- Table of Contents
-
- H3C S5500-SI Series Ethernet Switches Operation Manual-Release 1205-(V1.03)
- 00-1Cover
- 00-2Overview
- 01-Login Operation
- 02-Basic System Configuration and Maintenance Operation
- 03-File System Management Operation
- 04-VLAN Operation
- 05-QinQ-BPDU TUNNEL Operation
- 06-Port Correlation Configuration Operation
- 07-MAC Address Table Management Operation
- 08-MSTP Operation
- 09-IP Address and Performance Operation
- 10-IPv6 Configuration Operation
- 11-Routing Overview Operation
- 12-IPV4 Routing Operation
- 13-IPv6 Routing Operation
- 14-802.1x-HABP-MAC Authentication Operation
- 15-AAA-RADIUS-HWTACACS Operation
- 16-Multicast Protocol Operation
- 17-ARP Operation
- 18-DHCP Operation
- 19-ACL Operation
- 20-QoS Operation
- 21-Port Mirroring Operation
- 22-Cluster Operation
- 23-SNMP-RMON Operation
- 24-NTP Operation
- 25-DNS Operation
- 26-Information Center Operation
- 27-NQA Operation
- 28-SSH Terminal Service Operation
- 29-UDP Helper Operation
- 30-SSL-HTTPS Operation
- 31-PKI Operation
- 32-PoE-PoE Profile Operation
- 33-Appendix
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 28-SSH Terminal Service Operation | 5 MB |
Table of Contents
Chapter 1 SSH Terminal Service
1.3 Configuring the SSH Server
1.3.2 Configuring the Protocols for the SSH Client User Interface to Support
1.3.3 Creating/Destroying/Exporting RSA Keys
1.3.4 Configuring the Authentication Method for an SSH User
1.3.5 Specifying the Service Type of an SSH User
1.3.6 Setting the SSH Management Parameters
1.3.7 Configuring the Client RSA Public Key
1.4 Configuring the SSH Client
1.4.1 Generating the Client Keys
1.4.2 Specifying the IP address of the Server
1.4.3 Selecting the Protocol for Remote Connection
1.4.4 Selecting the SSH Version
1.4.5 Opening an SSH Connection with RSA
1.4.6 Opening an SSH Connection with Password
1.5 Configuring the Device as an SSH Client
1.5.1 Configuration Prerequisites
1.6 Displaying and Maintaining the SSH Protocol
1.7 SSH Server Configuration Example
1.8 SSH Client Configuration Example
2.2 Configuring the SFTP Server
2.2.1 Configuration Prerequisites
2.2.2 Enabling the SFTP Server
2.2.3 Configuring the SFTP Connection Idle Timeout Period
2.3 Configuring the SFTP Client
2.3.1 Specifying a Source IP Address or Interface for the SFTP Client
2.3.2 Establishing a Connection to the SFTP Server
2.3.3 Working with the SFTP Directories
2.3.5 Displaying Help Information
2.3.6 Disabling the SFTP Client
2.4 SFTP Configuration Example
Chapter 1 SSH Terminal Service
When configuring SSH2.0, go to these sections for information you are interested in:
l Configuring the Device as an SSH Client
l Displaying and Maintaining the SSH Protocol
l SSH Server Configuration Example
l SSH Client Configuration Example
1.1 SSH Overview
Secure shell (SSH) offers an approach to securely logging into a remote device. It can protect devices against attacks such as IP spoofing and plain text password interception.
The device can not only work as an SSH server to support connections with SSH clients, but also work as an SSH client to allow users to establish SSH connections with a remote device acting as the SSH server. Figure 1-1 and Figure 1-2 shows SSH connections established on the LAN and over the WAN respectively.

Figure 1-1 SSH connection on the local network

Figure 1-2 SSH connection over a WAN
& Note:
At present, the device supports two SSH versions: SSH2 and SSH1. Unless otherwise noted, SSH refers to SSH2 throughout this document.
To establish an SSH connection, the server and the client go through the following five stages:
1) Version number negotiation
l The server opens port 22 to listen to connection requests from clients.
l The client sends a TCP connection request to the server. After the TCP connection is established, the server sends the first packet to the client, which includes a version identification string in the format of “SSH-<primary protocol version number>.<secondary protocol version number>-<software version number>”. The primary and secondary protocol version numbers constitute the protocol version number, while the software version number is used for debugging.
l The client receives and resolves the packet. If the protocol version of the server is lower but supportable, the client uses the protocol version of the server; otherwise, the client uses its own protocol version.
l The client sends to the server a packet that contains the number of the protocol version it decides to use. The server compares the version carried in the packet with that of its own to determine whether it can cooperate with the client.
l If the negotiation is successful, the server and the client go on to key and algorithm negotiation; otherwise, the server breaks the TCP connection.
& Note:
All the packets above are transferred in plain text.
2) Key and algorithm negotiation
l The server and the client send key algorithm negotiation packets to each other, which include the supported server-side public key algorithm list, encryption algorithm list, MAC algorithm list, and compression algorithm list.
l Based on the received algorithm negotiation packets, the server and the client figure out the algorithms to be used.
l The server and the client use the DH key exchange algorithm and parameters such as the host key pair to generate the session key and session ID.
Through the above steps, the server and the client get the same session key, which is to be used to encrypt and decrypt data exchanged between the server and the client later. The server and the client use session ID in the authentication stage.
![]() Caution:
Caution:
Before the negotiation, the server must have already generated the server key pair and the host key pair, which are mainly used for generating the session key. The server key pair applies only to SSH1.
3) Authentication
The client sends to the server an authentication request, which includes the username and authentication method, and the server starts to authenticate the client.
SSH provides two authentication methods: password authentication and RSA authentication.
For password authentication:
l The client encrypts the username and password, encapsulates them into a password authentication request, and sends the request to the server.
l Upon receiving the request, the server decrypts the username and password, compares them against those it maintains, and then informs the client of the authentication result.
