIUS scheme radius1 and enter its view.
[AC2] radius scheme radius1
# Specify the IP addresses of the primary authentication and accounting RADIUS servers.
[AC2-radius-radius1] primary authentication 10.1.1.3
[AC2-radius-radius1] primary accounting 10.1.1.3
# Specify the shared keys for RADIUS authentication and accounting.
[AC2-radius-radius1] key authentication simple 12345
[AC2-radius-radius1] key accounting simple 12345
# Specify IP address 10.1.2.10 as the source IP address for outgoing RADIUS packets.
[AC2-radius-radius1] nas-ip 10.1.2.10
[AC2-radius-radius1] quit
# Create ISP domain dom1 and enter its view.
[AC2] domain dom1
# Configure the ISP domain to use RADIUS scheme radius1 for 802.1X user authentication, authorization, and accounting.
[AC2-isp-dom1] authentication lan-access radius-scheme radius1
[AC2-isp-dom1] authorization lan-access radius-scheme radius1
[AC2-isp-dom1] accounting lan-access radius-scheme radius1
[AC2-isp-dom1] quit
# Enable RADIUS session-control.
[AC2] radius session-control enable
# Enable RADIUS DAS and enter its view.
[AC2] radius dynamic-author server
# Specify the RADIUS server at 10.1.1.3 as a DAC and set the shared key to 12345 in plain text for authenticating DAE packets from the RADIUS server.
[AC2-radius-da-server] client ip 10.1.1.3 key simple 12345
[AC2-radius-da-server] quit
# Configure EAP relay as the method for the AC to exchange packets with the RADIUS server.
[AC2] dot1x authentication-method eap
3. Configure a manual AP:
# Create manual AP office and specify the AP model and serial ID.
[AC2] wlan ap office model WA5320
[AC2-wlan-ap-office] serial-id 219801A0YD8166E00012
# Set the AP connection priority to 5.
[AC2-wlan-ap-office] priority 5
# Specify AC 1 as a backup AC to AC 2.
[AC2-wlan-ap-office] backup-ac ip 10.1.1.46
# Enable master CAPWAP tunnel preemption.
[AC2-wlan-ap-office] wlan tunnel-preempt enable
[AC2-wlan-ap-office] quit
4. Configure a service template:
# Create service template service and enter its view.
[AC2] wlan service-template service
# Set the SSID to service.
[AC2-wlan-st-service] ssid service
# Assign clients coming online through the service template to VLAN 200.
[AC2-wlan-st-service] vlan 200
# Set the AKM mode to 802.1X.
[AC2-wlan-st-service] akm mode dot1x
# Specify the CCMP cipher suite and enable the RSN IE in beacon and probe responses.
[AC2-wlan-st-service] cipher-suite ccmp
[AC2-wlan-st-service] security-ie rsn
# Set the access authentication mode to 802.1X authentication.
[AC2-wlan-st-service] client-security authentication-mode dot1x
# Specify ISP domain dom1 as the 802.1X authentication domain.
[AC2-wlan-st-service] dot1x domain dom1
# Enable the service template.
[AC2-wlan-st-service] service-template enable
[AC2-wlan-st-service] quit
5. Configure a radio and bind service template service to the radio:
# Enter the view of AP office.
[AC2] wlan ap office
# Enter the view of radio 1, and bind service template service to radio 1.
[AC2-wlan-ap-office] radio 1
[AC2-wlan-ap-office-radio-1] service-template service
# Enable radio 1.
[AC2-wlan-ap-office-radio-1] radio enable
[AC2-wlan-ap-office-radio-1] quit
[AC2-wlan-ap-office] quit
Configuring the switch
# Create VLAN 100. The switch will use this VLAN to forward the traffic on the CAPWAP tunnels between the ACs and AP.
<Switch> system-view
[Switch] vlan 100
[Switch-vlan100] quit
# Create VLAN 200. The switch will use this VLAN to forward packets for the client.
[Switch] vlan 200
[Switch-vlan200] quit
# Configure GigabitEthernet 1/0/1 (the port connected to AC 1) as a trunk port, and assign the trunk port to VLANs 100 and 200.
