- Table of Contents
-
- H3C S5500-SI Series Ethernet Switches Operation Manual-Release 1205-(V1.03)
- 00-1Cover
- 00-2Overview
- 01-Login Operation
- 02-Basic System Configuration and Maintenance Operation
- 03-File System Management Operation
- 04-VLAN Operation
- 05-QinQ-BPDU TUNNEL Operation
- 06-Port Correlation Configuration Operation
- 07-MAC Address Table Management Operation
- 08-MSTP Operation
- 09-IP Address and Performance Operation
- 10-IPv6 Configuration Operation
- 11-Routing Overview Operation
- 12-IPV4 Routing Operation
- 13-IPv6 Routing Operation
- 14-802.1x-HABP-MAC Authentication Operation
- 15-AAA-RADIUS-HWTACACS Operation
- 16-Multicast Protocol Operation
- 17-ARP Operation
- 18-DHCP Operation
- 19-ACL Operation
- 20-QoS Operation
- 21-Port Mirroring Operation
- 22-Cluster Operation
- 23-SNMP-RMON Operation
- 24-NTP Operation
- 25-DNS Operation
- 26-Information Center Operation
- 27-NQA Operation
- 28-SSH Terminal Service Operation
- 29-UDP Helper Operation
- 30-SSL-HTTPS Operation
- 31-PKI Operation
- 32-PoE-PoE Profile Operation
- 33-Appendix
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 02-Basic System Configuration and Maintenance Operation | 2 MB |
Table of Contents
Chapter 1 Basic Configurations
1.1.1 Command Line Interface Overview
1.1.2 Online Help with Command Lines
1.1.5 Command Line Error Information
1.2.1 Entering/Exiting System View
1.2.2 Configuring CLI Language Mode
1.2.4 Configuring System Clock
1.2.7 Configuring User Levels and Command Levels
1.2.8 Displaying System Information
Chapter 2 System Maintaining and Debugging
2.1 System Maintaining and Debugging Overview
2.1.1 Introduction to System Maintaining and Debugging
2.1.2 Introduction to System Debugging
2.2 System Maintaining and Debugging
2.3 System Maintaining and Debugging Example
3.1 Device Management Overview
3.2 BootROM and Host Software Loading
3.2.1 Introduction to Loading Approaches
3.3 Configuring Device Management
3.3.2 Specifying a BootROM File for the Next Device Boot
3.3.3 Upgrading a BootROM File
3.3.4 Clearing the 16bit Interface Indexes Not Used in the Current System
3.4 Displaying and Maintaining Device Management Configuration
3.5 Device Management Configuration Example
3.5.1 Remote Upgrade Configuration Example
Chapter 1 Basic Configurations
While configuring BOOTP Client, go to these sections for information you are interested in:
1.1 CLI Features
This section covers the following topics:
l Command Line Interface Overview
l Online Help with Command Lines
l Command Line Error Information
1.1.1 Command Line Interface Overview
S5500-SI Series Ethernet Switches provide a series of configuration commands and command line interface for you to configure and maintain the Ethernet switches. The command line interface is featured by the following:
l Configure the command levels to make sure that unauthorized users cannot use related commands to configure a switch.
l You can enter <?> at any time to get the online help.
l Provide network test commands, such as tracert, and ping, to help you to diagnose the network.
l Provide plenty of detail debugging information to help you to diagnose and locate the network failures.
l Provide a function similar to Doskey to execute a history command.
l Adopt the partial match method to search for the keywords of a command line. You only need to enter a non-conflicting keyword to execute the command correctly.
1.1.2 Online Help with Command Lines
The following are the types of online help available with the CLI:
l Full help
l Fuzzy help
To obtain the desired help information, you can:
1) Enter “?” in any view to access all the commands in this view and brief description about them as well.
User view commands:
backup Backup next startup-configuration file to TFTP server
boot-loader Set boot loader
bootrom Update/read/backup/restore bootrom
cd Change current directory
clock Specify the system clock
cluster Run cluster command
copy Copy from one file to another
debugging Enable system debugging functions
delete Delete a file
dir List files on a file system
display Show running system information
<omitted>
2) Enter a command and a “?” separated by a space. If "?" is at the position of a keyword, all the keywords are given with a brief description.
<Sysname> language-mode ?
chinese Chinese environment
english English environment
3) Enter a command and a “?” separated by a space. If "?" is at the position of a parameter, the description about these parameters is given.
<Sysname> system-view
[Sysname] interface Vlan-interface ?
<1-4094> VLAN interface
[Sysname] interface Vlan-interface 1 ?
<cr>
[Sysname] interface Vlan-interface 1
Where, <cr> indicates that there is no parameter at this position. The command is then repeated in the next command line and executed if <Enter> is input.
<Sysname> pi?
ping
5) Enter a command followed by a character string and “?”. All the keywords starting with this string are listed.
<Sysname> display ver?
version
6) Press <tab> after entering the first several letters of a keyword to display the complete keyword, provided these letters can uniquely identify the keyword in this command.
7) You can view the help information in Chinese with the language-mode command.
1.1.3 Display Features
CLI offers the following features:
l It offers both English and Chinese help information. You can toggle between them.
l When the information displayed exceeds one screen, you can pause using one of the methods shown in Table 1-1
|
Action |
Function |
|
Enter <Space> when information display pauses |
Continues to display information of the next screen page |
|
Enter <Enter> when information display pauses |
Continues to display information of the next line. |
|
Enter <Ctrl+C> when information display pauses |
Stops the display and the command execution. |
1.1.4 History Command
The CLI can automatically save the commands that have been entered. You can invoke and repeatedly execute them as needed. By default, the CLI can save up to ten commands for each user. Table 1-2 lists the operation that you can perform.
Table 1-2 Access history commands
|
To do… |
Use the Key/command… |
Result |
|
View the history commands |
display history-command |
Displays the commands that you have entered |
|
Access the last history command |
Up-arrow key or <Ctrl+P> |
Displays the earlier history command, if there is any. Otherwise, the system rings alarm. |
|
Access the next history command |
Down-arrow key or <Ctrl+N> |
Displays the next history command, if there is any. Otherwise, the system clears the commands and rings alarm. |
& Note:
You may use arrow keys to access history commands in Windows 2000/XP Terminal or Telnet. However, the up-arrow and down-arrow keys are invalid in Windows 9X HyperTerminal, because they are defined in a different way. You can use <Ctrl+P> and <Ctrl+N> instead.
1.1.5 Command Line Error Information
The commands are executed only if they have no syntax error. Otherwise, error information is reported. Table 1-3 lists some common errors.
