- Table of Contents
-
- 11-Segment Routing Configuration Guide
- 00-Preface
- 01-SRv6 configuration
- 02-SRv6 TE policy configuration
- 03-SRv6 VPN overview
- 04-IP L3VPN over SRv6 configuration
- 05-EVPN L3VPN over SRv6 configuration
- 06-EVPN VPWS over SRv6 configuration
- 07-EVPN VPLS over SRv6 configuration
- 08-Public network IP over SRv6 configuration
- 09-SRv6 OAM configuration
- 10-SRv6 service chain configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 02-SRv6 TE policy configuration | 1.54 MB |
Contents
SID list creation through dynamic path calculation
SID list computation using PCE
Traffic steering to an SRv6 TE policy
SRv6 TE policy forwarding procedure
SRv6 TE policy transit node protection
SRv6 TE policy tasks at a glance
Manually creating an SRv6 TE policy and configuring its attributes
Automatically creating SRv6 TE policies by using ODN
Enabling the SRv6 capability for a PCC
Configuring PCEP session parameters
Configuring a candidate path and the SID lists of the path
Configuring a candidate path to use manually configured SID lists
Configuring a candidate path to create an SID list through affinity attribute-based path calculation
Configuring a candidate path to create an SID list through Flex-Algo-based path calculation
Configuring a candidate path to use PCE-computed SID lists
Configuring an ODN-created candidate path to use PCE-computed SID lists
Configuring PCE delegation to create candidate paths and SID lists
Enabling strict SID encapsulation for SID lists
Configuring dynamic path calculation timers
Enabling the device to distribute SRv6 TE policy candidate path information to BGP-LS
Shutting down an SRv6 TE policy
Configuring BGP to advertise BGP IPv6 SR policy routes
Restrictions and guidelines for BGP IPv6 SR policy routes advertisement
Enabling BGP to advertise BGP IPv6 SR policy routes
Configuring BGP to redistribute BGP IPv6 SR policy routes
Enabling advertising BGP IPv6 SR policy routes to EBGP peers
Configuring BGP to control BGP IPv6 SR policy route selection and advertisement
Configuring SRv6 TE policy traffic steering
Configuring the SRv6 TE policy traffic steering mode
Configuring color-based traffic steering
Configuring tunnel policy-based traffic steering
Configuring DSCP-based traffic steering
Configuring 802.1p-based traffic steering
Configuring service class-based traffic steering
Configuring TE class ID-based traffic steering
Configuring static route-based traffic steering
Configuring QoS policy-based traffic steering
Configuring Flowspec rule-based traffic steering
Enabling automatic route advertisement for an SRv6 TE policy
Configuring the SRv6 TE policy encapsulation mode
Configuring IPR for SRv6 TE policies
Restrictions and guidelines for IPR configuration
Configuring iFIT measurement for SRv6 TE policies
Configuring IPR path calculation for SRv6 TE policies
Enabling SBFD for SRv6 TE policies
Configuring the BFD echo packet mode for SRv6 TE policies
Enabling hot standby for SRv6 TE policies
Configuring path switchover and deletion delays for SRv6 TE policies
Setting the delay time for bringing up SRv6 TE policies
Configuring path connectivity verification for SRv6 TE policies
Configuring SRv6 TE policy transit node protection
Configuring SRv6 TE policy egress protection
Restrictions and guidelines for SRv6 TE policy egress protection configuration
Configuring candidate path reoptimization for SRv6 TE policies
Configuring flapping suppression for SRv6 TE policies
Configuring the TTL processing mode of SRv6 TE policies
Configuring SRv6 TE policy CBTS
Configuring a rate limit for an SRv6 TE policy
Enabling the device to drop traffic when an SRv6 TE policy becomes invalid
Enabling SRv6 TE policies to forward packets without using the last SID in the SID list
Specifying the packet encapsulation type preferred in optimal route selection
Enabling SRv6 TE policy logging
Enabling SNMP notifications for SRv6 TE policies
Configuring traffic forwarding statistics for SRv6 TE policies
Verifying and maintaining SRv6 TE policies
Verifying the SRv6 TE policy operation status and configuration
Verifying the SRv6 TE policy group operation status and configuration
Verifying the BGP IPv6 SR policy routing configuration
Verifying the SRv6 TE policy BFD and SBFD operation status
Verifying the SRv6 TE policy egress protection configuration
Displaying and clearing SRv6 TE policy forwarding statistics
Displaying SRv6 TE policy information for the PCE process
Displaying IPR-related information for SRv6 TE policies
SRv6 TE policy configuration examples
Example: Configuring SRv6 TE policy-based forwarding
Example: Configuring SRv6 TE policy egress protection
Example: Configuring SRv6 TE policy through ODN
Example: Configuring SRv6 TE policy-based forwarding with IPR
Configuring SRv6 TE policies
About SRv6 TE policies
SRv6 Traffic Engineering (SRv6 TE) policies apply to scenarios where multiple paths exist between a source node and a destination node on an SRv6 network. The device can use an SRv6 TE policy to flexibly steer traffic to a proper forwarding path.
SRv6 TE policy identification
An SRv6 TE policy is identified by the following items:
· BSID—SID of the ingress node (source node).
· Color—Color attribute for the forwarding path. You can use the color attribute to distinguish an SRv6 TE policy from other SRv6 TE policies that are configured for the same source and destination nodes.
· End-point—IPv6 address of the destination node.
SRv6 TE policy contents
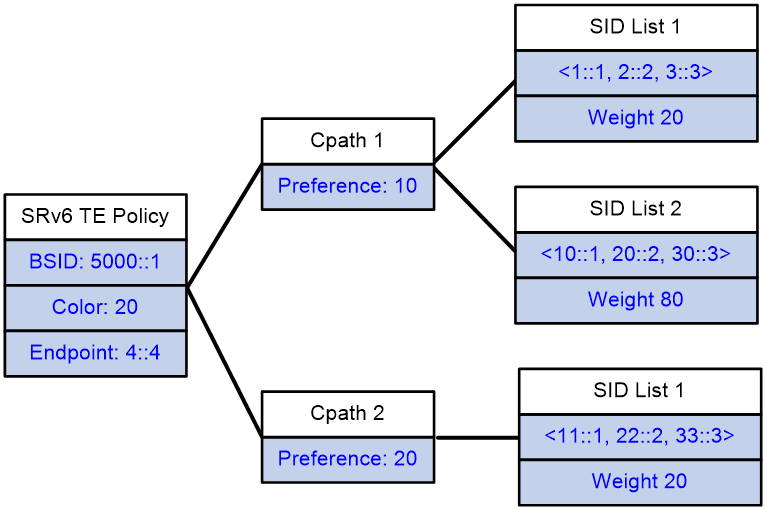
As shown in Figure 1, an SRv6 TE policy consists of candidate paths with different preferences. Each candidate path can have one or multiple subpaths identified by segment lists (also called SID lists).
· Candidate path
An SRv6 TE policy can have multiple candidate paths. Candidate paths are uniquely identified by their preference values. An SRv6 TE policy chooses a candidate path from all its candidate paths based on the preference values to forward traffic.
Two SRv6 TE policies cannot share the same candidate path.
· SID list
A SID list is a list of SIDs that indicates a packet forwarding path. Each SID is the IPv6 address of a node on the forwarding path.
A candidate path can have a single SID list or multiple SID lists that use different weight values. After an SRv6 TE policy chooses a candidate path with multiple SID lists, the traffic will be load shared among the SID lists based on weight values.
Figure 1 SRv6 TE policy contents
SRv6 TE policy creation
An SRv6 TE policy can be created in the following modes:
· Manual configuration from CLI
In this method, you need to manually configure the candidate settings for the SRv6 TE policy, such as candidate path preferences, SID lists and weights.
· Learning from a BGP IPv6 SR policy route
To support SRv6 TE policy, MP-BGP defines the BGP IPv6 SR address family and the Network Layer Reachability Information (NLRI) called the BGP IPv6 SR policy route. A BGP IPv6 SR policy route contains SRv6 TE policy settings, including the BSID, color, end-point, candidate preferences, SID lists, and SID list weights.
The device can advertise its local SRv6 TE policy settings to its BGP IPv6 SR policy peer through a BGP IPv6 SR policy route. The peer device can create a BGP IPv6 SR policy route according to the received SRv6 TE policy settings.
· Automatic creation by ODN
When the device receives a BGP route, it compares the color extended attribute value of the BGP route with the color value of the ODN template. If the color values match, the device automatically generates an SRv6 TE policy and two candidate paths for the policy.
¡ The policy uses the BGP route's next hop address as the end-point address and the ODN template's color value as the color attribute value of the policy.
¡ The candidate paths use preferences 100 and 200. You need to configure the SID lists for the candidate path with preference 200 through dynamic calculation based on affinity attribute or Flex-Algo, and use PCE to compute the SID lists for the candidate path with preference 100. For more information about SID list computation using PCE, see "SID list computation using PCE."
You can also manually create candidate paths for an ODN-created SRv6 TE policy.
SID list creation through dynamic path calculation
SID list creation through dynamic path calculation is supported on the source node of manually created SRv6 TE policies and automatically generated SRv6 TE policies through ODN.
The dynamic path calculation is performed based on affinity attribute or Flex-Algo.
Dynamic path calculation based on affinity attribute
An SRv6 TE policy performs dynamic path calculation based on affinity attribute as follows:
1. Select the links based on the affinity attribute rule.
The SRv6 TE policy selects links containing the bit values associated with the specified affinity attribute as required by the affinity attribute rule.