[Switch] interface gigabitethernet 1/0/1
[Switch-GigabitEthernet1/0/1] port link-type trunk
[Switch-GigabitEthernet1/0/1] port trunk permit vlan 100 200
[Switch-GigabitEthernet1/0/1] quit
# Configure GigabitEthernet 1/0/3 (the port connected to AC 2) as a trunk port, and assign the trunk port to VLANs 100 and 200.
[Switch] interface gigabitethernet 1/0/3
[Switch-GigabitEthernet1/0/3] port link-type trunk
[Switch-GigabitEthernet1/0/3] port trunk permit vlan 100 200
[Switch-GigabitEthernet1/0/3] quit
# Configure GigabitEthernet 1/0/2 (the port connected to the AP) as an access port. Assign the access port to VLAN 100.
[Switch] interface gigabitethernet 1/0/2
[Switch-GigabitEthernet1/0/2] port link-type access
[Switch-GigabitEthernet1/0/2] port access vlan 100
# Enable PoE on GigabitEthernet 1/0/2.
[Switch-GigabitEthernet1/0/2] poe enable
[Switch-GigabitEthernet1/0/2] quit
# Assign an IP address to VLAN-interface 100.
[Switch] interface vlan-interface 100
[Switch-Vlan-interface100] ip address 10.1.1.47 24
[Switch-Vlan-interface100] quit
# Assign an IP address to VLAN-interface 200.
[Switch] interface vlan-interface 200
[Switch-Vlan-interface200] ip address 10.1.2.2 24
[Switch-Vlan-interface200] quit
# Configure DHCP address pool 100. The switch will use this pool to assign an IP address to the AP.
[Switch] dhcp server ip-pool 100
[Switch-dhcp-pool-100] network 10.1.1.0 mask 255.255.255.0
[Switch-dhcp-pool-100] gateway-list 10.1.1.47
[Switch-dhcp-pool-100] quit
# Configure DHCP address pool 200. The switch will use this pool to assign an IP address to the client. In this example, the address of the DNS server is 10.1.2.2 (the gateway address). You must replace it with the actual address of the DNS server on your network.
[Switch] dhcp server ip-pool 200
[Switch-dhcp-pool-200] network 10.1.2.0 mask 255.255.255.0
[Switch-dhcp-pool-200] gateway-list 10.1.2.2
[Switch-dhcp-pool-200] dns-list 10.1.2.2
[Switch-dhcp-pool-200] quit
# Enable DHCP
[Switch] dhcp enable
Configuring the RADIUS server
In this example, the RADIUS server runs IMC PLAT 7.3 (E0605) and IMC UAM 7.1 (E0302).
