- Table of Contents
-
- 18-Network Management and Monitoring Configuration Guide
- 00-Preface
- 01-Information center configuration
- 02-Flow log configuration
- 03-Fast log output configuration
- 04-NetStream configuration
- 05-Sampler configuration
- 06-Mirroring configuration
- 07-Packet capture configuration
- 08-NQA configuration
- 09-Track configuration
- 10-BFD configuration
- 11-Error code detection configuration
- 12-Monitor Link configuration
- 13-Smart Link configuration
- 14-Interface backup configuration
- 15-Interface collaboration configuration
- 16-System maintenance and debugging configuration
- 17-NTP configuration
- 18-EAA configuration
- 19-Process monitoring and maintenance configuration
- 20-gRPC configuration
- 21-NETCONF configuration
- 22-CWMP configuration
- 23-SNMP configuration
- 24-RMON configuration
- 25-Event MIB configuration
- 26-GOLD configuration
- 27-Process placement configuration
- 28-Cloud connection configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 10-BFD configuration | 269.18 KB |
Contents
Single-hop detection and multihop detection
Restrictions and guidelines: BFD configuration
Configuring BFD sessions in echo packet mode
Configuring detection time settings
Configuring BFD sessions in control packet mode
About BFD session creation methods
Configuring the session establishment mode
Configuring the detection mode
Configuring a static BFD session
Configuring detection time settings
Configuring the authentication mode
Configuring the destination port number for multihop BFD control packets
Configuring the notification delay timer for session establishment failures
Associating the interface state with BFD
Configuring BFD
About BFD
Bidirectional forwarding detection (BFD) provides a general-purpose, standard, medium- and protocol-independent fast failure detection mechanism. It can detect and monitor the connectivity of forwarding paths to detect communication failures quickly so that measures can be taken to ensure service continuity and enhance network availability.
BFD can uniformly and quickly detect the failures of the bidirectional forwarding paths between two devices for upper-layer protocols such as routing protocols. The hello mechanism used by upper-layer protocols needs seconds to detect a link failure, while BFD can provide detection measured in milliseconds.
Mechanism
BFD establishes a session between two network devices to detect failures on the bidirectional forwarding paths between the devices and provide services for upper-layer protocols. BFD provides no neighbor discovery mechanism. Protocols that BFD services notify BFD of devices to which it needs to establish sessions. After a session is established, if no BFD control packet is received from the peer within the negotiated BFD interval, BFD notifies a failure to the protocol, which then takes appropriate measures.
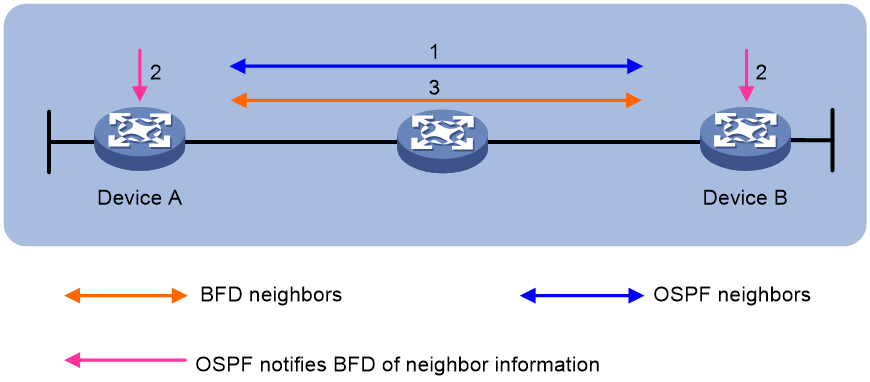
Figure 1 describes the operation of BFD for OSPF.
1. OSPF discovers neighbors by sending Hello packets and establishes neighbor relationships.
2. After establishing neighbor relationships, OSPF notifies BFD of the neighbor information, including destination and source addresses.
