- Table of Contents
-
- H3C S3100 Series Ethernet Switches Operation Manual (For Soliton)(V1.02)
- 00-1Cover
- 00-2Product Overview
- 01-CLI Operation
- 02-Login Operation
- 03-Configuration File Management Operation
- 04-VLAN Operation
- 05-Management VLAN Operation
- 06-IP Address-IP Performance Operation
- 07-Voice VLAN Operation
- 08-GVRP Operation
- 09-Port Basic Configuration Operation
- 10-Link Aggregation Operation
- 11-Port Isolation Operation
- 12-Port Security-Port Binding Operation
- 13-DLDP Operation
- 14-MAC Address Table Management Operation
- 15-MSTP Operation
- 16-Multicast Operation
- 17-802.1x-System Guard Operation
- 18-AAA Operation
- 19-MAC Address Authentication Operation
- 20-ARP Operation
- 21-DHCP Operation
- 22-ACL Operation
- 23-QoS-QoS Profile Operation
- 24-Mirroring Operation
- 25-Stack-Cluster Operation
- 26-SNMP-RMON Operation
- 27-NTP Operation
- 28-SSH Operation
- 29-File System Management Operation
- 30-FTP-SFTP-TFTP Operation
- 31-Information Center Operation
- 32-System Maintenance and Debugging Operation
- 33-VLAN-VPN Operation
- 34-HWPing Operation
- 35-IPv6 Management Operation
- 36-DNS Operation
- 37-Smart Link-Monitor Link Operation
- 38-Appendix
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 33-VLAN-VPN Operation | 430.45 KB |
Chapter 1 VLAN-VPN Configuration
1.1.1 Introduction to VLAN-VPN
1.1.2 Implementation of VLAN-VPN
1.1.3 Configuring the TPID for VLAN-VPN Packets
1.2.1 VLAN-VPN Configuration Task List
1.2.2 Enabling the VLAN-VPN Feature for a Port
1.2.3 Configuring the TPID Value for VLAN-VPN Packets
1.3 Displaying and Maintaining VLAN-VPN Configuration
1.4 VLAN-VPN Configuration Example
1.4.1 Transmitting User Packets through a Tunnel in the Public Network by Using VLAN-VPN
Chapter 2 Selective QinQ Configuration
2.2 Selective QinQ Configuration
2.2.1 Selective QinQ Configuration Task List
2.2.2 Configuring Global Tag Mapping Rules for Selective QinQ
2.2.3 Enabling the Selective QinQ Feature for a Port
2.3 Selective QinQ Configuration Example
2.3.1 Processing Private Network Packets by Their Types
Chapter 3 VLAN Mapping Configuration
3.1.1 Introduction to VLAN Mapping
3.1.2 VLAN Mapping Implementation
3.2.1 VLAN Mapping Configuration Task List
3.2.2 Enabling the VLAN Mapping Function Based on a Global VLAN Mapping Rule
3.2.3 Enabling the VLAN Mapping Function Based on a Port-level VLAN Mapping Rule
3.3 VLAN Mapping Configuration Example
3.3.1 Replacing the Private Network VLAN Tag through VLAN Mapping
Chapter 4 BPDU Tunnel Configuration.
4.1.1 Introduction to the BPDU Tunnel Feature
4.2.1 Configuration Prerequisites
4.2.2 Configuring a BPDU Tunnel
4.3 Displaying and Maintaining BPDU Tunnel Configuration
4.4 BPDU Tunnel Configuration Example
4.4.1 Transmitting STP Packets Through a Tunnel
Chapter 1 VLAN-VPN Configuration
When configuring VLAN-VPN, go to these sections for information you are interested in:
l Displaying and Maintaining VLAN-VPN Configuration
l VLAN-VPN Configuration Example
1.1 VLAN-VPN Overview
1.1.1 Introduction to VLAN-VPN
Virtual private network (VPN) is a new technology that emerges with the expansion of the Internet. It can be used for establishing private networks over the public network. With VPN, you can specify to process packets on the client or the access end of the service provider in specific ways, establish dedicated tunnels for user traffic on public network devices, and thus improve data security.
VLAN-VPN feature is a simple yet flexible Layer 2 tunneling technology. It tags private network packets with outer VLAN tags, thus enabling the packets to be transmitted through the service providers’ backbone networks with both inner and outer VLAN tags. In public networks, packets of this type are transmitted by their outer VLAN tags (that is, the VLAN tags of public networks), and the inner VLAN tags are treated as part of the payload.
Figure 1-1 describes the structure of the packets with single-layer VLAN tags.
![]()
Figure 1-1 Structure of packets with single-layer VLAN tags
Figure 1-2 describes the structure of the packets with double-layer VLAN tags.
![]()
Figure 1-2 Structure of packets with double-layer VLAN tags
Compared with MPLS-based Layer 2 VPN, VLAN-VPN has the following features:
l It provides Layer 2 VPN tunnels that are simpler.
l VLAN-VPN can be implemented through manual configuration. That is, signaling protocol-related configuration is not needed.
The VLAN-VPN feature provides you with the following benefits:
l Saves public network VLAN ID resource.
l You can have VLAN IDs of your own, which is independent of public network VLAN IDs.
l Provides simple Layer 2 VPN solutions for small-sized MANs or intranets.
