- Table of Contents
-
- 03-Policies
- 01-Security policy
- 02-Attack defense
- 03-Connection limit
- 04-uRPF
- 05-NAT
- 06-AFT
- 07-Application audit
- 08-Bandwidth management
- 09-Load balancing common configuration
- 10-Server load balancing
- 11-Outbound link load balancing
- 12-Inbound link load balancing
- 13-Transparent DNS proxy
- 14-Application proxy
- 15-NetShare control
- 16-Security policy hit analysis
- 17-Security policy redundancy analysis
- 18-Global load balancing
- 19-IP reputation
- 20-NAT66
- 21-Server connection detection
- 22-Security policy optimization
- 23-Server load balancing
- 24-Load balancing common configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 05-NAT | 352.94 KB |
NAT
This help contains the following topics:
¡ NAT444
¡ General restrictions and guidelines
¡ Restrictions and guidelines: NAT policy
¡ Restrictions and guidelines: Dynamic NAT
¡ Restrictions and guidelines: Static NAT
¡ Restrictions and guidelines: NAT Server
¡ Restrictions and guidelines: Dynamic NAT444
¡ Restrictions and guidelines: Address availability test
Introduction
Network Address Translation (NAT) translates an IP address in the IP packet header to another IP address. Typically, NAT is configured on gateways to enable private hosts to access external networks and external hosts to access private network resources such as a Web server.
NAT policy
The NAT policy contains a set of NAT rules to identify and translate matching packets. The packet match criteria include source security zone, destination security zone, source IP address, and destination IP address, and service. The NAT policy supports the following translation methods:
· Source address translation—Translates the source IP address and source port of the packets. The NO-PAT and PAT modes are supported. For more information about NO-PAT and PAT, see "Dynamic NAT."
· Destination address translation—Translates the destination IP address and destination port of the packets. The NAT policy supports translating different destination IP addresses and destination ports of the matching packets to the same IP address and port.
· Bidirectional translation—Translates the source IP address, source port, destination IP address, and destination port of the packets. The source address translation supports NO-PAT and PAT modes. The destination address translation supports translating different destination IP addresses and destination ports of the matching packets to the same IP address and port.
Dynamic NAT
Dynamic NAT uses an address pool to translate addresses. It applies to the scenario where a large number of internal users access the external network.
· NO-PAT
Not Port Address Translation (NO-PAT) translates a private IP address to an IP public address. The public IP address cannot be used by another internal host until it is released.
NO-PAT supports all IP packets.
· PAT
A NAT address group is a set of address ranges. The source address in a packet destined for an external network is translated into an address in one of the address ranges.
NAT Server
The NAT Server feature maps a public address and port number to the private IP address and port number of an internal server. This feature allows servers in the private network to provide services for external users. The following table describes the address-port mappings between an external network and an internal network for NAT Server.
Table 1 Address-port mappings for NAT Server
|
External network |
Internal network |
|
One public address |
One private address |
|
One public address and one public port number |
One private address and one private port number |
|
One public address and N consecutive public port numbers |
· One private address and one private port number · N consecutive private addresses and one private port number · One private address and N consecutive private port numbers |
|
N consecutive public addresses |
· One private address · N consecutive private addresses |
|
N consecutive public addresses and one public port number |
· One private address and one private port number · N consecutive private addresses and one private port number · One private address and N consecutive private port numbers |
|
One public address and one public port number |
One internal server group |
|
One public address and N consecutive public port numbers |
|
|
N consecutive public addresses and one public port number |
|
|
Public addresses matching an ACL |
One private address |
|
One private address and one private port |
|
|
Public addresses in an address object group |
One private address |
|
One private address and one private port |
You can add multiple internal servers to an internal server group for load sharing so that these servers provide the same service for external hosts. The NAT device chooses one internal server based on the weight and number of connections of the servers to respond to a request from an external host to the public address of the internal server group.
Static NAT
Static NAT creates a fixed mapping between a private address and a public address. It supports connections initiated from internal users to external network and from external users to the internal network. Static NAT applies to regular communications.
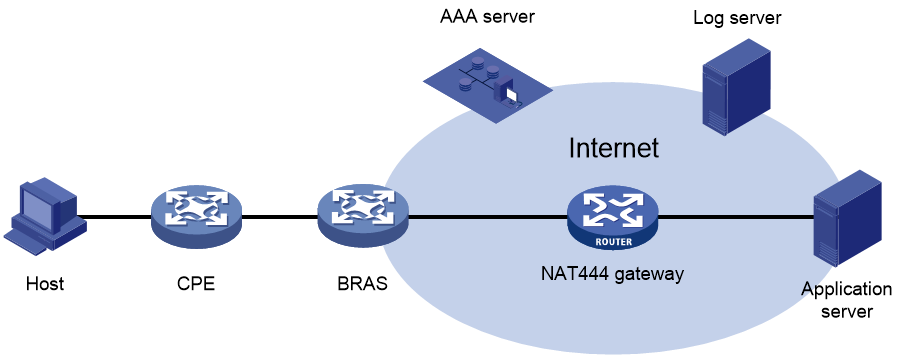
NAT444
NAT444 provides carrier-grade NAT by unifying the NAT444 gateway, AAA server, and log server. NAT444 introduces a second layer of NAT on the carrier side, with few changes on the customer side and the application server side. With port block assignment, NAT444 supports user tracking. It has become a preferred solution for carriers in transition to IPv6.