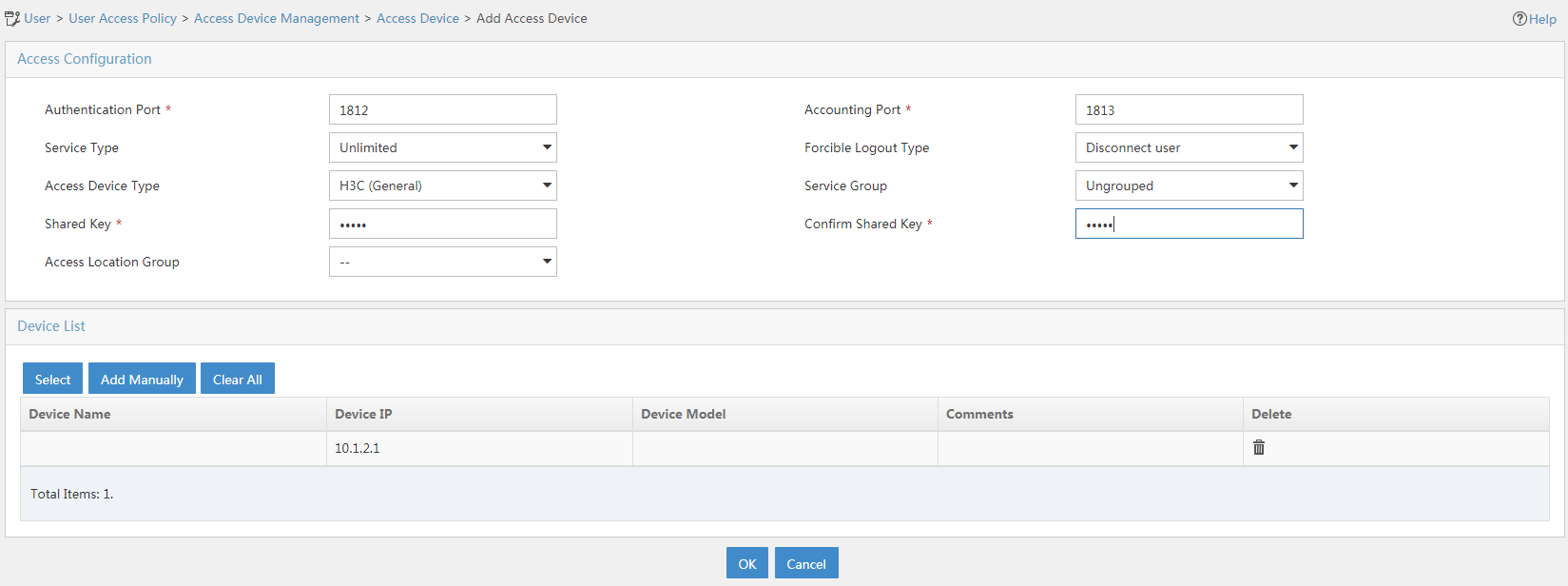
Adding AC 1 and AC 2 to IMC as access devices
This example only illustrates the process to add AC 1 to IMC as an access device. You can add access device AC 2 to IMC in the same way AC 1 is added to IMC as an access device.
To add AC 1 to IMC as an access device:
1. Log in to IMC and click the User tab.
2. From the navigation tree, select User Access Policy > Access Device Management > Access Device.
3. Click Add.
The Add Access Device page opens.
4. In the Access Configuration area, configure the following parameters, as shown in Figure 2:
¡ Enter 12345 in the Shared Key and Confirm Shared Key fields.
¡ Use the default values for other parameters.
5. In the Device List area, click Select or Add Manually to add AC 1 at 10.1.2.1 as an access device.
6. Click OK.
Figure 2 Adding an access device
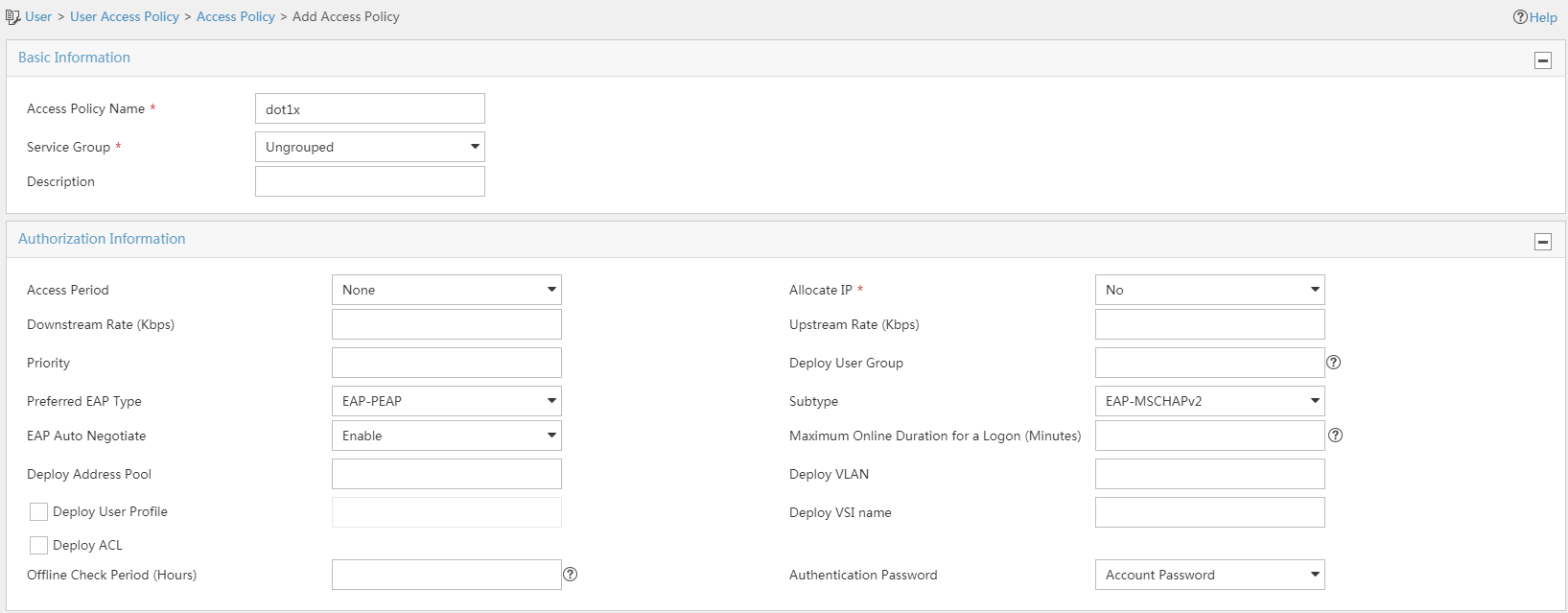
