- Table of Contents
-
- 18-Network Management and Monitoring Configuration Guide
- 00-Preface
- 01-Information center configuration
- 02-Flow log configuration
- 03-Fast log output configuration
- 04-NetStream configuration
- 05-Sampler configuration
- 06-Mirroring configuration
- 07-Packet capture configuration
- 08-NQA configuration
- 09-Track configuration
- 10-BFD configuration
- 11-Error code detection configuration
- 12-Monitor Link configuration
- 13-Smart Link configuration
- 14-Interface backup configuration
- 15-Interface collaboration configuration
- 16-System maintenance and debugging configuration
- 17-NTP configuration
- 18-EAA configuration
- 19-Process monitoring and maintenance configuration
- 20-gRPC configuration
- 21-NETCONF configuration
- 22-CWMP configuration
- 23-SNMP configuration
- 24-RMON configuration
- 25-Event MIB configuration
- 26-GOLD configuration
- 27-Process placement configuration
- 28-Cloud connection configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 01-Information center configuration | 361.21 KB |
Configuring the information center
Default output rules for diagnostic logs
Default output rules for security logs
Default output rules for hidden logs
Default output rules for trace logs
Log formats and field descriptions
Information center tasks at a glance
Enabling the information center
Outputting logs to various destinations
Outputting logs to the console
Outputting logs to the monitor terminal
Outputting logs to the log buffer
Setting the minimum storage period
About setting the minimum storage period
Setting the minimum storage period for logs in a module-specific log buffer or log file
Setting the minimum storage period for logs in the general log buffer and log file
Enabling synchronous information output
Configuring the character set encoding used on the information center
Enabling duplicate log suppression
Configuring log suppression for a module
Disabling an interface from generating link up or link down logs
Limiting output of security logs
Enabling SNMP notifications for system logs
Saving security logs to the security log file
Managing the security log file
Backing up log files to a remote server
Performing integrity check for a log file
Saving diagnostic logs to the diagnostic log file
Setting the maximum size of the trace log file
Display and maintenance commands for information center
Configuring the information center
About the information center
The information center on the device receives logs generated by source modules and outputs logs to different destinations according to log output rules. Based on the logs, you can monitor device performance and troubleshoot network problems.
Figure 1 Information center diagram
Log types
Logs are classified into the following types:
· Standard system logs—Record common system information. Unless otherwise specified, the term "logs" in this document refers to standard system logs.
· Diagnostic logs—Record debugging messages.
· Security logs—Record security information, such as authentication and authorization information.
· Hidden logs—Record log information not displayed on the terminal, such as input commands.
· Trace logs—Record system tracing and debugging messages, which can be viewed only after the devkit package is installed.
Log levels
Logs are classified into eight severity levels from 0 through 7 in descending order. The information center outputs logs with a severity level that is higher than or equal to the specified level. For example, if you specify a severity level of 6 (informational), logs that have a severity level from 0 to 6 are output.
|
Severity value |
Level |
Description |
|
0 |
Emergency |
The system is unusable. For example, the system authorization has expired. |
|
1 |
Alert |
Action must be taken immediately. For example, traffic on an interface exceeds the upper limit. |
|
2 |
Critical |
Critical condition. For example, the device temperature exceeds the upper limit, the power module fails, or the fan tray fails. |
|
3 |
Error |
Error condition. For example, the link state changes. |
|
4 |
Warning |
Warning condition. For example, an interface is disconnected, or the memory resources are used up. |
|
5 |
Notification |
Normal but significant condition. For example, a terminal logs in to the device, or the device reboots. |
|
6 |
Informational |
Informational message. For example, a command or a ping operation is executed. |
|
7 |
Debugging |
Debugging message. |
Log destinations
The system outputs logs to the following destinations: console, monitor terminal, log buffer, log host, and log file. Log output destinations are independent and you can configure them after enabling the information center. One log can be sent to multiple destinations.
Default output rules for logs
A log output rule specifies the source modules and severity level of logs that can be output to a destination. Logs matching the output rule are output to the destination. The default vSystem logs can be output to the console, monitor terminal, log hosts, log buffer, and log file, while the non-default vSystem logs can be output to the monitor terminal, log hosts, and log buffer. Table 2 shows the default log output rules.
|
Destination |
Log source modules |
Output switch |
Severity |
|
Console |
All supported modules |
Enabled |
Debugging |
|
Monitor terminal |
All supported modules |
Disabled |
Debugging |
|
Log host |
All supported modules |
Enabled |
Informational |
|
Log buffer |
All supported modules |
Enabled |
Informational |
|
Log file |
All supported modules |
Enabled |
Informational |
Default output rules for diagnostic logs
Diagnostic logs can only be output to the diagnostic log file, and cannot be filtered by source modules and severity levels. Table 3 shows the default output rule for diagnostic logs.
Table 3 Default output rule for diagnostic logs
|
Destination |
Log source modules |
Output switch |
Severity |
|
Diagnostic log file |
All supported modules |
Enabled |
Debugging |
Default output rules for security logs
Security logs can only be output to the security log file, and cannot be filtered by source modules and severity levels. Table 4 shows the default output rule for security logs.
Table 4 Default output rule for security logs
|
Destination |
Log source modules |
Output switch |
Severity |
|
Security log file |
All supported modules |
Disabled |
Debugging |
Default output rules for hidden logs
Hidden logs can be output to the log host, the log buffer, and the log file. Table 5 shows the default output rules for hidden logs.
Table 5 Default output rules for hidden logs
|
Destination |
Log source modules |
Output switch |
Severity |
|
Log host |
All supported modules |
Enabled |
Informational |
|
Log buffer |
All supported modules |
Enabled |
Informational |
|
Log file |
All supported modules |
Enabled |
Informational |
Default output rules for trace logs
Trace logs can only be output to the trace log file, and cannot be filtered by source modules and severity levels. Table 6 shows the default output rules for trace logs.
Table 6 Default output rules for trace logs
|
Destination |
Log source modules |
Output switch |
Severity |
|
Trace log file |
All supported modules |
Enabled |
Debugging |
Log formats and field descriptions
Log formats
The format of logs varies by output destinations. The following table shows the original format of log information, which might be different from what you see. The actual format varies by the log resolution tool used.