Figure 1 shows architecture of the NAT444 solution.
Figure 1 NAT444 solution architecture
Devices in this architecture provide services as follows:
· CPE—Performs customer-side address translation.
· BRAS—Provides endpoint access services and incorporates with the AAA server for authentication, authorization, and accounting.
· NAT444 gateway—Performs carrier-grade address translation.
· AAA server—Provides authentication, authorization, and accounting services.
· Log server—Records user access information and responds to user information queries.
NAT444 is a PAT translation based on port ranges. It maps multiple private IP addresses to one public IP address and uses a different port block for each private IP address. For example, the private IP address 10.1.1.1 of an internal host is mapped to the public IP address 202.1.1.1 and port block 10001 to 10256. When the internal host accesses public hosts, the source IP address 10.1.1.1 is translated to 202.1.1.1, and the source ports are translated to ports in the port block 10001 to 10256.
Static NAT444
The NAT gateway computes a static port block mapping before address translation. The mapping is between a private IP address and a public IP address with a port block.
When an internal user initiates a connection to the external network, the system performs the following operations:
· Locates a static mapping based on the private IP address of the user and obtains the public IP address and the port block in the mapping.
· Selects a public port number in the port block.
· Translates the private IP address to the public IP address and assigns the selected public port number.
The NAT gateway uses private IP addresses, public IP addresses, a port range, and a port block size to compute static mappings:
1. Divides the port range by the port block size to get the number of available port blocks for each public IP address.
This value is the base number for mapping.
2. Sorts the port blocks in ascending order of the start port number in each block.
3. Sorts the private IP addresses and the public IP addresses separately in ascending order.
4. Maps the first base number of private IP addresses to the first public IP address and its port blocks in ascending order.
For example, the number of available port blocks of each public IP address is m. The first m private IP addresses are mapped to the first public IP address and the m port blocks in ascending order. The next m private IP addresses are mapped to the second IP address and the m port blocks in ascending order. The other static port block mappings are created by analogy.
Dynamic NAT444
Dynamic NAT444 integrates functionalities of dynamic NAT and static NAT444. When an internal user initiates a connection to the external network, the dynamic NAT444 operates as follows:
1. Uses ACLs to implement translation control. It processes only packets that match an ACL permit rule.
2. Creates a mapping from the internal user's private IP address to a public IP address and a port block.
3. Translates the private IP address to the public IP address, and the source ports to ports in the selected port block for subsequent connections from the private IP address.
4. Withdraws the port block and deletes the dynamic port block mapping when all connections from the private IP address are disconnected.
Dynamic port block mapping supports port block extending. If the ports in the port block for a private address are all occupied, dynamic port block mapping translates the source port to a port in an extended port block.
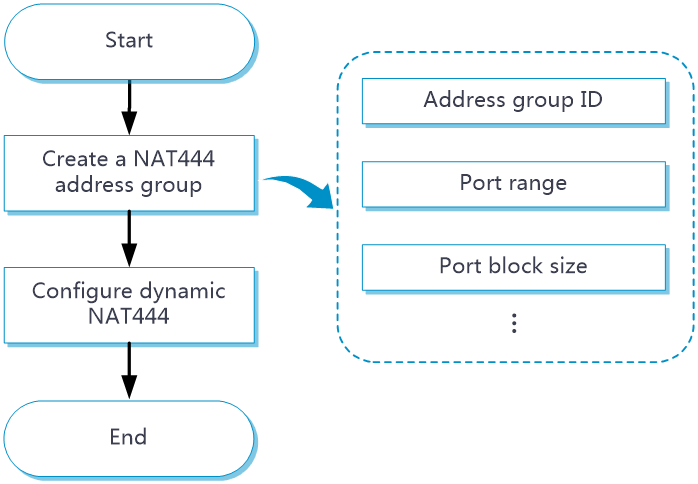
To configure dynamic NAT444, the following port block parameters are required in the NAT address group:
· Port range.
· Port block size.
· Number of extended port blocks.
NAT advanced settings
NAT address group
A NAT address group is used for dynamic NAT and can contain one or multiple IP address ranges and a port range.
· To configure dynamic NAT in PAT mode, you must add one or more IP address ranges and a port range to the address group. In addition, a port block size and the number of extended port blocks are required for dynamic NAT444.
· To configure dynamic NAT in NO-PAT mode, you only need to add one or multiple IP address ranges to the address group.
PAT mapping modes
The following PAT mapping modes are supported:
· Endpoint-Independent Mapping (EIM)—Uses the same IP and port mapping (EIM entry) for packets from the same source IP and port to any destinations. EIM allows external hosts to initiate connections to the translated IP addresses and ports of internal hosts. It allows internal hosts behind different NAT gateways to access each other.
· Address and Port-Dependent Mapping (APDM)—Uses different IP and port mappings for packets from the same source IP and port to different destination IP addresses and ports. APDM allows an external host to initiate connections to an internal host only under the condition that the internal host has previously accessed the external host. It is secure, but it does not allow internal hosts behind different NAT gateways to access each other.
