- Table of Contents
-
- 14-WLAN Configuration Guide (AC)
- 00-Preface
- 01-Compatibility of hardware and AC functionality
- 02-AP management configuration
- 03-Radio management configuration
- 04-WLAN access configuration
- 05-WLAN security configuration
- 06-WLAN authentication configuration
- 07-WIPS configuration
- 08-WLAN QoS configuration
- 09-WLAN roaming configuration
- 10-WLAN load balancing configuration
- 11-WLAN radio resource measurement configuration
- 12-Channel scanning configuration
- 13-Band navigation configuration
- 14-WLAN multicast optimization configuration
- 15-WLAN RRM configuration
- 16-WLAN IP snooping configuration
- 17-WLAN probe configuration
- 18-Spectrum management configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 02-AP management configuration | 500.66 KB |
Restrictions: Hardware compatibility with AP management
Restrictions and guidelines: AP management configuration
AP management tasks at a glance
Configuring CAPWAP tunnel establishment
Prerequisites for configuring CAPWAP tunnel establishment
Setting the discovery-response timeout timer
Setting the AP connection priority for the AC
Enabling the AC to respond only to unicast discovery requests
Enabling an AP to prefer discovering ACs by IPv6 address
Configuring the mapping between a software version and a hardware version of an AP model
Specifying the preferred location for the AC to obtain an AP image file
Deploying an image file to online APs
Configuring remote configuration synchronization
About remote configuration synchronization
Creating a Layer 2 aggregate interface
Assigning an interface to a Layer 2 aggregation group
Configuring basic VLAN settings
Assigning an access port to a VLAN
Assigning a trunk port to VLANs
Assigning a hybrid port to VLANs
Setting the trusted packet priority type
Synchronizing settings to online APs
Configuring CAPWAP tunnel encryption
Configuring CAPWAP tunnel latency detection
Setting the control tunnel keepalive timer for an AP
Setting the data tunnel keepalive interval for an AP
Setting the maximum fragment size for CAPWAP packets
Setting the TCP MSS for CAPWAP tunnels
Configuring AC request retransmission
Configuring preprovisioned settings for an AP
Configuring network settings for an AP group
Configuring global network settings
Assigning preprovisioned settings to APs
Managing the file system of an AP
Setting the statistics report interval
Setting the statistics fast report interval
Configuring auto loading of preprovisioned settings
Specifying the uplink interface type for APs
Configuring advanced features for AP management
Configuring AP power management
Configuring the default input power level
Enabling or disabling USB interfaces for APs
Configuring a description for the AC
Enabling time zone synchronization
Enabling service anomaly detection
Configuring an AP monitor group
Display and maintenance commands for AP management
AP management configuration examples
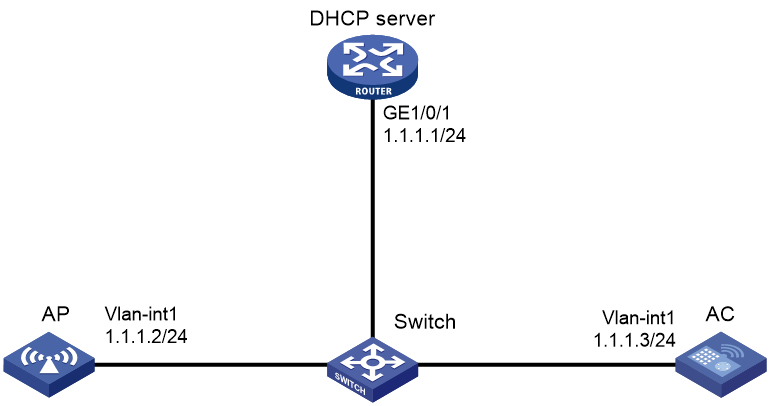
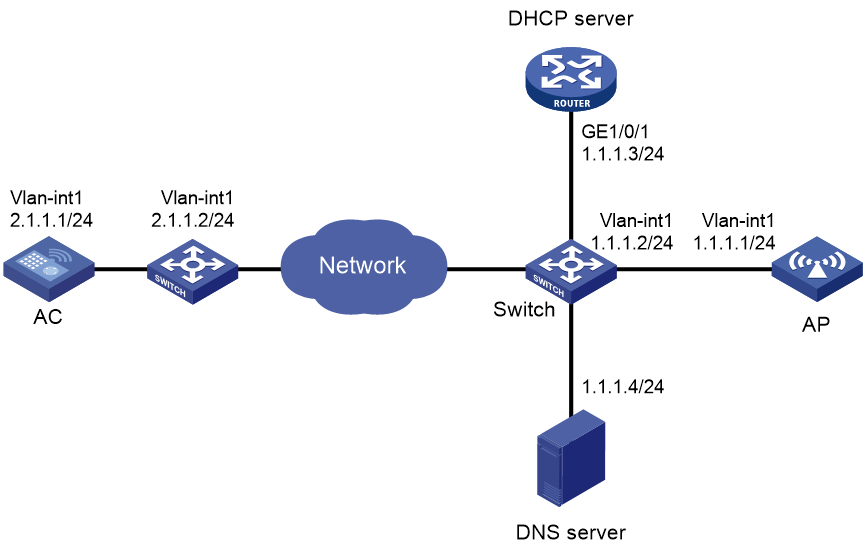
Example: Establishing a CAPWAP tunnel through DHCP
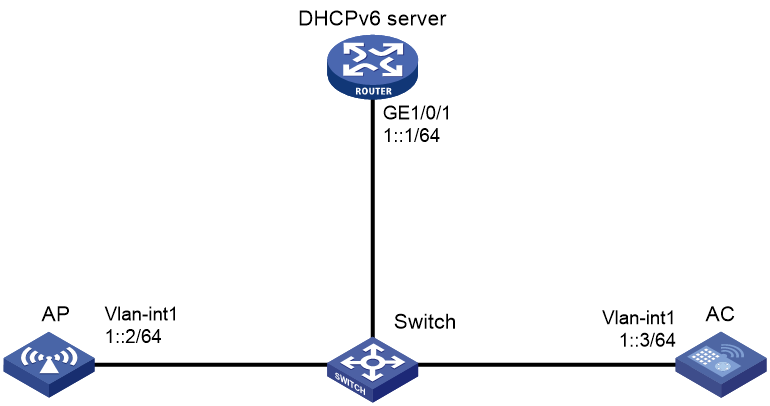
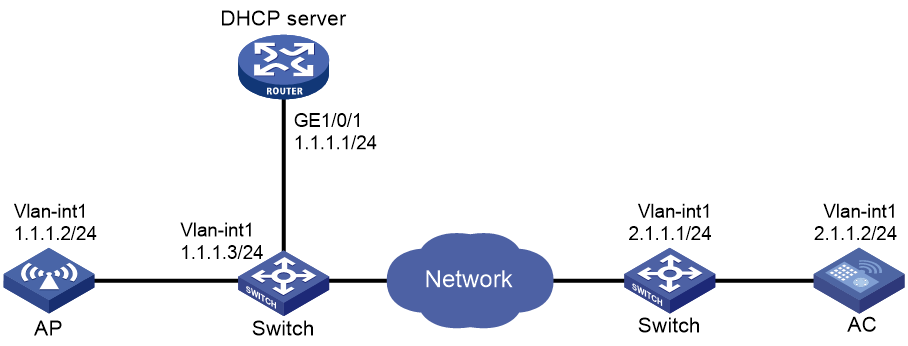
Example: Establishing a CAPWAP tunnel through DHCPv6
Example: Establishing a CAPWAP tunnel through DNS
Managing APs
About AP management
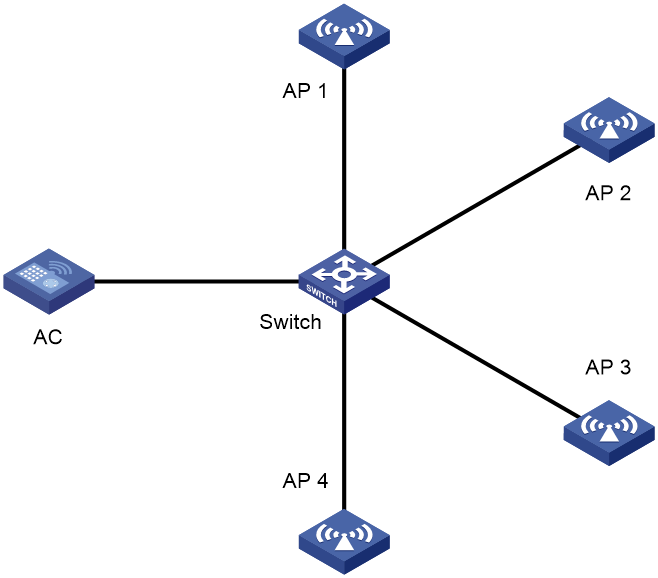
Managing a large number of APs is both time consuming and costly. The fit AP+AC network architecture enables an AC to implement centralized AP management and maintenance.
|
|
NOTE: The term "AC" in this document refers to MSR routers that can function as ACs. For information about routers that can function as ACs, see "Compatibility of MSR routers and AC functionality." |
CAPWAP tunnel
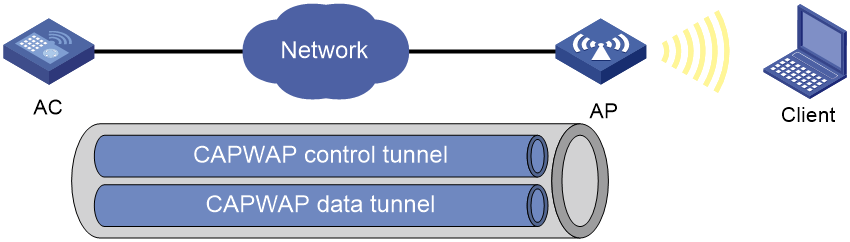
Control And Provisioning of Wireless Access Points (CAPWAP) defines how an AP communicates with an AC. It provides a generic encapsulation and transport mechanism between AP and AC. CAPWAP uses UDP and supports both IPv4 and IPv6.
As shown in Figure 1, an AC and an AP establish a data tunnel to forward data packets and a control tunnel to forward control packets.
AC discovery
After starting up with zero configurations, an AP automatically creates VLAN-interface 1 and enables the DHCP client, DHCPv6 client, and DNS features on the interface. Then it obtains its own IP address from the DHCP server and discovers ACs by using the following methods:
· Static IP address.
If AC IP addresses have been manually configured for the AP, the AP sends a unicast discovery request to each AC IP address to discover ACs.
· DHCP options.
The AP obtains AC IPv4 addresses from Option 138, Option 43, and IPv6 addresses from Option 52 sent from the DHCP server. It uses these addresses in descending order.
For more information about DHCP options, see Layer 3—IP Services Configuration Guide.
· DNS.
a. The AP obtains the domain name suffix from the DHCP server.
b. The AP adds the suffix to the host name.
c. The DNS server translates the domain name into IP addresses.
For more information about DNS, see Layer 3—IP Services Configuration Guide.
· Broadcast.
The AP broadcasts discovery requests to IP address 255.255.255.255 to discover ACs.
· IPv4 multicast:
The AP sends multicast discovery requests to IPv4 address 224.0.1.140 to discover ACs.
· IPv6 multicast.
The AP sends multicast discovery requests to IPv6 address FF0E::18C to discover ACs.
The methods of static IP address, DHCPv4 options, broadcast/IPv4 multicast, IPv4 DNS, IPv6 multicast, DHCPv6 option, and IPv6 DNS are used in descending order.
The AP does not stop AC discovery until it establishes a CAPWAP tunnel with one of the discovered ACs.
CAPWAP tunnel establishment
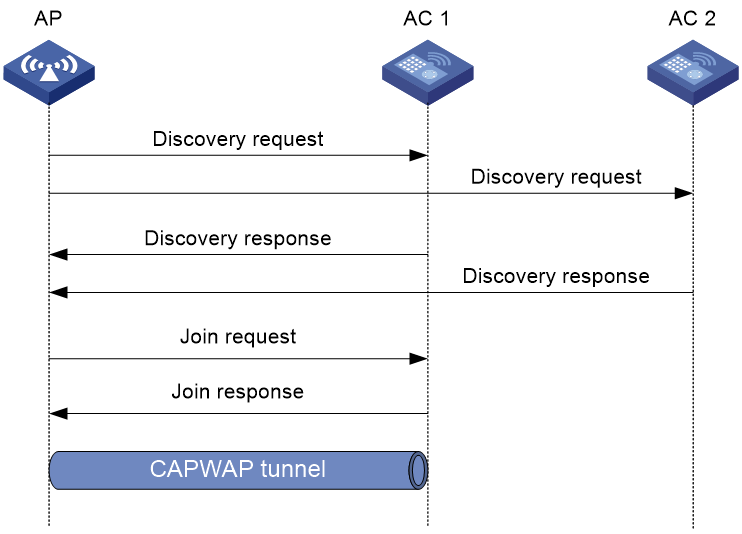
Figure 2 Establishing a CAPWAP tunnel
As shown in Figure 2, the AP and an AC establish a CAPWAP tunnel by using the following procedure:
1. The AP sends a discovery request to each AC to discover ACs.
2. Upon receiving a discovery request, an AC determines whether to send a discovery response by performing the following steps:
a. Identifies whether the discovery request is a unicast packet.
- Unicast packet—The AC proceeds to step b.
- Broadcast or multicast packet—The AC proceeds to step b if it is disabled with the feature of responding only to unicast discovery requests. If this feature is enabled, the AC does not send a discovery response.
- If manual AP configuration exists, the AC sends a discovery response to the AP. The discovery response contains information about whether the AC has the manual configuration for the AP, the AP connection priority, and the AC's load status.
- If no manual AP configuration exists, the AC proceeds to step c.
c. Identifies whether auto AP is enabled.
- If auto AP is enabled, the AC sends a discovery response to the AP. The discovery response contains the enabling status of auto AP, AP connection priority, and AC's load information.
- If auto AP is disabled, the AP does not send a discovery response.