¡ Link attribute—A 32-bit binary number. Each bit represents an attribute with a value of 0 or 1.
¡ Affinity attribute bit position—The value range is 0 to 32. When the affinity attribute value is N, it is compared with the N+1 bit of the link attribute (from right to left). The affinity attribute applies to the link only if the N+1 bit value of the link attribute is 1.
For example, for affinity attribute name blue associated with bit 1 and affinity attribute name red associated with bit 5, the link selection varies by affinity attribute rule type:
¡ For the include-any affinity attribute rule, a link is available for use if the link attribute has the second bit (associated with affinity attribute blue) or sixth bit (associated with affinity attribute red) set to 1.
¡ For the include-all affinity attribute rule, a link is available for use if the link attribute has both the second bit (associated with affinity attribute blue) and sixth bit (associated with affinity attribute red) set to 1.
¡ For the exclude-any affinity attribute rule, a link is not available for use if the link attribute has the second bit (associated with affinity attribute blue) or sixth bit (associated with affinity attribute red) set to 1.
2. Select the links based on the specified metric.
The SRv6 TE policy supports the following metrics:
¡ Hop count—Selects the link with minimum hops.
¡ IGP link cost—Selects the link with minimum IGP link cost.
¡ Interface latency—Selects the link with the minimum interface latency.
¡ TE cost—Selects the link with minimum TE cost.
After path calculation, the device sorts all link- or node-associated SIDs on the path in an ascending order of distance, and creates an SID list for the SRv6 TE policy. During SID selection, End SIDs take precedence over End.X SIDs.
Dynamic path calculation based on Flex-Algo
The SRv6 TE policy uses the specified Flex-Algo to perform dynamic path calculation. After path calculation, the device sorts all link- or node-associated SIDs on the path in an ascending order of distance, and creates an SID list for the SRv6 TE policy. During SID selection, End SIDs take precedence over End.X SIDs.
For more information about path calculation based on Flex-Algo, see IS-IS configuration in Layer 3—IP Routing Configuration Guide.
SID list computation using PCE
On an SRv6 TE policy network, an SRv6 node can act as a Path Computation Client (PCC) to use the paths computed by the Path Computation Element (PCE) to create SID lists for a candidate path.
Basic concepts
· PCE—An entity that provides path computation for network devices. It can provide intra-area path computation as well as complete SID list computation on a complicated network. A PCE can be stateless or stateful.
¡ Stateless PCE—Provides only path computation.
¡ Stateful PCE—Knows all path information maintained by a PCC, and performs intra-area path recomputation and optimization. A stateful PCE can be active or passive.
- Active stateful PCE—Accepts path delegation requests sent by a PCC and optimizes the paths.
- Passive stateful PCE—Only maintains path information for SID lists of a PCC. A passive stateful PCE does not accept path delegation requests sent by a PCC or optimize the paths.
· PCC—A PCC sends a request to a PCE for path computation and uses the path information returned by the PCE to establish forwarding paths. For a PCC to establish a PCEP session with a PCE, the PCC and PCE must be of the same type.
¡ Stateless PCC—Sends path computation requests to a PCE.
¡ Stateful PCC—Delegates SID list information to a stateful PCE. A stateful PCE can be active or passive.
- Active stateful PCC—Reports its SID list information to a PCE, and uses the paths computed by the PCE to create and update the SID lists.
- Passive stateful PCC—Only reports its SID list information to a PCE but does not use the PCE to compute or update path information for the SID lists.
· PCEP—Path Computation Element Protocol. PCEP runs between a PCC and a PCE, or between PCEs. It is used to establish PCEP sessions to exchange PCEP messages over TCP connections.
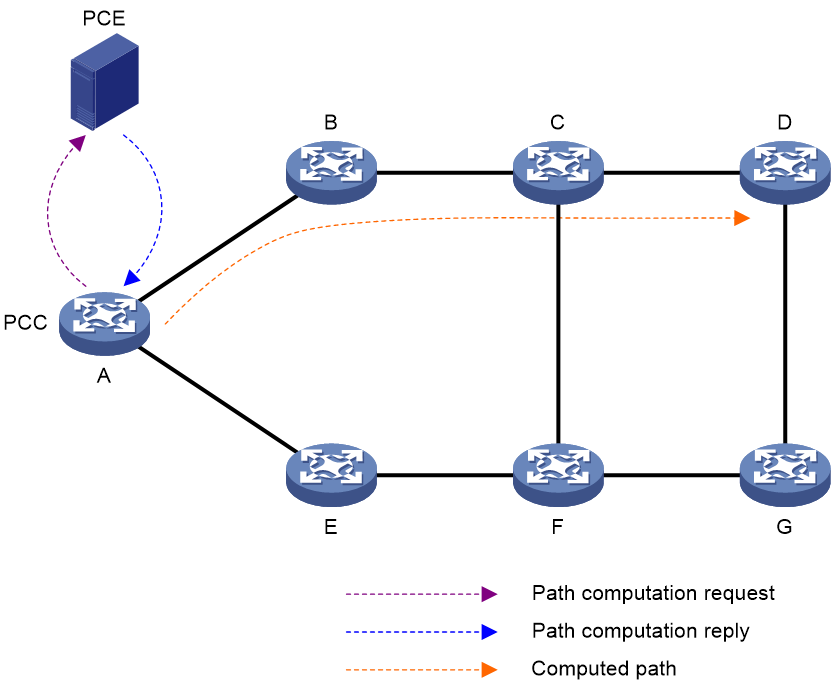
PCE path computation
As shown in Figure 2, the PCE path computation procedure is as follows:
1. The PCC sends a path computation request to the PCE.
2. The PCE computes paths after it receives the request.
3. The PCE replies the PCC with the computed path information.
4. The PCC creates SID lists for the SRv6 TE policy candidate path according to the path information computed by the PCE.
Figure 2 Path computation using PCE
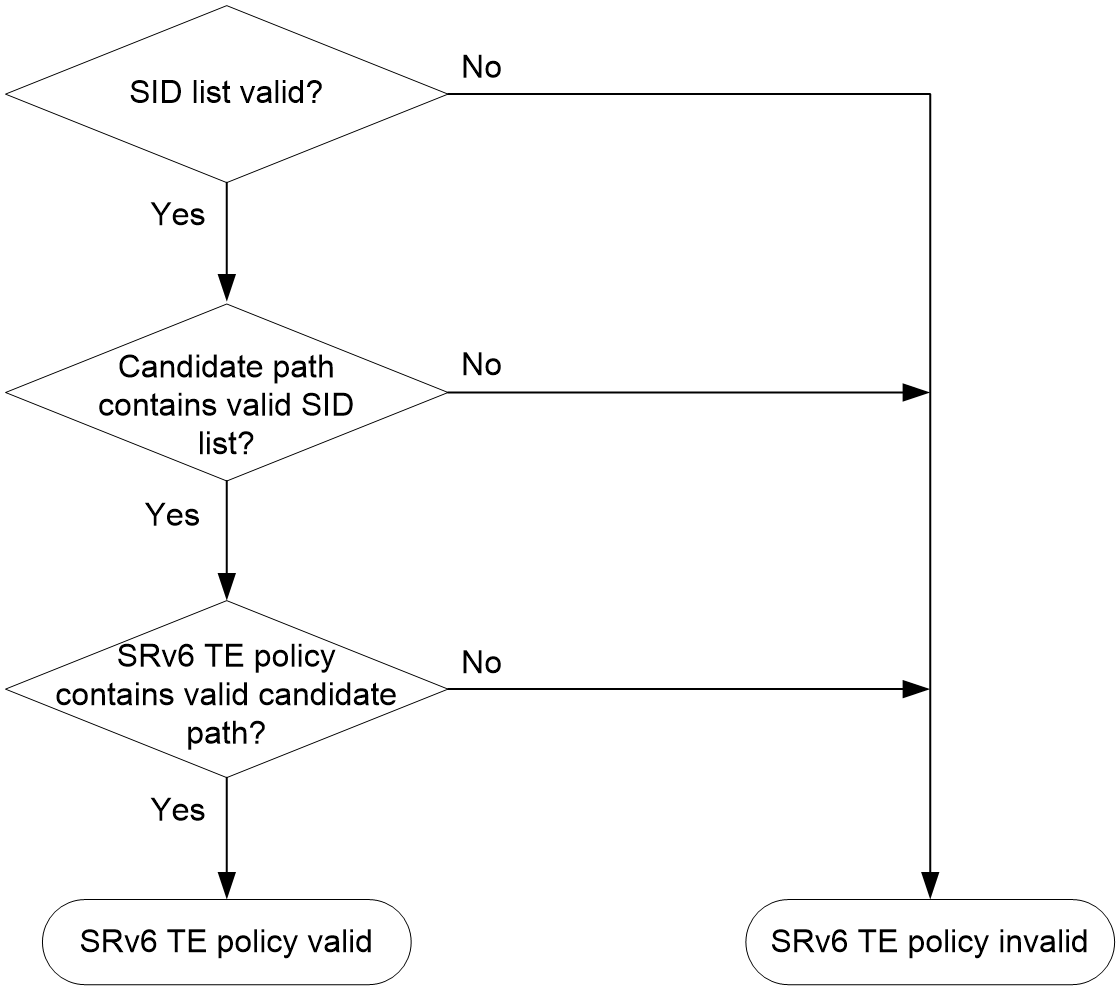
SRv6 TE policy validity
An SRv6 TE policy must be valid in order to ensure successful traffic forwarding.
