- Table of Contents
-
- 09-Security Configuration Guide
- 00-Preface
- 01-AAA configuration
- 02-802.1X configuration
- 03-MAC authentication configuration
- 04-Portal configuration
- 05-Web authentication configuration
- 06-Triple authentication configuration
- 07-Port security configuration
- 08-User profile configuration
- 09-Password control configuration
- 10-Keychain configuration
- 11-Public key management
- 12-PKI configuration
- 13-IPsec configuration
- 14-SSH configuration
- 15-SSL configuration
- 16-TCP attack prevention configuration
- 17-Attack detection and prevention configuration
- 18-IP source guard configuration
- 19-ARP attack protection configuration
- 20-ND attack defense configuration
- 21-uRPF configuration
- 22-SAVI configuration
- 23-MFF configuration
- 24-Crypto engine configuration
- 25-FIPS configuration
- 26-MACsec configuration
- 27-802.1X client configuration
- 28-SAVA configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 15-SSL configuration | 82.22 KB |
Contents
Restrictions and guidelines: SSL configuration
Configuring an SSL server policy
Configuring an SSL client policy
Disabling SSL protocol versions for the SSL server
Disabling SSL session renegotiation
Display and maintenance commands for SSL
Configuring SSL
About SSL
Secure Sockets Layer (SSL) is a cryptographic protocol that provides communication security for TCP-based application layer protocols such as HTTP. SSL has been widely used in applications such as e-business and online banking to provide secure data transmission over the Internet.
SSL security services
SSL provides the following security services:
· Privacy—SSL uses a symmetric encryption algorithm to encrypt data. It uses the asymmetric key algorithm of RSA to encrypt the key used by the symmetric encryption algorithm. For more information about RSA, see "Managing public keys."
· Authentication—SSL uses certificate-based digital signatures to authenticate the SSL server and client. The SSL server and client obtain digital certificates through PKI. For more information about PKI and digital certificates, see "Configuring PKI."
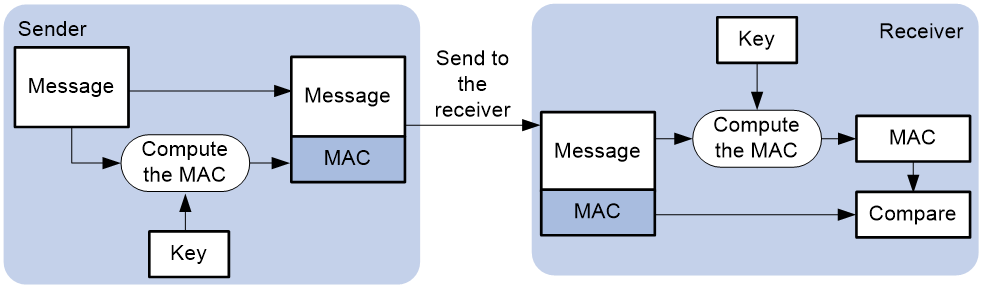
· Integrity—SSL uses the message authentication code (MAC) to verify message integrity. It uses a MAC algorithm and a key to transform a message of any length to a fixed-length message. Any change to the original message will result in a change to the calculated fixed-length message. As shown in Figure 1, the message integrity verification process is as follows:
a. The sender uses a MAC algorithm and a key to calculate a MAC value for a message. Then, it appends the MAC value to the message and sends the message to the receiver.
b. The receiver uses the same key and MAC algorithm to calculate a MAC value for the received message, and compares it with the MAC value appended to the message.
c. If the two MAC values match, the receiver considers the message intact. Otherwise, the receiver considers that the message was tampered with and it discards the message.
Figure 1 MAC algorithm diagram
SSL protocol stack
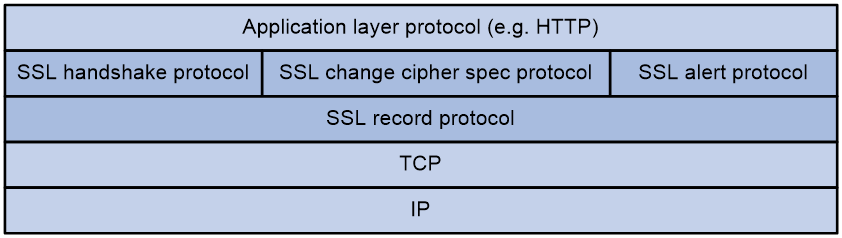
The SSL protocol stack includes the following protocols:
· SSL record protocol at the lower layer.
· SSL handshake protocol, SSL change cipher spec protocol, and SSL alert protocol at the upper layer.
The following describes the major functions of SSL protocols:
· SSL record protocol—Fragments data received from the upper layer, computes and adds MAC to the data, and encrypts the data.
· SSL handshake protocol—Negotiates the cipher suite used for secure communication, authenticates the server and client, and securely exchanges the keys between the server and client. The cipher suite that needs to be negotiated includes the symmetric encryption algorithm, key exchange algorithm, and MAC algorithm.