3. Upon receiving the discovery responses, the AP selects the optimal AC in descending order.
¡ AC that saves information about the AP.
¡ AC where the auto AP feature is enabled.
¡ AC with higher AP connection priority.
¡ AC with the lighter load.
¡ AC that is the earliest to respond.
4. The AP sends a join request to the optimal AC.
5. After receiving the join request, the AC examines the information in the request to determine whether to provide access services to the AP and sends a join response.
6. The AP examines the result code in the response upon receiving the join response:
¡ If the result code represents failure, the AP does not establish a CAPWAP tunnel with the AC.
¡ If the result code represents success, the AP establishes a CAPWAP tunnel with the AC.
APDB
The Access Point Information Database (APDB) on an AC stores the following AP information:
· AP models.
· Hardware version and software version mappings.
· Information about radios supported by AP models:
¡ Number of radios.
¡ Radio type.
¡ Valid region code.
¡ Valid antenna type.
¡ Maximum transmission power.
The AC can establish a CAPWAP tunnel with an AP only when the APDB contains the corresponding AP model information.
You can use the system script and user scripts to manage data in the APDB. The system script is released with the AC software version, and it is automatically loaded each time the AC starts. If you need to add new AP models, upgrade the AC software version (see Fundamentals Configuration Guide) or create a user script and load it on the AC (see "Configuring a description for the AC").
Protocols and standards
· RFC 5415, Control And Provisioning of Wireless Access Points (CAPWAP) Protocol Specification
Restrictions: Hardware compatibility with AP management
For information about MSR routers that can function as ACs, see "Compatibility of hardware and AC functionality."
Restrictions and guidelines: AP management configuration
You can configure APs by using the following methods:
· Configure APs one by one in AP view.
· Assign APs to an AP group and configure the AP group in AP group view.
· Configure all APs in global configuration view.
For an AP, the settings made in these views for the same parameter take effect in descending order of AP view, AP group view, and global configuration view.
AP management tasks at a glance
To configure AP management, perform the following tasks:
1. Configuring CAPWAP tunnel establishment
Choose one of the tasks of creating a manual AP and managing auto APs.
¡ (Optional.) Setting the discovery-response timeout timer
¡ (Optional.) Setting the AP connection priority for the AC
¡ (Optional.) Enabling the AC to respond only to unicast discovery requests
¡ (Optional.) Configuring AC rediscovery
¡ (Optional.) Enabling an AP to prefer discovering ACs by IPv6 address
2. (Optional.) Configuring an AP group
3. (Optional.) Upgrading APs' software
4. (Optional.) Configuring remote configuration synchronization
5. (Optional.) Configuring a CAPWAP tunnel
¡ Configuring CAPWAP tunnel encryption
¡ Configuring CAPWAP tunnel latency detection
¡ Setting the control tunnel keepalive timer for an AP
¡ Setting the data tunnel keepalive interval for an AP
¡ Setting the maximum fragment size for CAPWAP packets
¡ Setting the TCP MSS for CAPWAP tunnels
6. (Optional.) Configuring AC request retransmission
7. (Optional.) Preprovisioning APs
8. (Optional.) Enabling SNMP notifications
9. (Optional.) Maintaining APs
¡ Managing the file system of an AP
¡ Setting the statistics report interval
¡ Setting the statistics fast report interval
¡ Specifying the uplink interface type for APs
10. (Optional.) Configuring advanced features for AP management
11. (Optional.) Configuring AP power management
¡ Configuring the default input power level
¡ Enabling or disabling USB interfaces for APs
12. (Optional.) Maintaining ACs
¡ Configuring a description for the AC
¡ Enabling time zone synchronization
¡ Enabling service anomaly detection
Configuring CAPWAP tunnel establishment
Prerequisites for configuring CAPWAP tunnel establishment
Before you manage APs, complete the following tasks:
· Create a DHCP address pool on the DHCP server to assign IP addresses to APs.
· If DHCP options are used for AC discovery, configure Option 138, Option 43, or Option 52 in the specified DHCP address pool on the DHCP server.
· If DNS is used for AC discovery, configure the IP address of the DNS server and the AC domain name suffix in the specified DHCP address pool on the DHCP server. Then configure the mapping between the domain name and the AC IP address on the DNS server.
· Make sure the APs and the AC can reach each other.
For more information about DHCP and DNS, see Layer 3—IP Services Configuration Guide.
Creating a manual AP
About this task
You can create a manual AP on the AC based on the AP model, serial ID, and MAC address of the AP you are using. An AP prefers to establish a CAPWAP tunnel with an AC that saves the manual AP configuration.
Procedure
1. Enter system view.
system-view
2. Create a manual AP and enter its view.
wlan ap ap-name [ model model-name ]
You must specify the model name when you create an AP.
3. Specify the serial ID or the MAC address for the AP.
¡ Specify the serial ID for the AP.
serial-id serial-id
¡ Specify the MAC address for the AP.
mac-address mac-address
By default, neither the serial ID nor the MAC address is specified for an AP.
4. (Optional.) Configure a description for the AP.
description text
By default, an AP does not have a description.
Managing auto APs
About this task
The auto AP feature enables APs to connect to an AC without manual AP configuration. This feature simplifies configuration when you deploy a large number of APs in a WLAN.
For security purposes, you can use the following methods to authenticate auto APs:
· Local authentication.
The AC authenticates an auto AP by serial ID or MAC address. When an auto AP initiates a connection request, the AC uses an ACL specified by the wlan ap-authentication acl command to match the auto AP. Assume that the AC authenticates the auto AP by serial ID.
¡ If the serial ID matches a permit rule, the auto AP passes the authentication and associates with the AC.
¡ If the serial ID matches a deny rule, the auto AP fails the authentication and cannot associate with the AC.
¡ If the serial ID does not match a rule, the auto AP is determined as an unauthenticated auto AP. An unauthenticated auto AP can associate with the AC but cannot provide wireless services.
· Remote authentication.
Remote authentication is used for authenticating unauthenticated auto APs. The AC uses the serial ID or MAC address of an unauthenticated auto AP as the username and password and sends them to the authentication server for authentication. If the authentication succeeds, the AC accepts the AP. If it does not succeed, the AC rejects the AP.
· Manual authentication.
Manual authentication is used for authenticating unauthenticated auto APs.
The AC determines whether to accept an unauthenticated auto AP depending on the manual authentication configuration.
Restrictions and guidelines
To prevent illegal APs from associating with the AC, disable the auto AP feature after all required APs are associated with the AC.
You must convert auto APs to manual APs after they come online because of the following reasons:
· Auto APs can re-associate with the AC upon an AC reboot or CAPWAP tunnel termination only when they are converted to manual APs.
· You can individually configure auto APs only when they are converted to manual APs.
Tasks at a glance
To configure auto APs, perform the following tasks:
1. Enabling the auto AP feature
2. (Optional.) Converting auto APs to manual APs
3. (Optional.) Configuring auto AP authentication
Choose one of the following tasks:
¡ Configuring auto AP local authentication
¡ Configuring auto AP remote authentication
¡ Manually authenticating unauthenticated auto APs
4. (Optional.) Disabling unauthenticated auto APs from associating with the AC
5. (Optional.) Restarting unauthenticated auto APs
Prerequisites
Before you configure remote authentication for auto APs, specify an authentication domain and AAA scheme on the AC and create user accounts on the RADIUS server. For information about authentication domain and AAA scheme configuration, see AAA in Security Configuration Guide.
Enabling the auto AP feature
1. Enter system view.
system-view
2. Enable the auto AP feature.
wlan auto-ap enable
By default, the auto AP feature is disabled.
Converting auto APs to manual APs
1. Enter system view.
system-view
2. Convert auto APs to manual APs. Choose the options to configure as needed:
¡ Convert online auto APs to manual APs.
wlan auto-ap persistent { all | name auto-ap-name [ new-ap-name ] }
¡ Enable the auto AP conversion feature.
wlan auto-persistent enable
By default, the auto AP conversion feature is disabled.
The wlan auto-persistent enable command does not take effect on auto APs that are already online.
Configuring auto AP local authentication
1. Enter system view.
system-view
2. Specify an authentication method.
wlan ap-authentication method { mac-address | serial-id }
By default, the AC authenticates auto APs by MAC address.
3. Create a WLAN AP ACL.
acl wlan ap { acl-number | name acl-name }
For more information about this command, see ACL and QoS Command Reference.
4. Return to system view.
quit
5. Specify an ACL for authenticating auto APs.
wlan ap-authentication acl acl-number
By default, no ACL is specified for authenticating auto APs.
6. Create ACL rules for the WLAN AP ACL. Choose the options to configure as needed:
¡ Execute the following commands in sequence to manually create a rule:
acl wlan ap { acl-number | name acl-name }
rule [ rule-id ] { deny | permit } [ mac mac-address mac-mask ] [ serial-id serial-id ]
quit
¡ Import an auto AP authentication file to generate ACL rules.
wlan ap-authentication import file-name
Use either method or both methods according to actual network requirements.
7. Enable auto AP authentication.
wlan ap-authentication enable
By default, auto AP authentication is disabled.
Configuring auto AP remote authentication
1. Enter system view.
system-view
2. Specify an authentication domain for unauthenticated auto APs.
wlan ap-authentication domain domain-name
By default, no authentication domain is specified for unauthenticated auto APs.
Manually authenticating unauthenticated auto APs
1. Enter system view.
system-view
2. Manually authenticate unauthenticated auto APs.
wlan ap-authentication { accept | reject } ap-unauthenticated { all | name ap-name }
By default, manual authentication is not configured for unauthenticated auto APs.
Disabling unauthenticated auto APs from associating with the AC
1. Enter system view.
system-view
2. Disable unauthenticated auto APs from associating with the AC.
undo wlan ap-authentication permit-unauthenticated
By default, unauthenticated auto APs can associate with the AC but cannot provide wireless services.
This feature reduces waste of system resources.
Restarting unauthenticated auto APs
To restart unauthenticated auto APs, execute the following command in user view:
reset wlan ap unauthenticated
The auto APs will be reauthenticated after being restarted.
Setting the discovery-response timeout timer
About this task
The discovery-response timeout timer specifies the timeout time for an AP to wait for another discovery response. Whenever an AP receives a discovery response packet, the discovery-response timeout timer is created or refreshed. When the timeout timer expires, the AP sends a join request to the optimal AC.
Restrictions and guidelines
If the network condition is poor, set a larger discovery-response timeout timer.
Procedure
1. Enter system view.
system-view
2. Enter AP view or AP group view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
3. Set the discovery-response timeout timer.
discovery-response wait-time seconds
By default:
¡ In AP view, an AP uses the configuration in AP group view.
¡ In AP group view, the discovery-response timeout timer is 2 seconds.
Setting the AP connection priority for the AC
1. Enter system view.
system-view
2. Enter AP view or AP group view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
3. Set the AP connection priority for the AC.
priority priority
By default:
¡ In AP view, an AP uses the configuration in AP group view.
¡ In AP group view, the AP connection priority is 4.
Enabling the AC to respond only to unicast discovery requests
About this task
An AP can send unicast, multicast, and broadcast discovery requests to discover ACs. This feature enables an AC to respond only to unicast discovery requests.
Procedure
1. Enter system view.
system-view
2. Enable the AC to respond only to unicast discovery requests.
wlan capwap discovery-policy unicast
By default, the AC can respond to unicast, multicast, and broadcast discovery requests.
Configuring AC rediscovery
About this task
An AC enabled with AC rediscovery will add the CAPWAP Control IP Address message element to the discovery responses sent to APs. Upon receiving such a discovery response, an AP establishes a CAPWAP tunnel by using the following procedure:
1. Examines whether a discovery request has been sent to each IP address specified in the CAPWAP Control IP Address message element.
2. Performs either of the following operations:
¡ Sends a join request to the specified IP address representing the optimal AC for CAPWAP establishment if discovery requests have been sent.
¡ Sends a discovery request to each specified IP address to initiate a new AC discovery process if no discovery requests have been sent.
An AC disabled with AC rediscovery does not add the CAPWAP Control IP Address message element in discovery responses sent to APs. APs that receive the discovery responses will send join requests to the source IP address of the discovery responses to establish CAPWAP tunnels with the AC.
AC rediscovery applies to CMCC wireless networks where the CAPWAP Control IP Address message element is required in discovery responses from the AC.
Procedure
1. Enter system view.
system-view
2. Enter AP view, AP group view, or global configuration view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
¡ Enter global configuration view.
wlan global-configuration
3. Configure AC rediscovery.
control-address { disable | enable }
By default:
¡ In AP view, an AP uses the configuration in AP group view. If no configuration exists in AP group view, the AP uses the configuration in global configuration view.
¡ In AP group view, an AP uses the configuration in global configuration view.
¡ In global configuration view, AC rediscovery is disabled.
4. Specify the IP address to be added in the CAPWAP Control IP Address message element.
control-address { ip ipv4-address | ipv6 ipv6-address }
By default:
¡ In AP view, an AP uses the configuration in AP group view. If no configuration exists in AP group view, the AP uses the configuration in global configuration view.
¡ In AP group view, an AP uses the configuration in global configuration view.
¡ In global configuration view, the IP address in the element is the AC's IP address.
You can specify a maximum of three IPv4 or IPv6 addresses to be added in the CAPWAP Control IP Address message element.
Enabling an AP to prefer discovering ACs by IPv6 address
About this task
This feature enables an AP to discover ACs by using the static IP addresses, IPv6 multicast, DHCPv6 option, IPv6 DNS, DHCPv4 options, broadcast/IPv4 multicast, and IPv4 DNS successively. If the AP connects to an AC successfully with a discovered IP address, it stops AC discovery.
Procedure
1. Enter system view.
system-view
2. Enter AP view or AP group view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
3. Enter AP or AP group provision view.
provision
4. Enable an AP to prefer discovering ACs by IPv6 address.
ac discovery policy ipv6
By default:
¡ In AP view, an AP uses the configuration in AP group view.