The following describes the rules for identifying the validity of an SRv6 TE policy:
1. An SRv6 TE policy is valid only if it has valid candidate paths.
2. A candidate path is valid only if it has a valid SID list.
3. A SID list is valid if none of the following situations exists:
¡ The SID list is empty.
¡ The weight of the SID list is 0.
¡ An SR node and the first IPv6 address in the SID list cannot reach each other.
Figure 3 SRv6 TE policy validity determination
SRv6 TE policy group
An SRv6 TE policy group is a group of SRv6 TE policies that have the same endpoint address. Upon receiving a packet destined for that endpoint address, the device searches for the SRv6 TE policy containing the color value mapped to the DSCP or 802.1p value of the packet. The device will use the SRv6 TE policy to forward the packet.
An SRv6 TE policy group is identified by its group ID. It also has the following attributes:
· BSID—SID of the ingress node in the SRv6 TE policy group. It can steer traffic to the SRv6 TE policy group.
· Color—Color extended attribute of the SRv6 TE policy group. BGP routes that carry the same color value as the SRv6 TE policy group are recursed to the SRv6 TE policy group.
· Endpoint—IPv6 address of the egress node (destination node). If an SRv6 TE policy and an SRv6 TE policy group have the same value for the endpoint attribute, the SRv6 TE policy belongs to the SRv6 TE policy group.
You can create an SRv6 TE policy group by using the following methods:
· Manual creation at the CLI
This method requires manually configuring the destination node address of the SRv6 TE policy group.
· Automatic creation by ODN
When the device receives a BGP route, it compares the color extended attribute value of the BGP route with the color value of the ODN template. If the color values match, the device automatically generates an SRv6 TE policy group.
¡ The policy group uses the BGP route's next hop address as the endpoint address and the ODN template's color value as the color attribute value.
¡ The device will assign the smallest ID that is not in use to the SRv6 TE policy group.
Traffic steering to an SRv6 TE policy
The following modes are available to steer traffic to an SRv6 TE policy:
· BSID—If the destination IPv6 address of a received packet is the BSID of an SRv6 TE policy or SRv6 TE policy group, the device uses the SRv6 TE policy or SRv6 TE policy group to forward the packet.
· Color—The device searches for an SRv6 TE policy that has the same color and end-point address as the color and nexthop address of a BGP route. If a matching SRv6 TE policy exists, the device recurses the BGP route to that SRv6 TE policy. Then, when the device receives packets that match the BGP route, it forwards the packets through the SRv6 TE policy.
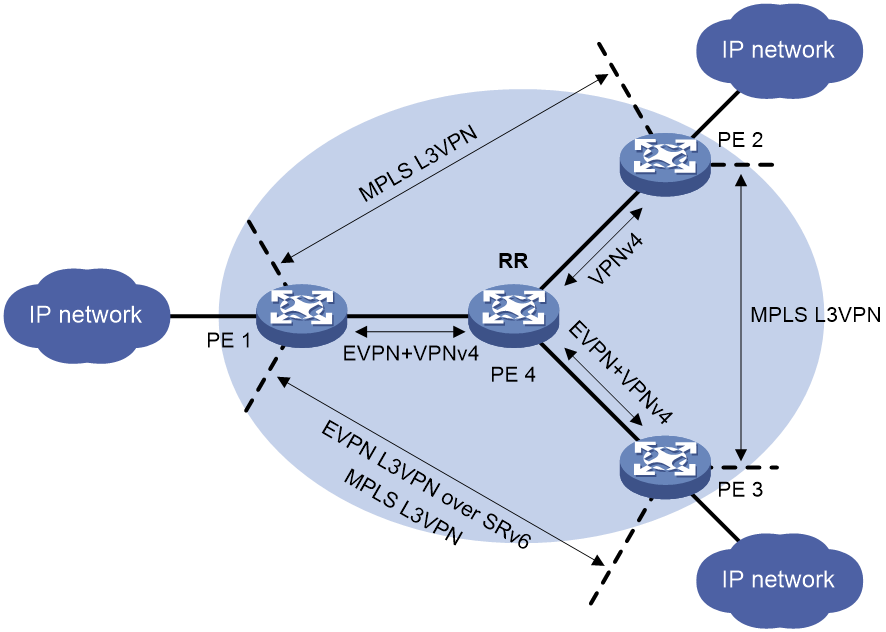
· Tunnel policy—In an MPLS L3VPN, EVPN L3VPN, EVPN VPLS, or EVPN VPWS network, use an SRv6 TE policy as the public tunnel to carry the packets of a VPN instance. For more information about the tunnel policy configuration, see MPLS Configuration Guide.
· DSCP—Create color-to-DSCP mappings for an SRv6 TE policy group, and create a tunnel policy that binds a destination IP address to the SRv6 TE policy group. Upon receiving a packet with the specified destination address, the device searches for the SRv6 TE policy containing the color value mapped to the DSCP value of the packet. The device will use the SRv6 TE policy to forward the packet.
The device obtains an SRv6 TE policy group for traffic steering as follows:
¡ Matches the destination IP address in a packet with a tunnel policy associated with an SRv6 TE policy group.
¡ Searches for an SRv6 TE policy group with color and endpoint address matching the color extended community attribute and next hop in a BGP route, and recurses the BGP route to the SRv6 TE policy group.
· 802.1p (or Dot1p)—Create color-to-802.1p mappings for an SRv6 TE policy group, and create a tunnel policy that binds a destination IP address to the SRv6 TE policy group. Upon receiving a packet with the specified destination address, the device searches for the SRv6 TE policy containing the color value mapped to the 802.1p value of the packet. The device will use the SRv6 TE policy to forward the packet.
The device obtains an SRv6 TE policy group for traffic steering as follows:
¡ Matches the destination IP address in a packet with a tunnel policy associated with an SRv6 TE policy group.
¡ Searches for an SRv6 TE policy group with color and endpoint address matching the color extended community attribute and next hop in a BGP route, and recurses the BGP route to the SRv6 TE policy group.
· Service class—Service class is a type of local ID on the device. You can use the remark service-class command to assign a service class to traffic. For more information about this command, see QoS commands in ACL and QoS Command Reference.
The device obtains an SRv6 TE policy group for traffic steering as follows:
¡ Matches the destination IP address in a packet with a tunnel policy associated with an SRv6 TE policy group.
¡ Searches for an SRv6 TE policy group with color and endpoint address matching the color extended community attribute and next hop in a BGP route, and recurses the BGP route to the SRv6 TE policy group.
After traffic is steered to an SRv6 TE policy group, the device matches the service class value in a packet with the service class mappings in the SRv6 TE policy group.
¡ If the service class value in the packet matches a color-to-service class mapping, and the SRv6 TE policy with the color attribute value in the mapping is valid, the device uses the SRv6 TE policy to forward the packet.
¡ If the service class value in the packet matches an SRv6 BE-to-service class mapping, and the SRv6 BE mode is valid, the device forwards the packet in SRv6 BE mode. In this mode, the device encapsulates a new IPv6 header to the packet, with the destination address in the new IPv6 header set to the VPN SID assigned to public or private network routes by the egress node of the SRv6 TE policy group. Then, the device performs an IPv6 routing table lookup to forward the encapsulated packet.
- If the VPN SID is reachable, the SRv6 BE mode is valid and the packet can be forwarded in SRv6 BE mode.
- If the VPN SID is unreachable, the SRv6 BE mode is invalid and the packet cannot be forwarded in SRv6 BE mode.
· TE class ID—Create mappings between color attribute values and TE class IDs for an SRv6 TE policy group. Upon receiving a packet, the device searches for the SRv6 TE policy containing the color attribute value mapped to the TE class ID of the packet. The device will use the SRv6 TE policy to forward the packet.
The device obtains an SRv6 TE policy group for traffic steering as follows:
¡ Matches the destination IP address in a packet with a tunnel policy associated with an SRv6 TE policy group.
¡ Searches for an SRv6 TE policy group with color and endpoint address matching the color extended community attribute and next hop in a BGP route, and recurses the BGP route to the SRv6 TE policy group.
· Static route—Directs traffic to an SRv6 TE policy through a static route. The device uses the SRv6 TE policy to forward the packets that match the static route.
· PBR—Directs traffic to an SRv6 TE policy through PBR. The device uses the SRv6 TE policy to forward the packets that match the PBR policy. For more information about PBR, see Layer 3—IP Routing Configuration Guide.
· QoS policy—Redirects traffic to an SRv6 TE policy through a QoS policy. The device uses the SRv6 TE policy to forward the packets that match the traffic classes of the QoS policy. For more information about QoS policies, see the QoS configuration in ACL and QoS Configuration Guide.
· Flowspec—Redirects traffic to an SRv6 TE policy through a Flowspec rule. The device uses the SRv6 TE policy to forward the packets that match the Flowspec rule. For more information about Flowspec, see ACL and QoS Configuration Guide.
· Automatic route advertisement—Advertises an SRv6 TE policy to IGP (IPv6 IS-IS or OSPFv3) for route computation to forward the matching traffic through the SRv6 TE policy.
An SRv6 TE policy supports only automatic route advertisement in IGP shortcut mode, which is also called autoroute announce. Autoroute announce regards the SRv6 TE policy tunnel as a link that connects the tunnel ingress and egress. The tunnel ingress includes the SRv6 TE policy tunnel in IGP route computation. It does not advertise the SRv6 TE policy tunnel in the IGP, so other devices do not include the SRv6 TE policy tunnel in route computation.