Table 7 Log formats
|
Output destination |
Format |
|
Console, monitor terminal, log buffer, or log file |
Example: |
|
Log host |
Non-customized format: Example: CMCC format: Example: RFC 5424 format: Example: SGCC format: Example: Unicom format: Example: |
Log field description
Table 8 Log field description
|
Field |
Description |
|
Prefix (information type) |
A log sent to the console, monitor terminal, log buffer, or log file has an identifier in front of the timestamp: · An identifier of percent sign (%) indicates a log with a level equal to or higher than informational. · An identifier of asterisk (*) indicates a debugging log or a trace log. · An identifier of caret (^) indicates a diagnostic log. |
|
PRI (priority) |
A log destined for the log host has a priority identifier in front of the timestamp. The priority is calculated by using this formula: facility*8+level, where: · facility is the facility name. Facility names local0 through local7 correspond to values 16 through 23. The facility name can be configured using the info-center loghost command. It is used to identify log sources on the log host, and to query and filter the logs from specific log sources. · level is in the range of 0 to 7. See Table 1 for more information about severity levels. |
|
Timestamp |
Records the time when the log was generated. Logs sent to the log host and those sent to the other destinations have different timestamp precisions, and their timestamp formats are configured with different commands. For more information, see Table 9 and Table 10. |
|
appcode |
Specifies the code of the module that generated the log. This field exists only in logs that are sent to the log host in DamDDoS format. |
|
vendor |
Vendor of the device that generated the log. This field exists only in logs that are sent to the log host in DamDDoS format. |
|
Hostip |
Source IP address of the log. If the info-center loghost source command is configured, this field displays the IP address of the specified source interface. Otherwise, this field displays the sysname. This field exists only in logs that are sent to the log host in unicom format. |
|
sn/Serial number |
Serial number of the master device that generated the log. To view the serial number of the master device, see the DEVICE_SERIAL_NUMBER field in the output of the display device manuinfo command. The Serial number field is displayed in logs that are sent to the log host in SGCC format only when you configure the info-center loghost locate-info with-sn command. The Serial number field is always displayed in logs that are sent to the log host in Unicom format no matter whether you configure the info-center loghost locate-info with-sn command. |
|
Sysname (host name or host IP address) |
The sysname is the host name or IP address of the device that generated the log. You can use the sysname command to modify the name of the device. |
|
%% (vendor ID) |
Indicates that the information was generated by an H3C device. This field exists only in logs sent to the log host. |
|
vv (version information) |
Identifies the version of the log, and has a value of 10. This field exists only in logs that are sent to the log host. |
|
Module |
Specifies the name of the module that generated the log. You can enter the info-center source ? command in system view to view the module list. |
|
Level |
Identifies the level of the log. See Table 1 for more information about severity levels. |
|
Mnemonic |
Describes the content of the log. It contains a string of up to 32 characters. |
|
Location |
Optional field that identifies the log sender. This field exists only in logs that are sent to the log host in non-customized or CMCC format. The field contains the following information: · vSys—Number of the non-default vSystem. · Devlp—IP address of the log sender. This field is available only when you configure the info-center loghost source command. · Slot—Member ID of the IRF member device that sent the log. · SN—Serial number of the master device that generated the log. To
view the serial number of the master device, see the DEVICE_SERIAL_NUMBER
field in the output of the display device manuinfo command. |
|
SysLoc |
Optional field that identifies the system information of the logs. This field exists only in logs that are sent to the log host in RFC 5424 format. The field contains the following information: · SysLoc@—Vendor number of the device that generates logs. · VendorID—Vendor ID. Currently, the fixed value is 10. · Level—Log level. · Slot—Member ID of the IRF member device that sent the log. · SN—Serial number of the master device that generated the log. To
view the serial number of the master device, see the DEVICE_SERIAL_NUMBER
field in the output of the display device manuinfo command. |
|
AppLoc |
Optional field that identifies the module information of the logs. This field exists only in logs that are sent to the log host in RFC 5424 format. The field contains the following information: · AppLoc@—Vendor number of the device that generates logs. · Line—User line used by the current user for login. · IPAddr—IP address used for user login. · User—Username for login. |
|
Devtype |
Device type. This field exists only in logs that are sent to the log host in SGCC format. |
|
Content |
Provides the content of the log. This field is displayed as follows: · For most logs, this field is displayed as one or multiple sentences. For example, VTY logged in from 192.168.1.21.. · For logs used to record the values of
different parameters, this field is displayed in the format of key information 1; key information 2; … key information n..
Each key information is in the format of keyword(keyword ID)=value or keyword(keyword ID)=(description ID)description. This field is displayed as follows: · For most logs not in DamDDoS format, this field is displayed as one or multiple sentences. For example, VTY logged in from 192.168.1.21.. · For logs used to record the values of
different parameters, this field is displayed in the format of key information 1; key information 2; … key information n..
Each key information is in the format of keyword(keyword ID)=value or keyword(keyword ID)=(description ID)description. |
Table 9 Timestamp precisions and configuration commands
|
Item |
Destined for the log host |
Destined for the console, monitor terminal, log buffer, and log file |
|
Precision |
Seconds |
Milliseconds |
|
Command used to set the timestamp format |
info-center timestamp loghost |
info-center timestamp |
Table 10 Description of the timestamp parameters
|
Timestamp parameters |
Description |
|
boot |
Time that has elapsed since system startup, in the format of xxx.yyy. xxx represents the higher 32 bits, and yyy represents the lower 32 bits, of milliseconds elapsed. Logs that are sent to all destinations other than a log host support this parameter. Example: 0.109391473 is a timestamp in the boot format. |
|
date |
Current date and time. · For logs output to a log host, the timestamp can be in the format of mmm dd hh:mm:ss yyyy (accurate to seconds) or mmm dd hh:mm:ss.ms yyyy (accurate to milliseconds). · For logs output to other destinations, the timestamp is in the format of MMM DD hh:mm:ss:ms YYYY. All logs support this parameter. Example: May 30 05:36:29:579 2018 is a timestamp in the date format in logs sent to the console. |
|
iso |
Timestamp format stipulated in ISO 8601, accurate to seconds (default) or milliseconds. Only logs that are sent to a log host support this parameter. Example: 2018-05-30T06:42:44 is a timestamp in the iso format accurate to seconds. A timestamp accurate to milliseconds is like 2018-05-30T06:42:44.708. |
|
none |
No timestamp is included. All logs support this parameter. Example: No timestamp is included. |
|
no-year-date |
Current date and time without year information, in the format of MMM DD hh:mm:ss:ms. Only logs that are sent to a log host support this parameter. Example: May 30 06:44:22 is a timestamp in the no-year-date format. |
vSystem support for features
Non-default vSystems support the following features:
· Outputting logs to the monitor terminal.
· Outputting logs to log hosts.
· Outputting logs to the log buffer.
For information about the support of non-default vSystems for the commands, see information center command reference. For information about vSystem, see Virtual Technologies Configuration Guide.
