- Table of Contents
-
- H3C S3100 Series Ethernet Switches Operation Manual (For Soliton)(V1.02)
- 00-1Cover
- 00-2Product Overview
- 01-CLI Operation
- 02-Login Operation
- 03-Configuration File Management Operation
- 04-VLAN Operation
- 05-Management VLAN Operation
- 06-IP Address-IP Performance Operation
- 07-Voice VLAN Operation
- 08-GVRP Operation
- 09-Port Basic Configuration Operation
- 10-Link Aggregation Operation
- 11-Port Isolation Operation
- 12-Port Security-Port Binding Operation
- 13-DLDP Operation
- 14-MAC Address Table Management Operation
- 15-MSTP Operation
- 16-Multicast Operation
- 17-802.1x-System Guard Operation
- 18-AAA Operation
- 19-MAC Address Authentication Operation
- 20-ARP Operation
- 21-DHCP Operation
- 22-ACL Operation
- 23-QoS-QoS Profile Operation
- 24-Mirroring Operation
- 25-Stack-Cluster Operation
- 26-SNMP-RMON Operation
- 27-NTP Operation
- 28-SSH Operation
- 29-File System Management Operation
- 30-FTP-SFTP-TFTP Operation
- 31-Information Center Operation
- 32-System Maintenance and Debugging Operation
- 33-VLAN-VPN Operation
- 34-HWPing Operation
- 35-IPv6 Management Operation
- 36-DNS Operation
- 37-Smart Link-Monitor Link Operation
- 38-Appendix
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 23-QoS-QoS Profile Operation | 403.54 KB |
Table of Contents
1.1.2 Traditional Packet Forwarding Service
1.1.3 New Applications and New Requirements
1.1.4 Major Traffic Control Techniques
1.2 QoS Supported by the S3100 Series Ethernet Switches
1.3 Introduction to QoS Features
1.3.4 Traffic Policing and Traffic Shaping
1.3.8 Flow-Based Traffic Accounting
1.4.1 Configuring Priority Trust Mode.
1.4.2 Configuring Priority Mapping
1.4.4 Configuring Traffic Policing
1.4.5 Configuring Traffic Shaping
1.4.6 Configuring Port Rate Limiting
1.4.7 Configuring Traffic Redirecting.
1.4.8 Configuring Queue Scheduling
1.4.9 Configuring Traffic Accounting
1.4.10 Enabling the Burst Function
1.4.11 Configuring Traffic Mirroring
1.5.1 Configuration Example of Traffic Policing
Chapter 2 QoS Profile Configuration
2.1.1 Introduction to QoS Profile
2.1.2 QoS Profile Application Mode
2.2.1 Configuring a QoS Profile
2.2.3 Displaying QoS Profile Configuration
2.3.1 QoS Profile Configuration Example
Chapter 1 QoS Configuration
1.1 Overview
1.1.1 Introduction to QoS
Quality of Service (QoS) is a concept concerning service demand and supply. It reflects the ability to meet customer needs. Generally, QoS does not focus on grading services precisely, but on improving services under certain conditions.
In an internet, QoS refers to the ability of the network to forward packets. The evaluation on QoS of a network can be based on different aspects because the network may provide various services. Generally, QoS refers to the ability to provide improved service by addressing the essential issues such as delay, jitter, and packet loss ratio in the packet forwarding process.
1.1.2 Traditional Packet Forwarding Service
In traditional IP networks, packets are treated equally. That is, the FIFO (first in first out) policy is adopted for packet processing. Network resources required for packet forwarding is determined by the order in which packets arrive. All the packets share the resources of the network. Network resources available to the packets completely depend on the time they arrive. This service policy is known as Best-effort, which delivers the packets to their destination with the best effort, with no assurance and guarantee for delivery delay, jitter, packet loss ratio, reliability, and so on.
The traditional Best-Effort service policy is only suitable for applications insensitive to bandwidth and delay, such as WWW, file transfer and E-mail.
1.1.3 New Applications and New Requirements
With the expansion of computer network, more and more networks become part of the Internet. The Internet gains rapid development in terms of scale, coverage and user quantities. More and more users use the Internet as a platform for their services and for data transmission.
Besides the traditional applications such as WWW, E-mail, and FTP, new services are developed on the Internet, such as tele-education, telemedicine, video telephone, videoconference and Video-on-Demand (VoD). Enterprise users expect to connect their regional branches together using VPN techniques for coping with daily business, for instance, accessing databases or manage remote equipments through Telnet.
All these new applications have one thing in common, that is, they have special requirements for bandwidth, delay, and jitter. For instance, bandwidth, delay, and jitter are critical for videoconference and VoD. As for other applications, such as transaction processing and Telnet, although bandwidth is not as critical, a too long delay may cause unexpected results. That is, they need to get serviced in time even if congestion occurs.
Newly emerging applications demand higher service performance from IP networks. In addition to simply delivering packets to their destinations, better network services are demanded, such as allocating dedicated bandwidth, reducing packet loss ratio, avoiding congestion, regulating network traffic, and setting priority of the packets. To meet those requirements, the network should be provided with better service capability.
1.1.4 Major Traffic Control Techniques
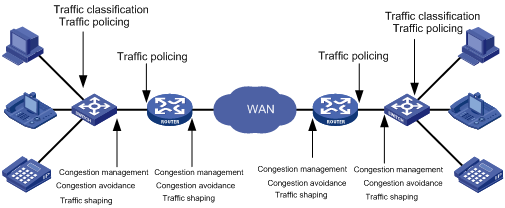
Figure 1-1 End-to-end QoS model
Traffic classification, traffic policing, traffic shaping, congestion management, and congestion avoidance are the foundations for a network to provide differentiated services. Mainly they implement the following functions.
l Traffic classification identifies traffic based on certain matching rules. It is a prerequisite for differentiated services and is usually applied in the inbound direction of a port.
l Traffic policing confines traffic to a specific specification and is usually applied in the inbound direction of a port. You can configure restriction or penalty measures against the exceeding traffic to protect carrier benefits and network resources.
l Traffic shaping adapts output traffic rate usually to the input capability of the receiving device to avoid packet drop and port congestion. Traffic shaping is usually applied in the outbound direction of a port.
l Congestion management handles resource competition during network congestion. Generally, it puts packets into queues first, and then schedules the packets with a certain algorithm. Congestion management is usually applied in the outbound direction of a port.
l Congestion avoidance monitors the use of network resources and drops packets actively when congestion reaches certain degree. It relieves network load by adjusting traffic. Congestion avoidance is usually applied in the outbound direction of a port.
Traffic classification is the basis of all the above-mentioned traffic management technologies. It identifies packets using certain rules and makes differentiated services possible. Traffic policing, traffic shaping, congestion management, and congestion avoidance are methods for implementing network traffic control and network resource management. They are occurrences of differentiated services.
1.2 QoS Supported by the S3100 Series Ethernet Switches
The S3100 series Ethernet switches support the QoS features listed in Table 1-1.