For RSA authentication:
l The client sends to the server an RSA authentication request containing its RSA public key modulus.
l The server validates the modulus. If the modulus is invalid, the authentication fails; otherwise, the server generates a 32-byte random number, converts it to a multiple precision (MP) integer (MSB first), encrypts it using the RSA public key from the client, and then sends a challenge to the client.
l Upon receiving the challenge, the client decrypts it with its private key and gets an MP integer, creates an MD5 value using the MP integer and the session ID, and then encrypts and sends the MD5 value to the server.
l After receiving the encrypted MD5 value, the server decrypts it to obtain the MD5 value and compares it with that locally calculated. If they match, the authentication succeeds.
& Note:
Besides password authentication and RSA authentication, SSH2.0 provides another two authentication methods:
l password-publickey: Performs both password authentication and RSA authentication of the client. A client running SSH1 client only needs to pass either type of the two, while a client running SSH2 client must pass both of them to login.
l all: Performs either password authentication or RSA authentication. The client tries RSA authentication first.
4) Session request
After passing authentication, the client sends a session request to the server, while the server listens to and processes the request from the client. If the client passes authentication, the server sends back to the client an SSH_SMSG_SUCCESS packet and goes on to the interactive session stage with the client. Otherwise, the server sends back to the client an SSH_SMSG_FAILURE packet, indicating that the processing fails or it cannot resolve the request.
5) Interactive session
In this stage, the server and the client exchanges data in this way:
l The client encrypts and sends the command to be executed to the server.
l The server decrypts and executes the command, and then encrypts and sends the result to the client.
l The client decrypts and displays the result on the terminal.
l During the interactive session phase, a client user can issue the commands to be executed by pasting command text on the client. Note that the text must be no more than 2,000 bytes in length and the commands pasted must be in the same view; otherwise, the server may be unable to execute the commands correctly.
l If the text exceeds 2000 bytes, you can upload the configuration file to the server and use the configuration file to restart the server so that the server executes the commands.
1.2 SSH Configuration Tasks
|
Task |
Remarks |
|
|
Required |
||
|
Configuring the Protocols for the SSH Client User Interface to Support |
Optional |
|
|
Required |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
1.3 Configuring the SSH Server
1.3.1 Enabling SSH Server
Follow these steps to enable the SSH server:
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Enable the SSH server |
ssh server enable |
Required Disabled by default |
1.3.2 Configuring the Protocols for the SSH Client User Interface to Support
After enabling the SSH server, you must configure the device to support the protocols for remote SSH login. Note that the configuration takes effect at next login.
Follow these steps to configure the protocols for the current user interface to support:
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Enter single-user interface view or multi-user interface view |
user-interface [ type-keyword ] number [ ending-number ] |
Required |
|
Set the login authentication method |
authentication-mode scheme [ command-authorization ] |
Required |
|
Specify the protocols for the user interfaces to support |
protocol inbound { all | ssh | telnet } |
Optional All of the two are supported by default. |
![]() Caution:
Caution:
l If you configure a user interface to support SSH, be sure to configure the corresponding authentication method with the authentication-mode scheme command.
l For a user interface configured to support SSH, you cannot configure the authentication-mode password command and the authentication-mode none command.
1.3.3 Creating/Destroying/Exporting RSA Keys
For successful SSH login, you must create the RSA key pairs at first. Without them, SSH login will fail even if you have SSH enabled.
You can display the created RSA host public key on the screen in a specified format, or export it to a specified file for use when configuring the key at a remote site.
I. Creating RSA keys
Follow these steps to create the host key pair and server key pair:
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Create the RSA host key pair and server key pair |
rsa local-key-pair create |
Required |
II. Destroying RSA keys
Follow these steps to destroy the host key pair and server key pair:
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Destroy the RSA host key pair and server key pair |
rsa local-key-pair destroy |
Required |
III. Displaying/exporting the public host key
Once created, the public host key can be displayed on the screen or exported to a specified file.
Follow these steps to export the host key pair:
|
To do… |
Use the command… |
Remarks |
|
Display the RSA host public key on the screen or export it to a specified file |
rsa local-key-pair export { ssh1 | ssh2 | openssh } [ filename ] |
Required You can configure the command in any view. |
![]() Caution:
Caution:
l The configuration of the rsa local-key-pair create command can survive a reboot. You only need to configure it once.
l When you create a key pair, if the key pair is already configured, the system will ask you whether you want to overwrite it.
l The length of a server/host key must be in the range 512 to 2048 bits. With SSH2, some clients require that the keys generated by the server must be at least or more than 768 bits.
1.3.4 Configuring the Authentication Method for an SSH User
The configured authentication method takes effect when the user logs in next time.
Follow these steps to configure the authentication method for an SSH user:
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Specify the authentication method for an SSH user |
ssh user username authentication-type { password | rsa | password-publickey | all } |
Optional RSA authentication by default |
![]() Caution:
Caution:
For a user using RSA authentication, you must configure the username and public keys on the device. For a user using password authentication, you can configure the accounting information on the device or the remote authentication server (such as RADIUS authentication server).
1.3.5 Specifying the Service Type of an SSH User
Follow these steps to specify the service type of an SSH user:
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Specify the service types of an SSH user |
ssh user username service-type { stelnet | sftp | all } |
Required stelnet by default |
![]() Caution:
Caution:
l For successful login through SFTP, you must set the user service type to sftp or all.
l You can set the service type of an SSH user to stelnet or all if the user does not need SFTP service.
1.3.6 Setting the SSH Management Parameters
SSH management includes:
l Enabling the SSH server to be compatible with SSH1
l Setting the server key pair update interval
l Setting the SSH user authentication timeout period
l Setting the maximum number of SSH authentication attempts
Setting the above parameters can help avoid malicious guess at and cracking of the keys and usernames, securing your SSH connections.
