87-MSR系列路由器总部双出口固定IP、分支动态地址IPsec备份的配置举例
本章节下载: 87-MSR系列路由器总部双出口固定IP、分支动态地址IPsec备份的配置举例 (146.65 KB)
MSR系列路由器总部双出口固定IP、分支动态地址IPsec备份的配置举例
|
Copyright © 2014 杭州华三通信技术有限公司 版权所有,保留一切权利。 非经本公司书面许可,任何单位和个人不得擅自摘抄、复制本文档内容的部分或全部, 并不得以任何形式传播。本文档中的信息可能变动,恕不另行通知。 |
|
目 录
本文档介绍总部双出口固定IP、分支动态地址IPSec备份的配置举例。
本文档不严格与具体软、硬件版本对应,如果使用过程中与产品实际情况有差异,请参考相关产品手册,或以设备实际情况为准。
本文档中的配置均是在实验室环境下进行的配置和验证,配置前设备的所有参数均采用出厂时的缺省配置。如果您已经对设备进行了配置,为了保证配置效果,请确认现有配置和以下举例中的配置不冲突。
本文档假设您已了解IPSEC和双出口特性。
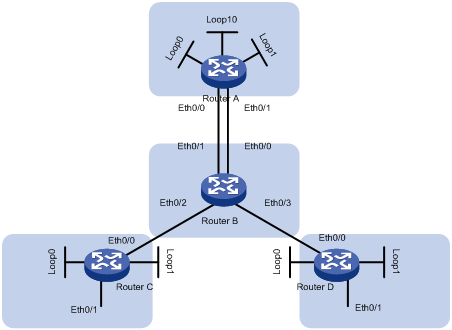
如图1所示,总部Router A使用运营商1、运营商2双出口,分支单出口。要求总部和分支之间通过IPSec建立VPN,并进行相互备份。部分分支与总部运营商1线路相连,运营商2链路作为备份;另一部分与总部运营商2线路相连,运营商1线路作为备份。
假设Router C是优选运营商2线路,Router D是优选运营商1线路。
图1 双出口固定IP、分支动态地址IPSec备份的配置组网图
|
设备 |
接口 |
IP地址 |
设备 |
接口 |
IP地址 |
|
Router A |
Eth0/0 |
2.1.1.1/24 |
Router C |
Eth0/0 |
4.1.1.1/24 |
|
|
Eth0/1 |
3.1.1.1/24 |
|
Eth0/1 |
10.1.1.1/24 |
|
|
Loop0 |
192.168.254.1/32 |
|
Loop0 |
192.168.254.2/32 |
|
|
Loop1 |
192.168.254.129/32 |
|
Loop1 |
192.168.254.130/32 |
|
|
Loop10 |
10.10.10.10/32 |
Router D |
Eth0/0 |
5.1.1.1/24 |
|
Router B |
Eth0/0 |
3.1.1.2/24 |
|
Eth0/1 |
11.1.1.1/24 |
|
|
Eth0/1 |
2.1.1.2/24 |
|
Loop1 |
192.168.254.3/32 |
|
|
Eth0/2 |
4.1.1.2/24 |
|
Loop2 |
192.168.254.131/32 |
|
|
Eth0/3 |
5.1.1.2/24 |
|
- |
|
为实现链路备份,为每个分支建立两条隧道,并设置备份路由。分支动态分配地址,使用野蛮模式建立IPSEC。
本举例是在Release 2317版本上进行配置和验证的。
· 在配置总部的IKE对等体的时候,不能配置remote-address,否则不能实现总部到多个分支的通信。
· 配置总部安全策略的时候,使用模板,不用配置ACL。
# 为运营商1线路创建LoopBack0
[RouterA] interface LoopBack0
[RouterA-LoopBack0] ip address 192.168.254.1 255.255.255.255
[RouterA-LoopBack0] quit
# 为运营商2线路创建LoopBack1
[RouterA] interface LoopBack1
[RouterA-LoopBack1] ip address 192.168.254.129 255.255.255.255
[RouterA-LoopBack1] quit
# 创建LoopBack10 模拟总部的内部网络
[RouterA] interface LoopBack10
[RouterA-LoopBack10] ip address 10.10.10.10 255.255.255.255
[RouterA-LoopBack10] quit
# 创建总部到分支Router C的运营商1GRE隧道
[RouterA] interface Tunnel 2
[RouterA-Tunnel2] ip address 7.1.1.2 255.255.255.0
[RouterA-Tunnel2] source 192.168.254.1
[RouterA-Tunnel2] destination 192.168.254.2
[RouterA-Tunnel2] keepalive
[RouterA-Tunnel2] quit
# 创建总部到分支Router D的运营商1GRE隧道
[RouterA] interface Tunnel 3
[RouterA-Tunnel3] ip address 12.1.1.2 255.255.255.0
[RouterA-Tunnel3] source 192.168.254.1
[RouterA-Tunnel3] destination 192.168.254.3
[RouterA-Tunnel3] keepalive
[RouterA-Tunnel3] quit
# 创建总部到分支Router C的运营商2 GRE隧道
[RouterA] interface Tunnel 130
[RouterA-Tunnel130] ip address 8.1.1.2 255.255.255.0
[RouterA-Tunnel130] source 192.168.254.129
[RouterA-Tunnel130] destination 192.168.254.130
[RouterA-Tunnel130] keepalive
[RouterA-Tunnel130] quit
# 创建总部到分支Router D的运营商2 GRE隧道
[RouterA] interface Tunnel 131
