- Table of Contents
-
- 04-Layer 3 Configuration Guide
- 00-Preface
- 01-ARP Configuration
- 02-IP Addressing Configuration
- 03-DHCP Configuration
- 04-DHCPv6 Configuration
- 05-DNS Configuration
- 06-IPv6 DNS Configuration
- 07-NAT Configuration
- 08-Adjacency Table Configuration
- 09-Flow Classification Configuration
- 10-IPv6 Basics Configuration
- 11-IP Performance Optimization Configuration
- 12-IP Routing Basics
- 13-Static Routing Configuration
- 14-IPv6 Static Routing Configuration
- 15-GRE Configuration
- 16-RIP Configuration
- 17-RIPng Configuration
- 18-Policy-Based Routing Configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 03-DHCP Configuration | 624.90 KB |
DHCP address allocation mechanisms
Dynamic IP address allocation process
IP address allocation sequence
DHCP server configuration task list
Configuring an address pool on the DHCP server
Configuring address allocation mode for a common address pool
Configuring dynamic address allocation for an extended address pool
Configuring a domain name suffix for the client
Configuring DNS servers for the client
Configuring WINS servers and NetBIOS node type for the client
Configuring BIMS server information for the client
Configuring gateways for the client
Configuring Option 184 parameters for the client with voice service
Configuring the TFTP server and bootfile name for the client
Specifying a server's IP address for the DHCP client
Configuring self-defined DHCP options
Enabling the DHCP server on an interface
Applying an extended address pool on an interface
Configuring the DHCP server security functions
Enabling unauthorized DHCP server detection
Configuring IP address conflict detection
Configuring the DHCP server to work with authorized ARP
Enabling client offline detection
Enabling handling of Option 82
Specifying the threshold for sending trap messages
Displaying and maintaining the DHCP server
DHCP server configuration examples
Static IP address assignment configuration example
Dynamic IP address assignment configuration example
Self-defined option configuration example
Troubleshooting DHCP server configuration
Configuring the DHCP relay agent
DHCP relay agent support for Option 82
DHCP relay agent configuration task list
Enabling the DHCP relay agent on an interface
Correlating a DHCP server group with a relay agent interface
Configuring the DHCP relay agent security functions
Configuring periodic refresh of dynamic client entries
Configuring the DHCP relay agent to work with authorized ARP
Enabling unauthorized DHCP server detection
Enabling DHCP starvation attack protection
Enabling client offline detection
Configuring the DHCP relay agent to release an IP address
Configuring the DHCP relay agent to handle Option 82
Displaying and maintaining the DHCP relay agent
DHCP relay agent configuration examples
DHCP relay agent configuration example
DHCP relay agent Option 82 support configuration example
Troubleshooting DHCP relay agent configuration
Enabling the DHCP client on an interface
Displaying and maintaining the DHCP client
DHCP client configuration example
Application of trusted and untrusted ports
DHCP snooping support for Option 82
DHCP snooping configuration task list
Configuring DHCP snooping basic functions
Configuring DHCP snooping to support Option 82
Configuring DHCP snooping entries backup
Enabling DHCP starvation attack protection
Enabling DHCP-REQUEST message attack protection
Enabling the DHCP snooping device to verify DHCP broadcast replies
Displaying and maintaining DHCP snooping
DHCP snooping configuration example
Obtaining an IP address dynamically
Configuring an interface to dynamically obtain an IP address through BOOTP
Displaying and maintaining BOOTP client configuration
BOOTP client configuration example
DHCP overview
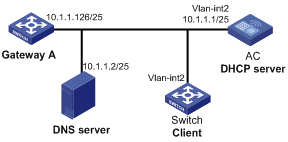
As shown in Figure 1, a DHCP client can obtain an IP address and other configuration parameters from a DHCP server on another subnet through a DHCP relay agent. For more information about the DHCP relay agent, see "Configuring the DHCP relay agent."
Figure 1 A typical DHCP application
DHCP address allocation mechanisms
DHCP supports the following mechanisms for IP address allocation:
· Static allocation—Network administrator assigns an IP address to a client (for example, a WWW server), and DHCP conveys the assigned address to the client.
· Automatic allocation—DHCP assigns a permanent IP address to a client.
· Dynamic allocation—DHCP assigns an IP address to a client for a limited period of time, which is called a lease. Most DHCP clients obtain their addresses in this way.
Dynamic IP address allocation process
Figure 2 Dynamic IP address allocation process
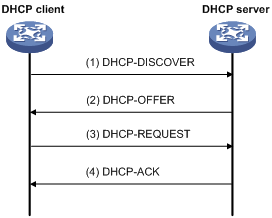
1. The client broadcasts a DHCP-DISCOVER message to locate a DHCP server.
2. Each DHCP server offers configuration parameters such as an IP address to the client in a DHCP-OFFER message. The sending mode of the DHCP-OFFER is determined by the flag field in the DHCP-DISCOVER message. For related information, see "DHCP message format."
3. If several DHCP servers send offers to the client, the client accepts the first received offer, and broadcasts it in a DHCP-REQUEST message to formally request the IP address.
4. All DHCP servers receive the DHCP-REQUEST message, but only the server selected by the client returns a DHCP-ACK message to confirm that the IP address has been allocated to the client, or a DHCP-NAK message to deny the IP address allocation.
¡ After the client receives the DHCP-ACK message, it broadcasts a gratuitous ARP packet to verify whether the IP address assigned by the server is already in use.
¡ If the client receives no response within the specified time, the client uses the assigned IP address. Otherwise, the client sends a DHCP-DECLINE message to the server to request an IP address again.
IP addresses offered by other DHCP servers can be assigned to other clients.
IP address lease extension
A dynamically assigned IP address has a lease. When the lease expires, the IP address is reclaimed by the DHCP server. To continue using the IP address, the client must extend the lease duration.
When half of the lease duration elapses, the DHCP client unicasts a DHCP-REQUEST to the DHCP server to extend the lease. Depending on the availability of the IP address, the DHCP server returns either a DHCP-ACK unicast confirming that the client's lease duration has been extended, or a DHCP-NAK unicast denying the request.
If the client receives no reply, it broadcasts another DHCP-REQUEST message for lease extension after seven eighths of the lease duration elapses. Again, depending on the availability of the IP address, the DHCP server returns either a DHCP-ACK unicast confirming that the client's lease duration has been extended, or a DHCP-NAK unicast denying the request.
DHCP message format
Figure 3 shows the DHCP message format, which is based on the BOOTP message format although DHCP uses some of the fields in significantly different ways. The numbers in parentheses indicate the size of each field in bytes.
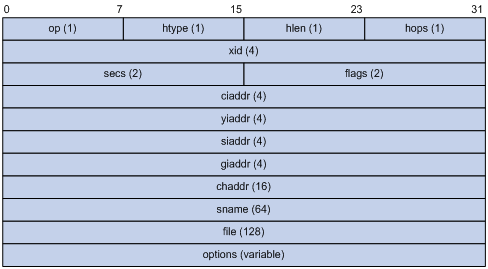
· op—Message type defined in option field. 1 = REQUEST, 2 = REPLY
· htype, hlen—Hardware address type and length of the DHCP client.
· hops—Number of relay agents a request message traveled.
· xid—Transaction ID, a random number chosen by the client to identify an IP address allocation.
· secs—Filled in by the client, the number of seconds elapsed since the client began address acquisition or renewal process. This field is reserved and set to 0.
· flags—The leftmost bit is defined as the BROADCAST (B) flag. If this flag is set to 0, the DHCP server sent a reply back by unicast. If this flag is set to 1, the DHCP server sent a reply back by broadcast. The remaining bits of the flags field are reserved for future use.
· ciaddr—Client IP address if the client has an IP address that is valid and usable. Otherwise, it is set to zero. (The client does not use this field to request a specific IP address to lease.)
· yiaddr—Your IP address. It is an IP address assigned by the DHCP server to the DHCP client.
· siaddr—Server IP address, from which the client obtained configuration parameters.
· giaddr—Gateway IP address. It is the IP address of the first relay agent that a request message travels.
· chaddr—Client hardware address.
· sname—Server host name, from which the client obtained configuration parameters.
· file—Bootfile name and path information, defined by the server to the client.
· options—Optional parameters field that is variable in length, which includes the message type, lease duration, subnet mask, domain name server IP address, and WINS IP address.
DHCP options
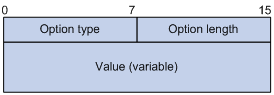
Common DHCP options
The following are common DHCP options:
· Option 3—Router option. It specifies the gateway address.
· Option 6—DNS server option. It specifies the DNS server's IP address.
· Option 33—Static route option. It specifies a list of classful static routes (the destination addresses in these static routes are classful) that a client should add into its routing table. If both Option 33 and Option 121 exist, Option 33 is ignored.
· Option 51—IP address lease option.
· Option 53—DHCP message type option. It identifies the type of the DHCP message.
· Option 55—Parameter request list option. It is used by a DHCP client to request specified configuration parameters. The option contains values that correspond to the parameters requested by the client.
· Option 60—Vendor class identifier option. It is used by a DHCP client to identify its vendor, and by a DHCP server to distinguish DHCP clients by vendor class and assign specific IP addresses to the DHCP clients.
· Option 66—TFTP server name option. It specifies a TFTP server to be assigned to the client.
· Option 67—Bootfile name option. It specifies the bootfile name to be assigned to the client.
· Option 121—Classless route option. It specifies a list of classless static routes (the destination addresses in these static routes are classless) that the requesting client should add to its routing table. If both Option 33 and Option 121 exist, Option 33 is ignored.
· Option 150—TFTP server IP address option. It specifies the TFTP server IP address to be assigned to the client.
For more information about DHCP options, see RFC 2132 and RFC 3442.
Custom options
Some options, such as Option 43, Option 82, and Option 184, have no standard definitions in RFC 2132.
Vendor-specific option (Option 43)
DHCP servers and clients use Option 43 to exchange vendor-specific configuration information.
The DHCP client can obtain the following information through Option 43:
· Auto-Configuration Server (ACS) parameters, including the ACS URL, username, and password.
· Service provider identifier, which is acquired by the Customer Premises Equipment (CPE) from the DHCP server and sent to the ACS for selecting vender-specific configurations and parameters.
· Access controller (AC) address, which is used by an AP to obtain the boot file or other control information from the AC. An AP can obtain a maximum of 16 AC addresses through Option 43.
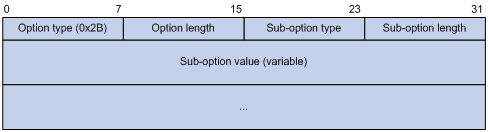
Network configuration parameters are carried in different sub-options of Option 43 as shown in Figure 5.
¡ Sub-option type—The field value can be 0x01 (an ACS parameter sub-option), 0x02 (a service provider identifier sub-option), or 0x80 (a PXE server address sub-option).
¡ Sub-option length—Excludes the sub-option type and sub-option length fields.
¡ Sub-option value—The value format varies with sub-options.
2. Sub-option value field formats:
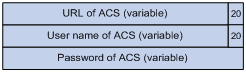
¡ ACS parameter sub-option value field—Contains variable ACS URL, username, and password separated by spaces (0x20) as shown in Figure 6.
Figure 6 ACS parameter sub-option value field
¡ Service provider identifier sub-option value field—Contains the service provider identifier.