Table 1-1 QoS features supported by the S3100 series Ethernet switches
|
Category |
Features |
Refer to… |
|
Traffic classification |
Incoming traffic classification based on ACLs of the following types: l Basic ACLs l Advanced ACLs l Layer-2 ACLs l IPv6 ACLs |
l For detailed information about ACLs, refer to the ACL module in this manual. l For information about traffic classification, refer to Traffic Classification. |
|
QoS action |
QoS actions for packets matching the specified ACL: l Priority marking l Traffic policing l Traffic redirecting l Traffic accounting l Traffic mirroring |
l For information about priority marking, refer to Priority Marking. l For information about traffic policing, refer to Traffic Policing and Traffic Shaping. l For information about traffic redirecting, refer to Traffic Redirecting. l For information about traffic accounting, refer to Flow-Based Traffic Accounting. l For information about traffic mirroring, refer to Traffic Mirroring. |
|
QoS actions directly configured as required: l Priority trust mode l Traffic shaping l Line rate l Burst |
l For information about priority trust mode, refer to Priority trust mode. l For information about traffic shaping, refer to Traffic Policing and Traffic Shaping. l For information about line rate, refer to Port Rate Limiting. l For information about the burst function, refer to Burst. |
|
|
Congestion management |
SP, WRR, and HQ-WRR queue scheduling algorithms |
For introduction to SP, WRR, and HQ-WRR queue scheduling algorithms, refer to Queue Scheduling. |
1.3 Introduction to QoS Features
1.3.1 Traffic Classification
Traffic here refers to service traffic; that is, all the packets passing the switch.
Traffic classification means identifying packets that conform to certain characteristics according to certain rules. It is the foundation for providing differentiated services.
In traffic classification, the priority bit in the type of service (ToS) field in IP packet header can be used to identify packets of different priorities. The network administrator can also define traffic classification policies to identify packets by the combination of source address, destination address, MAC address, IP protocol or the port number of an application. Normally, traffic classification is done by checking the information carried in packet header. Packet payload is rarely adopted for traffic classification. The identifying rule is unlimited in range. It can be a quintuplet consisting of source address, source port number, protocol number, destination address, and destination port number. It can also be simply a network segment.
1.3.2 Priority Trust Mode
I. Precedence types
1) IP precedence, ToS precedence, and DSCP precedence
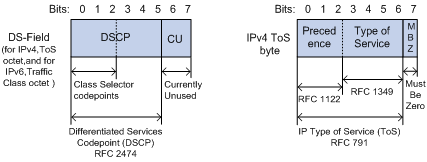
Figure 1-2 DS field and ToS byte
The ToS field in an IP header contains eight bits numbered 0 through 7, among which,
l The first three bits indicate IP precedence in the range 0 to 7.
l Bit 3 to bit 6 indicate ToS precedence in the range of 0 to 15.
l In RFC2474, the ToS field in IP packet header is also known as DS field. The first six bits (bit 0 through bit 5) of the DS field indicate differentiated service codepoint (DSCP) in the range of 0 to 63, and the last two bits (bit 6 and bit 7) are reserved.
Table 1-2 Description on IP Precedence
|
IP Precedence (decimal) |
IP Precedence (binary) |
Description |
|
0 |
000 |
Routine |
|
1 |
001 |
priority |
|
2 |
010 |
immediate |
|
3 |
011 |
flash |
|
4 |
100 |
flash-override |
|
5 |
101 |
critical |
|
6 |
110 |
internet |
|
7 |
111 |
network |
In a network providing differentiated services, traffics are grouped into the following four classes, and packets are processed according to their DSCP values.
l Expedited Forwarding (EF) class: In this class, packets can be forwarded regardless of link share of other traffic. The class is suitable for preferential services with low delay, low packet loss ratio, low jitter, and assured bandwidth (such as virtual leased line);
l Assured forwarding (AF) class: This class is further divided into four subclasses (AF1/2/3/4) and a subclass is further divided into three drop priorities, so the AF service level can be segmented. The QoS rank of the AF class is lower than that of the EF class;
l Class selector (CS) class: This class comes from the IP ToS field and includes eight subclasses;
Table 1-3 Description on DSCP precedence values
|
DSCP value (decimal) |
DSCP value (binary) |
Description |
|
46 |
101110 |
ef |
|
10 |
001010 |
af11 |
|
12 |
001100 |
af12 |
|
14 |
001110 |
af13 |
|
18 |
010010 |
af21 |
|
20 |
010100 |
af22 |
|
22 |
010110 |
af23 |
|
26 |
011010 |
af31 |
|
28 |
011100 |
af32 |
|
30 |
011110 |
af33 |
|
34 |
100010 |
af41 |
|
36 |
100100 |
af42 |
|
38 |
100110 |
af43 |
|
8 |
001000 |
cs1 |
|
16 |
010000 |
cs2 |
|
24 |
011000 |
cs3 |
|
32 |
100000 |
cs4 |
|
40 |
101000 |
cs5 |
|
48 |
110000 |
cs6 |
|
56 |
111000 |
cs7 |
|
0 |
000000 |
be (default) |
802.1p priority lies in Layer 2 packet headers and is applicable to occasions where the Layer 3 packet header does not need analysis but QoS must be assured at Layer 2.
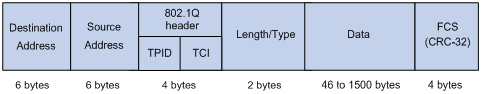
Figure 1-3 An Ethernet frame with an 802.1Q tag header
As shown in the figure above, each host supporting 802.1Q protocol adds a 4-byte 802.1Q tag header after the source address of the former Ethernet frame header when sending packets.
The 4-byte 802.1Q tag header consists of the tag protocol identifier (TPID, two bytes in length), whose value is 0x8100, and the tag control information (TCI, two bytes in length). Figure 1-4 describes the detailed contents of an 802.1Q tag header.
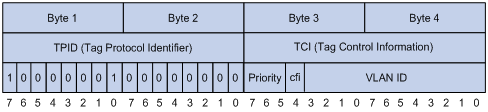
In the figure above, the priority field (three bits in length) in TCI is 802.1p priority (also known as CoS precedence), which ranges from 0 to 7.
Table 1-4 Description on 802.1p priority
|
802.1p priority (decimal) |
802.1p priority (binary) |
Description |
|
0 |
000 |
best-effort |
|
1 |
001 |
background |
|
2 |
010 |
spare |
|
3 |
011 |
excellent-effort |
|
4 |
100 |
controlled-load |
|
5 |
101 |
video |
|
6 |
110 |
voice |
|
7 |
111 |
network-management |
The precedence is called 802.1p priority because the related applications of this precedence are defined in detail in the 802.1p specifications.
3) Local precedence
Local precedence is a locally significant precedence that the device assigns to a packet. A local precedence value corresponds to one of the eight hardware output queues. Packets with the highest local precedence are processed preferentially. As local precedence is used only for internal queuing, a packet does not carry it after leaving the queue.
II. Priority trust mode
After a packet enters a switch, the switch sets the 802.1p priority and local precedence for the packet according to its own capability and the corresponding rules.
1) For a packet carrying no 802.1q tag
When a packet carrying no 802.1q tag reaches a port, the switch replaces the 802.1p priority of the received packet with the port priority, searches for the local precedence corresponding to the port priority of the receiving port in the 802.1p-to-local precedence mapping table, and assigns the local precedence to the packet.
2) For an 802.1q tagged packet
For incoming 802.1q tagged packets, you can configure the switch to trust packet priority with the priority trust command or to trust port priority with the undo priority trust command. By default, the S3100 series switches trust port priority.
l Trusting port priority
In this mode, the switch replaces the 802.1p priority of the received packet with the port priority, searches for the local precedence corresponding to the port priority of the receiving port in the 802.1p-to-local precedence mapping table, and assigns the local precedence to the packet.
l Trusting packet priority
After configuring to trust packet priority, you can specify the trusted priority type, which can be 802.1p priority or DSCP precedence. With trusting packet priority enabled, the switch trusts the 802.1p priority of received packets.
Table 1-5 describes the three trusted packet priority types.