Information center tasks at a glance
Managing standard system logs
1. Enabling the information center
2. Outputting logs to various destinations
Choose the following tasks as needed:
¡ Outputting logs to the console
¡ Outputting logs to the monitor terminal
¡ Outputting logs to log hosts
¡ Outputting logs to the log buffer
3. (Optional.) Setting the minimum storage period
4. (Optional.) Enabling synchronous information output
5. (Optional.) Configuring the character set encoding
6. (Optional.) Configuring log suppression
Choose the following tasks as needed:
¡ Enabling duplicate log suppression
¡ Configuring log suppression for a module
¡ Disabling an interface from generating link up or link down logs
¡ Limiting output of security logs
7. (Optional.) Enabling SNMP notifications for system logs
8. (Optional.) Backing up log files to a remote server
9. (Optional.) Performing integrity check for a log file
Managing hidden logs
1. Enabling the information center
2. Outputting logs to various destinations
Choose the following tasks as needed:
¡ Outputting logs to log hosts
¡ Outputting logs to the log buffer
3. (Optional.) Setting the minimum storage period
4. (Optional.) Enabling duplicate log suppression
Managing security logs
1. Enabling the information center
2. (Optional.) Enabling duplicate log suppression
¡ Saving security logs to the security log file
¡ Managing the security log file
4. (Optional.) Backing up log files to a remote server
5. (Optional.) Performing integrity check for a log file
Managing diagnostic logs
1. Enabling the information center
2. (Optional.) Enabling duplicate log suppression
3. Saving diagnostic logs to the diagnostic log file
Managing trace logs
1. Enabling the information center
2. (Optional.) Enabling duplicate log suppression
3. Setting the maximum size of the trace log file
Enabling the information center
About this task
The information center can output logs only after it is enabled.
Procedure
1. Enter system view.
system-view
2. Enable the information center.
info-center enable
The information center is enabled by default.
Outputting logs to various destinations
Outputting logs to the console
Restrictions and guidelines
The terminal monitor, terminal debugging, and terminal logging commands take effect only for the current connection between the terminal and the device. If a new connection is established, the default is restored.
Procedure
1. Enter system view.
system-view
2. Configure an output rule for sending logs to the console.
info-center source { module-name | default } console { deny | level severity }
For information about default output rules, see "Default output rules for logs."
3. (Optional.) Configure the timestamp format.
info-center timestamp { boot | date | none }
The default timestamp format is date.
4. Return to user view.
quit
5. Enable log output to the console.
terminal monitor
By default, log output to the console is enabled.
6. Enable output of debugging messages to the console.
terminal debugging
By default, output of debugging messages to the console is disabled.
This command enables output of debugging-level log messages to the console.
7. Set the lowest severity level of logs that can be output to the console.
terminal logging level severity
The default setting is 6 (informational).
Outputting logs to the monitor terminal
About this task
Monitor terminals refer to terminals that log in to the device through the VTY line.
Restrictions and guidelines
The terminal monitor, terminal debugging, and terminal logging commands take effect only for the current connection between the terminal and the device. If a new connection is established, the default is restored.
Procedure
1. Enter system view.
system-view
2. Configure an output rule for sending logs to the monitor terminal.
info-center source { module-name | default } monitor { deny | level severity }
For information about default output rules, see "Default output rules for logs."
3. (Optional.) Configure the timestamp format.
info-center timestamp { boot | date | none }
The default timestamp format is date.
4. Return to user view.
quit
5. Enable log output to the monitor terminal.
terminal monitor
By default, log output to the monitor terminal is disabled.
6. Enable output of debugging messages to the monitor terminal.
terminal debugging
By default, output of debugging messages to the monitor terminal is disabled.
This command enables output of debugging-level log messages to the monitor terminal.
7. Set the lowest level of logs that can be output to the monitor terminal.
terminal logging level severity
The default setting is 6 (informational).
Outputting logs to log hosts
About this task
You can specify log hosts for the default vSystem and non-default vSystems, thus the default vSystem logs and non-default vSystem logs can be output to their respective log hosts. After configuring log hosts for the default vSystem, you can execute the info-center loghost vsys-to-admin enable command to enable outputting the logs of non-default vSystems to the logs hosts specified on the default vSystem. Thus, you do not need to log in to each non-default vSystem to specify the log hosts.
Restrictions and guidelines
The device supports the following methods (in descending order of priority) for outputting logs of a module to designated log hosts:
· Fast log output.
For information about the modules that support fast log output and how to configure fast log output, see "Configuring fast log output."
· Flow log.
For information about the modules that support flow log output and how to configure flow log output, see "Configuring flow log."
· Information center.
If you configure multiple log output methods for a module, only the method with the highest priority takes effect.
Procedure
1. Enter system view.
system-view
2. Configure a log output filter or a log output rule. Choose one option as needed:
¡ Configure a log output filter.
info-center filter filter-name { module-name | default } { deny | level severity }
By default, no log output filters exist.
You can create multiple log output filters. When specifying a log host, you can apply a log output filter to the log host to control log output.
¡ Configure a log output rule for the log host output destination.
info-center source { module-name | default } loghost { deny | level severity }
For information about default output rules, see "Default output rules for logs."
The system chooses the settings to control log output to a log host in the following order:
a. Log output filter applied to the log host.
b. Log output rules configured for the log host output destination by using the info-center source command.
c. Default log output rules (see "Default output rules for logs").
3. (Optional.) Specify a source IP address for output logs.
info-center loghost source interface-type interface-number
By default, the source IP address of output logs is the primary IP address of their outgoing interfaces.
4. (Optional.) Specify the format in which logs are output to log hosts.
info-center format { cmcc | rfc5424 | sgcc | unicom }
By default, logs are output to log hosts in non-customized format.
Support for the sgcc keyword depends on device model. For more information, see the command reference.
5. (Optional.) Add the device serial number to the location field of logs sent to log hosts.
info-center loghost locate-info with-sn
By default, the device does not add the device serial number to the location field of logs sent to log hosts.
6. (Optional.) Configure the timestamp format.
info-center timestamp loghost { date [ with-milliseconds ] | iso [ with-milliseconds ] | no-year-date | none }
The default timestamp format is date.
7. Specify a log host and configure related parameters.
Default vSystem:
info-center loghost [ vpn-instance vpn-instance-name ] { hostname | ipv4-address | ipv6 ipv6-address } [ facility local-number | filter filter-name | format { cmcc | default | rfc5424 | sgcc | unicom } | port port-number | source-ip source-ip-address | tcp [ ssl-client-policy policy-name ] ] *
Non-default vSystem:
info-center loghost { ipv4-address | ipv6 ipv6-address } [ port port-number | tcp [ ssl-client-policy policy-name ] ] *
By default, no log hosts or related parameters are specified.
