- Table of Contents
-
- 04-Policies
- 01-Security policy
- 02-Security policy redundancy analysis
- 03-Security policy hit analysis
- 04-Security policy optimization
- 05-Policy-based NAT
- 06-Interface NAT
- 07-AFT
- 08-QoS
- 09-Bandwidth management
- 10-Application audit
- 11-Application proxy
- 12-IP reputation
- 13-Domain reputation
- 14-Blacklist
- 15-Connection limit
- 16-Server connection detection
- 17-Access rate limit
- 18-DLP
- 19-Server load balancing
- 20-Outbound link load balancing
- 21-Inbound link load balancing
- 22-Transparent DNS proxy
- 23-NetShare control
- 24-Zero trust policy
- 25-Trusted application proxies
- 26-Trusted API proxies
- 27-NAT66
- 28-uRPF
- 29-Load balancing common configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 18-DLP | 93.05 KB |
DLP
This help contains the following topics:
¡ Configure global configuration
¡ Configure resource management
Introduction
DLP policies
A DLP policy defines one or more signatures to identify illegal data transmission and defines defensive actions, for example, output alarm logs, and send alarm emails.
A DLP policy contains the following rules:
· Detection rules—Used to match keywords, file names, and other contents in the transmitted data.
· Identity rules—Used to match the IP addresses, email addresses, and other identity attributes of the senders.
· Response rules—Used to take preventive measures for data that matches detection rules and identity rules.
Restrictions and guidelines
Deleting a resource in the resource management page might cause the cascade deletion as follows:
· Deleting a regular expression will also delete all match conditions of detection rules that use the selected regular expression and might delete a DLP policy if no match conditions of detection rules exist in the DLP policy.