Follow these steps to set the SSH management parameters:
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Enable the SSH server to work with SSH1.x clients |
ssh server compatible-ssh1x enable |
Optional By default, the SSH server can work with SSH1.x clients. |
|
Set the server key pair update interval |
ssh server rekey-interval hours |
Optional 0 by default, that is, the server key pair is not updated. |
|
Set the SSH user authentication timeout period |
ssh server authentication-timeout time-out-value |
Optional 60 seconds by default |
|
Set the maximum number of SSH authentication attempts |
ssh server authentication-retries times |
Optional 3 by default |
1.3.7 Configuring the Client RSA Public Key
These configurations are required for an SSH user using RSA authentication. For an SSH user using password authentication, they are not required.
This configuration task is for configuring the RSA public key of a client with an SSH user. The RSA private key for the SSH user must be configured on the client. The client key pair is generated randomly by the SSH client software.
You can manually configure or import the RSA public key from a public key file. When you import a public key, the system automatically converts the public key to a string coded using the PKCS standard. Before importing the public key, you must upload the public key file to the server through FTP or TFTP.
![]() Caution:
Caution:
l When the device functions as the SSH server, you cannot use Secure CRT 4.07 to upload the client public key to the server.
l You configure any of these three commands to create an SSH user: ssh user assign rsa-key, ssh user authentication-type, and ssh user service-type. Up to 1024 SSH users can be created. By default, the authentication method for an SSH user is RSA and the service type is stelnet.
l If no SSH users are created, but there are local users whose service type is SSH, the SSH client can still logs in the SSH server through these users. Here, the system performs password authentication and the SSH service type is stelnet.
I. Configuring the client RSA public key manually
Follow these steps to configure the client RSA public key manually:
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Enter public key view |
rsa peer-public-key keyname |
Required |
|
Enter public key code view |
public-key-code begin |
— |
|
Configure the client public key |
Enter the content of the public key |
— The content must be a hexadecimal string that is generated randomly by the SSH-supported client software and coded compliant to PKCS. Spaces and carriage returns are allowed between characters. |
|
Return from public key code view to public key view |
public-key-code end |
— When you exit public key code view, the system automatically saves the public key. |
|
Return from public key view to system view |
peer-public-key end |
— |
|
Assign a public key to an SSH user |
ssh user username assign rsa-key keyname |
Required The public key must exist. If the user has already a public key, the new public key overwrites the old one. |
II. Importing the RSA public key from a public key file
Follow these steps to import the RSA public key from a public key file:
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Import the RSA public key from a public key file |
rsa peer-public-key keyname import sshkey filename |
Required |
1.4 Configuring the SSH Client
A variety of SSH client software are available, such as PuTTY and OpenSSH. For an SSH client to establish a connection with an SSH server, you must complete these configuration tasks:
l Specifying the IP address of the server.
l Selecting the protocol for remote connection as SSH. Usually, a client can use a variety of remote connection protocols, such as Telnet, Rlogin, and SSH. To establish an SSH connection, you must select SSH.
l Selecting the SSH version. Since the device supports SSH Server 2.0 now, select 2.0 or lower for the client.
l Specifying the RSA private key file. On the server, if RSA authentication is enabled for an SSH user and a public key is set for the user, the private key file corresponding to the public key must be specified on the client. RSA key pairs are generated by a tool of the client software.
The following takes the client software of PuTTY, PuTTYGen and SSHKEY as examples to illustrate how to configure the SSH client:
1.4.1 Generating the Client Keys
To generate the client key pair, run PuTTYGen.exe, choose SSH-2 RSA under Parameters and click Generate.
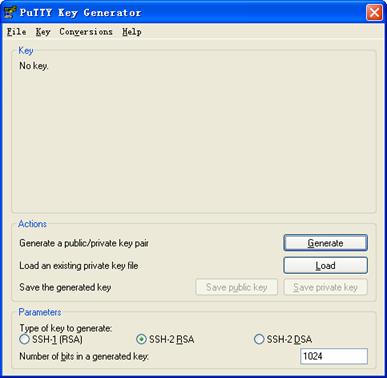
Figure 1-3 Generating the client keys (1)
Note that while generating the key pair, you must move the mouse continuously and keep the mouse off the green process bar in the blue box of shown in Figure 1-4. Otherwise, the process bar stops moving and the key pair generating process is stopped.
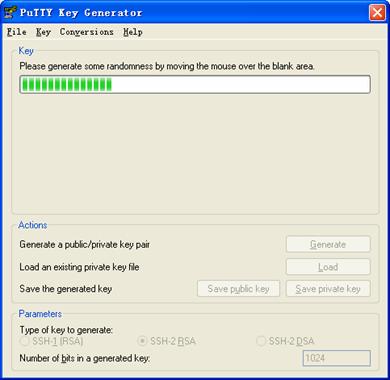
Figure 1-4 Generating the client keys (2)
After the key pair is generated, click Save public key and enter the name of the file for saving the public key (public in this case) to save the public key.
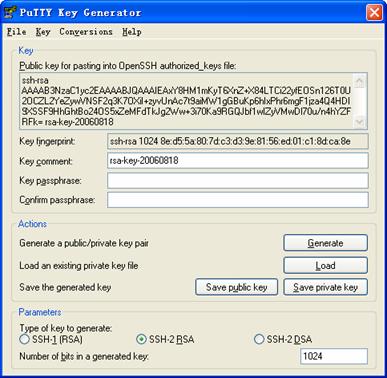
Figure 1-5 Generating the client keys (3)
Likewise, to save the private key, click Save private key. A warning window pops up to prompt you whether to save the private key without any precaution. Click Yes and enter the name of the file for saving the public key (private in this case) to save the private key.
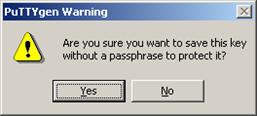
Figure 1-6 Generating the client keys (4)
To generate RSA public key in PKCS format, run SSHKEY.exe, click Browse and select the public key file, and then click Convert.