Table 1-3 Common command line errors
|
Error information |
Cause |
|
Unrecognized command |
The command was not found. |
|
The keyword was not found. |
|
|
Parameter type error |
|
|
The parameter value is beyond the allowed range. |
|
|
Incomplete command |
Incomplete command |
|
Too many parameters |
Too many parameters are input. |
|
Ambiguous command |
Parameter value input is ambiguous. |
|
Wrong parameter |
Wrong parameter |
1.1.6 Edit Features
The CLI provides the basic command edit functions and supports multi-line editing. The maximum length of each command is 256 characters. Table 1-4 lists these functions.
|
Key |
Function |
|
Common Keys |
If the editing buffer is not full, insert the character at the position of the cursor and move the cursor to the right. Otherwise, the alarm rings. |
|
<Backspace> key |
Delete the character to the left of the cursor and move the cursor back one character. If the cursor gets to the beginning of the command line, the alarm rings. |
|
Left-arrow key or <Ctrl+B> |
The cursor moves one character space to the left, and the alarm rings when the cursor gets to the beginning of the command line. |
|
Right-arrow key or <Ctrl+F> |
The cursor moves one character space to the right, and the alarm rings when the cursor gets to end of the command line. |
|
Up-arrow key or <Ctrl+P> |
Display history command |
|
Down-arrow key or <Ctrl+N> |
|
|
<Tab> key |
Pressing <Tab> after entering part of a keyword enables the fuzzy help function. If finding a unique match, the system will substitute the complete keyword for the incomplete one and display it in the next line. If there are several matches or no match at all, the system will not modify the incomplete keyword and display it again in the next line. |
1.1.7 Command Line view
Different command views are implemented according to different requirements. They are related to one another. For example, after logging in the switch, you will enter user view, in which you can only use some basic functions such as displaying the running state and statistics information. In user view, key in system-view to enter system view, in which you can key in different configuration commands and enter the corresponding views.
The command line provides the following views:
l User view
l System view
l Ethernet Port view
l NULL interface view
l VLAN view
l VLAN interface view
l LoopBack interface view
l Local-user view
l User interface view
l FTP Client view
l MST region view
l IGMP-Snooping view
l MLD-Snooping view
l Traffic classifier view
l Traffic behavior view
l QoS policy view
l Cluster view
l Port group view
l NQA view
l HWTACACS scheme view
l RSA public key view
l RSA key code view
l Route policy view
l Basic ACL view
l Advanced ACL view
l Layer 2 ACL view
l QinQ view
l RADIUS scheme view
l RIP view
l RIPng view
l ISP domain view
The following table describes the function features of different views and the ways to enter or quit.
Table 1-5 Command view function list
|
Command view |
Function |
Prompt |
Command to enter |
Command to exit |
|
User view |
Show the basic information about operation and statistics |
<Sysname> |
Enter right after connecting the switch |
quit disconnects to the switch |
|
System view |
Configure system parameters |
[Sysname] |
Key in system-view in user view |
quit or return returns to user view |
|
Ethernet Port view |
Configure Ethernet port parameters |
[Sysname- GigabitEthernet1/0/1] |
GigabitEthernet port view Key in interface gigabitethernet 1/0/1 in system view |
quit returns to system view return returns to user view |
|
NULL interface view |
Configure NULL interface parameters |
[Sysname-NULL0] |
Key in interface null 0 in system view |
quit returns to system view return returns to user view |
|
VLAN view |
Configure VLAN parameters |
[Sysname-vlan1] |
Key in vlan 1 in system view |
quit returns to system view return returns to user view |
|
VLAN interface view |
Configure IP interface parameters for a VLAN or a VLAN aggregation |
[Sysname-Vlan- interface1] |
Key in interface Vlan-interface 1 in system view |
quit returns to system view return returns to user view |
|
LoopBack interface view |
Configure LoopBack interface parameters |
[Sysname- LoopBack0] |
Key in interface loopback 0 in system view |
quit returns to system view return returns to user view |
|
Local-user view |
Configure local user parameters |
[Sysname-luser- user1] |
Key in local-user user1 in system view |
quit returns to system view return returns to user view |
|
User interface view |
Configure user interface parameters |
[Sysname-ui0] |
Key in user-interface 0 in system view |
quit returns to system view return returns to user view |
|
FTP Client view |
Configure FTP Client parameters |
[ftp] |
Key in ftp in user view |
quit returns to user view |
|
MST region view |
Configure MST region parameters |
[Sysname-mst- region] |
Key in stp region-configuration in system view |
quit returns to system view return returns to user view |
|
IGMP-Snooping view |
Configure IGMP–Snooping protocol parameters |
[Sysname-igmp- snooping] |
Key in igmp-snooping in system view |
quit returns to system view return returns to user view |
|
MLD-Snooping view |
Configure MLD-Snooping protocol parameters |
[Sysname-mld- snooping] |
Key in mld-snooping in system view |
quit returns to system view return returns to user view |
|
Traffic classifier view |
Configure traffic classifier related parameters |
[Sysname-classifier-test] |
Key in traffic classifier test in system view |
quit returns to system view return returns to user view |
|
Traffic behavior view |
Configure traffic behavior related parameters |
[Sysname-behavior-test] |
Key in traffic behavior test in system view |
quit returns to system view return returns to user view |
|
QoS policy view |
Configure QoS policy related parameters |
[Sysname- qospolicy-test] |
Key in qos policy test in system view |
quit returns to system view return returns to user view |
|
Cluster view |
Configure cluster parameters |
[Sysname-cluster] |
Key in cluster in system view |
quit returns to system view return returns to user view |
|
Port group view |
Configure manual port group parameters |
[Sysname-port- group-manual-test] |
Key in port-group manual test in system view |
quit returns to system view return returns to user view |
|
Configure aggregate port group parameters |
[Sysname-port- group-aggregation-1] |
Key in port-group aggregation 1 in system view |
||
|
NQA view |
Configure NQA test group parameters |
[Sysname-nqa- admin-test] |
Key in nqa admin test in system view |
quit returns to system view return returns to user view |
|
HWTACACS scheme view |
Configure HWTACACS parameters |
[Sysname- hwtacacs-test] |
Key in hwtacacs scheme test in system view |
quit returns to system view return returns to user view |
|
RSA public key view |
Configure RSA public key of SSH user |
[Sysname-rsa- public-key] |
Key in rsa peer-public-key 003 in system view |
peer-public-key end returns to system view |
|
RSA key code view |
Edit RSA public key of SSH user |
[Sysname-rsa-key- code] |
Key in public-key-code begin in RSA public key view |
public-key-code end returns to RSA public key view |
|
Route policy view |
Configure route policy |
[Sysname-route- policy] |
Key in route-policy policy1 permit node 10 in system view |
quit returns to system view return returns to user view |
|
Basic ACL view |
Define the sub rule of the basic ACL (in the range of 2,000 to 2,999) |
[Sysname-acl-basic-2000] |
Key in acl number 2000 in system view |
quit returns to system view return returns to user view |
|
Advanced ACL view |
Define the sub rule of the advanced ACL (in the range of 3,000 to 3,999) |
[Sysname-acl-adv- 3000] |
Key in acl number 3000 in system view |
quit returns to system view return returns to user view |
|
Layer 2 ACL view |
Define the sub rule of the Layer 2 ACL (in the range of 4,000 to 4,999) |
[Sysname-acl- ethernetframe-4000] |
Key in acl number 4000 in system view |
quit returns to system view return returns to user view |
|
QinQ view |
Create a QinQ instance and configure QinQ related parameters. |
[Sysname- GigabitEthernet1/0/1-vid-1] |
Key in vlan-vpn vid 1 in Ethernet port view |
quit returns to system view return returns to user view |
|
RADIUS scheme view |
Configure RADIUS parameters |
[Sysname-radius-1] |
Key in radius scheme 1 in system view |
quit returns to system view return returns to user view |
|
RIP view |
Configure RIP parameters |
[Sysname-rip-1] |
Key in rip in system view |
quit returns to system view return returns to user view |
|
RIPng view |
Configure RIPng parameters |
[Sysname-ripng-1] |
Key in ripng 1 in system view |
quit returns to system view return returns to user view |
|
ISP domain view |
Configure ISP domain parameters |
[Sysname-isp- aabbcc.net] |
Key in domain aabbcc.net in system view |
quit returns to system view return returns to user view |
1.2 Basic Configurations
This section covers the following topics:
l Entering/Exiting System View
l Configuring CLI Language Mode
l Configuring User Levels and Command Levels
l Displaying System Information
1.2.1 Entering/Exiting System View
Table 1-6 Follow these steps to enter/exit system view
|
To do… |
Use the command… |
Remarks |
|
Enter system view from user view |
system-view |
— |
|
Return to user view from system view |
quit |
— |
& Note:
With the quit command, you can return to the previous view or exit the system from user view. The hot key <Ctrl+Z> is equivalent to the return command.