[RouterA-Tunnel131] ip address 13.1.1.2 255.255.255.0
[RouterA-Tunnel131] source 192.168.254.129
[RouterA-Tunnel131] destination 192.168.254.131
[RouterA-Tunnel131] keepalive
[RouterA-Tunnel131] quit
#运营商2线路作为前往分支4.1.1.1主线路
[RouterA] ip route-static 4.1.1.0 255.255.255.0 3.1.1.2
#运营商1线路作为前往分支4.1.1.1的备份
[RouterA] ip route-static 4.1.1.0 255.255.255.0 2.1.1.2 preference 80
#运营商2线路作为前往分支5.1.1.1备份
[RouterA] ip route-static 5.1.1.0 255.255.255.0 3.1.1.2 preference 80
#运营商1线路作为前往分支5.1.1.1主线路
[RouterA] ip route-static 5.1.1.0 255.255.255.0 2.1.1.2
# 配置运营商2的GRE隧道为总部到分支RTC的主线路
[RouterA] ip route-static 10.1.1.0 255.255.255.0 Tunnel 130
# 配置运营商1的GRE隧道为总部到分支RTC的备份
[RouterA] ip route-static 10.1.1.0 255.255.255.0 Tunnel 2 preference 80
# 配置运营商2的GRE隧道为总部到分支RTD的备份
[RouterA] ip route-static 11.1.1.0 255.255.255.0 Tunnel 131 preference 80
# 配置运营商1的GRE隧道为总部到分支RTD的主线路
[RouterA] ip route-static 11.1.1.0 255.255.255.0 Tunnel 3
# 通过运营商1线路到达每个分支的LoopBack0
[RouterA] ip route-static 192.168.254.0 255.255.255.128 2.1.1.2
# 通过运营商2通线路到达每个分支的LoopBack1
[RouterA] ip route-static 192.168.254.128 255.255.255.128 3.1.1.2
# 由于分支端地址由拨号动态获取或存在NAT设备,所以使用野蛮模式IKE
[RouterA] ike peer branch
[RouterA-ike-peer-branch] exchange-mode aggressive
[RouterA-ike-peer-branch] pre-shared-key 123
[RouterA-ike-peer-branch] nat traversal
[RouterA-ike-peer-branch] quit
# 配置安全协议
[RouterA] ipsec proposal def
[RouterA-ipsec-transform-set-def] esp authentication-algorithm md5
# 总部用模板,不设置AC L
[RouterA-ipsec-transform-set-def] ipsec policy-template temp 1
[RouterA-ipsec-policy-template-temp-1] ike-peer branch
[RouterA-ipsec-policy-template-temp-1] proposal def
[RouterA-ipsec-policy-template-temp-1] quit
[RouterA] ipsec policy branch 1 isakmp template temp
#运营商1接口
[RouterA] interface ethernet 0/0
[RouterA-Ethernet0/0] port link-mode route
[RouterA-Ethernet0/0] ip address 2.1.1.1 255.255.255.0
[RouterA-Ethernet0/0] ipsec policy branch
[RouterA-Ethernet0/0] quit
#运营商2接口
[RouterA] interface ethernet 0/1
[RouterA-Ethernet0/1] port link-mode route
[RouterA-Ethernet0/1] ip address 3.1.1.1 255.255.255.0
[RouterA-Ethernet0/1] ipsec policy branch
[RouterA-Ethernet0/1] quit
# Router B来模拟Ineternet
[RouterB] interface ethernet 0/0
[RouterB-Ethernet0/0] port link-mode route
[RouterB-Ethernet0/0] ip address 3.1.1.2 255.255.255.0
[RouterB-Ethernet0/0] quit
[RouterB] interface ethernet 0/1
[RouterB-Ethernet0/1] port link-mode route
[RouterB-Ethernet0/1] ip address 2.1.1.2 255.255.255.0
[RouterB-Ethernet0/1] quit
[RouterB] interface ethernet 0/2
[RouterB-Ethernet0/2] port link-mode route
[RouterB-Ethernet0/2] ip address 4.1.1.2 255.255.255.0