3. BFD uses the information to establish BFD sessions.
Figure 1 BFD session establishment
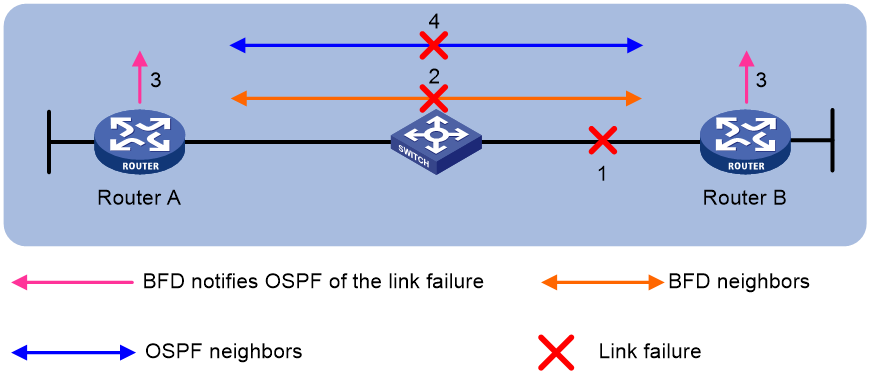
Figure 2 describes the BFD fault detection process.
1. BFD detects a link failure and tears down the session.
2. BFD notifies the neighbor unreachability to OSPF.
3. OSPF terminates the neighbor relationship on the link.
Single-hop detection and multihop detection
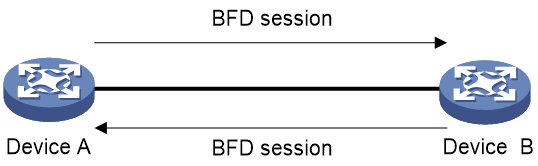
BFD can be used for single-hop and multihop detections.
· Single-hop detection—Detects the IP connectivity between two directly connected systems, for example, Device A and Device B as shown in Figure 3.
· Multihop detection—Detects any of the paths between two systems, for example, Device A and Device B as shown in Figure 4. These paths have multiple hops, and might overlap.
BFD session modes
BFD sessions use echo packets and control packets.
Echo packet mode
Echo packets are encapsulated into UDP packets. The packet contains destination port 3785, a destination IP address (transmitting interface's IP address), and a source IP address (transmitting interface's IP address).
The local end of the link sends echo packets to establish BFD sessions and monitor link status. The peer end does not establish BFD sessions and only forwards the packets back to the originating end. If the local end does not receive echo packets from the peer end within the detection time, it considers the session to be down.
BFD sessions in echo packet mode do not require both ends to support BFD. Upon receiving BFD echo packets, the peer end loops back the packets for detection purposes.
In echo packet mode, BFD supports only single-hop detection and the BFD session is independent of the operating mode.
Control packet mode
Control packets are encapsulated into UDP packets with port number 3784 for single-hop detection or port number 4784 for multihop detection.
The two ends of the link negotiate the establishment of BFD sessions by using the session parameters carried in control packets. Session parameters include session discriminators, desired minimum packet sending and receiving intervals, and local BFD session state.
Supported features
Table 1 shows the features supported by BFD.
Table 1 Features supported by BFD
|
Feature |
Reference |
|
IPv4 static routing |
Static routing in Layer 3—IP Routing Configuration Guide |
|
IPv6 static routing |
IPv6 static routing in Layer 3—IP Routing Configuration Guide |
|
RIP |
RIP in Layer 3—IP Routing Configuration Guide |
|
OSPF |
OSPF in Layer 3—IP Routing Configuration Guide |
|
OSPFv3 |
OSPFv3 in Layer 3—IP Routing Configuration Guide |
|
IS-IS |
IS-IS in Layer 3—IP Routing Configuration Guide |
|
BGP |
BGP in Layer 3—IP Routing Configuration Guide |
|
PIM |
PIM in IP Multicast Configuration Guide |
|
Track |
"Configuring Track" |
|
SDWAN |
SDWAN Configuration Guide |
Protocols and standards
· RFC 5880, Bidirectional Forwarding Detection (BFD)
· RFC 5881, Bidirectional Forwarding Detection (BFD) for IPv4 and IPv6 (Single Hop)
· RFC 5882, Generic Application of Bidirectional Forwarding Detection (BFD)
· RFC 5883, Bidirectional Forwarding Detection (BFD) for Multihop Paths
vSystem support for features
Non-default vSystems do not support the following features:
· Configuring the source IPv4 address for the BFD echo packets.