Adding an access policy
1. Click the User tab.
2. From the navigation tree, select User Access Policy > Access Policy.
3. Click Add.
4. On the Add Access Policy page, configure the following parameters, as shown in Figure 3:
¡ Enter dot1x in the Access Policy Name field.
¡ Select EAP-PEAP from the Preferred EAP Type list, and select EAP-MSCHAPv2 from the Subtype list.
The certificate subtype on the IMC server must be the same as the identity authentication method configured on the client.
Figure 3 Adding an access policy
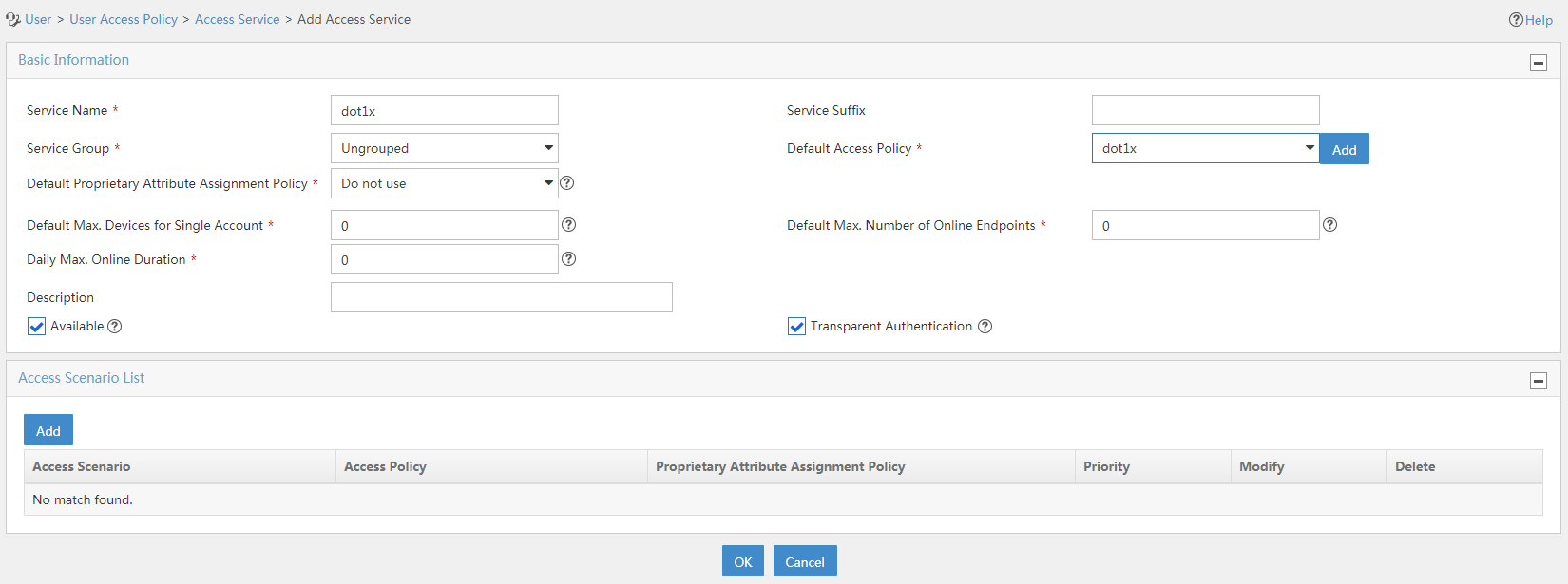
Adding an access service
1. Click the User tab.
2. From the navigation tree, select User Access Policy > Access Service.
3. Click Add.
4. On the Add Access Service page, configure the following parameters, as shown in Figure 4:
¡ Enter dot1x in the Service Name field.
¡ Select dot1x from the Default Access Policy list.