The value for the port-number argument must be the same as the value configured on the log host. Otherwise, the log host cannot receive logs.
The format specified by the info-center loghost command takes precedence over the format specified by the info-center format command. The source IP address specified by the info-center loghost command takes precedence over the source IP address specified by the info-center loghost source command.
To use an SSL client policy to encrypt the logs sent to a log host, configure the SSL client policy first. If you have not configured the SSL client policy, the SSL connection cannot be established and logs cannot be sent to the log host. For more information about SSL client policy configuration, see SSL VPN configuration in Security Configuration Guide.
8. (Optional.) Enable outputting the logs of non-default vSystems to log hosts specified on the default vSystem.
info-center loghost vsys-to-admin enable
By default, the non-default vSystem logs will not be output to the log hosts specified on the default vSystem.
Outputting logs to the log buffer
About this task
This feature enables log output to log buffers based on the log source modules. Log buffers include the following types:
· Separate module-specific log buffers—Logs generated by modules that have separate log buffers are saved to their respective log buffers.
For example, session logs and attack defense logs are saved to the session log buffer and the attack defense log buffer, respectively. With separate buffers, you can manage and view the module-specific logs and general logs conveniently.
The modules that have separate log buffers are determined by factory settings. To view the names of supported modules, use the display logbuffer module ? command. You can use the display logbuffer module module-name command to view buffered logs of the specified module.
· General log buffer—Logs generated by the system and the modules other than the modules that have separate log buffers are saved to the general log buffer.
You can use the display logbuffer command without the module keyword to view buffered logs in the general log buffer.
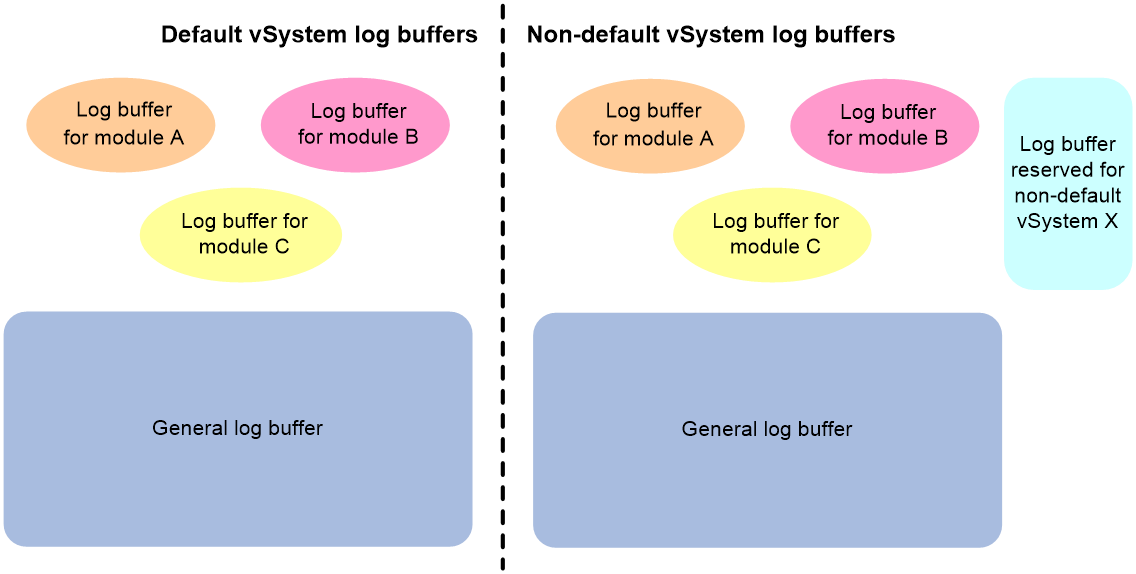
The saving of vSystem logs varies by vSystem log type.
· Default vSystem logs are saved in default vSystem log buffers, which include the default vSystem module-specific log buffers and the default vSystem general log buffer.
· Non-default vSystem logs are saved in non-default vSystem log buffers, which include the non-default vSystem module-specific log buffers and the non-default vSystem general log buffer. By default, for the same module, all non-default vSystems share and preempt the resources of the non-default log buffer for that module; all non-default vSystems share and preempt the resources of the non-default vSystem general log buffer.
You can use the info-center logbuffer reserved-size command to reserve a log buffer size for a non-default vSystem. The log buffer resources reserved for a non-default vSystem cannot be used by other vSystems. The reserved log buffer resources do not occupy the general log buffer resources of non-default vSystems. A non-default vSystem that has reserved log buffer resources will first use the reserved resources, and then use the non-default vSystem general log buffer when its reserved resources are insufficient.
Figure 2 Default vSystem log buffers and non-default vSystem log buffers
About this task
This feature enables log output to log buffers based on the log source modules. Log buffers include the following types:
· Separate module-specific or submodule-specific log buffers—Logs generated by modules and submodules that have separate log buffers are saved to their respective log buffers.
For example, session logs and attack defense logs are saved to the session log buffer and the attack defense log buffer, respectively. With separate buffers, you can manage and view the module-specific or submodule-specific logs and general logs conveniently.
The modules and submodules that have separate log buffers are determined by factory settings. To view the names of supported modules, use the display logbuffer module ? command. To view the names of supported submodules, use the display logbuffer module module-name submodule ? command. You can use the display logbuffer module module-name command to view buffered logs of the specified module. You can use the display logbuffer module module-name submodule submodule-name command to view buffered logs of the specified submodule.
· General log buffer—Logs generated by the system and the modules or submodules other than the modules or submodules that have separate log buffers are saved to the general log buffer.
You can use the display logbuffer command without the module keyword to view buffered logs in the general log buffer.