· Configuring the source IPv6 address for the BFD echo packets.
· Configuring the delay timer for BFD to notify upper-layer protocols of session establishment failures.
· Configuring the authentication mode for multihop BFD control packets.
· Configuring the destination port number for multihop BFD control packets.
· Configuring the multihop detection time multiplier in control packet mode and echo packet mode.
· Configuring the minimum interval for receiving multihop BFD echo packets.
· Configuring the minimum interval for receiving multihop BFD control packets.
· Configuring the minimum interval for sending multihop BFD control packets.
· Configuring the mode for establishing a BFD session.
· Configuring the BFD templates.
· Enabling SNMP notifications for BFD.
For information about vSystem support for a command, see the usage guidelines on that command in the command reference. For information about vSystem, see Virtual Technologies Configuration Guide.
Restrictions and guidelines: BFD configuration
· By default, the device runs BFD version 1 and is compatible with BFD version 0. You cannot change the BFD version to 0 through commands. When the peer device runs BFD version 0, the local device automatically switches to BFD version 0.
· After a BFD session is established, the two ends negotiate BFD parameters, including minimum sending interval, minimum receiving interval, initialization mode, and packet authentication, by exchanging negotiation packets. They use the negotiated parameters without affecting the session status.
BFD tasks at a glance
1. Configuring BFD sessions in echo packet mode
¡ Creating a static BFD session
¡ Configuring detection time settings
2. Configuring BFD sessions in control packet mode
¡ Configuring the session establishment mode
¡ Configuring the detection mode
¡ Configuring a static BFD session
¡ Configuring detection time settings
¡ Configuring the authentication mode
¡ Configuring the destination port number for multihop BFD control packets
¡ Configuring the notification delay timer for session establishment failures
¡ Associating the interface state with BFD
4. Enabling SNMP notifications for BFD
Configuring BFD sessions in echo packet mode
About this task
A static BFD session can be created manually by using the bfd static command or created dynamically when an application module collaborates with BFD.
Restrictions and guidelines
If you also configure uRPF on the device, follow these restrictions and guidelines:
· For the collaboration between an application module and a BFD session in echo packet mode, use an ACL for uRPF to permit echo packets from the peer device. Without the ACL configuration, uRPF will drop these echo packets.
· For a static BFD session, make sure the source IPv4/IPv6 address specified in the session can pass the uRPF check. If the source IPv4/IPv6 address cannot pass the check, uRPF will drop the echo packets from the peer device.
For more information about uRPF, see Security Configuration Guide.
Make sure the source IP address is not on the same network segment as any local interfaces. This avoids the following situations:
· A large number of ICMP redirect packets might be sent from the peer, resulting in link congestion.
· With malformed packet attack detection and prevention enabled, the local end might filter echo packets sent from the peer as malformed packets, resulting in BFD session establishment failure. For more information about malformed packet attack detection and prevention, see attack detection and prevention in Security Configuration Guide.
You cannot use BFD sessions in echo packet mode to detect paths over NAT.
Creating a static BFD session
About this task
A static BFD session in echo packet mode can be used to perform single-hop detection and multihop detection.
Restrictions and guidelines
You need to create a static BFD session in echo packet mode on only the local device to perform detection.