· Deleting an email server will also delete all actions that apply to the selected email server and might delete a response rule if no actions exist in the response rule.
· Deleting a file server simultaneously deletes all actions that apply to the selected file server and might delete a response rule if no actions exist in the response rule.
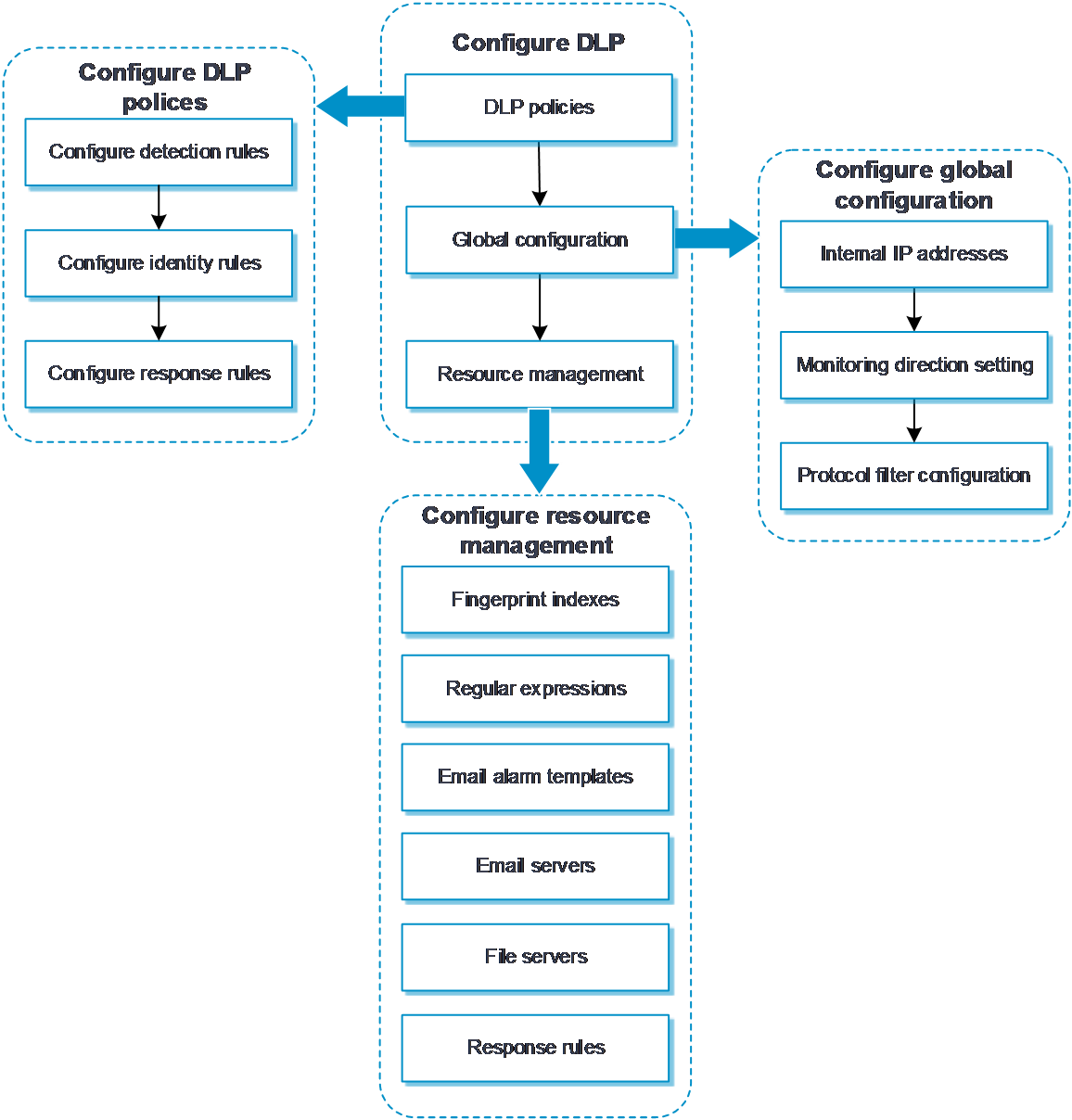
Configure DLP
Configure DLP as shown in Figure 1.
Figure 1 DLP configuration procedure
Configure a DLP policy
Configure a DLP policy, and then configure detection rules, identity rules, and response rules in the policy according to actual network security requirements.
Procedure
1. Click the Policies tab.
2. In the navigation pane, select DLP > DLP policies.
3. Click Create.
4. Configure parameters for the DLP policy.
Table 1 DLP policy configuration items
|
Item |
Description |
|
Policy name |
Enter the name of the DLP policy. The name is case sensitive and valid characters include Chinese characters, letters, digits, underscores (_), and hyphens (-). |
|
Description |
Enter a description for the DLP policy. |
|
Scan mode |
Select a scan mode: · Fast scan. · Complete scan. |
|
Start policy |
Select whether to start the DLP policy. |
5. Click the Detection rules tab.
a. Click Create in the Add rule area to create a detection rule.
b. Click Create in the Exceptional rules area to create an exceptional rule.
If the data matches an exceptional rule, the data does not match any detection rule. You can configure multiple detection rules and exceptional rules in a DLP policy.
Table 2 Detection rule configuration items
|
Item |
Description |
|
Name |
Enter the name of a detection rule. The name is case sensitive and valid characters include Chinese characters, letters, digits, underscores (_), and hyphens (-). |
|
Severity level |
Select the severity level of an event matching the detection rule: · High. · Medium. · Low. · Informational. |