¡ In AP group view, an AP prefers to discover ACs by IPv4 address.
Configuring an AP group
About this task
This feature enables you to configure multiple APs in a batch to reduce configuration workload.
APs in an AP group use the configuration of the group. By default, all APs belong to system-defined AP group default-group. The system-defined AP group cannot be deleted.
You can configure AP grouping rules by AP name, serial ID, MAC address, and IP address to add APs to the specified AP group. Priorities of these grouping rules are in descending order. If an AP does not match any grouping rules, it is added to the default AP group.
Restrictions and guidelines
An AP can be added to only one AP group.
You cannot delete an AP group that contains an AP. An AP group that has grouping rules but does not contain any APs can be deleted.
When you configure an AP grouping rule, follow these restrictions and guidelines:
· You cannot create the same grouping rule for different AP groups. If you do so, the most recent configuration takes effect.
· You cannot create grouping rules for the default AP group.
· AP grouping rules by IPv4 or IPv6 addresses for an AP group or for different AP groups cannot overlap with each other.
· An AP group supports a maximum of 32 AP grouping rules by IPv4 or IPv6 addresses.
Procedure
1. Enter system view.
system-view
2. Create an AP group and enter its view.
wlan ap-group group-name
By default, a default AP group exists.
3. (Optional.) Configure a description for the AP group.
description text
By default, an AP group does not have a description.
4. Create an AP grouping rule. Choose the options to configure as needed:
¡ Create an AP grouping rule by AP names.
ap ap-name-list
¡ Create an AP grouping rule by serial IDs.
serial-id serial-id
¡ Create an AP grouping rule by MAC addresses.
mac-address mac-address
¡ Create an AP grouping rule by IPv4 addresses.
if-match ip ip-address { mask-length | mask }
¡ Create an AP grouping rule by IPv6 addresses.
if-match ipv6 { ipv6-address prefix-length | ipv6-address/prefix-length }
5. (Optional.) Create an AP regrouping rule.
wlan re-group { ap ap-name | ap-group old-group-name | mac-address mac-address | serial-id serial-id } group-name
Upgrading APs' software
Configuring software upgrade
About this task
With software upgrade enabled, the AC examines the AP software version while establishing a CAPWAP tunnel with an AP. If this feature is disabled, the AC does not examine the software version of the AP and directly establishes a CAPWAP tunnel with the AP.
Software upgrade for an AP proceeds as follows:
1. The AP reports the software version and AP model information to the AC.
2. The AC examines the received AP software version.
¡ If a match is found, the AC establishes a CAPWAP tunnel with the AP.
¡ If no match is found, the AC sends a message that notifies the AP of the AP software version inconsistency.
3. Upon receiving the inconsistency message, the AP requests a software version from the AC.
4. The AC assigns the software version to the AP after receiving the request.
5. The AP upgrades the software version, restarts, and establishes a CAPWAP tunnel with the AC
Procedure
1. Enter system view.
system-view
2. Enter AP view, AP group view, or global configuration view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
¡ Enter global configuration view.
wlan global-configuration
3. Configure software upgrade.
firmware-upgrade { disable | enable }
By default:
¡ In AP view, an AP uses the configuration in AP group view. If no software upgrade configuration exists in AP group view, the AP uses the configuration in global configuration view.
¡ In AP group view, an AP uses the configuration in global configuration view.
¡ In global configuration view, the software upgrade feature is enabled.
Configuring the mapping between a software version and a hardware version of an AP model
About this task
Perform this task to configure the mapping between a software version and a hardware version of an AP model for software upgrade.
Perform this task only when the AP software version for an AP model stored in the APDB is inconsistent with the software version you expect for the AP model. To display the AP software version for each AP model in the APDB, use the display wlan ap-model command.
Restrictions and guidelines
To avoid CAPWAP tunnel establishment failure, use this feature under the guidance of H3C Support.
Procedure
1. Enter system view.
system-view
2. Configure the mapping between a software version and a hardware version of an AP model.
wlan apdb model-name hardware-version software-version
By default, the software version for a hardware version of an AP model is the software version that is stored in APDB user scripts.
Specifying the preferred location for the AC to obtain an AP image file
About this task
The AC assigns an AP image file to an AP if the AP requests a software version during CAPWAP tunnel establishment. You can specify the preferred location as the AC's RAM or local folder for the AC to obtain an AP image file. If the AC cannot obtain an AP image file from the preferred location, it obtains an AP image file from the other location. If no AP image file exists, the AC fails to obtain an image file and cannot assign a software version to the AP.
Restrictions and guidelines
The AC can assign only .ipe AP image files to APs.
If you specify the local folder, make sure the AC uses a CF or flash card as the default file system and the AP image file is stored in the root directory of the file system on the AC.
Procedure
1. Enter system view.
system-view
2. Specify the preferred location for the AC to obtain an AP image file.
wlan image-load filepath { local | ram }
By default, the AC prefers the AP image file stored in the RAM when assigning a software version to an AP.
Deploying an image file to online APs
About this task
This feature enables you to upgrade the image of all the online APs. For the upgrade to take effect, reboot the APs after upgrade.
Procedure
1. Enter system view.
system-view
2. Deploy an image file to all the online APs.
wlan ap-image-deploy
Configuring remote configuration synchronization
|
|
NOTE: Support for this feature depends on the AP model. |
About remote configuration synchronization
To update APs' configuration file or configure features that require a configuration file, you can use the map-configuration command to deploy a configuration file to APs. However, you must write related commands to the configuration file before deployment. This is time-consuming and is not applicable to a network with a large number of APs to deploy.
This feature enables the AC to directly synchronize AP settings such as VLAN, link aggregation, and port isolation changes to online APs.
Tasks at a glance
To configure remote configuration synchronization, perform the following tasks:
1. Creating a Layer 2 aggregate interface
2. Assigning an interface to a Layer 2 aggregation group
4. Configuring basic VLAN settings
5. Assigning a port to a VLAN
¡ Assigning an access port to a VLAN
¡ Assigning a trunk port to VLANs
¡ Assigning a hybrid port to VLANs
¡ Setting the trusted packet priority type
6. Synchronizing settings to online APs
Creating a Layer 2 aggregate interface
Restrictions and guidelines
When you create a Layer 2 aggregate interface, the system automatically creates a Layer 2 aggregation group with the same number. The aggregation group operates in static aggregation mode by default.
Aggregation mode change might cause Selected member ports to become Unselected. When you change the aggregation mode, make sure you understand the impact of the change on services.
The configuration will be synchronized to all online APs after remote configuration synchronization is activated.
Procedure
1. Enter system view.
system-view
2. Enter AP view or an AP group's AP model view.
¡ Enter AP view.
wlan ap ap-name
¡ Execute the following commands in sequence to enter an AP group's AP model view:
wlan ap-group group-name
ap-model ap-model
3. Create a Layer 2 aggregate interface and enter its view.
bridge-aggregation interface-number
4. Set the aggregation mode of an aggregation group and set the LACP state.
link-aggregation mode { dynamic | static }
By default:
¡ In an AP's Layer 2 aggregate interface view, the AP uses the configuration in an AP group's Layer 2 aggregate interface view.
¡ In an AP group's Layer 2 aggregate interface view, an aggregation group operates in static aggregation mode.
Assigning an interface to a Layer 2 aggregation group
Restrictions and guidelines
A Layer 2 Ethernet interface can be assigned only to a Layer 2 aggregation group and an Ethernet interface can belong to only one aggregation group.
After joining an aggregation group, an interface inherits the settings configured for the group.
Before you perform this task, make sure the specified aggregation group already exists and the AP supports Layer 2 aggregate interfaces.
The configuration will be synchronized to all online APs after remote configuration synchronization is activated.
Procedure
1. Enter system view.
system-view
2. Enter AP view or an AP group's AP model view.
¡ Enter AP view.
wlan ap ap-name
¡ Execute the following commands in sequence to enter an AP group's AP model view:
wlan ap-group group-name
ap-model ap-model
3. Enter Layer 2 Ethernet interface view or 2.5G Ethernet interface view.
¡ Enter GigabitEthernet interface view.
gigabitethernet interface-number
¡ Enter 2.5G Ethernet interface view.
smartrate-ethernet interface-number
4. Assign an interface to an aggregation group.
port link-aggregation group group-id
By default:
¡ In an AP's Layer 2 Ethernet interface view, the AP uses the configuration in an AP group's Layer 2 Ethernet interface view.
¡ In an AP group's Layer 2 Ethernet interface view, an interface does not belong to an aggregation group.
¡ In an AP's 2.5G Ethernet interface view, the AP uses the configuration in an AP group's 2.5G Ethernet interface view.
¡ In an AP group's 2.5G Ethernet interface view, an interface does not belong to an aggregation group.
Configuring port isolation
Restrictions and guidelines
The configuration in Layer 2 Ethernet interface view applies only to the interface.
The configuration in Layer 2 aggregate interface view applies to the Layer 2 aggregate interface and its aggregation member ports. If the device fails to apply the configuration to the aggregate interface, it does not assign any aggregation member port to the isolation group. If the failure occurs on an aggregation member port, the device skips the port and continues to assign other aggregation member ports to the isolation group.
The configuration will be synchronized to all online APs after remote configuration synchronization is activated.
Procedure
1. Enter system view.
system-view
2. Enter AP view or an AP group's AP model view.
¡ Enter AP view.
wlan ap ap-name
¡ Execute the following commands in sequence to enter an AP group's AP model view:
wlan ap-group group-name
ap-model ap-model
3. Enter Layer 2 Ethernet interface view, Layer 2 aggregate interface view, or 2.5G Ethernet interface view.
¡ Enter Layer 2 Ethernet interface view.
gigabitethernet interface-number
¡ Enter Layer 2 aggregate interface view.
bridge-aggregation interface-number
¡ Enter 2.5G Ethernet interface view.
smartrate-ethernet interface-number
4. Configure port isolation.
port-isolate { enable | disable }
By default:
¡ In an AP's Layer 2 Ethernet interface view, a port uses the configuration in an AP group's Layer 2 Ethernet interface view.
¡ In an AP group's Layer 2 Ethernet interface view, port isolation is enabled.
¡ In an AP's Layer 2 aggregate interface view, a port uses the configuration in an AP group's Layer 2 aggregate interface view.
¡ In an AP group's Layer 2 aggregate interface view, port isolation is enabled.
¡ In an AP's 2.5G Ethernet interface view, a port uses the configuration in an AP group's 2.5G Ethernet interface view.
¡ In an AP group's 2.5G Ethernet aggregate interface view, port isolation is enabled.
Configuring basic VLAN settings
Restrictions and guidelines
You cannot create or delete VLAN 1 (the default VLAN) or reserved VLANs.
The configuration will be synchronized to all online APs after remote configuration synchronization is activated.
Procedure
1. Enter system view.
system-view
2. Enter AP view or AP group view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
3. (Optional.) Create a VLAN and enter its view, or create a list of VLANs.
vlan { vlan-id1 [ to vlan-id2 ] | all }
By default, only VLAN 1 (the system default VLAN) exists.
4. Enter VLAN view.
vlan vlan-id
To configure a VLAN after you create a list of VLANs, you must perform this step.
5. Assign a name to the VLAN.
name text
By default:
¡ In an AP's VLAN view, a VLAN uses the configuration in an AP group's VLAN view.
¡ In an AP group's VLAN view, the name of a VLAN is VLAN vlan-id. The vlan-id argument specifies the VLAN ID in a four-digit format. If the VLAN ID has less than four digits, leading zeros are added. For example, the name of VLAN 100 is VLAN 0100.
6. Configure the description of the VLAN.
description text
By default:
¡ In an AP's VLAN view, a VLAN uses the configuration in an AP group's VLAN view.
¡ In an AP group's VLAN view, the description of a VLAN is VLAN vlan-id. The vlan-id argument specifies the VLAN ID in a four-digit format. If the VLAN ID has less than four digits, leading zeros are added. For example, the default description of VLAN 100 is VLAN 0100.
Assigning an access port to a VLAN
Restrictions and guidelines
The configuration will be synchronized to all online APs after remote configuration synchronization is activated.
Procedure
1. Enter system view.
system-view
2. Enter AP view or an AP group's AP model view.
¡ Enter AP view.
wlan ap ap-name
¡ Execute the following commands in sequence to enter an AP group's AP model view:
wlan ap-group group-name
ap-model ap-model
3. Enter Layer 2 Ethernet interface view, 2.5G Ethernet interface view, or Layer 2 aggregate interface view.
¡ Enter GigabitEthernet interface view.
gigabitethernet interface-number
¡ Enter 2.5G Ethernet interface view.
smartrate-ethernet interface-number
¡ Enter Layer 2 aggregate interface view.
bridge-aggregation interface-number
Use either command depending on AP models and network requirements.
4. Set the link type to access.
port link-type access
By default:
¡ In an AP's Layer 2 Ethernet interface view, a port uses the configuration in an AP group's Layer 2 Ethernet interface view.
¡ In an AP group's Layer 2 Ethernet interface view, all ports are access ports.
¡ In an AP's 2.5G Ethernet interface view, a port uses the configuration in an AP group's 2.5G Ethernet interface view.
¡ In an AP group's 2.5G Ethernet interface view, all ports are access ports.
¡ In an AP's Layer 2 aggregate interface view, a port uses the configuration in an AP group's Layer 2 aggregate interface view.
¡ In an AP group's Layer 2 aggregate interface view, all ports are access ports.
5. Assign the access port to a VLAN.
port access vlan vlan-id
By default:
¡ In an AP's Layer 2 Ethernet interface view, an access port uses the configuration in an AP group's Layer 2 Ethernet interface view.
¡ In an AP group's Layer 2 Ethernet interface view, an access port belongs to VLAN 1.
¡ In an AP's 2.5G Ethernet interface view, a port uses the configuration in an AP group's 2.5G Ethernet interface view.
¡ In an AP group's 2.5G Ethernet interface view, an access port belongs to VLAN 1.
¡ In an AP's Layer 2 aggregate interface view, a port uses the configuration in an AP group's Layer 2 aggregate interface view.
