- Table of Contents
-
- 01-Fundamentals Configuration Guide
- 00-Preface
- 01-CLI configuration
- 02-RBAC configuration
- 03-Login management configuration
- 04-FTP and TFTP configuration
- 05-File system management configuration
- 06-Configuration file management configuration
- 07-Software upgrade configuration
- 08-Automatic configuration
- 09-Multichassis configuration sync configuration
- 10-GIR configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 07-Software upgrade configuration | 125.65 KB |
Contents
Digitally signed software images
Restrictions and guidelines: Software upgrade
Upgrading device software by using the boot loader method
Software upgrade tasks at a glance
Specifying startup images and completing the upgrade
Synchronizing startup images from the master device to subordinate devices
Installing or uninstalling features and patches
About installing or uninstalling features and patches
Installing or upgrading features
Uninstalling features or patches
Verifying and maintaining software images
Displaying software images and version information
Upgrading software
About software upgrade
Software upgrade enables you to upgrade a software version, add new features, and fix software bugs. This chapter describes software types and release forms, compares software upgrade methods, and provides the procedures for upgrading software from the CLI.
Software types
The following software types are available:
· BootWare image—Also called the Boot ROM image. This image contains a basic segment and an extended segment.
¡ The basic segment is the minimum code that bootstraps the system.
¡ The extended segment enables hardware initialization and provides system management menus. When the device cannot start up correctly, you can use the menus to load software and the startup configuration file or manage files.
Typically, the BootWare image is integrated into the Boot image to avoid software compatibility errors.
· Comware image—Includes the following image subcategories:
¡ Boot image—A .bin file that contains the Linux operating system kernel. It provides process management, memory management, and file system management.
¡ System image—A .bin file that contains the Comware kernel and standard features, including device management, interface management, configuration management, and routing.
¡ Feature image—A .bin file that contains advanced or customized software features. You can purchase feature images as needed.
¡ Patch image—A .bin file that is released for fixing bugs without rebooting the device. A patch image does not add or remove features.
Patch images have the following types: incremental and non-incremental.
- Incremental patch images—Multiple incremental patch images can coexist on the device at the same time. A new patch image can cover all, part, or none of the functions provided by an old patch image.
- Non-incremental patch images—Only one non-incremental patch image can exist on the device. The device uninstalls the old non-incremental patch image before installing a new non-incremental patch image. A new non-incremental patch image covers all functions provided by an old non-incremental patch image.
An incremental patch image and a non-incremental patch image can coexist on the device.
Comware images that have been loaded are called current software images. Comware images specified to load at the next startup are called startup software images.
BootWare image, boot image, and system image are required for the device to operate.
Software release forms
Software images are released in one of the following forms:
· Separate .bin files. You must verify compatibility between software images.
· As a whole in one .ipe package file. The images in an .ipe package file are compatible. The system decompresses the file automatically, loads the .bin images and sets them as startup software images.
|
|
NOTE: Software image file names use the model-comware version-image type-release format. This document uses boot.bin and system.bin as boot and system image file names. |
Upgrade methods
|
Upgrade method |
Software types |
Remarks |
|
Upgrading from the CLI by using the boot loader method |
· BootWare image · Comware images |
This method is disruptive. You must reboot the entire device to complete the upgrade. |
|
Upgrading from the BootWare menu |
· BootWare image · Comware images |
Use this method when the device cannot start up correctly. To use this method, first connect to the console port and power cycle the device. Then, press Ctrl+B at prompt to access the BootWare menu. For more information about upgrading software from the BootWare menu, see the release notes for the software version. Use this method only when you do not have any other choice. |
This chapter covers only upgrading software from the CLI by using the boot loader method.
Software image loading
Startup software images
To upgrade software, you must specify the upgrade files as the startup software images for the device to load at next startup. You can specify two lists of software images: one main and one backup. The device first loads the main startup software images. If the main startup software images are not available, the devices loads the backup startup software images.
Image loading process at startup
At startup, the device performs the following operations after loading and initializing BootWare:
1. Loads main images.
2. If any main image does not exist or is invalid, loads the backup images.
3. If any backup image does not exist or is invalid, the device cannot start up.
Application scenarios
Software upgrade
When the current software cannot meet the requirements of network operation or user services, you can upgrade the software to optimize device performance to meet the requirements.
Feature and patch package installation
To fix software defects without upgrading the software version, you can install patch packages compatible with the software version. To expand service features on the device, you can install the corresponding feature packages.