[RouterB-Ethernet0/2] quit
[RouterB] interface ethernet 0/3
[RouterB-Ethernet0/3] port link-mode route
[RouterB-Ethernet0/3] ip address 5.1.1.2 255.255.255.0
[RouterB-Ethernet0/3] quit
[RouterB] ip route-static 192.168.254.1 255.255.255.255 2.1.1.1
[RouterB] ip route-static 192.168.254.2 255.255.255.255 4.1.1.1
[RouterB] ip route-static 192.168.254.3 255.255.255.255 5.1.1.1
[RouterB] ip route-static 192.168.254.129 255.255.255.255 3.1.1.1
[RouterB] ip route-static 192.168.254.130 255.255.255.255 4.1.1.1
[RouterB] ip route-static 192.168.254.131 255.255.255.255 5.1.1.1
# 为运营商1线路创建LoopBack0
[RouterC] interface LoopBack0
[RouterC-LoopBack0] ip address 192.168.254.2 255.255.255.255
[RouterC-LoopBack0] quit
# 为运营商2线路创建LoopBack1
[RouterC] interface LoopBack1
[RouterC-LoopBack1] ip address 192.168.254.130 255.255.255.255
[RouterC-LoopBack1] quit
# 创建运营商1线路的GRE隧道
[RouterC] interface Tunnel 2
[RouterC-Tunnel2] ip address 7.1.1.1 255.255.255.0
[RouterC-Tunnel2] source 192.168.254.2
[RouterC-Tunnel2] destination 192.168.254.1
[RouterC-Tunnel2] keepalive
[RouterC-Tunnel2] quit
# 创建运营商2线路的GRE隧道
[RouterC] interface Tunnel130
[RouterC-Tunnel130] ip address 8.1.1.1 255.255.255.0
[RouterC-Tunnel130] source 192.168.254.130
[RouterC-Tunnel130] destination 192.168.254.129
[RouterC-Tunnel130] keepalive
[RouterC-Tunnel130] quit
# 配置一条默认路由来制定出口方向
[RouterC] ip route-static 0.0.0.0 0.0.0.0 4.1.1.2
# 配置运营商1的GRE隧道为分支访问总部的备份线路
[RouterC] ip route-static 10.10.10.10 255.255.255.255 Tunnel 2 preference 80
# 配置运营商2的GRE隧道为分支访问总部的主线路
[RouterC] ip route-static 10.10.10.10 255.255.255.255 Tunnel 130
# 配置ACL 3000匹配运营商1线路GRE流量
[RouterC] acl number 3000
[RouterC-acl-adv-3000] rule 0 permit gre source 192.168.254.2 0 destination 192.1
68.254.1 0
[RouterC-acl-adv-3000] quit
# 配置ACL 3000匹配运营商2线路GRE流量
[RouterC] acl number 3001
[RouterC-acl-adv-3001] rule 0 permit gre source 192.168.254.130 0 destination 192
.168.254.129 0
[RouterC-acl-adv-3001] quit
# 配置运营商2线路的IKE对等体
[RouterC] ike peer telecom
[RouterC-ike-peer-telecom] exchange-mode aggressive
[RouterC-ike-peer-telecom] pre-shared-key 123
[RouterC-ike-peer-telecom] remote-address 3.1.1.1
[RouterC-ike-peer-telecom] nat traversal
[RouterC-ike-peer-telecom] quit
# 配置运营商1线路的IKE对等体
[RouterC] ike peer unicom
[RouterC-ike-peer-unicom] exchange-mode aggressive
[RouterC-ike-peer-unicom] pre-shared-key 123
[RouterC-ike-peer-unicom] remote-address 2.1.1.1
[RouterC-ike-peer-unicom] nat traversal
[RouterC-ike-peer-unicom] quit
# 配置安全协议
[RouterC] ipsec proposal def
[RouterC-ipsec-transform-set-def] esp authentication-algorithm md5
[RouterC-ipsec-transform-set-def] ipsec policy headquarter 1 isakmp