¡ In an AP group's Layer 2 aggregate interface view, an access port belongs to VLAN 1.
Make sure the VLAN has been created.
Assigning a trunk port to VLANs
Restrictions and guidelines
A trunk port can allow multiple VLANs. If you execute this command multiple times on a trunk port, the trunk port allows all the specified VLANs.
On a trunk port, packets from only the PVID can pass through untagged.
To prevent unauthorized VLAN users from accessing restricted resources through the port, use the port trunk permit vlan all command with caution.
The configuration will be synchronized to all online APs after remote configuration synchronization is activated.
Procedure
1. Enter system view.
system-view
2. Enter AP view or an AP group's AP model view.
¡ Enter AP view.
wlan ap ap-name
¡ Execute the following commands in sequence to enter an AP group's AP model view:
wlan ap-group group-name
ap-model ap-model
3. Enter Layer 2 Ethernet interface view, 2.5G Ethernet interface view, or Layer 2 aggregate interface view.
¡ Enter GigabitEthernet interface view.
gigabitethernet interface-number
¡ Enter 2.5G Ethernet interface view.
smartrate-ethernet interface-number
¡ Enter Layer 2 aggregate interface view.
bridge-aggregation interface-number
Use either command depending on AP models and network requirements.
4. Set the link type to trunk.
port link-type trunk
By default:
¡ In an AP's Layer 2 Ethernet interface view, a port uses the configuration in an AP group's Layer 2 Ethernet interface view.
¡ In an AP group's Layer 2 Ethernet interface view, all ports are access ports.
¡ In an AP's 2.5G Ethernet interface view, a port uses the configuration in an AP group's 2.5G Ethernet interface view.
¡ In an AP group's 2.5G Ethernet interface view, all ports are access ports.
¡ In an AP's Layer 2 aggregate interface view, a port uses the configuration in an AP group's Layer 2 aggregate interface view.
¡ In an AP group's Layer 2 aggregate interface view, all ports are access ports.
5. Assign the trunk port to the specified VLANs.
port trunk permit vlan { vlan-id-list | all }
By default:
¡ In an AP's Layer 2 Ethernet interface view, a trunk port uses the configuration in an AP group's Layer 2 Ethernet interface view.
¡ In an AP group's Layer 2 Ethernet interface view, a trunk port permits only VLAN 1.
¡ In an AP's 2.5G Ethernet interface view, a port uses the configuration in an AP group's 2.5G Ethernet interface view.
¡ In an AP group's 2.5G Ethernet interface view, a trunk port does not permit packets from any VLAN to pass through.
¡ In an AP's Layer 2 aggregate interface view, a trunk port uses the configuration in an AP group's Layer 2 aggregate interface view.
¡ In an AP group's Layer 2 aggregate interface view, a trunk port does not permit packets from any VLAN to pass through.
6. (Optional.) Set the PVID for the trunk port.
port trunk pvid vlan vlan-id
By default:
¡ In an AP's Layer 2 Ethernet interface view, a trunk port uses the configuration in an AP group's Layer 2 Ethernet interface view.
¡ In an AP group's Layer 2 Ethernet interface view, the PVID of a trunk port is VLAN 1.
¡ In an AP's 2.5G Ethernet interface view, a port uses the configuration in an AP group's 2.5G Ethernet interface view.
¡ In an AP group's 2.5G Ethernet interface view, the PVID of a trunk port is VLAN 1.
¡ In an AP's Layer 2 aggregate interface view, a trunk port uses the configuration in an AP group's Layer 2 aggregate interface view.
¡ In an AP group's Layer 2 aggregate interface view, the PVID of a trunk port is VLAN 1.
Assigning a hybrid port to VLANs
Restrictions and guidelines
You can use a nonexistent VLAN as the PVID of a hybrid port. When you delete the PVID of a hybrid port by using the undo vlan command, the PVID setting of the port does not change.
For correct packet transmission, set the same PVID for a hybrid port on an AP and the hybrid port on the switch connected to the AP.
To enable a hybrid port to transmit packets from its PVID, you must assign the hybrid port to the PVID by using the port hybrid vlan command.
The configuration will be synchronized to all online APs after remote configuration synchronization is activated.
Procedure
1. Enter system view.
system-view
2. Enter AP view or an AP group's AP model view.
¡ Enter AP view.
wlan ap ap-name
¡ Execute the following commands in sequence to enter an AP group's AP model view:
wlan ap-group group-name
ap-model ap-model
3. Enter Layer 2 Ethernet interface view, 2.5G Ethernet interface view, or Layer 2 aggregate interface view.
¡ Enter GigabitEthernet interface view:
gigabitethernet interface-number
¡ Enter 2.5G Ethernet interface view:
smartrate-ethernet interface-number
¡ Enter Layer 2 aggregate interface view.
bridge-aggregation interface-number
Use either command depending on AP models and network requirements.
4. Set the link type to hybrid.
port link-type hybrid
By default:
¡ In an AP's Layer 2 Ethernet interface view, a port uses the configuration in an AP group's Layer 2 Ethernet interface view.
¡ In an AP group's Layer 2 Ethernet interface view, all ports are access ports.
¡ In an AP's 2.5G Ethernet interface view, a port uses the configuration in an AP group's 2.5G Ethernet interface view.
¡ In an AP group's 2.5G Ethernet interface view, all ports are access ports.
¡ In an AP's Layer 2 aggregate interface view, a port uses the configuration in an AP group's Layer 2 aggregate interface view.
¡ In an AP group's Layer 2 aggregate interface view, all ports are access ports.
5. Assign the hybrid port to the specified VLANs.
port hybrid vlan vlan-id-list { tagged | untagged }
By default:
¡ In an AP's Layer 2 Ethernet interface view, a hybrid port uses the configuration in an AP group's Layer 2 Ethernet interface view.
¡ In an AP group's Layer 2 Ethernet interface view, a hybrid port is an untagged member of the VLAN to which the port belongs when its link type is access.
¡ In an AP's 2.5G Ethernet interface view, a port uses the configuration in an AP group's 2.5G Ethernet interface view.
¡ In an AP group's 2.5G Ethernet interface view, a hybrid port does not permit packets from any VLAN to pass through.
¡ In an AP's Layer 2 aggregate interface view, a hybrid port uses the configuration in an AP group's Layer 2 aggregate interface view.
¡ In an AP group's Layer 2 aggregate interface view, a hybrid port does not permit packets from any VLAN to pass through.
6. (Optional.) Set the PVID for the hybrid port.
port hybrid pvid vlan vlan-id
By default:
¡ In an AP's Layer 2 Ethernet interface view, a hybrid port uses the configuration in an AP group's Layer 2 Ethernet interface view.
¡ In an AP group's Layer 2 Ethernet interface view, the PVID of a hybrid port is the ID of the VLAN to which the port belongs when its link type is access.
¡ In an AP's 2.5G Ethernet interface view, a port uses the configuration in an AP group's 2.5G Ethernet interface view.
¡ In an AP group's 2.5G Ethernet interface view, the PVID of a hybrid port is the ID of the VLAN to which the port belongs when its link type is access.
¡ In an AP's Layer 2 aggregate interface view, a hybrid port uses the configuration in an AP group's Layer 2 aggregate interface view.
¡ In an AP group's Layer 2 aggregate interface view, the PVID of a hybrid port is 1.
Setting the trusted packet priority type
About this task
With a priority type and a port priority value specified for an interface, an AP assigns the priority of the specified type to all packets received on the interface.
The system supports the following trusted packet priority types:
· dot11e—Uses the 802.1e priority carried in packets for priority mapping.
· dscp—Uses the DSCP priority carried in packets for priority mapping.
Procedure
1. Enter system view.
system-view
2. Enter AP view or AP group's AP model view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group's AP model view.
wlan ap-group group-name
ap-model ap-model
3. Enter GigabitEthernet interface view, 2.5G Ethernet interface view, or Layer 2 aggregate interface view.
¡ Enter GigabitEthernet interface view.
gigabitethernet interface-number
¡ Enter 2.5G Ethernet interface view.
smartrate-ethernet interface-number
¡ Enter Layer 2 aggregate interface view.
bridge-aggregation interface-number
4. Set the trusted packet priority type.
qos trust { dot1p | dscp }
By default:
¡ In an AP's GigabitEthernet interface view, the AP uses the configuration in AP group view.
¡ In an AP group's GigabitEthernet interface view, no trusted packet priority type is set.
¡ In an AP's 2.5G Ethernet interface view, a port uses the configuration in an AP group's 2.5G Ethernet interface view.
¡ In an AP group's 2.5G Ethernet interface view, no trusted packet priority type is set.
¡ In an AP's Layer 2 aggregate interface view, the AP uses the configuration in AP group view.
¡ In an AP group's Layer 2 aggregate interface view, no trusted packet priority type is set.
Setting the port priority
About this task
With a priority type and a port priority value specified for an interface, an AP assigns the priority of the specified type to all packets received on the interface.
Procedure
1. Enter system view.
system-view
2. Enter AP view or AP group's AP model view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group's AP model view.
wlan ap-group group-name
ap-model ap-model
3. Enter GigabitEthernet interface view, 2.5G Ethernet interface view, or Layer 2 aggregate interface view.
¡ Enter GigabitEthernet interface view.
gigabitethernet interface-number
¡ Enter 2.5G Ethernet interface view.
smartrate-ethernet interface-number
¡ Enter Layer 2 aggregate interface view.
bridge-aggregation interface-number
4. Set the port priority.
qos priority priority-value
By default:
¡ In an AP's GigabitEthernet interface view, the AP uses the configuration in AP group view.
¡ In an AP group's GigabitEthernet interface view, the port priority is 0.
¡ In an AP's 2.5G Ethernet interface view, a port uses the configuration in an AP group's 2.5G Ethernet interface view.
¡ In an AP group's 2.5G Ethernet interface view, the port priority is 0.
¡ In an AP's Layer 2 aggregate interface view, the AP uses the configuration in AP group view.
¡ In an AP group's Layer 2 aggregate interface view, the port priority is 0.
Synchronizing settings to online APs
About this task
This feature enables the AC to directly synchronize AP settings such as VLAN, link aggregation, and port isolation changes to online APs.
Restrictions and guidelines
|
CAUTION: The remote configuration synchronization feature clears all VLAN, link aggregation, and port settings (except for port isolation settings) on online APs and issues the settings on the AC to the APs. Please use it with caution. |
This feature takes effect only when both remote configuration assignment and remote configuration synchronization are configured. If only remote configuration assignment is configured, the AC assigns only VLAN settings to the specified AP or AP group.
With remote configuration assignment enabled, APs request VLAN, link aggregation, and port settings from the AC automatically after coming online.
Remote configuration synchronization takes effect only when remote configuration assignment is enabled.
As a best practice, do not use both remote configuration synchronization and the map-configuration command on the AC. If you must use both of them on the AC, make sure the VLAN, link aggregation, and port isolation settings in the configuration file to be deployed do not conflict with the settings on the AC.
Procedure
1. Enter system view.
system-view
2. Enter AP view or AP group view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
3. Enable remote configuration assignment to assign VLAN settings to the AP.
remote-configuration enable
By default:
In AP view, an AP uses the configuration in AP group view.
In AP group view, remote configuration assignment is disabled.
4. Enable remote configuration synchronization.
remote-configuration synchronize
By default:
In AP view, an AP uses the configuration in AP group view.
In AP group view, remote configuration synchronization is disabled.
Configuring a CAPWAP tunnel
Configuring CAPWAP tunnel encryption
About this task
CAPWAP tunnel encryption uses the Datagram Transport Layer Security (DTLS) protocol to encrypt control and data packets transmitted over a CAPWAP tunnel.
When CAPWAP control tunnel encryption is enabled for an AP, the AC and the AP communicate as follows:
1. The AC sends a discovery response with the encryption flag to the AC.
2. The AP performs a DTLS handshake with the AC and then establishes a CAPWAP tunnel with the AC.
3. The AC and the AP encrypt control packets transmitted in the CAPWAP control tunnel after the DTLS handshake.
When CAPWAP data tunnel encryption is enabled for an AP, the AP exchanges encryption information including keys with the AC through the CAPWAP control tunnel upon receiving the first keepalive packet from the AC. After the exchange, the AC and the AP encrypt data packets transmitted in the CAPWAP data tunnel. Keepalive packets are not encrypted.
Restrictions and guidelines
After you enable CAPWAP control tunnel encryption, APs go offline and then come online again from the AC to re-establish CAPWAP tunnels.
CAPWAP control tunnel encryption requires a certificate. You can use the built-in certificate or specify a certificate for the AC. For the specified certificate to take effect, specify the certificate before enabling CAPWAP control tunnel encryption.
CAPWAP control tunnel encryption supports AP certificate verification to allow only APs with a matching certificate to come online. To use AP certificate verification, you must generate AP certificates, upload them to the AC, and execute the download file command to download the certificates to the corresponding APs. With the verification feature enabled, an AP can come online only when a certificate that uses the AP's MAC address as its CN exists on the AC.
Prerequisites
To use a non-built-in certificate, save the certificate, key, and CA certificate to the file system of the AC. These files can be in the .pem or .cer format.
Procedure
1. Enter system view.
system-view
2. Specify the certificate used for CAPWAP tunnel encryption.
wlan capwap encryption certificate cer-name key key-name ca ca-name
By default, the system uses the built-in certificate for CAPWAP tunnel encryption.
3. (Optional.) Enable AP certificate verification.
wlan ap-certificate verification
By default, AP certificate verification is disabled.
4. Enter AP view or AP group view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
5. Configure CAPWAP control tunnel encryption.
tunnel encryption { disable | enable }
By default:
¡ In AP view, an AP uses the configuration in AP group view.
¡ In AP group view, CAPWAP control tunnel encryption is disabled.
6. Configure CAPWAP data tunnel encryption.
data-tunnel encryption { disable | enable }
By default:
¡ In AP view, an AP uses the configuration in AP group view.