Table 1-5 Description on the two trusted packet priority types
|
Trusted priority type |
Description |
|
802.1p priority |
The switch searches for the local precedence corresponding to the 802.1p priority of the packet in the 802.1p-to-local precedence mapping table and assigns the local precedence to the packet. |
|
DSCP precedence |
The switch searches for the local precedence corresponding to the DSCP value of the packet in the DSCP-to-local precedence mapping table and assigns the local precedence to the packet. |
The S3100 series switches provide 802.1p-to-local-precedence and DSCP-to-local-precedence mapping tables for priority mapping. Table 1-6 through Table 1-7 list the default settings of these tables. You can configure these default priority mapping tables at the CLI. For detailed configuration, refer to Configuring Priority Trust Mode.
Table 1-6 CoS-precedence-to-local-precedence mapping table
|
CoS |
Local precedence |
|
0 |
1 |
|
1 |
0 |
|
2 |
0 |
|
3 |
1 |
|
4 |
2 |
|
5 |
2 |
|
6 |
3 |
|
7 |
3 |
Table 1-7 DSCP-precedence-to-local-precedence mapping table
|
DSCP |
Local precedence |
|
0 to 15 |
0 |
|
16 to 31 |
1 |
|
32 to 47 |
2 |
|
48 to 63 |
3 |
1.3.3 Priority Marking
l If 802.1p priority marking is configured, the traffic will be mapped to the local precedence corresponding to the re-marked 802.1p priority and assigned to the output queue corresponding to the local precedence.
l If DSCP marking is configured, the traffic will be marked with new DSCP precedence.
1.3.4 Traffic Policing and Traffic Shaping
The network will be made more congested by plenty of continuous burst packets if the traffic of each user is not limited. The traffic of each user must be limited in order to make better use of the limited network resources and provide better service for more users. For example, a traffic flow can be limited to get only its committed resources during a time period to avoid network congestion caused by excessive bursts.
Traffic policing and traffic shaping is each a kind of traffic control policy used to limit the traffic and the resource occupied by supervising the traffic. The regulation policy is implemented according to the evaluation result on the premise of knowing whether the traffic exceeds the specification when traffic policing or traffic shaping is performed. Normally, token bucket is used for traffic evaluation.
I. Token bucket
The token bucket can be considered as a container with a certain capacity to hold tokens. The system puts tokens into the bucket at the set rate. When the token bucket is full, the extra tokens will overflow and the number of tokens in the bucket stops increasing.
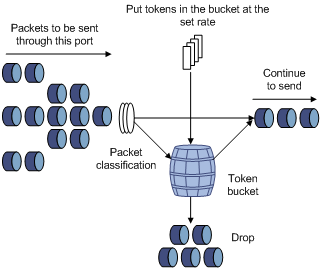
Figure 1-5 Evaluate the traffic with the token bucket
II. Evaluating the traffic with the token bucket
When token bucket is used for traffic evaluation, the number of the tokens in the token bucket determines the amount of the packets that can be forwarded. If the number of tokens in the bucket is enough to forward the packets, the traffic is conforming to the specification; otherwise, the traffic is nonconforming or excess.
Parameters concerning token bucket include:
l Average rate: The rate at which tokens are put into the bucket, namely, the permitted average rate of the traffic. It is generally set to committed information rate (CIR).
l Burst size: The capacity of the token bucket, namely, the maximum traffic size that is permitted in each burst. It is generally set to committed burst size (CBS). The set burst size must be greater than the maximum packet length.
One evaluation is performed on each arriving packet. In each evaluation, if the number of tokens in the bucket is enough, the traffic is conforming to the specification and you must take away some tokens whose number is corresponding to the packet forwarding authority; if the number of tokens in the bucket is not enough, it means that too many tokens have been used and the traffic is excess.
III. Traffic policing
The typical application of traffic policing is to supervise specific traffic into the network and limit it to a reasonable range, or to "discipline" the extra traffic. In this way, the network resources and the interests of the operators are protected. For example, you can limit HTTP packets to be within 50% of the network bandwidth. If the traffic of a certain connection is excess, traffic policing can choose to drop the packets or to reset the priority of the packets.
Traffic policing is widely used in policing the traffic into the network of internet service providers (ISPs). Traffic policing can identify the policed traffic and perform pre-defined policing actions based on different evaluation results. These actions include:
l Discarding the nonconforming packets.
l Forwarding the conforming packets or nonconforming packets.
l Marking the conforming packets with 802.1p precedence and then forwarding the packets.
l Marking the conforming packets or nonconforming packets with DSCP precedence and forwarding the packets.
IV. Traffic shaping
Traffic shaping is a measure to regulate the output rate of traffic actively. Its typical application is to control local traffic output based on the traffic policing indexes of downstream network nodes.
The major difference between traffic shaping and traffic policing is that the packets to be dropped in traffic policing are cached in traffic shaping——usually in buffers or queues, as shown in Figure 1-6. When there are enough tokens in the token bucket, the cached packets are sent out evenly. Another difference between traffic policing and traffic shaping is that traffic shaping may increase the delay while traffic policing hardly increases the delay.
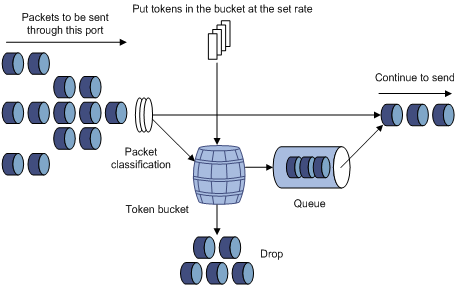
Figure 1-6 Diagram for traffic shaping
For example, if the device A sends packets to the device B. The device B will perform traffic policing on packets from the device A to drop the packets beyond the specification.
In order to avoid meaningless packet loss, you can perform traffic shaping on the packets on the egress of the device A and cache the packets beyond the traffic policing specification in the device A. When the next packets can be sent, the packets cached in the buffer queues will be taken out and sent. In this way, all the packets sent to the device B conforms to the traffic specification of the device B.
1.3.5 Port Rate Limiting
Port rate limiting refers to limiting the total rate of inbound or outbound packets on a port.
Port rate limiting can be implemented through token buckets. That is, if you perform port rate limiting configuration for a port, the token bucket determines the way to process the packets to be sent by this port or packets reaching the port. Packets can be sent or received if there are enough tokens in the token bucket; otherwise, they will be dropped.
Compared to traffic policing, port rate limiting applies to all the packets passing a port. It is a simpler solution if you want to limit the rate of all the packets passing a port.
1.3.6 Traffic Redirecting
Traffic redirecting identifies traffic using ACLs and redirects the matched packets to specific ports. By traffic redirecting, you can change the way in which a packet is forwarded to achieve specific purposes.
1.3.7 Queue Scheduling
When the network is congested, the problem that many packets compete for resources must be solved, usually through queue scheduling.
1) SP queuing
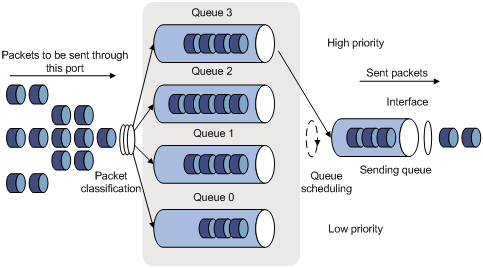
Figure 1-7 Diagram for SP queuing
SP queue-scheduling algorithm is specially designed for critical service applications. An important feature of critical services is that they demand preferential service in congestion in order to reduce the response delay. Assume that there are four output queues on the port and the preferential queue classifies the four output queues on the port into four classes, which are queue 3, queue 2, queue 1, and queue 0. Their priorities decrease in order.