NAT DNS mappings
With NAT DNS mappings, a user in the internal network can access internal servers by using their domain names when the DNS server is located on the public network. The NAT DNS mapping works in conjunction with NAT server mappings. A NAT DNS mapping maps the domain name of an internal server to the public IP address, public port number, and protocol type of the internal server. A NAT server mapping maps the public IP and port to the private IP and port of the internal server.
The DNS reply from the external DNS server contains only the domain name and public IP address of the internal server in the payload. The NAT interface might have multiple NAT server mappings with the same public IP address but different private IP addresses. DNS ALG might find an incorrect internal server by using only the public IP address. If a NAT DNS mapping is configured, DNS ALG can obtain the public IP address, public port number, and protocol type of the internal server by using the domain name. Then it can find the correct internal server by using the public IP address, public port number, and protocol type of the internal server.
NAT hairpin
NAT hairpin allows internal hosts to access each other through NAT. The source and destination IP address of the packets are translated on the interface connected to the internal network. NAT hairpin works in conjunction with NAT Server, outbound dynamic NAT, or outbound static NAT. To provide service correctly, you must configure NAT hairpin on the same interface module as its collaborative NAT feature.
NAT hairpin includes C/S and P2P modes:
· C/S—Allows internal hosts to access internal servers through NAT addresses. The destination IP address of the packet going to the internal server is translated by matching the NAT Server configuration. The source IP address is translated by matching the outbound dynamic or static NAT entries.
· P2P—Allows internal hosts to access each other through NAT. The internal hosts first register their public addresses to an external server. Then, the hosts communicate with each other by using the registered IP addresses. To configure the P2P mode, you must configure outbound PAT on the interface connected to the external network and enable the EIM mapping mode.
NAT ALG
NAT ALG (Application Level Gateway) translates address or port information in the application layer payloads to ensure connection establishment.
NAT global settings
On a WAN network where two output interfaces of the NAT device are in the same security zone, if the link of one interface fails, traffic is switched to the link of the other interface. The NAT device retains old session entries after link switchover. Internal users cannot access the external network because the NAT device uses old session entries to match the user traffic. To avoid this issue, enable NAT session recreation to ensure availability of NAT services. The device will recreate NAT sessions when user traffic arrives.
Address availability test
This feature uses NQA templates to probe the availability of addresses in a NAT address group. The probe process is as follows:
1. After you specify an NQA probe template for the NAT address group, the device periodically sends probe packets to the destination address specified in the NQA template. The device uses addresses in the NAT address group one by one as the source address of the probe packets.
2. If the device does not receive a reply for a probed address, the device excludes the address from the address pool and temporarily prohibits the address from being used for address translation.
3. The excluded IP address is used as the source IP address for the probe packet at the next probe period. The address can be used for address translation if the probe reply is received for it.
Restrictions and guidelines
General restrictions and guidelines
· If a packet matches both a NAT policy rule and a common rule (rule configured in static NAT, dynamic NAT, static NAT444, dynamic NAT444, or NAT server), the packet is translated as follows:
¡ For source and destination address translation method:
- If the translation methods of the NAT policy rule and the common NAT rule are the same, the device translates the packet by using the NAT policy rule.
- If the translation methods of the NAT policy rule and the common NAT rule are different, the device translates the packet by using the two rules.
¡ If the translation method of the NAT policy rule is bidirectional, the device translates the packet by using the NAT policy rule, and the common NAT rule does not take effect.
· Typically, configure inbound static NAT with outbound dynamic NAT, NAT Server, or outbound static NAT to implement bidirectional NAT.
· If you perform all the translation methods on an interface, the NAT rules are sorted in the following descending order:
a. NAT Server.
b. Static NAT.
c. NAT444 static port block mapping.
d. Dynamic NAT and NAT444 dynamic port block mapping.
Dynamic NAT and NAT444 dynamic port block mapping have the same priority. Dynamic NAT rules and NAT444 dynamic port block mapping rules are sorted in descending order of ACL numbers.
· When you add address ranges to a NAT address group, make sure address ranges do not overlap.
· For a distributed device, the number of IP addresses in all NAT address groups cannot be smaller than the number of security engines. Otherwise, some security engines cannot obtain NAT address resources.
Restrictions and guidelines: NAT policy
· By default, the NAT rules in the NAT policy are sorted in descending order of their configuration order. You can rearrange NAT rules to change their priorities. A rule has a higher priority than rules listed after it.
· A NAT or NAT444 address group cannot be used by both PAT and NO-PAT modes.
Restrictions and guidelines: Dynamic NAT
You can configure multiple outbound dynamic NAT rules on an interface.
· A NAT rule with an ACL takes precedence over a rule without any ACL.
· If two ACL-based dynamic NAT rules are configured, the rule with the higher ACL number has higher priority.
Restrictions and guidelines: Static NAT
· When you specify object groups, follow these restrictions and guidelines:
¡ The public or private IPv4 address object group can contain only one IPv4 address object.
¡ The quantity of IPv4 addresses in the private IPv4 address object group cannot be larger than that in the public IPv4 address object group.
¡ The object in the public IPv4 address object group cannot be an address range.