¡ In AP group view, CAPWAP data tunnel encryption is disabled.
Configuring CAPWAP tunnel latency detection
About this task
This feature enables an AC to detect the transmission latency of CAPWAP control frames or data frames from an AP to the AC and back.
This feature takes effect only on the master AC after a CAPWAP tunnel is established.
When an AP goes offline, CAPWAP tunnel latency detection automatically stops. To restart CAPWAP tunnel latency detection when the AP comes online, execute the tunnel latency-detect start command again.
To display CAPWAP tunnel latency information, use the display wlan tunnel latency ap name command.
Procedure
1. Enter system view.
system-view
2. Enter AP view.
wlan ap ap-name
3. Configure CAPWAP tunnel latency detection.
tunnel latency-detect { start | stop }
By default, CAPWAP tunnel latency detection is not started.
Setting the control tunnel keepalive timer for an AP
About this task
An AP sends echo requests to the AC at the specified echo interval to identify whether the CAPWAP control tunnel is operating correctly. The AC responds by sending echo responses. If the AP does not receive any echo responses before the keepalive timer expires, the AP terminates the connection. If the AC does not receive any echo requests before the keepalive timer expires, the AC terminates the connection.
The keepalive time is the echo interval multiplied by the maximum number of echo request transmission attempts. If the calculated value exceeds 120 seconds, the keepalive time is rounded to 120 seconds.
Restrictions and guidelines
Setting the echo interval to 0 seconds disables an AP from sending echo requests. This setting is for test use only. For correct AC and AP communication, do not set the echo interval to 0 seconds.
Procedure
1. Enter system view.
system-view
2. Enter AP view or AP group view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
3. Set the interval for the AP to send echo requests.
echo-interval interval
By default:
¡ In AP view, an AP uses the configuration in AP group view.
¡ In AP group view, the echo interval is 10 seconds.
4. Set the maximum number of echo request transmission attempts.
echo-count count
By default:
¡ In AP view, an AP uses the configuration in AP group view.
¡ In AP group view, the maximum number of echo request transmission attempts is 3.
Setting the data tunnel keepalive interval for an AP
About this task
An AP sends data channel keepalive packets to the AC at the specified keepalive intervals after a CAPWAP tunnel is established between the AP and the AC.
Procedure
1. Enter system view.
system-view
2. Enter AP view or AP group view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
3. Set the data tunnel keepalive interval.
keepalive-interval interval
By default:
¡ In AP view, an AP uses the configuration in AP group view.
¡ In AP group view, the data tunnel keepalive interval is 10 seconds.
Setting the maximum fragment size for CAPWAP packets
About this task
Perform this task to prevent intermediate devices from dropping packets between AC and AP if the AP connects to the AC across the Internet.
Any maximum fragment size modification takes effect immediately on online APs.
Procedure
1. Enter system view.
system-view
2. Enter AP view or AP group view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
3. Set the maximum fragment size for CAPWAP control or data packets.
fragment-size { control control-size | data data-size }
By default:
¡ In AP view, an AP uses the configuration in AP group view.
¡ In AP group view, the maximum fragment size for CAPWAP control packets and data packets is 1450 bytes and 1500 bytes, respectively.
Setting the TCP MSS for CAPWAP tunnels
About this task
Perform this task to set the value of the Maximum Segment Size (MSS) option in SYN packets transmitted over a CAPWAP tunnel.
The MSS option informs the receiver of the largest segment that the sender can accept. Each end announces its MSS during TCP connection establishment. If the size of a TCP segment is smaller than or equal to the MSS of the receiver, TCP sends the TCP segment without fragmentation. If not, TCP fragments the segment based on the receiver's MSS.
Procedure
1. Enter system view.
system-view
2. Set the TCP MSS for CAPWAP tunnels.
wlan tcp mss value
The default setting is 1460 bytes.
Specifying a region code
About this task
A region code determines characteristics such as available frequencies, available channels, and transmit power level. Set a valid region code before configuring an AP.
To prevent regulation violation caused by region code modification, lock the region code.
Procedure
1. Enter system view.
system-view
2. Enter AP view, AP group view, global configuration view, AP provision view, or AP group provision view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
¡ Enter global configuration view.
wlan global-configuration
¡ Execute the following commands in sequence to enter AP provision view:
wlan ap ap-name
provision
¡ Execute the following commands in sequence to enter AP group provision view:
wlan ap-group group-name
provision
3. Specify a region code.
region-code code
By default:
¡ In AP view, an AP uses the configuration in AP group view. If no region code exists in AP group view, the AP uses the configuration in global configuration view.
¡ In AP group view, an AP uses the configuration in global configuration view.
¡ In global configuration view, the region code is CN.
¡ In AP provision view, an AP uses the configuration in AP group provision view.
¡ In AP group provision view, no region code is specified.
4. (Optional.) Lock the region code.
region-code-lock enable
By default:
¡ In AP view, an AP uses the configuration in AP group view. If no region code exists in AP group view, the AP uses the configuration in global configuration view.
¡ In AP group view, an AP uses the configuration in global configuration view.
¡ In global configuration view, the region code is not locked.
5. Return to system view.
quit
6. Enter service template view.
wlan service-template service-template-name
7. (Optional.) Include or exclude region codes in beacon frames and probe responses and specify the installation environment type.
region-code-ie { disable | enable { any | indoor | outdoor } }
By default, beacon frames and probe responses contain region codes and the installation environment type is any.
Procedure
1. Enter system view.
system-view
2. Enter global configuration view.
wlan global-configuration
3. Specify a region code.
region-code code
By default, the region code is CN.
4. (Optional.) Lock the region code.
region-code-lock enable
By default, the region code is not locked.
5. Return to system view.
quit
6. Enter service template view.
wlan service-template service-template-name
7. (Optional.) Include or exclude region codes in beacon frames and probe responses and specify the installation environment type.
region-code-ie { disable | enable { any | indoor | outdoor } }
By default, beacon frames and probe responses contain region codes and the installation environment type is any.
Configuring AC request retransmission
About this task
The AC retransmits a request to an AP at the retransmission interval until the maximum number of request retransmission attempts is reached or a response is received.
Procedure
1. Enter system view.
system-view
2. Enter AP view or AP group view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
3. Set the maximum number of request retransmission attempts.
retransmit-count value
By default:
¡ In AP view, an AP uses the configuration in AP group view.
¡ In AP group view, the maximum number of request retransmission attempts is 3.
4. Set the interval at which an AC request is retransmitted.
retransmit-interval interval
By default:
¡ In AP view, an AP uses the configuration in AP group view.
¡ In AP group view, the retransmission interval is 5 seconds.
Preprovisioning APs
About AP preprovisioning
AP preprovisioning allows you to configure network settings for fit APs on an AC. The AC automatically assigns these settings to the fit APs in run state through CAPWAP tunnels in a batch. These settings will be saved in preprovisioned configuration file wlan_ap_prvs.xml on the APs. This reduces the workload in large WLAN networks.
Restrictions and guidelines
This feature takes effect only on master ACs. For information about master ACs, see "Configuring dual-link backup."
The save wlan ap-provision command has the same effect as the reset wlan ap provision command if no preprovisioned settings exist.
Tasks at a glance
To configure AP preprovisioning, perform the following tasks:
1. Configuring preprovisioned settings
Choose one of the following tasks:
¡ Configuring preprovisioned settings for an AP
¡ Configuring network settings for an AP group
2. Assigning preprovisioned settings to APs
3. (Optional.) Configuring auto loading of preprovisioned settings
Configuring preprovisioned settings for an AP
1. Enter system view.
system-view
2. Enter AP view.
wlan ap ap-name
3. Enable AP preprovisioning and enter AP provision view.
provision
By default, an AP uses the configuration in AP group provision view. If no configuration exists in AP group provision view, the AP uses the configuration in global provision view.
4. Specify an AC for the AP.
ac { host-name host-name | ip ipv4-address }
By default, an AP uses the configuration in AP group provision view. If no configuration exists in AP group provision view, the AP uses the configuration in global provision view.
5. Specify an IPv4 address for the management VLAN interface.
ip address ipv4-address { mask | mask-length }
By default, no IPv4 address is specified for the management VLAN interface.
6. Specify an IPv6 address for the management VLAN interface.
ipv6 address { ipv6-address prefix-length | ipv6-address/prefix-length }
By default, no IPv6 address is specified for the management VLAN interface.
7. Set the gateway IP address.
gateway { ip ipv4-address | ipv6 ipv6-address }
By default, no gateway IP address is specified for an AP.
8. Specify a DNS server.
dns server { ip ipv4-address | ipv6 ipv6-address }
By default, an AP uses the configuration in AP group provision view. If no configuration exists in AP group provision view, the AP uses the configuration in global provision view.
9. Set a DNS domain name suffix.
dns domain domain-name
By default, an AP uses the configuration in AP group provision view. If no configuration exists in AP group provision view, the AP uses the configuration in global provision view.
Configuring network settings for an AP group
1. Enter system view.
system-view
2. Enter AP group view.
wlan ap-group group-name
3. Enable AP preprovisioning and enter AP group provision view.
provision
By default, an AP uses the configuration in global provision view.
4. Specify an AC.
ac { host-name host-name | ip ipv4-address }
By default, an AP uses the configuration in global provision view.
5. Specify a DNS server.
dns server { ip ipv4-address | ipv6 ipv6-address }
By default, an AP uses the configuration in global provision view.
6. Set a domain name suffix for the DNS server.
dns domain domain-name
By default, an AP uses the configuration in global provision view.
Configuring global network settings
1. Enter system view.
system-view
2. Enter global configuration view.
wlan global-configuration
3. Enable AP preprovisioning and enter global provision view.
provision
By default, AP preprovisioning is disabled.
4. Specify an AC.
ac { host-name host-name | ip ipv4-address }
By default, no AC is specified for an AP.
5. Specify a DNS server.
dns server { ip ipv4-address | ipv6 ipv6-address }
By default, no DNS server is specified for an AP.
6. Set a domain name suffix for the DNS server.
dns domain domain-name
By default, no domain name suffix is set for a DNS server.
Assigning preprovisioned settings to APs
About this task
Perform this task to enable the AC to assign preprovisioned settings to an AP with which the AC has established a CAPWAP tunnel. The preprovisioned settings will be saved to configuration file wlan_ap_prvs.xml on the AP, and the settings will overwrite the network settings originally saved in the configuration file.
You can use the following methods to assign preprovisioned settings to an AP:
· Manual configuration—You save the preprovisioned settings to configuration file wlan_ap_prvs.xml on the AP after it comes online. The settings take effect immediately.
· Auto assignment of preprovisioned settings—The preprovisioned settings are assigned to an AP when it is coming online. The AP will establish a CAPWAP tunnel with the AC specified in the preprovisioned settings. For information about optimal AC selection , see "CAPWAP tunnel establishment."
Restrictions and guidelines
Manually assigned preprovisioned settings immediately take effect on an online AP. Modifying the AC address configuration in the configuration file of the AP will trigger a new optimal AC selection process. The AP will terminate the original CAPWAP tunnel and establish a CAPWAP tunnel with the new AC.
Saving the network settings to the configuration file on an AP
To save the network settings to preprovisioned configuration file wlan_ap_prvs.xml on the specified AP or all APs, execute the following command in any view:
save wlan ap provision { all | name ap-name }
Configuring auto assignment of preprovisioned settings
1. Enter system view.
system-view
2. Enter AP view or AP group view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
3. Configure auto assignment of preprovisioned settings for the AP.
provision auto-update { disable | enable }
By default:
In PA view, an AP uses the configuration in AP group view.
In AP group view, auto assignment of preprovisioned settings is disabled.
Enabling SNMP notifications
About this task
To report critical WLAN events to an NMS, enable SNMP notifications. For WLAN event notifications to be sent correctly, you must also configure SNMP as described in Network Management and Monitoring Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enable SNMP notifications.
¡ Enable SNMP notifications for AP management.
snmp-agent trap enable wlan ap
By default, SNMP notifications for AP management are disabled.
¡ Enable SNMP notifications for CAPWAP.
snmp-agent trap enable wlan capwap
By default, SNMP notifications for CAPWAP are disabled.
Maintaining APs
Resetting APs
To reset all APs or the specified AP, execute the following command in user view:
reset wlan ap { all | ap-group group-name | model model-name | name ap-name | native }
Renaming a manual AP
1. Enter system view.
system-view
2. Rename a manual AP.
wlan rename-ap ap-name new-ap-name
Managing the file system of an AP
About this task
You can perform the following tasks on an AC to manage files for an AP after the AP establishes a CAPWAP tunnel with the AC:
· View file information for the AP.
· Delete a file from the AP.
· Download an image file from the AC to the AP.
Restrictions and guidelines
This feature takes effect only on master ACs.
In an AC hierarchy, you must upload the image file to the storage media of the associated local AC before executing the download file command on the central AC.
Procedure
1. Display information about files or file folders on an AP.
display wlan ap name ap-name files
2. Enter system view.
system-view
3. Enter AP view.
wlan ap ap-name
4. Manage files on the AP.
¡ Delete a file from the AP.
delete file filename
¡ Download an image file to the AP.
download file file-name
Setting the statistics report interval
About this task
Perform this task to change the interval for an AP to report its statistics. You can use the statistics to monitor the operating status of radios on the AP.
Procedure
1. Enter system view.
system-view
2. Enter AP view or AP group view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
¡ Enter global configuration view.
wlan global-configuration
3. Set the statistics report interval.
statistics-interval interval
By default:
¡ In AP view, an AP uses the configuration in AP group view. If no configuration exists in AP group view, the AP uses the configuration in global configuration view.
¡ In AP group view, an AP uses the configuration in global configuration view.
¡ In global configuration view, the statistics report interval is 50 seconds.
Setting the statistics fast report interval
About this task
This task enables an AP to fast report specific statistics to the AC. APs can fast report only channel usage statistics to the AC.
Setting the interval to 0 disables an AP from fast reporting statistics to the AC.