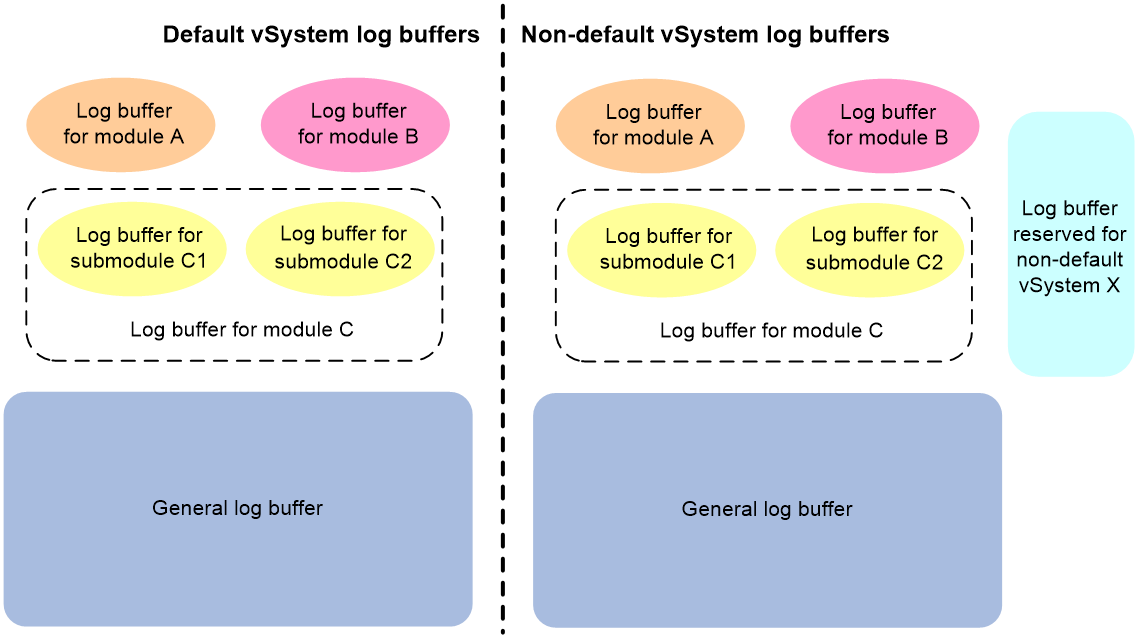
The saving of vSystem logs varies by vSystem log type.
· Default vSystem logs are saved in default vSystem log buffers, which include the default vSystem module-specific or submodule-specific log buffers and the default vSystem general log buffer.
· Non-default vSystem logs are saved in non-default vSystem log buffers, which include the non-default vSystem module-specific or submodule-specific log buffers and the non-default vSystem general log buffer. By default, for the same module, all non-default vSystems share and preempt the resources of the non-default log buffer for that module; all non-default vSystems share and preempt the resources of the non-default vSystem general log buffer.
You can use the info-center logbuffer reserved-size command to reserve a log buffer size for a non-default vSystem. The log buffer resources reserved for a non-default vSystem cannot be used by other vSystems. The reserved log buffer resources do not occupy the general log buffer resources of non-default vSystems. A non-default vSystem that has reserved log buffer resources will first use the reserved resources, and then use the non-default vSystem general log buffer when its reserved resources are insufficient.
Figure 3 Default vSystem log buffers and non-default vSystem log buffers
Procedure
1. Enter system view.
system-view
2. (Optional.) Configure an output rule for sending logs to the log buffer.
info-center source { module-name | default } logbuffer { deny | level severity }
For information about the default output rules, see "Default output rules for logs."
3. (Optional.) Configure the timestamp format.
info-center timestamp { boot | date | none }
The default timestamp format is date.
4. Enable log output to the log buffer.
info-center logbuffer
By default, log output to the log buffer is enabled.
5. (Optional.) Set the maximum size of the log buffer for a module.
info-center logbuffer module module-name size buffersize
By default, a maximum of 512 logs can be buffered.
This command takes effect on only default vSystem modules that have separate log buffers.
6. (Optional.) Set the maximum size of the general log buffer.
info-center logbuffer size buffersize
By default, a maximum of 512 logs can be buffered.
This command takes effect on only the default vSystem general log buffer.
7. (Optional.) Specify the log buffer size reserved for non-default vSystems.
a. Enter vSystem view.
vsys vsys-name [ id vsys-id ]
b. Specify the log buffer size reserved for the current non-default vSystem.
info-center logbuffer reserved-size reserved-size-value
By default, all non-default vSystems share and preempt the non-default vSystem log buffer resources.
Saving logs to the log file
About this task
The log file feature enables log output to log files based on the log source modules. Log files include the following types:
· Separate module-specific log files—Logs generated by modules that have separate log files are output to their respective log files.
For example, session logs and attack defense logs are output to the session log file and the attack defense log file, respectively. With separate log files, you can manage and view the module-specific logs and general logs conveniently.
The modules that have separate log files are determined by factory settings. To view the names of supported modules, use the info-center logfile module ? command. You can use the more command in user view to view logs in a module-specified log file.
· General log file—Logs generated by the system and the modules other than the modules that have separate log files are output to the general log file.
The system saves logs from the log file buffer to the log file. After saving logs to the log file, the system clears the log file buffer.
Log saving from the log file buffer to the log file is triggered by the following situations:
· Periodic saving.
· A manual immediate saving of buffered logs to the log file.
· The log file buffer is full.
A log file is automatically created when needed and has a maximum capacity. The log file capacity restrictions are as follows:
· When log file overwrite-protection is enabled and no log file space is available, the device stops saving new logs.
· When log file overwrite-protection is disabled and no log file space or storage device space is available, the system will replace the oldest logs with new logs.
· When log file overwrite-protection is disabled and no log file space or storage device space is available:
¡ For modules that use separate log files, the system replaces the oldest logs with new logs.
¡ For modules that use general log files, the system creates new log files as needed. The log files are named as logfile1.log, logfile2.log, and so on.
When logfile1.log is full, the system compresses logfile1.log as logfile1.log.gz and creates a new log file named logfile2.log. The process repeats until the last log file is full.
After the last log file is full, the device repeats the following process:
i The device locates the oldest compressed log file logfileX.log.gz and creates a new file using the same name (logfileX.log).
ii When logfileX.log is full, the device compresses the log file as logfileX.log.gz to replace the existing file logfileX.log.gz.
|
TIP: · Clean up the storage space of the device regularly to ensure sufficient storage space for the log file feature. · As a best practice, back up the log files regularly to avoid loss of important logs. |
Configuring a module-specific log file
1. Enter system view.
system-view
2. (Optional.) Configure an output rule for sending logs to the log file.
info-center source { module-name | default } logfile { deny | level severity }
For information about the default output rules, see "Default output rules for logs."
3. Enable the log file feature.
info-center logfile enable
By default, the log file feature is enabled.
This command takes effect on both module-specific log files and the general log file.
4. (Optional.) Set the maximum log file size.
info-center logfile module module-name size-quota size
The maximum log file size for the general log file and module-specific log file is 10 MB and 1 MB, respectively.
5. (Optional.) Set the alarm threshold for log file usage of the module.
info-center logfile module module-name alarm-threshold usage
The default alarm threshold for log file usage ratio is 80%. When the usage ratio of the log file reaches 80%, the system outputs a message to inform the user.
Setting the alarm threshold value to 0 disables the log file usage alarm feature for the module.