1.2.2 Configuring CLI Language Mode
Table 1-7 Follow these steps to configure CLI language mode
|
To do… |
Use the command… |
Remarks |
|
Switch CLI language mode |
language-mode { chinese | english } |
Optional CLI language is English by default. |
1.2.3 Configuring Device Name
Table 1-8 Follow these steps to configure the device name
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Configure the router name |
sysname sysname |
Optional By default, the device name is H3C. |
1.2.4 Configuring System Clock
Table 1-9 Follow these steps to configure the system clock
|
To do… |
Use the command… |
Remarks |
|
Set the standard time |
clock datetime time date |
Optional |
|
Set the time zone |
clock timezone time-zone-name { add | minus } time |
Optional |
|
Set a daylight summer time scheme |
clock summer-time zone-name one-off start-time start-date end-time end-date add-time |
Optional |
|
clock summer-time zone-name repeating start-time start-date end-time end-date add-time |
1.2.5 Configuring a Banner
I. Introduction to banner
A banner is the greeting information that the system displays when a user connects to the device, undergoes login authentication, or performs interactive configuration. An administrator can set a banner as required.
Currently, the following types of banners are supported.
l Shell banner: Also known as session banner, it is displayed when the user enters a Console session.
l User interface banner: Also known as incoming banner, it is displayed when the user interface is activated through a TTY modem.
l Login banner: It is displayed if password authentication is enabled and an authentication scheme is configured.
l motd banner: It is displayed before the authentication is started.
l Authorization banner: It is also known as legal banner. Before the user logs in, the system prompts some copyright or authorization information, then displays the legal banner, and waits while the user confirms whether to proceed with the authentication or to log in. If the user enters "Y" or directly press Enter, the authentication or login procedure is started; if the user enters "N", the user quits the authentication or login. Note that "Y" and "N" are case insensitive.
II. Setting a banner
You can configure a banner in two ways. One is to enter all the banner text immediately following the command keyword. The starting character and ending character of the text entered must be the same. These two characters, however, will not be part of the banner. In this mode, up to 510 characters, including the command keyword, starting character, and ending character, can be entered. The other is to enter all the banner text in multiple lines by pressing Enter. In this case, up to 2,000 characters can be entered.
To enter the banner text in multiple lines, you can use one of the following three methods:
l Directly press Enter following the command keyword, then enter the contents, and finish setting the banner by an ending character "%". In this case, neither the Enter sign nor "%" is part of the banner.
l Press Enter after entering a character following the command keyword, then enter the contents and finish setting the banner by an ending character the same as the character entered in the first line. In this case, neither the character in the first line nor the ending character is part of the banner.
l Press Enter after entering multiple characters (with different characters at both ends) following the command keyword, then enter the contents and finish setting the banner by an ending character the same as the first character in the first line. In this case, neither the first character in the first line nor the ending character is part of the banner.
Table 1-10 Follow these steps to configure a banner
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Configure the banner to be displayed at login |
header incoming text |
Optional |
|
Configure the banner to be displayed at login authentication |
header login text |
Optional |
|
Configure the banner to be displayed when a user enters user view |
header shell text |
Optional |
|
Configure the banner to be displayed before the login interface |
header motd text |
Optional |
1.2.6 Configuring CLI Hotkeys
Table 1-11 Follow these steps to configure CLI hotkeys
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Configure CLI hotkeys |
hotkey { CTRL_G | CTRL_L | CTRL_O | CTRL_T | CTRL_U } command |
Optional The <CTRL+G>, <CTRL+L> and <CTRL+O> hotkeys are specified with command lines by default. |
|
Display hotkeys |
display hotkey |
Available in any view. Refer to Table 1-12 for hotkeys reserved by system. |
& Note:
By default, the <CTRL+G>, <CTRL+L> and <CTRL+O> hotkeys are configured with command line and the <CTRL+T> and <CTRL+U> commands are NULL.
l <CTRL+G> corresponds to the display current-configuration command.
l <CTRL+L> corresponds to the display ip routing-table command.
l <CTRL+O> corresponds to the undo debugging all command.
Table 1-12 Hotkeys reserved by the system
|
Hotkey |
Function |
|
<CTRL+A> |
Move the cursor to the beginning of the current line. |
|
<CTRL+B> |
Move the cursor one character to the left. |
|
<CTRL+C> |
Stop performing a command. |
|
<CTRL+D> |
Delete a character. |
|
<CTRL+E> |
Move the cursor to the end of the current line. |
|
<CTRL+F> |
Move the cursor one character to the right. |
|
<CTRL+H> |
Delete the character to the left of the cursor. |
|
<CTRL+K> |
Break an outward connection. |
|
<CTRL+N> |
Display the next command after history command buffer. |
|
<CTRL+P> |
Display the next command before history command buffer. |
|
<CTRL+R> |
Redisplay the current line information. |
|
<CTRL+V> |
Paste the content in the clipboard. |
|
<CTRL+W> |
Delete all the characters in a continuous string to the left of the cursor. |
|
<CTRL+X> |
Delete all the characters to the left of the cursor. |
|
<CTRL+Y> |
Delete all the characters to the right of the cursor. |
|
<CTRL+Z> |
Exit to user view. |
|
<CTRL+]> |
Break an inward connection or redirect connection. |
|
<Esc+B> |
Move the cursor to the leading character of the continuous string to the left. |
|
<Esc+D> |
Delete all the characters of the continuous string to the left of the cursor. |
|
<Esc+F> |
Move the cursor to the front of the next continuous string to the right. |
|
<Esc+N> |
Move the cursor down by one line (available before press the Enter key) |
|
<Esc+P> |
Move the cursor up by one line (available before press the Enter key) |
|
<Esc+<> |
Specify the cursor as the beginning of the clipboard. |
|
<Esc+>> |
Specify the cursor as the ending of the clipboard. |
& Note:
These hotkeys are defined by the system. When a user interacts with the device from terminal software, they may be defined to perform other operations. If so, the definition of the terminal software will dominate.