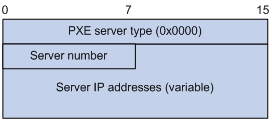
¡ AC address sub-option value field—Contains the PXE server type that can only be 0, the server number that indicates the number of PXE servers contained in the sub-option, and server IP addresses, as shown in Figure 7.
Figure 7 AC address sub-option value field
Relay agent option (Option 82)
Option 82 is the relay agent option in the option field of the DHCP message. It records the location information about the DHCP client. When a DHCP relay agent or DHCP snooping device receives a client's request, it adds Option 82 to the request message and sends it to the server.
The administrator can use Option 82 to locate the DHCP client and further implement security control and accounting. The DHCP server can use Option 82 to provide individual configuration policies for the clients.
Option 82 can contain up to 255 sub-options and must have at least one sub-option. The relay agent option 82 supports two sub-options: sub-option 1 (Circuit ID) and sub-option 2 (Remote ID). The DHCP snooping option 82 supports three sub-options: sub-option 1 (Circuit ID), sub-option 2 (Remote ID), and sub-option 9 (private padding format).
Option 82 has no standard definition. Its padding formats vary with vendors.
There are two methods for configuring Option 82:
· User-defined method—Manually specify the content of Option 82.
· Non-user-defined method—Pad Option 82 in the default normal format, verbose format, private format, or standard format.
|
|
NOTE: Only the DHCP snooping device supports sub-option 9, padded in either private or standard format. |
If you choose normal format or verbose format, you can specify the code type for the sub-options as ASCII or HEX.
· Normal padding format:
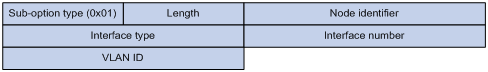
¡ Sub-option 1—Contains the VLAN ID and interface number of the interface that received the client's request. The value of the sub-option type is 1, and that of the circuit ID type is 0.
Figure 8 Sub-option 1 in normal padding format

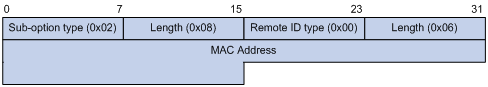
¡ Sub-option 2—Contains the MAC address of the DHCP relay agent interface or the MAC address of the DHCP snooping device that received the client's request. The value of the sub-option type is 2, and that of the remote ID type is 0.
Figure 9 Sub-option 2 in normal padding format
· Verbose padding format:
¡ Sub-option 1—Contains the user-specified access node identifier (ID of the device that adds Option 82 in DHCP messages), and the type, number, and VLAN ID of the interface that received the client's request. The VLAN ID field has a fixed length of 2 bytes. All the other padding contents of sub-option 1 are length variable. See Figure 10.
Figure 10 Sub-option 1 in verbose padding format
¡ Sub-option 2—Contains the MAC address of the DHCP relay agent interface or the MAC address of the DHCP snooping device that received the client's request. It has the same format as that in normal padding format. See Figure 9.
· Private padding format:
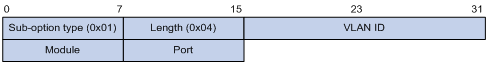
¡ Sub-option 1—Contains the VLAN ID of the interface that received the client's request, module, and port (number of the receiving port). The value of the sub-option type is 1.
Figure 11 Sub-option 1 in private padding format
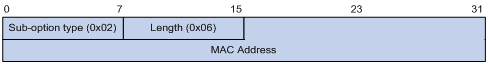
¡ Sub-option 2—Contains the MAC address of the DHCP snooping device that received the client's request. The value of the sub-option type is 2.
Figure 12 Sub-option 2 in private padding format
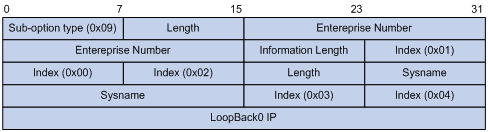
¡ Sub-option 9—Contains the sysname and the primary IP address of the Loopback0 interface. The value of the sub-option type is 9.
Figure 13 Sub-option 9 in private padding format
· Standard padding format:
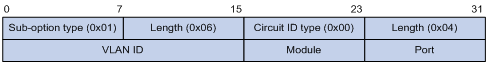
¡ Sub-option 1—Contains the VLAN ID of the interface that received the client's request, module, and port (number of the receiving port). The value of the sub-option type is 1, and the value of the circuit ID type is 0.
Figure 14 Sub-option 1 in standard padding format
¡ Sub-option 2—Contains the MAC address of the DHCP snooping device that received the client's request. The value of the sub-option type is 2, and that of the remote ID type is 0. It has the same format as sub-option 2 in normal padding format. See Figure 9.
Option 184
Option 184 is a reserved option. You can define the parameters in the option as needed. The device supports Option 184 carrying voice related parameters, so a DHCP client with voice functions can get voice parameters from the DHCP server.
Option 184 has the following sub-options:
· Sub-option 1—Specifies the IP address of the primary network calling processor, which serves as the network calling control source and provides program download services.
· Sub-option 2—Specifies the IP address of the backup network calling processor. DHCP clients contact the backup processor when the primary one is unreachable.
· Sub-option 3—Specifies the voice VLAN ID and the result whether or not the DHCP clients takes this ID as the voice VLAN.
· Sub-option 4—Specifies the failover route that includes the IP address and the number of the target user. A Session Initiation Protocol (SIP) user uses this IP address and number to directly establish a connection to the target SIP user when both the primary and backup calling processors are unreachable.
For Option 184, you must define sub-option 1 to make other sub-options take effect.
Protocols and standards
· RFC 2131, Dynamic Host Configuration Protocol
· RFC 2132, DHCP Options and BOOTP Vendor Extensions
· RFC 1542, Clarifications and Extensions for the Bootstrap Protocol
· RFC 3046, DHCP Relay Agent Information Option
· RFC 3442, The Classless Static Route Option for Dynamic Host Configuration Protocol (DHCP) version 4
Configuring the DHCP server
Overview
The DHCP server is well suited to networks where:
· Manual configuration and centralized management are difficult to implement.
· IP addresses are limited. For example, an ISP limits the number of concurrent online users, and most users must acquire IP addresses dynamically.
· Most hosts do not need fixed IP addresses.
DHCP address pool
DHCP address pools include common and extended address pools:
· Common address pool—Supports both static binding and dynamic allocation.
· Extended address pool—Supports only dynamic allocation.
Common address pool structure
The organization of the common address pool database can be compared to a tree. The root of the tree is the address pool for natural networks, branches are address pools for subnets, and leaves are addresses statically bound to clients. For the same level address pools, a previously configured pool has a higher selection priority than a new one.
At the very beginning, subnets inherit network parameters and clients inherit subnet parameters. Therefore, common parameters (for example, a DNS server address) should be configured at the highest (network or subnet) level of the tree.
The new configuration at the higher level (parent) of the tree is:
· Inherited if the lower level (child) has no such configuration.
IP address lease durations are not inherited.
· Overridden if the lower level (child) has such configuration.
|
|
NOTE: The extended address pools on a DHCP server are independent of each other, and no inheritance relationship exists among them. |
Principles for selecting an address pool
The DHCP server observes the following principles to select an address pool when assigning an IP address to a client:
1. If there is an address pool where an IP address is statically bound to the MAC address or ID of the client, the DHCP server selects this address pool and assigns the statically bound IP address to the client. For the configuration of this address pool, see "Configuring static address allocation."
2. If the receiving interface has an extended address pool referenced, the DHCP server assigns an IP address from this address pool. If no IP address is available in the address pool, the DHCP server fails to assign an address to the client. For the configuration of such an address pool, see "Configuring dynamic address allocation for an extended address pool."
3. Otherwise, the DHCP server selects the smallest common address pool that contains the IP address of the receiving interface (if the client and the server reside on the same subnet), or the smallest common address pool that contains the IP address specified in the giaddr field of the client's request (if a DHCP relay agent is in-between). If no IP address is available in the address pool, the DHCP server fails to assign an address to the client because it cannot assign an IP address from the parent address pool to the client. For the configuration of such an address pool, see "Configuring dynamic address allocation."
For example, two common address pools, 1.1.1.0/24 and 1.1.1.0/25, are configured on the DHCP server. If the IP address of the interface receiving DHCP requests is 1.1.1.1/25, the DHCP server selects IP addresses for clients from address pool 1.1.1.0/25. If no IP address is available in the address pool, the DHCP server fails to assign addresses to clients. If the IP address of the interface receiving DHCP requests is 1.1.1.130/25, the DHCP server selects IP addresses for clients from the 1.1.1.0/24 address pool.
|
|
NOTE: To make sure correct IP address allocation, keep the IP addresses for dynamic allocation within the subnet where the interface of the DHCP server or DHCP relay agent resides. |
IP address allocation sequence
A DHCP server assigns an IP address to a client in the following sequence:
1. IP address statically bound to the client's MAC address or ID.
2. IP address that was ever assigned to the client.
3. IP address designated by the Option 50 field in a DHCP-DISCOVER message.
Option 50 is the requested IP address field in DHCP-DISCOVER messages. It is padded by the client to specify the IP address that the client wants to obtain. The contents to be padded depend on the client.
4. First assignable IP address found in an extended or common address pool.
5. IP address that was a conflict or passed its lease duration.
If no IP address is assignable, the server does not respond.
DHCP server configuration task list
|
Remarks |
|
|
Required. |
|
|
Required. |
|
|
Required. |
|
|
Required by the extended address pool configuration. When configuring a common address pool, ignore this task. |
|
|
Optional. |
|
|
Optional. |
|
|
Optional. |
|
|
Optional. |
Configuring an address pool on the DHCP server
Configuration task list
|
Task |
Remarks |
|
|
Required. |
||
|
Configuring address allocation mode for a common address pool |
Required to configure either of the two for the common address pool configuration. |
|
|
Configuring dynamic address allocation for an extended address pool |
Required for the extended address pool configuration. |
|
|
Optional. |
||
|
Configuring WINS servers and NetBIOS node type for the client |
||
|
Configuring Option 184 parameters for the client with voice service |
||
|
Configuring the TFTP server and bootfile name for the client |
||
Creating a DHCP address pool
When you create a DHCP address pool, specify it as a common address pool or an extended address pool.
To create a DHCP address pool:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Create a DHCP address pool and enter its view. |
dhcp server ip-pool pool-name [ extended ] |
No DHCP address pool is created by default. |
A common address pool and an extended address pool are different in address allocation mode configuration. Configurations of other parameters (such as the domain name suffix and DNS server address) for them are the same.
Configuring address allocation mode for a common address pool
|
|
CAUTION: You can configure either a static binding or dynamic address allocation for a common address pool, but not both. |
You need to specify a subnet for dynamic address allocation. A static binding is a special address pool containing only one IP address.
Configuring static address allocation
Some DHCP clients, such as a WWW server, need fixed IP addresses. To provide a fixed IP address for such a client, you can statically bind the MAC address or ID of the client to an IP address in a DHCP address pool. When the client requests an IP address, the DHCP server assigns the IP address in the static binding to the client.
Follow these guidelines when you configure static address allocation:
· Use the static-bind ip-address command together with static-bind mac-address or static-bind client-identifier to accomplish a static binding configuration.
· In a DHCP address pool, if you execute the static-bind mac-address command before the static-bind client-identifier command, the latter overwrites the former, and vice versa.