[RouterC-ipsec-policy-isakmp-headquarter-1] security acl 3000
[RouterC-ipsec-policy-isakmp-headquarter-1] ike-peer unicom
[RouterC-ipsec-policy-isakmp-headquarter-1] proposal def
[RouterC-ipsec-policy-isakmp-headquarter-1] quit
[RouterC] ipsec policy headquarter 2 isakmp
[RouterC-ipsec-policy-isakmp-headquarter-2] security acl 3001
[RouterC-ipsec-policy-isakmp-headquarter-2] ike-peer telecom
[RouterC-ipsec-policy-isakmp-headquarter-2] proposal def
[RouterC-ipsec-policy-isakmp-headquarter-2] quit
[RouterC] interface ethernet 0/0
[RouterC-Ethernet0/0] port link-mode route
[RouterC-Ethernet0/0] ip address 4.1.1.1 255.255.255.0
[RouterC-Ethernet0/0] ipsec policy headquarter
[RouterC-Ethernet0/0] quit
[RouterC] interface ethernet 0/1
[RouterC-Ethernet0/1] port link-mode route
[RouterC-Ethernet0/1] ip address 10.1.1.1 255.255.255.0
[RouterC-Ethernet0/1] quit
# 为运营商1线路创建LoopBack0
[RouterD] interface LoopBack0
[RouterD-LoopBack0] ip address 192.168.254.3 255.255.255.255
[RouterD-LoopBack0] quit
# 为运营商2线路创建LoopBack1
[RouterD] interface LoopBack1
[RouterD-LoopBack1] ip address 192.168.254.131 255.255.255.255
[RouterD-LoopBack1] quit
# 创建运营商1线路的GRE隧道
[RouterD] interface Tunnel 3
[RouterD-Tunnel3] ip address 12.1.1.1 255.255.255.0
[RouterD-Tunnel3] source 192.168.254.3
[RouterD-Tunnel3] destination 192.168.254.1
[RouterD-Tunnel3] keepalive
[RouterD-Tunnel3] quit
# 创建运营商2线路的GRE隧道
[RouterD] interface Tunnel 131
[RouterD-Tunnel131] ip address 13.1.1.1 255.255.255.0
[RouterD-Tunnel131] source 192.168.254.131
[RouterD-Tunnel131] destination 192.168.254.129
[RouterD-Tunnel131] keepalive
[RouterD-Tunnel131] quit
# 配置一条默认路由来制定出口方向
[RouterD] ip route-static 0.0.0.0 0.0.0.0 5.1.1.2
# 配置运营商1的GRE隧道为分支访问总部的主线路
[RouterD] ip route-static 10.10.10.10 255.255.255.255 Tunnel 3
# 配置运营商2的GRE隧道为分支访问总部的备份线路
[RouterD] ip route-static 10.10.10.10 255.255.255.255 Tunnel 131 preference 80
# 配置ACL 3000匹配运营商1线路GRE流量
[RouterD] acl number 3000
[RouterD-acl-adv-3000] rule 0 permit gre source 192.168.254.3 0 destination 192.1
68.254.1 0
[RouterD-acl-adv-3000] quit
# 配置ACL 3001匹配运营商2线路GRE流量
[RouterD] acl number 3001
[RouterD-acl-adv-3001] rule 0 permit gre source 192.168.254.131 0 destination 192
.168.254.129 0
[RouterD-acl-adv-3001] quit
# 配置运营商2线路的IKE对等体
[RouterD] ike peer telecom
[RouterD-ike-peer-telecom] exchange-mode aggressive
[RouterD-ike-peer-telecom] pre-shared-key 123
[RouterD-ike-peer-telecom] remote-address 3.1.1.1
[RouterD-ike-peer-telecom] nat traversal
[RouterD-ike-peer-telecom] quit
# 配置运营商1线路的IKE对等体
[RouterD] ike peer unicom
[RouterD-ike-peer-unicom] exchange-mode aggressive
[RouterD-ike-peer-unicom] pre-shared-key 123