1.2.7 Configuring User Levels and Command Levels
All the commands are defaulted to different views and categorized into four levels: visit, monitor, system, and manage, identified respectively by 0 through 3. If a user wants to acquire a higher privilege, he must switch to a higher user level, and it requires password to do so for the security’s sake.
The following table describes the default level of the commands.
Table 1-13 Default command levels
|
Level |
Privilege |
Command |
|
0 |
Visit |
ping, tracert, telnet |
|
1 |
Monitor |
display, debugging |
|
2 |
System |
All configuration commands except for those at manage level |
|
3 |
Manage |
FTP, TFTP, Xmodem, and file system operation commands |
Table 1-14 Follow these steps to configure user level and command level
|
To do… |
Use the command… |
Remarks |
|
Switch the user level |
super [ level ] |
Optional |
|
Enter system view |
system-view |
— |
|
Configure the password to switch the user level |
super password [ level user-level ] { simple | cipher } password |
Optional By default, no password is required to switch the user level. |
|
Configure the command level in system view |
command-privilege level level view view command |
Optional Change the command level only when necessary; otherwise, inconvenience may be caused to maintenance and operations. |
& Note:
l The commands available depend on the user level when the user login a device. For example, if the user level is 3 and the command level of VTY 0 interface is 1, the user can user command below level 3 (inclusive).
l When configuring the password for switching user level with the super password command, the user level is defaulted to 3 if no user level is specified.
l Cipher passwords are recommended, as simple ones are easy getting stolen.
l Users can switch to a lower user level unconditionally. To switch to a higher user level, however, they need to enter the password needed (The password can be set with the super password command.). If the entered password is incorrect or no password is configured, the switch fails. Therefore, before switching to a higher user level, users should configure the password needed.
1.2.8 Displaying System Information
In terms of function, you may collect these types of system status information with the display command:
l Configuration information
l Operating information
l Statistics
Table 1-15 Follow these steps to display system status information
|
To do… |
Use the command… |
|
Display information on system version |
display version |
|
Display information on the system clock |
display clock |
|
Display information on terminal users |
display users [ all ] |
|
Display the current configurations |
display current-configuration [ interface interface-type [ interface-number ] | configuration [ configuration-type ] ] | [ by-linenum ] | [ | { begin | include | exclude } text ] ] |
|
Display the valid configuration under current view |
display this [ by-linenum ] |
|
Display clipboard information |
display clipboard |
|
Display and save statistics of each module’s running status in the system |
display diagnostic-information |
During daily maintenance or when the system is operating abnormally, users need to view each module’s running status to find the problem. Therefore, they are required to execute the corresponding display commands one by one. To collect more information one time, users can execute the display diagnostic-information command in any view to display statistics of each module’s running status in the system. Use the display diagnostic-information command to collect at one time the information displayed by each of the following commands:
l display clock
l display version
l display device
l display current-configuration
l display saved-configuration
l display interface
l display memory
l display logbuffer
l display vlan all
l display history-command
l display trapbuffer
l display loopback-detection
l display dhcp-snooping
l display igmp-snooping group
l display mld-snooping group
l display gvrp statistics
l display ipv6 statistics
l display mac-address
l display link-aggregation summary
l display stp brief
l display arp all
l display ip interface
l display ip statistics
l display ipv6 interface
l display ipv6 fib
l display fib
l display ipv6 neighbors all
l display ip routing-table
l display ipv6 routing-table
l <omitted>
& Note:
l The display commands discussed above are for the global configuration. Refer to the corresponding section for the display command for specific protocol and interface.
l If no configuration file is enabled when starting the device, no information is displayed by the display saved-configuration command; otherwise, the information of the configuration file is displayed. For detailed information of the display saved-configuration command, see the File System Management part.
Chapter 2 System Maintaining and Debugging
When maintaining and debugging the system, go to these sections for information you are interested in:
l System Maintaining and Debugging Overview
l System Maintaining and Debugging
l System Maintaining and Debugging Example
2.1 System Maintaining and Debugging Overview
2.1.1 Introduction to System Maintaining and Debugging
You can use the ping command and the tracert command to verify the current network connectivity.
I. The ping command
Users can use the ping command to verify whether a device with a specified address is reachable, and to examine the network connectivity.
The ping command involves the follows steps in its execution:
1) The source device sends ICMP ECHO-REQUEST packets to the destination device.
2) If the network is functioning properly, the destination device will respond by sending the source device ICMP ECHO-REPLY packets after receiving the ICMP ECHO-REQUEST packets.
3) If there is network failure, the source device will display information indicating that the address is unreachable.
4) Display the relative statistics after execution of the ping command.
Output of the ping command includes:
l Information on the destination’s responses towards each ICMP ECHO-REQUEST packet: if the source device has received the ICMP ECHO-REPLY packet within the time-out timer, it will display the number of bytes of the ECHO-REPLY packet, the packet sequence number, Time To Live (TTL), and the response time.
l If within the period set by the time-out timer, the destination device has not received the response packets, it will display the prompt information.
l The ping command can apply to the destination’s name or IP address, if the destination’s name is unknown, the prompt information will be displayed.
l The statistics from execution of the command, which include number of sent packets, number of received ECHO-REPLY packets, percentage of packets that were not received, the minimum, average, and maximum response time.
& Note:
l For a low-speed network, you are recommended to use a larger value for the time-out timer (indicated by the -t parameter in the command) when configuring the ping command.
l If you specify the packet sending interface by providing the –i keyword when configuring the ping command, you can ping only the addresses in a directly connected network segment.
II. The tracert command
By using the tracert command, you can trace the routers involved in delivering a packet from source to destination. This is useful for identification of failed node(s) in the event of network failure.
The tracert command involves the following steps in its execution:
1) The source device sends a packet with a TTL value of 1 to the destination device.
2) The first hop (the router that first receives the packet) responds by sending a TTL-expired ICMP message with its IP address encapsulated to the source. In this way, the source device can get the address of the first router.
3) The source device sends a packet with a TTL value of 2 to the destination device.
4) The second hop responds with a TTL-expired ICMP message, which gives the source device the address of the second router.
5) The above process continues until the ultimate destination device is reached. In this way, the source device can trace the addresses of all the routers that have been used to get to the destination device.
2.1.2 Introduction to System Debugging
For the majority of protocols and new features provided, the system provides corresponding debugging functions to help users diagnose errors.
The following two switches control the display of debugging information:
l Protocol debugging switch, which controls protocol-specific debugging information
l Screen output function, which controls whether to output the debugging information on a certain screen.
Figure 2-1 illustrates the relationship between the protocol debugging switch and the screen output switch. Only when both are turned on can debugging information be output on a terminal.