1.1.2 Implementation of VLAN-VPN
With the VLAN-VPN feature enabled, no matter whether or not a received packet already carries a VLAN tag, the switch will tag the received packet with the default VLAN tag of the receiving port and add the source MAC address to the MAC address table of the default VLAN. When a packet reaches a VLAN-VPN-enabled port:
l If the packet already carries a VLAN tag, the packet becomes a dual-tagged packet.
l Otherwise, the packet becomes a packet carrying the default VLAN tag of the port.
1.1.3 Configuring the TPID for VLAN-VPN Packets
A VLAN tag uses the tag protocol identifier (TPID) field to identify the protocol type of the tag. The value of this field is 0x8100 for IEEE 802.1Q.
Figure 1-3 illustrates the structure of the IEEE 802.1Q VLAN tag in an Ethernet frame.
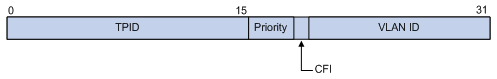
Figure 1-3 The structure of the VLAN tag in an Ethernet frame
An S3100 switch determines whether a received frame is VLAN tagged by comparing its own TPID with the TPID field in the received frame. If they match, the frame is considered as a VLAN tagged frame. If not, the switch tags the frame with the default VLAN tag of the receiving port.
By default, S3100 series switches adopt the IEEE 802.1Q TPID value 0x8100. Some vendors, however, use other TPID values such as 0x9100. For compatibility with these systems, the S3100 series switches allow you to change the TPID that a port uses when tagging a received VLAN-VPN frame as needed. When doing that, you should set the same TPID on both the customer-side port and the service provider-side port.
The TPID in an Ethernet frame has the same position with the protocol type field in a frame without a VLAN tag. To avoid problems in packet forwarding and handling, you cannot set the TPID value to any of the values in the table below.
Table 1-1 Commonly used protocol type values in Ethernet frames
|
Protocol type |
Value |
|
ARP |
0x0806 |
|
IP |
0x0800 |
|
MPLS |
0x8847/0x8848 |
|
IPX |
0x8137 |
|
IS-IS |
0x8000 |
|
LACP |
0x8809 |
|
802.1x |
0x888E |
1.2 VLAN-VPN Configuration
1.2.1 VLAN-VPN Configuration Task List
Complete the following tasks to configure VLAN-VPN:
|
Task |
Remarks |
|
Required |
|
|
Optional |
1.2.2 Enabling the VLAN-VPN Feature for a Port
Follow these steps to enable the VLAN-VPN feature for a port:
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Enter Ethernet port view |
interface interface-type interface-number |
— |
|
Enable the VLAN-VPN feature on the port |
vlan-vpn enable |
Required By default, the VLAN-VPN feature is disabled on a port. |
![]() Caution:
Caution:
The VLAN mapping function and the VLAN VPN function are mutually exclusive on the same port.
1.2.3 Configuring the TPID Value for VLAN-VPN Packets
For your device to correctly identify the VLAN tagged frames from the public network, make sure that the TPID you will use is the same as that used on the peer device in the public network.
Follow these steps to configure the TPID for VLAN-VPN packets :
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Set the TPID value on the port |
vlan-vpn tpid value |
Required Do not set the TPID value to any of the protocol type values listed in Table 1-1. For H3C series switches, the TPID defaults to 0x8100. |
1.3 Displaying and Maintaining VLAN-VPN Configuration
|
To do... |
Use the command... |
Remarks |
|
Display the VLAN-VPN configurations of all the ports |
display port vlan-vpn |
Available in any view |
1.4 VLAN-VPN Configuration Example
1.4.1 Transmitting User Packets through a Tunnel in the Public Network by Using VLAN-VPN
I. Network requirements
As shown in Figure 1-4, Switch A and Switch B are both S3100 series switches. They connect the users to the servers through the public network.
l PC users and PC servers are in VLAN 100 created in the private network, while terminal users and terminal servers are in VLAN 200, which is also created in the private network. The VLAN VPN connection is established in VLAN 1040 of the public network.
l Switches of other vendors’ are used in the public network. They use the TPID value 0x9200.
l Employ VLAN-VPN on Switch A and Switch B to enable the PC users and PC servers to communicate with each through a VPN, and employ VLAN-VPN on Switch A and Switch B to enable the Terminal users and Terminal servers to communicate with each other through a VPN.
II. Network diagram
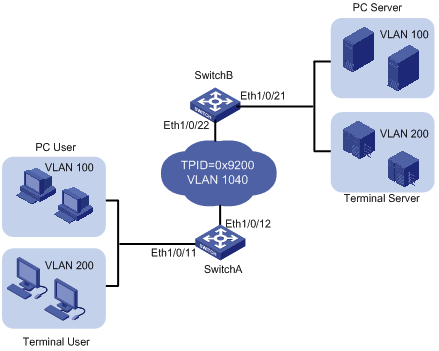
Figure 1-4 Network diagram for VLAN-VPN configuration
III. Configuration procedure
l Configure Switch A.
# Enable the VLAN-VPN feature on Ethernet 1/0/11 of Switch A and tag the packets received on this port with the tag of VLAN 1040 as the outer VLAN tag.
<SwitchA> system-view
[SwitchA] vlan 1040
[SwitchA-vlan1040] port Ethernet 1/0/11
[SwitchA-vlan1040] quit
[SwitchA] interface Ethernet 1/0/11
[SwitchA-Ethernet1/0/11] vlan-vpn enable
[SwitchA-Ethernet1/0/11] quit
# Set the global TPID value to 0x9200 (for intercommunication with the devices in the public network) and configure Ethernet 1/0/12 as a trunk port permitting packets of VLAN 1024.