· If you use the static-bind ip-address, static-bind mac-address, or static-bind client-identifier command multiple times in the DHCP address pool, the most recent configuration takes effect.
· The IP address of the static binding cannot be an interface address of the DHCP server. Otherwise, an IP address conflict may occur, making the bound client unable to obtain an IP address correctly.
· The ID of the static binding must be identical to the ID displayed by using the display dhcp client verbose command on the client. Otherwise, the client cannot obtain an IP address.
· The specified lease duration takes effect but the lease duration displayed by the display dhcp server ip-in-use all command is still Unlimited.
· When the device serves as a DHCP client or BOOTP client, you must bind the DHCP client's ID to an IP address, or bind the BOOTP client's MAC address to an IP address on the DHCP server. Otherwise, the DHCP or BOOTP client cannot obtain a static IP address.
· If the interfaces on a DHCP client share the same MAC address, specify the client ID, rather than MAC address, in a static binding to identify the requesting interface. If you do not do this, the client may fail to obtain an IP address.
To configure a static binding in a common address pool:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter common address pool view. |
dhcp server ip-pool pool-name |
N/A |
|
3. Specify the IP address. |
static-bind ip-address ip-address [ mask-length | mask mask ] |
No IP addresses are statically bound by default. |
|
4. Specify the MAC address or client ID. |
· Specify the MAC address: · Specify the client ID: |
Use either of the commands. Neither is bound statically by default. |
|
5. Specify the lease duration for the IP address. |
expired { day day [ hour hour [ minute minute [ second second ] ] ] | unlimited } |
Optional. By default, the lease duration of the IP address is unlimited. |
Configuring dynamic address allocation
For dynamic address allocation, you must configure a DHCP address pool, specify one and only one address range for the pool, and specify the lease duration. A DHCP address pool can have only one lease duration.
To avoid address conflicts, configure the DHCP server to exclude IP addresses used by the gateway or FTP server from dynamic allocation.
Follow these guidelines when you configure dynamic address allocation:
· In common address pool view, if you use the network or network ip range command multiple times, the most recent configuration takes effect.
· After you exclude IP addresses from automatic allocation by using the dhcp server forbidden-ip command, neither a common address pool nor an extended address pool can assign these IP addresses through dynamic address allocation.
· You can exclude multiple IP address ranges from allocation.
To configure dynamic address allocation for a common address pool:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter common address pool view. |
dhcp server ip-pool pool-name |
N/A |
|
3. Specify a subnet. |
network network-address [ mask-length | mask mask ] |
Not specified by default. |
|
4. Specify the IP address range on the subnet for dynamic allocation. |
network ip range min-address max-address |
Optional. Not specified by default. |
|
5. Specify the address lease duration. |
expired { day day [ hour hour [ minute minute ] [ second second ] ] | unlimited } |
Optional. One day by default. |
|
6. Return to system view. |
quit |
N/A |
|
7. Exclude IP addresses from automatic allocation. |
dhcp server forbidden-ip low-ip-address [ high-ip-address ] |
Optional. Except IP addresses of the DHCP server interfaces, all addresses in the DHCP address pool are assignable by default. |
Configuring dynamic address allocation for an extended address pool
Extended address pools support dynamic address allocation only.
When configuring an extended address pool, you must specify:
· Assignable IP address range
· Mask
After the assignable IP address range and the mask are specified, the address pool becomes valid.
To configure dynamic address allocation for an extended address pool:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter extended address pool view. |
dhcp server ip-pool pool-name extended |
N/A |
|
3. Specify the IP address range. |
network ip range min-address max-address |
Not specified by default. |
|
4. Specify the IP address mask. |
network mask mask |
Not specified by default. |
|
5. Specify the IP address range for the DHCP clients of a specific vendor. |
vendor-class-identifier hex-string&<1-255> ip range min-address max-address |
Optional. Not configured by default. |
|
6. Specify the address lease duration. |
expired { day day [ hour hour [ minute minute [ second second ] ] ] | unlimited } |
Optional. One day by default. |
|
7. Exclude IP addresses from dynamic allocation. |
forbidden-ip ip-address&<1-8> |
Optional. Except IP addresses of the DHCP server interfaces, all addresses in the DHCP address pool are assignable by default. |
Excluded IP addresses specified with the forbidden-ip command in DHCP address pool view are not assignable in the current extended address pool, but are assignable in other address pools.
Configuring a domain name suffix for the client
You can specify a domain name suffix in each DHCP address pool on the DHCP server to provide the clients with the domain name suffix. With this suffix assigned, the client only needs to input part of a domain name, and the system adds the domain name suffix for name resolution. For more information about DNS, see "Configuring IPv4 DNS."
To configure a domain name suffix in the DHCP address pool:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter DHCP address pool view. |
dhcp server ip-pool pool-name [ extended ] |
N/A |
|
3. Specify a domain name suffix. |
domain-name domain-name |
Not specified by default. |
Configuring DNS servers for the client
To access hosts on the Internet through domain names, a DHCP client must contact a DNS server to resolve names. You can specify up to eight DNS servers in a DHCP address pool.
To configure DNS servers in a DHCP address pool:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter DHCP address pool view. |
dhcp server ip-pool pool-name [ extended ] |
N/A |
|
3. Specify DNS servers. |
dns-list ip-address&<1-8> |
No DNS server is specified by default. |
Configuring WINS servers and NetBIOS node type for the client
A Microsoft DHCP client using NetBIOS protocol must contact a Windows Internet Naming Service (WINS) server for name resolution. You can specify up to eight WINS servers for such clients in a DHCP address pool.
Specify a NetBIOS node type for the clients to approach name resolution. There are four NetBIOS node types:
· b (broadcast)-node—A b-node client sends the destination name in a broadcast message. The destination returns its IP address to the client after receiving the message.
· p (peer-to-peer)-node—A p-node client sends the destination name in a unicast message to the WINS server, and the WINS server returns the destination IP address.
· m (mixed)-node—An m-node client broadcasts the destination name. If it receives no response, it unicasts the destination name to the WINS server to get the destination IP address.
· h (hybrid)-node—An h-node client unicasts the destination name to the WINS server. If it receives no response, it broadcasts the destination name to get the destination IP address.
To configure WINS servers and NetBIOS node type in a DHCP address pool:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter DHCP address pool view. |
dhcp server ip-pool pool-name [ extended ] |
N/A |
|
3. Specify WINS servers. |
nbns-list ip-address&<1-8> |
Optional for b-node. No WINS server is specified by default. |
|
4. Specify the NetBIOS node type. |
netbios-type { b-node | h-node | m-node | p-node } |
Not specified by default. |
Configuring BIMS server information for the client
Perform this task to provide the Branch Intelligent Management System (BIMS) server IP address, port number, and shared key for the clients. The DHCP clients contact the BIMS server to get configuration files and perform software update and backup.
To configure the BIMS server IP address, port number, and shared key in the DHCP address pool:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter DHCP address pool view. |
dhcp server ip-pool pool-name [ extended ] |
N/A |
|
3. Specify the BIMS server IP address, port number, and shared key. |
bims-server ip ip-address [ port port-number ] sharekey [ cipher | simple ] key |
No BIMS server information is specified by default. |
Configuring gateways for the client
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter DHCP address pool view. |
dhcp server ip-pool pool-name [ extended ] |
N/A |
|
3. Specify gateways. |
gateway-list ip-address&<1-8> |
No gateway is specified by default. You can specify up to eight gateways in a DHCP address pool. |
Configuring Option 184 parameters for the client with voice service
To assign calling parameters to DHCP clients with voice service, you must configure Option 184 on the DHCP server. For more information about Option 184, see "Option 184."
To configure option 184 parameters in a DHCP address pool:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter DHCP address pool view. |
dhcp server ip-pool pool-name [ extended ] |
N/A |
|
3. Specify the IP address of the primary network calling processor. |
voice-config ncp-ip ip-address |
Not primary network calling processor is specified by default. |
|
4. Specify the IP address of the backup network calling processor. |
voice-config as-ip ip-address |
Optional. No backup network calling processor is specified by default. |
|
5. Configure the voice VLAN. |
voice-config voice-vlan vlan-id { disable | enable } |
Optional. No voice VLAN is configured by default. |
|
6. Specify the failover IP address and dialer string. |
voice-config fail-over ip-address dialer-string |
Optional. No failover IP address or dialer string is specified by default. |
Configuring the TFTP server and bootfile name for the client
For the DHCP server to support client auto-configuration, specify the IP address or name of a TFTP server and the bootfile name in the DHCP address pool. You do not need to perform any configuration on the DHCP client.
The DHCP client obtains these parameters from the DHCP server, and uses them to contact the TFTP server to request the configuration file used for system initialization.
1. When a router starts up without loading any configuration file, the system sets an active interface (such as the interface of the default VLAN) as the DHCP client to request from the DHCP server for parameters, such as an IP address and name of a TFTP server, and the bootfile name.
2. After receiving related parameters, the DHCP client sends a TFTP request to obtain the configuration file from the specified TFTP server for system initialization. If the client cannot get such parameters, it performs system initialization without loading any configuration file.
To configure the IP address and name of the TFTP server and the bootfile name in the DHCP address pool:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter DHCP address pool view. |
dhcp server ip-pool pool-name [ extended ] |
N/A |
|
3. Specify the IP address or the name of the TFTP server. |
· Specify the TFTP server: · Specify the name of the TFTP server: |
Use either command. Not specified by default. |
|
4. Specify the bootfile name. |
bootfile-name bootfile-name |
Not specified by default. |
Specifying a server's IP address for the DHCP client
Some DHCP clients need to obtain configuration information from a server, such as a TFTP server. You can specify the IP address of that server in each address pool of the DHCP server. The DHCP server sends the server's IP address to DHCP clients along with other configuration information.
To specify the IP address of a server:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter DHCP address pool view. |
dhcp server ip-pool pool-name [ extended ] |
N/A |
|
3. Specify the IP address of a server. |
next-server ip-address |
Not specified by default. |
Configuring self-defined DHCP options
|
|
CAUTION: Be careful when configuring self-defined DHCP options because such configuration may affect DHCP operation. |
By configuring self-defined DHCP options, you can
· Define new DHCP options. New configuration options come out with DHCP development. To support these new options, you can add them into the attribute list of the DHCP server.
· Define existing DHCP options. Vendors use Option 43 to define options that have no unified definitions in RFC 2132. The self-defined DHCP option enables DHCP clients to obtain vendor-specific information.
· Extend existing DHCP options. When the current DHCP options cannot meet the customers' requirements (for example, you cannot use the dns-list command to configure more than eight DNS server addresses), you can configure a self-defined option for extension.
To configure a self-defined DHCP option in a DHCP address pool:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter DHCP address pool view. |
dhcp server ip-pool pool-name [ extended ] |
N/A |
|
3. Configure a self-defined DHCP option. |
option code { ascii ascii-string | hex hex-string&<1-16> | ip-address ip-address&<1-8> } |
No self-defined DHCP option is configured by default. |
See Table 1 for a description of common options and corresponding commands.
|
Option |
Option name |
Corresponding command |
Command parameter |
|
3 |
Router Option |
gateway-list |
ip-address |
|
6 |
Domain Name Server Option |
dns-list |
ip-address |
|
15 |
Domain Name |
domain-name |
ascii |
|
44 |
NetBIOS over TCP/IP Name Server Option |
nbns-list |
ip-address |
|
46 |
NetBIOS over TCP/IP Node Type Option |
netbios-type |
hex |
|
66 |
TFTP server name |
tftp-server |
ascii |
|
67 |
Bootfile name |
bootfile-name |
ascii |
|
43 |
Vendor Specific Information |
N/A |
hex |
Enabling DHCP
Enable DHCP to validate other DHCP configurations.