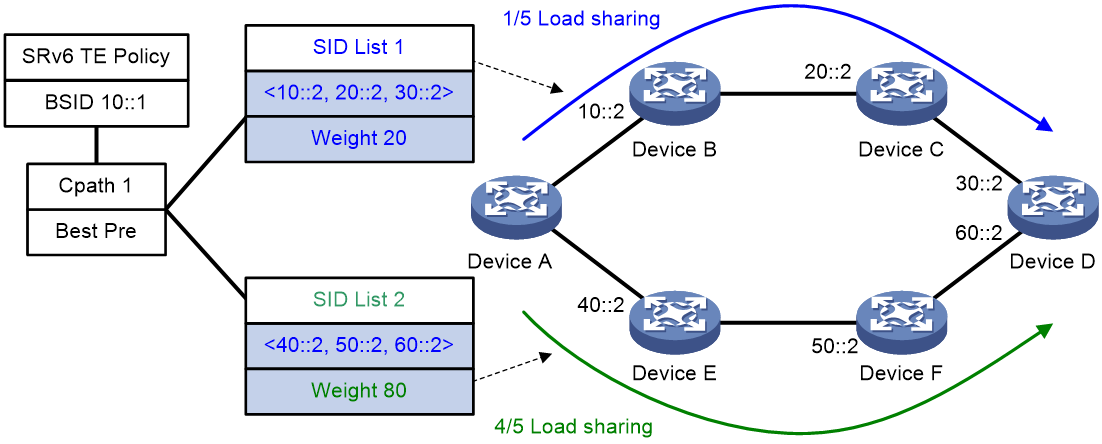
SRv6 TE policy path selection
After traffic is steered in to an SRv6 TE policy, the SRv6 TE policy selects a forwarding path for the traffic as follows:
1. Selects the valid candidate path that has the highest preference.
2. Performs Weighted ECMP (WECMP) load sharing among the SID lists of the selected candidate path. The load of SID list x is equal to Weight x/(Weight 1 + Weight 2 + … + Weight n).
For example, as shown in Figure 4, Device A first selects a valid SRv6 TE policy by BSID. Then, the device selects a candidate path by preference. The candidate path has two valid SID lists: SID list 1 and SID list 2. The weight value of SID list 1 is 20 and the weight value of SID list 2 is 80. One fifth of the traffic will be forwarded through the subpath identified by SID list 1. Four fifth of the traffic will be forwarded through the subpath identified by SID list 2.
Figure 4 SRv6 TE policy path selection
SRv6 TE policy forwarding procedure
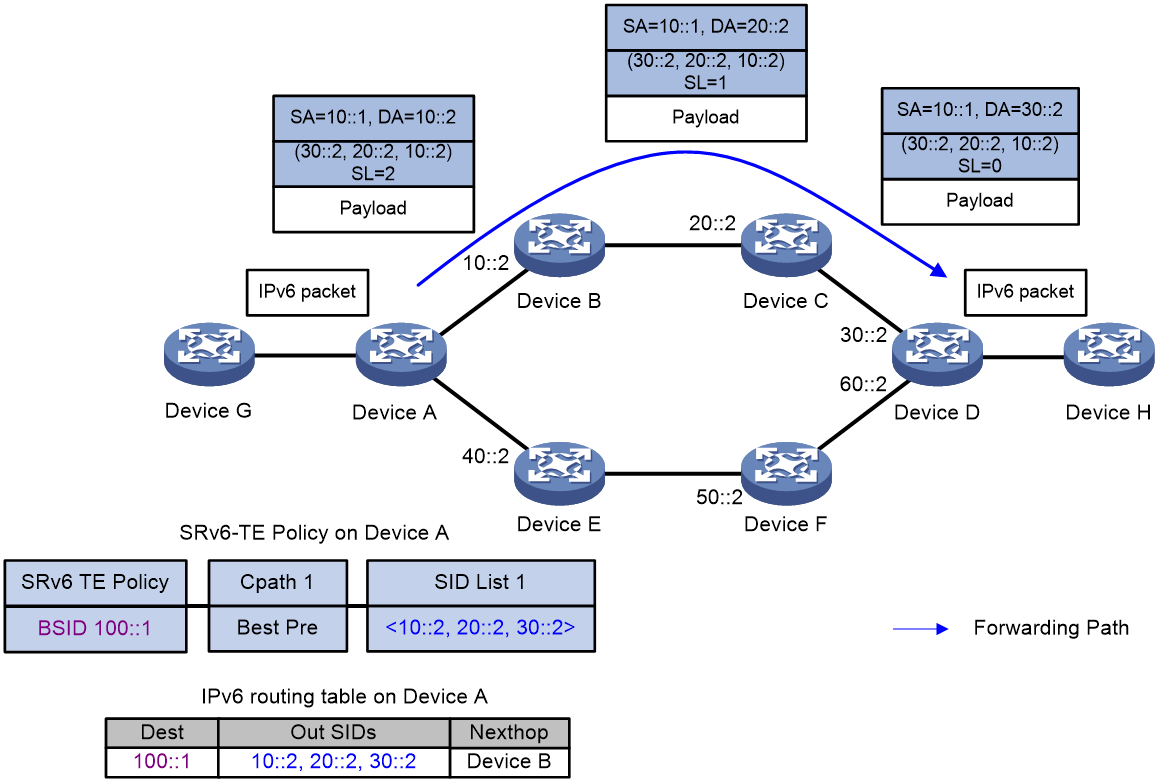
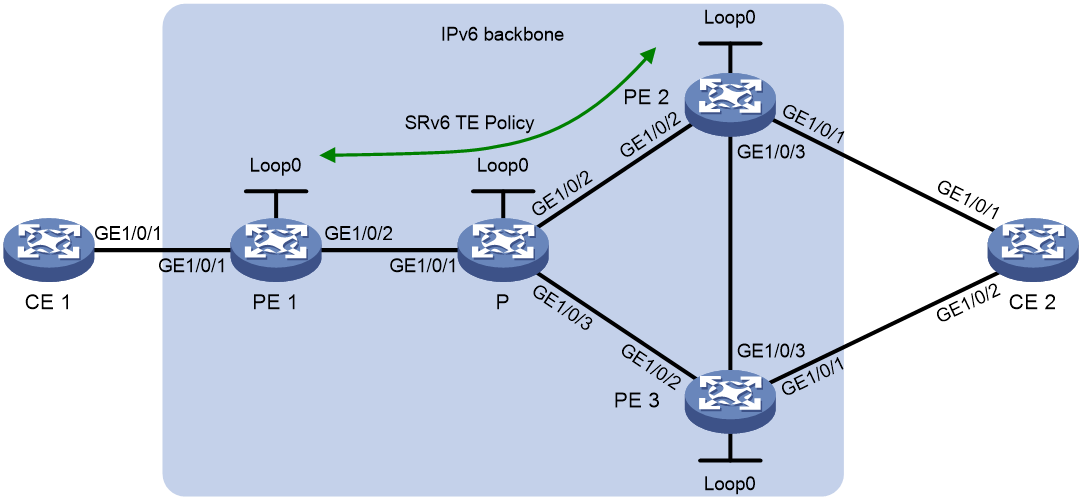
As shown in Figure 5, the SRv6 TE policy forwarding procedure is as follows (BSID-based traffic steering as an example):
1. After Device A receives a packet with destination address 100::1, it searches its IPv6 routing table and determines that the address is a BSID. Then, Device A encapsulates the packet with an SRH header according to the SRv6 TE policy of the BSID. The SRH header contains SID list {10::2, 20::2, 30::2}, where 10::2 is the SID for Device B, 20::2 is the SID for Device C, and 30::2 is the SID for Device D.
2. Device A forward the packet to the next hop Device B.
3. After Device B receives the packet, it obtains the next hop Device C from the SRH, and then forwards the packet to Device C.
4. After Device C receives the packet, it obtains the next hop Device D from the SRH, and then forwards the packet to Device D.
5. After Device D receives the packet, it identifies that the SL value is 0 in the SRH. So Device D decapsulates the packet. Device D deletes the SRH header and forwards the packet according to the destination address of the packet.
Figure 5 SRv6 TE policy forwarding diagram
SRv6 TE policy CBTS
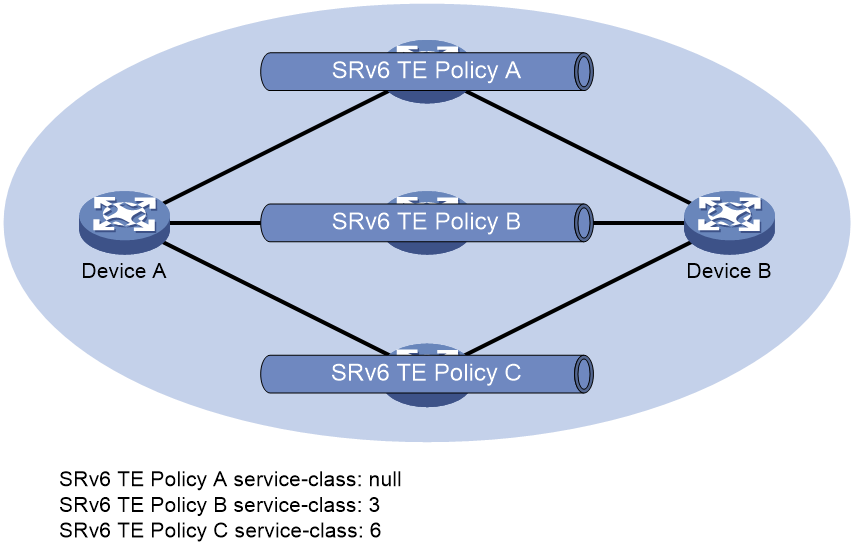
About SRv6 TE policy CBTS
SRv6 TE policy Class Based Tunnel Selection (CBTS) enables dynamic routing and forwarding of traffic with service class values over different SRv6 TE policy tunnels between the same tunnel headend and tailend. Unlike load sharing that selects multiple tunnels to forward the matching traffic, CBTS uses a dedicated tunnel for a certain class of service.