When creating a static BFD session, you must specify a peer IPv4 or IPv6 address. The system checks only the format of the IP address but not its correctness. If the peer IPv4 or IPv6 address is incorrect, the static BFD session cannot be established.
Different static BFD sessions cannot have the same local discriminator.
For a static BFD session in echo packet mode, the device selects the source IP address of echo packets as follows:
· As a best practice, specify the source IP address for echo packets when creating a static BFD session. If you do not specify the source IP address, the device uses the IP address specified in the bfd echo-source-ip or bfd echo-source-ipv6 command as the source IP address of echo packets.
· Without the source-ip/source-ipv6 or bfd echo-source-ip/bfd echo-source-ipv6 keyword specified, the device uses the IPv4 or IPv6 address specified for the destination-ip/destination-ipv6 keyword as the source IPv4 or IPv6 address of echo packets.
Creating a static BFD session for single-hop detection
1. Enter system view.
system-view
2. (Optional.) Configure the source IP address of echo packets.
¡ Configure the source IP address of echo packets.
bfd echo-source-ip ip-address
By default, no source IPv4 address is configured for echo packets.
¡ Configure the source IPv6 address of echo packets.
bfd echo-source-ipv6 ipv6-address
By default, no source IPv6 address is configured for echo packets.
The source IPv6 address of echo packets can only be a global unicast address.
3. Create a static BFD session and enter static BFD session view.
IPv4:
bfd static session-name [ peer-ip ipv4-address interface interface-type interface-number destination-ip ipv4-address [ source-ip ipv4-address ] one-arm-echo discriminator { local local-value | auto } ]
IPv6:
bfd static session-name [ peer-ipv6 ipv6-address interface interface-type interface-number destination-ipv6 ipv6-address [ source-ipv6 ipv6-address ] one-arm-echo discriminator { local local-value | auto } ]
Creating a static BFD session for multihop detection
1. Enter system view.
system-view
2. (Optional.) Configure the source IP address of echo packets.
¡ Configure the source IP address of echo packets.
bfd echo-source-ip ip-address
By default, no source IPv4 address is configured for echo packets.
¡ Configure the source IPv6 address of echo packets.
bfd echo-source-ipv6 ipv6-address
By default, no source IPv6 address is configured for echo packets.
The source IPv6 address of echo packets can only be a global unicast address.
3. Create a static BFD session and enter static BFD session view.
IPv4:
bfd static session-name [ peer-ip ipv4-address [ vpn-instance vpn-instance-name ] destination-ip ipv4-address [ source-ip ipv4-address ] one-arm-echo discriminator { local local-value | auto } ]
IPv6:
bfd static session-name [ peer-ipv6 ipv6-address [ vpn-instance vpn-instance-name ] destination-ipv6 ipv6-address [ source-ipv6 ipv6-address ] one-arm-echo discriminator { local local-value | auto } ]
Configuring detection time settings
About this task
When creating a BFD session in echo packet mode, you can configure the minimum interval for receiving BFD echo packets and the detection time multiplier for the device.
Configure detection time settings for single-hop BFD detection
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Set the minimum interval for receiving BFD echo packets.
bfd min-echo-receive-interval interval
The default setting varies by device model. For more information, see the command reference.
4. Set the detection time multiplier.
bfd detect-multiplier value
The default value varies by device model. For more information, see the command reference.
Configure detection time settings for multihop BFD detection
1. Enter system view.
system-view
2. Set the minimum interval for receiving BFD echo packets.
bfd multi-hop min-echo-receive-interval interval
The default setting varies by device model. For more information, see the command reference.
3. Set the detection time multiplier.
bfd multi-hop detect-multiplier value
The default value varies by device model. For more information, see the command reference.
Configuring BFD sessions in control packet mode
About BFD session creation methods
BFD sessions in control packet mode can be created statically or established dynamically.
BFD sessions are distinguished by the local discriminator and remote discriminator in control packets. The main difference between a statically created session and a dynamically established session is that they obtain the local discriminator and remote discriminator in different ways.