Figure 2-1 The relationship between the protocol and screen debugging switch
2.2 System Maintaining and Debugging
2.2.1 System Maintaining
Table 2-1 Follow these steps to maintain the system
|
To do… |
Use the command… |
Remarks |
|
Check whether a specified IP address can be reached |
ping [ ip ] [ -a source-ip | -c count | -f | -h ttl | -i interface-type interface-number | -m interval | -n | -p pad | -q | -r | -s packet-size | -t timeout | -tos tos | -v] * { ip-address | hostname } |
Optional Available in any view |
|
View the routes from the source to the destination |
tracert [ -a source-ip | -f first-ttl | -m max-ttl | -p port | -q packet-number | -w timeout ] * { ip-address | hostname } |
2.2.2 System Debugging
Table 2-2 Follow these steps to debug the system
|
To do… |
Use the command… |
Remarks |
|
Enable debugging for a specified module |
debugging { all [ timeout time-value ] | module-name [ option ] } |
Available in user view |
|
Enable the terminal debugging |
terminal debugging |
|
|
Display the enabled debugging function |
display debugging [ interface interface-type interface-number ] [ module-name ] |
Available in any view |
& Note:
l The debugging commands are usually used by the administrator in diagnosing network failure.
l Output of the debugging information may reduce system efficiency, especially during execution of the debugging all command.
l After completing the debugging, you can use the undo debugging all command to disable all the debugging functions.
l The debugging output can be displayed only after you enable the current terminal to monitor system information by using the terminal monitor command and execute the debugging and terminal debugging commands.
2.3 System Maintaining and Debugging Example
I. Network requirements
l The IP address of the destination device is 10.1.1.4.
l Display the routers used while forwarding packets from the current device to the destination device.
II. Network diagram (omitted here)
III. Configuration procedure
<Sysname> tracert 10.1.1.4
traceroute to 10.1.1.4 (10.1.1.4) 30 hops max, 40 bytes packet, press CTRL_C to break
1 128.3.112.1 19 ms 19 ms 0 ms
2 128.32.216.1 39 ms 39 ms 19 ms
3 128.32.136.23 39 ms 40 ms 39 ms
4 128.32.168.22 39 ms 39 ms 39 ms
5 128.32.197.4 40 ms 59 ms 59 ms
6 131.119.2.5 59 ms 59 ms 59 ms
7 129.140.70.13 99 ms 99 ms 80 ms
8 129.140.71.6 139 ms 239 ms 319 ms
9 129.140.81.7 220 ms 199 ms 199 ms
10 10.1.1.4 239 ms 239 ms 239 ms
The above output shows that nine routers are used from the source to the destination device.
Chapter 3 Device Management
& Note:
You can express the path to and the names of the BootROM upgrade file, boot application, and configuration file in the Flash in the following formats:
l "Path + file name": That is, the full file name is used to indicate a file under the specified path. A full file name can contain up to 63 characters.
l "File name": That is, only the file name, without path name, is used to indicate a file under the current working path. A file name can contain up to 56 characters.
l BootROM upgrade file, boot file, and configuration file can be stored under the root directory flash:/ only.
When configuring device management, go to these sections for information you are interested in:
l BootROM and Host Software Loading
l Configuring Device Management
l Displaying and Maintaining Device Management Configuration
l Device Management Configuration Example
3.1 Device Management Overview
Through the device management function, you can view the current working state of devices, configure operation parameters, and perform daily device maintenance and management.
Currently, the following device management functions are available:
l Rebooting a device
l Specifying a scheduled device reboot
l Specifying a BootROM file for the next device reboot
l Upgrading a BootROM file
3.2 BootROM and Host Software Loading
Traditionally, the loading of switch software is accomplished through a serial port. This approach is slow, inconvenient, and cannot be used for remote loading. To resolve these problems, the TFTP and FTP modules are introduced into the switch. With these modules, you can load/download software/files conveniently to the switch through an Ethernet port.
This chapter introduces how to load BootROM and host software to a switch locally and how to do this remotely.
3.2.1 Introduction to Loading Approaches
I. You can load software locally by using:
l XMODEM through Console port
l TFTP through Ethernet port
l FTP through Ethernet port
II. You can load software remotely by using:
l FTP
l TFTP
& Note:
The BootROM software version should be compatible with the host software version when you load the BootROM and host software.
3.2.2 Local Software Loading
If your terminal is directly connected to the switch, you can load the BootROM and host software locally.
Before loading the software, make sure that your terminal is correctly connected to the switch to insure successful loading.
& Note:
The loading process of the BootROM software is the same as that of the host software, except that during the former process, you should press <Ctrl+U> and <Enter> after entering the Boot Menu and the system gives different prompts. The following text mainly describes the BootROM loading process.
I. Boot Menu
Starting......
***********************************************************
* *
* H3C S5500-28C-SI BOOTROM, Version 117 *
* *
***********************************************************
Copyright (c) 2004-2007 H3C Technologies Co., Ltd.
Creation date : Apr 15 2007, 20:31:56
CPU Clock Speed : 264MHz
BUS Clock Speed : 33MHz
Memory Size : 128MB
Mac Address : 000fe2bee200
Press Ctrl-B to enter Boot Menu...
Press <Ctrl+B>. The system displays:
Password :
& Note:
To enter the Boot Menu, you should press <Ctrl+B> within five seconds after the information “Press Ctrl-B to enter Boot Menu...” appears. Otherwise, the system starts to decompress the program; and if you want to enter the Boot Menu at this time, you will have to restart the switch.
Input the correct BootROM password (no password is need by default). The system enters the Boot Menu:
BOOT MENU
1. Download application file to flash
2. Select application file to boot
3. Display all files in flash
4. Delete file from flash
5. Modify bootrom password
6. Enter bootrom upgrade menu
7. Skip current configuration file
8. Set bootrom password recovery
9. Set switch startup mode
0. Reboot
Enter your choice(0-9):
II. Loading Software Using XMODEM through Console Port
XMODEM is a file transfer protocol that is widely used due to its simplicity and good performance. XMODEM transfers files via Console port. It supports two types of data packets (128 bytes and 1 KB), two check methods (checksum and CRC), and multiple attempts of error packet retransmission (generally the maximum number of retransmission attempts is ten).
The XMODEM transmission procedure is completed by a receiving program and a sending program: The receiving program sends negotiation characters to negotiate a packet checking method. After the negotiation, the sending program starts to transmit data packets. When receiving a complete packet, the receiving program checks the packet using the agreed method. If the check succeeds, the receiving program sends an acknowledgement character and the sending program proceeds to send another packet; otherwise, the receiving program sends a negative acknowledgement character and the sending program retransmits the packet.
1) Loading BootROM software
Step 1: At the prompt "Enter your choice(0-9):" in the Boot Menu, press <6> or <Ctrl+U>, and then press <Enter> to enter the BootROM update menu shown below:
Bootrom update menu:
1. Set TFTP protocol parameter
2. Set FTP protocol parameter
3. Set XMODEM protocol parameter
0. Return to boot menu
Enter your choice(0-3):
Step 2: Enter 3 in the above menu to download the BootROM software using XMODEM. The system displays the following download baud rate setting menu:
Please select your download baudrate:
1.* 9600
2. 19200
3. 38400
4. 57600
5. 115200
0. Return
Enter your choice (0-5):
Step 3: Choose an appropriate download baud rate. For example, if you enter 5, the baud rate 115200 bps is chosen and the system displays the following information:
Download baudrate is 115200 bps
Please change the terminal's baudrate to 115200 bps and select XMODEM protocol
Press enter key when ready
& Note:
If you have chosen 9600 bps as the download baud rate, you need not modify the HyperTerminal’s baud rate, and therefore you can skip Step 4 and 5 below and proceed to Step 6 directly. In this case, the system will not display the above information.