5. Click OK.
Figure 4 Adding an access service
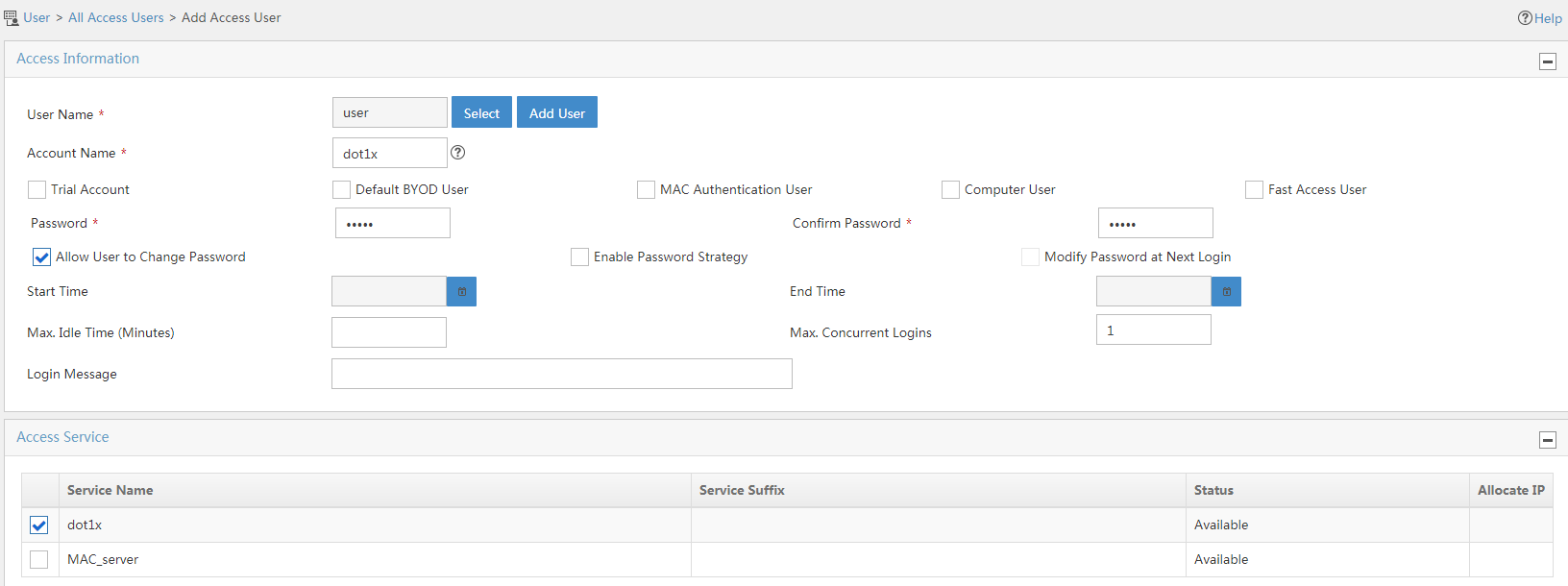
Adding an access user
1. Click the User tab.
2. From the navigation tree, select Access User > Access User.
The access user list opens.
3. Click Add.
The Add Access User page opens.
4. In the Access Information area, configure the following parameters, as shown in Figure 5:
a. Click Select or Add User to associate the user with IMC Platform user user.
b. Enter dot1x in the Account Name field.
c. Enter dot1x123 in the Password and Confirm Password fields.
5. In the Access Service area, select dot1x from the list.
6. Click OK.
Figure 5 Adding an access user account
Configuring the client
Prerequisites
Make sure the client has been installed with the EAP-PEAP certificate.
This example uses Windows 7 Service Pack 1 to describe the procedure.
Procedure
Perform the following tasks to create wireless network service and configure properties for the wireless network:
1. Click Start, and then select Control Panel.
2. In the control panel, click View network status and tasks below Network and Internet.
3. Click Manage wireless networks.
4. Click Add.
5. Click Manually create a network profile.
6. Configure the wireless network profile:
¡ Set the network name to service. (The network name is the same as the SSID in the service template on the ACs.)
¡ Set the security type to WPA2-Enterprise.
¡ Set the encryption type to AES.
¡ Retain the default settings for other parameters.
7. Click Next.
8. After the wireless network is added successfully, click Change connection settings.
9. In the wireless network properties dialog box, click the Security tab.
10. Select Microsoft: Protected EAP (PEAP) as the network authentication method, and clear the Remember my credentials for this connection each time I'm logged on option.
11. Click Settings next to Microsoft: Protected EAP (PEAP).
12. In the Protected EAP Properties dialog box that opens, configure the following parameters:
a. Clear the Validate server certificate and Enable Fast Reconnect options.
b. Set the authentication method to Secured password (EAP MSCHAP v2).
c. Click Configure next to Secured password (EAP MSCHAP v2).
d. In the EAP MSCHAPv2 Properties dialog box that opens, clear the Automatically use my Windows logon name and password (and domain if any) option, and then click OK.
e. Click OK.
13. In the wireless network properties dialog box, click Advanced settings.
14. On the 802.1X settings tab, select user authentication as the authentication mode.
15. On the 802.11 settings tab, clear the Enable Pairwise Master Key (PMK) caching option, and then click OK.
16. Click OK.
Verifying the configuration
1. Verify the AC backup and switchover functionality:
# Verify that the AP associates with AC 1 and comes online. (Details not shown.)
# Shut down VLAN-interface 100 on AC 1. (Details not shown.)
# Verify that the AP automatically associates with AC 2 and comes online in less than 3 minutes, during which traffic is interrupted. The state of the AP changes to R/M (Run/Master) on AC 2 after it comes up.
[AC2] display wlan ap all
Total number of APs: 1
Total number of connected APs: 1
Total number of connected manual APs: 1
Total number of connected auto APs: 0
Total number of connected common APs: 1
Total number of connected WTUs: 0
Total number of inside APs: 0
Maximum supported APs: 512
Remaining APs: 512
Total AP licenses: 128
Local AP licenses: 128
Server AP licenses: 0
Remaining local AP licenses: 127
Sync AP licenses: 0
AP information
State : I = Idle, J = Join, JA = JoinAck, IL = ImageLoad
C = Config, DC = DataCheck, R = Run M = Master, B = Backup
AP name APID State Model Serial ID
office 2 R/M WA5320 219801A0YD8166E00012
# Bring up VLAN-interface 100 on AC 1. (Details not shown.)
# Verify that the AP re-associates with AC 1 and its state changes to R/M (Run/Master) on AC 1 after a successful association. At the same time, the state of the AP changes to R/B on AC 2.