To enable DHCP:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable DHCP. |
dhcp enable |
By default, DHCP is disabled. |
|
3. Enable log output on the DHCP server. |
dhcp server log enable |
Optional. By default, the DHCP server outputs logs. |
Enabling the DHCP server on an interface
Perform this task to enable the DHCP server on an interface. Upon receiving a DHCP request on the interface, the DHCP server assigns an IP address and other configuration parameters from the DHCP address pool to the DHCP client.
Configuration guidelines
Follow these guidelines when you enable the DHCP server on an interface:
· If a DHCP relay agent exists between the DHCP server and client, the DHCP server, regardless of whether the subaddress keyword is used, selects an IP address from the address pool containing the primary IP address of the DHCP relay agent's interface (connected to the client) for a requesting client.
· When the DHCP server and client are on the same subnet:
¡ With the keyword subaddress specified, the DHCP server preferably assigns an IP address from an address pool that resides on the same subnet as the primary IP address of the server interface (connecting to the client). If the address pool contains no assignable IP address, the server assigns an IP address from an address pool that resides on the same subnet as the secondary IP addresses of the server interface. If the interface has multiple secondary IP addresses, each address pool is tried in turn for address allocation.
¡ Without the keyword subaddress specified, the DHCP server can only assign an IP address from the address pool that resides on the same subnet as the primary IP address of the server interface.
Configuration procedure
To enable the DHCP server on an interface:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable the DHCP server on the interface. |
dhcp select server global-pool [ subaddress ] |
Optional. The default setting is enabled by default. |
Applying an extended address pool on an interface
After you create an extended address pool and apply it on an interface, a DHCP server, upon receiving a client's request on the interface, attempts to assign the client the statically bound IP address first and then an IP address from the specified address pool. If no IP address is available in this address pool, address allocation fails, and the DHCP server does not assign the client any IP address from other address pools.
Only an extended address pool can be applied on the interface. The address pool to be referenced must already exist.
To apply an extended address pool on an interface:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Apply an extended address pool on the interface. |
dhcp server apply ip-pool pool-name |
Optional. By default, the DHCP server has no extended address pool applied on its interface, and assigns an IP address from a common address pool to a requesting client. |
Configuring the DHCP server security functions
Configuration prerequisites
Before you perform this configuration, complete the following configurations on the DHCP server:
1. Enable DHCP.
2. Configure the DHCP address pool.
Enabling unauthorized DHCP server detection
Unauthorized DHCP servers on a network may assign wrong IP addresses to DHCP clients.
With unauthorized DHCP server detection enabled, the DHCP server checks whether a DHCP request contains Option 54 (Server Identifier Option). If yes, the DHCP server records in the option the IP address of the DHCP server that assigned an IP address to a requesting DHCP client and records the receiving interface. The administrator can use this information to check for unauthorized DHCP servers.
To enable unauthorized DHCP server detection:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable unauthorized DHCP server detection. |
dhcp server detect |
Disabled by default. |
With the unauthorized DHCP server detection enabled, the device logs each detected DHCP server once. The administrator can use the log information to find unauthorized DHCP servers.
Configuring IP address conflict detection
Before assigning an IP address, the DHCP server pings that IP address.
· If the server receives a response within the specified period, it selects and pings another IP address.
· If it receives no response, the server continues to ping the IP address until a specific number of ping packets are sent. If still no response is received, the server assigns the IP address to the requesting client. (The DHCP client probes the IP address by sending gratuitous ARP packets.)
To configure IP address conflict detection:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Specify the maximum number of ping packets to be sent for conflict detection. |
dhcp server ping packets number |
Optional. The default setting is one. The value 0 disables IP address conflict detection. |
|
3. Configure the ping timeout time. |
dhcp server ping timeout milliseconds |
Optional. The default setting is 500 ms. The value 0 disables IP address conflict detection. |
Configuring the DHCP server to work with authorized ARP
Only the clients that obtain an IP address from the DHCP server are considered as authorized clients. If the DHCP server also serves as the gateway, the DHCP server can work with authorized ARP to block unauthorized clients and prevent ARP spoofing attacks.
To enable the DHCP server to work with authorized ARP, perform the following:
· Configure the DHCP server to support authorized ARP—The DHCP server notifies authorized ARP to add/delete/change authorized ARP entries when adding/deleting/changing IP address leases.
· Enable authorized ARP—The ARP automatic learning function is disabled after you enable authorized ARP. ARP entries are added according to the IP address leases specified by the DHCP server, to avoid learning incorrect ARP entries.
The DHCP server works with authorized ARP for the following purposes:
· Only the clients that have obtained IP addresses from the DHCP server and have their ARP entries recorded on the DHCP server are authorized clients and can access the network normally.
· The clients that have not obtained IP addresses from the DHCP server are considered unauthorized clients and are unable to access the network.
· Disabling ARP automatic learning prevents network attacks such as IP/MAC address spoofing attacks, and only authorized users can access the network.
Configuration guidelines
Follow these guidelines when you configure the DHCP server to work with authorized ARP:
· Authorized ARP can only be configured on VLAN interfaces.
· When the working mode of the interface is changed from DHCP server to DHCP relay agent, neither the IP address leases nor the authorized ARP entries are deleted. Because these ARP entries may conflict with new ARP entries generated on the DHCP relay agent. H3C recommends you delete the existing IP address leases by using the reset dhcp server ip-in-use command before changing the interface working mode to DHCP relay agent.
· Disabling the DHCP server to support authorized ARP dose not delete the IP address leases, but deletes the corresponding authorized ARP entries.
For more information about authorized ARP, see Security Configuration Guide. For more information about the arp authorized enable command, see Security Command Reference.
Configuration procedure
To configure the DHCP server to work with authorized ARP:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable the DHCP server to work with authorized ARP. |
dhcp update arp |
Not enabled by default. |
|
4. Enable authorized ARP. |
arp authorized enable |
Disabled by default. |
Enabling client offline detection
With this feature enabled, the DHCP server considers that a DHCP client goes offline when the ARP entry for the client ages out. In addition, it removes the client's IP-to-MAC binding entry and releases the IP address of the client. Removing an ARP entry manually does not remove the corresponding client's IP-to-MAC binding.
To enable offline detection:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable offline detection. |
dhcp server client-detect enable |
Disabled by default. |
Enabling handling of Option 82
If the server is configured to ignore Option 82, it assigns an IP address to the client without adding Option 82 in the response message.
Configuration prerequisites
Before you perform this configuration, complete the following configurations on the DHCP server:
1. Enable DHCP.
2. Configure the DHCP address pool.
Enabling Option 82 handling
To enable the DHCP server to handle Option 82:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable the server to handle Option 82. |
dhcp server relay information enable |
Optional. Enabled by default. |
To support Option 82 requires configuring both the DHCP server and relay agent (or the device enabled with DHCP snooping). For more information, see "Configuring the DHCP relay agent" and "Configuring DHCP snooping."
Specifying the threshold for sending trap messages
Configuration prerequisites
Before you perform the configuration, use the snmp-agent target-host command to specify the destination address of the trap messages. For more information about the command, see Network Management and Monitoring Command Reference.
Configuration procedure
A DHCP server sends trap messages to the network management server when one of the following items reaches the specified threshold:
· The ratio of successfully allocated IP addresses to received DHCP requests
· The average IP address use of the address pool
· The maximum IP address use of the address pool
Trap messages help network administrators know the latest usage information about the DHCP server.
To specify the threshold for sending trap messages:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Specify the threshold for sending trap messages to the network management server. |
dhcp server threshold { allocated-ip threshold-value | average-ip-use threshold-value | max-ip-use threshold-value } |
Optional. Disabled by default. |
Displaying and maintaining the DHCP server
|
|
NOTE: A restart of the DHCP server or execution of the reset dhcp server ip-in-use command deletes all lease information. The DHCP server denies any DHCP request for lease extension, and the client must request an IP address again. |
|
Task |
Command |
Remarks |
|
Display information about IP address conflicts. |
display dhcp server conflict { all | ip ip-address } [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display information about lease expiration. |
display dhcp server expired { all | ip ip-address | pool [ pool-name ] } [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display information about assignable IP addresses. |
display dhcp server free-ip [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display IP addresses excluded from automatic allocation in the DHCP address pool. |
display dhcp server forbidden-ip [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display information about bindings. |
display dhcp server ip-in-use { all | ip ip-address | pool [ pool-name ] } [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display information about DHCP server statistics. |
display dhcp server statistics [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display tree organization information about address pools. |
display dhcp server tree { all | pool [ pool-name ] } [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Clear information about IP address conflicts. |
reset dhcp server conflict { all | ip ip-address } |
Available in user view. |
|
Clear information about dynamic bindings. |
reset dhcp server ip-in-use { all | ip ip-address | pool [ pool-name ] } |
Available in user view. |
|
Clear information about DHCP server statistics. |
reset dhcp server statistics |
Available in user view. |
DHCP server configuration examples
DHCP networking involves two types:
· The DHCP server and client are on the same subnet and perform direct message delivery.
· The DHCP server and client are not on the same subnet and communicate with each other through a DHCP relay agent.
The DHCP server configuration for the two types is the same.
Static IP address assignment configuration example
Network requirements
As shown in Figure 15, Switch (DHCP client) obtains a static IP address, DNS server address, and gateway address from AC (DHCP server).
Configuration procedure
1. Configure the IP address of VLAN-interface 2 on AC:
<AC> system-view
[AC] interface vlan-interface 2
[AC-Vlan-interface2] ip address 10.1.1.1 25
[AC-Vlan-interface2] quit
2. Configure the DHCP server:
# Enable DHCP.
[AC] dhcp enable
# Create DHCP address pool 0, configure a static IP-MAC binding, DNS server and gateway in it.
[AC] dhcp server ip-pool 0
[AC-dhcp-pool-0] static-bind ip-address 10.1.1.5 25
[AC-dhcp-pool-0] static-bind mac-address 000f-e200-0002
[AC-dhcp-pool-0] dns-list 10.1.1.2
[AC-dhcp-pool-0] gateway-list 10.1.1.126
[AC-dhcp-pool-0] quit
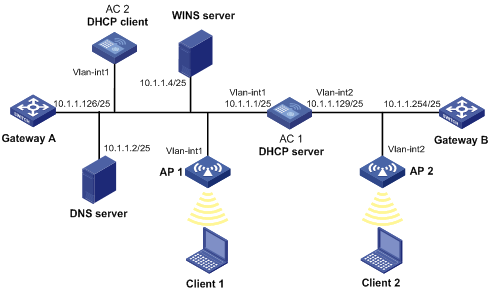
Dynamic IP address assignment configuration example
Network requirements
· As shown in Figure 16, the DHCP server (AC 1) assigns IP address to clients in subnet 10.1.1.0/24, which is subnetted into 10.1.1.0/25 and 10.1.1.128/25.
· The IP addresses of VLAN-interfaces 1 and 2 on AC 1 are 10.1.1.1/25 and 10.1.1.129/25 respectively.
