- Table of Contents
-
- 09-Security Configuration Guide
- 00-Preface
- 01-AAA configuration
- 02-802.1X configuration
- 03-MAC authentication configuration
- 04-Portal configuration
- 05-Web authentication configuration
- 06-Triple authentication configuration
- 07-Port security configuration
- 08-User profile configuration
- 09-Password control configuration
- 10-Keychain configuration
- 11-Public key management
- 12-PKI configuration
- 13-IPsec configuration
- 14-SSH configuration
- 15-SSL configuration
- 16-TCP attack prevention configuration
- 17-Attack detection and prevention configuration
- 18-IP source guard configuration
- 19-ARP attack protection configuration
- 20-ND attack defense configuration
- 21-uRPF configuration
- 22-SAVI configuration
- 23-MFF configuration
- 24-Crypto engine configuration
- 25-FIPS configuration
- 26-MACsec configuration
- 27-802.1X client configuration
- 28-SAVA configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 05-Web authentication configuration | 158.46 KB |
Contents
Configuring Web authentication
Advantages of Web authentication
Web authentication support for VLAN assignment
Web authentication support for authorization ACLs
Restrictions and guidelines: Web authentication configuration
Web authentication task at a glance
Prerequisites for Web authentication
Configuring a Web authentication server
Configuring a local portal service
Specifying a Web authentication domain
Setting the redirection wait time
Configuring a Web authentication-free subnet
Setting the maximum number of Web authentication users
Configuring online Web authentication user detection
Configuring Web authentication to support Web proxy
Display and maintenance commands for Web authentication
Web authentication configuration examples
Example: Configuring Web authentication by using the local authentication method
Example: Configuring Web authentication by using the RADIUS authentication method
Troubleshooting Web authentication
Failure to come online (local authentication interface using the default ISP domain
Configuring Web authentication
About Web authentication
Web authentication is deployed on Layer 2 Ethernet interfaces of the access device to control user access to networks. The access device redirects unauthenticated users to the specified website. The users can access the resources on the website without authentication. If the users want to access other network resources, they must pass authentication.
Advantages of Web authentication
Web authentication has the following advantages:
· Allows users to perform authentication through webpages without installing client software.
· Provides ISPs with diversified management choices and extended functions. For example, the ISPs can place advertisements, provide community services, and publish information on the authentication page.
Web authentication system
A typical Web authentication system consists of four basic components: authentication client, access device, local portal Web server, and AAA server.
Figure 1 Web authentication system using the local portal server
Authentication client
An authentication client is a Web browser that runs HTTP or HTTPS.
Access device
An access device has the following functions:
· Redirects all user HTTP or HTTPS requests that do not match authentication-free rules to the Web authentication page before authentication.
· Interacts with the AAA server to complete authentication, authorization, and accounting. For more information about AAA, see "Configuring AAA."
· Allows users that pass authentication to access authorized network resources.
Local portal Web server
The access device acts as the local portal Web server. The local portal Web server pushes the Web authentication page to authentication clients and obtains user authentication information (username and password).
AAA server
An AAA server interacts with the access device to implement user authentication, authorization, and accounting. A RADIUS server can perform authentication, authorization, and accounting for Web authentication users. An LDAP server can perform authentication for Web authentication users.
Web authentication process
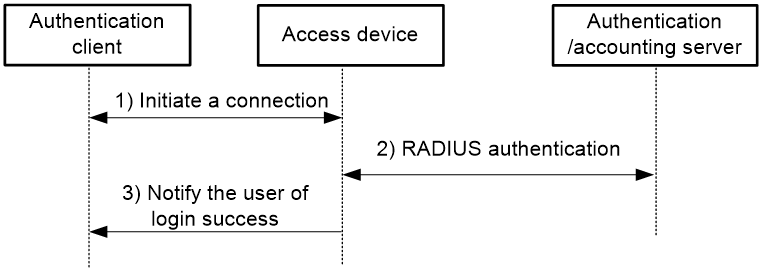
Figure 2 Web authentication process
The Web authentication process is as follows:
1. An unauthenticated user sends an HTTP or HTTPS request. When the access device receives the HTTP or HTTPS request on a Layer 2 Ethernet interface enabled with Web authentication, it redirects the request to the Web authentication page. The user enters the username and password on the Web authentication page.
If the user requests the Web authentication page or free Web resources, the access device permits the request. No Web authentication is performed.