Following are configurations on PC. Take the HyperTerminal using Windows operating system as example.
Step 4: Choose [File/Properties] in HyperTerminal, click <Configure> in the pop-up dialog box, and then select the baud rate of 115200 bps in the Console port configuration dialog box that appears, as shown in Figure 3-1, Figure 3-2.

Figure 3-1 Properties dialog box

Figure 3-2 Console port configuration dialog box
Step 5: Click the <Disconnect> button to disconnect the HyperTerminal from the switch and then click the <Connect> button to reconnect the HyperTerminal to the switch, as shown in Figure 3-3.

Figure 3-3 Connect and disconnect buttons
& Note:
The new baud rate takes effect only after you disconnect and reconnect the HyperTerminal program.
Step 6: Press <Enter> to start downloading the program. The system displays the following information:
Now please start transfer file with XMODEM protocol.
If you want to exit, Press <Ctrl+X>.
Loading ...CCCCCCCCCC
Step 7: Choose [Transfer/Send File] in the HyperTerminal’s window, and click <Browse> in pop-up dialog box, as shown in Figure 3-4. Select the software you need to download, and set the protocol to XMODEM.
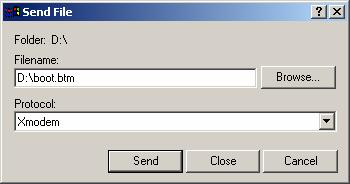
Figure 3-4 Send file dialog box
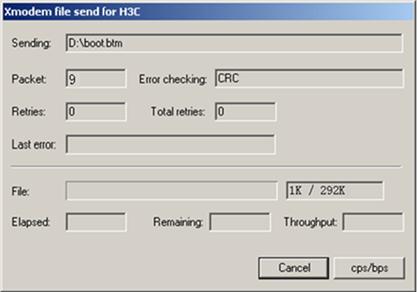
Step 8: Click <Send>. The system displays the page, as shown in Figure 3-5.
Step 9: After the download completes, the system displays the following information:
Loading ...CCCCCCCCCC done!
Step 10: Reset HyperTerminal’s baud rate to 9600 bps (refer to Step 4 and 5). Then, press any key as prompted. The system will display the following information when it completes the loading.
Bootrom updating.....................................done!
& Note:
l If the HyperTerminal’s baud rate is not reset to 9600 bps, the system prompts "Your baudrate should be set to 9600 bps again! Press enter key when ready".
l You need not reset the HyperTerminal’s baud rate and can skip the last step if you have chosen 9600 bps. In this case, the system upgrades BootROM automatically and prompts “Bootrom updating now.....................................done!”.
2) Loading host software
Follow these steps to load the host software:
Step 1: Select <1> in Boot Menu and press <Enter>. The system displays the following information:
1. Set TFTP protocol parameter
2. Set FTP protocol parameter
3. Set XMODEM protocol parameter
0. Return to boot menu
Enter your choice(0-3):
Step 2: Enter 3 in the above menu to download the host software using XMODEM.
The subsequent steps are the same as those for loading the BootROM software, except that the system gives the prompt for host software loading instead of BootROM loading.
III. Loading Software Using TFTP through Ethernet Port
TFTP, one protocol in TCP/IP protocol suite, is used for trivial file transfer between client and server. It uses UDP to provide unreliable data stream transfer service.
1) Loading BootROM software

Figure 3-6 Local loading using TFTP
Step 1: As shown in Figure 3-6, connect the switch through an Ethernet port to the TFTP server, and connect the switch through the Console port to the configuration PC.
& Note:
You can use one PC as both the configuration device and the TFTP server.
Step2: Run the TFTP server program on the TFTP server, and specify the path of the program to be downloaded.
![]() Caution:
Caution:
TFTP server program is not provided with the H3C S5500-SI Series Ethernet Switches.
Step 3: Run the HyperTerminal program on the configuration PC. Start the switch. Then enter the Boot Menu.
At the prompt "Enter your choice(0-9):" in the Boot Menu, press <6> or <Ctrl+U>, and then press <Enter> to enter the BootROM update menu shown below:
Bootrom update menu:
1. Set TFTP protocol parameter
2. Set FTP protocol parameter
3. Set XMODEM protocol parameter
0. Return to boot menu
Enter your choice(0-3):
Step 4: Enter 1 to in the above menu to download the BootROM software using TFTP. Then set the following TFTP-related parameters as required:
Load File name :S5500.btm
Switch IP address :1.1.1.2
Server IP address :1.1.1.1
Step 5: Press <Enter>. The system displays the following information:
Are you sure you want to update your bootrom? Yes or No(Y/N)
Step 6: Enter Y to start file downloading or N to return to the Bootrom update menu. If you enter Y, the system begins to download and update the BootROM software. Upon completion, the system displays the following information:
Loading........................................done
Bootrom updating..........done!
2) Loading host software
Step 1: Select <1> in Boot Menu and press <Enter>. The system displays the following information:
1. Set TFTP protocol parameter
2. Set FTP protocol parameter
3. Set XMODEM protocol parameter
0. Return to boot menu
Enter your choice(0-3):
Step 2: Enter 1 in the above menu to download the host software using TFTP.
The subsequent steps are the same as those for loading the BootROM program, except that the system gives the prompt for host software loading instead of BootROM loading.
![]() Caution:
Caution:
When loading BootROM and host software using Boot menu, you are recommended to use the PC directly connected to the device as TFTP server to promote upgrading reliability.
IV. Loading Software Using FTP through Ethernet Port
FTP is an application-layer protocol in the TCP/IP protocol suite. It is used for file transfer between server and client, and is widely used in IP networks.
You can use the switch as an FTP client or a server, and download software to the switch through an Ethernet port. The following is an example.
1) Loading BootROM software

Figure 3-7 Local loading using FTP client
Step 1: As shown in Figure 3-7, connect the switch through an Ethernet port to the FTP server, and connect the switch through the Console port to the configuration PC.
& Note:
You can use one computer as both configuration device and FTP server.
Step 2: Run the FTP server program on the FTP server, configure an FTP user name and password, and copy the program file to the specified FTP directory.
Step 3: Run the HyperTerminal program on the configuration PC. Start the switch. Then enter the Boot Menu.
At the prompt "Enter your choice(0-9):" in the Boot Menu, press <6> or <Ctrl+U>, and then press <Enter> to enter the BootROM update menu shown below:
Bootrom update menu:
1. Set TFTP protocol parameter
2. Set FTP protocol parameter
3. Set XMODEM protocol parameter
0. Return to boot menu
Enter your choice(0-3):
Step 4: Enter 2 in the above menu to download the BootROM software using FTP. Then set the following FTP-related parameters as required:
Load File name :S5500.btm
Switch IP address :10.1.1.2
Server IP address :10.1.1.1
FTP User Name :switch
FTP User Password :hello
Step 5: Press <Enter>. The system displays the following information:
Are you sure you want to update your bootrom? Yes or No(Y/N)
Step 6: Enter Y to start file downloading or N to return to the Bootrom update menu. If you enter Y, the system begins to download and update the program. Upon completion, the system displays the following information:
Loading........................................done
Bootrom updating..........done!