· In address pool 10.1.1.0/25, the address lease duration is ten days and twelve hours, domain name suffix aabbcc.com, DNS server address 10.1.1.2/25, gateway 10.1.1.126/25, and WINS server 10.1.1.4/25.
· In address pool 10.1.1.128/25, the address lease duration is five days, domain name suffix aabbcc.com, DNS server address 10.1.1.2/25, and gateway address 10.1.1.254/25, and there is no WINS server address.
· The domain name and DNS server address on subnets 10.1.1.0/25 and 10.1.1.128/25 are the same. Therefore, the domain name suffix and DNS server address can be configured only for subnet 10.1.1.0/24. Subnet 10.1.1.128/25 can inherit the configuration of subnet 10.1.1.0/24.
|
|
NOTE: In this example, the number of requesting clients connected to VLAN-interface 1 should be no more than 122, and that of clients connected to VLAN-interface 2 should be no more than 124. |
Configuration procedure
1. Specify IP addresses for VLAN interfaces. (Details not shown.)
2. Configure basic functions of the AC. For more information, see WLAN Configuration Guide. (Details not shown.)
3. Configure the DHCP server:
# Enable DHCP.
<AC 1> system-view
[AC 1] dhcp enable
# Exclude IP addresses (addresses of the DNS server, WINS server and gateways).
[AC 1] dhcp server forbidden-ip 10.1.1.2
[AC 1] dhcp server forbidden-ip 10.1.1.4
[AC 1] dhcp server forbidden-ip 10.1.1.126
[AC 1] dhcp server forbidden-ip 10.1.1.254
# Configure DHCP address pool 0 (address range, client domain name suffix, and DNS server address).
[AC 1] dhcp server ip-pool 0
[AC 1-dhcp-pool-0] network 10.1.1.0 mask 255.255.255.0
[AC 1-dhcp-pool-0] domain-name aabbcc.com
[AC 1-dhcp-pool-0] dns-list 10.1.1.2
[AC 1-dhcp-pool-0] quit
# Configure DHCP address pool 1 (address range, gateway, lease duration, and WINS server).
[AC 1] dhcp server ip-pool 1
[AC 1-dhcp-pool-1] network 10.1.1.0 mask 255.255.255.128
[AC 1-dhcp-pool-1] gateway-list 10.1.1.126
[AC 1-dhcp-pool-1] expired day 10 hour 12
[AC 1-dhcp-pool-1] nbns-list 10.1.1.4
[AC 1-dhcp-pool-1] quit
# Configure DHCP address pool 2 (address range, gateway, and lease duration).
[AC 1] dhcp server ip-pool 2
[AC 1-dhcp-pool-2] network 10.1.1.128 mask 255.255.255.128
[AC 1-dhcp-pool-2] expired day 5
[AC 1-dhcp-pool-2] gateway-list 10.1.1.254
Self-defined option configuration example
Network requirements
As shown in Figure 17, the AC and AP belong to different subnets. The DHCP client (AP) obtains an IP address that belongs to subnet 10.10.1.0/24 from the DHCP server (AC).
The DHCP server assigns configuration information to DHCP clients through Option 43, a self-defined option. The format of Option 43 is shown in Figure 5. The value of Option 43 configured on the DHCP server in this example is 80 07 00 00 01 0A 01 01 01. The number 80 is the value of the sub-option type. The number 07 is the value of the sub-option length. The numbers 00 00 are the value of the PXE server type. The number 01 indicates the number of servers. The numbers 0A 01 01 01 indicate that the IP address of the AC is 10.1.1.1.

Configuration procedure
1. Specify IP addresses for the interfaces (Details not shown.).
2. Configure the DHCP server:
# Enable DHCP.
<AC> system-view
[AC] dhcp enable
# Configure DHCP address pool 0.
[AC] dhcp server ip-pool 0
# Specify the assignable IP address range in the address pool 0 for dynamic allocation.
[AC-dhcp-pool-0] network 10.10.1.0 mask 255.255.255.0
# Configure the values for Option 43.
[AC-dhcp-pool-0] option 43 hex 80 07 00 00 01 0A 01 01 01
Verifying the configuration
After the configuration, the AP can obtain an IP address from the AC. You can use the display dhcp server ip-in-use command to view the IP address assigned to the AP.
Troubleshooting DHCP server configuration
Symptom
A client's IP address dynamically obtains from the DHCP server conflicts with another IP address.
Analysis
Another host on the subnet might have the same IP address.
Solution
1. Disable the client's network adapter or disconnect the client's network cable. Ping the IP address of the client on another host to check whether there is a host using the same IP address.
2. If a ping response is received, the IP address has been manually configured on a host. Execute the dhcp server forbidden-ip command on the DHCP server to exclude the IP address from dynamic allocation.
3. Enable the network adapter or connect the network cable, release the IP address, and obtain another one on the client. For example, to release the IP address and obtain another one on a Windows XP DHCP client:
a. In Windows environment, execute the cmd command to enter the DOS environment.
b. Enter ipconfig /release to relinquish the IP address.
c. Enter ipconfig /renew to obtain another IP address.
Configuring the DHCP relay agent
The DHCP relay agent configuration is supported only on VLAN interfaces.
Overview
Fundamentals
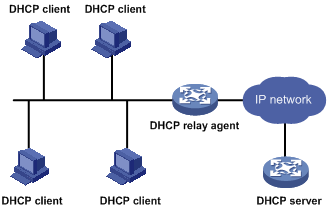
Figure 18 shows a typical application of the DHCP relay agent.
Figure 18 DHCP relay agent application
The DHCP server and client interact with each other in the same way regardless of whether the relay agent exists (see "Dynamic IP address allocation process").
Figure 19 DHCP relay agent work process
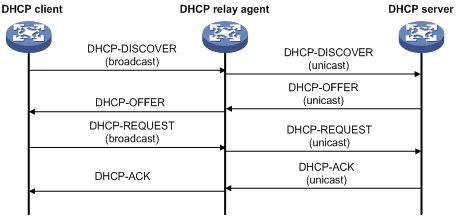
1. After receiving a DHCP-DISCOVER or DHCP-REQUEST broadcast message from a DHCP client, the DHCP relay agent fills the giaddr field of the message with its IP address and forwards the message to the designated DHCP server in unicast mode.
2. Based on the giaddr field, the DHCP server returns an IP address and other configuration parameters in a response to the relay agent, and the relay agent conveys it to the client.
DHCP relay agent support for Option 82
Option 82 records the location information about the DHCP client. It enables the administrator to locate the DHCP client for security control and accounting purposes. For more information, see "Relay agent option (Option 82)."
If the DHCP relay agent supports Option 82, it handles a DHCP request according to Option 82, if any. The handling strategies are described in Table 2.
If a response returned by the DHCP server contains Option 82, the DHCP relay agent removes the Option 82 before forwarding the response to the client.
Table 2 Handling strategies of the DHCP relay agent
|
If a DHCP request has… |
Handling strategy |
Padding format |
The DHCP relay agent… |
|
Option 82 |
Drop |
Random |
Drops the message. |
|
Keep |
Random |
Forwards the message without changing Option 82. |
|
|
Replace |
normal |
Forwards the message after replacing the original Option 82 with the Option 82 padded in normal format. |
|
|
verbose |
Forwards the message after replacing the original Option 82 with the Option 82 padded in verbose format. |
||
|
user-defined |
Forwards the message after replacing the original Option 82 with the user-defined Option 82. |
||
|
no Option 82 |
N/A |
normal |
Forwards the message after adding Option 82 padded in normal format. |
|
N/A |
verbose |
Forwards the message after adding the Option 82 padded in verbose format. |
|
|
N/A |
user-defined |
Forwards the message after adding the user-defined Option 82. |
DHCP relay agent configuration task list
|
Task |
Remarks |
|
Required. |
|
|
Required. |
|
|
Correlating a DHCP server group with a relay agent interface |
Required. |
|
Optional. |
|
|
Optional. |
|
|
Optional. |
|
|
Optional. |
Enabling DHCP
Enable DHCP to validate other DHCP relay agent settings.
To enable DHCP:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable DHCP. |
dhcp enable |
Disabled by default. |
Enabling the DHCP relay agent on an interface
With the DHCP relay agent enabled, an interface forwards incoming DHCP requests to a DHCP server for address allocation.
An IP address pool that contains the IP address of the DHCP relay agent interface must be configured on the DHCP server. Otherwise, the DHCP clients connected to the relay agent cannot obtain correct IP addresses.
To enable the DHCP relay agent on an interface:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable the DHCP relay agent on the current interface. |
dhcp select relay |
With DHCP is enabled, an interface works in the DHCP server mode. |
Correlating a DHCP server group with a relay agent interface
To improve availability, you can specify several DHCP servers as a group on the DHCP relay agent and correlate a relay agent interface with the server group. When the interface receives request messages from clients, the relay agent forwards them to all DHCP servers of the group.
Configuration guidelines
Follow these guidelines when you correlate a DHCP server group with a relay agent interface:
· You can specify up to 20 DHCP server groups on the relay agent.
· You can specify up to eight DHCP server addresses for each DHCP server group.
· The IP addresses of DHCP servers and those of relay agent's interfaces that connect DHCP clients cannot be on the same subnet. Otherwise, the client cannot obtain an IP address.
· A DHCP server group can correlate with one or multiple DHCP relay agent interfaces, while a relay agent interface can only correlate with one DHCP server group. If you use the dhcp relay server-select command multiple times, the most recent configuration takes effect. However, if the specified DHCP server group does not exist, the interface still uses the previous correlation.
· The group-id argument in the dhcp relay server-select command is configured by using the dhcp relay server-group command.
Configuration procedure
To correlate a DHCP server group with a relay agent interface:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Create a DHCP server group and add a server into the group. |
dhcp relay server-group group-id ip ip-address |
Not created by default. |
|
3. Enter interface view. |
interface interface-type interface-number |
N/A |
|
4. Correlate the DHCP server group with the current interface. |
dhcp relay server-select group-id |
By default, no interface is correlated with any DHCP server group. |
Configuring the DHCP relay agent security functions
Configuring address check
Address check can block illegal hosts from accessing external networks.
With this feature enabled, the DHCP relay agent can dynamically record clients' IP-to-MAC bindings after they obtain IP addresses through DHCP. You can also configure static IP-to-MAC bindings on the DHCP relay agent so that users can access external networks by using fixed IP addresses.
Upon receiving a packet from a host, the DHCP relay agent checks the source IP and MAC addresses in the packet against the recorded dynamic and static bindings. If no match is found, the DHCP relay agent does not learn the ARP entry of the host, and does not forward any reply to the host, which therefore cannot access external networks through the DHCP relay agent.
Configuration guidelines
Follow these guidelines when you configure address check:
· The dhcp relay address-check enable command can be executed only on VLAN interfaces.
· Before enabling address check on an interface, you must enable the DHCP service, and enable the DHCP relay agent on the interface. Otherwise, the address check configuration is ineffective.
· The dhcp relay address-check enable command only checks IP and MAC addresses, but not interfaces.
· When using the dhcp relay security static command to bind an interface to a static binding entry, make sure that the interface is configured as a DHCP relay agent. Otherwise, address entry conflicts may occur.
· When a synchronous/asynchronous serial interface requests an IP address through DHCP, the DHCP relay agent does not record the corresponding IP-to-MAC binding.