[RouterD-ike-peer-unicom] remote-address 2.1.1.1
[RouterD-ike-peer-unicom] nat traversal
[RouterD-ike-peer-unicom] quit
# 配置安全协议
[RouterD] ipsec proposal def
[RouterD-ipsec-transform-set-def] esp authentication-algorithm md5
[RouterD-ipsec-transform-set-def] ipsec policy headquarter 1 isakmp
[RouterD-ipsec-policy-isakmp-headquarter-1] security acl 3000
[RouterD-ipsec-policy-isakmp-headquarter-1] ike-peer unicom
[RouterD-ipsec-policy-isakmp-headquarter-1] proposal def
[RouterD-ipsec-policy-isakmp-headquarter-1] quit
[RouterD] ipsec policy headquarter 2 isakmp
[RouterD-ipsec-policy-isakmp-headquarter-2] security acl 3001
[RouterD-ipsec-policy-isakmp-headquarter-2] ike-peer telecom
[RouterD-ipsec-policy-isakmp-headquarter-2] proposal def
[RouterD-ipsec-policy-isakmp-headquarter-2] quit
[RouterD] interface ethernet 0/0
[RouterD-Ethernet0/0] port link-mode route
[RouterD-Ethernet0/0] ip address 5.1.1.1 255.255.255.0
[RouterD-Ethernet0/0] ipsec policy headquarter
[RouterD-Ethernet0/0] quit
[RouterD] interface ethernet 0/1
[RouterD-Ethernet0/1] port link-mode route
[RouterD-Ethernet0/1] ip address 11.1.1.1 255.255.255.0
[RouterD-Ethernet0/1] quit
1) Router A上查看IPSec状态
<RouterA>display ipsec sa brief
total phase-2 IPv4 SAs: 8
Src Address Dst Address SPI Protocol Algorithm
-----------------------------------------------------------------------------
3.1.1.1 4.1.1.1 4273063068 ESP E:NULL
A:HMAC-MD5-96
4.1.1.1 2.1.1.1 1601976515 ESP E:NULL
A:HMAC-MD5-96
2.1.1.1 4.1.1.1 373419746 ESP E:NULL
A:HMAC-MD5-96
2.1.1.1 5.1.1.1 432547588 ESP E:NULL
A:HMAC-MD5-96
3.1.1.1 5.1.1.1 2730487603 ESP E:NULL
A:HMAC-MD5-96
5.1.1.1 3.1.1.1 3287952200 ESP E:NULL
A:HMAC-MD5-96
4.1.1.1 3.1.1.1 1353440193 ESP E:NULL
A:HMAC-MD5-96
5.1.1.1 2.1.1.1 4151631860 ESP E:NULL
A:HMAC-MD5-96
total phase-2 IPv6 SAs: 0
Src Address Dst Address SPI Protocol Algorithm
-----------------------------------------------------------------------------
2) 网关设备和链路均正常工作时,Router C与Router D两个分支都可以连通总部
<RouterC>ping 10.10.10.10
PING 10.10.10.10: 56 data bytes, press CTRL_C to break
Reply from 10.10.10.10: bytes=56 Sequence=0 ttl=255 time=3 ms
Reply from 10.10.10.10: bytes=56 Sequence=1 ttl=255 time=3 ms
Reply from 10.10.10.10: bytes=56 Sequence=2 ttl=255 time=3 ms
Reply from 10.10.10.10: bytes=56 Sequence=3 ttl=255 time=3 ms
Reply from 10.10.10.10: bytes=56 Sequence=4 ttl=255 time=3 ms
--- 10.10.10.10 ping statistics ---
5 packet(s) transmitted
5 packet(s) received
0.00% packet loss
round-trip min/avg/max = 3/3/3 ms
<RouterD>ping 10.10.10.10
PING 10.10.10.10: 56 data bytes, press CTRL_C to break