In queue scheduling, SP sends packets in the queue with higher priority strictly following the priority order from high to low. When the queue with higher priority is empty, packets in the queue with lower priority are sent. You can put critical service packets into the queues with higher priority and put non-critical service (such as e-mail) packets into the queues with lower priority. In this case, critical service packets are sent preferentially and non-critical service packets are sent when critical service groups are not sent.
2) WRR queuing
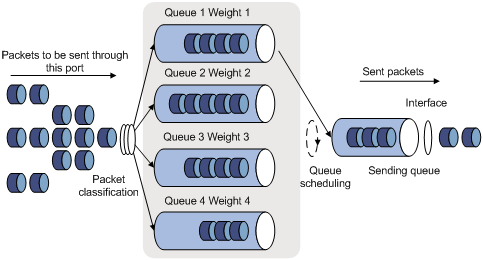
Figure 1-8 Diagram for WRR queuing
WRR queue-scheduling algorithm schedules all the queues in turn and every queue can be assured of a certain service time. Assume there are four output queues on a port. WRR configures a weight value for each queue, which is w3, w2, w1, and w0 for queue 3 through queue 0. The weight value indicates the proportion of obtaining resources. On a 100 M port, configure the weight value of WRR queue-scheduling algorithm to 5, 3, 1, and 1 (corresponding to w3, w2, w1, and w0 in order). In this way, the queue with the lowest priority can get 10 Mbps bandwidth (100-Mbps × 1/ (5 + 3 + 1 + 1)) at least, and the disadvantage of SP queue-scheduling that the packets in queues with lower priority may not get service for a long time is avoided. Another advantage of WRR queue is that: though the queues are scheduled in order, the service time for each queue is not fixed; that is to say, if a queue is empty, the next queue will be scheduled. In this way, the bandwidth resources are made full use.
3) HQ-WRR queuing
HQ-WRR is an improvement over WRR. Assume there are four priority queues on a port and queue 3 allocated with the highest priority, the switch will ensure that this queue get served first and will perform round-robin scheduling to the other three queues when the traffic has exceeded the bandwidth capacity of a port.
1.3.8 Flow-Based Traffic Accounting
The function of traffic-based traffic accounting is to use ACL rules in traffic classification and perform traffic accounting on the packets matching the ACL rules. You can get the statistics of the packets you are interested in through this function.
1.3.9 Burst
The Burst function can provide better packet cache function and traffic forwarding performance. It is suitable for networks where
l Large amount of broadcast/multicast packets and large burst traffic exist.
l Packets of high-rate links are forwarded to low-rate links or packets of multiple links with the equal rates are forwarded to a single link that is of the same rate as that of the incoming links.
Although the burst function helps reduce the packet loss ratio and improve packet processing capability in the networks mentioned above, it may affect QoS performance. So, use this function with caution.
1.3.10 Traffic Mirroring
Traffic mirroring identifies traffic using ACLs and duplicates the matched packets to the destination port. For information about port mirroring, refer to the Mirroring module of this manual.
1.4 QoS Configuration
Table 1-8 QoS configuration tasks
|
Task |
Remarks |
|
Optional |
|
|
Optional |
|
|
Optional |
|
|
Optional |
|
|
Optional |
|
|
Optional |
|
|
Optional |
|
|
Optional |
|
|
Optional |
|
|
Optional |
|
|
Optional |
|
|
Optional |
1.4.1 Configuring Priority Trust Mode
The switch provides the following two priority trust modes:
l Trusting port priority
By default, the S3100 series trust port priority.
l Trusting packet priority
You can configure the switch to trust the 802.1p priority or DSCP precedence of packets. If no trusted priority type is specified, the switch trusts the 802.1p priority of received packets.
For detailed information about priority trust mode, refer to Priority trust mode.
I. Configuration prerequisites
The priority trust mode to be configured is determined.
II. Configuration procedure
You can configure to trust port priority or packet priority. Table 1-9 shows the detailed configuration procedure.
Table 1-9 Configure priority trust mode
|
Operation |
Command |
Description |
||
|
Enter system view |
system-view |
— |
||
|
Configure to trust port priority |
Configure to trust port priority |
undo priority trust |
Optional By default, the S3100 series switches trust port priority. |
Use either approach |
|
Enter Ethernet port view |
interface interface-type interface-number |
— |
||
|
Configure the port priority |
priority priority-level |
Optional By default, the port priority is 0. |
||
|
Exit to system view |
quit |
— |
||
|
Configure to trust packet priority |
Configure to trust packet priority |
priority trust |
Required By default, the S3100 series switches trust port priority. l If you configure to trust packet priority without specifying the trusted priority type, the switch trusts the 802.1p priority of the received packets. l On the S3100 series switches, to configure to trust DSCP precedence of packets, you should configure the priority trust command first and then use the priority-trust command to specify the DSCP precedence. |
|
|
Specify the trusted priority type |
priority-trust { cos | dscp } |
Required If you configure to trust packet priority without specifying the trusted priority type, the switch trusts the 802.1p (CoS) priority of the received packets. |
||
III. Configuration examples
# Configure to trust port priority and set the priority of Ethernet 1/0/1 to 7.
<Sysname> system-view
[Sysname] undo priority trust
[Sysname] interface Ethernet 1/0/1
[Sysname-Ethernet1/0/1] priority 7
# Configure to trust the DSCP precedence of the received packets.
<Sysname> system-view
[Sysname] priority trust
[Sysname] priority-trust dscp
# Configure to trust the 802.1p priority of the received packets.
Approach I:
<Sysname> system-view
[Sysname] priority trust
Approach II:
<Sysname> system-view
[Sysname] priority-trust cos
1.4.2 Configuring Priority Mapping
You can modify the CoS-precedence-to-local-precedence and DSCP-precedence-to-local-precedence mapping tables as required to mark packets with different priorities.
I. Configuration prerequisites
The target CoS-precedence-to-local-precedence and DSCP-precedence-to-local-precedence mapping tables are determined.
II. Configuration procedure
Table 1-10 Configure CoS-precedence-to-local-precedence mapping table
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Configure CoS-precedence-to-local-precedence mapping table |
qos cos-local-precedence-map cos0-map-local-prec cos1-map-local-prec cos2-map-local-prec cos3-map-local-prec cos4-map-local-prec cos5-map-local-prec cos6-map-local-prec cos7-map-local-prec |
Required |
Table 1-11 Configure DSCP-precedence-to-local-precedence mapping table
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Configure DSCP-precedence-to-local-precedence mapping table |
qos dscp-local-precedence-map dscp-list : local-precedence |
Required |
III. Configuration example
l Configure the CoS-precedence-to-local-precedence mapping relationship as follows: 0 to 0, 1 to 0, 2 to 1, 3 to 1, 4 to 2, 5 to 2, 6 to 3, and 7 to 3.
l Display the configuration.
Configuration procedure:
<Sysname> system-view
[Sysname] qos cos-local-precedence-map 0 0 1 1 2 2 3 3
[Sysname] display qos cos-local-precedence-map
cos-local-precedence-map:
cos(802.1p) : 0 1 2 3 4 5 6 7
local precedence(queue) : 0 0 1 1 2 2 3 3
1.4.3 Marking Packet Priority
Refer to section Priority Marking for information about marking packet priority.
Marking packet priority can be implemented in the following two ways:
l Through traffic policing
When configuring traffic policing, you can define the action of marking the 802.1p priority and DSCP precedence for packets exceeding the traffic specification. Refer to section Configuring Traffic Policing.
l Through the traffic-priority command
You can use the traffic priority command to mark the 802.1p priority, local precedence and DSCP precedence of the packets.
I. Configuration prerequisites
The following items are defined or determined before the configuration:
l The ACL rules used for traffic classification are specified. Refer to the ACL module of this manual for related information.
l The type and value of the precedence to be marked for the packets matching the ACL rules are determined.
