- Table of Contents
-
- H3C Campus Fixed-Port Switches CLI-Based Quick Start Configuration Guide-6W101
- 01-H3C Devices CLI Reference
- 02-Login Management Quick Start Configuration Guide
- 03-Configuration File Management Quick Start Configruation Guide
- 04-Software Upgrade Quick Start Configuration Guide
- 05-Device Management Quick Start Configuration Guide
- 06-NTP Quick Start Configuration Guide
- 07-RBAC Quick Start Configuration Guide
- 08-IRF Quick Start Configuration Guide
- 09-Ethernet Interface Quick Start Configuration Guide
- 10-VLAN Quick Start Configuration Guide
- 11-Port Isolation Quick Start Configuration Guide
- 12-Loop Detection Quick Start Configuration Guide
- 13-QinQ Quick Start Configuration Guide
- 14-MAC Address Table Quick Start Configuration Guide
- 15-Ethernet Link Aggregation Quick Start Configuration Guide
- 16-Spanning Tree Quick Start Configuration Guide
- 17-DHCP Quick Start Configuration Guide
- 18-OSPF Quick Start Configuration Guide
- 19-Static Routing Quick Start Configuration Guide
- 20-Basic RIP Quick Start Configuration Guide
- 21-PBR Quick Start Configuration Guide
- 22-IGMP Snooping Quick Start Configuration Guide
- 23-Packet Filtering Quick Start Configuration Guide
- 24-QoS Quick Start Configuration Guide
- 25-IP Source Guard Quick Start Configuration Guide
- 26-SSH Quick Start Configuration Guide
- 27-Port Security Quick Start Configuration Guide
- 28-VRRP Quick Start Configuration Guide
- 29-PoE Quick Start Configuration Guide
- 30-Mirroring Quick Start Configuration Guide
- 31-Information Center Quick Start Configuration Guide
- 32-SNMP Quick Start Configuration Guide
- 33-LAN Networks Quick Start Configuration Guide
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 23-Packet Filtering Quick Start Configuration Guide | 58.84 KB |
Packet Filtering Quick Start Configuration Guide
Copyright © 2022 New H3C Technologies Co., Ltd. All rights reserved.
No part of this manual may be reproduced or transmitted in any form or by any means without prior written consent of New H3C Technologies Co., Ltd.
Except for the trademarks of New H3C Technologies Co., Ltd., any trademarks that may be mentioned in this document are the property of their respective owners.
The information in this document is subject to change without notice.
Contents
Configuring packet filtering
Introduction
The following information uses an example to describe the basic procedure for configuring packet filtering.
Network configuration
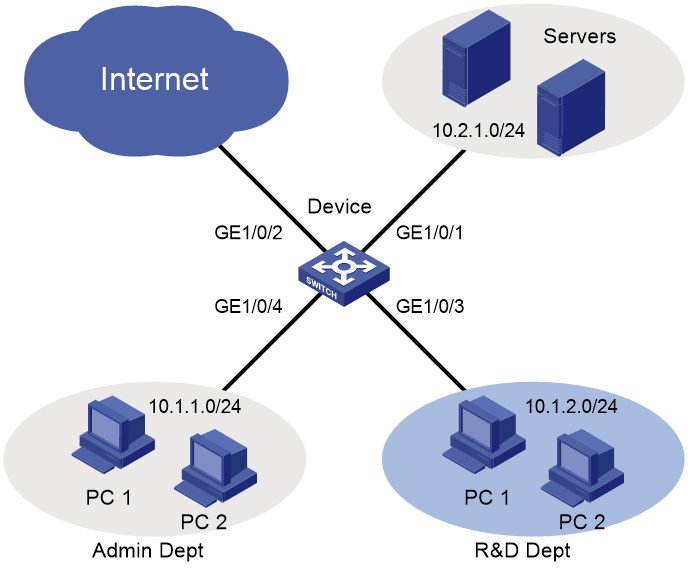
As shown in Figure 1, a company interconnects its departments through the device. Configure packet filtering to:
· Permit access from the Admin Dept at any time to the Internet and servers and deny access from the Admin Dept to the R&D Dept.
· Permit access from the R&D Dept to the servers and deny access from the R&D Dept to the Internet and the Admin Dept.