¡ For static NAT mappings to take effect, make sure address object groups in the mappings do not have excluded addresses.
¡ If you modify an address object group, the changes will be reflected in the static NAT mapping that uses it.
· You must specify a VRF if you deploy outbound static NAT in VPN networks. The specified VRF must be the VRF to which the NAT interface belongs.
· When you specify an ACL, follow these restrictions and guidelines:
¡ If you do not specify an ACL, the source addresses of all outgoing packets and the destination addresses of all incoming packets are translated.
¡ If you specify an ACL and do not specify the reverse address translation, the source addresses of outgoing packets permitted by the ACL are translated. The destination addresses of packets are not translated for connections actively initiated by external hosts to the internal hosts.
¡ If you specify both an ACL and the reverse address translation, the source addresses of outgoing packets permitted by the ACL are translated. If packets of connections actively initiated by external hosts to the internal hosts are permitted by ACL reverse matching, the destination addresses are translated. ACL reverse matching works as follows:
- Compares the source IP address/port of a packet with the destination IP addresses/ports in the ACL.
- Translates the destination IP address of the packet according to the mapping, and then compares the translated destination IP address/port with the source IP addresses/ports in the ACL.
Restrictions and guidelines: NAT Server
· When you configure a load shared NAT server mapping, you must make sure a user uses the same public address and public port to access the same service on an internal server. For this purpose, make sure value N in the following mappings is equal to or less than the number of servers in the internal server group:
¡ One public address and N consecutive public port numbers are mapped to one internal server group.
¡ N consecutive public addresses and one public port number are mapped to one internal server group.
· An internal server with a larger weight receives a larger percentage of connections in the internal server group.
· You must specify a VRF if you configure NAT server mappings in VPN networks. The specified VRF must be the VRF to which the NAT interface belongs.
· When you configure object group-based NAT server mappings, object groups for matching public addresses can only be IPv4 address object groups configured with subnets, IP address ranges, or host addresses. The IPv4 address object groups cannot have excluded IPv4 addresses.
Restrictions and guidelines: Dynamic NAT444
You can configure multiple outbound NAT rules on an interface.
· A NAT rule with an ACL takes precedence over a rule without any ACL.
· If two ACL-based dynamic NAT rules are configured, the rule with the higher ACL number has higher priority.
Restrictions and guidelines: Address availability test
· A NAT address group can use multiple NQA probe templates. An IP address can be used for address translation as long as a reply is returned for this address in one NQA template probe.
· The NQA probe template does not support the source IP address configuration.
Configure NAT
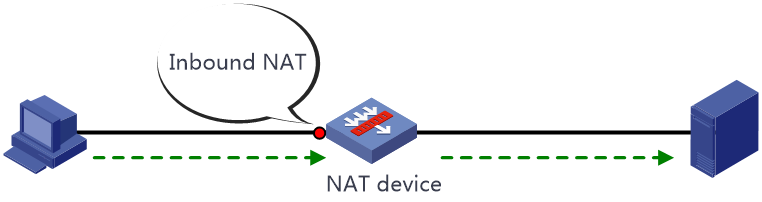
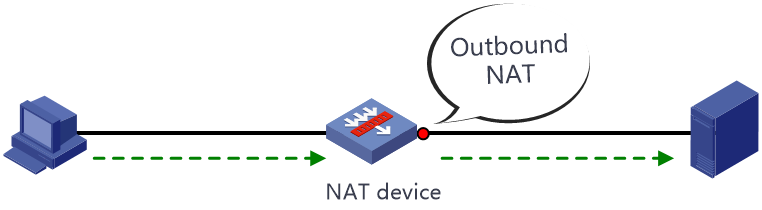
NAT can be performed in the inbound or outbound direction.
· Inbound NAT—Performs address translation for packets received on an interface, as shown in Figure 2.
· Outbound NAT—Performs address translation for packets sent out of an interface, as shown in Figure 3.
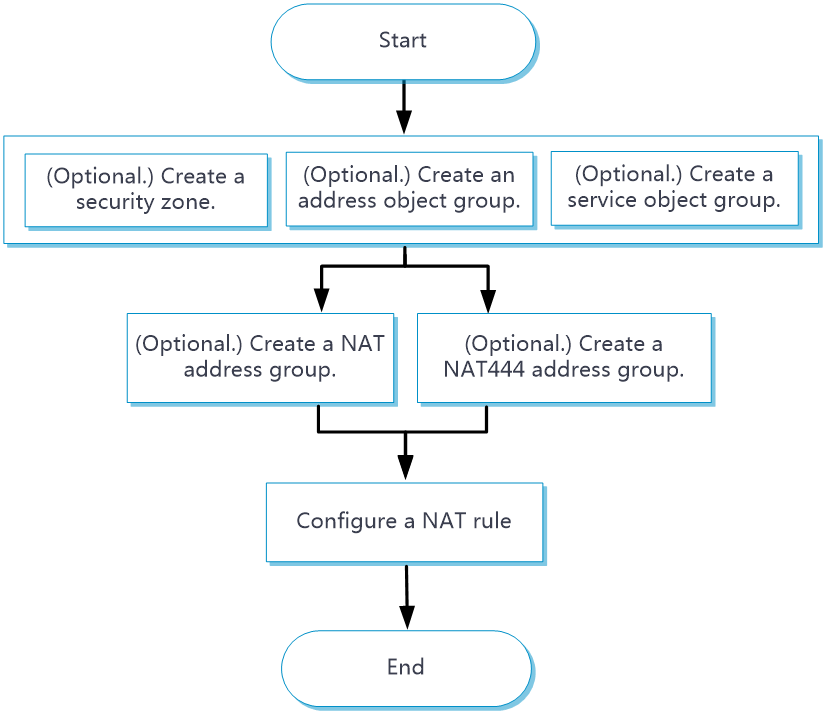
Configure NAT policy
The NAT policy uses the security zone, address object group, and service object group as the packet match criteria and supports source address translation, destination address translation, and bidirectional translation.