[SwitchA] vlan-vpn tpid 9200
[SwitchA] interface Ethernet 1/0/12
[SwitchA-Ethernet1/0/12] port link-type trunk
[SwitchA-Ethernet1/0/12] port trunk permit vlan 1040
l Configure Switch B.
# Enable the VLAN-VPN feature on Ethernet 1/0/21 of Switch B and tag the packets received on this port with the tag of VLAN 1040 as the outer VLAN tag.
<SwitchB> system-view
[SwitchB] vlan 1040
[SwitchB-vlan1040] port Ethernet 1/0/21
[SwitchB-vlan1040] quit
[SwitchB] interface Ethernet 1/0/21
[SwitchB-Ethernet1/0/21] vlan-vpn enable
# Set the global TPID value to 0x9200 (for intercommunication with the devices in the public network) and set Ethernet 1/0/22 as a trunk port permitting packets of VLAN 1024.
[SwitchB-Ethernet1/0/21] quit
[SwitchB] vlan-vpn tpid 9200
[SwitchB] interface Ethernet 1/0/22
[SwitchB-Ethernet1/0/22] port link-type trunk
[SwitchB-Ethernet1/0/22] port trunk permit vlan 1040
& Note:
l Do not configure VLAN 1040 as the default VLAN of Ethernet 1/0/12 of Switch A and Ethernet 1/0/22 of Switch B. Otherwise, the outer VLAN tag of a packet will be removed during transmission.
l In this example, both Ethernet1/0/11 of Switch A and Ethernet1/0/21 of Switch B are access ports. In cases where the ports are trunk ports or hybrid ports, you need to configure the two ports to remove the outer VLAN tags before transmitting packets of VLAN 1040. Refer to VLAN in this manual for detailed configuration.
l Configure the devices in the public network
# As the devices in the public network are from other vendors, only the basic principles are introduced here. That is, you need to configure the devices connecting to Ethernet 1/0/12 of Switch A and Ethernet 1/0/22 of Switch B to permit the corresponding ports to transmit tagged packets of VLAN 1040.
IV. Data transfer process
The following describes how a packet is forwarded from Switch A to Switch B in this example.
1) As Ethernet 1/0/11 of Switch A is a VLAN-VPN port, when a packet from the customer’s network side reaches this port, it is tagged with the default VLAN tag of the port (VLAN 1040).
2) The TPID value of the outer VLAN tag is set to 0x9200 before the packet is forwarded to the public network through Ethernet1/0/12 of Switch A.
3) The outer VLAN tag of the packet remains unchanged while the packet travels in the public network, till it reaches Ethernet1/0/22 of Switch B.
4) After the packet reaches Switch B, it is forwarded through Ethernet1/0/21 of Switch B. As the port belongs to VLAN 1040 and is an access port, the outer VLAN tag (the tag of VLAN 1040) of the packet is removed before the packet is forwarded, which restores the packet to a packet tagged with only the private VLAN tag and enables it to be forwarded to its destination networks.
5) It is the same case when a packet travels from Switch B to Switch A.
Chapter 2 Selective QinQ Configuration
When configuring selective QinQ, go to these sections for information you are interested in:
l Selective QinQ Configuration
l Selective QinQ Configuration Example
2.1 Selective QinQ Overview
2.1.1 Selective QinQ Overview
Selective QinQ is an enhanced application of the VLAN-VPN feature. With the selective QinQ feature, you can configure inner-to-outer VLAN tag mapping, according to which you can add different outer VLAN tags to the packets with different inner VLAN tags.
The selective QinQ feature makes the service provider network structure more flexible. You can classify the terminal users on the port connecting to the access layer device according to their VLAN tags, and add different outer VLAN tags to these users. In the public network, you can configure QoS policies based on outer VLAN tags to assign different priorities to different packets, thus providing differentiated services. See Figure 2-1 for details.
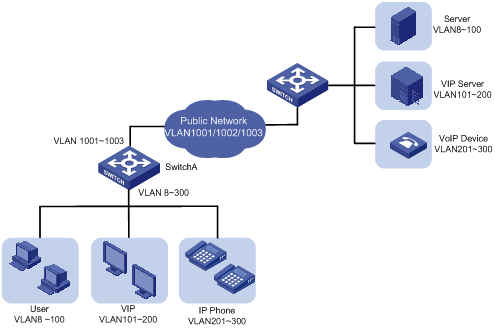
Figure 2-1 Diagram for a selective QinQ implementation
In this implementation, Switch A is an access device of the service provider. The users connecting to it include common customers (in VLAN 8 to VLAN 100), VIPs (in VLAN 101 to VLAN 200), and IP telephone users (in VLAN 201 to VLAN 300). Packets of all these users are forwarded by Switch A to the public network.
After the selective QinQ feature and the inner-to-outer tag mapping feature are enabled on the port connecting Switch A to these users, the port will add different outer VLAN tags to the packets according to their inner VLAN tags. For example, you can configure to add the tag of VLAN 1002 to the packets of IP telephone users in VLAN 201 to VLAN 300 and forward the packets to the VoIP device, which is responsible for processing IP telephone services.
To guarantee the quality of voice packet transmission, you can configure QoS policies in the public network to reserve bandwidth for packets of VLAN 1002 and forward them preferentially.
In this way, you can configure different forwarding policies for data of different type of users, thus improving the flexibility of network management. On the other hand, network resources are well utilized, and users of the same type are also isolated by their inner VLAN tags. This helps to improve network security.