2. The access device and the AAA server exchange RADIUS packets to authenticate the user.
3. If the user passes RADIUS authentication, the local portal Web server pushes a login success page to the authentication client.
If the user fails RADIUS authentication, the local portal Web server pushes a login failure page to the authentication client.
Web authentication support for VLAN assignment
Authorization VLAN
Web authentication uses VLANs authorized by the AAA server or the access device to control network resource access of authenticated users.
After a user passes Web authentication, the AAA server or the access device authorizes the user to access a VLAN. If the authorization VLAN does not exist, the access device first creates the VLAN and then assigns the user access interface as an untagged member to the VLAN. If the authorization VLAN already exists, the access device directly assigns the user access interface as an untagged member to the VLAN. Then, the user can access resources in the authorization VLAN.
Table 1 describes the way the access device handles authorization VLANs for Web authenticated users.
|
Port type |
VLAN manipulation |
|
· Access port · Trunk port · Hybrid port with MAC-based-VLAN disabled |
The device assigns the port to the first authenticated user's authorization VLAN. The authorization VLAN becomes the PVID. All Web authentication users on the port must be assigned the same authorization VLAN. If a different authorization VLAN is assigned to a subsequent user, the user cannot pass Web authentication. |
|
Hybrid port with MAC-based VLAN enabled |
The device maps the MAC address of each user to its own authorization VLAN regardless of whether the port is a tagged member. The PVID of the port does not change. |
Auth-Fail VLAN
An Auth-Fail VLAN is a VLAN assigned to users who fail authentication. The Auth-Fail VLAN provides network resources such as the patch server, virus definitions server, client software server, and anti-virus software server to the users. The users can use these resources to upgrade their client software or other programs.
Web authentication supports Auth-Fail VLAN on an interface that performs MAC-based access control. If a user on the interface fails authentication, the access devices creates a MAC VLAN entry based on the MAC address of the user and adds the user to the Auth-Fail VLAN. Then, the user can access the portal-free IP resources in the Auth-Fail VLAN. All HTTP or HTTPS requests to non-portal-free IP resources will be redirected to the authentication page. If the user still fails authentication, the interface remains in the Auth-Fail VLAN. If the user passes authentication, the access device removes the interface from the Auth-Fail VLAN and assigns the interface to a VLAN as follows:
· If the authentication server assigns an authorization VLAN to the user, the access device assigns the interface to the authorization VLAN.
· If the authentication server does not assign an authorization VLAN to the user, the access device assigns the interface to the default VLAN.
Web authentication support for authorization ACLs
Web authentication uses ACLs authorized by the AAA server or the access device to control user access to network resources and limit user access rights. When a user passes authentication, the AAA server and the access device assigns an authorization ACL to the access interface of the user. The access device filters traffic from the user on the access interface according to the authorized ACL.
You must configure the authorization ACLs on the access device if you specify authorization ACLs on the authentication server.
To change the access control criteria for the user, you can specify a different authorization ACL on the authentication server or change rules in the authorization ACL on the access device.
The device supports the following types of authorization ACLs:
· Basic ACLs (ACL 2000 to ACL 2999).
· Advanced ACLs (ACL 3000 to ACL 3999).
For an authorization ACL to take effect, make sure the ACL exists and has ACL rules excluding rules configured with the counting, established, fragment, or logging keyword. For more information about ACL rules, see ACL commands in ACL and QoS Command Reference.
Restrictions and guidelines: Web authentication configuration
To access the resources in the authorization or Auth-Fail VLAN, a user must update the IP address of the client after being assigned to the authorization or Auth-Fail VLAN.
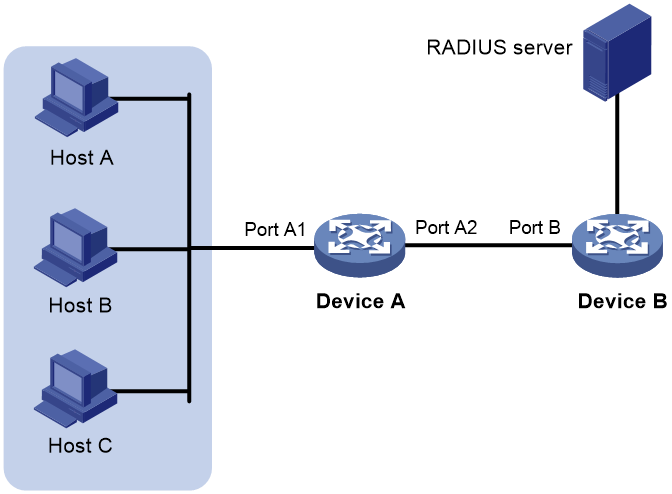
As a best practice, perform Web authentication on users directly connected to the device. As shown in Figure 3, if you enable Web authentication on Port B to authenticate non-directly connected users (the hosts), you must follow these restrictions and guidelines:
· If the RADIUS server assigns an authorization VLAN to the users, make sure the following conditions are met:
¡ The link between Device A and Device B is a trunk link.