[AC1] display wlan ap all
...
[AC2] display wlan ap all
Total number of APs: 1
Total number of connected APs: 1
Total number of connected manual APs: 1
Total number of connected auto APs: 0
Total number of connected common APs: 1
Total number of connected WTUs: 0
Total number of inside APs: 0
Maximum supported APs: 512
Remaining APs: 512
Total AP licenses: 128
Local AP licenses: 128
Server AP licenses: 0
Remaining local AP licenses: 127
Sync AP licenses: 0
AP information
State : I = Idle, J = Join, JA = JoinAck, IL = ImageLoad
C = Config, DC = DataCheck, R = Run M = Master, B = Backup
AP name APID State Model Serial ID
office 2 R/B WA5320 219801A0YD8166E00012
2. Connect the client to the wireless network. (Details not shown.)
3. On AC 1, perform the following tasks to verify that the client has passed authentication and come online:
# Display detailed WLAN client information.
[AC1] display wlan client verbose
Total number of clients: 1
MAC address : cc3a-61a8-fb8c
IPv4 address : 10.1.2.3
IPv6 address : N/A
Username : user
AID : 1
AP ID : 3
AP name : office
Radio ID : 1
SSID : service
BSSID : 741f-4ad4-1fe0
VLAN ID : 200
Sleep count : 0
Wireless mode : 802.11ac
Channel bandwidth : 80MHz
SM power save : Disabled
Short GI for 20MHz : Supported
Short GI for 40MHz : Supported
Short GI for 80MHz : Supported
Short GI for 160/80+80MHz : Not supported
STBC RX capability : Not supported
STBC TX capability : Not supported
LDPC RX capability : Not supported
SU beamformee capability : Not supported
MU beamformee capability : Not supported
Beamformee STS capability : N/A
Block Ack : N/A
Supported VHT-MCS set : NSS1 0, 1, 2, 3, 4, 5, 6, 7, 8, 9
Supported HT MCS set : 0, 1, 2, 3, 4, 5, 6, 7
Supported rates : 6, 9, 12, 18, 24, 36, 48, 54 Mbps
QoS mode : WMM
Listen interval : 10
RSSI : 0
Rx/Tx rate : 0/0
Authentication method : Open system
Security mode : RSN
AKM mode : 802.1X
Cipher suite : CCMP
User authentication mode : 802.1X
Authorization ACL ID : N/A
Authorization user profile : N/A
Roam status : N/A
Key derivation : SHA1
PMF status : N/A
Forwarding policy name : N/A
Online time : 0days 0hours 0minutes 15seconds
FT status : Inactive
# Display online 802.1X user information.
[AC1] display dot1x connection
Total connections: 1
User MAC address : cc3a-61a8-fb8c
AP name : office
Radio ID : 1
SSID : service
BSSID : 741f-4ad4-1fe0
Username : user
Authentication domain : dom1
IPv4 address : 10.1.2.3
Authentication method : EAP
Initial VLAN : 200
Authorization VLAN : 200
Authorization ACL number : N/A
Authorization user profile : N/A
Termination action : Default
Session timeout period : 36000001 s
Online from : 2015/12/21 11:27:11
Online duration : 0h 1m 1s
Configuration files
· AC 1:
#
dot1x authentication-method eap
#
vlan 1
#
vlan 100
#
vlan 200
#
wlan service-template service
ssid service
vlan 200
akm mode dot1x
cipher-suite ccmp
security-ie rsn
client-security authentication-mode dot1x
dot1x domain dom1
service-template enable
#
interface Vlan-interface100
ip address 10.1.1.46 255.255.255.0
#
interface Vlan-interface200
ip address 10.1.2.1 255.255.255.0
#
interface GigabitEthernet1/0/1
port link-type trunk