2) Loading host software
Follow these steps to load the host software:
Step 1: Select <1> in Boot Menu and press <Enter>. The system displays the following information:
1. Set TFTP protocol parameter
2. Set FTP protocol parameter
3. Set XMODEM protocol parameter
0. Return to boot menu
Enter your choice(0-3):
Enter 2 in the above menu to download the host software using FTP.
The subsequent steps are the same as those for loading the BootROM program, except for that the system gives the prompt for host software loading instead of BootROM loading.
![]() Caution:
Caution:
When loading BootROM and host software using Boot menu, you are recommended to use the PC directly connected to the device as FTP server to promote upgrading reliability.
3.2.3 Remote Software Loading
If your terminal is not directly connected to the switch, you can telnet to the switch, and use FTP or TFTP to load BootROM and host software remotely.
I. Remote Loading Using FTP
1) Loading Process Using FTP Client
As shown in Figure 3-8, a PC is used as both the configuration device and the FTP server. You can telnet to the switch, and then execute the FTP commands to download the BootROM program s5500.btm from the remote FTP server (with an IP address 10.1.1.1) to the switch.

Figure 3-8 Remote loading using FTP
Step 1: Download the software to the switch using FTP commands.
<Sysname> ftp 10.1.1.1
Trying 10.1.1.1 ...
Press CTRL+K to abort
Connected to 10.1.1.1
220 WFTPD 2.0 service (by Texas Imperial Software) ready for new user
User(10.1.1.1:(none)):switch
331 Give me your password, please
Password:
230 Logged in successfully
[ftp] get s5500.btm
227 Entering Passive Mode (10,1,1,1,4,125)
150 "D:\s5500.btm" file ready to send (291284 bytes) in ASCII mode
....226 Transfer finished successfully.
FTP: 291284 byte(s) received in 4.393 second(s), 66.00K byte(s)/sec.
[ftp] bye
221 Windows FTP Server (WFTPD, by Texas Imperial Software) says goodbye.
<Sysname>
& Note:
When using different FTP server software on PC, different information will be output to the switch.
Step 2: Update the BootROM program on the switch.
<Sysname> bootrom update file s5500.btm
This command will update bootrom file, Continue? [Y/N]y
Now updating bootrom, please wait...
Step 3: Restart the switch.
<H3C> reboot
& Note:
Before restarting the switch, make sure you have saved all other configurations that you want, so as to avoid losing configuration information.
Loading the host software is the same as loading the BootROM program, except for that the file to be downloaded is the host software file, and that you need to use the boot-loader command to select the host software at reboot of the switch.
After the above operations, the BootROM and host software loading is completed.
Pay attention to the following:
l The loading of BootROM and host software takes effect only after you restart the switch with the reboot command.
l If the space of the Flash memory is not enough, you can delete the useless files in the Flash memory before software downloading.
l No power-down is permitted during software loading.
2) Loading Process Using FTP Server
As shown in Figure 3-9, the switch is used as the FTP server. You can telnet to the switch, and then execute the FTP commands to download the BootROM program s5500.btm from the switch.

Figure 3-9 Remote loading using FTP server
Step 1: As shown in Figure 3-9, connect the switch through an Ethernet port to the PC (with IP address 10.1.1.1)
Step 2: Configure the IP address of VLAN1 on the switch to 192.168.0.39, and subnet mask to 255.255.255.0.
& Note:
You can configure the IP address for any VLAN on the switch for FTP transmission. However, before configuring the IP address for a VLAN interface, you have to make sure whether the IP addresses of this VLAN and PC are routable.
<Sysname> system-view
[Sysname] interface Vlan-interface 1
[Sysname-Vlan-interface1] ip address 192.168.0.39 255.255.255.0
Step 3: Enable FTP service on the switch, configure the FTP user name to test and password to pass.
[Sysname-Vlan-interface1] quit
[Sysname] ftp server enable
% Start FTP server
[Sysname] local-user test
New local user added.
[Sysname-luser-test] password simple pass
[Sysname-luser-test] service-type ftp
Step 4: Enable FTP client software on PC. Refer to Figure 3-10 for the command line interface in Windows operating system.
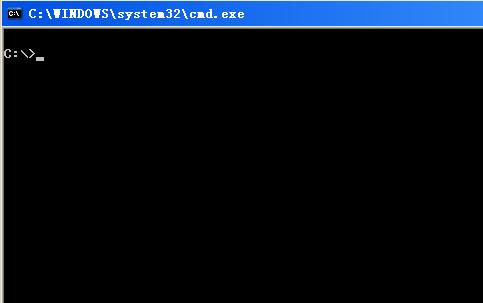
Figure 3-10 Command line interface
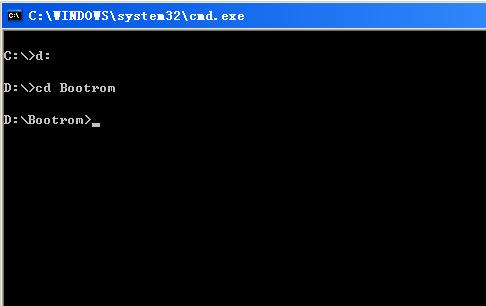
Step 5: Enter cd in the interface to switch to the path that the BootROM upgrade file is to be stored, and assume the name of the path is “D:\Bootrom”, as shown in Figure 3-11.
Step 6: Enter “ftp 192.168.0.39” and enter the user name test, password pass, as shown in Figure 3-12, to log on the FTP server.
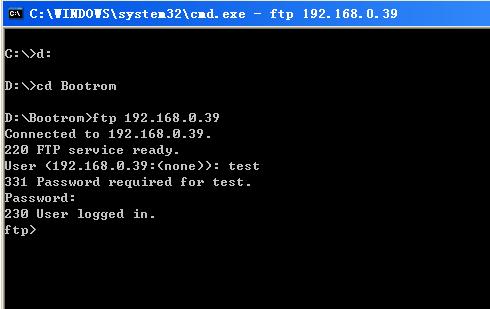
Figure 3-12 Log on the FTP server
Step 7: Use the put command to upload the file s5500.btm to the switch, as shown in Figure 3-13.
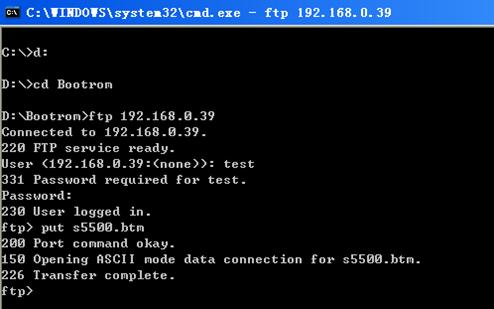
Figure 3-13 Upload file s5500.btm to the switch
Step 8: Configure s5500.btm to be the BootROM at reboot, and then restart the switch.