¡ The PVIDs of Port A1 and Port B are the same as the authorization VLAN ID.
· If the RADIUS server does not assign an authorization VLAN to the users, make sure the PVIDs of Port A1 and Port B are the same.
Figure 3 Web authentication for non-directly connected users
Web authentication task at a glance
To configure Web authentication, perform the following tasks:
1. Configuring a Web authentication server
2. Configuring a local portal service
3. Enabling Web authentication
4. (Optional.) Specifying a Web authentication domain
5. (Optional.) Setting the redirection wait time
6. (Optional.) Configuring a Web authentication-free subnet
7. (Optional.) Setting the maximum number of Web authentication users
8. (Optional.) Configuring online Web authentication user detection
9. (Optional.) Configuring an Auth-Fail VLAN
10. (Optional.) Configuring Web authentication to support Web proxy
Prerequisites for Web authentication
The device supports two methods for Web authentication, which are local authentication and RADIUS authentication.
To use the RADIUS authentication method, you must complete the following tasks:
· Install a RADIUS server and configure the RADIUS server properly.
· Make sure the authentication client, the access device, and the RADIUS server can reach each other.
· Configure user accounts on the RADIUS server and configure the RADIUS client information on the access device.
To use the local authentication method, you must configure local users on the access device.
For more information about RADIUS clients and local users, see "Configuring AAA."
Configuring a Web authentication server
Restrictions and guidelines
Specify the IP address of a Layer 3 interface on the device that is routable to the Web client as the listening IP address of the Web authentication server. As a best practice, use the IP address of a loopback interface rather than that of a Layer 3 interface. A loopback interface has the following advantages:
· The status of a loopback interface is stable. There will be no authentication page access failures caused by interface failures.
· A loopback interface does not forward received packets to any networks, avoiding impact on system performances when there are many network access requests.
Procedure
1. Enter system view.
system-view
2. Create a Web authentication server and enter its view.
web-auth server server-name
3. Specify the IP address and port number of the Web authentication server.
ip ipv4-address port port-number
The port number of the Web authentication server must be the same as the listening port of the local portal Web service.
4. Specify the redirection URL for the Web authentication server.
url url-string
The IP address and port number in the specified redirection URL must be the same as those of the Web authentication server.
5. (Optional.) Add parameters to the redirection URL of the Web authentication server.
url-parameter parameter-name { original-url | source-address | source-mac | value expression }
By default, no parameters are added to the redirection URL of a Web authentication server.
Configuring a local portal service
For information about the local portal service configuration, see "Configuring portal authentication."
Enabling Web authentication
Restrictions and guidelines
For Web authentication to operate correctly, do not enable port security or configure the port security mode on the Layer 2 Ethernet interface enabled with Web authentication. For more information about port security, see "Configuring port security."
The default HTTPS redirect listening port number on the device is 6654. To change the HTTPS redirect listening port number, see HTTP redirect configuration in Layer 3—IP Services Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Enable Web authentication and specify the Web authentication server.
web-auth enable apply server server-name
By default, Web authentication is disabled.
Specifying a Web authentication domain
About this task
You can specify different authentication domains for Web authentication users on different interfaces. After you specify a Web authentication domain on an interface, the device uses the authentication domain for AAA of all Web authentication users on the interface, ignoring the domain names carried in the usernames.
The device selects the authentication domain for a Web authentication user on an interface in this order:
1. The authentication domain specified for the interface.
2. The authentication domain carried in the username.
3. The system default authentication domain.
4. The ISP domain configured to accommodate users assigned to nonexistent domains.
If the selected domain does not exist on the device, user authentication fails. For information about ISP domains, see "Configuring AAA."
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Specify an authentication domain for Web authentication users on the interface.
web-auth domain domain-name
By default, no authentication domain is specified for Web authentication users.