Figure 4 NAT policy configuration procedure
Procedure
1. (Optional.) Create a security zone. (Details not shown.)
2. (Optional.) Create an address object group. (Details not shown.)
3. (Optional.) Create a service object group. (Details not shown.)
4. (Optional.) Create a NAT address group.
a. Click the Policies tab.
b. In the navigation pane, select NAT > Dynamic NAT > NAT Address Groups.
c. Click Create.
d. Create a NAT address group.
e. Click OK.
5. (Optional.) Create a NAT444 address group.
a. Click the Policies tab.
b. In the navigation pane, select NAT > Dynamic NAT444> NAT444 Address Groups.
c. Click Create.
d. Create a NAT444 address group.
e. Click OK.
6. Create a NAT rule.
a. Click the Policies tab.
b. In the navigation pane, select NAT > NAT Policy.
c. Click Create.
d. Create a NAT rule.
e. Click OK.
Table 2 Configuration items for NAT policy
|
Item |
Description |
||
|
Rule name |
Enter the name of a NAT rule. Chinese characters are supported. |
||
|
Rule description |
Enter the description of the NAT rule. |
||
|
Change Mode |
Select a translation method. The following translation methods are supported: · Source address translation—Translates the source IP address of the packets. · Destination address translation—Translates the destination IP address of the packets. · Bidirectional translation—Translates both the source IP address and destination IP address of the packets. |
||
|
Original packets |
Src zone |
Select source security zones for packet match. |
|
|
Dst zone |
Select destination security zones for packet match. Only the source address translation method supports using the destination security zone as the packet match criteria. |
||
|
Source IP |
Select a source IP address object group for packet match. |
||
|
Destination IP |
Select a destination IP address object group for packet match. |
||
|
Service |
Select a service object group for packet match. |
||
|
Translated packets |
Source address translation |
Translation method |
Select a source address translation mode: · NO-PAT—Uses NO-PAT for source address translation. · PAT—Uses PAT for source address translation. · No translation—This rule and rules with lower priority than this rule are not used for source address translation. |
|
Address type |
Select a NAT address type for source address translation: · Address group—Uses IP addresses in the NAT address group for source address translation. · NAT444 address group—Uses IP addresses in the NAT444 address group for source address translation. |
||
|
Source address after NAT |
Select a NAT address group or NAT444 address group for source address translation. |
||
|
Allow reverse NAT |
Enable reverse address translation. Reverse address translation uses existing NO-PAT entries to translate the destination address for connections actively initiated from the external network to the internal network. This option is available only when the translation mode is set to NO-PAT. |
||
|
Port preservation |
Try to preserve port number for PAT. This option is available only when the translation mode is set to PAT. |
||
|
Destination address translation |
Translation method |
Select a destination address translation method: · Many-to-one address translation—Translates destination IP addresses of matching packets to one IP address. · No translation—This rule and rules with lower priority than this rule are not used for source address translation. |
|
|
Destination IP after NAT |
Set the destination IP address after translation. |
||
|
Port after NAT |
Set the destination port after translation. |
||
|
Enable this rule |
Enable this NAT rule. |
||
|
Counting |
Enable the counting of times that the rule is matched. |
||
Configure dynamic NAT
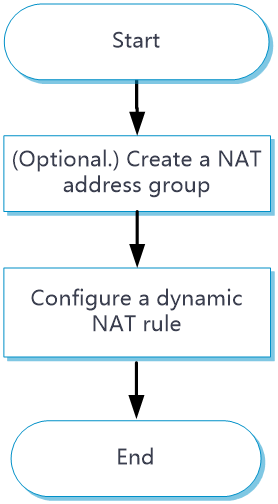
Only outbound dynamic NAT is supported in the current software version. You can configure ACL-based outbound dynamic NAT or object group-based outbound dynamic NAT. Figure 5 shows the configuration procedure for dynamic NAT.
Figure 5 Dynamic NAT configuration procedure
Procedure
1. (Optional.) Create a NAT address group.
a. Click the Policies tab.
b. In the navigation pane, select NAT > Dynamic NAT > NAT Address Groups.
c. Click Create.
d. Create a NAT address group as shown in Table 3.