6. (Optional.) Specify the log file directory.
info-center logfile directory dir-name
By default, the log file is saved in the logfile directory under the root directory of the storage device.
This command takes effect on both module-specific log files and the general log file.
This command cannot survive an IRF reboot or a master/subordinate switchover.
7. Save logs in the log file buffer to the log file. Choose one or both options as needed:
¡ Configure the automatic log file saving interval.
info-center logfile frequency freq-sec
The default log file saving interval is 86400 seconds.
This command takes effect on both module-specific log files and the general log file.
¡ Immediately save logs from the log file buffer to the log file.
logfile save
This command is available in any view.
This command takes effect on both module-specific log files and the general log file.
Configuring the general log file
1. Enter system view.
system-view
2. (Optional.) Configure an output rule for sending logs to the log file.
info-center source { module-name | default } logfile { deny | level severity }
For information about the default output rules, see "Default output rules for logs."
3. Enable the log file feature.
info-center logfile enable
By default, the log file feature is enabled.
This command takes effect on both module-specific log files and the general log file.
4. (Optional.) Set the maximum log file size.
info-center logfile size-quota size
The maximum log file size for the general log file is 10 MB.
5. (Optional.) Specify the log file directory.
info-center logfile directory dir-name
By default, the log file is saved in the logfile directory under the root directory of the storage device.
This command takes effect on both module-specific log files and the general log file.
This command cannot survive an IRF reboot or a master/subordinate switchover.
6. Save logs in the log file buffer to the log file. Choose one or both options as needed:
¡ Configure the automatic log file saving interval.
info-center logfile frequency freq-sec
The default log file saving interval is 86400 seconds.
This command takes effect on both module-specific log files and the general log file.
¡ Immediately save logs from the log file buffer to the log file.
logfile save
This command is available in any view.
This command takes effect on both module-specific log files and the general log file.
Setting the minimum storage period
About setting the minimum storage period
Use this feature to set the minimum storage period for logs in log buffers and log files. This feature ensures that logs will not be overwritten by new logs during a set period of time.
Logs of the modules that have separate log buffers and log files are output to their respective log buffers or log files. Logs of other modules and the system logs are output to the general log buffer or log file. By default, when a log buffer or log file is full, new logs will automatically overwrite the oldest logs. After the minimum storage period is set, the system identifies the storage period of a log to determine whether to delete the log. The system current time minus a log's generation time is the log's storage period.
· If the storage period of a log is shorter than or equal to the minimum storage period, the system does not delete the log. The new log will not be saved.
· If the storage period of a log is longer than the minimum storage period, the system deletes the log to save the new log.
Setting the minimum storage period for logs in a module-specific log buffer or log file
1. Enter system view.
system-view
2. Set the minimum storage period for logs stored in the log buffer or log file of a module.
info-center syslog module module-name min-age min-age
By default, the log minimum storage period is not set.
Setting the minimum storage period for logs in the general log buffer and log file
1. Enter system view.
system-view
2. Set the minimum storage period for logs stored in the general log buffer and log file.
info-center syslog min-age min-age
By default, the log minimum storage period is not set.
Enabling synchronous information output
About this task
System log output interrupts ongoing configuration operations, obscuring previously entered commands. Synchronous information output shows the obscured commands. It also provides a command prompt in command editing mode, or a [Y/N] string in interaction mode so you can continue your operation from where you were stopped.
Procedure
1. Enter system view.
system-view
2. Enable synchronous information output.
info-center synchronous
By default, synchronous information output is disabled.
Configuring the character set encoding used on the information center
About this task
The information center supports outputting log messages by using the GB18030 or UTF-8 encoding. By default, the GB18030 encoding is used.
For the login terminal to correctly display Chinese characters in log messages received from the information center, the information center and the terminal must use the same character set encoding.
Procedure
1. Enter system view.
system-view
2. Enable the information center to use the UTF-8 encoding.
info-center syslog utf-8 enable
By default, the information center uses the GB18030 encoding for outputting log messages.
Configuring log suppression
Enabling duplicate log suppression
About this task
The information center on the device outputs logs generated by service modules. The device identifies logs that have the same module name, level, mnemonic, location, and text as duplicate logs.
In some scenarios, for example, ARP attack or link failure, the service modules will generate a large volume of duplicate logs during a short period of time. Recording and output of consecutive duplicate logs wastes system and network resources. To resolve this issue, you can enable duplicate log suppression.
With this feature enabled, when a service module generates a log, the information center outputs the log and starts the duplicate log suppression timer. The suppression period of the duplicate log suppression timer varies by phase. The suppression periods in phase 1, 2, and later phases are 30 seconds, 2 minutes, and 10 minutes, respectively.
After you enable duplicate log suppression, the system starts suppression upon outputting a log:
· If only duplicate logs of the log are received during the suppression period of a phase, the information center does not output the duplicate logs. When the suppression period of the phase expires, the information center outputs the suppressed log and the number of times the log is suppressed, and starts the next suppression phase.
· If a different log is received during the suppression period of any phase, the information center performs the following operations:
¡ Stops suppression on the log, and outputs the suppressed log and the number of times the log is suppressed.
¡ Outputs the different log and starts phase-1 suppression for that log.
· If no log is received within the suppression period of any phase, the information center deletes the duplicate log suppression timer, stops suppression on the log, and does not output any log.
Procedure
1. Enter system view.
system-view
2. Enable duplicate log suppression.
info-center logging suppress duplicates
By default, duplicate log suppression is disabled.
Examples
The following example uses SHELL_CMD logs to verify the duplicate log suppression feature. After the user executes a command on the device, the information center receives a SHELL_CMD log generated by the shell module, encapsulates the log, and then outputs the log to the log buffer.
1. Verify the suppression effect in phases 1, 2, 3, and 4 of a log (with suppression period of 30 seconds, 2 minutes, 10 minutes, and 10 minutes):
# In a lab environment, continuously execute the display logbuffer command for 25 minutes.
# View the output logs in the log buffer.
<Sysname> display logbuffer
Log buffer: Enabled
Max buffer size: 1024
Actual buffer size: 512
Dropped messages: 0
Overwritten messages: 0
Current messages: 5
%Jul 20 13:01:20:615 2022 Sysname SHELL/6/SHELL_CMD: -Line=con0-IPAddr=**-User=**; Command is display logbuffer
%Jul 20 13:01:50:718 2022 Sysname SHELL/6/SHELL_CMD: -Line=con0-IPAddr=**-User=**; Command is display logbuffer This message repeated 2 times in last 30 seconds.
%Jul 20 13:03:50:732 2022 Sysname SHELL/6/SHELL_CMD: -Line=con0-IPAddr=**-User=**; Command is display logbuffer This message repeated 5 times in last 2 minutes.