· The local discriminator and remote discriminator of a static BFD session are specified manually in the bfd static command or in features associated with BFD.
· The local discriminator of a dynamic BFD session is assigned by the device, and the remote discriminator is obtained during BFD session negotiation. A created session without manually specified local and remote discriminators is a dynamic BFD session.
Restrictions and guidelines
BFD version 0 does not support the following commands:
· bfd session init-mode.
· bfd authentication-mode.
· bfd demand enable.
· bfd echo enable.
Configuring the session establishment mode
About this task
BFD can use the following operating modes to establish a session:
· Active mode—BFD actively sends BFD control packets regardless of whether any BFD control packet is received from the peer.
· Passive mode—BFD does not send control packets until a BFD control packet is received from the peer.
At least one end must operate in active mode for a BFD session to be established.
Procedure
1. Enter system view.
system-view
2. Configure the BFD session establishment mode.
bfd session init-mode { active | passive }
By default, BFD uses the active mode to establish a session.
Configuring the detection mode
About this task
After a BFD session is established, the two ends can operate in the following modes:
· Asynchronous mode—The device periodically sends BFD control packets. The device considers that the session is down if it does not receive any BFD control packets within the detection interval.
· Demand mode—The Demand mode can be used to reduce the overhead when a large number of BFD sessions exist.
¡ If the peer end is operating in Asynchronous mode (default), the peer end stops sending BFD control packets after receiving control packets with the D bit set. In this scenario, BFD detects only the link between the local end and the peer end. The device considers that the session is down if it does not receive any BFD control packets within the detection interval.
¡ If both ends are operating in Demand mode, they stop sending BFD control packets. In this scenario, the system uses features other than BFD, such as Hello packets and hardware CC, to verify the connectivity to another system.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Specify the Demand mode for the BFD session.
bfd demand enable
By default, a BFD session is in Asynchronous mode.
Configuring a static BFD session
About this task
A static BFD session can be used for single-hop detection and multihop detection.
Restrictions and guidelines for static BFD session configuration
If a static BFD session is created on the remote end, the static BFD session must be created on the local end.
When creating a static BFD session, you must specify a peer IPv4 or IPv6 address. The system checks only the format of the IP address but not its correctness. If the peer IPv4 or IPv6 address is incorrect, the static BFD session cannot be established.
Different static BFD sessions cannot have the same local discriminator.
Creating a static BFD session for single-hop detection of network layer connectivity
1. Enter system view.
system-view
2. Create a static BFD session and enter static BFD session view.
IPv4:
bfd static session-name peer-ip ipv4-address interface interface-type interface-number source-ip ipv4-address discriminator local local-value remote remote-value
For a static BFD session to be established, specify the IPv4 address of the peer interface where the static BFD session resides for the peer-ip ipv4-address option. Specify the IPv4 address of the local interface where the static BFD session resides for the source-ip ipv4-address option.
IPv6:
bfd static session-name peer-ipv6 ipv6-address interface interface-type interface-number source-ipv6 ipv6-address discriminator local local-value remote remote-value
For a static BFD session to be established, specify the IPv6 address of the peer interface where the static BFD session resides for the peer-ipv6 ipv6-address option. Specify the IPv6 address of the local interface where the static BFD session resides for the source-ipv6 ipv6-address option.
Creating a static BFD session for single-hop detection of data link layer connectivity
1. Enter system view.
system-view
2. Create a static BFD session and enter static BFD session view.
bfd static session-name peer-ip default-ip interface interface-type interface-number source-ip ip-address discriminator local discr-value remote discr-value
For a static BFD session to be established, specify the IPv6 address of the local interface where the static BFD session resides for the source-ip ip-address option.
3. (Optional.) Associate the interface state with the static BFD session.
process-interface-status
By default, the state of a static BFD session does not affect the state of the data link layer of the interface.