II. Configuration procedure
You can mark priority for all the packets matching specific ACL rules, or for packets that match specific ACL rules and are of a VLAN, of a port group, or pass a port.
Table 1-12 Mark the priority for the packets matching specific ACL rules
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Mark the priorities for packets matching specific ACL rules |
traffic-priority inbound acl-rule { dscp dscp-value | cos cos-value | local-precedence pre-value }* |
Required |
Table 1-13 Mark the priority for packets that are of a VLAN and match specific ACL rules
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Mark the priorities for packets matching specific ACL rules |
traffic-priority vlan vlan-id inbound acl-rule { dscp dscp-value | cos cos-value | local-precedence pre-value }* |
Required |
Table 1-14 Mark the priority for packets that are of a port group and match specific ACL rules
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Enter port group view |
port-group group-id |
— |
|
Mark the priorities for packets matching specific ACL rules |
traffic-priority inbound acl-rule { dscp dscp-value | cos cos-value | local-precedence pre-value }* |
Required |
Table 1-15 Mark the priority for packets passing a port and matching specific ACL rules
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Enter Ethernet port view |
interface interface-type interface-number |
— |
|
Mark the priorities for packets matching specific ACL rules |
traffic-priority inbound acl-rule { dscp dscp-value | cos cos-value | local-precedence pre-value }* |
Required |
& Note:
The priority marking function configured on a VLAN is only applicable to packets tagged with 802.1Q header.
III. Configuration example
l Ethernet 1/0/1 belongs to VLAN 2 and is connected to the 10.1.1.0/24 network segment.
l Mark the DSCP precedence as 56 for the packets from the 10.1.1.0/24 network segment.
1) Method I
<Sysname> system-view
[Sysname] acl number 2000
[Sysname-acl-basic-2000] rule permit source 10.1.1.1 0.0.0.255
[Sysname-acl-basic-2000] quit
[Sysname] interface Ethernet1/0/1
[Sysname-Ethernet1/0/1] traffic-priority inbound ip-group 2000 dscp 56
2) Method II
<Sysname> system-view
[Sysname] acl number 2000
[Sysname-acl-basic-2000] rule permit source 10.1.1.1 0.0.0.255
[Sysname-acl-basic-2000] quit
[Sysname] traffic-priority vlan 2 inbound ip-group 2000 dscp 56
1.4.4 Configuring Traffic Policing
Refer to section Traffic Policing and Traffic Shaping for information about traffic policing. Note that, the target-rate argument is committed information rate (CIR), and the burst-bucket-size argument is committed burst size (CBS).
I. Configuration prerequisites
l The ACL rules used for traffic classification are defined. Refer to the ACL module of this manual for information about defining ACL rules.
l The rate limit for traffic policing, and the actions for the packets exceeding the rate limit are determined.
II. Configuration procedure
You can configure traffic policing for all the packets matching specific ACL rules, or for the packets that match specific ACL rules and are of a VLAN, of a port group, or pass a port.
Table 1-16 Configure traffic policing for all the packets matching specific ACL rules
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Configure traffic policing |
traffic-limit inbound acl-rule target-rate [ burst-bucket burst-bucket-size ] [ conform con-action ] [ exceed exceed-action ] [ meter-statistic ] |
Required By default, traffic policing is disabled. |
|
Clear the traffic policing statistics |
reset traffic-limit inbound acl-rule |
Optional |
Table 1-17 Configure traffic policing for packets that are of a VLAN and match specific ACL rules
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Configure traffic policing |
traffic-limit vlan vlan-id inbound acl-rule target-rate [ burst-bucket burst-bucket-size ] [ conform con-action ] [ exceed exceed-action ] [ meter-statistic ] |
Required By default, traffic policing is disabled. |
|
Clear the traffic policing statistics |
reset traffic-limit vlan vlan-id inbound acl-rule |
Optional |
Table 1-18 Configure traffic policing for packets that are of a port group and match specific ACL rules
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Enter port group view |
port-group group-id |
— |
|
Configure traffic policing |
traffic-limit inbound acl-rule target-rate [ burst-bucket burst-bucket-size ] [ conform con-action ] [ exceed exceed-action ] [ meter-statistic ] |
Required By default, traffic policing is disabled. |
|
Clear the traffic policing statistics |
reset traffic-limit inbound acl-rule |
Optional |
Table 1-19 Configure traffic policing for packets passing a port and matching specific ACL rules
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Enter Ethernet port view |
interface interface-type interface-number |
— |
|
Configure traffic policing |
traffic-limit inbound acl-rule target-rate [ burst-bucket burst-bucket-size ] [ conform con-action ] [ exceed exceed-action ] [ meter-statistic ] |
Required By default, traffic policing is disabled. |
|
Clear the traffic policing statistics |
reset traffic-limit inbound acl-rule |
Optional |
& Note:
Traffic policing configured on a VLAN is only applicable to packets tagged with 802.1Q header.
III. Configuration example
l Ethernet 1/0/1 belongs to VLAN 2 and is connected to the 10.1.1.0/24 network segment
l Perform traffic policing on the packets from the 10.1.1.0/24 network segment, setting the rate to 128 kbps
l Mark the DSCP precedence as 56 for the inbound packets exceeding the rate limit.
1) Method I
<Sysname> system-view
[Sysname] acl number 2000
[Sysname-acl-basic-2000] rule permit source 10.1.1.1 0.0.0.255
[Sysname-acl-basic-2000] quit
[Sysname] interface Ethernet1/0/1
[Sysname-Ethernet1/0/1] traffic-limit inbound ip-group 2000 128 exceed remark-dscp 56
2) Method II
<Sysname> system-view
[Sysname] acl number 2000
[Sysname-acl-basic-2000] rule permit source 10.1.1.1 0.0.0.255
[Sysname-acl-basic-2000] quit
[Sysname] traffic-limit vlan 2 inbound ip-group 2000 128 exceed remark-dscp 56
1.4.5 Configuring Traffic Shaping
Refer to section Traffic Policing and Traffic Shaping for information about traffic shaping.
I. Configuration prerequisites
l The maximum traffic rate and the burst size are determined.
l The port where traffic shaping is to be configured is determined.
II. Configuration procedure
Table 1-20 Configure traffic shaping
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Enter Ethernet port view |
interface interface-type interface-number |
— |
|
Configure traffic shaping |
traffic-shape queue queue-id max-rate burst-size |
Required Traffic shaping is not enabled by default. |
III. Configuration examples
# Perform traffic shaping for all the traffic to be transmitted through Ethernet 1/0/1, with the maximum traffic rate being 640 kbps and the burst size being 16 KB.
<Sysname> system-view
[Sysname] interface Ethernet1/0/1
[Sysname-Ethernet1/0/1] traffic-shape 640 16
1.4.6 Configuring Port Rate Limiting
Refer to section Port Rate Limiting for information about port rate limiting. Note that, the target-rate argument is committed information rate (CIR).
I. Configuration prerequisites
l The port on which port rate limiting configuration is to be performed is determined.
l The target rate and the direction of rate limiting (inbound or outbound) are determined.
II. Configuration procedure
Table 1-21 Configure port rate limiting
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Enter Ethernet port view |
interface interface-type interface-number |
— |
|
Configure port rate limiting |
line-rate { inbound | outbound } target-rate |
Required By default, port rate limiting is disabled. |
III. Configuration example
l Configure port rate limiting for inbound packets on Ethernet 1/0/1.
l The rate limit is 1,024 Kbps
Configuration procedure:
<Sysname> system-view
[Sysname] interface Ethernet 1/0/1
[Sysname-Ethernet1/0/1] line-rate inbound 1024
1.4.7 Configuring Traffic Redirecting
Refer to section Traffic Redirecting for information about traffic redirecting.
