- Table of Contents
-
- 12-Security Configuration Guide
- 00-Preface
- 01-Security zone configuration
- 02-AAA configuration
- 03-802.1X configuration
- 04-MAC authentication configuration
- 05-Portal configuration
- 06-Port security configuration
- 07-User profile configuration
- 08-Password control configuration
- 09-Keychain configuration
- 10-Public key management
- 11-PKI configuration
- 12-IPsec configuration
- 13-Group domain VPN configuration
- 14-SSH configuration
- 15-SSL configuration
- 16-SSL VPN configuration
- 17-ASPF configuration
- 18-APR configuration
- 19-mGRE configuration
- 20-Session management
- 21-Connection limit configuration
- 22-Object group configuration
- 23-Object policy configuration
- 24-Attack detection and prevention configuration
- 25-IP source guard configuration
- 26-ARP attack protection configuration
- 27-ND attack defense configuration
- 28-uRPF configuration
- 29-Crypto engine configuration
- 30-FIPS configuration
- 31-Application account auditing configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 27-ND attack defense configuration | 75.81 KB |
Contents
Configuring source MAC-based ND attack detection
About source MAC-based ND attack detection
Display and maintenance commands for source MAC-based ND attack detection
Configuring interface-based ND attack suppression
About interface-based ND attack suppression
Display and maintenance commands for interface-based ND attack suppression
Enabling source MAC consistency check for ND messages
Configuring ND attack defense
About ND attack defense
IPv6 Neighbor Discovery (ND) attack defense is able to identify forged ND messages to prevent ND attacks.
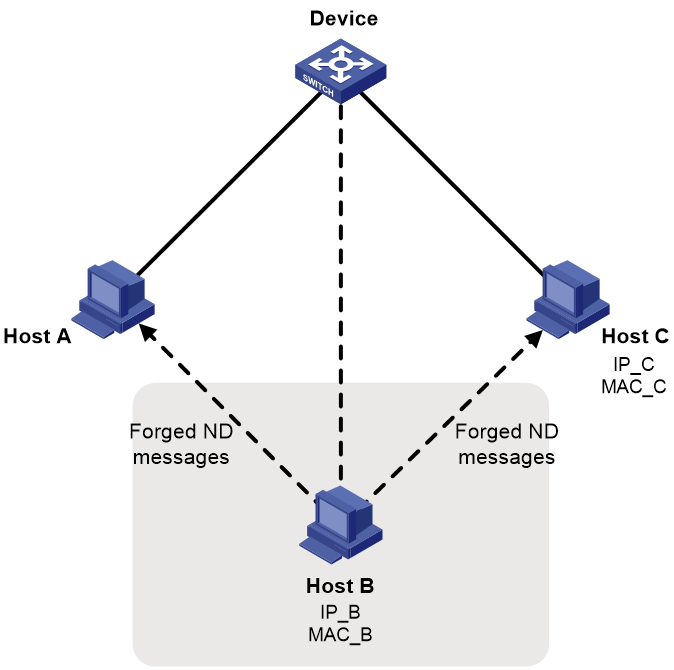
The IPv6 ND protocol does not provide any security mechanisms and is vulnerable to network attacks. As shown in Figure 1, an attacker can send the following forged ICMPv6 messages to perform ND attacks:
· Forged NS/NA/RS messages with an IPv6 address of a victim host. The gateway and other hosts update the ND entry for the victim with incorrect address information. As a result, all packets intended for the victim are sent to the attacking terminal.
· Forged RA messages with the IPv6 address of a victim gateway. As a result, all hosts attached to the victim gateway maintain incorrect IPv6 configuration parameters and ND entries.
Configuring source MAC-based ND attack detection
About source MAC-based ND attack detection
Source MAC-based ND attack detection checks the number of ND messages delivered to the CPU on a per source MAC basis. If the number of messages from the same MAC address within 5 seconds exceeds the threshold, the device generates an ND attack entry for the MAC address. The processing of the ND messages matching this entry depends on the detection mode. With ND logging enabled (by using the ipv6 nd check log enable command), source MAC-based ND attack detection processes the messages as follows:
· Filter mode—Filters out subsequent ND messages sent from the MAC address, and generates log messages.
· Monitor mode—Only generates log messages.
The device uses the entry aging time (fixed at 300 seconds) and the threshold to calculate a value:
The calculated value = (threshold/5) × 300
The device monitors the number of dropped packets for an entry. When the entry aging time is reached, it compares the number with the calculated value and takes actions accordingly:
· If the number of dropped packets is higher than or equal to the calculated value, the device resets the aging time for the entry.
· If the number of dropped packets is lower than the calculated value, the system deletes the entry and marks MAC address in the entry as a common MAC address.
Restrictions and guidelines
When you change the detection mode from monitor to filter, the filter mode takes effect immediately.