Table 3 Configuration items for a NAT address group
|
Item |
Description |
|
Address group ID |
Enter the ID of a NAT address group. |
|
Address group name |
Enter the name of the NAT address group. |
|
VRRP group |
Specify a VRRP group for high availability purposes. The master device in the VRRP group uses the virtual IP address and virtual MAC address to answer ARP requests. Support for the VRRP group feature depends on the device model. |
|
Port range |
Specify a port range for address translation. |
|
Address probe |
Select NQA templates to probe the availability of addresses in the NAT address group for outbound address translation. |
|
Address group members |
Add IP address ranges to the NAT address group. The NAT address group uses these IP address ranges to translate source IP addresses of the packets sent to the external network. |
e. Click OK.
2. Configure ACL-based dynamic NAT.
a. Click the Policies tab.
b. In the navigation pane, select NAT > Dynamic NAT > Policy Configuration.
c. Click the Outbound Dynamic NAT (ACL-Based) tab.
d. Click Create.
e. Create an ACL-based outbound dynamic NAT rule, as shown in Table 4.
Table 4 Configuration items for ACL-based outbound dynamic NAT
|
Item |
Description |
||
|
Interface |
Interface to which the NAT rule is applied. Outbound dynamic NAT is typically configured on the interface connected to the external network. |
||
|
ACL |
ACL for packet matching. If you specify an ACL, NAT translates the source IP addresses of outgoing packets permitted by the ACL. If you do not specify an ACL, NAT translates all packets. |
||
|
Source address after NAT |
Select the NAT address for address translation: · NAT address group—IP addresses in the NAT address group are used for address translation. · Easy IP—The IP address of the specified interface is used for address translation.
|
||
|
VRF |
VRF to which the source addresses belong after translation. The default setting is Public network.
|
||
|
Translation mode |
Dynamic NAT translation mode: · PAT—Uses the IP addresses in the address group or the IP address of the interface to translate IP addresses of the matching packets. Source ports in the matching packets are also translated. · NO-PAT—Uses the IP addresses in the address group to translate IP addresses of the matching packets. Source ports in the matching packets are not translated. |
||
|
Port preservation |
Try to preserve port number for PAT. This option is available only when the translation mode is set to PAT. |
||
|
Allow reverse NAT |
Enable reverse address translation. Reverse address translation uses existing NO-PAT entries to translate the destination address for connections actively initiated from the external network to the internal network. This option is available only when the translation mode is set to NO-PAT. |
||
|
Enable this rule |
Enable this NAT rule. |
f. Click OK.
3. Configure object group-based dynamic NAT.
a. Click the Policies tab.
b. In the navigation pane, select NAT > Dynamic NAT > Policy Configuration.
c. Click the Outbound Dynamic NAT (Object Group-Based) tab.
d. Click Create.
e. Create an object group-based outbound dynamic NAT rule, as shown in Table 5.
Table 5 Configuration items for object group-based outbound dynamic NAT
|
Item |
Description |
||
|
Rule name |
Enter the name of a NAT rule. |
||
|
Rule description |
Enter the description of the NAT rule. |
||
|
Output interface |
Interface to which the NAT rule is applied. Outbound dynamic NAT is typically configured on the interface connected to the external network. |
||
|
Source IP |
Source IP address object group for the NAT rule. You can configure multiple source IP address object groups for a NAT rule. Each source IP object group is an independent packet match criterion. |
||
|
Destination IP |
Destination IP address object group for the NAT rule. You can configure multiple destination IP address object groups for a NAT rule. Each destination IP object group is an independent packet match criterion. |
||
|
Service |
Service object group for the NAT rule. You can configure multiple service object groups for a NAT rule. Each service object group is an independent packet match criterion.
|
||
|
Action |
Dynamic NAT translation mode: · PAT—Uses the IP addresses in the address group or the IP address of the interface to translate IP addresses of the matching packets. Source ports in the matching packets are also translated. · NO-PAT—Uses the IP addresses in the address group to translate IP addresses of the matching packets. Source ports in the matching packets are not translated. · Easy IP—Uses the IP address of the specified interface for address translation. · No translation—Does not translate matching packets. |
||
|
Source address after NAT |
NAT address group for source address translation.
|
||
|
Port reservation |
Try to preserve port number for PAT. This option is available only when the translation mode is set to PAT. |
||
|
Allow reverse NAT |
Enable reverse address translation. Reverse address translation uses existing NO-PAT entries to translate the destination address for connections actively initiated from the external network to the internal network. This option is available only when the translation mode is set to NO-PAT. |
||
|
Enable this rule |
Enable this NAT rule. |
f. Click OK.
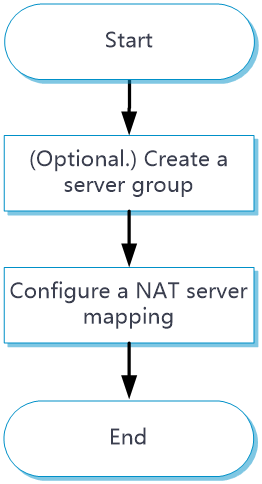
Configure NAT Server
Configure the NAT Server feature as shown in Figure 6.
Figure 6 NAT Server configuration procedure
Procedure
1. (Optional.) Create a server group.
a. Click the Policies tab.
b. In the navigation pane, select NAT > NAT Servers > NAT Server Groups.
c. Click Create.
d. Create a server group.
e. Click OK.