I. Configuration prerequisites
l The ACL rules used for traffic classification are defined. Refer to the ACL module of this manual for information about defining ACL rules.
l The traffic redirecting destination is determined.
II. Configuration procedure
You can redirect all the packets matching specific ACL rules, or packets that match specific ACL rules and are of a VLAN, of a port group, or pass a port.
Table 1-22 Redirect all the packets matching specific ACL rules
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Configure traffic redirecting |
traffic-redirect inbound acl-rule { cpu | interface interface-type interface-number } |
Required |
Table 1-23 Redirect packets that are of a VLAN and match specific ACL rules
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Configure traffic redirecting |
traffic-redirect vlan vlan-id inbound acl-rule { cpu | interface interface-type interface-number } |
Required |
Table 1-24 Redirect packets that are of a port group and match specific ACL rules
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Enter port group view |
port-group group-id |
— |
|
Configure traffic redirecting |
traffic-redirect inbound acl-rule { cpu | interface interface-type interface-number } |
Required |
Table 1-25 Redirect packets passing a port and matching specific ACL rules
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Enter Ethernet port view |
interface interface-type interface-number |
— |
|
Configure traffic redirecting |
traffic-redirect inbound acl-rule { cpu | interface interface-type interface-number } |
Required |
& Note:
l The traffic redirecting function configured on a VLAN is only applicable to packets tagged with 802.1Q header.
l Packets redirected to the CPU are not forwarded.
l If the traffic is redirected to a Combo port in down state, the system automatically redirects the traffic to the port corresponding to the Combo port in up state. Refer to the Port Basic Configuration module of this manual for information about Combo ports.
III. Configuration example
l Ethernet 1/0/1 belongs to VLAN 2 and is connected to the 10.1.1.0/24 network segment.
l Redirect all the packets from the 10.1.1.0/24 network segment to Ethernet 1/0/7.
1) Method I
<Sysname> system-view
[Sysname] acl number 2000
[Sysname-acl-basic-2000] rule permit source 10.1.1.1 0.0.0.255
[Sysname-acl-basic-2000] quit
[Sysname] interface Ethernet1/0/1
[Sysname-Ethernet1/0/1] traffic-redirect inbound ip-group 2000 interface Ethernet1/0/7
2) Method II
<Sysname> system-view
[Sysname] acl number 2000
[Sysname-acl-basic-2000] rule permit source 10.1.1.1 0.0.0.255
[Sysname-acl-basic-2000] quit
[Sysname] traffic-redirect vlan 2 inbound ip-group 2000 interface Ethernet1/0/7
1.4.8 Configuring Queue Scheduling
Refer to section Queue Scheduling for information about queue scheduling.
I. Configuration prerequisites
The algorithm for queue scheduling to be used and the related parameters are determined.
II. Configuration procedure
Table 1-26 Configure queue scheduling
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Configure queue scheduling |
queue-scheduler { strict-priority | hq-wrr queue0-weight queue1-weight queue2-weight | wrr queue0-weight queue1-weight queue2-weight queue3-weight } |
Required By default, all the ports adopt the WRR queue scheduling algorithm, with the weights for queues 0 to 3 as 1, 2, 3, and 4. |
III. Configuration example
# Adopt the WRR queue scheduling algorithm, with the weight for queue 0, queue 1, queue 2, and queue 3 as 12, 8, 4, and 1.
Display the configuration information after configuration.
Configuration procedure:
<Sysname> system-view
[Sysname] queue-scheduler wrr 12 8 4 1
[Sysname] display queue-scheduler
Queue scheduling mode: weighted round robin
weight of queue 0: 12
weight of queue 1: 8
weight of queue 2: 4
weight of queue 3: 1
1.4.9 Configuring Traffic Accounting
Refer to section Flow-Based Traffic Accounting for information about traffic accounting.
I. Configuration prerequisites
The ACL rules for traffic classification are defined. Refer to the ACL module of this manual for information about defining ACL rules.
II. Configuration procedure
You can generate traffic statistics or clear traffic statistics on all the packets matching specific ACL rules, or on packets that match specific ACL rules and are of a VLAN, of a port group, or pass a port.
Table 1-27 Generate traffic statistics on all the packets matching specific ACL rules
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Generate the statistics on the packets matching specific ACL rules |
traffic-statistic inbound acl-rule |
Required |
|
Clear the statistics on the packets matching specific ACL rules |
reset traffic-statistic inbound acl-rule |
Optional |
Table 1-28 Generate traffic statistics on packets that are of a VLAN and match specific ACL rules
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Generate the statistics on the packets matching specific ACL rules |
traffic-statistic vlan vlan-id inbound acl-rule |
Required |
|
Clear the statistics on the packets matching specific ACL rules |
reset traffic-statistic vlan vlan-id inbound acl-rule |
Optional |
Table 1-29 Generate traffic statistics on packets that are of a port group and match specific ACL rules
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Enter port group view |
port-group group-id |
— |
|
Generate the statistics on the packets matching specific ACL rules |
traffic-statistic inbound acl-rule |
Required |
|
Clear the statistics on the packets matching specific ACL rules |
reset traffic-statistic inbound acl-rule |
Optional |
Table 1-30 Generate traffic statistics on packets passing a port and matching specific ACL rules
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Enter Ethernet port view |
interface interface-type interface-number |
— |
|
Generate the statistics on the packets matching specific ACL rules |
traffic-statistic inbound acl-rule |
Required |
|
Clear the statistics on the packets matching specific ACL rules |
reset traffic-statistic inbound acl-rule |
Optional |
& Note:
The traffic accounting function configured on a VLAN is only applicable to packets tagged with 802.1Q header.
III. Configuration example
l Ethernet 1/0/1 is connected to the 10.1.1.0/24 network segment.
l Generate statistics on the packets sourced from the 10.1.1.0/24 network segment.
l Clear the statistics.
1) Method I
<Sysname> system-view
[Sysname] acl number 2000
[Sysname-acl-basic-2000] rule permit source 10.1.1.1 0.0.0.255
[Sysname-acl-basic-2000] quit
[Sysname] interface Ethernet1/0/1
[Sysname-Ethernet1/0/1] traffic-statistic inbound ip-group 2000
[Sysname-Ethernet1/0/1] reset traffic-statistic inbound ip-group 2000
2) Method II
<Sysname> system-view
[Sysname] acl number 2000
[Sysname-acl-basic-2000] rule permit source 10.1.1.1 0.0.0.255
[Sysname-acl-basic-2000] quit
[Sysname] traffic-statistic vlan 2 inbound ip-group 2000
[Sysname] reset traffic-statistic vlan 2 inbound ip-group 2000
1.4.10 Enabling the Burst Function
Refer to section Burst for information about the burst function.
I. Configuration prerequisites
The burst function is required.
II. Configuration procedure
Table 1-31 Enable the burst function
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Enable the burst function |
burst-mode enable |
Required By default, the burst function is disabled. |
III. Configuration example
Enable the burst function.
Configuration procedure:
<Sysname> system-view
[Sysname] burst-mode enable
1.4.11 Configuring Traffic Mirroring
Refer to section Traffic Mirroring for information about traffic mirroring.
I. Configuration prerequisites
l The ACL rules for traffic classification are defined. Refer to the ACL module of this manual for information about defining ACL rules.
l The destination mirroring port is determined.
II. Configuration procedure
You can configure traffic mirroring on all the packets matching specific ACL rules, or on packets that match specific ACL rules and are of a VLAN, of a port group, or pass a port.