6. Click Create in the Match condition area.
7. Configure the match condition parameters.
Table 3 Match condition configuration items
|
Item |
Description |
|
Match type |
Select a match type for the detection rule: · Regular expression. · Keyword. · Fingerprint file. · File name. · File size. · File type. · Protocol. |
|
Occurrence count method |
Select an occurrence count method: · Count the number of matched regular expression—Select this method when the match type is set to Regular expression. · Check existence—Select this method when the match type is set to keyword. · Count the total number of matches—Select this method when the match type is set to fingerprint file. This field is available only when the match type is set to Regular expression, keyword, or fingerprint file. |
|
Counting scope |
Select a counting scope: · Single file. · All file. This field is available only when the match type is set to Regular expression or keyword. |
|
Regular expression |
Enter a regular expression. This field is available only when the match type is set to Regular expression. |
|
Case sensitive |
Select whether the keyword for matching is case sensitive. This field is available only when the match type is set to keyword. |
|
Keyword |
Select a criterion for keyword matching: · Match keywords—A true keyword match. · Match neighbor keywords—A fuzzy keyword match. You can configure left neighbor keyword, right neighbor keyword, and maximum distance. This field is available only when the match type is set to keyword. |
|
Match whole word only |
Select whether to match whole word only. This field is available only when the match type is set to keyword. This field takes effect only for English keywords. |
|
Fingerprint file |
Select a fingerprint file for matching. This field is available only when the match type is set to Fingerprint file. |
|
Threshold |
Enter a matching threshold with the sample file contents. This field is available only when the match type is set to Fingerprint file. |
|
File type |
Select a file type for matching. This field is available only when the match type is set to File type. |
|
File name |
Enter a file name. This field is available only when the match type is set to File name. |
|
Maximum |
Enter the maximum file size. This field is available only when the match type is set to File size. If both the maximum file size and the minimum file size are set to 0, the file size is not limited. |
|
Minimum |
Enter the minimum file size. This field is available only when the match type is set to File size. If both the maximum file size and the minimum file size are set to 0, the file size is not limited. |
|
Protocol |
Select a protocol for matching. This field is available only when the match type is set to Protocol. |
8. Click OK.
9. Click the Identity Rules tab.
a. Click Create in the Add rule area to create an identity rule.
b. Click Create in the Exceptional rules area to create an exceptional rule.
If the data matches an exceptional rule, the data does not match any identity rule. You can configure multiple identity rules and exceptional rules in a DLP policy.
Table 4 Identity rule configuration items
|
Item |
Description |
|
Name |
Enter the name of an identity rule. The name is case sensitive and valid characters include Chinese characters, letters, digits, underscores (_), and hyphens (-). |
|
Severity level |
Select the severity level of an event matching the identity rule: · High. · Medium. · Low. · Informational. |
10. Click Create in the Match condition area.
11. Configure the match condition parameters.
Table 5 Match condition configuration items
|
Item |
Description |
|
Match type |
Select a match type for the identity rule: · Sender/user. · Recipient/user. |
|
Email addresses |
Enter email addresses for matching. |
|
Recipient type |
Select a recipient type: · Match all address—All destination email addresses match the entered email addresses. · Match any address—Only a specific number of destination email addresses match the entered email addresses. This field is available only when the match type is set to Recipient/user. |
|
Threshold |
Enter a matching threshold with the email addresses. This field is available only when the recipient type is set to Match any address. |
|
IP version |
Select an IP version: · IPv4. · IPv6. |
|
IP addresses |
Enter IP addresses for matching. |
|
User |
Select or enter users for matching. |
|
Host names |
Enter host names for matching. This field is available only when the match type is set to Recipient/user. |
12. Click OK.
13. Click the Response Rules tab.
Create or select a response rule. You can configure multiple response rules for a DLP policy.
14. Click OK.
Configure global configuration
The global configuration applies to all DLP policies.
Procedure
1. Click the Policies tab.
2. In the navigation pane, select DLP > Global Configuration.
3. On the Internal IP addresses tab, configure the IPv4 address object groups and IPv6 address object groups.
4. Click Apply.
5. Click the Monitoring Direction Setting tab.
6. Configure the monitoring direction parameters.
Table 6 Monitoring direction configuration items
|
Item |
Description |
|
Monitoring direction |
Select a monitoring direction: · Bidirection—The DLP module monitors the packets sent to the internal network from the external network or packets sent to the external network from the internal network. · External to internal—The DLP module monitors the packets sent to the internal network from the external network. · Internal to external—The DLP module monitors the packets sent to the external network from the internal network. · No monitoring—The DLP module does not monitor packets. |