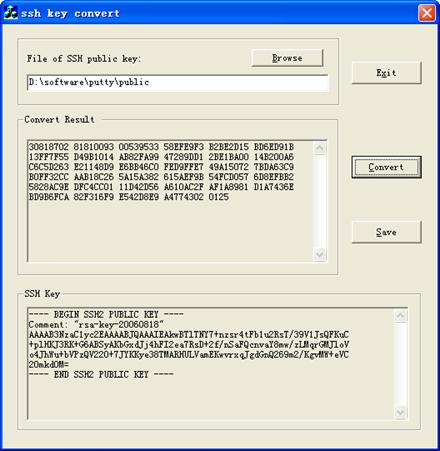
Figure 1-7 Generating the client keys (5)
1.4.2 Specifying the IP address of the Server
Launch PuTTY.exe. The following window appears.
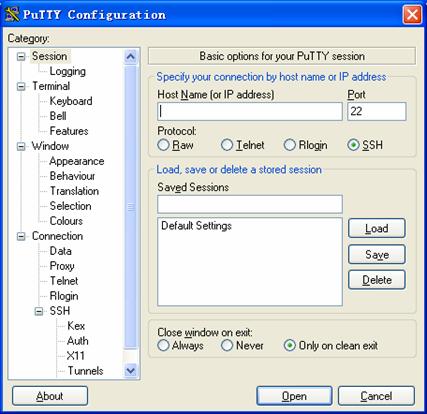
Figure 1-8 SSH client configuration interface 1
In the Host Name (or IP address) text box, enter the IP address of the server, 10.110.28.10, for example. Note that there must be a route available between the IP address of the server and the client.
1.4.3 Selecting the Protocol for Remote Connection
As shown in Figure 1-8, select SSH under Protocol.
1.4.4 Selecting the SSH Version
From the category on the left pane of the window, select SSH under Connection. The window as shown in Figure 1-9 appears.
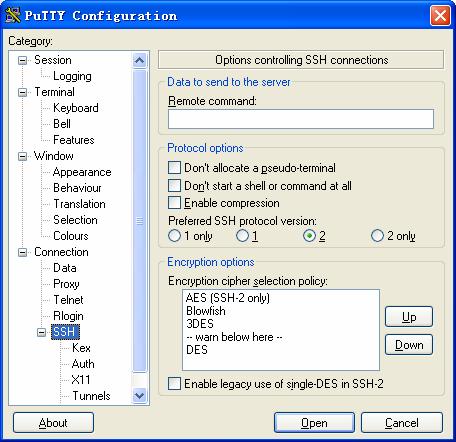
Figure 1-9 SSH client configuration interface 2
Under Protocol options, select 2 from Preferred SSH protocol version.
1.4.5 Opening an SSH Connection with RSA
If the client needs to use RSA authentication, you must specify the RSA private key file. If the client needs to use password authentication, this is not required.
From the category on the left of the window, Select Connection/SSH/Auth. The following window appears.
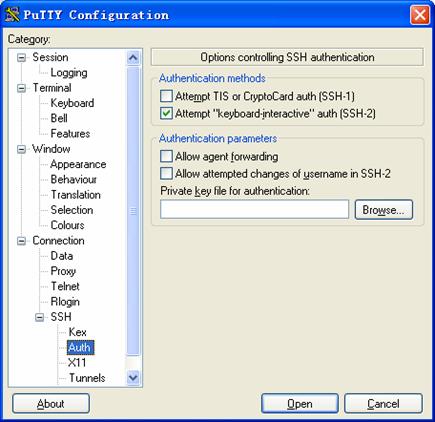
Figure 1-10 SSH client configuration interface 3
Click Browse… to bring up the file selection window, navigate to the private key file and click OK.
1.4.6 Opening an SSH Connection with Password
1) From the window shown in Figure 1-10, click Open. The following SSH client interface appears. If the connection is normal, you will be prompted to enter the username and password, as shown in Figure 1-11.

Figure 1-11 SSH client interface
2) Enter the username and password to establish an SSH connection.
3) To log out, enter the quit command.
1.5 Configuring the Device as an SSH Client
1.5.1 Configuration Prerequisites
Complete the configuration of the SSH server. For detailed configuration information, refer to Configuring the SSH Server
1.5.2 Configuration Procedure
When the device connects to the SSH server as an SSH client, you can configure the SSH client to authenticate the SSH server during the first access.
l The first authentication means that when the SSH client accesses the server for the first time and is not configured with the server host public key, the user can choose to continue accessing the server and save the host public key on the client for future authentication of the server.
l With first authentication not supported, the client cannot authenticate the server if it is not configured with the server host public key. In this case, you must configure the host public key of the server and specify the key name on the client beforehand, so that the client can authenticate the server.
l You can configure the client to use a specified IP address or interface to access the SSH.