Table 1-32 Configure traffic mirroring globally
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Enter Ethernet port view of the destination port |
interface interface-type interface-number |
— |
|
Define the current port as the destination port |
monitor-port |
Required |
|
Exit current view |
quit |
— |
|
Reference ACLs for identifying traffic flows and perform traffic mirroring for packets that match. |
mirrored-to inbound acl-rule { cpu | monitor-interface } |
Required |
Table 1-33 Configure traffic mirroring for a VLAN
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Enter Ethernet port view of the destination port |
interface interface-type interface-number |
— |
|
Define the current port as the destination port |
monitor-port |
Required |
|
Exit current view |
quit |
— |
|
Reference ACLs for identifying traffic flows and perform traffic mirroring for packets that match. |
mirrored-to vlan vlan-id inbound acl-rule { cpu | monitor-interface } |
Required |
Table 1-34 Configure traffic mirroring for a port group
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Enter Ethernet port view of the destination port |
interface interface-type interface-number |
— |
|
Define the current port as the destination port |
monitor-port |
Required |
|
Exit current view |
quit |
— |
|
Enter port group view |
port-group group-id |
— |
|
Reference ACLs for identifying traffic flows and perform traffic mirroring for packets that match. |
mirrored-to inbound acl-rule { cpu | monitor-interface } |
Required |
Table 1-35 Configure traffic mirroring for a port
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Enter Ethernet port view of the destination port |
interface interface-type interface-number |
— |
|
Define the current port as the destination port |
monitor-port |
Required |
|
Exit current view |
quit |
— |
|
Enter Ethernet port view of traffic mirroring configuration |
interface interface-type interface-number |
— |
|
Reference ACLs for identifying traffic flows and perform traffic mirroring for packets that match. |
mirrored-to inbound acl-rule { cpu | monitor-interface } |
Required |
& Note:
The traffic mirroring function configured on a VLAN is only applicable to packets tagged with 802.1Q header.
III. Configuration example
Network requirements:
l Ethernet 1/0/1 is connected to the 10.1.1.0/24 network segment.
l Duplicate the packets from network segment 10.1.1.0/24 to the destination mirroring port Ethernet 1/0/4.
1) Method I
<Sysname> system-view
[Sysname] acl number 2000
[Sysname-acl-basic-2000] rule permit source 10.1.1.0 0.0.0.255
[Sysname-acl-basic-2000] quit
[Sysname] interface Ethernet 1/0/4
[Sysname-Ethernet1/0/4] monitor-port
[Sysname-Ethernet1/0/4] quit
[Sysname] interface Ethernet 1/0/1
[Sysname-Ethernet1/0/1] mirrored-to inbound ip-group 2000 monitor-interface
2) Method II
<Sysname> system-view
[Sysname] acl number 2000
[Sysname-acl-basic-2000] rule permit source 10.1.1.0 0.0.0.255
[Sysname-acl-basic-2000] quit
[Sysname] interface Ethernet 1/0/4
[Sysname-Ethernet1/0/4] monitor-port
[Sysname-Ethernet1/0/4] quit
[Sysname] mirrored-to vlan 2 inbound ip-group 2000 monitor-interface
1.4.12 Displaying QoS
After the above configuration, you can execute the display command in any view to view the running status of QoS and verify the configuration.
Table 1-36 Display QoS
|
Operation |
Command |
Description |
|
Display the CoS-precedence-to-local-precedence mapping relationship |
display qos cos-local-precedence-map |
Available in any view |
|
Display the DSCP-precedence-to-local-precedence mapping relationship |
display qos dscp-local-precedence-map |
|
|
Display queue scheduling algorithm and related parameters |
display queue-scheduler |
|
|
Display the QoS-related configuration of a port or all the ports |
display qos-interface { interface-type interface-number | unit-id } all |
|
|
Display rate limiting configuration of a port or all the ports |
display qos-interface { interface-type interface-number | unit-id } line-rate |
|
|
Display traffic policing configuration of a port or all the ports |
display qos-interface { interface-type interface-number | unit-id } traffic-limit |
|
|
Display priority marking configuration of a port or all the ports |
display qos-interface { interface-type interface-number | unit-id } traffic-priority |
|
|
Display traffic redirecting configuration of a port or all the ports |
display qos-interface { interface-type interface-number | unit-id } traffic-redirect |
|
|
Display traffic shaping configuration of a port or all the ports |
display qos-interface { interface-type interface-number | unit-id } traffic-shape |
|
|
Display traffic accounting configuration of a port or all the ports |
display qos-interface { interface-type interface-number | unit-id } traffic-statistic |
|
|
Display traffic mirroring configuration of a port or all the ports |
display qos-interface { interface-type interface-number | unit-id } mirrored-to |
|
|
Display the configuration of traffic mirroring, traffic policing, priority marking, traffic redirecting, or traffic accounting performed for all the packets |
display qos-global { all | mirrored-to | traffic-limit | traffic-priority | traffic-redirect | traffic-statistic } |
|
|
Display the configuration of traffic mirroring, traffic policing, priority marking, traffic redirecting, or traffic accounting performed for packets of a VLAN |
display qos-vlan [ vlan-id ] { all | mirrored-to | traffic-limit | traffic-priority | traffic-redirect | traffic-statistic } |
|
|
Display the configuration of traffic mirroring, traffic policing, priority marking, traffic redirecting, or traffic accounting performed for packets of a port group |
display qos-port-group [ group-id ] { all | mirrored-to | traffic-limit | traffic-priority | traffic-redirect | traffic-statistic } |
1.5 QoS Configuration Example
1.5.1 Configuration Example of Traffic Policing
I. Network requirement
An enterprise network connects all the departments through an S3100 Ethernet switch. The R&D department belongs to the network segment 192.168.1.0/24 and connects to the switch through Ethernet 1/0/1; the marketing department belongs to the network segment 192.168.2.0/24 and connects to the switch through Ethernet 1/0/2.
Configure traffic policing to satisfy the following requirements:
l Set the maximum rate of outbound IP packets sourced from the marketing department to 64 kbps. Drop the packets exceeding the rate limit.
l Set the maximum rate of outbound IP packets sourced from the R&D department to 128 kbps. Drop the packets exceeding the rate limit.
II. Network diagram
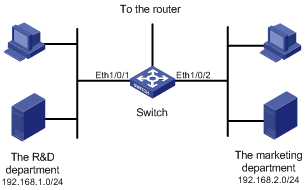
Figure 1-9 Network diagram for traffic policing configuration
III. Configuration procedure
1) Define an ACL for traffic classification.
# Create ACL 2000 and enter basic ACL view to classify packets sourced from the 192.168.1.0/24 network segment.
<Sysname> system-view
[Sysname] acl number 2000
[Sysname-acl-basic-2000] rule permit source 192.168.1.0 0.0.0.255
[Sysname-acl-basic-2000] quit
# Create ACL 2001 and enter basic ACL view to classify packets sourced from the 192.168.2.0/24 network segment.
[Sysname] acl number 2001
[Sysname-acl-basic-2001] rule permit source 192.168.2.0 0.0.0.255
[Sysname-acl-basic-2001] quit
2) Configure traffic policing
# Set the maximum rate of outbound IP packets sourced from the R&D department to 128 kbps.
[Sysname] interface Ethernet 1/0/1
[Sysname-Ethernet1/0/1] traffic-limit inbound ip-group 2000 128 exceed drop
# Set the maximum rate of outbound IP packets sourced from the marketing department to 64 kbps.
[Sysname] interface Ethernet 1/0/2
[Sysname-Ethernet1/0/2] traffic-limit inbound ip-group 2001 64 exceed drop
Chapter 2 QoS Profile Configuration
2.1 Overview
2.1.1 Introduction to QoS Profile
QoS profile is a set of QoS configurations. It provides an easy way for performing and managing QoS configuration. A QoS profile can contain one or multiple QoS actions. In networks where hosts change their positions frequently, you can define QoS policies for the specific hosts and add the QoS policies to a QoS profile. When a host is connected to another port of a switch, you can simply apply the corresponding QoS profile to the port statically or dynamically to maintain the same QoS configuration performed for the host.