2.2 Selective QinQ Configuration
2.2.1 Selective QinQ Configuration Task List
Complete the following tasks to configure selective QinQ:
|
Task |
Remarks |
|
Required |
|
|
Optional |
2.2.2 Configuring Global Tag Mapping Rules for Selective QinQ
Table 2-1 Configure global tag mapping rules for selective QinQ
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Configure the outer VLAN tag and enter QinQ view |
vlan-vpn vid vlan-id |
Required |
|
Configure to add outer VLAN tags to the packets with the specific inner VLAN tags |
raw-vlan-id inbound vlan-id-list |
Required By default, the feature of adding an outer VLAN tag to the packets with the specific inner VLAN tags is disabled. |
& Note:
Do not enable both the selective QinQ function and the DHCP snooping function on a switch. Otherwise, the DHCP snooping function may operate improperly.
2.2.3 Enabling the Selective QinQ Feature for a Port
Table 2-2 Enable the selective QinQ feature
|
Operation |
Command |
|
|
Enter system view |
system-view |
— |
|
Enter Ethernet port view |
interface interface-type interface-number |
— |
|
Enable the selective QinQ feature |
vlan-vpn selective enable |
Required By default, the selective QinQ feature is not enabled on a port. |
2.3 Selective QinQ Configuration Example
2.3.1 Processing Private Network Packets by Their Types
I. Network requirements
l Ethernet 1/0/3 of Switch A provides public network access for PC users and IP phone users. PC users belong to VLAN 100 through VLAN 108, and IP phone users belong to VLAN 200 through VLAN 230. Ethernet 1/0/5 of Switch A is connected to the public network. The peer end of Switch A is Switch B.
l Ethernet 1/0/11 of Switch B is connected to the public network. Ethernet 1/0/12 and Ethernet1/0/13 of Switch B provide network access for PC servers belonging to VLAN 100 through VLAN 108 and voice gateways (for IP phone users) belonging to VLAN 200 through VLAN 230 respectively.
l The public network permits packets of VLAN 1000 and VLAN 1200. Apply QoS policies for these packets to reserve bandwidth for packets of VLAN 1200. That is, packets of VLAN 1200 have higher transmission priority over packets of VLAN 1000.
l Employ the selective QinQ feature on Switch A and Switch B to differentiate traffic of PC users from that of IP phone users, for the purpose of using QoS policies to guarantee higher priority for voice traffic.
l To reduce broadcast packets in the network, enable the inter-VLAN MAC address replicating feature for selective QinQ.
II. Network diagram
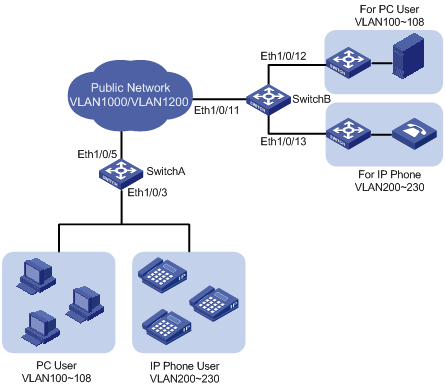
Figure 2-2 Network diagram for selective QinQ configuration
III. Configuration procedure
l Configure Switch A.
# Create VLAN 1000, VLAN 1200 and VLAN 5 (the default VLAN of Ethernet 1/0/3) on SwitchA.
<SwitchA> system-view
[SwitchA] vlan 1000
[SwitchA-vlan1000] quit
[SwitchA] vlan 1200
[SwitchA-vlan1200] quit
[SwitchA] vlan 5
[SwitchA-vlan5] quit
# Configure Ethernet 1/0/5 as a hybrid port and configure it not to remove VLAN tags when forwarding packets of VLAN 5, VLAN 1000, and VLAN 1200.
[SwitchA] interface Ethernet 1/0/5
[SwitchA-Ethernet1/0/5] port link-type hybrid
[SwitchA-Etherent1/0/5] port hybrid vlan 5 1000 1200 tagged
[SwitchA-Ethernet1/0/5] quit
# Configure Ethernet 1/0/3 as a hybrid port and configure VLAN 5 as its default VLAN. Configure Ethernet 1/0/3 to remove VLAN tags when forwarding packets of VLAN 5, VLAN 1000, and VLAN 1200.
[SwitchA] interface Ethernet 1/0/3
[SwitchA-Ethernet1/0/3] port link-type hybrid
[SwitchA-Ethernet1/0/3] port hybrid pvid vlan 5
[SwitchA-Etherent1/0/3] port hybrid vlan 5 1000 1200 untagged
# Configure global tag mapping rules for selective QinQ to insert VLAN 1000 tag as the outer VLAN tag in packets with the tags of VLAN 100 through VLAN 108 as the inner tags, and insert VLAN 1200 tag as the outer VLAN tag in packets with the tags of VLAN 200 through VLAN 230 as the inner tags.
[SwitchA-Ethernet1/0/3] quit
[SwitchA] vlan-vpn vid 1000
[SwitchA-vid-1000] raw-vlan-id inbound 100 to 108
[SwitchA-vid-1000] quit
[SwitchA] vlan-vpn vid 1200
[SwitchA-vid-1200] raw-vlan-id inbound 200 to 230
# Enable the selective QinQ feature on Ethernet 1/0/3.
[SwitchA-vid-1200] quit
[SwitchA] interface Ethernet 1/0/3
[SwitchA-Ethernet1/0/3] vlan-vpn selective enable
After the above configuration, packets of VLAN 100 through VLAN 108 (that is, packets of PC users) are tagged with the tag of VLAN 1000 as the outer VLAN tag when they are forwarded to the public network by Switch A; and packets of VLAN 200 through VLAN 230 (that is, packets of IP phone users) are tagged with the tag of VLAN 1200 as the outer VLAN tag when they are forwarded to the public network.
l Configure Switch B.