%Jul 20 13:13:50:830 2022 Sysname SHELL/6/SHELL_CMD: -Line=con0-IPAddr=**-User=**; Command is display logbuffer This message repeated 10 times in last 10 minutes.
%Jul 20 13:23:50:211 2022 Sysname SHELL/6/SHELL_CMD: -Line=con0-IPAddr=**-User=**; Command is display logbuffer This message repeated 6 times in last 10 minutes.
The output shows the following information:
¡ The information center received the log SHELL/6/SHELL_CMD: -Line=con0-IPAddr=**-User=**; Command is display logbuffer.
¡ In phase 1, the log was suppressed twice by the information center.
¡ In phase 2, the log was suppressed five times by the information center.
¡ In phase 3, the log was suppressed 10 times by the information center.
¡ In phase 4, the log was suppressed six times by the information center.
2. Continue to verify how duplicate log suppression works when a different log is received during the suppression period of a log:
# Execute the display logbuffer command three times, and then execute the display interface brief command.
# View the output logs in the log buffer.
<Sysname> display logbuffer
Log buffer: Enabled
Max buffer size: 1024
Actual buffer size: 512
Dropped messages: 0
Overwritten messages: 0
Current messages: 5
%Jul 20 13:01:20:615 2022 Sysname SHELL/6/SHELL_CMD: -Line=con0-IPAddr=**-User=**; Command is display logbuffer
%Jul 20 13:01:50:718 2022 Sysname SHELL/6/SHELL_CMD: -Line=con0-IPAddr=**-User=**; Command is display logbuffer This message repeated 2 times in last 30 seconds.
%Jul 20 13:03:50:732 2022 Sysname SHELL/6/SHELL_CMD: -Line=con0-IPAddr=**-User=**; Command is display logbuffer This message repeated 5 times in last 2 minutes.
%Jul 20 13:13:50:830 2022 Sysname SHELL/6/SHELL_CMD: -Line=con0-IPAddr=**-User=**; Command is display logbuffer This message repeated 10 times in last 10 minutes.
%Jul 20 13:23:50:211 2022 Sysname SHELL/6/SHELL_CMD: -Line=con0-IPAddr=**-User=**; Command is display logbuffer This message repeated 6 times in last 10 minutes.
%Jul 20 13:24:56:205 2022 Sysname SHELL/6/SHELL_CMD: -Line=con0-IPAddr=**-User=**; Command is display logbuffer This message repeated 3 times in last 1 minute 6 seconds.
%Jul 20 13:25:41:205 2022 Sysname SHELL/6/SHELL_CMD: -Line=con0-IPAddr=**-User=**; Command is display interface brief.
<Sysname>
The output shows the following information:
¡ The information center stopped suppression for the log SHELL/6/SHELL_CMD: -Line=con0-IPAddr=**-User=**; Command is display logbuffer.
¡ The information center output the log SHELL/6/SHELL_CMD: -Line=con0-IPAddr=**-User=**; Command is display interface brief, and started suppression for it.
Configuring log suppression for a module
About this task
This feature suppresses output of logs. You can use this feature to filter out the logs that you are not concerned with.
Perform this task to configure a log suppression rule to suppress output of all logs or logs with a specific mnemonic value for a module.
Procedure
1. Enter system view.
system-view
2. Configure a log suppression rule for a module.
info-center logging suppress module module-name mnemonic { all | mnemonic-value }
By default, the device does not suppress output of any logs from any modules.
Disabling an interface from generating link up or link down logs
About this task
By default, an interface generates link up or link down log information when the interface state changes. In some cases, you might want to disable certain interfaces from generating this information. For example:
· You are concerned about the states of only some interfaces. In this case, you can use this function to disable other interfaces from generating link up and link down log information.
· An interface is unstable and continuously outputs log information. In this case, you can disable the interface from generating link up and link down log information.
Use the default setting in normal cases to avoid affecting interface status monitoring.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Disable the interface from generating link up or link down logs.
undo enable log updown
By default, an interface generates link up and link down logs when the interface state changes.
Limiting output of security logs
About this task
When the device processes the following security services, a large number of security logs will be generated and sent to the information center, which will cause overload of the information center:
· AFT.
· ASPF.
· Data filtering.
· File filtering.
· URL filtering.
· NAT.
· Session management.
· Anti-virus.
· Application audit and management.
· IPS.
· NetShare Control.
· Server connection detection.
· Attack detection and prevention.
This feature allows you to set the maximum number of security logs that can be sent per second to the information center. With this feature configured, the device will discard the subsequent security logs when the number of security logs sent to the information center per second reaches the maximum value allowed. Set an appropriate maximum value according to your network condition.
Procedure
1. Enter system view.
system-view
2. Set the maximum number of security logs that can be sent per second.
security syslog rate-limit max-value
By default, the device can send a maximum of 1000 security logs per second to the information center.
Enabling SNMP notifications for system logs
About this task
This feature enables the device to send an SNMP notification for each log message it outputs. The device encapsulates the logs in SNMP notifications and then sends them to the SNMP module and the log trap buffer.
You can configure the SNMP module to send received SNMP notifications in SNMP traps or informs to remote hosts. For more information, see "Configuring SNMP."
To view the traps in the log trap buffer, access the MIB corresponding to the log trap buffer.
Procedure
1. Enter system view.
system-view
2. Enable SNMP notifications for system logs.
snmp-agent trap enable syslog
By default, the device does not send SNMP notifications for system logs.
3. Set the maximum number of traps that can be stored in the log trap buffer.
info-center syslog trap buffersize buffersize
By default, the log trap buffer can store a maximum of 1024 traps.
Managing security logs
Saving security logs to the security log file
About this task
Security logs are very important for locating and troubleshooting network problems. Generally, security logs are output together with other logs. It is difficult to identify security logs among all logs.
To solve this problem, you can save security logs to the security log file without affecting the current log output rules.
After you enable the security log file feature, the system processes security logs as follows:
1. Outputs security logs to the security log file buffer.
2. Saves logs from the security log file buffer to the security log file at the specified interval.
If you have the security-audit role, you can also manually save security logs to the security log file.
3. Clears the security log file buffer immediately after the security logs are saved to the security log file.
Restrictions and guidelines
The device supports only one security log file. The system will overwrite old logs with new logs when the security log file is full. To avoid security log loss, you can set an alarm threshold for the security log file usage ratio. When the alarm threshold is reached, the system outputs a message to inform you of the alarm. You can log in to the device with the security-audit user role and back up the security log file to prevent the loss of important data.