Digitally signed software images
The software images for the device are digitally signed for authenticity and integrity verification. This mechanism ensures that the software installed on the system is from a trusted source and has not been tampered with in the transfer, storage, or installation phase.
The system performs software digital signature verification for authenticity and integrity in the following situations:
· Before the system loads a software image during startup. If the digital signature verification fails, the system will not load the image and you will receive a digital signature verification failure message.
· When you specify a software image to upgrade the device from the BootWare menu. If the digital signature verification fails, the system will not set the image for upgrade and you will receive a digital signature verification failure message.
· Before the system loads a BootWare image to the Normal area of BootWare. If the digital signature verification fails, the system will not load the image and you will receive a digital signature verification failure message.
· When you specify a software image as a startup image through the boot loader. The system will verify the digital signature of the image before it updates the startup image list with the specified image. If the digital signature verification fails, the system will not update the startup image list and you will receive a digital signature verification failure message.
· Before the system activates a feature or patch image. If the digital signature verification fails, the system will not activate the image and you will receive a digital signature verification failure message.
Restrictions and guidelines: Software upgrade
Do not execute the install or boot-loader file command before the current upgrade action completes.
As a best practice, store the startup images in a fixed storage medium. If you store the startup images in a hot swappable storage medium, do not remove the hot swappable storage medium during the startup process.
Upgrading device software by using the boot loader method
Software upgrade tasks at a glance
To upgrade software, perform one of the following tasks:
1. Specifying startup images and completing the upgrade
2. (Optional.) Synchronizing startup images from the master device to subordinate devices
Prerequisites
1. Use the display version command to verify the current BootWare image version and startup software version.
2. Use the release notes for the upgrade software version to evaluate the upgrade impact on your network and verify the following items:
¡ Software and hardware compatibility.
¡ Version and size of the upgrade software.
¡ Compatibility of the upgrade software with the current BootWare image and startup software image.
3. Use the dir command to verify that each IRF member device has sufficient storage space for the upgrade images. If the storage space is not sufficient, delete unused files by using the delete /unreserved command. For more information, see "Managing file systems."
4. Use FTP or TFTP to transfer the upgrade image file to the root directory of a file system. For more information about FTP and TFTP, see "Configuring FTP" or "Configuring TFTP." For more information about file systems, see "Managing file systems."
Specifying startup images and completing the upgrade
Perform the following steps in user view:
1. Specify main or backup startup images for all member devices.
¡ Use an .ipe file:
boot-loader file ipe-filename [ patch filename&<1-30> ] { all | slot slot-number } { backup | main [ undecompressed ] }
¡ Use .bin files:
boot-loader file boot filename system filename [ feature filename&<1-30> ] [ patch filename&<1-30> ] { all | slot slot-number } { backup | main }
|
|
NOTE: The system will verify the digital signature of the specified images before it updates the startup image list with the specified images. If the digital signature verification fails, the system will not update the startup image list and you will receive a digital signature verification failure message. |
As a best practice in a multichassis IRF fabric, specify the all keyword for the command. If you use the slot slot-number option to upgrade member devices one by one, version inconsistencies occur among the member devices during the upgrade.
2. Save the running configuration.
save
This step ensures that any configuration you have made can survive a reboot.
3. Reboot the IRF fabric.
reboot
4. (Optional.) Verify the software image settings.
display boot-loader [ slot slot-number ]
Verify that the current software images are the same as the startup software images.
Synchronizing startup images from the master device to subordinate devices
About this task
Perform this task when the startup images on subordinate devices are not the same version as those on the master device.
This task synchronizes startup images that are running on the master device to subordinate devices. If any of the startup images does not exist or is invalid, the synchronization fails.
The startup images synchronized to subordinate devices are set as main startup images, regardless of whether the source startup images are main or backup.
Procedure
Perform the following steps in user view:
1. Synchronize startup images from the master to subordinate devices.
boot-loader update { all | slot slot-number }
2. Reboot the subordinate devices.
reboot slot slot-number [ force ]
Installing or uninstalling features and patches
About installing or uninstalling features and patches
You can install a new feature or patch image, or upgrade an existing feature image.
Restrictions and guidelines
To ensure a successful image installation or upgrade, do not reboot the device during the image installation or upgrade.
After installing a feature image, you must log in to the device again to use the commands provided in the image.