# Create VLAN 1000, VLAN 1200, VLAN 12 (the default VLAN of Ethernet1/0/12) and VLAN 13 (the default VLAN of Ethernet1/0/13) on Switch B.
<SwitchB> system-view
[SwitchB] vlan 1000
[SwitchB-vlan1000] quit
[SwitchB] vlan 1200
[SwitchB-vlan1200] quit
[SwitchB] vlan 12 to 13
# Configure Ethernet 1/0/11 as a hybrid port, and configure Ethernet 1/0/11 not to remove VLAN tags when forwarding packets of VLAN 12, VLAN 13, VLAN 1000, and VLAN 1200.
<SwitchB> system-view
[SwitchB] interface Ethernet 1/0/11
[SwitchB-Etherent1/0/11] port link-type hybrid
[SwitchB-Etherent1/0/11] port hybrid vlan 12 13 1000 1200 tagged
# Configure Ethernet1/0/12 as a hybrid port and configure VLAN 12 as its default VLAN . Configure Ethernet 1/0/12 to remove VLAN tags when forwarding packets of VLAN 12 and VLAN 1000.
[SwitchB] interface Ethernet 1/0/12
[SwitchB-Etherent1/0/12] port link-type hybrid
[SwitchB-Etherent1/0/12] port hybrid pvid vlan 12
[SwitchB-Etherent1/0/12] port hybrid vlan 12 1000 untagged
[SwitchB-Ethernet1/0/12] quit
# Configure Ethernet 1/0/13 as a hybrid port and configure VLAN 13 as its default VLAN . Configure Ethernet 1/0/13 to remove VLAN tags when forwarding packets of VLAN 13 and VLAN 1200.
[SwitchB] interface Ethernet 1/0/13
[SwitchB-Etherent1/0/13] port link-type hybrid
[SwitchB-Etherent1/0/13] port hybrid pvid vlan 13
[SwitchB-Etherent1/0/13] port hybrid vlan 13 1200 untagged
After the above configuration, Switch B can forward packets of VLAN 1000 and VLAN 1200 to the corresponding servers through Ethernet 1/0/12 and Ethernet 1/0/13 respectively.
To make the packets from the servers be transmitted to the clients in the same way, you need to configure the selective QinQ feature on SwitchB. The configuration on Switch B is similar to that on Switch A and is thus omitted.
& Note:
l A selective QinQ-enabled device tags a user packet with an outer VLAN tag regardless of the VLAN tag of the user packet, so there is no need to configure user VLANs on the device.
l Make sure the packets of the default VLAN of a selective QinQ-enabled port are permitted on both the local port and the port connecting to the public network.
Chapter 3 VLAN Mapping Configuration
3.1 VLAN Mapping Overview
3.1.1 Introduction to VLAN Mapping
The VLAN mapping function can replace the private network VLAN tag of a customer packet with a public network VLAN tag, so that the customer packet can be transmitted within the public network in a way conforming to the public network layout. When the packet reaches the peer customer network, the VLAN tag of the packet is restored to the previous private network VLAN tag. In this way, the packet is transmitted to the destination properly.
With the VLAN mapping function enabled, when the switch receives a packet tagged with a network VLAN tag, it looks up the mapping rules configured for the matched VLAN tag and then replaces the existing VLAN tag with the corresponding one (if the matched mapping rule exists).
Figure 3-1 shows the structure of a packet tagged with a private network VLAN tag.
![]()
Figure 3-1 The structure of a packet tagged with a private network VLAN tag
Figure 3-2 shows the structure of a packet after VLAN tag replacement.
![]()
Figure 3-2 The structure of a packet tagged with a public network VLAN tag
Different from VLAN VPN and selective QinQ, the VLAN mapping function does not cause a packet to carry multiple VLAN tags. A packet is transmitted with only one VLAN tag. Therefore, you need to make sure the private network VLAN tags can be restored before customer packets enter the destination private network for customer packets to be transmitted properly.
3.1.2 VLAN Mapping Implementation
You can configure VLAN mapping rules for each port of an S3100 series switch. With the VLAN mapping function enabled on a port, the port maps private network VLAN tags to the corresponding public network VLAN tags for packets to be forwarded to the public network and performs the converse operation for the packets to be forwarded to the destination private network.
3.2 Configuring VLAN Mapping
3.2.1 VLAN Mapping Configuration Task List
Table 3-1 VLAN mapping configuration task list
|
Task |
Description |
|
Enabling the VLAN Mapping Function Based on a Global VLAN Mapping Rule |
Use either of the tasks |
|
Enabling the VLAN Mapping Function Based on a Port-level VLAN Mapping Rule |
![]() Caution:
Caution:
The VLAN mapping function and the VLAN VPN function are mutually exclusive on the same port.
3.2.2 Enabling the VLAN Mapping Function Based on a Global VLAN Mapping Rule
Table 3-2 Enable the VLAN mapping function based on a global VLAN mapping rule
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Define a VLAN mapping rule |
vlan-mapping vlan old-vlan-id remark new-vlan-id |
Required By default, no VLAN mapping rule is defined. |
|
Enter Ethernet port view |
interface interface-type interface-number |
— |
|
Enable the VLAN mapping function |
vlan-mapping enable |
Required By default, the VLAN mapping function is disabled. |
& Note:
l A port that is in a link aggregation port group cannot have the VLAN Mapping feature enabled.
l The VLAN mapping function and the protocol-based VLAN function are mutually exclusive on the same port.
l Enabling the VLAN mapping function based on a global VLAN mapping rule for a port also enables the selective QinQ function on the port.