· SSL change cipher spec protocol—Notifies the receiver that subsequent packets are to be protected based on the negotiated cipher suite and key.
· SSL alert protocol—Sends alert messages to the receiving party. An alert message contains the alert severity level and a description.
SSL protocol versions
SSL protocol versions include SSL 2.0, SSL 3.0, TLS 1.0 (or SSL 3.1), TLS 1.1, and TLS 1.2. Because SSL 3.0 is known to be insecure, you can disable SSL 3.0 for the SSL server to ensure security.
FIPS compliance
The device supports the FIPS mode that complies with NIST FIPS 140-2 requirements. Support for features, commands, and parameters might differ in FIPS mode (see "Configuring FIPS") and non-FIPS mode.
Restrictions and guidelines: SSL configuration
By default, the SSL server can communicate with clients running all SSL protocol versions. When the server receives an SSL 2.0 Client Hello message from a client, it notifies the client to use a later version for communication.
SSL tasks at a glance
Configuring the SSL server
· Configuring an SSL server policy
· (Optional.) Disabling SSL protocol versions for the SSL server
· (Optional.) Disabling SSL session renegotiation
Configuring the SSL client
Configuring an SSL client policy
Configuring an SSL server policy
About this task
An SSL server policy is a set of SSL parameters used by the device when the device acts as the SSL server. An SSL server policy takes effect only after it is associated with an application such as HTTPS.
Procedure
1. Enter system view.
system-view
2. Create an SSL server policy and enter its view.
ssl server-policy policy-name
3. Specify a PKI domain for the SSL server policy.
pki-domain domain-name
By default, no PKI domain is specified for an SSL server policy.
If SSL server authentication is required, you must specify a PKI domain and request a local certificate for the SSL server in the domain.
For information about configuring a PKI domain, see "Configuring PKI."
4. Specify the cipher suites that the SSL server policy supports.
In non-FIPS mode:
ciphersuite { dhe_rsa_aes_128_cbc_sha | dhe_rsa_aes_128_cbc_sha256 | dhe_rsa_aes_256_cbc_sha | dhe_rsa_aes_256_cbc_sha256 | ecdhe_ecdsa_aes_128_cbc_sha256 | ecdhe_ecdsa_aes_128_gcm_sha256 | ecdhe_ecdsa_aes_256_cbc_sha384 | ecdhe_ecdsa_aes_256_gcm_sha384 | ecdhe_rsa_aes_128_cbc_sha256 | ecdhe_rsa_aes_128_gcm_sha256 | ecdhe_rsa_aes_256_cbc_sha384 | ecdhe_rsa_aes_256_gcm_sha384 | exp_rsa_des_cbc_sha | exp_rsa_rc2_md5 | exp_rsa_rc4_md5 | rsa_3des_ede_cbc_sha | rsa_aes_128_cbc_sha | rsa_aes_128_cbc_sha256 | rsa_aes_256_cbc_sha | rsa_aes_256_cbc_sha256 | rsa_des_cbc_sha | rsa_rc4_128_md5 | rsa_rc4_128_sha } *
In FIPS mode:
ciphersuite { ecdhe_ecdsa_aes_128_cbc_sha256 | ecdhe_ecdsa_aes_256_cbc_sha384 | ecdhe_ecdsa_aes_128_gcm_sha256 | ecdhe_ecdsa_aes_256_gcm_sha384 | ecdhe_rsa_aes_128_cbc_sha256 | ecdhe_rsa_aes_128_gcm_sha256 | ecdhe_rsa_aes_256_cbc_sha384 | ecdhe_rsa_aes_256_gcm_sha384 | rsa_aes_128_cbc_sha | rsa_aes_128_cbc_sha256 | rsa_aes_256_cbc_sha | rsa_aes_256_cbc_sha256 } *
By default, an SSL server policy supports all cipher suites.
5. (Optional.) Set the maximum number of sessions that the SSL server can cache and the session cache timeout time.
session { cachesize size | timeout time } *
By default, the SSL server can cache a maximum of 500 sessions, and the session cache timeout time is 3600 seconds.
6. Enable mandatory or optional SSL client authentication.
client-verify { enable | optional }
By default, SSL client authentication is disabled. The SSL server does not perform digital certificate-based authentication on SSL clients.
When authenticating a client by using the digital certificate, the SSL server verifies the certificate chain presented by the client. It also verifies that the certificates in the certificate chain (except the root CA certificate) are not revoked.
7. (Optional.) Enable the SSL server to send the complete certificate chain to the client during SSL negotiation.
certificate-chain-sending enable
By default, the SSL server sends the server certificate rather than the complete certificate chain to the client during negotiation.
Configuring an SSL client policy
About this task
An SSL client policy is a set of SSL parameters used by the device when the device acts as the SSL client. The SSL client uses the settings in the client policy to establish a connection to the server. An SSL client policy takes effect only after it is associated with an application such as DDNS. For information about DDNS, see the DNS configuration in Layer 3—IP Services Configuration Guide.
