- Table of Contents
-
- 08-Configuration Examples
- 01-Web Login Configuration Examples
- 02-Internet Access Through a Static IP Address Configuration Examples
- 03-Internet access through PPPoE configuration examples
- 04-Signature Library Upgrade Configuration Examples
- 04-Software Upgrade Examples(only for F50X0-D and F5000-AK5X5 firewalls)
- 05-Software Upgrade Examples
- 06-Static routing configuration examples
- 07-OSPF configuration examples
- 08-BGP configuration examples
- 09-RIP configuration examples
- 10-DHCP configuration examples
- 11-DNS configuration examples
- 12-Object Group Configuration Examples
- 13-Public key management configuration examples
- 14-Security Policy Configuration Examples
- 15-Attack defense configuration examples
- 16-Connection Limit Configuration Examples
- 17-IPS Configuration Examples
- 18-URL Filtering Configuration Examples
- 19-Anti-Virus Configuration Examples
- 20-Data Filtering Configuration Examples
- 21-File Filtering Configuration Examples
- 22-APR-Based Security Policy Configuration Examples
- 23-Bandwidth Management Configuration Examples
- 24-NAT configuration examples
- 25-NAT hairpin configuration examples
- 26-IPsec configuration examples
- 27-SSL VPN configuration examples
- 28-Server Load Balancing Configuration Examples
- 29-Outbound Link Load Balancing Configuration Examples
- 30-Inbound Link Load Balancing Configuration Examples
- 31-Transparent DNS Proxy Configuration Examples
- 32-Context Configuration Examples
- 32-Context Configuration Examples(only for F50X0-D and F5000-AK5X5 firewalls)
- 33-IRF configuration examples
- 34-High Availability Group Configuration Examples
- 35-NAT Flow Logging Configuration Examples
- 36-User identification configuration examples
- 37-Server Connection Detection Configuration Examples
- 38-IP Reputation Configuration Examples
- 39-NPTv6 Configuration Examples
- 40-SSL Decryption Configuration Examples
- 41-MAC Address Learning Through a Layer 3 Device Configuration Examples
- 42-WAF Configuration Examples
- 43-NetShare Control Configuration Examples
- 44-4G Configuration Examples
- 45-WLAN Configuration Examples
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 40-SSL Decryption Configuration Examples | 88.19 KB |
SSL decryption configuration examples
The following information provides SSL decryption configuration examples.
This document is not restricted to specific software or hardware versions. Procedure and information in the examples might be slightly different depending on the software or hardware version of the device.
The configuration examples were created and verified in a lab environment, and all the devices were started with the factory default configuration. When you are working on a live network, make sure you understand the potential impact of every command on your network.
The following information is provided based on the assumption that you have basic knowledge of SSL decryption.
When configuring SSL decryption, make sure the security policy allows the security zones and the Local security zone to communicate with each other.
After SSL decryption is configured, the IPS capture action becomes invalid.
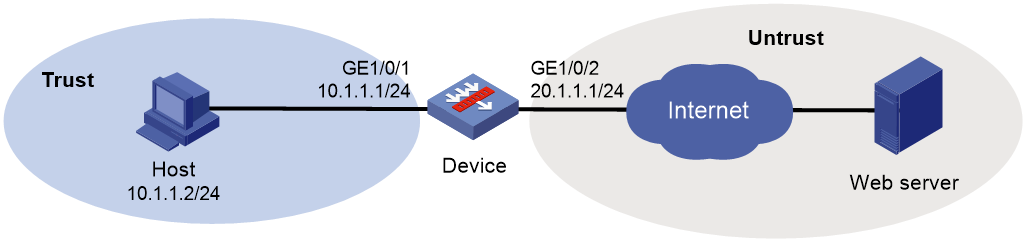
Network configuration
As shown in Figure 1, the device acts as the security gateway of an enterprise. The device cannot inspect SSL-encrypted packets (such as HTTPS packets), masking the security threats inside of the packets. To improve the internal network security, configure SSL decryption on the device to decrypt HTTPS packets for IPS inspection.
Software versions used
This configuration example was created and verified on F9345 of the F1060 device.
Procedure
1. Assign IP addresses to interfaces:
# On the top navigation bar, click Network.
# From the navigation pane, select Interface Configuration > Interfaces.
# Click the Edit icon for GE 1/0/1.
# In the dialog box that opens, configure the interface:
a. Select the Trust security zone.
b. On the IPv4 Address tab, enter the IP address and mask of the interface. In this example, enter 10.1.1.2/24.
c. Use the default settings for other parameters.
d. Click OK.
# Add GE 1/0/2 to the Untrust security zone and set its IP address to 20.1.1.1/24 in the same way you configure GE 1/0/1.
2. Configure settings for routing:
This example configures a static route.
# On the top navigation bar, click Network.
# From the navigation pane, select Routing > Static Routing.
# On the IPv4 Static Routing tab, click Create.
# In the dialog box that opens, configure a static IPv4 route to reach 0.0.0.0:
a. Enter destination IP address 0.0.0.0.
b. Enter mask length 0.
c. Enter next hop address 20.1.1.2.
d. Use the default settings for other parameters.
e. Click OK.