3.2.3 Enabling the VLAN Mapping Function Based on a Port-level VLAN Mapping Rule
Table 3-3 Enable the VLAN mapping function based on a port-level VLAN mapping rule
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Enter Ethernet port view |
interface interface-type interface-number |
— |
|
Define a VLAN mapping rule |
vlan-mapping vlan old-vlan-id remark new-vlan-id |
Required This command also enables the VLAN mapping function for the port. By default, no VLAN mapping rule is defined, and the VLAN mapping function is not enabled on a port. |
& Note:
l A port that is in a link aggregation port group cannot have the VLAN Mapping feature enabled.
l When configuring a VLAN mapping rule, make sure that the mapping relationship between private network VLANs and public network VLANs is one-to-one.
l To modify a VLAN mapping relationship, you need to delete the corresponding VLAN mapping rule and then define a new one.
l The VLAN mapping function based on global VLAN mapping rules is mutually exclusive with the VLAN mapping function based on port-level VLAN mapping rules.
l The VLAN mapping function and the protocol-based VLAN function are mutually exclusive on the same port.
l To use the VLAN mapping function together with the ARP detection function, you need to enable ARP detection in both the initial VLAN and the mapped VLAN. For detailed description of the ARP detection function, refer to the ARP part of the manual.
l You are not allowed to configure both the VLAN mapping function and the IP filtering function on the device. For description of the IP filter function, refer to the DHCP part of the manual.
3.3 VLAN Mapping Configuration Example
3.3.1 Replacing the Private Network VLAN Tag through VLAN Mapping
I. Network requirements
Two customer networks are connected to the public network through Switch A and Switch B. Configure the VLAN mapping function to enable packets to be exchanged between the two networks through the public network VLANs.
l Switch A provides network access for terminal devices in VLAN 100 and VLAN 200 through Ethernet 1/0/11 and Ethernet 1/0/12. On the other side of the public network, Switch B provides network access for servers in VLAN 100 and VLAN 200 through Ethernet 1/0/15 and Ethernet 1/0/16.
l Ethernet 1/0/10 of Switch A connects the customer network to the public network, and so does Ethernet 1/0/17 of Switch B.
l It is required that packets of VLAN 100 and the packets of VLAN 200 of the two customer networks are transmitted in the public network carrying the tag of VLAN 500 and the tag of VLAN 600.
II. Network diagram
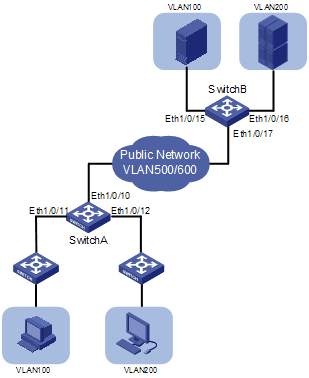
Figure 3-3 Network diagram for VLAN mapping configuration
III. Configuration procedure
& Note:
In this example, the VLAN mapping function is enabled based on port-level VLAN mapping rules.
# Create customer VLANs VLAN 100 and VLAN 200 and service VLANs VLAN 500 and VLAN 600 on Switch A.
<SwitchA> system-view
[SwitchA] vlan 100
[SwitchA-vlan100] quit
[SwitchA] vlan 200
[SwitchA-vlan200] quit
[SwitchA] vlan 500
[SwitchA-vlan500] quit
[SwitchA] vlan 600
[SwitchA-vlan600] quit
# As Ethernet 1/0/11 of Switch A not only receives packets of the customer VLAN but also forward packets from the service provider network, you need to configure the port as a trunk port or hybrid port. In the following part, configure Ethernet 1/0/11 as a hybrid port and configure the port to permit the packets of VLAN 100 and VLAN 500 to pass through with VLAN tags.
[SwitchA] interface Ethernet 1/0/11
[SwitchA-Ethernet1/0/11] port link-type hybrid
[SwitchA-Ethernet1/0/11] port hybrid vlan 100 tagged
[SwitchA-Ethernet1/0/11] port hybrid vlan 500 tagged
[SwitchA-Ethernet1/0/11] quit
# Add Ethernet 1/0/12 to VLAN 200 and VLAN 600 in the same way.
[SwitchA] interface Ethernet 1/0/12
[SwitchA-Ethernet1/0/12] port link-type hybrid
[SwitchA-Ethernet1/0/12] port hybrid vlan 200 tagged
[SwitchA-Ethernet1/0/12] port hybrid vlan 600 tagged
[SwitchA-Ethernet1/0/12] quit
& Note:
l If you configure Ethernet 1/0/11 and Ethernet 1/0/12 as trunk ports, you also need to add the two ports to the corresponding customer VLANs and service VLANs.
l In the above example, VLAN 1 is the default VLAN and permitted to pass through all the ports by default. If you have changed default VLAN of a port, you need to configure the port to permit the default VLAN to pass through.
# Configure Ethernet 1/0/10 of Switch A as a trunk port capable of transmitting packets of VLAN 500 and VLAN 600.
[SwitchA] interface Ethernet 1/0/10
[SwitchA-Ethernet1/0/10] port link-type trunk
[SwitchA-Ethernet1/0/10] port trunk permit vlan 500 600
[SwitchA-Ethernet1/0/10] quit
# Define a VLAN mapping rule on Ethernet 1/0/11 that maps VLAN 100 to VLAN 500 and enable the VLAN mapping function on Ethernet 1/0/11.