Configuration procedure
To create a static binding and enable address check:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Create a static binding. |
dhcp relay security static ip-address mac-address [ interface interface-type interface-number ] |
Optional. No static binding is created by default. |
|
3. Enter interface view. |
interface interface-type interface-number |
N/A |
|
4. Enable address check. |
dhcp relay address-check enable |
Disabled by default. |
Configuring periodic refresh of dynamic client entries
A DHCP client unicasts a DHCP-RELEASE message to the DHCP server to release its IP address. The DHCP relay agent simply conveys the message to the DHCP server and does not remove the IP-to-MAC entry of the client.
With this feature, the DHCP relay agent uses the IP address of a client and the MAC address of the DHCP relay interface to periodically send a DHCP-REQUEST message to the DHCP server.
· If the server returns a DHCP-ACK message or does not return any message within a specific interval, the DHCP relay agent ages out the entry.
· If the server returns a DHCP-NAK message, the relay agent keeps the entry.
To configure periodic refresh of dynamic client entries:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable periodic refresh of dynamic client entries. |
dhcp relay security refresh enable |
Optional. Enabled by default. |
|
3. Configure the refresh interval. |
dhcp relay security tracker { interval | auto } |
Optional. The default setting is auto. The auto interval is calculated by the relay agent according to the number of client entries. |
Configuring the DHCP relay agent to work with authorized ARP
Only clients that obtain an IP address from the DHCP server are considered as authorized clients. If the DHCP relay agent serves as the gateway, it can work with authorized ARP to block unauthorized clients and prevent ARP spoofing attacks.
To enable the DHCP relay agent to work with authorized ARP:
· Configure the DHCP relay agent to support authorized ARP—With this function enabled, the DHCP relay agent automatically records DHCP clients' IP-to-MAC bindings (called client entries), and notifies authorized ARP to add/delete/change authorized ARP entries when adding/deleting/changing client entries.
· Enable authorized ARP—The ARP automatic learning function is disabled after you enable authorized ARP. ARP entries are added according to the client entries recorded by the DHCP relay agent to avoid learning incorrect ARP entries.
The DHCP relay agent works with authorized ARP for the following purposes:
· Only the clients that have obtained IP addresses from the DHCP server and have their IP-to-MAC bindings recorded on the DHCP relay agent are authorized clients. Only authorized clients can access the network.
· Clients that have not obtained IP addresses from the DHCP server are considered unauthorized clients and are unable to access the network.
· Disabling ARP automatic learning prevents network attacks such as IP/MAC address spoofing attacks, and only authorized users can access the network, enhancing network security.
Configuration guidelines
· Authorized ARP can only be configured on VLAN interfaces.
· Disabling the DHCP relay agent to support authorized ARP deletes the corresponding authorized ARP entries.
· Because the DHCP relay agent does not notify the authorized ARP module of the static bindings, you need to configure the corresponding static ARP entries for authorized users that have statically specified IP addresses.
· For more information about authorized ARP, see Security Configuration Guide. For more information about the arp authorized enable command, see Security Command Reference.
Configuration procedure
To configure the DHCP relay agent to work with authorized ARP:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable the DHCP relay agent to work with authorized ARP. |
dhcp update arp |
Not enabled by default. |
|
4. Enable authorized ARP. |
arp authorized enable |
Not enabled by default. |
Enabling unauthorized DHCP server detection
Unauthorized DHCP servers may assign wrong IP addresses to DHCP clients.
With unauthorized DHCP servers detection enabled, the DHCP relay agent checks whether a request contains Option 54 (Server Identifier Option). If yes, the DHCP relay agent records in the option the IP address of the DHCP server that assigned an IP address to a requesting DHCP client, and records the receiving interface. The administrator can use this information to check for unauthorized DHCP servers.
The relay agent logs a DHCP server only once.
To enable unauthorized DHCP server detection:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable unauthorized DHCP server detection. |
dhcp relay server-detect |
Disabled by default. |
Enabling DHCP starvation attack protection
A DHCP starvation attack occurs when an attacker constantly sends forged DHCP requests using different MAC addresses in the chaddr field to a DHCP server. This exhausts the IP address resources of the DHCP server so legitimate DHCP clients cannot obtain IP addresses. The DHCP server may also fail to work because of exhaustion of system resources. The following methods are available to relieve or prevent such attacks.
· To relieve a DHCP starvation attack that uses DHCP packets encapsulated with different source MAC addresses, you can limit the number of ARP entries that a Layer 3 interface can learn or MAC addresses that a Layer 2 port can learn. You can also configure an interface that has learned the maximum MAC addresses to discard packets whose source MAC addresses are not in the MAC address table.
· To prevent a DHCP starvation attack that uses DHCP requests encapsulated with the same source MAC address, you can enable MAC address check on the DHCP relay agent. The DHCP relay agent compares the chaddr field of a received DHCP request with the source MAC address in the frame header. If they are the same, the DHCP relay agent decides this request as valid and forwards it to the DHCP server. If not, it discards the DHCP request.
To enable MAC address check:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable MAC address check. |
dhcp relay check mac-address |
The default setting is disabled. |
A DHCP relay agent changes the source MAC addresses of DHCP packets before forwarding them out. Therefore, enable MAC address check only on the DHCP relay agent directly connected to the DHCP clients. If you enable this feature on an intermediate relay agent, it may discard valid DHCP packets and the sending clients do not obtain IP addresses.
Enabling client offline detection
With this feature enabled, the DHCP relay agent considers that a DHCP client goes offline when the ARP entry for the client ages out. In addition, it removes the client entry and sends a DHCP-RELEASE message to the DHCP server to release the IP address of the client.
To enable offline detection:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable offline detection. |
dhcp relay client-detect enable |
Disabled by default. |
Removing an ARP entry manually does not remove the corresponding client's IP-to-MAC binding. When the client goes offline, use the undo dhcp relay security command to remove the IP-to-MAC binding manually.
Configuring the DHCP relay agent to release an IP address
You can configure the relay agent to release a client's IP address. The relay agent sends a DHCP-RELEASE message that contains the specified IP address. Upon receiving the DHCP-RELEASE message, the DHCP server releases the IP address. Meanwhile, the client entry is removed from the DHCP relay agent. The IP address to be released must be available in a dynamic client entry.
To configure the DHCP relay agent to send DHCP-RELEASE messages:
|
Step |
Command |
|
1. Enter system view. |
system-view |
|
2. Configure the DHCP relay agent to release an IP address. |
dhcp relay release ip client-ip |
Dynamic client entries can be generated only after you enable address check and authorized ARP support on the DHCP relay agent.
Configuring the DHCP relay agent to handle Option 82
Configuration prerequisites
Before performing this configuration, complete the following tasks:
1. Enable DHCP.
2. Enable the DHCP relay agent on the specified interface.
3. Correlate a DHCP server group with relay agent interfaces.
To support Option 82, you must perform related configurations on both the DHCP server and relay agent. For more information about DHCP server configuration, see "Configuring the DHCP server."
If the handling strategy of the DHCP relay agent is configured as replace, you must configure a padding format for Option 82. If the handling strategy is keep or drop, you need not configure any padding format.
The system name (sysname) if padded in sub-option 1 (node identifier) of Option 82 must not contain spaces. Otherwise, the DHCP relay agent drops the message.
Configuration procedure
To configure the DHCP relay agent to support Option 82:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable the relay agent to handle Option 82. |
dhcp relay information enable |
The default setting is disabled. |
|
4. Configure the strategy for handling DHCP requests containing Option 82. |
dhcp relay information strategy { drop | keep | replace } |
Optional. The default setting is replace. |
|
5. Configure non-user-defined Option 82. |
· Configure the padding format for Option 82: · Configure the code type for the circuit
ID sub-option: · Configure the code type for the remote ID
sub-option: |
Optional. By default: · The padding format for Option 82 is normal. · The code type for the circuit ID sub-option depends on the padding format of Option 82. Each field has its own code type. · The code type for the remote ID sub-option is hex. The remote ID sub-option configuration and the circuit ID sub-option configuration apply to non-user-defined Option 82 only. |
|
6. Configure user-defined Option 82. |
· Configure the padding content for the circuit
ID sub-option: · Configure the padding content for the remote
ID sub-option: |
Optional. By default, the padding content depends on the padding format of Option 82. |
Displaying and maintaining the DHCP relay agent
|
Task |
Command |
Remarks |
|
Display information about DHCP server groups correlated to a specific or all interfaces. |
display dhcp relay { all | interface interface-type interface-number } [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display Option 82 configuration information on the DHCP relay agent. |
display dhcp relay information { all | interface interface-type interface-number } [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display information about bindings of DHCP relay agents. |
display dhcp relay security [ ip-address | dynamic | static ] [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display statistics information about bindings of DHCP relay agents. |
display dhcp relay security statistics [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display information about the refreshing interval for entries of dynamic IP-to-MAC bindings. |
display dhcp relay security tracker [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display information about the configuration of a specific or all DHCP server groups. |
display dhcp relay server-group { group-id | all } [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display packet statistics on the DHCP relay agent. |
display dhcp relay statistics [ server-group { group-id | all } ] [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Clear packet statistics on the DHCP relay agent. |
reset dhcp relay statistics [ server-group group-id ] |
Available in user view. |
DHCP relay agent configuration examples
DHCP relay agent configuration example
Network requirements
As shown in Figure 20, VLAN-interface 1 on the DHCP relay agent (AC) connects to the network where DHCP clients reside. The IP address of VLAN-interface 1 is 10.10.1.1/24 and IP address of VLAN-interface 2 is 10.1.1.2/24 that communicates with the DHCP server 10.1.1.1/24. In Figure 20, AC forwards messages between DHCP clients and the DHCP server.
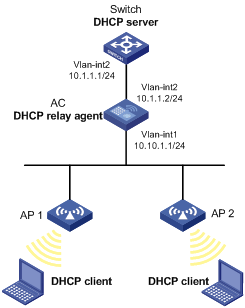
Configuration procedure
# Specify IP addresses for the interfaces. (Details not shown.)
# Configure basic functions of the AC. For more information, see WLAN Configuration Guide. (Details not shown.)
# Enable DHCP.
<AC> system-view
[AC] dhcp enable
# Add DHCP server 10.1.1.1 into DHCP server group 1.
[AC] dhcp relay server-group 1 ip 10.1.1.1
# Enable the DHCP relay agent on VLAN-interface 1.
[AC] interface vlan-interface 1
[AC-Vlan-interface1] dhcp select relay
# Correlate VLAN-interface 1 to DHCP server group 1.
[AC-Vlan-interface1] dhcp relay server-select 1
|
|
NOTE: · Performing the configuration on the DHCP server is also required to guarantee the client-server communication through the relay agent. For DHCP server configuration information, see "DHCP server configuration examples." · Because the DHCP relay agent and server are on different subnets, you need to configure a static route or dynamic routing protocol to make them reachable to each other. |
DHCP relay agent Option 82 support configuration example
Network requirements
· As shown in Figure 20, enable Option 82 on the DHCP relay agent (AC).
· Configure the handling strategy for DHCP requests containing Option 82 as replace.
· Configure the padding content for the circuit ID sub-option as company001 and for the remote ID sub-option as device001.
· AC forwards DHCP requests to the DHCP server (Switch) after replacing Option 82 in the requests, so that the DHCP clients can obtain IP addresses.