port trunk permit vlan 1 100 200
#
radius scheme radius1
primary authentication 10.1.1.3
primary accounting 10.1.1.3
key authentication cipher $c$3$Bb61SHV2ZsVYPJU2+RFB/8ntk0uCQkmxdA==
key accounting cipher $c$3$w03NfxnBmfDuedv9/xo7ESnoxKjowmmX9A==
nas-ip 10.1.2.1
#
radius dynamic-author server
client ip 10.1.1.3 key cipher $c$3$AkTEB7OgMYnCqsfDeplhoAgXUek/rVrLZw==
#
domain dom1
authentication lan-access radius-scheme radius1
authorization lan-access radius-scheme radius1
accounting lan-access radius-scheme radius1
#
wlan ap office model WA5320
serial-id 219801A0YD8166E00012
wlan tunnel-preempt enable
priority 7
backup-ac ip 10.1.1.6
radio 1
radio enable
service-template service
#
· AC 2:
#
dot1x authentication-method eap
#
vlan 1
#
vlan 100
#
vlan 200
#
wlan service-template service
ssid service
vlan 200
akm mode dot1x
cipher-suite ccmp
security-ie rsn
client-security authentication-mode dot1x
dot1x domain dom1
service-template enable
#
interface Vlan-interface100
ip address 10.1.1.6 255.255.255.0
#
interface Vlan-interface200
ip address 10.1.2.10 255.255.255.0
#
interface GigabitEthernet1/0/3
port link-type trunk
port trunk permit vlan 1 100 200
#
radius scheme radius1
primary authentication 10.1.1.3
primary accounting 10.1.1.3
key authentication cipher $c$3$Bb61SHV2ZsVYPJU2+RFB/8ntk0uCQkmxdA==
key accounting cipher $c$3$w03NfxnBmfDuedv9/xo7ESnoxKjowmmX9A==
nas-ip 10.1.2.10
#
radius dynamic-author server
client ip 10.1.1.3 key cipher $c$3$AkTEB7OgMYnCqsfDeplhoAgXUek/rVrLZw==
#
domain dom1
authentication lan-access radius-scheme radius1
authorization lan-access radius-scheme radius1
accounting lan-access radius-scheme radius1
#
wlan ap office model WA5320
serial-id 219801A0YD8166E00012
wlan tunnel-preempt enable
priority 5
backup-ac ip 10.1.1.46
radio 1
radio enable
service-template service
#
· Switch:
#
dhcp enable
#
vlan 1
#
vlan 100
#
vlan 200
#
dhcp server ip-pool 100
gateway-list 10.1.1.47
network 10.1.1.0 mask 255.255.255.0
#
dhcp server ip-pool 200
gateway-list 10.1.2.2
dns-list 10.1.2.2
network 10.1.2.0 mask 255.255.255.0
#
interface Vlan-interface100
ip address 10.1.1.47 255.255.255.0
#
interface Vlan-interface200
ip address 10.1.2.2 255.255.255.0
#
interface GigabitEthernet1/0/1
port link-type trunk
port trunk permit vlan 1 100 200
#
interface GigabitEthernet1/0/2
port link-type access
port access vlan 100
poe enable
#
#
interface GigabitEthernet1/0/3
port link-type trunk
port trunk permit vlan 1 100 200
#
Related documentation
· AP and WT Management Configuration Guide in H3C Access Controllers Configuration Guides
· AP and WT Management Command Reference in H3C Access Controllers Command References
· High Availability Configuration Guide in H3C Access Controllers Configuration Guides
· High Availability Command Reference in H3C Access Controllers Command References
· User Access and Authentication Configuration Guide in H3C Access Controllers Configuration Guides
· User Access and Authentication Command Reference in H3C Access Controllers Command References
· WLAN Access Configuration Guide in H3C Access Controllers Configuration Guides
· WLAN Access Command Reference in H3C Access Controllers Command References