Prerequisites
Use FTP or TFTP commands to transfer the image file to the default file system on the master device. You do not need to transfer or copy the image file to subordinate member devices. The system will automatically copy the image file to the subordinate members when you activate the images on them. For more information about FTP and TFTP, see "Configuring FTP" and "Configuring TFTP."
Installing or upgrading features
1. (Optional.) Identify the recommended ISSU method and the possible impact of the upgrade.
install activate feature filename&<1-30> slot slot-number test
2. Activate features in the specified files.
install activate feature filename&<1-30> slot slot-number
|
|
NOTE: The software images for the device are digitally signed. The system verifies the digital signature of a feature image for authenticity and integrity before it activates it. If the digital signature verification fails, the system will not activate the image and you will receive a digital signature verification failure message. |
3. Commit the software change.
install commit
For the image changes to take effect after a reboot, you must perform a commit operation.
Installing patches
1. Activate patches in a file.
install activate patch filename { all | slot slot-number }
|
|
NOTE: The software images for the device are digitally signed. The system verifies the digital signature of a patch image for authenticity and integrity before it activates it. If the digital signature verification fails, the system will not activate the image and you will receive a digital signature verification failure message. |
You can specify only one patch image file for this command at a time. However, you can execute this command multiple times to install multiple patch image files.
2. Commit the software change.
install commit
Images run in memory immediately after they are activated. For other images to take effect after a reboot, you must execute this command to commit the software change.
Uninstalling features or patches
Restrictions and guidelines
After uninstalling a feature image, you must log in to the device again for the commands in the image to be removed.
Procedure
1. Deactivate the features or patches installed from an image file.
install deactivate feature filename&<1-30> slot slot-number
install deactivate patch filename { all | slot slot-number }
You can specify only one patch image file for this command at a time. However, you can execute this command multiple times to deactivate multiple patch image files.
2. Commit the software change.
install commit
This step removes the image file from the startup image list but does not delete the image file from the default file system.
To prevent deactivated images from running after a reboot, you must commit the software changes by using the install commit command.
Verifying and maintaining software images
Displaying software images and version information
Perform display tasks in any view.
· Display current software images and startup software images.
display boot-loader [ slot slot-number ]
· Display active software images.
display install active [ slot slot-number ] [ verbose ]
· Display main startup software images.
display install committed [ slot slot-number ] [ verbose ]
· Display inactive software images in the root directories of file systems.
display install inactive [ slot slot-number ] [ verbose ]
· Display system version information.
display version
Displaying startup software image upgrade records
To display startup software image upgrade records, execute the following command in any view:
display version-update-record
Software upgrade examples
Example: Upgrading device software
Network configuration
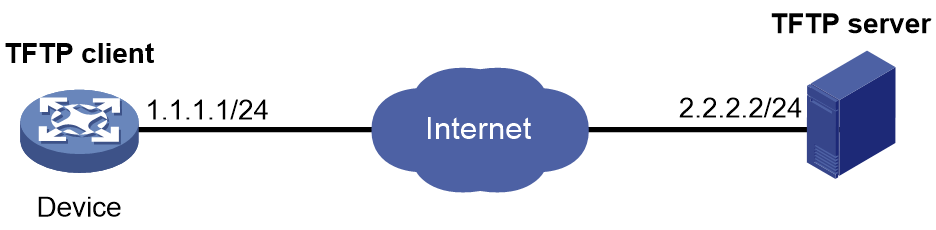
As shown in Figure 1, use the file startup-a2105.ipe to upgrade software images for the device.
Prerequisites
Configure IP addresses and routes. Make sure the device and the TFTP server can reach each other. (Details not shown.)
Procedure
# Configure TFTP settings on both the device and the TFTP server. (Details not shown.)
# Display information about the current software images.
<Sysname> display version
# Back up the current software images.
<Sysname> copy boot.bin boot_backup.bin
<Sysname> copy system.bin system_backup.bin
# Specify boot_backup.bin and system_backup.bin as the backup startup image files.
<Sysname> boot-loader file boot flash:/boot_backup.bin system flash:/system_backup.bin backup
# Use TFTP to download the startup-a2105.ipe image file from the TFTP server to the root directory of the flash memory.
<Sysname> tftp 2.2.2.2 get startup-a2105.ipe
# Specify startup-a2105.ipe as the main startup image file.
<Sysname> boot-loader file flash:/startup-a2105.ipe main
# Verify the startup image settings.
<Sysname> display boot-loader
# Reboot the device to complete the upgrade.
<Sysname> reboot
# Verify that the device is running the correct software.
<Sysname> display version