Configuration procedure
# Specify IP addresses for the interfaces. (Details not shown.)
# Configure basic functions of the AC. For more information, see WLAN Configuration Guide. (Details not shown.)
# Enable DHCP.
<AC> system-view
[AC] dhcp enable
# Add DHCP server 10.1.1.1 into DHCP server group 1.
[AC] dhcp relay server-group 1 ip 10.1.1.1
# Enable the DHCP relay agent on VLAN-interface 1.
[AC] interface vlan-interface 1
[AC-Vlan-interface1] dhcp select relay
# Correlate VLAN-interface 1 to DHCP server group 1.
[AC-Vlan-interface1] dhcp relay server-select 1
# Enable the DHCP relay agent to support Option 82, and perform Option 82-related configurations.
[AC-Vlan-interface1] dhcp relay information enable
[AC-Vlan-interface1] dhcp relay information strategy replace
[AC-Vlan-interface1] dhcp relay information circuit-id string company001
[AC-Vlan-interface1] dhcp relay information remote-id string device001
|
|
NOTE: You need to perform corresponding configurations on the DHCP server to make the Option 82 configurations function normally. |
Troubleshooting DHCP relay agent configuration
Symptom
DHCP clients cannot obtain any configuration parameters through the DHCP relay agent.
Analysis
Some problems may occur with the DHCP relay agent or server configuration.
Solution
To locate the problem, enable debugging and execute the display command on the DHCP relay agent to view the debugging information and interface state information.
Verify the following:
1. DHCP is enabled on the DHCP server and relay agent.
2. The DHCP server has an address pool on the same subnet as the DHCP clients.
3. The DHCP server and DHCP relay agent can reach each other.
4. The relay agent interface connected to DHCP clients is correlated with a correct DHCP server group and the IP addresses of the group members are correct.
Configuring DHCP client
The DHCP client configuration is supported only on VLAN interfaces.
You cannot configure an interface of an aggregation group as a DHCP client.
When multiple VLAN interfaces with the same MAC address use DHCP for IP address acquisition through a relay agent, the DHCP server cannot be a Windows Server 2000 or Windows Server 2003.
Introduction to DHCP client
With DHCP client enabled, an interface uses DHCP to obtain configuration parameters such as an IP address from the DHCP server.
Enabling the DHCP client on an interface
To enable the DHCP client on an interface:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable the DHCP client on the interface. |
ip address dhcp-alloc [ client-identifier mac interface-type interface-number ] |
Disabled by default. |
An interface can be configured to acquire an IP address in multiple ways. The latest configuration overwrites the previous one.
Secondary IP addresses cannot be configured on an interface that is enabled with the DHCP client.
If the IP address that interface A obtains from the DHCP server is on the same network segment as the IP address of interface B, interface A neither uses the IP address nor requests any IP address from the DHCP server, unless the IP address of interface B is manually deleted and interface A is brought up again by first executing the shutdown command and then the undo shutdown command or the DHCP client is re-enabled on interface A by executing the undo ip address dhcp-alloc command and then the ip address dhcp-alloc command.
Displaying and maintaining the DHCP client
|
Task |
Command |
Remarks |
|
Display specified configuration information. |
display dhcp client [ verbose ] [ interface interface-type interface-number ] [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
DHCP client configuration example
Network requirements
As shown in Figure 16, AC 2 contacts the DHCP server through VLAN-interface 1 to obtain an IP address on a LAN.
Configuration procedure
The following is the configuration on AC 2 shown in Figure 16.
# Enable the DHCP client on VLAN-interface 1.
<AC 2> system-view
[AC 2] interface vlan-interface 1
[AC 2-Vlan-interface1] ip address dhcp-alloc
|
|
NOTE: To implement the DHCP client-server model, you need to perform related configuration on the DHCP server. For more information, see "DHCP server configuration examples." |
Configuring DHCP snooping
A DHCP snooping-enabled device must be either between the DHCP client and relay agent, or between the DHCP client and server. It does not work if it is between the DHCP relay agent and DHCP server.
After configuring DHCP snooping on a WLAN-ESS interface, to make the configuration take effect, use the service-template disable command to disable the service template first, and then use the service-template enable command to enable the service template again.
Overview
DHCP snooping defines trusted and untrusted ports to make sure that clients obtain IP addresses only from authorized DHCP servers.
· Trusted—A trusted port can forward DHCP messages normally to make sure the clients get IP addresses from authorized DHCP servers.
· Untrusted—An untrusted port discards received DHCP-ACK and DHCP-OFFER messages to prevent unauthorized servers from assigning IP addresses.
DHCP snooping reads DHCP-ACK messages received from trusted ports and DHCP-REQUEST messages to create DHCP snooping entries. A DHCP snooping entry includes the MAC and IP addresses of a client, the port that connects to the DHCP client, and the VLAN of the port.
The ARP fast-reply feature needs to use DHCP snooping entries. ARP fast-reply is implemented based on DHCP snooping entries to reduce ARP broadcast traffic. For more information, see "Configuring ARP fast-reply."
Application of trusted and untrusted ports
As shown in Figure 21, configure the DHCP snooping device's port that is connected to the DHCP server as a trusted port. The trusted port forwards response messages from the DHCP server to the client. So the DHCP client can obtain an IP address from the authorized DHCP server.
Figure 21 Configuring trusted and untrusted ports
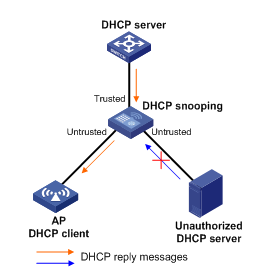
DHCP snooping support for Option 82
Option 82 records the location information about the DHCP client so the administrator can locate the DHCP client for security control and accounting purposes. For more information about Option 82, see "Relay agent option (Option 82)."
If DHCP snooping supports Option 82, it handles clients' requests according to Option 82. Table 3 describes the handling strategies.
If a reply returned by the DHCP server contains Option 82, the DHCP snooping device removes the Option 82 before forwarding the reply to the client. If the reply contains no Option 82, the DHCP snooping device forwards it directly.
Table 3 Handling strategies of DHCP snooping
|
If a DHCP request has… |
Handling strategy |
Padding format |
The DHCP snooping device… |
|
Option 82 |
Drop |
N/A |
Drops the message. |
|
Keep |
Random |
Forwards the message without changing Option 82. |
|
|
Replace |
normal |
Forwards the message after replacing the original Option 82 with the Option 82 padded in normal format. |
|
|
verbose |
Forwards the message after replacing the original Option 82 with the Option 82 padded in verbose format. |
||
|
user-defined |
Forwards the message after replacing the original Option 82 with the user-defined Option 82. |
||
|
Append |
normal |
Forwards the message without changing Option 82. |
|
|
verbose |
Forward the message without changing Option 82. |
||
|
private |
Forwards the message after adding sub-option 9 to option 82 or adding content to sub-option 9 that option 82 contains. |
||
|
standard |
Forwards the message without changing Option 82. |
||
|
user-defined |
Forwards the message without changing Option 82. |
||
|
no Option 82 |
N/A |
normal |
Forwards the message after adding the Option 82 padded in normal format. |
|
N/A |
private |
Forwards the message after adding Option 82 padded in private format. |
|
|
N/A |
standard |
Forwards the message after adding Option 82 padded in standard format. |
|
|
N/A |
verbose |
Forwards the message after adding the Option 82 padded in verbose format. |
|
|
N/A |
user-defined |
Forwards the message after adding the user-defined Option 82. |
The handling strategy and padding format for Option 82 on the DHCP snooping device are the same as those on the relay agent.
DHCP snooping configuration task list
|
Task |
Remarks |
|
Required. |
|
|
Optional. |
|
|
Optional. |
|
|
Optional. |
|
|
Optional. |
|
|
Enabling the DHCP snooping device to verify DHCP broadcast replies |
Optional. |
Configuring DHCP snooping basic functions
Follow these guidelines to configure DHCP snooping basic functions:
· You must specify the ports connected to authorized DHCP servers as trusted ports to make sure that DHCP clients can obtain valid IP addresses. The trusted ports and the ports connected to DHCP clients must be in the same VLAN.
· You can specify Layer 2 Ethernet interfaces, Layer 2 aggregate interfaces, and WLAN-ESS interfaces as trusted ports. For more information about aggregate interfaces, see Layer 2 Configuration Guide. For more information about WLAN-ESS interfaces, see WLAN Configuration Guide.
· If a Layer 2 Ethernet interface is added to an aggregation group, the DHCP snooping configuration of the interface does not take effect. After the interface quits the aggregation group, the configuration becomes effective.
· DHCP snooping can work with basic QinQ or flexible QinQ. When receiving a packet without any VLAN tag from the DHCP client to the DHCP server, the DHCP snooping device adds a VLAN tag to the packet. If the packet has one VLAN tag, the device adds another VLAN tag to the packet and records the two VLAN tags in a DHCP snooping entry. The newly added VLAN tag is the outer tag. If the packet has two VLAN tags, the device directly forwards the packet to the DHCP server without adding any tag. If you need to add a new VLAN tag and meanwhile modify the original VLAN tag for the packet, DHCP snooping cannot work with flexible QinQ.
To configure DHCP snooping basic functions:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable DHCP snooping. |
dhcp-snooping |
Disabled by default. |
|
3. Enter Ethernet interface view. |
interface interface-type interface-number |
The interface connects to the DHCP server. |
|
4. Specify the port as a trusted port that records the IP-to-MAC bindings of clients. |
dhcp-snooping trust |
After DHCP snooping is enabled, a port is an untrusted port by default. |
|
5. Return to system view. |
quit |
N/A |
|
6. Enter interface view. |
interface interface-type interface-number |
The interface indirectly connects to the DHCP client. |
|
7. Specify the port as a trusted port that does not record the IP-to-MAC bindings of clients. |
dhcp-snooping trust no-user-binding |
Optional. After DHCP snooping is enabled, a port is an untrusted port by default. |
|
8. Return to system view |
quit |
N/A |
|
9. Configure DHCP snooping to record Option 55 and Option 60 for the user. |
dhcp-snooping binding record user-identity |
Optional. Disabled by default. |
Configuring DHCP snooping to support Option 82
Follow these guidelines to configure DHCP snooping to support Option 82:
· You can only configure DHCP snooping to support Option 82 on Layer 2 Ethernet interfaces, Layer 2 aggregate interfaces, and WLAN-ESS interfaces.
· If a Layer 2 Ethernet interface is added to an aggregation group, enabling DHCP snooping to support Option 82 on the interface does not take effect. After the interface quits the aggregation group, the configuration becomes effective.
· To support Option 82, perform configurations on both the DHCP server and the DHCP snooping device. For configuration on a DHCP server, see "Configuring the DHCP server."
· If the handling strategy of the DHCP-snooping device is configured as replace, configure a padding format for Option 82. If the handling strategy is keep or drop, you do not need to configure any padding format.
· If Option 82 contains the device name, the device name must contain no spaces. Otherwise, the DHCP-snooping device drops the message. You can use the sysname command to specify the device name. For more information about this command, see Fundamentals Command Reference.
· If DHCP snooping and QinQ work together or the DHCP snooping device receives a DHCP packet with two VLAN tags, and the normal or verbose padding format is adopted for Option 82, DHCP snooping fills the VLAN ID field of sub-option 1 with outer VLAN tag.inner VLAN tag. For example, if the outer VLAN tag is 10 (a in hexadecimal) and the inner VLAN tag is 20 (14 in hexadecimal), the VLAN ID is 000a.0014.