Reply from 10.10.10.10: bytes=56 Sequence=0 ttl=255 time=3 ms
Reply from 10.10.10.10: bytes=56 Sequence=1 ttl=255 time=2 ms
Reply from 10.10.10.10: bytes=56 Sequence=2 ttl=255 time=2 ms
Reply from 10.10.10.10: bytes=56 Sequence=3 ttl=255 time=3 ms
Reply from 10.10.10.10: bytes=56 Sequence=4 ttl=255 time=2 ms
--- 10.10.10.10 ping statistics ---
5 packet(s) transmitted
5 packet(s) received
0.00% packet loss
round-trip min/avg/max = 2/2/3 ms
3) 当运营商1线路Tunnel 2故障时时,总部可以ping通分支Router D
<RouterA>ping 11.1.1.1
PING 11.1.1.1: 56 data bytes, press CTRL_C to break
Reply from 11.1.1.1: bytes=56 Sequence=0 ttl=255 time=3 ms
Reply from 11.1.1.1: bytes=56 Sequence=1 ttl=255 time=3 ms
Reply from 11.1.1.1: bytes=56 Sequence=2 ttl=255 time=2 ms
Reply from 11.1.1.1: bytes=56 Sequence=3 ttl=255 time=3 ms
Reply from 11.1.1.1: bytes=56 Sequence=4 ttl=255 time=3 ms
--- 11.1.1.1 ping statistics ---
5 packet(s) transmitted
5 packet(s) received
0.00% packet loss
round-trip min/avg/max = 2/2/3 ms
# 此时根据路由表可知,运营商1线路故障,总部通过运营商2线路连接分支Router D
<RouterA>dis ip routing-table
Routing Tables: Public
Destinations : 16 Routes : 16
Destination/Mask Proto Pre Cost NextHop Interface
3.1.1.0/24 Direct 0 0 3.1.1.1 Eth0/1
3.1.1.1/32 Direct 0 0 127.0.0.1 InLoop0
4.1.1.0/24 Static 60 0 3.1.1.2 Eth0/1
5.1.1.0/24 Static 80 0 3.1.1.2 Eth0/1
8.1.1.0/24 Direct 0 0 8.1.1.2 Tun130
8.1.1.2/32 Direct 0 0 127.0.0.1 InLoop0
10.1.1.0/24 Static 60 0 8.1.1.2 Tun130
10.10.10.10/32 Direct 0 0 127.0.0.1 InLoop0
11.1.1.0/24 Static 80 0 13.1.1.2 Tun131
13.1.1.0/24 Direct 0 0 13.1.1.2 Tun131
13.1.1.2/32 Direct 0 0 127.0.0.1 InLoop0
127.0.0.0/8 Direct 0 0 127.0.0.1 InLoop0
127.0.0.1/32 Direct 0 0 127.0.0.1 InLoop0
192.168.254.1/32 Direct 0 0 127.0.0.1 InLoop0
192.168.254.128/25 Static 60 0 3.1.1.2 Eth0/1
192.168.254.129/32 Direct 0 0 127.0.0.1 InLoop0
· Router A:
#
ike peer branch
exchange-mode aggressive
pre-shared-key cipher $c$3$L79wq+pDjevyzrepMRZrsdAqH50WVA==
nat traversal
#
ipsec transform-set def
encapsulation-mode tunnel
transform esp
esp authentication-algorithm md5
#
ipsec policy-template temp 1
ike-peer branch
transform-set def
#
ipsec policy branch 1 isakmp template temp
#
user-group system
group-attribute allow-guest
#
local-user admin
password cipher $c$3$40gC1cxf/wIJNa1ufFPJsjKAof+QP5aV
authorization-attribute level 3
service-type telnet
#
cwmp
undo cwmp enable
#
interface Aux0
async mode flow
link-protocol ppp
#
interface Cellular0/0
async mode protocol
link-protocol ppp
#
interface Ethernet0/0
port link-mode route
ip address 2.1.1.1 255.255.255.0
ipsec policy branch
#
interface Ethernet0/1
port link-mode route
ip address 3.1.1.1 255.255.255.0