7. Click Apply.
8. Click the Protocol filter configuration tab and select protocols to be monitored by the DLP module.
9. Click Apply.
Configure resource management
Configure fingerprint indexes
1. Click the Policies tab.
2. In the navigation pane, select DLP > Resource Management.
3. On the Fingerprint Indexes tab, click Create.
4. Configure the fingerprint file resource parameters.
Table 7 Fingerprint file resource configuration items
|
Item |
Description |
|
Name |
Enter the name of the fingerprint file resource. |
|
Fingerprint file |
Import a fingerprint file. |
5. Click OK, and then you can view the newly created fingerprint file resource on the Fingerprint Indexes tab.
Configure regular expressions
1. Click the Policies tab.
2. In the navigation pane, select DLP > Resource Management.
3. On the Regular Expressions tab, click Create.
4. Configure the regular expression parameters.
Table 8 Regular expression configuration items
|
Item |
Description |
|
Name |
Enter the name of the regular expression. |
|
Regular expression |
Enter a regular expression. |
5. Click OK, and then you can view the newly created regular expression on the Regular Expressions tab.
Configure email alarm templates
1. Click the Policies tab.
2. In the navigation pane, select DLP > Resource Management.
3. On the Email Alarm Templates tab, click Create.
4. Configure the email alarm template parameters.
Table 9 Email alarm template configuration items
|
Item |
Description |
|
Name |
Enter the name of the email alarm template. |
|
Email server |
Enter an email server for sending emails. |
|
Recipients |
Enter the recipient email addresses. |
|
Cc recipients |
Enter the recipient email addresses for carbon copy. |
|
Bcc recipients |
Enter the recipient email addresses for blind carbon copy. |
|
Theme |
Enter the theme of alarm emails. |
|
Body |
Enter the contents of alarm emails. |
5. Click OK, and then you can view the newly created email alarm template on the Email Alarm Templates tab.
Configure email servers
1. Click the Policies tab.
2. In the navigation pane, select DLP > Resource Management.
3. On the Email Servers tab, click Create.
4. Configure the email server parameters.
Table 10 Email server configuration items
|
Item |
Description |
|
Name |
Enter the name of the email server. |
|
Server address |
Enter the IP address or host name of the email server. |
|
Encrypted |
Select whether to encrypt the interaction with the email server. |
|
Authenticated |
Select whether authentication is required for accessing the email server. |
|
Username |
Enter the username for accessing the email server. |
|
Password |
Enter the password for accessing the email server. |
|
Sender |
Enter the email address of the email server for sending emails. |
5. Click OK, and then you can view the newly created email server on the Email Servers tab.
Configure file servers
1. Click the Policies tab.
2. In the navigation pane, select DLP > Resource Management.
3. On the File Servers tab, click Create.
4. Configure the file server parameters.
Table 11 File server configuration items
|
Item |
Description |
|
Name |
Enter the name of the file server. |
|
Type |
Select a file server type: · Local. · FTP. |
|
Path |
Enter a file storage path, for example, ftp://1.1.1.1/abc/. This field is available only when the file server type is FTP. |
|
Username |
Enter the username for accessing the FTP server. This field is available only when the file server type is FTP. |
|
Password |
Enter the password for accessing the FTP server. This field is available only when the file server type is FTP. |
5. Click OK, and then you can view the newly created file server on the File Servers tab.
Configure response rules
1. Click the Policies tab.
2. In the navigation pane, select DLP > Resource Management.
3. On the Response Rules tab, click Create.
4. Configure the response rule parameters.
Table 12 Response rule configuration items
|
Item |
Description |
|
Name |
Enter the name of the response rule. The name is case sensitive and valid characters include Chinese characters, letters, digits, underscores (_), and hyphens (-). |
|
Description |
Enter a description for the response rule. |
5. Click Create in the Match condition area. You can configure multiple match conditions in a response rule.
Table 13 Match condition configuration items
|
Item |
Description |
|
Match type |
Select a match type for the response rule: · Severity level. · Protocol. |
|
Operator type |
Select an operator type: · Belong to—Indicates that the match type belongs to the specified type value. · Not belong to—Indicates that the match type does not belong to the specified type value. |
|
Type value |
Select a type value. The type value varies by the selected match type. |
6. Click OK.
7. Click Create in the Action area. You can configure multiple actions in a response rule.
Table 14 Action configuration items
|
Item |
Description |
|
Action type |
Select an action type for the response rule: · Upload files. · Add comments. · Send logs. · Send emails. |
|
File server |
Select a file server name. This filed is available only when the action type is set to Upload files. |
|
Comments |
Enter the comments for suspicious data transmission. This filed is available only when the action type is set to Add comments. |
|
Email alarm template |
Select an email alarm template. This filed is available only when the action type is set to Send emails. |
8. Click OK.
9. Click OK, and then you can view the newly created response rule on the Response Rules tab.