[SwitchA] interface Ethernet 1/0/11
[SwitchA-Ethernet1/0/11] vlan-mapping vlan 100 remark 500
[SwitchA-Ethernet1/0/11] quit
# Define a VLAN mapping rule on Ethernet 1/0/12 that maps VLAN 200 to VLAN 600 and enable the VLAN mapping function on Ethernet 1/0/12.
[SwitchA] interface Ethernet 1/0/12
[SwitchA-Ethernet1/0/12] vlan-mapping vlan 200 remark 600
After the above configurations, Switch A maps the VLAN tags of the customer packets received through Ethernet 1/0/11 and Ethernet 1/0/12 to the corresponding public network VLAN tags as defined in the VLAN mapping rules and then forwards the packet to public network for transmission. In order that the customer packets can be exchanged properly between the two customer networks, you need to define the same VLAN mapping rules on Switch B on the other end of the public network. The detailed configuration procedure is similar to that of Switch A and thus is omitted here.
Chapter 4 BPDU Tunnel Configuration
When configuring BPDU tunnel, go to these sections for information you are interested in:
l Displaying and Maintaining BPDU Tunnel Configuration
l BPDU Tunnel Configuration Example
4.1 BPDU Tunnel Overview
4.1.1 Introduction to the BPDU Tunnel Feature
Normally, Layer 2 protocols are needed in a LAN for network topology maintenance and management. For example, spanning tree protocol (STP) is used for maintaining spanning trees and preventing loops. Huawei group management protocol (HGMP) is used for managing network topology and devices in a network.
When multiple branch networks of an organization are connected together through a public network, you can combine the corresponding network nodes into one so as to maintain the branch networks as a whole. This requires the packets of some of the user’s Layer 2 protocol packets be transmitted across the provider’s network without getting involved in the computation of the public network.
The BPDU Tunnel feature is designed to address the above requirements. It enables some Layer 2 protocol packets of private networks to be transmitted along tunnels established in the public network.
4.1.2 BPDU Tunnel Fundamental
I. Layer 2 protocol packet identification
Different from the processing of data packets, a Layer 2 protocol packet is classified first when it reaches a network device. A Layer 2 protocol packet conforming to IEEE standards carries a special destination MAC address (for example, the destination MAC address of an STP protocol packet is 0180-c200-0000) and contains a type field. Some proprietary protocols adopt the same packet structure, where a private MAC address is used to identify the corresponding proprietary protocol, and the type field is used to identify the specific protocol type.
II. Transmitting BPDU packets transparently
As shown in Figure 4-1, the network on the top is the service provider network, and the one on the bottom is a customer network. The service provider network contains edge devices connecting the customer network to the service provider network. The customer network contains Network A and Network B. You can make the BPDU packets of the customer network to be transmitted in the service provider network transparently by enabling the BPDU tunnel feature on the edge devices at both ends of the service provider network.
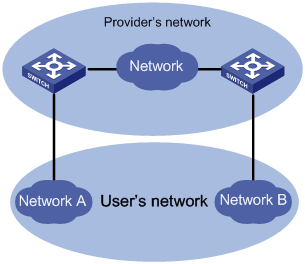
Figure 4-1 BPDU Tunnel network hierarchy
l When a BPDU packet coming from a customer network reaches an edge device in the service provider network, the edge device changes the destination MAC address carried in the packet from a protocol-specific MAC address to a private multicast MAC address, which can be defined using a command. A packet with this multicast address as its destination address is called a tunnel packet. In the service provider network, the tunnel packet can be forwarded as a normal data packet.
l Before the device in the service provider network forwards the packet to the destination customer network, the edge device will identify the tunnel packet, determine the packet type based on the type field in the packet, restore its destination MAC address to the original protocol-specific MAC address and then forward the packet to the access device on the user side. This ensures the packet to be forwarded is consistent with the packet before entering the tunnel. So, a tunnel here acts as a local link for user devices. It enables Layer 2 protocols to run on a virtual local network.
Figure 4-2 and Figure 4-3 show the structure of a BPDU packet before and after it enter a BPDU tunnel.
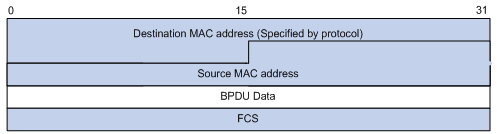
Figure 4-2 The structure of a BPDU packet before it enters a BPDU tunnel
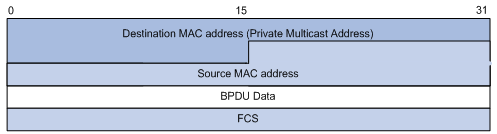
Figure 4-3 The structure of a BPDU packet after it enters a BPDU tunnel
![]() Caution:
Caution:
To prevent the devices in the service provider network from processing the tunnel packets as other protocol packets, the MAC address of a tunnel packet must be a multicast address uniquely assigned to the BPDU tunnel in the service provider network.
4.2 BPDU Tunnel Configuration
You can establish BPDU tunnels between S3100 series Ethernet switches for the packets of the following protocols:
l LACP (link aggregation control protocol)
l STP (spanning tree protocol)
l HGMP-related protocols, including: NDP (neighbor discovery protocol), NTDP (neighbor topology discovery protocol), cluster MRC (cluster member remote control), and HABP (Huawei authentication bypass protocol)
l Proprietary protocols of other vendors, including CDP (CISCO discovery protocol), PAGP (port aggregation protocol), PVST (per-VLAN spanning tree), VTP (VLAN trunk protocol), and UDLD (uni-directional link discovery)
4.2.1 Configuration Prerequisites
The edge devices can communicate with the user devices properly.