Follow these steps to configure the device as an SSH client:
|
To do… |
Use the command… |
Remarks |
|
|
Enter system view |
system-view |
— |
|
|
Disable the first authentication function |
undo ssh client first-time |
Optional Enabled by default |
|
|
Enter public key view |
rsa peer-public-key keyname |
Optional |
|
|
Enter public key code view |
public-key-code begin |
— |
|
|
Configure the server public key |
Enter the content of the public key |
— The content must be a hexadecimal string that is generated randomly by the SSH-supported client software and coded compliant to PKCS. Spaces and carriage returns are allowed between characters. |
|
|
Return from public key code view to public key view |
public-key-code end |
— When you exit public key code view, the system automatically saves the public key. |
|
|
Return from public key view to system view |
peer-public-key end |
— |
|
|
Configure the host public key of the server on the client |
ssh client authentication server { server-ip | server-name } assign rsa-key keyname |
Optional |
|
|
Specify the source IP address or source interface of the SSH client |
Specify the source IPv4 address or source interface of the SSH client |
ssh client source { ip ip-address | interface interface-type interface-number } |
Optional IP address or interface specified by the route by default |
|
Specify the source IPv6 address or source interface of the SSH client |
ssh client ipv6 source { ipv6 ipv6-address | interface interface-type interface-number } |
||
|
Establish a connection between the SSH client and the server, and specify the preferred key exchange algorithm, encryption algorithms, and HMAC algorithms of the client and the server |
Establish a connection between the SSH client and the IPv4 server, and specify the preferred key exchange algorithm, encryption algorithms, and HMAC algorithms of the client and the server |
ssh2 { host-ip | host-name } [ port-number ] [ prefer_kex { dh_group1 | dh_exchange_group } | prefer_ctos_cipher { des | aes128} | prefer_stoc_cipher { des | aes128 } | prefer_ctos_hmac { sha1 | sha1_96 | md5 | md5_96 } | prefer_stoc_hmac { sha1 | sha1_96 | md5 | md5_96 } ]* |
Use one command as required. |
|
Establish a connection between the SSH client and the IPv6 server, and specify the preferred key exchange algorithm, encryption algorithms, and HMAC algorithms of the client and the server |
ssh2 ipv6 { ipv6-address | host-name } [ port-number ] [ prefer_ctos_cipher { aes128 | des } | prefer_ctos_hmac { md5 | md5_96 | sha1 | sha1_96 } | prefer_kex { dh_exchange_group | dh_group1 } | prefer_stoc_cipher { aes128 | des } | prefer_stoc_hmac { md5 | md5_96 | sha1 | sha1_96 } ] * |
||
1.6 Displaying and Maintaining the SSH Protocol
|
To do… |
Use the command… |
Remarks |
|
Display information about the public keys of the host key pair and server key pair |
display rsa local-key-pair public |
Available in any view |
|
Display information about the peer RSA public keys |
display rsa peer-public-key [ brief | name keyname ] |
Available in any view |
|
Display the source IP address or interface currently set for the SFTP client |
display sftp client source |
Available in any view |
|
Display the source IP address or interface currently set for the SSH client |
display ssh client source |
Available in any view |
|
Display the status information or session information of an SSH server |
display ssh server { status | session } |
Available in any view |
|
Display the mappings between host public keys and SSH servers saved on a client |
display ssh server-info |
Available in any view |
|
Display information about a specified or all SSH users |
display ssh user-information [ username ] |
Available in any view |
1.7 SSH Server Configuration Example
I. Network requirements
As shown in Figure 1-12, a local SSH connection is established between the configuration terminal (SSH client) and the switch for secure data exchange. The username of the SSH client is client001, and the password is aabbcc.
II. Network diagram

Figure 1-12 Network diagram for SSH server configuration
III. Configuration procedure
The configuration procedure varies with login authentication modes. However, you must complete the following three configuration tasks before any configuration procedure.
First, create an RSA host key pair and server key pair and enable the SSH server.
<Switch> system-view
[Switch] rsa local-key-pair create
The range of public key size is (512 ~ 2048).
NOTES: If the key modulus is greater than 512,
It will take a few minutes.
Input the bits in the modulus[default = 1024]:
Generating keys...
.....++++++++++++
...++++++++++++
................++++++++
.............++++++++
......Done!
[Switch] ssh server enable
& Note:
If you have created an RSA host key pair and server key pair, you can skip this step.
Then, you must create a VLAN interface on the switch and assign an IP address, which the SSH client will use as the destination for SSH connection.
[Switch] interface vlan-interface 1
[Switch-Vlan-interface1] ip address 192.168.0.1 255.255.255.0
[Switch-Vlan-interface1] quit
Finally, you must configure an IP address (192.168.0.2 in this case) for the SSH client. This IP address and that of the VLAN interface on the switch must be in the same network segment.
1) Set the SSH authentication method as password
# Set the authentication method for the SSH client to AAA. (AAA adopts the default ISP domain system and the default scheme local.)
[Switch] user-interface vty 0 4
[Switch-ui-vty0-4] authentication-mode scheme
# Set the protocol that a remote user uses to login as SSH.
[Switch-ui-vty0-4] protocol inbound ssh
[Switch-ui-vty0-4] quit
# Create local user client001,Set the service type to SSH, Specify commands of level 3 are available to the user.
[Switch] local-user client001
[Switch-luser-client001] password simple aabbcc
[Switch-luser-client001] service-type ssh level 3
[Switch-luser-client001] quit
The SSH authentication timeout period, number of SSH authentication attempts and server key pair update interval can be the default values.
After the above configurations, complete these tasks on the client to login to the server securely:
l Run the SSH2.0-enabled client software.
l Configure 192.168.0.1 as the IP address of the SSH server.
l Set the protocol type to SSH.
l Set the protocol version to 2.
l Initiate the SSH connection, enter the username of client001 and password of aabbcc as prompted.
2) Set the SSH authentication method to RSA
# Set the authentication method of the user interface to AAA.
[Switch] user-interface vty 0 4
[Switch-ui-vty0-4] authentication-mode scheme
# Set the command level for the login users to 3.
[Switch-ui-vty0-4] user privilege level 3
# Set the protocol that a remote user uses to login as SSH.
[Switch-ui-vty0-4] protocol inbound ssh
[Switch-ui-vty0-4] quit
# Set the SSH user authentication method as RSA.
[Switch] ssh user client001 authentication-type rsa
At this time, the client supporting SSH2.0 will generate a random RSA key pair, including public key and private key. You need to add the RSA public key, a hexadecimal character string encoded by the SSHKEY.EXE software in accordance with the public key cryptography standards (PKCS), to the rsa peer-public-key on the specified SSH server in the following way.