ipsec policy branch
#
interface NULL0
#
interface LoopBack0
ip address 192.168.254.1 255.255.255.255
#
interface LoopBack1
ip address 192.168.254.129 255.255.255.255
#
interface LoopBack10
ip address 10.10.10.10 255.255.255.255
#
interface Tunnel2
ip address 7.1.1.2 255.255.255.0
source 192.168.254.1
destination 192.168.254.2
keepalive 10 3
#
interface Tunnel3
ip address 12.1.1.2 255.255.255.0
source 192.168.254.1
destination 192.168.254.3
keepalive 10 3
#
interface Tunnel130
ip address 8.1.1.2 255.255.255.0
source 192.168.254.129
destination 192.168.254.130
keepalive 10 3
#
interface Tunnel131
ip address 13.1.1.2 255.255.255.0
source 192.168.254.129
destination 192.168.254.131
keepalive 10 3
#
ip route-static 4.1.1.0 255.255.255.0 3.1.1.2
ip route-static 4.1.1.0 255.255.255.0 2.1.1.2 preference 80
ip route-static 5.1.1.0 255.255.255.0 3.1.1.2 preference 80
ip route-static 5.1.1.0 255.255.255.0 2.1.1.2
ip route-static 10.1.1.0 255.255.255.0 Tunnel130
ip route-static 10.1.1.0 255.255.255.0 Tunnel2 preference 80
ip route-static 11.1.1.0 255.255.255.0 Tunnel3
ip route-static 11.1.1.0 255.255.255.0 Tunnel131 preference 80
ip route-static 192.168.254.0 255.255.255.128 2.1.1.2
ip route-static 192.168.254.128 255.255.255.128 3.1.1.2
#
· Router B:
#
interface Ethernet0/0
port link-mode route
ip address 3.1.1.2 255.255.255.0
#
interface Ethernet0/1
port link-mode route
ip address 2.1.1.2 255.255.255.0
#
interface Ethernet0/2
port link-mode route
ip address 4.1.1.2 255.255.255.0
#
interface Ethernet0/3
port link-mode route
ip address 5.1.1.2 255.255.255.0
#
ip route-static 192.168.254.1 255.255.255.255 2.1.1.1
ip route-static 192.168.254.2 255.255.255.255 4.1.1.1
ip route-static 192.168.254.3 255.255.255.255 5.1.1.1
ip route-static 192.168.254.129 255.255.255.255 3.1.1.1
ip route-static 192.168.254.130 255.255.255.255 4.1.1.1
ip route-static 192.168.254.131 255.255.255.255 5.1.1.1
#
· Router C:
#
acl number 3000
rule 0 permit gre source 192.168.254.2 0 destination 192.168.254.1 0
acl number 3001
rule 0 permit gre source 192.168.254.130 0 destination 192.168.254.129 0
#
ike peer telecom
exchange-mode aggressive
pre-shared-key cipher $c$3$Eclh00SfISOK0Ya+YpYW1XlCpO7Ubw==
remote-address 3.1.1.1
nat traversal
#
ike peer unicom
exchange-mode aggressive
pre-shared-key cipher $c$3$ITGbqGRZ8oxRNeVc9UewnVVgJ2oQdA==
remote-address 2.1.1.1
nat traversal
#
ipsec transform-set def
encapsulation-mode tunnel
transform esp
esp authentication-algorithm md5
#
ipsec policy headquarter 1 isakmp
security acl 3000
ike-peer unicom
transform-set def
#
ipsec policy headquarter 2 isakmp
security acl 3001
ike-peer telecom