4.2.2 Configuring a BPDU Tunnel
Follow these steps to configure a BPDU tunnel:
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Configure a private multicast MAC address for packets transmitted along the tunnel |
bpdu-tunnel tunnel-dmac mac-address |
Optional By default, the destination MAC address for packets transmitted along a BPDU tunnel is 010f-e200-0003. |
|
Enter Ethernet port view |
interface interface-type interface-number |
— |
|
Enable BPDU tunnel for packets of a specific protocol |
bpdu-tunnel protocol-type |
Required By default, BPDU tunnel is disabled for packets of any protocol. |
& Note:
l If BPDU tunnel transparent transmission is enabled for packets of a protocol, the protocol cannot be enabled on the port. For example, if you execute the bpdu-tunnel lacp command, the lacp enable command cannot be executed on the port.
l The bpdu-tunnel stp command is mutually exclusive with the vlan-vpn tunnel command. Refer to MSTP part of this manual for details.
l To enable BPDU tunnel transmission for PAGP packets, LACP packets and UDLD packets, make sure that the links the service provider provides are point-to-point links. Otherwise, these protocols cannot operate properly.
l Because the NDP configuration and NTDP configuration cannot be synchronized to ports in an aggregation group, make sure that NDP and NTDP are not enabled on any port in an aggregation group before enabling the service provider network to use aggregation group to transmit HGMP packets through BPDU tunnels.
l The bpdu-tunnel cdp command is mutually exclusive with the voice vlan legacy command. Refer to Voice VLAN part of this manual for details.
l If a BPDU-tunnel-enabled port receives a tunnel packet from the customer’s network, errors occur in the network and the tunnel packet will be dropped directly.
4.3 Displaying and Maintaining BPDU Tunnel Configuration
|
To do... |
Use the command... |
Remarks |
|
Display the private multicast MAC address used by the tunnel packets |
display bpdu-tunnel |
Available in any view |
4.4 BPDU Tunnel Configuration Example
4.4.1 Transmitting STP Packets Through a Tunnel
I. Network requirements
l Customer1 and Customer2 are devices operating in a customer network; Provider1 and Provider2 are edge devices operating in the service provider network. The two devices receive data from the customer network by using Ethernet1/0/1 and Ethernet1/0/2 respectively.
l Provider1 and Provider2 are connected through trunk links, which permit packets of all VLANs.
l Enable the service provider network to transmit STP packets of the customer network through BPDU tunnel. The destination MAC address for tunnel packets is 010f-e233-8b22.
l Enable the VLAN-VPN feature for the service provider network, and enable the service provider network to use VLAN 100 to transmit data packets of the customer network.
II. Network diagram
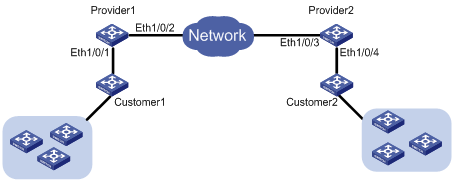
Figure 4-4 Network diagram for BPDU Tunnel configuration
III. Configuration procedure
1) Configure Provide1.
# Disable STP on Ethernet1/0/1.
<Sysname> system-view
[Sysname] interface Ethernet 1/0/1
[Sysname-Ethernet1/0/1] stp disable
# Enable the BPDU tunnel feature for STP BPDUs on Ethernet1/0/1.
[Sysname-Ethernet1/0/1] bpdu-tunnel stp
# Enable the VLAN-VPN feature on Ethernet1/0/1 and use VLAN 100 to transmit user data packets through BPDU tunnels.
[Sysname-Ethernet1/0/1] port access vlan 100
[Sysname-Ethernet1/0/1] vlan-vpn enable
# Configure the destination MAC address for protocol packets transmitted through the BPDU tunnel.
[Sysname-Ethernet1/0/1] quit
[Sysname] bpdu-tunnel tunnel-dmac 010f-e233-8b22
# Configure Ethernet1/0/2 as a trunk port that permits packets of all VLANs.
[Sysname] interface Ethernet 1/0/2
[Sysname-Ethernet1/0/2] port link-type trunk
[Sysname-Ethernet1/0/2] port trunk permit vlan all
2) Configure Provider2.
# Disable STP on Ethernet1/0/4.
<Sysname> system-view
[Sysname] interface Ethernet 1/0/4
[Sysname-Ethernet1/0/4] stp disable
# Enable BPDU tunnel for STP packets.
[Sysname-Ethernet1/0/4] bpdu-tunnel stp
# Enable VLAN-VPN and use VLAN 100 to transmit user data packets through BPDU tunnels.
[Sysname-Ethernet1/0/4] port access vlan 100
[Sysname-Ethernet1/0/4] vlan-vpn enable
# Configure the destination MAC address for the packets transmitted in the tunnel.
[Sysname-Ethernet1/0/4] quit
[Sysname] bpdu-tunnel tunnel-dmac 010f-e233-8b22
# Configure Ethernet1/0/3 as a trunk port that permits packets of all VLANs.
[Sysname] interface Ethernet 1/0/3
[Sysname-Ethernet1/0/3] port link-type trunk
[Sysname-Ethernet1/0/3] port trunk permit vlan all
