- Table of Contents
-
- 10-Security
- 00-Preface
- 01-AAA configuration
- 02-802.1X configuration
- 03-802.1X client configuration
- 04-MAC authentication configuration
- 05-Portal configuration
- 06-User profile configuration
- 07-Password control configuration
- 08-Public key management
- 09-PKI configuration
- 10-IPsec configuration
- 11-SSH configuration
- 12-SSL configuration
- 13-Session management
- 14-Connection limit configuration
- 15-Attack detection and prevention configuration
- 16-IP source guard configuration
- 17-ARP attack protection configuration
- 18-ND attack defense configuration
- 19-User isolation configuration
- 20-ASPF configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 14-Connection limit configuration | 102.06 KB |
Feature and hardware compatibility
Command and hardware compatibility
Connection limit configuration task list
Creating a connection limit policy
Configuring the connection limit policy
Applying the connection limit policy
Displaying and maintaining connection limits
Connection limit configuration example
Troubleshooting connection limits
ACLs in the connection limit rules with overlapping segments
Configuring connection limits
Overview
The connection limit feature enables the device to monitor and limit the number of established connections.
As shown in Figure 1, the following problems might exist:
· If Host B initiates a large number of connections in a short period of time, it might exhaust system resources and cause Host A to be unable to access the Internet.
· If the internal server receives a large number of connection requests in a short period of time, the server cannot process other requests.
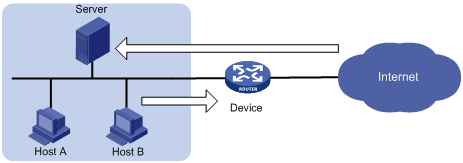
To resolve these problems, configure connection limits on all interfaces or on an interface by applying the configured connection limit policies globally or to the interface.
Compatibility information
Feature and hardware compatibility
|
Hardware series |
Model |
Connection limit compatibility |
|
WX1800H series |
WX1804H WX1810H WX1820H |
Yes |
|
WX2500H series |
WX2510H WX2540H WX2560H |
Yes |
|
WX3000H series |
WX3010H WX3010H-L WX3010H-X WX3024H WX3024H-L |
Yes: · WX3010H · WX3010H-X · WX3024H No: · WX3010H-L · WX3024H-L |
|
WX3500H series |
WX3508H WX3510H WX3520H WX3540H |
Yes |
|
WX5500E series |
WX5510E WX5540E |
Yes |
|
WX5500H series |
WX5540H WX5560H WX5580H |
Yes |
|
Access controller modules |
EWPXM1MAC0F EWPXM1WCME0 EWPXM2WCMD0F LSQM1WCMX20 LSQM1WCMX40 LSUM1WCME0 LSUM1WCMX20RT LSUM1WCMX40RT |
Yes |
Command and hardware compatibility
The WX1800H series, WX2500H series, and WX3000H series access controllers do not support the slot keyword or the slot-number argument.
Connection limit configuration task list
|
Tasks at a glance |
|
(Required.) Creating a connection limit policy |
|
(Required.) Configuring the connection limit policy |
|
(Required.) Applying the connection limit policy |
Creating a connection limit policy
A connection limit policy contains a set of connection limit rules, each of which defines a range of connections and the criteria for limiting the connections.
To create a connection limit policy:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Create a connection limit policy and enter its view. |
connection-limit { ipv6-policy | policy } policy-id |
By default, no connection limit policy exists. |
Configuring the connection limit policy
To use a connection limit policy, you need to add limit rules to the policy. Each rule defines a range of connections and the criteria for limiting the connections. Connections in the range will be limited based on the criteria. The criteria include upper/lower connection limit and connection establishment rate limit. When the number of matching connections reaches the upper limit, the device does not accept new connections until the number of connections drops below the lower limit. The device will send logs when the number of connections exceeds the upper limit and when the number of connections drops below the lower limit. If the matching connections are limited based on the establishment rate, the number of connections established per second cannot exceed the rate limit. The connections that do not match any connection limit rules are not limited.
In each connection limit rule, an ACL is used to define the connection range. In addition, the rule also uses the following filtering methods to further limit the connections:
· per-destination—Limits user connections by destination IP address.
· per-service—Limits user connections by service (transport layer protocol and service port).
· per-source—Limits user connections by source IP address.
You can select more than one filtering method, and the selected methods take effect at the same time. For example, if you specify both per-destination and per-service, the user connections using the same service and destined to the same IP address are limited. If you do not specify any filtering methods in a limit rule, all user connections in the range are limited.
When a connection limit policy is applied, connections on the device match all limit rules in the policy in ascending order of rule IDs. H3C recommends that you specify a smaller range and more filtering methods in a rule with a smaller ID.