2. Configure a NAT server rule.
a. Click the Policies tab.
b. In the navigation pane, select NAT > NAT Servers > Policy Configuration.
c. Click Create.
d. Create a NAT server rule, as shown in Table 6.
Table 6 NAT server configuration items
|
Item |
Description |
|
Rule name |
Enter the name of a NAT server rule. |
|
Interface |
Interface to which the NAT server rule is applied. The NAT server rule is typically configured on the interface connected to the external network. |
|
Protocol type |
Specify a protocol type. If you do not specify a protocol type, the configuration applies to packets of all protocols. |
|
Mapping |
Select an address-port mapping. For more information, see Table 1. |
|
Mapping description |
Mapping description for identification when a large number of NAT mappings exist. |
|
Public IP |
Public IP address that the server advertises to the external network. |
|
Public port |
Public port number or port range, depending on the mapping method. When you specify a port range, make sure the end port is greater than the start port. |
|
Public port VRF |
VRF to which the advertised public IP addresses belong. The default setting is Public network. |
|
Server IP |
Private IP address or address range, depending on the mapping method. In the address range, the end address must be greater than the start address. The number of addresses in the range must equal the number of ports in the public port range. |
|
Server port |
Private port number or port range, depending on the mapping method. When you specify a port range, make sure the end port is higher than the start port. |
|
Server VRF |
VRF to which the NAT server belongs. The default setting is Public network. |
|
ACL for packet matching |
If you specify an ACL, NAT translates packets permitted by the ACL. If you do not specify an ACL, NAT translates all packets. |
|
VRRP group |
Specify a VRRP group for high availability purposes. The master device in the VRRP group uses the virtual IP address and virtual MAC address to answer ARP requests. Support for the VRRP group feature depends on the device model. |
|
Allow reverse NAT |
Allow reverse address translation. Reverse address translation applies to connections actively initiated by internal servers to the external network. It translates the private IP addresses of the internal servers to their public IP addresses. This option is available only when the mapping type is set to One single public address with one single or no public port. |
|
Enable this rule |
Enable this NAT server rule. |
e. Click OK.
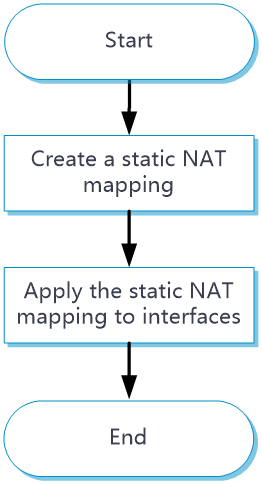
Configure static NAT
Only outbound static NAT is supported in the current software version. Configure static NAT as shown in Figure 7.
Figure 7 Static NAT configuration procedure
Procedure
1. Click the Policies tab.
2. In the navigation pane, select NAT > Static NAT > Policy Configuration.
3. Click Create.
4. Create a static NAT mapping.
Table 7 Static NAT configuration items
|
Item |
Description |
|
Translation method |
Select an address translation method: · One-to-one—Performs address translation from a private IP address to a public IP address. · Net-to-net—Performs address translation from a private network to a public network · Address object group—Performs address object group-based address translation. |
|
Private address |
Private IP address. The parameter setting depends on the translation method. If address object group-based translation method is selected, you must specify an IPv4 address object group. |
|
Public VRF |
VRF to which the public IP address belongs. The default setting is Public network. |
|
Private VRF |
VRF to which the private IP address belongs. The default setting is Public network. |
|
Public address |
Public IP address. The parameter setting depends on the translation method. If address object group-based translation method is selected, you must specify an IPv4 address object group. |
|
ACL |
Specify an ACL to define the destination IP addresses that internal hosts can access. |
|
VRRP group |
Specify a VRRP group for high availability purposes. The master device in the VRRP group uses the virtual IP address and virtual MAC address to answer ARP requests. Support for the VRRP group feature depends on the device model. |
|
Allow reverse NAT |
Allow reverse address translation. Reverse address translation applies to connections actively initiated by external hosts to the internal host. It uses the mapping to translate the destination address for packets of these connections if the packets are permitted by ACL reverse matching. |
|
Enable this rule |
Enable this static NAT rule. |
4. Click OK.
5. Click the Policies tab.
6. In the navigation pane, select NAT > Static NAT > Apply Policy.
7. Select one or multiple interfaces.
8. Click Enable.
Configure dynamic NAT444
Configure dynamic NAT444 as shown in Figure 8.
Figure 8 Dynamic NAT444 configuration procedure
Procedure
1. Create a NAT444 address group.
a. Click the Policies tab.
b. In the navigation pane, select NAT > Dynamic NAT444> NAT444 Address Groups.
c. Click Create.
d. Create a NAT444 address group as shown in Table 8.
Table 8 Configuration items for a NAT444 address group
|
Item |
Description |
|
Address group ID |
Enter the ID of an address group. |
|
VRRP group |
Specify a VRRP group for high availability purposes. The master device in the VRRP group uses the virtual IP address and virtual MAC address to answer ARP requests. Support for the VRRP group feature depends on the device model. |
|
Port range |
Specify a port range for address translation. |
|
Port block size |
Set the port block size. |
|
Number of extended port blocks |
Enter the number of extended port blocks. When the pre-allocated port block for a private IP address runs out of port resources, the device assigns extended port blocks to the private address. |
|
Address probe |
Select NQA templates to probe the availability of addresses in the NAT address group for outbound address translation. |
|
Address group members |
Add IP address ranges to the address group. The NAT444 address group uses these IP address ranges to translate source IP addresses of the packets sent to the external network. |
e. Click OK.