3. Import the trusted SSL decryption certificate:
# On the top navigation bar, click Policies.
# From the navigation pane, select Application Proxy > SSL Decryption Certificates.
# Click Import.
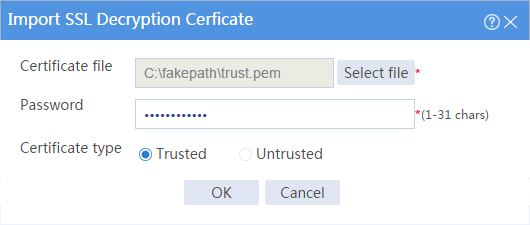
# In the dialog box that opens, configure the following settings, as shown in Figure 2:
a. Select file trust.pem.
b. Enter the password of the file.
c. Set the certificate type to Trusted.
# Click OK.
Figure 2 Importing the trusted SSL decryption certificate
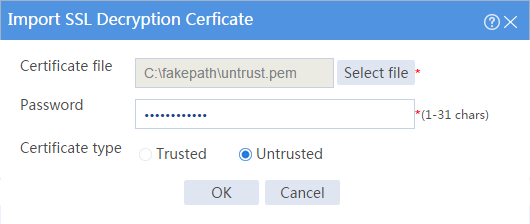
# Import the untrusted SSL decryption certificate in the same way you import the trusted SSL decryption certificate, as shown in Figure 3.
Figure 3 Importing the untrusted SSL decryption certificate
4. Install and trust the trusted SSL decryption certificate on the browser from the internal network. (Details not shown.)
5. Configure a proxy policy:
# On the top navigation bar, click Policies.
# From the navigation pane, select Application Proxy > Proxy Policy.
# Click Create.
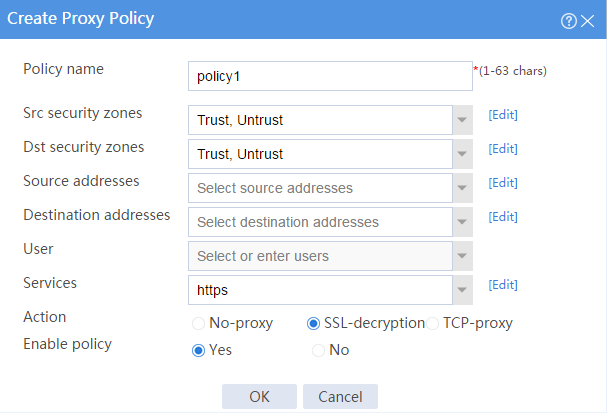
# In the dialog box that opens, configure a proxy policy:
¡ Enter policy name policy1.
¡ Select source security zones Trust and Untrust.
¡ Select destination security zones Trust and Untrust.
¡ Select service https.
¡ Select action SSL-decryption.
¡ Enable the policy.
# Click OK. The device performs decryption on HTTPS packets that match the proxy policy.
Figure 4 Creating a proxy policy
6. Configure IPS. For more information, see "IPS configuration examples."
7. Configure security policies:
# On the top navigation bar, click Policies.
# From the navigation pane, select Security Policies > Security Policies.
# Click Create, and then click Create a policy.
# Configure security policy trust-untrust for IPS inspection on the traffic from the internal network to the external network:
¡ Enter policy name trust-untrust.
¡ Select source zone Trust.
¡ Select destination zone Untrust.
¡ Select type IPv4.
¡ Select action Permit.
¡ Select source IPv4 address 10.1.1.0/24.
¡ Select IPS profile ips in the Content security area.
¡ Use the default settings for other parameters.
¡ Click OK.
# Configure security policy untrust-trust for IPS inspection on the traffic from the external network to the internal network:
¡ Enter policy name untrust-trust.
¡ Select source zone Untrust.
¡ Select destination zone Trust.
¡ Select type IPv4.
¡ Select action Permit.
¡ Select source IPv4 addresses 10.1.1.0/24.
¡ Select IPS profile ips in the Content security area.
¡ Use the default settings for other parameters.
¡ Click OK.
# Create security policy trust-local to ensure that the device can act as a proxy server to proxy the traffic from the client to the server:
¡ Enter policy name trust-local.
¡ Select source zones Trust and Local.
¡ Select destination zones Local and Trust.
¡ Select type IPv4.
¡ Select action Permit.
¡ Use the default settings for other parameters.
¡ Click OK.
# Create security policy untrust-local to ensure that the device can act as a proxy client to proxy the traffic from the server to the client:
¡ Enter policy name untrust-local.
¡ Select source zones Untrust and Local.
¡ Select destination zones Local and Untrust.
¡ Select type IPv4.
¡ Select action Permit.
¡ Use the default settings for other parameters.
¡ Click OK.
Verifying the configuration
Verify that the device can perform SSL decryption on HTTPS packets, and then perform IPS inspection on the encrypted packets.