Procedure
1. Enter system view.
system-view
2. Enable the security log file feature.
info-center security-logfile enable
By default, the security log file feature is disabled.
3. Set the interval at which the system saves security logs.
info-center security-logfile frequency freq-sec
The default security log file saving interval is 86400 seconds.
4. (Optional.) Set the maximum size for the security log file.
info-center security-logfile size-quota size
By default, the maximum security log file size is 10 MB.
5. (Optional.) Set the alarm threshold of the security log file usage.
info-center security-logfile alarm-threshold usage
By default, the alarm threshold of the security log file usage ratio is 80. When the usage of the security log file reaches 80%, the system will send a message.
Managing the security log file
Restrictions and guidelines
To use the security log file management commands, you must have the security-audit user role. For information about configuring the security-audit user role, see AAA in Security Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Change the directory of the security log file.
info-center security-logfile directory dir-name
By default, the security log file is saved in the seclog directory in the root directory of the storage device.
This command cannot survive an IRF reboot or a master/subordinate switchover.
3. Manually save all logs in the security log file buffer to the security log file.
security-logfile save
This command is available in any view.
4. (Optional.) Display the summary of the security log file.
display security-logfile summary
This command is available in any view.
Backing up log files to a remote server
About this task
You can use this feature to back up the following log files to a remote server through FTP, TFTP, or SCP so as to enhance the log file security:
· General log files under the directory specified by the info-center logfile directory command. Module-specific log files will not be backed up.
· Security log files under the directory specified by the info-center security-logfile directory command.
The device supports only one general log file and one security log file. It automatically backs up the general or security log file to the remote server every time logs are written into the log file.
The device supports multiple general log files and one security log file. The backup mechanism is as follows:
· When a general log file is full, the device automatically backs up the log file to the remote server.
· Every time logs are written into the security log file, the device automatically backs up the log file to the remote server.
Procedure
1. Enter system view.
system-view
2. Specify the username and password for logging in to the remote server to back up log files.
info-center file-server user user-name password { cipher | simple } password
By default, the username and password for logging in to the remote server to back up log files are not specified.
If you execute this command multiple times, the most recent configuration takes effect.
3. Back up log files to the remote server.
info-center file-server transport-type { ftp | scp | tftp } { ipv4-address | ipv6 ipv6-address } [ port port-number ] [ vpn-instance vpn-instance-name ] [ directory directory ] filename-prefix filename-prefix [ file-type { logfile | security-logfile } ]
By default, the device does not back up log files to a remote server.
If you execute this command multiple times, the most recent configuration takes effect.
Performing integrity check for a log file
About this task
When the information center saves a log message to the log file, it uses the default device master key to calculate a digest for the log file and saves the digest in the log file. The digest is used to perform integrity check for the log file.
When this feature is configured, the information center uses the master key to recalculate a digest for the log file and then compares the digest with that saved in the log file. If the two digests are consistent, the log file passes the integrity check. If they do not match, the log file fails the integrity check.
About this task
When the information center saves a log message to the log file, it uses the device master key to calculate a digest for the log file and saves the digest in the log file. The digest is used to perform integrity check for the log file. You can use the default device master key or a master key configured by using the set master-key command. For more information about the master key, see public key management in Security Configuration Guide.
When this feature is configured, the information center uses the master key to recalculate a digest for the log file and then compares the digest with that saved in the log file. If the two digests are consistent, the log file passes the integrity check. If they do not match, the log file fails the integrity check.
Restrictions and guidelines
Currently, only standard system log files and security log files support integrity check, while diagnostic log files and trace log files do not support integrity check.
Procedure
To perform integrity check for a log file, execute the following command in user view:
check logfile file-path
For successful execution of this command, the file extension must be .log or .log.gz.
Saving diagnostic logs to the diagnostic log file
About this task
By default, the diagnostic log file feature saves diagnostic logs from the diagnostic log file buffer to the diagnostic log file at the specified saving interval. You can also manually trigger an immediate saving of diagnostic logs to the diagnostic log file. After saving diagnostic logs to the diagnostic log file, the system clears the diagnostic log file buffer.
The device supports only one diagnostic log file. The diagnostic log file has a maximum capacity. When the capacity is reached, the system replaces the oldest diagnostic logs with new logs.
Procedure
1. Enter system view.
system-view
2. Enable the diagnostic log file feature.
info-center diagnostic-logfile enable
By default, the diagnostic log file feature is enabled.
3. (Optional.) Set the maximum diagnostic log file size.
info-center diagnostic-logfile quota size
By default, the maximum diagnostic log file size is 10 MB.
4. (Optional.) Specify the diagnostic log file directory.
info-center diagnostic-logfile directory dir-name
By default, the diagnostic log file is saved in the diagfile folder under the root directory of the default file system.
This command cannot survive an IRF reboot or a master/subordinate switchover.
5. Save diagnostic logs in the diagnostic log file buffer to the diagnostic log file. Choose one option as needed:
¡ Configure the automatic diagnostic log file saving interval.
info-center diagnostic-logfile frequency freq-sec
The default diagnostic log file saving interval is 86400 seconds.
¡ Manually save diagnostic logs to the diagnostic log file.
diagnostic-logfile save
This command is available in any view.
Setting the maximum size of the trace log file
About this task
The device has only one trace log file. When the trace log file is full, the device overwrites the oldest trace logs with new ones.
Procedure
1. Enter system view.
system-view
2. Set the maximum size for the trace log file.
info-center trace-logfile quota size
The default maximum trace log file size is 1 MB.
Display and maintenance commands for information center
|
IMPORTANT: Non-default vSystems do not support some of the display and maintenance commands. For information about vSystem support for these commands, see information center command reference. |
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display the character set encoding used on the device or the login terminal. |
display character-set [ terminal ] |
|
Display the diagnostic log file configuration. |
display diagnostic-logfile summary |
|
Display the information center configuration. |
display info-center |
|
Display information about log output filters. |
display info-center filter [ filtername ] |
|
Display the log output rules by source modules. |
display info-center source [ module module-name ] |
|
Display log buffer information and buffered logs. Non-default vSystems do not support the vsys keyword. |
display logbuffer [ vsys vsys-name ] [ module module-name [ submodule submodule-name ] ] [ reverse ] [ level severity | size buffersize | slot slot-number ] * [ last-mins mins ] |
|
Display the log buffer summary. |
display logbuffer summary [ level severity | slot slot-number ] * |
|
Display the log file configuration. |
display logfile summary |
|
Display summary information of the security log file (security-audit user role required). |
display security-logfile summary |
|
Clear the log buffer. |
reset logbuffer [ module module-name [ submodule submodule-name ] ] |