Procedure
1. Enter system view.
system-view
2. Enter AP view or AP group view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
3. Set the interval at which an AP fast reports statistics to the AC.
statistics-interval fast-report fast-report-interval
By default:
¡ In AP view, an AP uses the configuration in AP group view.
¡ In AP group view, the fast report interval is 0 seconds. An AP does not fast report statistics to the AC.
Configuring auto loading of preprovisioned settings
About this task
Auto loading of preprovisioned settings ensures successful CAPWAP tunnel establishment between AP and AC. An AP uses the following procedure to discover an AC when you enable this feature:
1. Uses the preprovisioned settings to discover an AC that has the AP's manual or auto AP configuration.
2. Reboots and uses other methods to discover ACs if AC discovery fails.
3. Reboots and uses the preprovisioned settings again to discover ACs if the AP still fails to discover the target AC.
This AC discovery process will be repeated until the AP discovers the target AC to establish a CAPWAP tunnel.
Procedure
1. Enter system view.
system-view
2. Enter AP view or AP group view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
3. Configure auto loading of preprovisioned settings for the AP.
provision auto-recovery { disable | enable }
By default:
¡ In AP view, an AP uses the configuration in AP group view.
¡ In AP group view, auto loading of preprovisioned settings is enabled.
Setting a LED lighting mode
About this task
You can configure LEDs on an AP to flash in the following modes:
· quiet—All LEDs are off.
· awake—All LEDs flash once every minute. Support for this mode depends on the AP model.
· always-on—All LEDs are steady on. Support for this mode depends on the AP model.
· normal—How LEDs flash in this mode varies by AP model. This mode can identify the running status of an AP.
Restrictions and guidelines
If you set the LED lighting mode to awake or always-on in AP group view, the setting takes effect only on member APs that support the specified LED lighting mode.
Procedure
1. Enter system view.
system-view
2. Enter AP view or AP group view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
3. Set a LED lighting mode.
led-mode { always-on | awake | normal | quiet }
By default:
¡ In AP view, an AP uses the configuration in AP group view.
¡ In AP group view, the LED lighting mode is normal.
Specifying the uplink interface type for APs
About this task
An AP can use a dialer interface or VLAN interface as an uplink interface for connecting to the AC. You can perform this task to specify the uplink interface type.
If you specify the dialer type, an AP uses a dialer interface to connect to the AC unless no dialer interface is available or the IP address of the dialer interface cannot be obtained. If AC association with the VLAN interface also fails, the AP tries with the dialer interface and VLAN interface alternatively until a connection is established.
If you specify the VLAN type, an AP can only use a VLAN interface to connect to the AC.
Procedure
1. Enter system view.
system-view
2. Specify the uplink interface type for APs.
wlan up-link type { dialer | vlan }
By default, the uplink interface type is dialer.
Configuring advanced features for AP management
Configuring remote AP
About this task
Remote AP enables an AP to automatically perform the following operations when the CAPWAP tunnel to the AC is disconnected:
· Forward client traffic.
· Provide client access services if local authentication is enabled and association is enabled at the AP.
Remote AP is applicable to telecommuting, small branches, and SOHO solutions.
Restrictions and guidelines
Remote AP takes effect only on APs that operate in local forwarding mode.
When the tunnel between the AC and AP is recovered, clients that use the AC as the authenticator need reauthentication. Clients that use the AP as the authenticator remain online.
Procedure
1. Enter system view.
system-view
2. Enter AP view or AP group view.
¡ Enter AP view.
wlan ap ap-name
¡ Enter AP group view.
wlan ap-group group-name
3. Configure remote AP.
hybrid-remote-ap { disable | enable }
By default:
¡ In AP view, an AP uses the configuration in AP group view.
¡ In AP group view, remote AP is disabled.
Configuring AP power management
Configuring the default input power level
|
|
NOTE: Support for this feature depends on the AP model. |
About this task
Configure the default input power level for an AP in case the AP cannot obtain its input power level at startup.
An AP automatically detects power supply modes to obtain its input power level at startup. If the AP fails to obtain the input power level, it operates at the low power level before associating with an AC. After the association, it operates at the configured default input power level.
An AP can be powered through a power adapter or through its PoE or PoE+ ports. The following table shows the relationship between the AP's power supply mode and input power level:
|
Power supply mode |
Input power level |
|
· Power adapter. · Multiple PoE+ ports. · Combination of PoE and PoE+ ports. |
High |
|
· Single PoE+ port · Multiple PoE ports |
Middle |
|
Single PoE port |
Low |
An AP's support for MIMO modes and USB interfaces varies by input power level, as shown in Table 1.
Table 1 AP's support for MIMO modes and USB interfaces
|
Input power level |
Supported MIMO modes |
Whether USB interfaces can be enabled |
|
High |
1×1, 2×2, 3×3, and 4×4. |
Yes. |
|
Middle |
1×1, 2×2, 3×3, and 4×4. |
Yes when the MIMO mode is 1×1 or 2×2. |
|
Low |
1×1. |
No. |
Restrictions and guidelines
When you configure the default input power level for an AP, make sure the setting matches its power mode. An excessively low input power level prevents the AP from operating correctly. An excessively high input power level causes overload of the AP in case of power shortage.
Procedure
1. Enter system view.
system-view
2. Enter AP view or an AP group's AP model view.
¡ Enter AP view.
wlan ap ap-name
¡ Execute the following commands in sequence to enter an AP group's AP model view:
wlan ap-group group-name
ap-model ap-model
3. Configure the default input power level.
power-level default { high | low | middle }
By default:
¡ In AP view, an AP uses the configuration in an AP group's AP model view.
¡ In an AP group's AP model view, the default input power level is middle.
Enabling or disabling USB interfaces for APs
|
|
NOTE: Support for this feature depends on the AP model. |
About this task
After you enable USB interfaces for an AP, the USB interfaces become active only when either of the following requirements is met:
· The input power level of the AP is high.
· The input power level of the AP is middle and the MIMO mode is 1×1 or 2×2.
For information about input power levels, see "Configuring the default input power level." For information about MIMO modes, see "Configuring radio management."
Procedure
1. Enter system view.
system-view
2. Enter AP view or an AP group's AP model view.
¡ Enter AP view.
wlan ap ap-name
¡ Execute the following commands in sequence to enter an AP group's AP model view:
wlan ap-group group-name
ap-model ap-model
3. Enable or disable USB interfaces.
usb { enable | disable }
By default:
¡ In AP view, an AP uses the configuration in an AP group's AP model view.
¡ In an AP group's AP model view, USB interfaces are disabled.
Maintaining ACs
Configuring a description for the AC
1. Enter system view.
system-view
2. Configure a description for the AC.
wlan description text
By default, an AC does not have a description.
Enabling time zone synchronization
About this task
This feature enables APs to synchronize time and time zone information from the AC at association and at specific intervals after association.
Procedure
1. Enter system view.
system-view
2. Enable time zone synchronization.
wlan timezone-sync enable
By default, time zone synchronization is disabled.
Loading an APDB user script
About this task
This task allows you to add new AP models to the APDB without upgrading AC software.
Restrictions and guidelines
Make sure the user script is valid. Invalid scripts can cause loading failure.
The AP models in the user script must be different from the AP models in the system script.
If you load multiple user scripts on the AC, the most recently loaded user script overwrites the old user scripts.
To reload a user script when the following conditions exist, you must delete the related AP models or use the wlan apdb command to restore the original software version:
· A manual AP or an online auto AP whose model is listed in the old user script exists.
· APs of an AP model listed in the old user script have been added to an AP group.
· The old user script includes an AP model whose software version was already configured.
For more information about the wlan apdb command, see WLAN Command Reference.
To prevent AP model configuration lost after an AC reboot, you must reload a user script when you rename, or delete the user script in the file system.
When you replace a user script, the AP model configuration in the old user script will be lost upon an AC reboot if the new user script does not contain AP model configuration of the old script. In this case, you must reload the new user script.
Procedure
1. Enter system view.
system-view
2. Load an APDB user script.
wlan apdb file user.apdb
By default, no user script is loaded on the AC.
Enabling service anomaly detection
About this task
This feature enables an AC to check service status and start a reboot timer (10 minutes) upon detecting that no APs are associated with the AC. When the reboot timer expires, the AC restarts. If an AP comes online before the timer expires, the AC deletes the timer.
With this feature disabled, the AC cannot restart automatically if a service exception occurs. As a best practice, do not disable this feature.
Procedure
1. Enter system view.
system-view
2. Enable service anomaly detection.
wlan detect-anomaly enable
By default, service anomaly detection is disabled.
Disabling the WLAN function
About this task
|
CAUTION: Disabling the WLAN function logs off all online APs. Please use this feature with caution. |
This feature disables the device from providing WLAN services and releases ports used by CAPWAP and LWAPP tunnels.
Procedure
1. Enter system view.
system-view
2. Disable the WLAN function.
undo wlan enable
By default, the WLAN function is enabled.
Configuring an AP monitor group
About AP monitor groups
APs in an AP monitor group can report client quantity, radio traffic, channel usage, and AP anomalies to the AC.
Restrictions and guidelines
You can add a maximum of 32 APs to an AP monitor group.
Procedure
1. Enter system view.
system-view
2. Create an AP monitor group and enter its view.
wlan vip-ap-group
3. Add an AP to the AP monitor group.
ap-name ap-name
By default, no APs exist in an AP monitor group.
4. (Optional.) Set the interval at which the AP reports statistics to the AC.
report-interval interval
By default, an AP reports statistics to the AC at intervals of 50 seconds.
Display and maintenance commands for AP management
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display information about all APs or the specified AP. |
display wlan ap { all | name ap-name } [ verbose ] |
|
Display address information for all APs or the specified AP. |
display wlan ap { all | name ap-name } address |
|
Display the configuration status of the band navigation feature for all APs. |
display wlan ap all feature band-navigation |
|
Display configuration status of CAPWAP features. |
display wlan ap all feature capwap |
|
Display AP connection records on the AC. |
display wlan ap { all | name ap-name } connection-record |
|
Display AP descriptions on the AC. |
display wlan ap description |
|
Display GPS information for all APs or the specified AP. |
display wlan ap { all | name ap-name } gps |
|
Display AP group information for all APs or the specified AP. |
display wlan ap { all | name ap-name } group |
|
Display AP online duration. |
display wlan ap { all | name ap-name } online-time |
|
Display AP region code information. |
display wlan ap { all | name ap-name } region-code |
|
Display the reboot logs of the specified AP. |
display wlan ap name ap-name reboot-log |
|
Display running configuration for all APs or the specified AP. |
display wlan ap { all | ap ap-name } running-configuration [ verbose ] |
|
Display tunnel latency information for the specified CAPWAP tunnel. |
display wlan ap name ap-name tunnel latency |
|
Display association failure records for APs. |
display wlan ap statistics association-failure-record |
|
Display information about AP image downloading. |
display wlan ap statistics image-download [ failed | in-progress | succeeded ] |
|
Display online AP quantity records. |
display wlan ap statistics online-record [ datetime date time [ count count ] ] |
|
Display CAPWAP tunnel down records. |
display wlan ap statistics tunnel-down-record |
|
Display information about distribution of attached APs for ACs. |
In standalone mode: display wlan ap-distribution all In IRF mode: display wlan ap-distribution { all | slot slot-number } |
|
Display the attachment location of an AP. |
display wlan ap-distribution ap-name ap-name |
|
Display information about all AP groups or the specified AP group. |
display wlan ap-group [ brief | name group-name ] |
|
Display AP model information. |
display wlan ap-model { all | name model-name } |
|
Display the WLAN device role. |
display wlan device role |
|
Display the number of installed WLAN licenses. |
display wlan license |
|
Clear AP connection records on the AC. |
reset wlan ap { all | name ap-name } connection-record |
|
Delete configuration file wlan_ap_prvs.xml from all APs or the specified AP. |
reset wlan ap provision { all | name ap-name } |
|
Clear the reboot logs of all APs or the specified AP. |
reset wlan ap reboot-log { all | name ap-name } |
|
Clear tunnel latency information for all CAPWAP tunnels or the specified CAPWAP tunnel. |
reset wlan tunnel latency ap { all | name ap-name } |
AP management configuration examples
Example: Establishing a CAPWAP tunnel through DHCP
Network configuration
As shown in Figure 3, configure the AP to obtain its IP address and AC IP address from the DHCP server through DHCP Option 43. The AP uses the IP address of the AC to establish a CAPWAP tunnel with the AC.
Procedure
1. Configure the DHCP server:
# Enable the DHCP service.
[DHCP server] dhcp enable
# Configure DHCP address pool 1.
[DHCP server] dhcp server ip-pool 1
[DHCP server-dhcp-pool-1] network 1.1.1.0 mask 255.255.255.0
# Configure Option 43 to specify the IP address of the AC in address pool 0. The right-most bytes 01010103 (1.1.1.3) represent the IP address of the AC.
[DHCP server-dhcp-pool-1] option 43 hex 800700000101010103
[DHCP Server-dhcp-pool-1] quit
[DHCP Server] quit
2. Configure the AC:
# Set the IP address of VLAN-interface 1 on the AC to 1.1.1.3/24.
[AC] interface vlan-interface 1
[AC-Vlan-interface1] ip address 1.1.1.3 24
[AC-Vlan-interface1] quit
# Create an AP named ap1 with model WA4320i-ACN, and set its serial ID to 210235A1BSC123000050.
[AC] wlan ap ap1 model WA4320i-ACN
[AC-wlan-ap-ap1] serial-id 210235A1BSC123000050
[AC-wlan-ap-ap1] quit
# Start up the AP. The AP performs the following operations:
¡ Obtains its IP address 1.1.1.2 from the DHCP server.
¡ Obtains the IP address of the AC through Option 43.
¡ Establishes a CAPWAP tunnel with the AC.
Verifying the configuration
# Verify that you can see the following information:
· The AP obtains the IP address of the AC through DHCP.
· The AP and the AC have established a CAPWAP tunnel.
· The AP is in Run state.