How SRv6 TE policy CBTS works
SRv6 TE policy CBTS processes traffic mapped to a priority as follows:
1. Uses a traffic behavior to set a service class value for the traffic.
2. Configures a service class for an SRv6 TE policy.
3. Compares the service class value of the traffic with the service class values of the SRv6 TE policy tunnels and forwards the traffic to a matching tunnel.
SRv6 TE policy tunnel selection rules
SRv6 TE policy CBTS uses the following rules to select an SRv6 TE policy tunnel for the traffic to be forwarded:
· If an SRv6 TE policy tunnel has the same service class value as the traffic, CBTS uses this tunnel.
· If multiple SRv6 TE policy tunnels have the same service class value as the traffic, CBTS selects a tunnel based on the flow forwarding mode:
¡ If there is only one flow and flow-based load sharing is set, CBTS randomly selects a matching tunnel for packets of the same flow.
¡ If there are multiple flows or if there is only one flow but packet-based load sharing is set, CBTS uses all matching tunnels to load share the packets.
For more information about the flow identification and load sharing mode, see the ip load-sharing mode command in Layer 3—IP Services Command Reference.
· If the traffic does not match any SRv6 TE policy tunnels by service class value, CBTS randomly selects a tunnel from all SRv6 TE policy tunnels with the lowest forwarding priority. An SRv6 TE policy that has a smaller service class value has a lower forwarding priority. An SRv6 TE policy that is not configured with a service class value has the lowest priority.
SRv6 TE policy CBTS application scenario
As shown in Figure 6, CBTS selects SRv6 TE policy tunnels for traffic from Device A to Device B as follows:
· Uses SRv6 TE policy B to forward traffic with service class value 3.
· Uses SRv6 TE policy C to forward traffic with service class value 6.
· Uses SRv6 TE policy A to forward traffic with service class value 4.
· Uses SRv6 TE policy A to forward traffic with no service class value.
Figure 6 Uses SRv6 TE policy CBTS application scenario
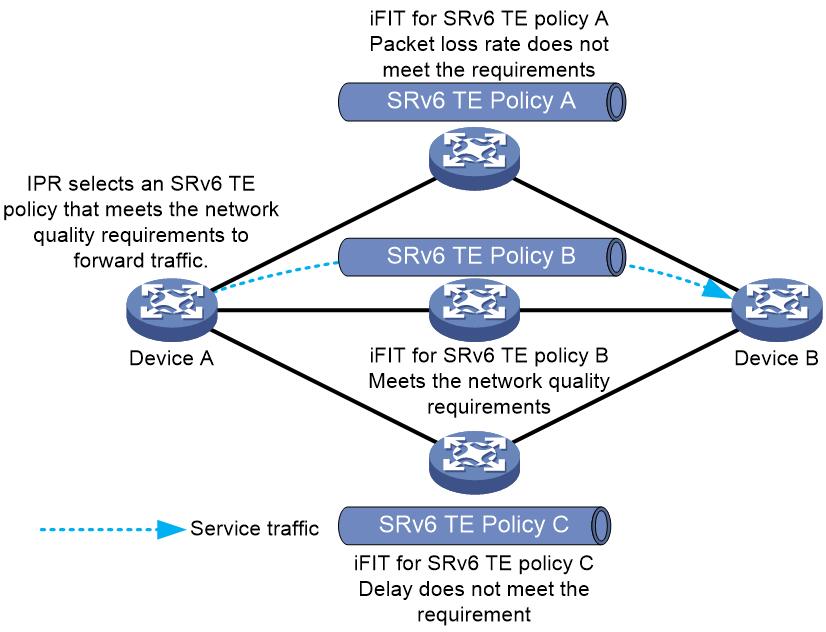
IPR for SRv6 TE policies
About this feature
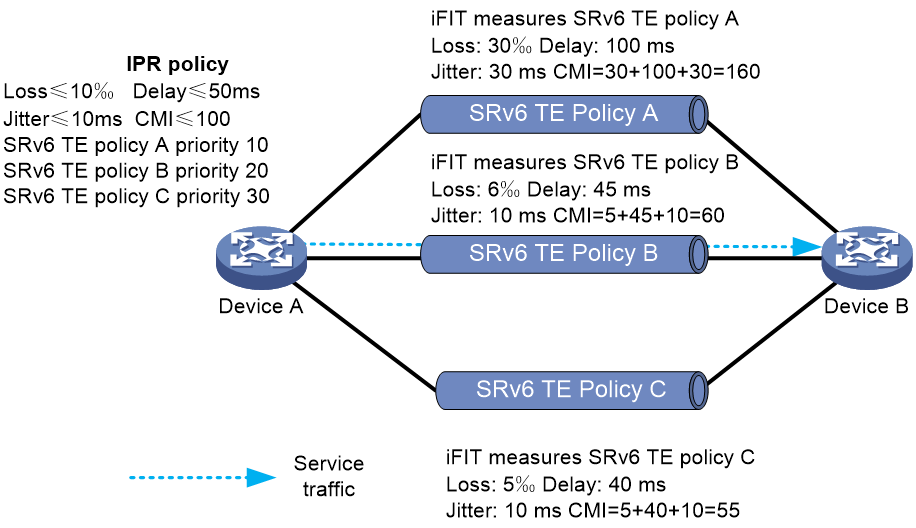
As shown in Figure 7, establish an SRv6 TE policy group between two nodes in the network, which contains multiple SRv6 TE policy tunnels. The network quality of different SRv6 TE policy tunnels in the SRv6 TE policy group might vary and change in real time. You can use Intelligent Policy Route (IPR) to automatically switch over traffic in one forwarding path to another forwarding path based on the network quality of the SRv6 TE policy tunnels. IPR ensures that service traffic is always forwarded through a forwarding path that meets the network quality requirements.
The IPR feature of SRv6 TE policies uses the real-time network quality measurement capability of iFIT to evaluate the network quality of SRv6 TE policy tunnels. The feature excludes SRv6 TE policy tunnels that do not meet the network quality requirements based on the measurement results of iFIT, finds the SRv6 TE policy tunnel with the highest priority through calculation, and steers traffic to this SRv6 TE policy tunnel for forwarding.
IPR operating mechanism
IPR is mainly accomplished through the collaboration of the following functions:
· The iFIT measurement function of SRv6 TE policies.
· The IPR path calculation function of SRv6 TE policies.
· The function of steering service traffic to an IPR policy.
IPR uses the following procedure to forward traffic:
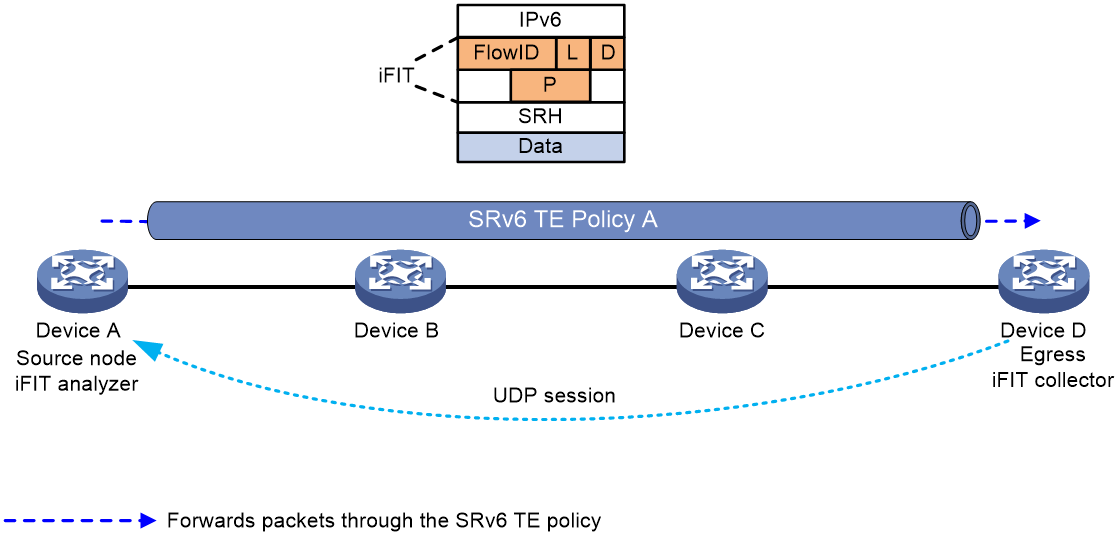
1. Uses iFIT to measure the network quality of SRv6 TE policies.
As shown in Figure 8, configure iFIT on the source and egress nodes of each SRv6 TE policy to measure the end-to-end packet loss rate, delay, and jitter of each SRv6 TE policy. The source node analyzes and calculates the real-time packet loss rate, delay, and jitter data for each SRv6 TE policy. iFIT uses the following procedure to measure the network quality of an SRv6 TE policy:
a. The source node, which operates in analyzer operating mode, automatically creates an iFIT instance and assigns a flow ID to the instance.
b. Acts as the data sender, the source node encapsulates the original packets with the DOH header carrying the iFIT option field and the SRH header when it forwards the packets through the SRv6 TE policy. The iFIT option field contains a flow ID that identifies a target flow, the L bit (packet loss measurement color bit), the D bit (delay measurement color bit), and the measurement interval. The source node colors the L and D bits of the packets within an iFIT measurement interval. It then performs the following operations:
- Uses the color information of the packets to count the number of packets transmitted through the SRv6 TE policy within the measurement interval.