4. (Optional.) Configure the timer that delays reporting the first static BFD session establishment failure to the data link layer.
first-fail-timer seconds
By default, the first static BFD session establishment failure is not reported to the data link layer.
This command takes effect only after you configure the process-interface-status command.
5. (Optional.) Enable special processing for the static BFD session.
special-processing [ admin-down | authentication-change | session-up ] *
By default, all types of special processing are disabled for a static BFD session.
Creating a static BFD session for multihop detection
1. Enter system view.
system-view
2. Create a static BFD session and enter static BFD session view.
IPv4:
bfd static session-name peer-ip ipv4-address [ vpn-instance vpn-instance-name ] source-ip ipv4-address discriminator local local-value remote remote-value
For a static BFD session to be established, specify the IPv4 address of the peer interface where the static BFD session resides for the peer-ip ipv4-address option. Specify the IPv4 address of the local interface where the static BFD session resides for the source-ip ipv4-address option.
IPv6:
bfd static session-name peer-ipv6 ipv6-address [ vpn-instance vpn-instance-name ] source-ipv6 ipv6-address discriminator local local-value remote remote-value
For a static BFD session to be established, specify the IPv6 address of the peer interface where the static BFD session resides for the peer-ipv6 ipv6-address option. Specify the IPv6 address of the local interface where the static BFD session resides for the source-ipv6 ipv6-address option.
Configuring detection time settings
About this task
When creating a BFD session in control packet mode, you can configure the minimum interval for receiving and transmitting BFD control packets and the detection time multiplier for the device.
Configure detection time settings for single-hop BFD detection
1. Enter system view.
system-view
2. Enter interface view or static BFD session view.
¡ Enter interface view.
interface interface-type interface-number
¡ Enter static BFD session view.
bfd static session-name
The static BFD session must already exist.
3. Set the minimum interval for transmitting single-hop BFD control packets.
bfd min-transmit-interval interval
The default setting varies by device model. For more information, see the command reference.
4. Set the minimum interval for receiving single-hop BFD control packets.
bfd min-receive-interval interval
The default setting varies by device model. For more information, see the command reference.
5. Set the single-hop detection time multiplier.
bfd detect-multiplier value
The default value varies by device model. For more information, see the command reference.
Configure detection time settings for multihop BFD detection
1. Enter system view.
system-view
2. Set the multihop detection time multiplier.
bfd multi-hop detect-multiplier value
The default value varies by device model. For more information, see the command reference.
3. Set the minimum interval for receiving multihop BFD control packets.
bfd multi-hop min-receive-interval interval
The default setting varies by device model. For more information, see the command reference.
4. Set the minimum interval for transmitting multihop BFD control packets.
bfd multi-hop min-transmit-interval interval
The default setting varies by device model. For more information, see the command reference.
Configuring the authentication mode
About this task
You can configure authentication settings, including algorithm and key, to enhance BFD session security.
Configure the authentication mode for a single-hop BFD session
1. Enter system view.
system-view
2. Enter interface view or static BFD session view.
¡ Enter interface view.
interface interface-type interface-number
¡ Enter static BFD session view.
bfd static session-name
The static BFD session must already exist.
To configure parameters for a static BFD session, you must enter its view.
3. Configure the authentication mode for single-hop control packets.
bfd authentication-mode { hmac-md5 | hmac-mmd5 | hmac-msha1 | hmac-sha1 | m-md5 | m-sha1 | md5 | sha1 | simple } key-id { cipher cipher-string | plain plain-string }
By default, no authentication mode is configured for single-hop control packets.
Configure the authentication mode for a multihop BFD session
1. Enter system view.
system-view
2. (Optional.) Enter static BFD session view.
bfd static session-name
The static BFD session must already exist.
To configure parameters for a static BFD session, you must enter its view.