[AC] display wlan ap name ap1 verbose
AP name : ap1
AP ID : 1
AP group name : default-group
State : Run
Backup type : Master
Online time : 0 days 1 hours 25 minutes 12 seconds
System up time : 0 days 2 hours 22 minutes 12 seconds
Model : WA4320i-ACN
Region code : CN
Region code lock : Disable
Serial ID : 210235A1BSC123000050
MAC address : 0AFB-423B-893C
IP address : 1.1.1.2
UDP port number : 18313
H/W version : Ver.C
S/W version : E2321
Boot version : 1.01
USB state : N/A
Power level : N/A
Power info : N/A
Description : wtp1
Priority : 4
Echo interval : 10 seconds
Echo count : 3 counts
Keepalive interval : 10 seconds
Discovery-response wait-time : 2 seconds
Statistics report interval : 50 seconds
Fragment size (data) : 1500
Fragment size (control) : 1450
MAC type : Local MAC & Split MAC
Tunnel mode : Local Bridging & 802.3 Frame & Native Frame
CWPCAP data-tunnel status : Up
Discovery type : DHCP
Retransmission count : 3
Retransmission interval : 5 seconds
Firmware upgrade : Enabled
Sent control packets : 1
Received control packets : 1
Echo requests : 147
Lost echo responses : 0
Average echo delay : 3
Last reboot reason : User soft reboot
Latest IP address : 10.1.0.2
Current AC IP : N/A
Tunnel down reason : Request wait timer expired
Connection count : 1
Backup Ipv4 : Not configured
Backup Ipv6 : Not configured
Tunnel encryption : Disabled
Data-tunnel encryption : Disabled
Data-tunnel encryption state : Not encrypted
LED mode : Normal
Remote configuration : Enabled Radio 1:
Basic BSSID : 7848-59f6-3940
Admin state : Up
Radio type : 802.11ac
Antenna type : internal
Client dot11ac-only : Disabled
Client dot11n-only : Disabled
Channel bandwidth : 20/40/80MHz
Operating bandwidth : 20/40/80MHz
Secondary channel offset : SCB
Short GI for 20MHz : Supported
Short GI for 40MHz : Supported
Short GI for 80MHz : Supported
Short GI for 160MHz : Not supported
mimo : Not Config
Green-Energy-Management : Disabled
A-MSDU : Enabled
A-MPDU : Enabled
LDPC : Not Supported
STBC : Supported
Operational VHT-MCS Set:
Mandatory : Not configured
Supported : NSS1 0,1,2,3,4,5,6,7,8,9
NSS2 0,1,2,3,4,5,6,7,8,9
Multicast : Not configured
Operational HT MCS Set:
Mandatory : Not configured
Supported : 0, 1, 2, 3, 4, 5, 6, 7, 8, 9,
10, 11, 12, 13, 14, 15
Multicast : Not configured
Channel : 44(auto)
Channel usage(%) : 15
Max power : 20 dBm
Operational rate:
Mandatory : 6, 12, 24 Mbps
Multicast : Auto
Supported : 9, 18, 36, 48, 54 Mbps
Disabled : Not configured
Distance : 1 km
ANI : Enabled
Fragmentation threshold : 2346 bytes
Beacon interval : 100 TU
Protection threshold : 2346 bytes
Long retry threshold : 4
Short retry threshold : 7
Maximum rx duration : 2000 ms
Noise Floor : -102 dBm
Smart antenna : Enabled
Smart antenna policy : Auto
Protection mode : rts-cts
Continuous mode : N/A
HT protection mode : No protection
Radio 2:
Basic BSSID : 7848-59f6-3950
Admin state : Down
Radio type : 802.11n(2.4GHz)
Antenna type : internal
Client dot11n-only : Disabled
Channel bandwidth : 20/40MHz
Secondary channel offset : SCA
Channel auto-switch : Enabled
Short GI for 20MHz : Supported
Short GI for 40MHz : Supported
A-MSDU : Enabled
A-MPDU : Enabled
LDPC : Not Supported
STBC : Supported
Operational HT MCS Set:
Mandatory : Not configured
Supported : 0, 1, 2, 3, 4, 5, 6, 7, 8, 9,
10, 11, 12, 13, 14, 15, 16, 17,
18, 19, 20, 21, 22, 23, 24, 25,
26, 27, 28, 29, 30, 31
Multicast : Not configured
Channel : 5(auto)
Channel usage(%) : 0
Max power : 20 dBm
Preamble type : Short
Operational rate:
Mandatory : 1, 2, 5.5, 11 Mbps
Multicast : Auto
Supported : 6, 9, 12, 18, 24, 36, 48, 54 Mbps
Disabled : Not configured
Distance : 1 km
ANI : Enabled
Fragmentation threshold : 2346 bytes
Beacon interval : 100 TU
Protection threshold : 2346 bytes
Long retry threshold : 4
Short retry threshold : 7
Maximum rx duration : 2000 ms
Noise Floor : 0 dBm
Smart antenna : Enabled
Smart antenna policy : Auto
Protection mode : rts-cts
Continuous mode : N/A
HT protection mode : No protection
Example: Establishing a CAPWAP tunnel through DHCPv6
Network configuration
As shown in Figure 4, configure the AP to obtain its IP address and AC IP address from the DHCPv6 server through DHCP Option 52. The AP uses the IP address of the AC to establish a CAPWAP tunnel with the AC.
Procedure
1. Configure the DHCPv6 server:
# Assign an IPv6 address to GigabitEthernet 1/0/1.
<DHCPv6 Server> system-view
[DHCPv6 Server] interface gigabitethernet 1/0/1
[DHCPv6 Server-GigabitEthernet1/0/1] ipv6 address 1::1/64
# Disable RA message advertising suppression.
[DHCPv6 Server-GigabitEthernet1/0/1] undo ipv6 nd ra halt
# Set the managed address configuration flag (M) to 1 in RA advertisements to be sent.
[DHCPv6 Server-GigabitEthernet1/0/1] ipv6 nd autoconfig managed-address-flag
# Set the other stateful configuration flag (O) to 1 in RA advertisements to be sent.
[DHCPv6 Server-GigabitEthernet1/0/1] ipv6 nd autoconfig other-flag
# Enable the DHCPv6 service on GigabitEthernet 1/0/1.
[DHCPv6 Server-GigabitEthernet1/0/1] ipv6 dhcp select server
[DHCPv6 Server-GigabitEthernet1/0/1] quit
# Create a DHCPv6 address pool, and specify an IPv6 subnet for dynamic allocation in the DHCPv6 address pool.
[DHCPv6 Server] ipv6 dhcp pool 1
[DHCPv6 Server-dhcp6-pool-1] network 1::0/64
# Configure Option 52 that specifies an AC address 1::3 in DHCPv6 address pool 1.
[DHCPv6 Server-dhcp-pool-1] option 52 hex 00010000000000000000000000000003
[DHCPv6 Server-dhcp-pool-1] quit
[DHCPv6 Server] quit
2. Configure the AC:
# Set the IP address of VLAN-interface 1 to 1::3/64.
<AC> system-view
[AC] interface vlan-interface 1
[AC-Vlan-interface1] ipv6 address 1::3 64
# Create an AP named ap1 with model WA4320i-ACN, and set its serial ID to 210235A1BSC123000050.
[AC] wlan ap ap1 model WA4320i-ACN
[AC-wlan-ap-ap1] serial-id 210235A1BSC123000050
[AC-wlan-ap-ap1] quit
# Start up the AP. The AP performs the following operations:
¡ Obtains its IPv6 address 1::2 from the DHCP server.
¡ Obtains the IPv6 address of the AC through Option 52.
¡ Establishes a CAPWAP tunnel with the AC.
Verifying the configuration
# Verify that you can view the following information:
· The AP obtains the IP address of the AC through DHCP.
· The AP and the AC have established a CAPWAP tunnel.
· The AP is in Run state.
[AC] display wlan ap name ap1 verbose
AP name : ap1
AP ID : 1
AP group name : default-group
State : Run
Backup type : Master
Online time : 0 days 1 hours 25 minutes 12 seconds
System up time : 0 days 2 hours 22 minutes 12 seconds
Model : WA4320i-ACN
Region code : CN
Region code lock : Disable
Serial ID : 210235A1BSC123000050
MAC address : 0AFB-423B-893C
IP address : 1::2
UDP port number : 18313
H/W version : Ver.C
S/W version : E2321
Boot version : 1.01
USB state : N/A
Power level : N/A
Power info : N/A
Description : wtp1
Priority : 4
Echo interval : 10 seconds
Echo count : 3 counts
Keepalive interval : 10 seconds
Discovery-response wait-time : 2 seconds
Statistics report interval : 50 seconds
Fragment size (data) : 1500
Fragment size (control) : 1450
MAC type : Local MAC & Split MAC
Tunnel mode : Local Bridging & 802.3 Frame & Native Frame
CWPCAP data-tunnel status : Up
Discovery type : DHCP
Retransmission count : 3
Retransmission interval : 5 seconds
Firmware upgrade : Enabled
Sent control packets : 1
Received control packets : 1
Echo requests : 147
Lost echo responses : 0
Average echo delay : 3
Last reboot reason : User soft reboot
Latest IP address : 10.1.0.2
Current AC IP : N/A
Tunnel down reason : Request wait timer expired
Connection count : 1
Backup Ipv4 : Not configured
Backup Ipv6 : Not configured
Tunnel encryption : Disabled
Data-tunnel encryption : Disabled
Data-tunnel encryption state : Not encrypted
LED mode : Normal
Remote configuration : Enabled
Radio 1:
Basic BSSID : 7848-59f6-3940
Admin state : Up
Radio type : 802.11ac
Antenna type : internal
Client dot11ac-only : Disabled
Client dot11n-only : Disabled
Channel bandwidth : 20/40/80MHz
Operating bandwidth : 20/40/80MHz
Secondary channel offset : SCB
Short GI for 20MHz : Supported
Short GI for 40MHz : Supported
Short GI for 80MHz : Supported
Short GI for 160MHz : Not supported
mimo : Not Config
Green-Energy-Management : Disabled
A-MSDU : Enabled
A-MPDU : Enabled
LDPC : Not Supported
STBC : Supported
Operational VHT-MCS Set:
Mandatory : Not configured
Supported : NSS1 0,1,2,3,4,5,6,7,8,9
NSS2 0,1,2,3,4,5,6,7,8,9
Multicast : Not configured
Operational HT MCS Set:
Mandatory : Not configured
Supported : 0, 1, 2, 3, 4, 5, 6, 7, 8, 9,
10, 11, 12, 13, 14, 15
Multicast : Not configured
Channel : 44(auto)
Channel usage(%) : 15
Max power : 20 dBm
Operational rate:
Mandatory : 6, 12, 24 Mbps
Multicast : Auto
Supported : 9, 18, 36, 48, 54 Mbps
Disabled : Not configured
Distance : 1 km
ANI : Enabled
Fragmentation threshold : 2346 bytes
Beacon interval : 100 TU
Protection threshold : 2346 bytes
Long retry threshold : 4
Short retry threshold : 7
Maximum rx duration : 2000 ms
Noise Floor : -102 dBm
Smart antenna : Enabled
Smart antenna policy : Auto
Protection mode : rts-cts
Continuous mode : N/A
HT protection mode : No protection
Radio 2:
Basic BSSID : 7848-59f6-3950
Admin state : Down
Radio type : 802.11n(2.4GHz)
Antenna type : internal
Client dot11n-only : Disabled
Channel bandwidth : 20/40MHz
Secondary channel offset : SCA
Channel auto-switch : Enabled
Short GI for 20MHz : Supported
Short GI for 40MHz : Supported
A-MSDU : Enabled
A-MPDU : Enabled
LDPC : Not Supported
STBC : Supported
Operational HT MCS Set:
Mandatory : Not configured
Supported : 0, 1, 2, 3, 4, 5, 6, 7, 8, 9,
10, 11, 12, 13, 14, 15, 16, 17,
18, 19, 20, 21, 22, 23, 24, 25,
26, 27, 28, 29, 30, 31
Multicast : Not configured
Channel : 5(auto)
Channel usage(%) : 0
Max power : 0 dBm
Preamble type : Short
Operational rate:
Mandatory : 1, 2, 5.5, 11 Mbps
Multicast : Auto
Supported : 6, 9, 12, 18, 24, 36, 48, 54 Mbps
Disabled : Not configured
Distance : 1 km
ANI : Enabled
Fragmentation threshold : 2346 bytes
Beacon interval : 100 TU
Protection threshold : 2346 bytes
Long retry threshold : 4
Short retry threshold : 7
Maximum rx duration : 2000 ms
Noise Floor : 5 dBm
Smart antenna : Enabled
Smart antenna policy : Auto
Protection mode : rts-cts
Continuous mode : N/A
HT protection mode : No protection
Example: Establishing a CAPWAP tunnel through DNS
Network configuration
As shown in Figure 5, configure the AP to obtain the IP address of the AC through DNS to establish a CAPWAP tunnel with the AC.
Procedure
1. Configure the DHCP server:
# Enable the DHCP service, configure DHCP address pool 1, and set the domain name suffix of the AC to abc.
[DHCP server] dhcp enable
[DHCP server] dhcp server ip-pool 1
[DHCP server-dhcp-pool-1] network 1.1.1.0 mask 255.255.255.0
[DHCP server-dhcp-pool-1] domain-name abc
[DHCP server-dhcp-pool-1] dns-list 1.1.1.4
[DHCP server-dhcp-pool-1] gateway-list 1.1.1.2
[DHCP server-dhcp-pool-1] quit
[DHCP server] quit
2. Configure a mapping between domain name h3c.abc and IP address 2.1.1.1/24. For more information, see Layer 3—IP Services Configuration Guide. (Details not shown.)