# Configure the RSA public key of the client manually or import it from a public key file, Switch001, for example.
[Switch] rsa peer-public-key Switch001
[Switch-rsa-public-key] public-key-code begin
[Switch-rsa-key-code]30818602 818078C4 32AD7864 BB0137AA 516284BB 3F55F0E3
[Switch-rsa-key-code]F6DD9FC2 4A570215 68D2B3F7 5188A1C3 2B2D40BE D47A08FA
[Switch-rsa-key-code]CF41AF4E 8CCC2ED0 C5F9D1C5 22FC0625 BA54BCB3 D1CBB500
[Switch-rsa-key-code]A177E917 642BE3B5 C683B0EB 1EC041F0 08EF60B7 8B6ED628
[Switch-rsa-key-code]9830ED46 0BA21FDB F55E7C81 5D1A2045 54BFC853 5358E5CF
[Switch-rsa-key-code]7D7DDF25 03C44C00 E2F49539 5C4B0201 25
[Switch-rsa-key-code] public-key-code end
[Switch-rsa-public-key] peer-public-key end
Or:
[Switch] rsa peer-public-key Switch001 import sshkey Switch001
# Specify a public key of Switch001 for user client001.
[Switch] ssh user client001 assign rsa-key Switch001
& Note:
On the client, you need to specify the corresponding RSA private key of the RSA public key for the SSH user client001.
By now, you can run SSH2.0 on the terminal containing the RSA private key and perform corresponding configuration to establish an SSH connection.
1.8 SSH Client Configuration Example
I. Network requirements
As shown in Figure 1-13, SwitchA is an SSH client and needs to login to SwitchB through the SSH protocol. The username of the SSH client is client001 and the password is aabbcc.
II. Network diagram

Figure 1-13 Network diagram for SSH client configuration
III. Configuration procedure
1) Configure SwitchB
# Create an RSA host key pair and server key pair and enable the SSH server.
<SwitchB> system-view
[SwitchB] rsa local-key-pair create
The range of public key size is (512 ~ 2048).
NOTES: If the key modulus is greater than 512,
It will take a few minutes.
Input the bits in the modulus[default = 1024]:
Generating keys...
..........++++++++++++
....................++++++++++++
............++++++++
...........................++++++++
......Done!
[SwitchB] ssh server enable
& Note:
If you have created an RSA host key pair and server key pair, you can skip this step.
# Create a VLAN interface and assign an IP address, which the SSH client will use as the destination for SSH connection.
[SwitchB] interface vlan-interface 1
[SwitchB-Vlan-interface1] ip address 10.165.87.136 255.255.255.0
[SwitchB-Vlan-interface1] quit
# Set the authentication method of the user interface to AAA for SSH client. (AAA adopts the default ISP domain system and the default scheme local.)
[SwitchB] user-interface vty 0 4
[SwitchB-ui-vty0-4] authentication-mode scheme
# Set the protocol that a remote user uses to login as SSH.
[SwitchB-ui-vty0-4] protocol inbound ssh
[SwitchB-ui-vty0-4] quit
# Create local user client001, Set the service type to SSH, Specify commands of level 3 are available to the user.
[SwitchB] local-user client001
[SwitchB-luser-client001] password simple aabbcc
[SwitchB-luser-client001] service-type ssh level 3
[SwitchB-luser-client001] quit
# Set the SSH authentication method to password. The SSH authentication timeout period, number of SSH authentication attempts and server key pair update interval can be the default values.)
& Note:
If you set the SSH authentication method to RSA, you need to configure a host public key of Switch A. For the specific configuration, refer to .1.7 SSH Server Configuration Example .
2) Configure SwitchA
# Configure an IP address (10.165.87.137 in this case) for the VLAN interface on SwitchA. This IP address and that of the VLAN interface on SwitchB must be in the same network segment.
<SwitchA> system-view
[SwitchA] interface vlan-interface 1
[SwitchA-Vlan-interface1] ip address 10.165.87.137 255.255.255.0
[SwitchA-Vlan-interface1] quit
# Initiate an SSH connection to server 10.165.87.136, using the default algorithms.
[SwitchA] ssh2 10.165.87.136
username: client001
Trying 10.165.87.136
Press CTRL+K to abort
Connected to 10.165.87.136...
The Server is not autherncated.Do you continue access it?(Y/N):y
Do you want to save the server's public key?(Y/N):y
Enter password:
**************************************************************************
* Copyright(c) 2004-2007 Hangzhou H3C Tech. Co., Ltd. All rights reserved. *
* Without the owner's prior written consent, *
* no decompiling or reverse-engineering shall be allowed. *
**************************************************************************
<SwitchA>
Chapter 2 SFTP Service
When configuring SFTP, go to these sections for information you are interested in:
2.1 SFTP Overview
The secure file transfer protocol (SFTP) is a new feature in SSH 2.0.
SFTP uses the SSH connection to provide secure data transfer. The device can serve as the SFTP server, allowing a remote user to login to the SFTP server for secure file management and transfer. The device can also server as an SFTP client, enabling a user to login from the device to a remote device for secure file transfer.
2.2 Configuring the SFTP Server
2.2.1 Configuration Prerequisites
l You have configured the SSH server. For the detailed configuration procedure, refer to SSH Configuration Tasks
l You have used the ssh user service-type command to set the service type of SSH users to sftp or all. For configuration procedure, refer to Specifying the Service Type of an SSH User
2.2.2 Enabling the SFTP Server
This configuration task is to enable the SFTP service so that a client can login to the SFTP server through SFTP.
Follow these steps to enable the SFTP server:
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Enable the SFTP server |
sftp server enable |
Required Disabled by default |
& Note:
When the device functions as the SFTP server, only one client can access the SFTP server at a time. If the SFTP client uses WinSCP, a file on the server cannot be modified directly; it can only be downloaded to a local place, modified, and then uploaded to the server.
2.2.3 Configuring the SFTP Connection Idle Timeout Period
Once the idle period of an SFTP connection exceeds the specified threshold, the system automatically tears the connection down.