To configure the connection limit policy:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter connection limit policy view. |
connection-limit { ipv6-policy | policy } policy-id |
N/A |
|
3. Configure a connection limit rule. |
· In IPv4 connection limit policy view: · In IPv6 connection limit policy view: |
By default, no connection limit rules exist. |
|
4. (Optional.) Configure a description for the connection limit policy. |
By default, the connection limit policy does not have a description. |
Applying the connection limit policy
To make a connection limit policy take effect, apply it globally or to an interface. The connection limit policy applied to an interface takes effect only on the specified connections on the interface. The connection limit policy applied globally takes effect on all the specified connections on the device.
Different connection limit policies can be applied to individual interfaces as well as globally on the device. In this case, the device matches connections against these policies in the order of the policy on the inbound interface, the global policy, and the policy on the outbound interface. It cannot accept new connections as long as the number of connections reaches the lowest upper connection limit defined by these policies.
To apply a connection limit policy:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Apply a connection limit policy. |
· Apply a connection limit policy
globally: · Apply a connection limit policy to an interface: a. interface interface-type interface-number b. connection-limit apply { ipv6-policy | policy } policy-id |
By default, no connection limit is applied. Only one IPv4 connection limit policy and one IPv6 connection limit policy can be applied globally or to an interface. A new IPv4 or IPv6 connection limit policy overwrites the old policy. |
Displaying and maintaining connection limits
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display the connection limit policy information. |
display connection-limit { ipv6-policy | policy } { all | policy-id } |
|
Display the connection limit statistics globally or on an interface. |
display connection-limit statistics { global | interface interface-type interface-number } [ slot slot-number ] |
|
Display statistics about IPv6 connections matching connection limit rules globally or on an interface. |
display connection-limit { ipv6-stat-nodes | stat-nodes } { global | interface interface-type interface-number } [ slot slot-number ] [ destination destination-ip | service-port port-number | source source-ip ] * [ count ] |
|
Clear the connection limit statistics globally or on an interface. |
reset connection-limit statistics { global | interface interface-type interface-number } [ slot slot-number ] |
Connection limit configuration example
Network requirements
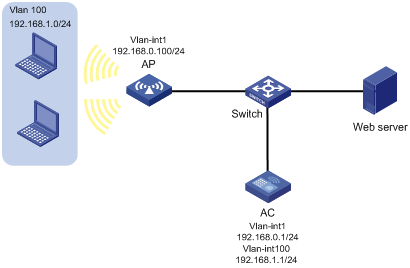
As shown in Figure 2, all hosts access the Web server through the wireless network. To ensure the availability of the service resources, configure the AC to allow a maximum of 100 HTTP connections from each host to the Web server.
Configuration procedure
# Create ACL 3000 to permit HTTP requests to the Web server.
<AC> system-view
[AC] acl advanced 3000
[AC-acl-ipv4-adv-3000] rule permit tcp source 192.168.1.0 0.0.0.255 destination-port eq 80
[AC-acl-ipv4-adv-3000] quit
# Create connection limit policy 1.
[AC] connection-limit policy 1
# Configure connection limit rule 1 to permit a maximum of 100 connections from each host matching ACL 3000. When the number of connections exceeds 100, new connections cannot be established until the number drops below 50.
[AC-connection-limit-policy-1] limit 1 acl 3000 per-source amount 100 50
[AC-connection-limit-policy-1] quit
# Apply connection limit policy 1 globally.
[AC] connection-limit apply global policy 1
Verifying the configuration
# Display information about the connection limit policy.
[AC] display connection-limit policy 1
IPv4 connection limit policy 1 has been applied 1 times, and has 1 limit rules.
Limit rule list:
Policy Rule Stat Type HiThres LoThres rate ACL
-------------------------------------------------------------------------------
1 1 Src 100 50 0 3000
Application list:
Global
Troubleshooting connection limits
ACLs in the connection limit rules with overlapping segments
Symptom
A connection limit policy has two rules. Rule 1 sets the upper limit to 10 for the connections from each host on segment 192.168.0.0/24. Rule 2 sets the upper limit to 100 for the connections from 192.168.0.100/24.
<AC> system-view
[AC] acl basic 2001
[AC-acl-ipv4-basic-2001] rule permit source 192.168.0.0 0.0.0.255
[AC-acl-ipv4-basic-2001] quit
[AC] acl basic 2002
[AC-acl-ipv4-basic-2002] rule permit source 192.168.0.100 0
[AC-acl-ipv4-basic-2002] quit
[AC] connection-limit policy 1
[AC-connection-limit-policy-1] limit 1 acl 2001 per-destination amount 10 5
[AC-connection-limit-policy-1] limit 2 acl 2002 per-destination amount 100 10
As a result, the host at 192.168.0.100 can only initiate a maximum of 10 connections to the external network.
Solution
To resolve the problem:
1. Rearrange the two connection limit rules by exchanging their rule IDs.
2. If the problem persists, contact H3C Support.