2.1.2 QoS Profile Application Mode
I. Dynamic application mode
A QoS profile can be applied dynamically to a user or a group of users passing 802.1x authentication. To apply QoS profiles dynamically, a user name-to-QoS profile mapping table is required on the AAA server. For a switch operating in this mode, after a user passes the 802.1x authentication, the switch looks up the user name-to-QoS profile mapping table for the QoS profile using the user name and then applies the QoS profile found to the port the user is connected to.
Corresponding to the 802.1x authentication modes, dynamic QoS profile application can be user-based and port-based.
l User-based QoS profile application
The switch generates a new QoS profile by adding user source MAC address information to the identifying rule defined in the existing QoS profile and then applies the new QoS profile to the port the user is connected to.
l Port-based QoS profile application
The switch directly applies the QoS profile to the port the user is connected to.
& Note:
A user-based QoS profile application fails if the traffic classification rule defined in the QoS profile contains source address information (including source MAC address information, source IP address information, and VLAN information).
II. Manual application mode
You can use the apply command to manually apply a QoS profile to a port.
2.2 QoS Profile Configuration
Table 2-1 QoS profile configuration tasks
|
Operation |
Description |
Related section |
|
Configure a QoS Profile |
Required |
Section Configuring a QoS Profile |
|
Configure to apply a QoS Profile dynamically |
Optional |
Section Applying a QoS Profile |
|
Apply a QoS Profile manually |
Optional |
Section Applying a QoS Profile |
2.2.1 Configuring a QoS Profile
I. Configuration prerequisites
l The ACL rules used for traffic classification are defined. Refer to the ACL module of this manual for information about defining ACL rules.
l The type and number of actions in the QoS profile are specified.
II. Configuration procedure
Table 2-2 Configure a QoS profile
|
Operation |
Command |
Description |
|
Enter system view |
system-view |
— |
|
Create a QoS profile and enter QoS profile view |
qos-profile profile-name |
Required If the specified QoS profile already exists, you enter the QoS profile view directly. |
|
Configure traffic policing |
traffic-limit inbound acl-rule target-rate [ burst-bucket burst-bucket-size ] [ conform con-action ] [ exceed exceed-action ] [ meter-statistic ] |
Optional |
|
Configure packet filtering |
packet-filter inbound acl-rule |
Optional Refer to the ACL module of this manual for information about packet filtering. |
|
Configure priority marking |
traffic-priority inbound acl-rule { dscp dscp-value | cos cos-value | local-precedence pre-value }* |
Optional |
2.2.2 Applying a QoS Profile
You can configure to apply a QoS profile dynamically or simply apply a QoS profile manually.
I. Configuration prerequisites
l To configure to apply a QoS profile dynamically, make sure 802.1x is enabled both globally and on the port, and the authentication mode is determined. For information about 802.1x, refer to the 802.1x and System Guard module of this manual.
l To apply a QoS profile manually, make sure the port to which the QoS profile is to be applied is determined.
l The QoS profile to be applied is determined.
II. Configuration procedure
Table 2-3 Configure to apply a QoS profile dynamically
|
Operation |
Command |
Description |
|
|
Enter system view |
system-view |
— |
|
|
Enter Ethernet port view |
interface interface-type interface-number |
— |
|
|
Specify the mode to apply a QoS profile |
Configure the mode to apply a QoS profile as port-based |
qos-profile port-based |
Optional By default, the mode to apply a QoS profile is user-based. l If the 802.1x authentication mode is MAC address-based, the mode to apply a QoS profile must be configured user-based. l If the 802.1x authentication mode is port-based, the mode to apply a QoS profile must be configured as port-based. |
|
Configure the mode to apply a QoS profile as user-based |
undo qos-profile port-based |
||
Table 2-4 Apply a QoS profile manually
|
Operation |
Command |
Description |
||
|
Enter system view |
system-view |
— |
||
|
Apply a QoS profile to specific ports |
In system view |
apply qos-profile profile-name interface interface-list |
Select either of the operations. By default, a port has no QoS profile applied to it. |
|
|
In Ethernet port view |
Enter Ethernet port view |
interface interface-type interface-number |
||
|
Apply a QoS profile to the current port |
apply qos-profile profile-name |
|||
2.2.3 Displaying QoS Profile Configuration
After the above configuration, you can execute the display command in any view to view the running status of the QoS profile and verify the configuration.
Table 2-5 Display QoS profile configuration
|
Operation |
Command |
Description |
|
Display QoS profile configuration |
display qos-profile { all | name profile-name | interface interface-type interface-number | user user-name } |
Available in any view |
2.3 Configuration Example
2.3.1 QoS Profile Configuration Example
I. Network requirements
All departments of a company are interconnected through a switch. The 802.1x protocol is used to authenticate users and control their access to network resources. A user name is someone, and the authentication password is hello. It is connected to Ethernet 1/0/1 of the switch and belongs to the test.net domain.
It is required to configure a QoS profile to limit the rate of all the outbound IP packets of the user to 128 kbps and configuring to drop the packets exceeding the target packet rate.
II. Network diagram
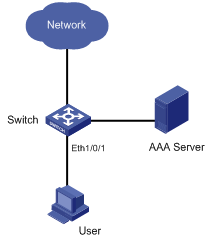
Figure 2-1 Network diagram for QoS profile configuration
III. Configuration procedure
1) Configuration on the AAA server
# Configure the user authentication information and the matching relationship between the user name and the QoS profile. Refer to the user manual of the AAA server for detailed configuration.
2) Configuration on the switch
# Configure IP addresses for the RADIUS server.
<Sysname> system-view
[Sysname] radius scheme radius1
[Sysname-radius-radius1] primary authentication 10.11.1.1
[Sysname-radius-radius1] primary accounting 10.11.1.2
[Sysname-radius-radius1] secondary authentication 10.11.1.2
[Sysname-radius-radius1] secondary accounting 10.11.1.1
# Set the encryption passwords for the switch to exchange packets with the authentication RADIUS servers and accounting RADIUS servers.
[Sysname-radius-radius1] key authentication money
[Sysname-radius-radius1] key accounting money
# Configure the switch to delete the user domain name from the user name and then send the user name to the RADIUS sever.
[Sysname-radius-radius1] user-name-format without-domain
[Sysname-radius-radius1] quit
# Create the user domain test.net and specify radius1 as your RADIUS server group.
[Sysname] domain test.net
[Sysname-isp-test.net] radius-scheme radius1
[Sysname-isp-test.net] quit
# Create ACL 3000 to permit IP packets destined for any IP address.
[Sysname] acl number 3000
[Sysname-acl-adv-3000] rule 1 permit ip destination any
[Sysname-acl-adv-3000] quit
# Define a QoS profile named “example” to limit the rate of matched packets to 128 kbps and configuring to drop the packets exceeding the target packet rate.
[Sysname] qos-profile example
[Sysname-qos-profile-example] traffic-limit inbound ip-group 3000 128 exceed drop
# Enable 802.1x.
[Sysname] dot1x
[Sysname] dot1x interface Ethernet1/0/1
After the configuration, the QoS profile named “example” will be applied to the user with user name “someone” automatically after the user passes the authentication.