Setting the redirection wait time
About this task
The redirection wait time determines the length of time that the device waits to redirect a user to the specified webpage after the user passes Web authentication.
You need to change the redirection wait time in some scenarios, for example, when a user needs to update the client IP address after passing Web authentication. To ensure that the specified webpage can be successfully opened, set the redirection wait time to be greater than the time that the user takes to update the IP address of the client.
Procedure
1. Enter system view.
system-view
2. Enter Web authentication server view.
web-auth server server-name
3. Set the redirection wait time.
redirect-wait-time period
By default, the redirection wait time for authenticated users is 5 seconds.
Configuring a Web authentication-free subnet
About this task
You can configure a Web authentication-free subnet so that users can freely access the network resources in the subnet without being authenticated.
Restrictions and guidelines
As a best practice, do not configure the same address value for a Web authentication-free subnet and a 802.1X free IP. Otherwise, when you cancel one of the configuration, the other configuration does not take effect, either.
Procedure
1. Enter system view.
system-view
2. Configure a Web authentication-free subnet.
web-auth free-ip ip-address { mask-length | mask }
Setting the maximum number of Web authentication users
Restrictions and guidelines
If the maximum number of online Web authentication users you set is less than that of the current online Web authentication users, the limit can be set successfully and does not impact the online Web authentication users. However, the system does not allow new Web authentication users to log in until the number drops down below the limit.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Set the maximum number of Web authentication users on the interface.
web-auth max-user max-number
By default, the maximum number of Web authentication users is 1024.
Configuring online Web authentication user detection
About this task
This feature enables the device to detect packets of an online user at the specified detection interval. If no packet from the user is received within the interval, the device logs out the user and notifies the RADIUS server to stop accounting for the user.
Restrictions and guidelines
To prevent the device from mistakenly logging out users, set the detection interval to be the same as the aging time of MAC address entries.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Enable online Web authentication user detection.
web-auth offline-detect interval interval
By default, online Web authentication user detection is disabled.
Configuring an Auth-Fail VLAN
Restrictions and guidelines
To make the Auth-Fail VLAN take effect, you must also enable MAC-based VLAN on the interface, and set the subnet of the Auth-Fail VLAN as the Web authentication-free subnet.
Because MAC-based VLAN takes effect only on Hybrid ports, Auth-Fail VLAN also takes effect only on Hybrid ports.
If a VLAN is specified as the super VLAN, do not configure the VLAN as an Auth-Fail VLAN of an interface. If a VLAN is specified as an Auth-Fail VLAN of an interface, do not configure the VLAN as a super VLAN.
Do not delete the VLAN that has been configured as an Auth-Fail VLAN. To delete this VLAN, first cancel the Auth-Fail VLAN configuration by using undo web-auth auth-fail vlan command.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Configure an Auth-Fail VLAN.
web-auth auth-fail vlan authfail-vlan-id
By default, no Auth-Fail VLAN is configured on an interface.
Configuring Web authentication to support Web proxy
About this task
By default, proxied HTTP requests cannot trigger Web authentication but are silently dropped. To allow such HTTP requests to trigger Web authentication, specify the port numbers of the Web proxy servers on the device.
Restrictions and guidelines
If a user's browser uses the Web Proxy Auto-Discovery (WPAD) protocol to discover Web proxy servers, you must perform the following tasks:
· Add the port numbers of the Web proxy servers on the device.
· Configure authentication-free rules to allow user packets destined for the IP address of the WPAD server to pass without authentication.
For Web authentication to support Web proxy:
· You must add the port numbers of the Web proxy servers on the device.
· Users must make sure their browsers that use a Web proxy server do not use the proxy server for the listening IP address of the local portal Web server. Thus, HTTP packets that the Web authentication user sends to the local portal Web server are not sent to the Web proxy server.
Procedure
1. Enter system view.
system-view
2. Add a Web proxy server port number.
web-auth proxy port port-number
You can execute this command multiple times to specify multiple port numbers of Web proxy servers.