Follow these steps to configure the SFTP connection idle timeout period:
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Configure the SFTP connection idle timeout period |
sftp server idle-timeout time-out-value |
Optional 10 minutes by default |
2.3 Configuring the SFTP Client
2.3.1 Specifying a Source IP Address or Interface for the SFTP Client
The client accesses the SFTP server using the specified IP address and port address.
Follow these steps to specify a source IP address or interface for the SFTP client:
|
To do… |
Use the command… |
Remarks |
|
|
Enter system view |
system-view |
— |
|
|
Specify a source IP address or interface for the SFTP client |
Specify a source IPv4 address or interface for the SFTP client |
sftp client source { ip ip-address | interface interface-type interface-number } |
Optional Use one command as required. By default, an SFTP client uses the interface address specified by the route of the device to access the SFTP server. |
|
Specify a source IPv6 address or interface for the SFTP client |
sftp client ipv6 source { ipv6 ipv6-address | interface interface-type interface-number } |
||
2.3.2 Establishing a Connection to the SFTP Server
This configuration task is to enable the SFTP client to establish a connection with the remote SFTP server and enter SFTP client view.
Follow these steps to enable the SFTP client:
|
To do… |
Use the command… |
Remarks |
|
|
Enter system view |
system-view |
— |
|
|
Establish a connection to the remote SFTP server and enter SFTP client view |
Establish a connection to the remote IPv4 SFTP server and enter SFTP client view |
sftp { host-ip | host-name } [ port-number ] [ prefer_kex { dh_group1 | dh_exchange_group } | prefer_ctos_cipher { des | aes128 } | prefer_stoc_cipher { des | aes128 } | prefer_ctos_hmac { sha1 | sha1_96 | md5 | md5_96 } | prefer_stoc_hmac { sha1 | sha1_96 | md5 | md5_96 } ]* |
Use one command as required. |
|
Establish a connection to the remote IPv6 SFTP server and enter SFTP client view |
sftp ipv6 { ipv6-address | host-name } [ port-number ] [ prefer_ctos_cipher { aes128 | des } | prefer_ctos_hmac { md5 | md5_96 | sha1 | sha1_96 } | prefer_kex { dh_exchange_group | dh_group1 } | prefer_stoc_cipher { aes128 | des } | prefer_stoc_hmac { md5 | md5_96 | sha1 | sha1_96 } ] * |
||
2.3.3 Working with the SFTP Directories
SFTP directory operations include:
l Changing or displaying the current working directory
l Displaying files under a specified directory or the directory information
l Changing the name of a specified directory on the server
l Creating or deleting a directory
Follow these steps to work with the SFTP directories:
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Establish a connection to the remote SFTP server and enter SFTP client view |
sftp { host-ip | host-name } [ port-number ] [ prefer_kex { dh_group1 | dh_exchange_group } | prefer_ctos_cipher { des | aes128 } | prefer_stoc_cipher { des | aes128 } | prefer_ctos_hmac { sha1 | sha1_96 | md5 | md5_96 } | prefer_stoc_hmac { sha1 | sha1_96 | md5 | md5_96 } ]* |
Required |
|
Change the name of a specified directory on the SFTP server |
rename old-name new-name |
Optional You unnecessarily follow this sequence to carry out the commands. The dir command functions as the ls command does. |
|
Change the working directory of the remote SFTP server |
cd [ remote-path ] |
|
|
Return to the upper-level directory |
cdup |
|
|
Display the current working directory of the remote SFTP server |
pwd |
|
|
Display files under a specified directory |
dir [ remote-path ] |
|
|
ls [ remote-path ] |
||
|
Create a new directory on the remote SFTP server |
mkdir remote-path |
|
|
Delete a directory from the SFTP server |
rmdir remote-path |
2.3.4 Working with SFTP Files
l Changing the name of a file
l Downloading a file
l Uploading a file
l Displaying a list of the files
l Deleting a file
Follow these steps to work with SFTP files:
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Establish a connection to the remote SFTP server and enter SFTP client view |
sftp { host-ip | host-name } [ port-number ] [ prefer_kex { dh_group1 | dh_exchange_group } | prefer_ctos_cipher { des | aes128 } | prefer_stoc_cipher { des | aes128 } | prefer_ctos_hmac { sha1 | sha1_96 | md5 | md5_96 } | prefer_stoc_hmac { sha1 | sha1_96 | md5 | md5_96 } ]* |
Required |
|
Change the name of a specified file on the SFTP server |
rename old-name new-name |
Optional. |
|
Download a file from the remote server and save it locally |
get remote-file [ local-file ] |
Optional |
|
Upload a local file to the remote SFTP server |
put local-file [ remote-file ] |
Optional |
|
Display the files under a specified directory |
dir [ remote-path ] |
Optional The dir command functions as the ls command. |
|
ls [ remote-path ] |
||
|
Delete a file from the SFTP server |
delete remote-file |
Optional The delete command functions as the remove command. |
|
remove remote-file |
2.3.5 Displaying Help Information
This configuration task is to display a list of all commands or the help information of an SFTP client command, such as the command format and parameters.
Follow these steps to display a list of all commands or the help information of an SFTP client command:
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Establish a connection to the remote SFTP server and enter SFTP client view |
sftp { host-ip | host-name } [ port-number ] [ prefer_kex { dh_group1 | dh_exchange_group } | prefer_ctos_cipher { des | aes128 } | prefer_stoc_cipher { des | aes128 } | prefer_ctos_hmac { sha1 | sha1_96 | md5 | md5_96 } | prefer_stoc_hmac { sha1 | sha1_96 | md5 | md5_96 } ]* |
Required |
|
Display a list of all commands or the help information of an SFTP client command |
help [ all | command-name ] |
Optional |
2.3.6 Disabling the SFTP Client
This configuration task is to disable the SFTP client.