Procedure
1. Configure access to the Admin Dept.
# Create an IPv4 advanced ACL numbered 3000.
<Device> system-view
[Device] acl advanced 3000
# Configure a rule to deny packets from the R&D Dept.
[Device-acl-ipv4-adv-3000] rule deny ip destination 10.1.2.0 0.0.0.255
[Device-acl-ipv4-adv-3000] quit
# Apply IPv4 advanced ACL 3000 to filter incoming packets on GigabitEthernet 1/0/4.
[Device] interface gigabitethernet 1/0/4
[Device-GigabitEthernet1/0/4] packet-filter 3000 inbound
[Device-GigabitEthernet1/0/4] quit
2. Configure access to the R&D Dept.
# Create an IPv4 advanced ACL numbered 3001.
[Device] acl advanced 3001
# Configure a rule to permit packets from the Admin Dept.
[Device-acl-ipv4-adv-3001] rule permit ip destination 10.2.1.0 0.0.0.255
# Configure a rule to deny all other packets.
[Device-acl-ipv4-adv-3001] rule deny ip
# Apply IPv4 advanced ACL 3001 to filter incoming packets on GigabitEthernet 1/0/3.
[Device] interface gigabitethernet 1/0/3
[Device-GigabitEthernet1/0/3] packet-filter 3001 inbound
[Device-GigabitEthernet1/0/3] quit
Verify the configuration
# Display ACL application information for inbound packet filtering.
[Device] display packet-filter interface inbound
Interface: GigabitEthernet1/0/3
Inbound policy:
IPv4 ACL 3001
Interface: GigabitEthernet1/0/4
Inbound policy:
IPv4 ACL 3000
The output shows that GigabitEthernet 1/0/3 and GigabitEthernet 1/0/4 are successfully applied with ACLs for packet filtering.
# Verify that a website on the Internet cannot be pinged from a PC in the R&D Dept.
C:\>ping www.google.com
Pinging www.google.com [172.217.194.99] with 32 bytes of data:
Request timed out.
Request timed out.
Request timed out.
Request timed out.
Ping statistics for 173.194.127.242:
Packets: Sent = 4, Received = 0, Lost = 4 (100% loss),
C:\>
# Verify that a server can be pinged from a PC in the R&D Dept.
C:\>ping 10.2.1.10
Ping 192.168.1.60 (10.2.1.10): 56 data bytes, press CTRL+C to break
56 bytes from 10.2.1.10: icmp_seq=0 ttl=255 time=12.963 ms
56 bytes from 10.2.1.10: icmp_seq=1 ttl=255 time=4.168 ms
56 bytes from 10.2.1.10: icmp_seq=2 ttl=255 time=7.390 ms
56 bytes from 10.2.1.10: icmp_seq=3 ttl=255 time=3.363 ms
56 bytes from 10.2.1.10: icmp_seq=4 ttl=255 time=2.901 ms
C:\>
# Verify that a website on the Internet can be pinged from a PC in the Admin Dept.
C:\>ping www.google.com
Pinging www.google.com [172.217.194.99] with 32 bytes of data:
Reply from 172.217.194.99: bytes=32 time=30ms TTL=50
Reply from 172.217.194.99: bytes=32 time=30ms TTL=50
Reply from 172.217.194.99: bytes=32 time=30ms TTL=50
Reply from 172.217.194.99: bytes=32 time=30ms TTL=50
Ping statistics for 172.217.194.99:
Packets: Sent = 4, Received = 4, Lost = 0 (0% loss),
Approximate round trip times in milli-seconds:
Minimum = 30ms, Maximum = 30ms, Average = 30ms
C:\>
Configuration files
#
interface Ten-GigabitEthernet1/0/3
port link-mode bridge
packet-filter 3001 inbound
#
interface Ten-GigabitEthernet1/0/4
port link-mode bridge
packet-filter 3000 inbound
#
acl advanced 3000
rule 0 deny ip destination 10.1.2.0 0.0.0.255
#
acl advanced 3001
rule 0 permit ip destination 10.2.1.0 0.0.0.255
rule 5 deny ip
#
Related documentation
· ACL configuration in the ACL and QoS configuration guide for the device.
· ACL commands in the ACL and QoS command reference for the device.