Display and maintenance commands for Web authentication
Execute display commands in any view.
|
Task |
Command |
|
Display Web authentication configuration information on interfaces. |
display web-auth [ interface interface-type interface-number ] |
|
Display Web authentication-free subnets. |
display web-auth free-ip |
|
Display Web authentication server information. |
display web-auth server [ server-name ] |
|
Display Web authentication user information. |
display web-auth user [ interface interface-type interface-number | slot slot-number ] |
Web authentication configuration examples
Example: Configuring Web authentication by using the local authentication method
Network configuration
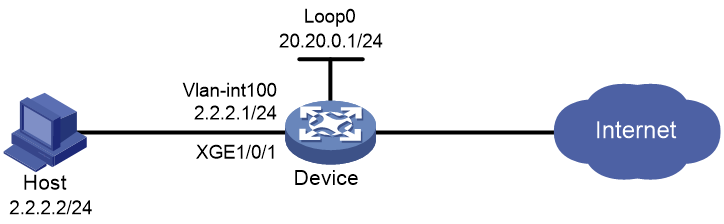
As shown in Figure 4, the host is directly connected to the device through Ten-GigabitEthernet 1/0/1.
Configure Web authentication on Ten-GigabitEthernet 1/0/1, and use local authentication and authorization for the users.
Configure the device to use HTTP to transfer the authentication data.
Procedure
1. Assign IP addresses to the host and the device as shown in Figure 4, and make sure the host and the device can reach each other. (Details not shown.)
2. Configure a local user:
# Create a local network access user named localuser.
<Device>system-view
[Device] local-user localuser class network
# Set the password to localpass in plaintext form for user localuser.
[Device-luser-network-localuser] password simple localpass
# Authorize the user to use LAN access services.
[Device-luser-network-localuser] service-type lan-access
[Device-luser-network-localuser] quit
3. Configure an ISP domain:
# Create an ISP domain named local.
[Device] domain local
# Configure the ISP domain to perform local authentication, authorization, and accounting for LAN access users.
[Device-isp-local] authentication lan-access local
[Device-isp-local] authorization lan-access local
[Device-isp-local] accounting lan-access local
[Device-isp-local] quit
4. Configure a local portal Web service:
# Create an HTTP-based local portal Web service and enter its view.
[Device] portal local-web-server http
# Specify file defaultfile.zip as the default authentication page file for the local portal Web service. (Make sure the authentication page file already exists in the root directory of the storage medium on the device.)
[Device-portal-local-websvr-http] default-logon-page defaultfile.zip
# Specify the HTTP listening port number as 80 for the portal Web service.
[Device–portal-local-websvr-http] tcp-port 80
[Device-portal-local-websvr-http] quit
5. Configure Web authentication:
# Create a Web authentication server named user.
[Device] web-auth server user
# Configure the redirection URL for the Web authentication server as http://20.20.0.1/portal/.
[Device-web-auth-server-user] url http://20.20.0.1/portal/
# Specify 20.20.0.1 as the IP address and 80 as the port number for the Web authentication server.
[Device-web-auth-server-user] ip 20.20.0.1 port 80
[Device-web-auth-server-user] quit
# Specify ISP domain local as the Web authentication domain.
[Device] interface ten-gigabitethernet 1/0/1
[Device-Ten-GigabitEthernet1/0/1] web-auth domain local
# Enable Web authentication by using Web authentication server user.
[Device-Ten-GigabitEthernet1/0/1] web-auth enable apply server user
[Device-Ten-GigabitEthernet1/0/1] quit
Verifying the configuration
# Display online Web authentication user information after user localuser passes Web authentication.
<Device> display web-auth user
Total online web-auth users: 1
User Name: localuser
MAC address: acf1-df6c-f9ad
Access interface: Ten-GigabitEthernet1/0/1
Initial VLAN: 100
Authorization VLAN: N/A
Authorization ACL ID: N/A
Authorization user profile: N/A
Example: Configuring Web authentication by using the RADIUS authentication method
Network configuration
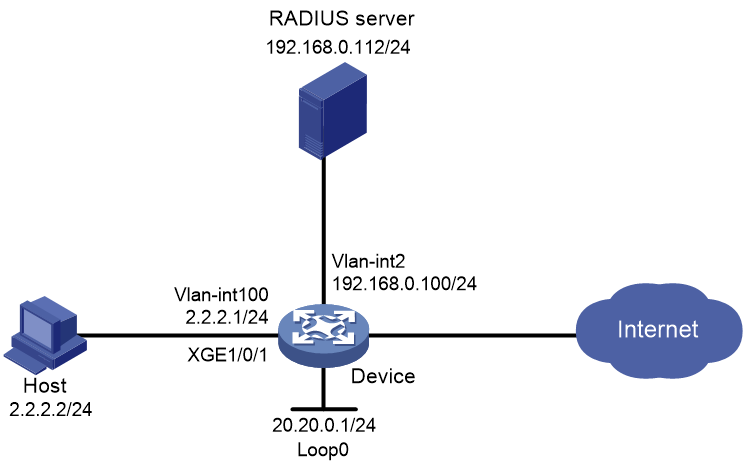
As shown in Figure 5, the host is directly connected to the device through Ten-GigabitEthernet 1/0/1.