transform-set def
#
user-group system
group-attribute allow-guest
#
cwmp
undo cwmp enable
#
interface Aux0
async mode flow
link-protocol ppp
#
interface Cellular0/0
async mode protocol
link-protocol ppp
#
interface Ethernet0/0
port link-mode route
ip address 4.1.1.1 255.255.255.0
ipsec policy headquarter
#
interface Ethernet0/1
port link-mode route
ip address 10.1.1.1 255.255.255.0
#
interface NULL0
#
interface LoopBack0
ip address 192.168.254.2 255.255.255.255
#
interface LoopBack1
ip address 192.168.254.130 255.255.255.255
#
interface Tunnel2
ip address 7.1.1.1 255.255.255.0
source 192.168.254.2
destination 192.168.254.1
keepalive 10 3
#
interface Tunnel130
ip address 8.1.1.1 255.255.255.0
source 192.168.254.130
destination 192.168.254.129
keepalive 10 3
#
ip route-static 0.0.0.0 0.0.0.0 4.1.1.2
ip route-static 10.10.10.10 255.255.255.255 Tunnel2 preference 80
ip route-static 10.10.10.10 255.255.255.255 Tunnel130
#
· Router D
#
acl number 3000
rule 0 permit gre source 192.168.254.3 0 destination 192.168.254.1 0
acl number 3001
rule 0 permit gre source 192.168.254.131 0 destination 192.168.254.129 0
#
ike peer telecom
exchange-mode aggressive
pre-shared-key cipher $c$3$DgSOJydCGR9QSclrdyLA92iZ0Fnzcw==
remote-address 3.1.1.1
nat traversal
#
ike peer unicom
exchange-mode aggressive
pre-shared-key cipher $c$3$Fpv6Rh/hTBsYdTPEa6Au28lg+IyVFg==
remote-address 2.1.1.1
nat traversal
#
ipsec transform-set def
encapsulation-mode tunnel
transform esp
esp authentication-algorithm md5
#
ipsec policy headquarter 1 isakmp
security acl 3000
ike-peer unicom
transform-set def
#
ipsec policy headquarter 2 isakmp
security acl 3001
ike-peer telecom
transform-set def
#
interface LoopBack0
ip address 192.168.254.3 255.255.255.255
#
interface LoopBack1
ip address 192.168.254.131 255.255.255.255
#
interface Ethernet0/0
port link-mode route
ip address 5.1.1.1 255.255.255.0
ipsec policy headquarter
#
interface Ethernet0/1
port link-mode route
ip address 11.1.1.1 255.255.255.0
#
interface Tunnel3
ip address 12.1.1.1 255.255.255.0
source 192.168.254.3
destination 192.168.254.1
keepalive 10 3
#
interface Tunnel131
ip address 13.1.1.1 255.255.255.0
source 192.168.254.131
destination 192.168.254.129
keepalive 10 3
#
ip route-static 0.0.0.0 0.0.0.0 5.1.1.2
ip route-static 10.10.10.10 255.255.255.255 Tunnel3
ip route-static 10.10.10.10 255.255.255.255 Tunnel131 preference 80
ip route-static 192.168.254.1 255.255.255.255 5.1.1.2
ip route-static 192.168.254.129 255.255.255.255 5.1.1.2
#
· H3C MSR 系列路由器 命令参考(V5)-R2311
· H3C MSR 系列路由器 配置指导(V5)-R2311
不同款型规格的资料略有差异, 详细信息请向具体销售和400咨询。H3C保留在没有任何通知或提示的情况下对资料内容进行修改的权利!