<Sysname> bootrom update file s5500.btm
This command will update bootrom file, Continue? [Y/N]y
Now updating bootrom, please wait...
<Sysname> reboot
When rebooting the switch, use the file s5500.btm as BootROM to finish BootROM loading.
Loading the host software is the same as loading the BootROM program, except for that the file to be downloaded is the host software file, and that you need to use the boot-loader command to select the host software at reboot of the switch.
& Note:
l The steps listed above are performed in the Windows operating system, if you use other FTP client software, refer to the corresponding user’s guide before operation.
l Only the configurations steps concerning loading are illustrated here, for detailed description on the corresponding configuration commands, refer to the chapter “File System Management”.
II. Remote Loading Using TFTP
The remote loading using TFTP is similar to that using FTP. The only difference is that TFTP is used instead of FTP to load software to the switch, and the switch can only act as a TFTP client.
3.3 Configuring Device Management
3.3.1 Rebooting a Device
When a fault occurs to a running device, you can remove the fault by rebooting the device, depending on the actual situation. You can set a time at which the device can automatically reboot. You can also set a delay so that the device can automatically reboot in the delay.
Table 3-1 Follow these steps to reboot a device
|
To do… |
Use the command… |
Remarks |
|
Reboot the whole system |
reboot |
Optional |
|
Enable the scheduled reboot function and specify a specific reboot time and date |
schedule reboot at hh:mm [ date ] |
Optional The scheduled reboot function is disabled by default. |
|
Enable the scheduled reboot function and specify a reboot wait time |
schedule reboot delay { hh:mm | mm } |
|
|
Display the reboot time of a device |
display schedule reboot |
Optional You can execute the command in any view. |
![]() Caution:
Caution:
l The precision of the device timer is 1 minute. One minute before the reboot time, the device will prompt “REBOOT IN ONE MINUTE” and will reboot in one minute.
l The execution of the reboot, schedule reboot at, and schedule reboot delay commands can reboot a device. As a result, the ongoing services will be interrupted. You must be careful to use these commands.
3.3.2 Specifying a BootROM File for the Next Device Boot
A BootROM file is an application file adopted by the device. When multiple BootROM files are available on the storage media, you can specify a file for the next device boot by executing the following command.
Table 3-2 Follow these steps to specify an APP file for the next device boot
|
To do… |
Use the command… |
Remarks |
|
Specify the BootROM file used for the next boot |
boot-loader file file-url { backup | main } |
Required |
3.3.3 Upgrading a BootROM File
During the operation of the device, you can use the BootROM files in the storage media to upgrade those that are running on the device.
Since the BootROM files of switching and routing processing units (SRPUs) and line processing units (LPUs) vary with devices, users are easily confused to make serious mistakes when upgrading BootROM files. After the validity check function is enabled, the device will strictly check the BootROM upgrade files for correctness and version configuration information to ensure a successful upgrade. You are recommended to enable the validity check function before upgrading BootROM files.
Table 3-3 Follow these steps to upgrade a BootROM file
|
To do… |
Use the command… |
Remarks |
|
Enter system view |
system-view |
— |
|
Enable the validity check function when upgrading a BootROM file |
bootrom-update security-check enable |
Optional By default, the validity check function is disabled at the time of upgrading a BootROM file. |
|
Return to user view |
quit |
— |
|
Upgrade the BootROM file |
bootrom update file file-url |
Required All contents of the BootROM file are operated by default. |
& Note:
Restart the device to validate the upgraded BootROM files.
3.3.4 Clearing the 16bit Interface Indexes Not Used in the Current System
In practical networks, the network management software requires the device to provide a uniform, stable 16bit interface index. That is, a one-to-one relationship should be kept between the interface name and the interface index in the same device.
For the purpose of the stability of an interface index, the system will save the 16bit interface index when a card or logical interface is removed.
If you repeatedly insert and remove different subcards or interface cards to create or delete a large amount of logical interface, the interface indexes will be used up, which will result in interface creation failures. To avoid such a case, you can clear all 16bit interface indexes saved but not used in the current system in user view.
After the above operation,
l for a re-created interface, the new interface index may not be consistent with the original one.
l for existing interfaces, their interface indexes remain unchanged.
Table 3-4 Follow the step below to clear the 16bit interface indexes not used in the current system
|
To do… |
Use the command… |
|
Clear the 16bit interface indexes saved but not used in the current system |
reset unused porttag |
![]() Caution:
Caution:
3.4 Displaying and Maintaining Device Management Configuration
Table 3-5 Displaying and Maintaining device management configuration
|
To do… |
Use the command… |
|
Display the BootROM file used for the next boot |
display boot-loader |
|
Display the statistics of the CPU usage |
display cpu-usage [ number [ offset ] [ verbose ] [ from-device ] ] |
|
Display the information about the boards and cards on the device |
display device [ manuinfo | subslot subslot-number | verbose ] |
|
Display the temperature information of devices |
display environment |
|
Display the operating state of fans in a device |
display fan [ fan-id ] |
|
Display the usage of the memory of a device |
display memory |
|
Display the power state of a device |
display power [ power-id ] |
|
Display the reboot time of a device |
display schedule reboot |
3.5 Device Management Configuration Example
3.5.1 Remote Upgrade Configuration Example
I. Network requirements
l Device serves as the FTP client and the remote PC as the FTP server. The switch.bin program and the boot.btm program are both saved under the switch directory of the FTP server.
l The IP address of a VLAN interface on the device is 1.1.1.1/24, the IP address of the FTP server is 2.2.2.2/24, and the route between the device and the FTP server is reachable.
l You can log in to the FTP server via Telnet to download the application program and remotely upgrade the device through command lines.
II. Network diagram

Figure 3-14 Network diagram for remote upgrade
III. Configuration procedure
l Configuration on the FTP server
# Set the FTP username to switch and password to hello.
# Configure the user to have access to the switch directory.
l Configuration on Device
![]() Caution:
Caution:
If the size of the Flash on the device is not large enough, delete the original application programs from the Flash before downloading.
# Enter the following command in user view to log in to the FTP server.
<Sysname> ftp 2.2.2.2
Trying 2.2.2.2 ...
Press CTRL+K to abort
Connected to 2.2.2.2
220 WFTPD 2.0 service (by Texas Imperial Software) ready for new user
User(2.2.2.2:(none)):switch
331 Give me your password, please
Password:
230 Logged in successfully
[ftp]
# Enter the authorization directory of the FTP server.
[ftp] cd switch
# Download the switch.bin and boot.btm programs to the Flash of the device.
[ftp] get switch.bin
[ftp] get boot.btm
# Clear the FTP connection and return to user view.
[ftp] quit
<Sysname>
# Enter system view.
<Sysname> system-view
# Enable the validity check function for BootROM file upgrade.
[Sysname] bootrom-update security-check enable
[Sysname] quit
# Upgrade the BootROM file of the SRPU.
<Sysname> bootrom update file boot.btm
# Specify the application program for the next boot on SRPU 0.
<Sysname> boot-loader file switch.bin main
# Reboot the device. The application program is upgraded now.
<Sysname> reboot