3. Configure the authentication mode for multihop BFD control packets.
bfd multi-hop authentication-mode { hmac-md5 | hmac-mmd5 | hmac-msha1 | hmac-sha1 | m-md5 | m-sha1 | md5 | sha1 | simple } key-id { cipher cipher-string | plain plain-string }
By default, no authentication mode is configured for multihop BFD control packets.
Configuring the destination port number for multihop BFD control packets
About this task
IANA assigned port number 4784 to BFD for multihop BFD detection in control packet mode. By default, H3C devices use 4784 as the destination port number for multihop BFD control packets, while devices from other vendors might use 3784. To avoid BFD session establishment failures, make sure the devices on both ends of the BFD session use the same destination port number for multihop BFD control packets.
Restrictions and guidelines
This command applies to only new multihop BFD sessions in control packet mode.
Procedure
1. Enter system view.
system-view
2. Configure the destination port number for multihop BFD control packets.
bfd multi-hop destination-port port-number
The default setting is 4784.
Configuring the notification delay timer for session establishment failures
About this task
By default, BFD does not notify upper-layer protocols of session establishment failures. The notification is required in some scenarios. For example, upon a session establishment failure in an aggregate link, the aggregate link can place the associated member port in Unselected state based on the failure notification. You can configure the delay timer for BFD to notify upper-layer protocols of session establishment failures.
Restrictions and guidelines
This feature does not apply to BFD sessions in echo packet mode.
Procedure
1. Enter system view.
system-view
2. Set the delay timer for BFD to notify upper-layer protocols of session establishment failures.
bfd init-fail-timer seconds
By default, BFD does not notify upper-layer protocols of session establishment failures.
|
CAUTION: For session establishment failures caused by configuration mismatches at the two ends, this command can cause the upper-layer protocol to act incorrectly. Therefore, use this command with caution. BFD status mismatch and BFD authentication configuration mismatch are examples of configuration mismatches. |
Enabling the echo function
About this task
When you use Asynchronous mode BFD to detect the connectivity between directly connected devices, you can enable the echo function. This function enables the local system to periodically send echo packets to the remote system and reduces the control packet receiving rate to save bandwidth usage. The remote system loops back the echo packets to the local system without processing them. If the local system does not receive echo packets looped back from the remote system in a consecutive number of times, the local system declares the BFD session down.
This function is supported only for single-hop detection.
Restrictions and guidelines
This function does not take effect on BFD sessions associated with interface states.
Procedure
1. Enter system view.
system-view
2. Enter interface view or static BFD session view.
¡ Enter interface view.
interface interface-type interface-number
¡ Enter static BFD session view.
bfd static session-name
The static BFD session must be an existing session used to detect data link layer connectivity.
3. Enable the echo function.
bfd echo [ receive | send ] enable
By default, the echo function is disabled.
Associating the interface state with BFD
About this task
By creating a BFD session for single-hop detection through exchange of BFD control packets, this feature implements fast link detection. When BFD detects a link fault, it sets the link layer protocol state to DOWN(BFD). This behavior helps applications relying on the link layer protocol state achieve fast convergence. The source IP address of control packets is specified manually, and the destination IP address is fixed at 224.0.0.184. As a best practice, specify the IP address of the interface as the source IP address. If the interface does not have an IP address, specify a unicast IP address other than 0.0.0.0 as the source IP address.
You can associate the state of the following interfaces with BFD:
· Layer 3 Ethernet interfaces and subinterfaces. For BFD detection to take effect, do not configure this feature on both a Layer 3 Ethernet interface and its subinterface.
· Layer 3 aggregate interfaces, Layer 3 aggregate subinterfaces, and member ports (Layer 3 Ethernet interfaces only) in a Layer 3 aggregation group. For BFD detection to take effect, do not configure this feature on any two of the interface types at the same time.
· VLAN interfaces.