- Records the timestamps of the packets with the D bit set to 1 and sent through the SRv6 TE policy within the measurement interval.
c. Acts as the data receiver, the egress node, which operates in collector operating mode, parses the iFIT option field in packets to obtain iFIT measurement information (including the measurement interval) for the SRv6 TE policy. It then performs the following operations:
- Uses the color information of the packets to count the number of packets received through the SRv6 TE policy within the measurement interval.
- Records the timestamps of the packets with the D bit set to 1 and received through the SRv6 TE policy within the measurement interval.
d. The egress node performs the following operations:
- Establishes a UDP session with the source node through the source address of the received packets.
- Returns the packet count statistics and packet timestamps to the source node through the UDP session according to the iFIT measurement interval of the SRv6 TE policy.
e. The source node analyzes and calculates the packet loss rate, delay, and jitter of the packets forwarded through the SRv6 TE policy.
Figure 8 iFIT measurement diagram
2. Uses IPR path calculation for path selection and switchover.
As shown in Figure 9, the source node of SRv6 TE policies periodically calculates the current optimal SRv6 TE policy based on the following items:
¡ The packet loss rate, delay, and jitter data measured by iFIT for different SRv6 TE policies.
¡ The path selection priority of each SRv6 TE policy.
IPR path calculation requires IPR policies. An IPR policy is an SLA-based policy for selecting the optimal SRv6 TE policy. You can define the following contents in an IPR policy:
¡ SLA thresholds for service traffic, including the delay threshold, packet loss rate threshold, jitter threshold, and Composite Measure Indicator (CMI) threshold. CMI is calculated by using the following formula: CMI = delay (ms) + jitter (ms) + packet loss rate (‰).
¡ Mappings between color attribute values of SRv6 TE policies and path selection priority values. The smaller the value, the higher the priority.
¡ Switchover period between SRv6 TE policies and WTR period.
The operating mechanism for IPR path calculation is as follows:
a. The source node periodically performs path calculation according to the IPR calculation period. When calculating the optimal SRv6 TE policy, it first measures whether the delay, packet loss rate, jitter, and CMI values of each SRv6 TE policy cross the SLA thresholds defined in an IPR policy. If any of the values crosses an SLA threshold, the source node does not use the SRv6 TE policy as a candidate forwarding path to participate in optimal SRv6 TE policy selection. If iFIT fails to measure the delay, packet loss rate, jitter, and CMI values of an SRv6 TE policy, but the SRv6 TE policy is valid, it can still be used as a candidate path for path selection.
b. The source node selects the SRv6 TE policy with the smallest path selection priority value from the candidate SRv6 TE policies as the optimal SRv6 TE policy. If multiple SRv6 TE policies have the same path selection priority, they can load share traffic.
c. When the source node of SRv6 TE policies calculates a different optimal SRv6 TE policy than the one currently used by a service, it does not immediately switch over the traffic of that service to the new optimal SRv6 TE policy. Instead, it waits for a switchover period. This mechanism prevents SRv6 TE policy flapping from causing frequent forwarding path switchover for service traffic.
Figure 9 Diagram for IPR path calculation
3. Steers service traffic to an IPR policy as follows:
a. Uses one of the following methods to obtain an SRv6 TE policy group for traffic steering:
- Matches the destination IP address in a packet with a tunnel policy associated with an SRv6 TE policy group.
- Searches for an SRv6 TE policy group with color and endpoint address matching the color extended community attribute and next hop in a BGP route, and recurses the BGP route to the SRv6 TE policy group.
b. Configure TE class ID-based traffic steering for the SRv6 TE policy group.
c. Configure mappings between TE class IDs and IPR policies. The optimal SRv6 TE policy is dynamically selected from the SRv6 TE policy group for forwarding service traffic.
BFD for SRv6 TE policy
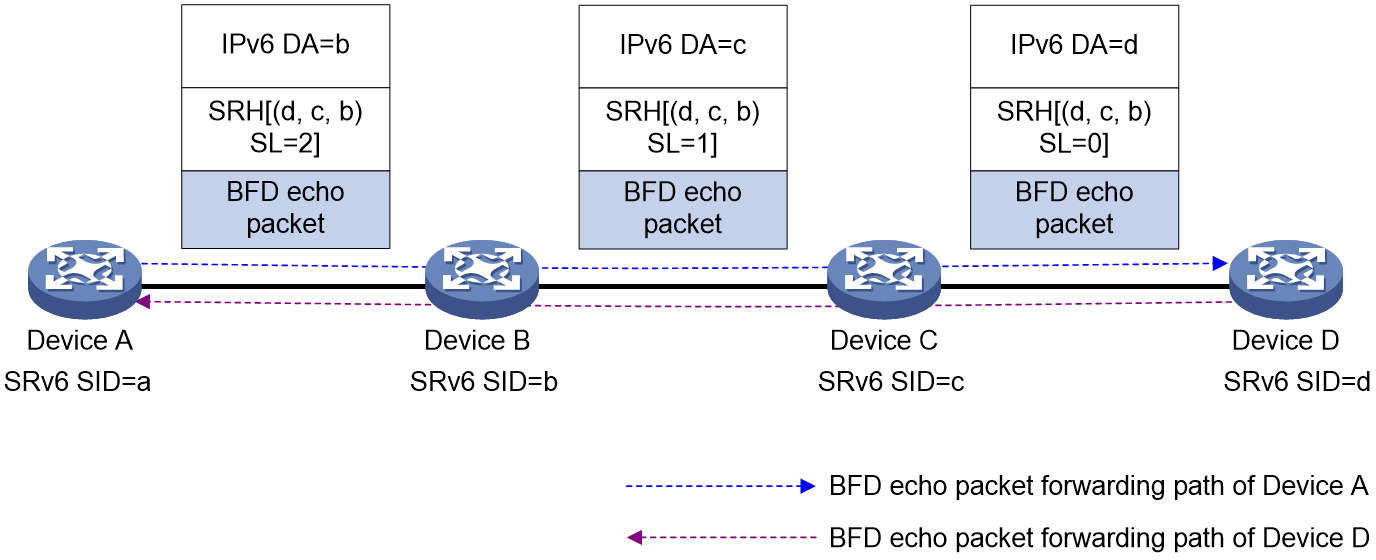
Echo BFD for SRv6 TE policy
If a candidate path of an SRv6 TE policy contains multiple SID lists, the SRv6 TE policy establishes a BFD session for each SID list to detect validity of the corresponding forwarding paths.
As shown in Figure 10, configure an SRv6 TE policy on Device A and use echo BFD to detect the SRv6 TE policy. The detection process is as follows:
1. The source node sends BFD echo packets that each encapsulates a SID list of the SRv6 TE policy.
2. After the endpoint node receives an BFD echo packet, it sends the BFD echo packet back to the source node by using the IPv6 routing table.
3. If the source node can receive the BFD echo packet within the detection timeout time, it determines the corresponding SID list (forwarding path) of the SRv6 TE policy is available. If no BFD echo packet is received, the device determines that the SID list is faulty. If all the SID lists for the primary path are faulty, BFD triggers a primary-to-backup path switchover.
Figure 10 Echo BFD for SRv6 TE policy procedure
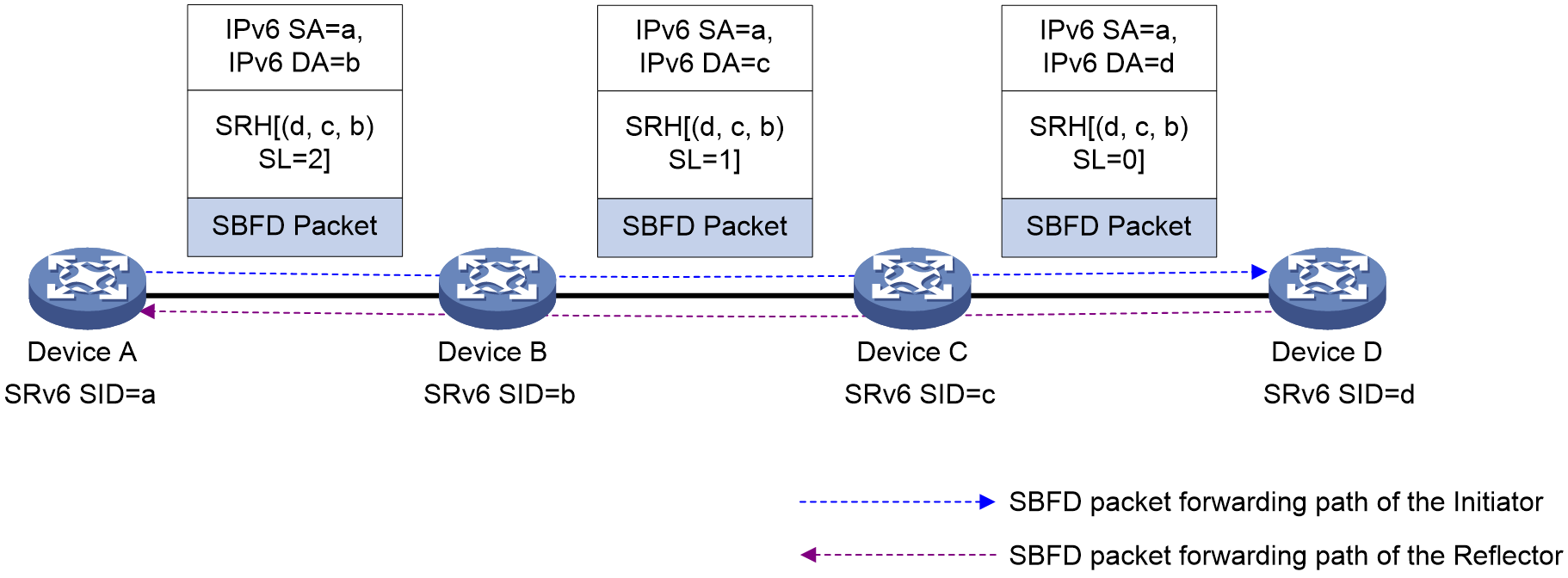
SBFD for SRv6 TE policy
An SRv6 TE policy cannot maintain its status by exchanging messages between devices. You can configure seamless BFD (SBFD) to verify the connectivity of an SRv6 TE policy to implement fast failover in milliseconds.