Configure Web authentication on Ten-GigabitEthernet 1/0/1, and use a RADIUS server to perform authentication and authorization for the users.
Configure the device to use HTTP to transfer the authentication data.
Procedure
1. Configure the RADIUS server properly to provide authentication and accounting functions for users. In this example, the username is configured as user1 on the RADIUS server. (Details not shown.)
2. Create VLANs, assign IP addresses to the VLAN interfaces, and assign interfaces to the VLANs. Make sure the host, the RADIUS server, and the device can reach each other. (Details not shown.)
3. Configure a RADIUS scheme:
# Create a RADIUS scheme named rs1.
<Device> system-view
[Device] radius scheme rs1
# Specify the primary authentication server and primary accounting server, and configure the keys for communication with the servers.
[Device-radius-rs1] primary authentication 192.168.0.112
[Device-radius-rs1] primary accounting 192.168.0.112
[Device-radius-rs1] key authentication simple radius
[Device-radius-rs1] key accounting simple radius
# Exclude the ISP domain name from the username sent to the RADIUS server.
[Device-radius-rs1] user-name-format without-domain
[Device-radius-rs1] quit
4. Configure an authentication domain:
# Create an ISP domain named dm1.
[Device] domain dm1
# Configure AAA methods for the ISP domain
[Device-isp-dm1] authentication lan-access radius-scheme rs1
[Device-isp-dm1] authorization lan-access radius-scheme rs1
[Device-isp-dm1] accounting lan-access radius-scheme rs1
[Device-isp-dm1] quit
5. Configure a local portal Web service:
# Create an HTTP-based local portal Web service.
[Device] portal local-web-server http
# Specify the file defaultfile.zip as the default authentication page file for the local portal Web service. (Make sure the authentication page file already exists in the root directory of the storage medium on the device.)
[Device-portal-local-websvr-http] default-logon-page defaultfile.zip
# Specify 80 as the port number listened by the local portal Web service.
[Device–portal-local-websvr-http] tcp-port 80
[Device-portal-local-websvr-http] quit
6. Configure Web authentication:
# Create Web authentication server named user.
[Device] web-auth server user
# Specify http://20.20.0.1/portal/ as the redirection URL for the Web authentication server.
[Device-web-auth-server-user] url http://20.20.0.1/portal/
# Specify the IP address of the Web authentication server as 20.20.0.1 (the IP address of Loopback 0) and the port number as 80.
[Device-web-auth-server-user] ip 20.20.0.1 port 80
[Device-web-auth-server-user] quit
# Specify domain dml as the Web authentication domain.
[Device] interface ten-gigabitethernet 1/0/1
[Device-Ten-GigabitEthernet1/0/1] web-auth domain dm1
# Enable Web authentication by using Web authentication server user.
[Device-Ten-GigabitEthernet1/0/1] web-auth enable apply server user
[Device-Ten-GigabitEthernet1/0/1] quit
Verifying the configuration
# Display Web authentication user information after user user1 passes Web authentication.
<Device> display web-auth user
Total online web-auth users: 1
User Name: user1
MAC address: acf1-df6c-f9ad
Access interface: Ten-GigabitEthernet1/0/1
Initial VLAN: 100
Authorization VLAN: N/A
Authorization ACL ID: N/A
Authorization user profile: N/A
Troubleshooting Web authentication
Failure to come online (local authentication interface using the default ISP domain
Symptom
No authentication domain is specified for the local authentication interface. A user fails to pass Web authentication to come online.
Analysis
If no Web authentication domain is specified, the system default ISP domain (domain system) is used for Web authentication. The system default domain uses the local authentication method by default. Using these default domain settings, the local authentication should have operated correctly.
The local authentication fails might because that the authentication method of the system default domain is changed or the system default domain is changed.
Solution
To resolve the problem, perform the following tasks:
1. Use the display domain command to identify whether the AAA methods for Web users in the system default domain are local.
2. If the AAA methods for Web users in the system default domain are not local, reconfigure the AAA methods as local.