2. Configure ACL-based dynamic NAT444.
a. Click the Policies tab.
b. In the navigation pane, select NAT > Dynamic NAT444> Policy Configuration.
c. Click the Outbound Dynamic NAT444 (ACL-Based) tab.
d. Click Create.
e. Configure an ACL-based NAT444 dynamic rule as shown in Table 9.
Table 9 Configuration items for ACL-based dynamic NAT444
|
Item |
Description |
||
|
Interface |
Interface to which the dynamic NAT444 rule is applied. An interface can be configured with multiple outbound address translation rules. |
||
|
ACL for packet matching |
If you specify an ACL, NAT translates packets permitted by the ACL. If you do not specify an ACL, NAT translates all packets. |
||
|
Address group |
Select a NAT444 address group for source address translation. |
||
|
VRF |
VRF to which the source addresses belong after translation. The default setting is Public network.
|
||
|
Translation method |
Dynamic NAT translation mode: · PAT—Uses the IP addresses in the address group or the IP address of the interface to translate IP addresses of the matching packets. Source ports in the matching packets are also translated. · NO-PAT—Uses the IP addresses in the address group to translate IP addresses of the matching packets. Source ports in the matching packets are not translated. As a best practice, do not use this mode for dynamic NAT444. |
||
|
Allow reverse NAT |
This option is available only when the translation mode is set to NO-PAT. As a best practice, do not select this option for dynamic NAT 444. |
f. Click OK.
3. Configure object group-based dynamic NAT.
a. Click the Policies tab.
b. In the navigation pane, select NAT > Dynamic NAT > Policy Configuration.
c. Click the Outbound Dynamic NAT444 (Object Group-Based) tab.
d. Click Create.
e. Create an object group-based outbound dynamic NAT444 rule, as shown in Table 10.
Table 10 Configuration items for object group-based dynamic NAT444
|
Item |
Description |
||
|
Rule name |
Enter the name of a NAT444 rule. |
||
|
Rule description |
Enter the description of a NAT444 rule. |
||
|
Interface |
Interface to which the NAT444 rule is applied. An interface can be configured with multiple outbound dynamic NAT444 rules. |
||
|
Source IP |
Source IP address object group for the NAT444 rule. You can configure multiple source IP address object groups for a NAT444 rule. Each source IP object group is an independent packet match criterion. |
||
|
Destination IP |
Destination IP address object group for the NAT444 rule. You can configure multiple destination IP address object groups for a NAT444 rule. Each destination IP object group is an independent packet match criterion. |
||
|
Service |
Service object group for the NAT444 rule. You can configure multiple service object groups for a NAT444 rule. Each service object group is an independent packet match criterion.
|
||
|
Action |
Dynamic NAT444 translation mode: · PAT—Uses the IP addresses in the address group or the IP address of the interface to translate IP addresses of the matching packets. Source ports in the matching packets are also translated. · NO-PAT—Uses the IP addresses in the address group to translate IP addresses of the matching packets. Source ports in the matching packets are not translated. As a best practice, do not use this mode in NAT444 dynamic rules. |
||
|
Source address after NAT |
NAT address group for source address translation.
|
||
|
Allow reverse NAT |
This option is available only when the translation mode is set to NO-PAT. As a best practice, do not use this mode in NAT444 dynamic translation. |
f. Click OK.
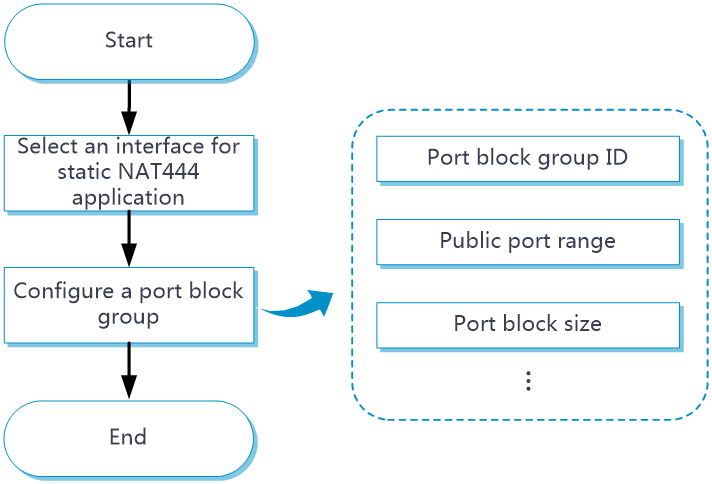
Configure static NAT444
Configure static NAT444 as shown in Figure 9.
Figure 9 Static NAT444 configuration procedure
Procedure
1. Click the Policies tab.
2. In the navigation pane, select NAT > Static NAT444.
3. Click Create.
4. Select an interface.
5. Select or create a port block group.
6. Click OK.