Restrictions and guidelines
The echo function does not take effect on BFD sessions associated with interface states.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Associate the interface state with BFD.
bfd detect-interface source-ip ip-address [ discriminator local local-value remote remote-value ] [ template template-name ]
By default, the interface state is not associated with BFD. BFD does not set the link layer protocol of the interface to DOWN(BFD) state when detecting a failure.
4. (Optional.) Configure the timer that delays reporting the first BFD session establishment failure to the data link layer.
bfd detect-interface first-fail-timer seconds
By default, the first BFD session establishment failure is not reported to the data link layer.
5. (Optional.) Enable special processing for BFD sessions.
bfd detect-interface special-processing [ admin-down | authentication-change | session-up ] *
By default, all types of special processing are disabled for BFD sessions.
Configuring a BFD template
About this task
Perform this task to specify BFD parameters in a template for sessions without next hops. You can configure BFD parameters for LSPs and PWs through a BFD template.
Procedure
1. Enter system view.
system-view
2. Create a BFD template and enter BFD template view.
bfd template template-name
3. (Optional.) Configure the authentication mode for BFD control packets.
bfd authentication-mode { hmac-md5 | hmac-mmd5 | hmac-msha1 | hmac-sha1 | m-md5 | m-sha1 | md5 | sha1 | simple } key-id { cipher cipher-string | plain plain-string }
By default, no authentication is performed.
4. Set the detection time multiplier.
bfd detect-multiplier value
The default value varies by device model. For more information, see the command reference.
5. Set the minimum interval for receiving BFD echo packets.
bfd min-echo-receive-interval interval
The default setting varies by device model. For more information, see the command reference.
6. Set the minimum interval for receiving BFD control packets.
bfd min-receive-interval interval
The default setting varies by device model. For more information, see the command reference.
7. Set the minimum interval for transmitting BFD control packets.
bfd min-transmit-interval interval
The default setting varies by device model. For more information, see the command reference.
Enabling SNMP notifications for BFD
About this task
To report critical BFD events to an NMS, enable SNMP notifications for BFD. For BFD event notifications to be sent correctly, you must also configure SNMP as described in Network Management and Monitoring Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enable SNMP notifications for BFD.
snmp-agent trap enable bfd
By default, SNMP notifications are enabled for BFD.
Display and maintenance commands for BFD
Execute the display command in any view and the reset command in user view.
|
IMPORTANT: Non-default vSystems do not support some of the display and maintenance commands. For information about vSystem support for these commands, see High Availability Command Reference. |
|
Task |
Command |
|
Display BFD session information. |
display bfd session [ discriminator local local-value | static name session-name | verbose ] display bfd session [ [ dynamic ] [ control | echo ] [ ip ] [ state { down | admin-down | init | up } ] [ discriminator remote remote-value ] [ peer-ip ipv4-address [ vpn-instance vpn-instance-name ] ] [ verbose ] ] display bfd session [ [ dynamic ] [ control | echo ] [ ipv6 ] [ state { down | admin-down | init | up } ] [ discriminator remote remote-value ] [ peer-ipv6 ipv6-address [ vpn-instance vpn-instance-name ] ] [ verbose ] ] display bfd session [ [ dynamic ] [ control | echo ] [ state { down | admin-down | init | up } ] [ discriminator remote remote-value ] [ [ peer-ip ipv4-address [ vpn-instance vpn-instance-name ] ] | [ peer-ipv6 ipv6-address [ vpn-instance vpn-instance-name ] ] ] [ verbose ] ] display bfd session [ [ static ] [ ip ] [ state { down | admin-down | init | up } ] [ discriminator remote remote-value ] [ peer-ip ipv4-address [ vpn-instance vpn-instance-name ] ] [ verbose ] display bfd session [ [ static ] [ ipv6 ] [ state { down | admin-down | init | up } ] [ discriminator remote remote-value ] [ peer-ipv6 ipv6-address [ vpn-instance vpn-instance-name ] ] [ verbose ] |
|
Clear BFD session statistics. |
reset bfd session statistics |