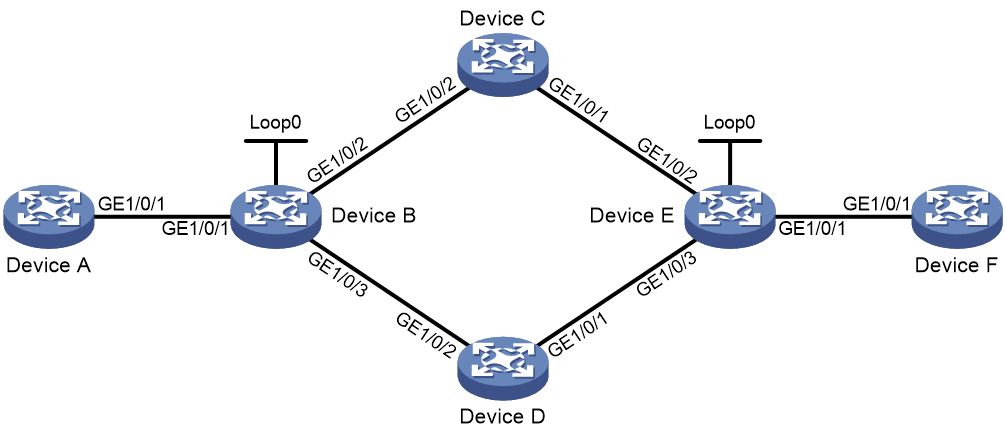
As shown in Figure 11, configure an SRv6 TE policy on Device A and use SBFD to detect the SRv6 TE policy. The detection process is as follows:
1. The source node (Device A, the initiator) and sends SBFD packets that encapsulate the SID lists of the primary and backup candidate paths of the SRv6 TE policy.
2. After the destination node (Device E, the reflector) receives an SBFD packets, it checks whether the remote discriminator carried the packet is the same as the local discriminator. If yes, the reflector sends the SBFD response packet to the initiator by using the IPv6 routing table. If no, the reflector drops the SBFD packet.
3. If the source node can receive the SBFD response within the detection timeout time, it determines the corresponding SID list (forwarding path) of the SRv6 TE policy is available. If no response is received, the device determines that the SID list is faulty. If all the SID lists for the primary path are faulty, SBFD triggers a primary-to-back path switchover.
Figure 11 SBFD for SRv6 TE policy procedure
|
|
NOTE: Because SBFD responses are forwarded according to the IPv6 routing table lookup, all SBFD sessions for the SRv6 TE policies that have the same source and destination nodes use the same path to send responses. A failure of the SBFD response path will cause all the SBFD sessions to be down and consequentially packets cannot be forwarded through the SRv6 TE policies. |
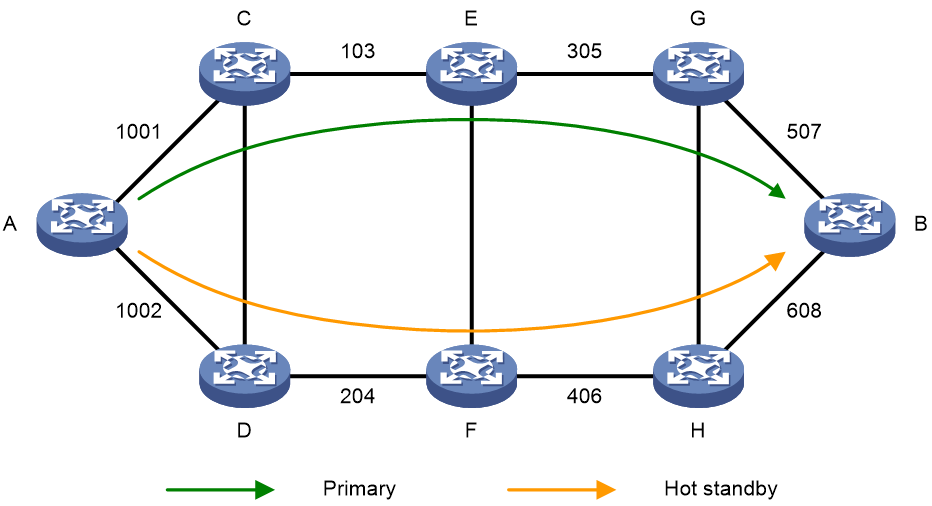
SRv6 TE policy hot standby
If an SRv6 TE policy has multiple valid candidate paths, the device chooses the candidate path with the greatest preference value. If the chosen path fails, the SRv6 TE policy must select another candidate path. During path reselection, packet loss might occur and thus affect service continuity.
The SRv6-TE hot standby feature can address this issue. This feature takes the candidate path with the greatest preference value as the primary path and that with the second greatest preference value as the backup path in hot standby state. As shown in Figure 12, when the forwarding paths corresponding to all SID lists of the primary path fails, the standby path immediately takes over to minimize service interruption.
Figure 12 SRv6 TE policy hot standby
You can configure both the hot standby and SBFD features for an SR-TE policy. Use SBFD to detect the availability of the primary and standby paths specified for hot standby. If all SID lists of the primary path become unavailable, the standby path takes over and a path recalculation is performed. The standby path becomes the new primary path, and a new standby path is selected. If both the primary and standby paths fail, the SR-TE policy will calculate new primary and standby paths.
SRv6 TE policy transit node protection
Protection path failure
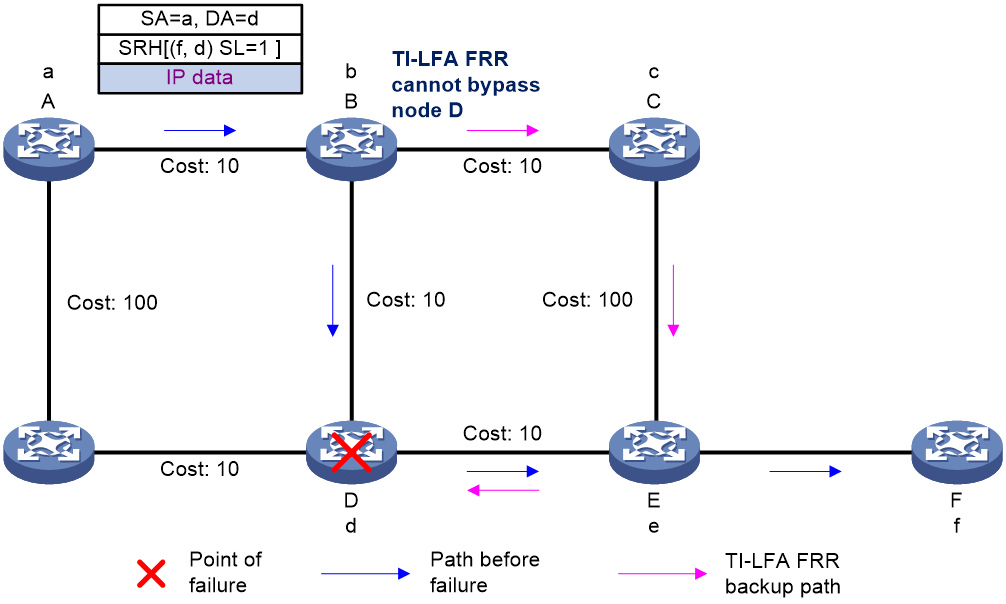
The SID list of an SRv6 TE policy specifies the nodes or links that packets must traverse. As shown in Figure 13, node A forwards packets to node F through an SRv6 TE policy. The SID list of the optimal candidate path contains the End.SIDs of node D and egress node F. Therefore, the packet arrives at node D before reaching egress node F. If TI-LFA FRR is enabled on node B and node D fails, the backup path calculated by TI-LFA FRR will still use the End.SID of node D as destination. As a result, the backup path cannot bypass node D and thus cannot provide service protection.
Figure 13 Protection path failure
Transit node protection (SRv6 TE FRR)
To resolve the protection path failure caused by strict node constraints in an SRv6 TE policy, SRv6 TE FRR is introduced.
After SRv6 TE FRR is enabled, when a transit node of an SRv6 TE policy fails, the upstream node (enabled with SRv6 TE FRR) of the faulty node can take over to forward packets. The upstream node is called a proxy forwarding node. During proxy forwarding, the faulty node is bypassed by traffic.
After SRv6 TE FRR is enabled on a node, upon receiving a packet that contains an SRH and the SL in the SRH is greater than 0 (SL>0), the node will act as a proxy forwarding node in any of the following scenarios:
· The node does not find a matching forwarding entry in the IPv6 FIB.
· The next hop address of the packet is the destination address of the packet, and the outgoing interface for the destination address is in DOWN state.