To configure DHCP snooping to support Option 82:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable DHCP snooping to support Option 82. |
dhcp-snooping information enable |
Disabled by default. |
|
4. Configure the handling strategy for requests containing Option 82. |
dhcp-snooping information strategy { append | drop | keep | replace } |
Optional. replace by default. |
|
5. Configure Option 82 in the non-user-defined padding format. |
· Configure the padding format for Option 82: · Configure the code type for the circuit
ID sub-option: · Configure the code type for the remote ID
sub-option: · Enable sub-option 9: |
Optional. By default: · The padding format for Option 82 is normal. · The code type for the circuit ID sub-option depends on the padding format of Option 82. Each field has its own code type. · The code type for the remote ID sub-option is hex. · Sub-option 9 is not enabled. The private padding format supports only the hex code type. The remote ID sub-option configuration and the circuit ID sub-option code type configuration apply to non-user-defined Option 82 only. For sub-option 9 configuration, when append strategy is adopted, the sysname and the primary IP address of the Loopback0 interface are padded. When some other strategy is adopted, only the sysname is padded. |
|
6. Configure user-defined Option 82. |
· Configure the padding content for the circuit
ID sub-option: · Configure the padding content for the remote
ID sub-option: · Configure the padding content for the
sub-option 9: |
Optional. By default: · The padding content for the circuit ID sub-option depends on the padding format of Option 82. · The padding content for the remote ID sub-option depends on the padding format of Option 82. · Sub-option 9 is not padded. |
Configuring DHCP snooping entries backup
DHCP snooping entries cannot survive a reboot. If the DHCP snooping device is rebooted, security modules that use DHCP snooping entries to authenticate users reject requests from clients until new entries are learned.
The DHCP snooping entries backup feature enables you to store DHCP snooping entries in a file. When the DHCP snooping device reboots, it reads DHCP snooping entries from this file.
To configure DHCP snooping entries backup:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Specify the name of the file for storing DHCP snooping entries. |
dhcp-snooping binding database filename filename |
Not specified by default. DHCP snooping entries are stored immediately after this command is used and then updated at the interval set by the dhcp-snooping binding database update interval command. |
|
3. Back up DHCP snooping entries to the file. |
dhcp-snooping binding database update now |
Optional. DHCP snooping entries are stored to the file each time this command is used. |
|
4. Set the interval at which the DHCP snooping entry file is refreshed. |
dhcp-snooping binding database update interval minutes |
Optional. By default, the file is not refreshed periodically. |
After DHCP snooping is disabled with the undo dhcp-snooping command, the device deletes all DHCP snooping entries, including those stored in the file.
Enabling DHCP starvation attack protection
A DHCP starvation attack occurs when an attacker constantly sends forged DHCP requests using different MAC addresses in the chaddr field to a DHCP server. This exhausts the IP address resources of the DHCP server so legitimate DHCP clients cannot obtain IP addresses. The DHCP server may also fail to work because of exhaustion of system resources. You can protect against starvation attacks in the following ways:
· To relieve a DHCP starvation attack that uses DHCP packets encapsulated with different source MAC addresses, you can limit the number of MAC addresses that a Layer 2 port can learn.
· To prevent a DHCP starvation attack that uses DHCP requests encapsulated with the same source MAC address, you can enable MAC address check on the DHCP snooping device. With this function enabled, the DHCP snooping device compares the chaddr field of a received DHCP request with the source MAC address field of the frame. If they are the same, the request is considered valid and forwarded to the DHCP server. If not, the request is discarded.
To enable MAC address check:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable MAC address check. |
dhcp-snooping check mac-address |
Disabled by default. You can enable MAC address check only on Layer 2 Ethernet interfaces, Layer 2 aggregate interfaces, and WLAN-ESS interfaces. |
Enabling DHCP-REQUEST message attack protection
Attackers may forge DHCP-REQUEST messages to renew the IP address leases for legitimate DHCP clients that no longer need the IP addresses. These forged messages keep a victim DHCP server renewing the leases of IP addresses instead of releasing the IP addresses. This wastes IP address resources.
To prevent such attacks, you can enable DHCP-REQUEST message check on DHCP snooping devices. This feature uses DHCP snooping entries to check incoming DHCP-REQUEST messages.
· If a matching entry is found for a message, the DHCP snooping device compares the entry with the message information. If they are consistent, the DHCP-REQUEST message is considered a valid lease renewal request and forwarded to the DHCP server. If they are not consistent, the message is considered as a forged lease renewal request and discarded.
· If no matching entry is found, the message is considered valid and forwarded to the DHCP server.
To enable DHCP-REQUEST message check:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable DHCP-REQUEST check. |
dhcp-snooping check request-message |
Disabled by default. You can enable DHCP-REQUEST check only on Layer 2 Ethernet interfaces, Layer 2 aggregate interfaces, and WLAN-ESS interfaces. |
Enabling the DHCP snooping device to verify DHCP broadcast replies
By default, if the DHCP server sends DHCP-OFFER and DHCP-ACK messages to a broadcast address, these messages are sent to all ACs and then to all APs. This burdens the WLAN network.
The DHCP broadcast reply verification function enables the DHCP snooping device to drop DHCP-OFFER and DHCP-ACK broadcast messages that do not match any DHCP snooping entries. This function limits the number of broadcasts in a WLAN, saving network resources.
To enable the DHCP snooping device to verify DHCP broadcast replies:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable the DHCP snooping device to verify DHCP broadcast replies. |
dhcp-snooping verify reply-message |
By default, the DHCP snooping device does not verify DHCP broadcast replies. It forwards the replies to the destination broadcast address. |
Displaying and maintaining DHCP snooping
|
Task |
Command |
Remarks |
|
Display DHCP snooping entries. |
display dhcp-snooping [ ip ip-address ] [ verbose ] [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display Option 82 configuration information on the DHCP snooping device. |
display dhcp-snooping information { all | interface interface-type interface-number } [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display DHCP packet statistics on the DHCP snooping device. |
display dhcp-snooping packet statistics [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display information about trusted ports. |
display dhcp-snooping trust [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Display the information about DHCP snooping entry file. |
display dhcp-snooping binding database [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
|
Clear DHCP snooping entries. |
reset dhcp-snooping { all | ip ip-address } |
Available in user view. |
|
Clear DHCP packet statistics on the DHCP snooping device. |
reset dhcp-snooping packet statistics |
Available in user view. |
DHCP snooping configuration example
ACs have either 10 GE or GE interfaces. Table 4 identifies the Ethernet interfaces (GigabitEthernet 1/0/1, in this example) on different types of ACs.
If the AC is an AC module installed on a switch, make sure the internal Ethernet interface that connects the switch to the AC module has correct settings, including in particular VLAN settings.
Table 4 AC Ethernet interfaces
|
Hardware |
AC Ethernet interfaces |
|
AC modules (installed in a switch) |
|
|
LSQM1WCMD0 LSRM1WCM3A1 LSUM3WCMD0 LSUM1WCME0 |
The internal Ethernet interface that connects the AC module to the switch. |
|
Wireless switches |
|
|
WX3024E WX3010E |
The internal Ethernet interface that connects the AC engine to the switching engine. |
|
ACs |
|
|
WX6103 |
The internal Ethernet interface that connects the MPU to the switching module. |
|
WX5002V2 WX5004 WX3510E WX3540E WX5510E |
Any Ethernet interface on the AC. |
|
WX2540E WAC360 WAC361 |
Any LAN or WAN interfaces on the AC. |
|
WX5540E |
The internal Ethernet interface that connects the AC engine to the switching engine. |
Network requirements
· As shown in Figure 22, the AC is connected to a DHCP server through GigabitEthernet 1/0/1, and to the AP through GigabitEthernet 1/0/2.
· GigabitEthernet 1/0/1 forwards DHCP server responses while the other two do not.
· Switch 2 records clients' IP-to-MAC address bindings in DHCP-REQUEST messages and DHCP-ACK messages received from trusted ports.
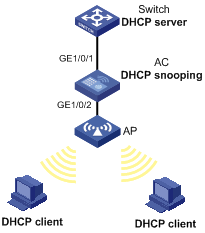
Configuration procedure
# Configure basic functions of the AC. For more information, see WLAN Configuration Guide. (Details not shown.)
# Enable DHCP snooping.
<AC> system-view
[AC] dhcp-snooping
# Specify GigabitEthernet 1/0/1 as trusted.
[AC] interface gigabitethernet 1/0/1
[AC-GigabitEthernet1/0/1] dhcp-snooping trust
[AC-GigabitEthernet1/0/1] quit
Configuring BOOTP client
BOOTP client configuration applies to only VLAN interfaces.
If several VLAN interfaces sharing the same MAC address obtain IP addresses through a BOOTP relay agent, the BOOTP server cannot be a Windows Server 2000 or Windows Server 2003.
BOOTP application
After you specify an interface of a device as a BOOTP client, the interface can use BOOTP to get information (such as IP address) from the BOOTP server.
To use BOOTP, an administrator must configure a BOOTP parameter file for each BOOTP client on the BOOTP server. The parameter file contains information such as MAC address and IP address of a BOOTP client. When a BOOTP client sends a request to the BOOTP server, the BOOTP server searches for the BOOTP parameter file and returns the corresponding configuration information.
BOOTP is usually used in relatively stable environments. In network environments that change frequently, DHCP is more suitable.
Because a DHCP server can interact with a BOOTP client, you can use the DHCP server to configure an IP address for the BOOTP client, without any BOOTP server.
Obtaining an IP address dynamically
A BOOTP client dynamically obtains an IP address from a BOOTP server as follows:
1. The BOOTP client broadcasts a BOOTP request, which contains its own MAC address.
2. The BOOTP server receives the request and searches the configuration file for the corresponding IP address and other information according to the MAC address of the BOOTP client.
3. The BOOTP server returns a BOOTP response to the BOOTP client.
4. The BOOTP client obtains the IP address from the received response.
Protocols and standards
· RFC 951, Bootstrap Protocol (BOOTP)
· RFC 2132, DHCP Options and BOOTP Vendor Extensions
· RFC 1542, Clarifications and Extensions for the Bootstrap Protocol
Configuring an interface to dynamically obtain an IP address through BOOTP
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Configure an interface to dynamically obtain an IP address through BOOTP. |
ip address bootp-alloc |
By default, an interface does not use BOOTP to obtain an IP address. |
Displaying and maintaining BOOTP client configuration
|
Task |
Command |
Remarks |
|
Display BOOTP client information. |
display bootp client [ interface interface-type interface-number ] [ | { begin | exclude | include } regular-expression ] |
Available in any view. |
BOOTP client configuration example
Network requirement
As shown in Figure 16, AC 2's port belonging to VLAN 1 is connected to the LAN. VLAN-interface 1 obtains an IP address from the DHCP server by using BOOTP.
Configuration procedure
The following describes only the configuration on AC 2 serving as a client.
# Configure VLAN-interface 1 to dynamically obtain an IP address from the DHCP server.
<AC 2> system-view
[AC 2] interface vlan-interface 1
[AC 2-Vlan-interface1] ip address bootp-alloc
|
|
NOTE: To make the BOOTP client obtain an IP address from the DHCP server, you need to perform additional configurations on the DHCP server. For more information, see "DHCP server configuration examples." |

