- Table of Contents
-
- 04-Policies
- 01-Security policy
- 02-Security policy redundancy analysis
- 03-Security policy hit analysis
- 04-Security policy optimization
- 05-Policy-based NAT
- 06-Interface NAT
- 07-AFT
- 08-QoS
- 09-Bandwidth management
- 10-Application audit
- 11-Application proxy
- 12-IP reputation
- 13-Domain reputation
- 14-Blacklist
- 15-Connection limit
- 16-Server connection detection
- 17-Access rate limit
- 18-DLP
- 19-Server load balancing
- 20-Outbound link load balancing
- 21-Inbound link load balancing
- 22-Transparent DNS proxy
- 23-NetShare control
- 24-Zero trust policy
- 25-Trusted application proxies
- 26-Trusted API proxies
- 27-NAT66
- 28-uRPF
- 29-Load balancing common configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 17-Access rate limit | 87.42 KB |
Access rate limit
Introduction
This feature limits the number of connections established per second to prevent DDoS attacks from degrading device performance.
The device supports the following types of access rate limit:
· Public network protection—Limits the number of connections from the public network to the internal network based on destination IP address.
· Internal network protection—Limits the number of connections from the internal network to the public network based on source IP address.
Configure access rate limit
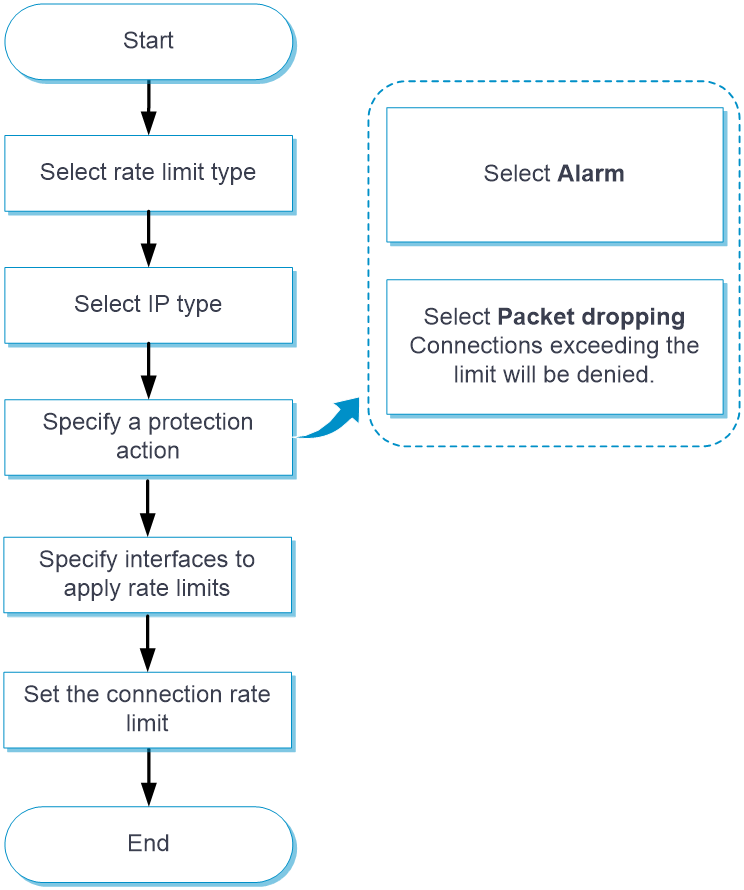
Configure access rate limit as shown in Figure 1.
Figure 1 Access rate limit configuration procedure