Follow these steps to disable the SFTP client:
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Establish a connection to the remote SFTP server and enter SFTP client view |
sftp { host-ip | host-name } [ port-number ] [ prefer_kex { dh_group1 | dh_exchange_group } | prefer_ctos_cipher { des | aes128 } | prefer_stoc_cipher { des | aes128 } | prefer_ctos_hmac { sha1 | sha1_96 | md5 | md5_96 } | prefer_stoc_hmac { sha1 | sha1_96 | md5 | md5_96 } ]* |
— |
|
Terminate the connection to the remote SFTP server and return to system view |
bye |
Required. These three commands function in the same way. |
|
exit |
||
|
quit |
2.4 SFTP Configuration Example
I. Network requirements
As shown in Figure 2-1, an SSH connection is established between SwitchA and SwitchB. SwitchA, an SFTP client, uses the username client001 and password aabbcc to login to SwitchB for file management and file transfer.
II. Network diagram

Figure 2-1 Network diagram for SFTP configuration
III. Configuration procedure
1) Configure the SFTP server (SwitchB)
# Create an RSA host key pair and server key pair and enable the SSH server.
<SwitchB> system-view
[SwitchB] rsa local-key-pair create
The range of public key size is (512 ~ 2048).
NOTES: If the key modulus is greater than 512,
It will take a few minutes.
Input the bits in the modulus[default = 1024]:
Generating keys...
..........++++++++++++
....................++++++++++++
............++++++++
...........................++++++++
......Done!
[SwitchB] ssh server enable
& Note:
If you have created an RSA host key pair and server key pair, you can skip this step.
# Create a VLAN interface on SwitchB and assign an IP address, which the SSH client uses as the destination for SSH connection.
[SwitchB] interface Vlan-interface 1
[SwitchB-Vlan-interface1] ip address 192.168.0.1 255.255.255.0
[SwitchB-Vlan-interface1] quit
# Set the authentication method on the user interface to AAA. (AAA adopts the default ISP domain system and the default scheme local.)
[SwitchB] user-interface vty 0 4
[SwitchB-ui-vty0-4] authentication-mode scheme
# Set the protocol that a remote user uses to login as SSH.
[SwitchB-ui-vty0-4] protocol inbound ssh
[SwitchB-ui-vty0-4] quit
# Create local user client001, Set the service type to SSH, Specify commands of level 3 are available to the user.
[SwitchB] local-user client001
[SwitchB-luser-client001] password simple aabbcc
[SwitchB-luser-client001] service-type ssh level 3
[SwitchB-luser-client001] quit
# Set the SSH authentication method to password. The SSH authentication timeout period, number of SSH authentication attempts and server key pair update interval can be default values.
& Note:
If you set the SSH authentication method to RSA, you need to configure the host public key of SwitchA. For the specific configuration, refer to .1.7 SSH Server Configuration Example
# Specify the user service type as SFTP.
[SwitchB] ssh user client001 service-type sftp
# Enable the SFTP server.
[SwitchB] sftp server enable
2) Configure the SFTP client (SwitchA)
# Configure an IP address (192.168.0.2 in this case) for the VLAN interface on SwitchA. This IP address and that of the VLAN interface on SwitchB must be in the same network segment.
<SwitchA> system-view
[SwitchA] interface vlan-interface 1
[SwitchA-Vlan-interface1] ip address 192.168.0.2 255.255.255.0
[SwitchA-Vlan-interface1] quit
# Establish a connection with the remote SFTP server and enter SFTP client view.
[SwitchA] sftp 192.168.0.1
Input Username: client001
Trying 192.168.0.1 ...
Press CTRL+K to abort
Connected to 192.168.0.1 ...
The Server is not authenticated. Do you continue access it? [Y/N]:y
Do you want to save the server's public key? [Y/N]:y
Enter password:
sftp-client>
# Display files under the current directory of the server, delete the file of z, and check that the file is deleted successfully.
sftp-client> dir
-rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg
-rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2
-rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey1
drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new
-rwxrwxrwx 1 noone nogroup 225 Sep 01 06:55 pub
-rwxrwxrwx 1 noone nogroup 0 Sep 01 08:00 z
sftp-client> delete z
The following files will be deleted:
/z
Are you sure to delete it? [Y/N]:y
This operation may take a long time.Please wait...
File successfully Removed
sftp-client> dir
-rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg
-rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2
-rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey1
drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new
-rwxrwxrwx 1 noone nogroup 225 Sep 01 06:55 pub
# Add a directory named new1 and check that it is created successfully.
sftp-client> mkdir new1
New directory created
sftp-client> dir
-rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg
-rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2
-rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey1
drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new
-rwxrwxrwx 1 noone nogroup 225 Sep 01 06:55 pub
drwxrwxrwx 1 noone nogroup 0 Sep 02 06:30 new1
# Change the directory name new1 to new2 and check that the directory name is changed successfully.
sftp-client> rename new1 new2
File successfully renamed
sftp-client> dir
-rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg
-rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2
-rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey1
drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new
-rwxrwxrwx 1 noone nogroup 225 Sep 01 06:55 pub
drwxrwxrwx 1 noone nogroup 0 Sep 02 06:33 new2
# Download the pubkey2 file from the server and save it local file public.
sftp-client> get pubkey2 public
Remote file:/pubkey2 ---> Local file: public
Downloading file successfully ended
# Upload a local file named pu to the server, save it as puk, and check the file is uploaded successfully.
sftp-client> put pu puk
Local file:pu ---> Remote file: /puk
Uploading file successfully ended
sftp-client> dir
-rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg
-rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2
-rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey1
drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new
drwxrwxrwx 1 noone nogroup 0 Sep 02 06:33 new2
-rwxrwxrwx 1 noone nogroup 283 Sep 02 06:35 pub
-rwxrwxrwx 1 noone nogroup 283 Sep 02 06:36 puk
sftp-client>
# Terminate the connection with the remote SFTP server.
sftp-client> quit
Bye
[SwitchA]