When you change the detection mode from filter to monitor, the device continues filtering messages that match existing attack entries.
Procedure
1. Enter system view.
system-view
2. Enable source MAC-based ND attack detection and set the detection mode.
ipv6 nd source-mac { filter | monitor }
By default, source MAC-based ND attack detection is disabled.
3. Set the threshold for source MAC-based ND attack detection.
ipv6 nd source-mac threshold threshold-value
The default setting is 30.
4. Enable the ND logging feature.
ipv6 nd check log enable
By default, the ND logging feature is disabled.
Display and maintenance commands for source MAC-based ND attack detection
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display the configuration of source MAC-based ND attack detection. |
display ipv6 nd source-mac configuration |
|
Display source MAC-based ND attack detection entries. |
In standalone mode: display ipv6 nd source-mac interface interface-type interface-number [ verbose ] display ipv6 nd source-mac { mac mac-address | vlan vlan-id } [ verbose ] display ipv6 nd source-mac [ count | verbose ] In IRF mode: display ipv6 nd source-mac interface interface-type interface-number [ slot slot-number ] [ verbose ] display ipv6 nd source-mac { mac mac-address | vlan vlan-id } slot slot-number [ verbose ] display ipv6 nd source-mac slot slot-number [ count | verbose ] |
|
Delete source MAC-based ND attack detection entries. |
In standalone mode: reset ipv6 nd source-mac [ interface interface-type interface-number | mac mac-address | vlan vlan-id ] In IRF mode: reset ipv6 nd source-mac [ interface interface-type interface-number | mac mac-address | vlan vlan-id ] [ slot slot-number ] |
Configuring interface-based ND attack suppression
About interface-based ND attack suppression
This feature rate limits ND request on each Layer 3 interface to prevent ND spoofing attacks. It monitors the number of ND requests that each Layer 3 interface received within 5 seconds. If the number on an interface exceeds the threshold, the device creates an ND attack suppression entry for the interface. During the suppression period (fixed at 300 seconds), the device drops ND messages received on this interface.
When the suppression time expires, the system examines the number of dropped ND messages on the interface within the suppression time:
· If the number is higher than or equal to the calculated value, the device resets the suppression time for the entry and continues ND suppression on the interface.
The calculated value = (threshold/5) × 300
· If the number is lower than the calculated value, the device deletes the suppression entry.
Restrictions and guidelines
As a best practice, enable this feature on the gateway.
Procedure
1. Enter system view.
system-view
2. Enable interface-based ND attack suppression.
ipv6 nd attack-suppression enable per-interface
By default, interface-based ND attack suppression is disabled.
3. Set the threshold for triggering ND attack suppression.
ipv6 nd attack-suppression threshold threshold-value
By default, the threshold for triggering ND attack suppression is 1000.
Display and maintenance commands for interface-based ND attack suppression
Execute display commands in any view.
|
Task |
Command |
|
Display the configuration of interface-based ND attack suppression. |
display ipv6 nd attack-suppression configuration |
|
Display interface-based ND attack suppression entries. |
In standalone mode: display ipv6 nd attack-suppression per-interface [ count | verbose ] In IRF mode: display ipv6 nd attack-suppression per-interface slot slot-number [ count | verbose ] |
|
Display interface-based ND attack suppression entries on an interface. |
display ipv6 nd attack-suppression per-interface interface interface-type interface-number [ verbose ] |
|
Delete interface-based ND attack suppression entries. |
In standalone mode: reset ipv6 nd attack-suppression per-interface [ interface interface-type interface-number ] In IRF mode: reset ipv6 nd attack-suppression per-interface [ interface interface-type interface-number ] [ slot slot-number ] |
|
Clear statistics for ND messages dropped by interface-based ND attack suppression. |
In standalone mode: reset ipv6 nd attack-suppression per-interface statistics [ interface interface-type interface-number ] In IRF mode: reset ipv6 nd attack-suppression per-interface statistics [ interface interface-type interface-number ] [ slot slot-number ] |
Enabling source MAC consistency check for ND messages
About this task
The source MAC consistency check feature is typically configured on gateways to prevent ND attacks.
This feature checks the source MAC address and the source link-layer address for consistency for each arriving ND message.
· If the source MAC address and the source link-layer address are not the same, the device drops the packet.
· If the addresses are the same, the device continues learning ND entries.
The ND logging feature logs source MAC inconsistency events, and it sends the log messages to the information center. The information center can then output log messages from different source modules to different destinations. For more information about the information center, see Network Management and Monitoring Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enable source MAC consistency check for ND messages.
ipv6 nd mac-check enable
By default, source MAC consistency check is disabled for ND messages.
3. (Optional.) Enable the ND logging feature.
ipv6 nd check log enable
By default, the ND logging feature is disabled.
As a best practice, disable the ND logging feature to avoid excessive ND logs.