Restrictions and guidelines
As a best practice to enhance system security, do not specify SSL 3.0 for the SSL client policy.
Procedure
1. Enter system view.
system-view
2. Create an SSL client policy and enter its view.
ssl client-policy policy-name
3. Specify a PKI domain for the SSL client policy.
pki-domain domain-name
By default, no PKI domain is specified for an SSL client policy.
If SSL client authentication is required, you must specify a PKI domain and request a local certificate for the SSL client in the PKI domain.
For information about configuring a PKI domain, see "Configuring PKI."
4. Specify the preferred cipher suite for the SSL client policy.
In non-FIPS mode:
prefer-cipher { dhe_rsa_aes_128_cbc_sha | dhe_rsa_aes_128_cbc_sha256 | dhe_rsa_aes_256_cbc_sha | dhe_rsa_aes_256_cbc_sha256 | ecdhe_ecdsa_aes_128_cbc_sha256 | ecdhe_ecdsa_aes_128_gcm_sha256 | ecdhe_ecdsa_aes_256_cbc_sha384 | ecdhe_ecdsa_aes_256_gcm_sha384 | ecdhe_rsa_aes_128_cbc_sha256 | ecdhe_rsa_aes_128_gcm_sha256 | ecdhe_rsa_aes_256_cbc_sha384 | ecdhe_rsa_aes_256_gcm_sha384 | exp_rsa_des_cbc_sha | exp_rsa_rc2_md5 | exp_rsa_rc4_md5 | rsa_3des_ede_cbc_sha | rsa_aes_128_cbc_sha | rsa_aes_128_cbc_sha256 | rsa_aes_256_cbc_sha | rsa_aes_256_cbc_sha256 | rsa_des_cbc_sha | rsa_rc4_128_md5 | rsa_rc4_128_sha }
The default preferred cipher suite in non-FIPS mode is rsa_rc4_128_md5.
In FIPS mode:
prefer-cipher { ecdhe_ecdsa_aes_128_cbc_sha256 | ecdhe_ecdsa_aes_128_gcm_sha256 | ecdhe_ecdsa_aes_256_cbc_sha384 | ecdhe_ecdsa_aes_256_gcm_sha384 | ecdhe_rsa_aes_128_cbc_sha256 | ecdhe_rsa_aes_128_gcm_sha256 | ecdhe_rsa_aes_256_cbc_sha384 | ecdhe_rsa_aes_256_gcm_sha384 | rsa_aes_128_cbc_sha | rsa_aes_128_cbc_sha256 | rsa_aes_256_cbc_sha | rsa_aes_256_cbc_sha256 }
The default preferred cipher suite in FIPS mode is rsa_aes_128_cbc_sha.
5. Specify the SSL protocol version for the SSL client policy.
In non-FIPS mode:
version { ssl3.0 | tls1.0 | tls1.1 | tls1.2 }
In FIPS mode:
version { tls1.0 | tls1.1 | tls1.2 }
By default, an SSL client policy uses TLS 1.0.
6. Enable the SSL client to authenticate servers through digital certificates.
server-verify enable
By default, SSL server authentication is enabled.
Disabling SSL protocol versions for the SSL server
About this task
To enhance system security, you can disable the SSL server from using specific SSL protocol versions (SSL 3.0, TLS 1.0, and TLS 1.1) for session negotiation.
Restrictions and guidelines
Disabling an SSL protocol version does not affect the availability of earlier SSL protocol versions. For example, if you execute the ssl version tls1.1 disable command, TLS 1.1 is disabled but TLS 1.0 is still available for the SSL server.
Procedure
1. Enter system view.
system-view
2. Disable SSL protocol versions for the SSL server.
In non-FIPS mode:
ssl version { ssl3.0 | tls1.0 | tls1.1 } * disable
By default, the SSL server supports SSL 3.0, TLS 1.0, TLS 1.1, and TLS 1.2.
In FIPS mode:
ssl version { tls1.0 | tls1.1 } * disable
By default, the SSL server supports TLS 1.0, TLS 1.1, and TLS 1.2.
Disabling SSL session renegotiation
About this task
The SSL session renegotiation feature enables the SSL client and server to reuse a previously negotiated SSL session for an abbreviated handshake.
Disabling session renegotiation causes more computational overhead to the system but it can avoid potential risks.
Restrictions and guidelines
Disable SSL session renegotiation only when explicitly required.
Procedure
1. Enter system view.
system-view
2. Disable SSL session renegotiation.
ssl renegotiation disable
By default, SSL session renegotiation is enabled.
Display and maintenance commands for SSL
Execute display commands in any view.
|
Task |
Command |
|
Display SSL client policy information. |
display ssl client-policy [ policy-name ] |
|
Display SSL server policy information. |
display ssl server-policy [ policy-name ] |