3. Configure the AC:
# Set the IP address of VLAN-interface 1 to 2.1.1.1/24.
[AC] interface vlan-interface 1
[AC-Vlan-interface1] ip address 2.1.1.1 24
[AC-Vlan-interface1] quit
# Configure a default route with next hop address 2.1.1.2.
[AC] ip route-static 0.0.0.0 0 2.1.1.2
# Create an AP named ap1 with model WA4320i-ACN, and set its serial ID to 210235A1BSC123000050.
[AC] wlan ap ap1 model WA4320i-ACN
[AC-wlan-ap-ap1] serial-id 210235A1BSC123000050
# Start up the AP.
[AC-wlan-ap-ap1] quit
The AP performs the following operations:
¡ Obtains its IP address 1.1.1.1, the domain name suffix of the AC, and the IP address of the DNS server from the DHCP server.
¡ Adds the domain name suffix to the hostname.
¡ Informs the DNS client to translate the domain name into an IP address.
¡ Uses the IP address of the AC to establish a CAPWAP tunnel with the AC.
Verifying the configuration
# Verify that you can see the following information:
· The AP and the AC have established a CAPWAP tunnel.
· The AP is in Run state.
· The AP obtains the IP address of the AC through DNS.
[AC] display wlan ap name ap1 verbose
AP name : ap1
AP ID : 1
AP group name : default-group
State : Run
Backup type : Master
Online time : 0 days 1 hours 25 minutes 12 seconds
System up time : 0 days 2 hours 22 minutes 12 seconds
Model : WA4320i-ACN
Region code : CN
Region code lock : Disable
Serial ID : 210235A1BSC123000050
MAC address : 0AFB-423B-893C
IP address : 1.1.1.2
UDP port number : 18313
H/W version : Ver.C
S/W version : E2321
Boot version : 1.01
USB state : N/A
Power level : N/A
Power info : N/A
Description : wtp1
Priority : 4
Echo interval : 10 seconds
Echo count : 3 counts
Keepalive interval : 10 seconds
Discovery-response wait-time : 2 seconds
Statistics report interval : 50 seconds
Fragment size (data) : 1500
Fragment size (control) : 1450
MAC type : Local MAC & Split MAC
Tunnel mode : Local Bridging & 802.3 Frame & Native Frame
CWPCAP data-tunnel status : Up
Discovery type : DNS
Retransmission count : 3
Retransmission interval : 5 seconds
Firmware upgrade : Enabled
Sent control packets : 1
Received control packets : 1
Echo requests : 147
Lost echo responses : 0
Average echo delay : 3
Last reboot reason : User soft reboot
Latest IP address : 10.1.0.2
Current AC IP : N/A
Tunnel down reason : Request wait timer expired
Connection count : 1
Backup Ipv4 : Not configured
Backup Ipv6 : Not configured
Tunnel encryption : Disabled
Data-tunnel encryption : Disabled
Data-tunnel encryption state : Not encrypted
LED mode : Normal
Remote configuration : Enabled
Radio 1:
Basic BSSID : 7848-59f6-3940
Admin state : Up
Radio type : 802.11ac
Antenna type : internal
Client dot11ac-only : Disabled
Client dot11n-only : Disabled
Channel bandwidth : 20/40/80MHz
Operating bandwidth : 20/40/80MHz
Secondary channel offset : SCB
Short GI for 20MHz : Supported
Short GI for 40MHz : Supported
Short GI for 80MHz : Supported
Short GI for 160MHz : Not supported
mimo : Not Config
Green-Energy-Management : Disabled
A-MSDU : Enabled
A-MPDU : Enabled
LDPC : Not Supported
STBC : Supported
Operational VHT-MCS Set:
Mandatory : Not configured
Supported : NSS1 0,1,2,3,4,5,6,7,8,9
NSS2 0,1,2,3,4,5,6,7,8,9
Multicast : Not configured
Operational HT MCS Set:
Mandatory : Not configured
Supported : 0, 1, 2, 3, 4, 5, 6, 7, 8, 9,
10, 11, 12, 13, 14, 15
Multicast : Not configured
Channel : 44(auto)
Channel usage(%) : 15
Max power : 20 dBm
Operational rate:
Mandatory : 6, 12, 24 Mbps
Multicast : Auto
Supported : 9, 18, 36, 48, 54 Mbps
Disabled : Not configured
Distance : 1 km
ANI : Enabled
Fragmentation threshold : 2346 bytes
Beacon interval : 100 TU
Protection threshold : 2346 bytes
Long retry threshold : 4
Short retry threshold : 7
Maximum rx duration : 2000 ms
Noise Floor : -102 dBm
Smart antenna : Enabled
Smart antenna policy : Auto
Protection mode : rts-cts
Continuous mode : N/A
HT protection mode : No protection
Radio 2:
Basic BSSID : 7848-59f6-3950
Admin state : Down
Radio type : 802.11n(2.4GHz)
Antenna type : internal
Client dot11n-only : Disabled
Channel bandwidth : 20/40MHz
Secondary channel offset : SCA
Channel auto-switch : Enabled
Short GI for 20MHz : Supported
Short GI for 40MHz : Supported
A-MSDU : Enabled
A-MPDU : Enabled
LDPC : Not Supported
STBC : Supported
Operational HT MCS Set:
Mandatory : Not configured
Supported : 0, 1, 2, 3, 4, 5, 6, 7, 8, 9,
10, 11, 12, 13, 14, 15, 16, 17,
18, 19, 20, 21, 22, 23, 24, 25,
26, 27, 28, 29, 30, 31
Multicast : Not configured
Channel : 5(auto)
Channel usage(%) : 0
Max power : 20 dBm
Preamble type : Short
Operational rate:
Mandatory : 1, 2, 5.5, 11 Mbps
Multicast : Auto
Supported : 6, 9, 12, 18, 24, 36, 48, 54 Mbps
Disabled : Not configured
Distance : 1 km
ANI : Enabled
Fragmentation threshold : 2346 bytes
Beacon interval : 100 TU
Protection threshold : 2346 bytes
Long retry threshold : 4
Short retry threshold : 7
Maximum rx duration : 2000 ms
Noise Floor : 0 dBm
Smart antenna : Enabled
Smart antenna policy : Auto
Protection mode : rts-cts
Continuous mode : N/A
HT protection mode : No protection
Example: Configuring the auto AP feature
Network configuration
As shown in Figure 6, enable the auto AP feature on the AC. The AP obtains the AC IP address through DHCP Option 43 and establishes a CAPWAP tunnel with the AC.
Procedure
1. Configure the DHCP server:
# Enable the DHCP service.
<DHCP server> system-view
[DHCP server] dhcp enable
# Configure DHCP address pool 1.
[DHCP server] dhcp server ip-pool 1
[DHCP server-dhcp-pool-1] network 1.1.1.0 mask 255.255.255.0
# Configure Option 43 to specify the IP address of the AC in address pool 0. The right-most bytes 02010102 (2.1.1.2) represent the IP address of the AC.
[DHCP server-dhcp-pool-1] option 43 ip-address hex 800700000102010102
[DHCP Server-dhcp-pool-1] gateway-list 1.1.1.3
[DHCP Server-dhcp-pool-1] quit
[DHCP Server] quit
2. Configure the AC:
# Set the IP address of VLAN-interface 1 on the AC to 2.1.1.2/24.
[AC] interface vlan-interface 1
[AC-Vlan-interface1] ip address 2.1.1.2 24
[AC-Vlan-interface1] quit
# Configure a default route with next hop address 2.1.1.1.
[AC] ip route-static 0.0.0.0 0 2.1.1.1
# Enable auto AP.
[AC] wlan auto-ap enable
Verifying the configuration
# Verify that the AP has established a CAPWAP tunnel with the AC.
[AC] display wlan ap name 0011-2200-0101 verbose
AP name : 0011-2200-0101
AP ID : 1
AP group name : default-group
State : Run
Backup type : Master
Online time : 0 days 1 hours 25 minutes 12 seconds
System up time : 0 days 2 hours 22 minutes 12 seconds
Model : WA4320i-ACN
Region code : CN
Region code lock : Disable
Serial ID : 219801A0CNC138011454
MAC address : 0011-2200-0101
IP address : 1.1.1.2
UDP port number : 18313
H/W version : Ver.C
S/W version : E2321
Boot version : 1.01
USB state : N/A
Power level : N/A
Power info : N/A
Description : wtp1
Priority : 4
Echo interval : 10 seconds
Echo count : 3 counts
Keepalive interval : 10 seconds
Discovery-response wait-time : 2 seconds
Statistics report interval : 50 seconds
Fragment size (data) : 1500
Fragment size (control) : 1450
MAC type : Local MAC & Split MAC
Tunnel mode : Local Bridging & 802.3 Frame & Native Frame
CWPCAP data-tunnel status : Up
Discovery type : DHCP
Retransmission count : 3
Retransmission interval : 5 seconds
Firmware upgrade : Enabled
Sent control packets : 1
Received control packets : 1
Echo requests : 147
Lost echo responses : 0
Average echo delay : 3
Last reboot reason : User soft reboot
Latest IP address : 10.1.0.2
Current AC IP : N/A
Tunnel down reason : Request wait timer expired
Connection count : 1
Backup Ipv4 : Not configured
Backup Ipv6 : Not configured
Tunnel encryption : Disabled
Data-tunnel encryption : Disabled
Data-tunnel encryption state : Not encrypted
LED mode : Normal
Remote configuration : Enabled
Radio 1:
Basic BSSID : 7848-59f6-3940
Admin state : Up
Radio type : 802.11ac
Antenna type : internal
Client dot11ac-only : Disabled
Client dot11n-only : Disabled
Channel bandwidth : 20/40/80MHz
Operating bandwidth : 20/40/80MHz
Secondary channel offset : SCB
Short GI for 20MHz : Supported
Short GI for 40MHz : Supported
Short GI for 80MHz : Supported
Short GI for 160MHz : Not supported
mimo : Not Config
Green-Energy-Management : Disabled
A-MSDU : Enabled
A-MPDU : Enabled
LDPC : Not Supported
STBC : Supported
Operational VHT-MCS Set:
Mandatory : Not configured
Supported : NSS1 0,1,2,3,4,5,6,7,8,9
NSS2 0,1,2,3,4,5,6,7,8,9
Multicast : Not configured
Operational HT MCS Set:
Mandatory : Not configured
Supported : 0, 1, 2, 3, 4, 5, 6, 7, 8, 9,
10, 11, 12, 13, 14, 15
Multicast : Not configured
Channel : 44(auto)
Channel usage(%) : 15
Max power : 20 dBm
Operational rate:
Mandatory : 6, 12, 24 Mbps
Multicast : Auto
Supported : 9, 18, 36, 48, 54 Mbps
Disabled : Not configured
Distance : 1 km
ANI : Enabled
Fragmentation threshold : 2346 bytes
Beacon interval : 100 TU
Protection threshold : 2346 bytes
Long retry threshold : 4
Short retry threshold : 7
Maximum rx duration : 2000 ms
Noise Floor : -102 dBm
Smart antenna : Enabled
Smart antenna policy : Auto
Protection mode : rts-cts
Continuous mode : N/A
HT protection mode : No protection
Radio 2:
Basic BSSID : 7848-59f6-3950
Admin state : Down
Radio type : 802.11b
Antenna type : internal
Client dot11n-only : Disabled
Channel bandwidth : 20MHz
Operating bandwidth : 20MHz
Secondary channel offset : SCN
Short GI for 20MHz : Supported
Short GI for 40MHz : Supported
A-MSDU : Enabled
A-MPDU : Enabled
LDPC : Not Supported
STBC : Supported
Operational HT MCS Set:
Mandatory : Not configured
Supported : 0, 1, 2, 3, 4, 5, 6, 7, 8, 9,
10, 11, 12, 13, 14, 15
Multicast : Not configured
Channel : 5(auto)
Channel usage(%) : 0
Max power : 20 dBm
Preamble type : Short
Operational rate:
Mandatory : 1, 2, 5.5, 11 Mbps
Multicast : Auto
Supported : 6, 9, 12, 18, 24, 36, 48, 54 Mbps
Disabled : Not configured
Distance : 1 km
ANI : Enabled
Fragmentation threshold : 2346 bytes
Beacon interval : 100 TU
Protection threshold : 2346 bytes
Long retry threshold : 4
Short retry threshold : 7
Maximum rx duration : 2000 ms
Noise Floor : 0 dBm
Smart antenna : Enabled
Smart antenna policy : Auto
Protection mode : rts-cts
Continuous mode : N/A
HT protection mode : No protection
Example: Configuring AP groups
Network configuration
As shown in Figure 7, configure AP groups and add AP 1 to AP group group1, and AP 2, AP 3, and AP 4 to AP group group2.
Procedure
1. Configure APs to obtain their IP addresses and the AC IP address from the DHCP server. (Details not shown.)
2. Configure manual APs. (Details not shown.)
3. Configure AP groups:
# Create an AP group named group1.
[AC] wlan ap-group group1
# Add AP 1 to AP group group1.
[AC-wlan-ap-group-group1] ap ap1
[AC-wlan-ap-group-group1] quit
# Create an AP group named group2.
# Add AP 2, AP 3, and AP 4 to AP group group2.
[AC-wlan-ap-group-group2] ap ap2 ap3 ap4
[AC-wlan-ap-group-group2] quit
[AC] quit
Verifying the configuration
# Verify that AP 1 is in AP group group1, and AP 2, AP 3, and AP 4 are in AP group group2.
[AC-wlan-ap-group-group2] display wlan ap-group
Total number of AP groups: 3
AP group name : default-group
Description : Not configured
AP model : Not configured
APs : Not configured
AP group name : group1
Description : Not configured
AP model : WA4320i-ACN
AP grouping rules:
AP name : ap1
Serial ID : Not configured
MAC address : Not configured
IPv4 address : Not configured
IPv6 address : Not configured
APs : ap1 (AP name)
AP group name : group2
Description : Not configured
AP model : WA4320i-ACN
AP grouping rules:
AP name : ap2, ap3, ap4
Serial ID : Not configured
MAC address : Not configured
IPv4 address : Not configured
IPv6 address : Not configured
APs : ap2 (AP name), ap3 (AP name), ap4 (AP name)