· The matching local SRv6 SID is an END.X SID, and the outgoing interface for the END.X SID is in DOWN state.
· The outgoing interface in the matching route is NULL0.
A proxy forwarding node forwards packets as follows:
· Decrements the SL value in the SRH of a packet by 1.
· Copies the next SID to the DA field in the outer IPv6 header, so as to use the SID as the destination address of the packet.
· Looks up the forwarding table by the destination address and then forwards the packet.
In this way, the proxy forwarding node bypasses the fault node. This transit node failure protection technology is referred to as SRv6 TE FRR.
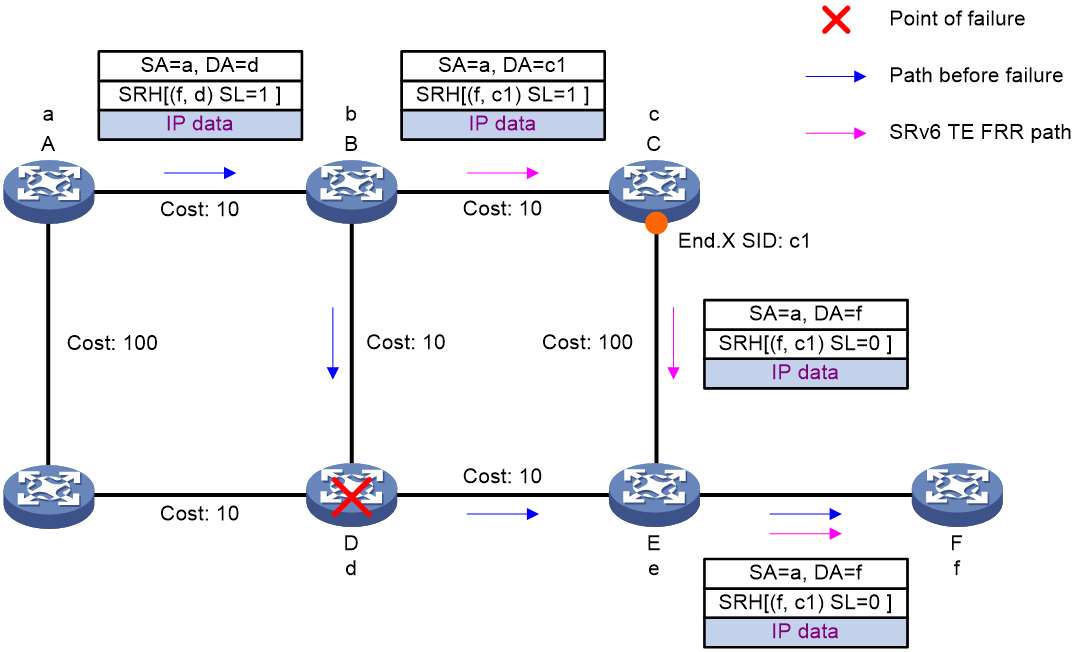
Figure 14 SRv6 TE FRR for transit node failure protection
As shown in Figure 14, after a packet is steered into an SRv6 TE policy, the packet is forwarded as instructed by the SID list {d, f}.
When node D fails, the node failure protection process is as follows:
1. Upstream node B detects that the next hop of the packet is faulty. In this situation, the output interface for the destination address of the packet is in DOWN state, and the SL value is greater than 0. Therefore, node B performs the proxy forwarding behavior: Decrements the SL value by 1, copies the next SID to the DA field in the outer IPv6 header, and then forwards the packet according to the SID (destination address of the packet). Because the SL value is now 0, node B can remove the SRH and then search the related table to forward the packet based on the destination address (f).
2. Node B forwards the packet as follows:
¡ If the route to node F is converged (the next hop in the route is node C), node B uses the converged shortest path to forward the packet to node C.
¡ If the route to node F is not converged (the primary next hop in the route is node D), node B uses the TI-LFA computed backup path to forward packet. The backup path's repair list is <c1>. Therefore, node B encapsulates an SRH to the packet to add backup path Segment List c1, and then forwards the packet over the backup path to node F.
Special processing on the source node
If source node A (ingress node) of the SRv6 TE policy detects the failure of node D (the first SID in the SID list is unreachable), node A then places the SRv6 TE policy to the down state. The device cannot forward packets through the SRv6 TE policy or trigger SRv6 TE FRR.
To resolve this issue, enable the bypass feature for the SRv6 TE policy on the source node. This feature enables the source node to generate a route that uses the first SID as the destination address and the NULL0 interface as the outgoing interface. The route ensures that the SRv6 TE policy is in up state when the first SID is unreachable, so as to trigger SRv6 TE FRR.
After node A triggers SRv6 TE FRR, node A decrements the SL value by 1, copies the next SID (f) to the DA field in the outer IPv6 header, and then forwards the packet to node B according to the SID (destination address of the packet).
When node B receives the packet, it processes the packet as follows:
· If the route to node F is converged (the next hop in the route is node C), node B uses the converged shortest path to forward the packet to node C.
· If the route to node F is not converged (the primary next hop in the route is node D), node B uses the TI-LFA computed backup path to forward the packet to node F.
SRv6 egress protection
This feature provides egress node protection in IP L3VPN over SRv6, EVPN L3VPN over SRv6, EVPN VPLS over SRv6, EVPN VPWS over SRv6, or IP public network over SRv6 networks where the public tunnel is an SRv6 TE policy tunnel.
SRv6 TE policy egress protection applies only to the dual homing scenario where a CE is dual-homed to PEs. To implement SRv6 TE policy egress protection, the egress node and the protected egress node must have the same forwarding entries.
|
IMPORTANT: · SRv6 TE policy egress protection is not supported in EVPN VPLS over SRv6 and EVPN VPWS over SRv6 networks if dual homing is configured in the networks and the redundancy mode is single-active. · In addition to scenarios where SRv6 TE policies act as tunnels, SRv6 TE policy egress protection also takes effect on scenarios where SRv6 BE-based forwarding is used. |
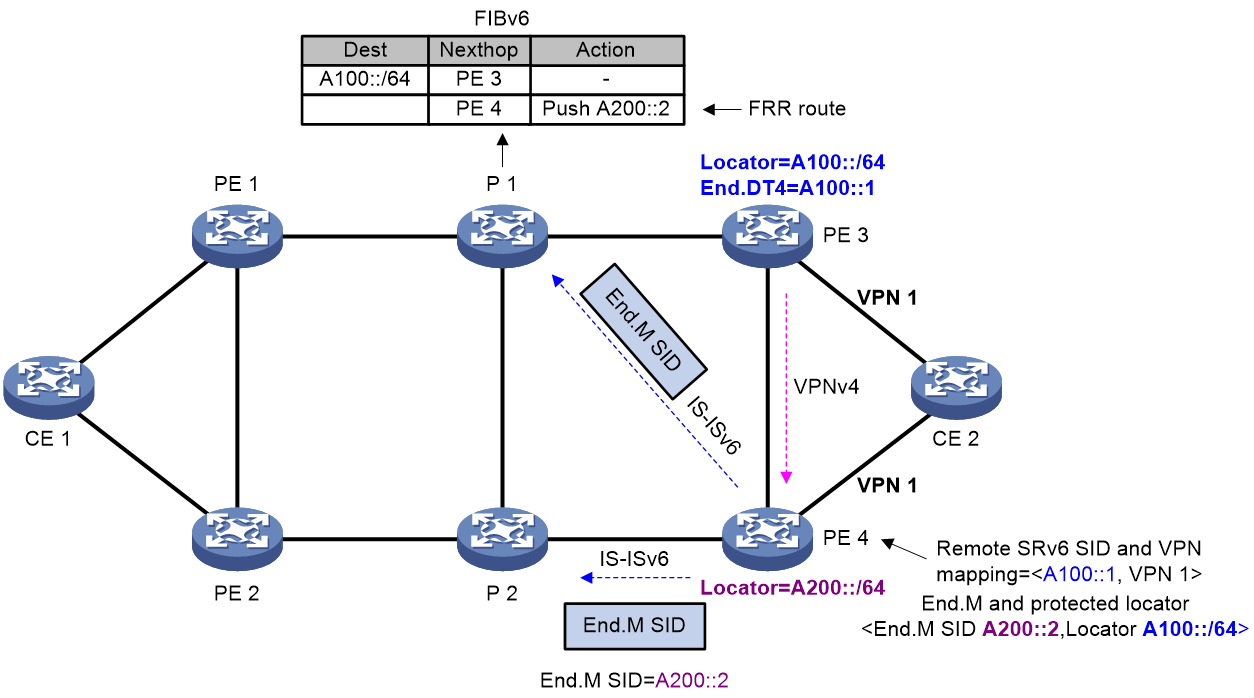
As shown in Figure 15, an SRv6 TE policy is deployed between PE 1 and PE 3. PE 3 is the egress node (endpoint node) of the SRv6 TE policy. To improve forwarding reliability, CE 2 is dual-homed to PE 3 and PE 4, and PE 4 is enabled to protect PE 3.
Figure 15 SRv6 egress protection
End.M SID
In SRv6 TE policy egress protection, an End.M SID is used to protect the SRv6 SIDs in a specific locator. If an SRv6 SID advertised by the remote device (PE 3 in this example) is within the locator, the protection node (PE 4) uses the End.M SID to protect that SRv6 SID (remote SRv6 SID).
PE 4 takes different actions as instructed by an End.M SID in different network scenarios:
· IP L3VPN/EVPN L3VPN/IP public network over SRv6 TE policy scenario
a. Removes the outer IPv6 header to obtain the remote SRv6 SID from the inner packet.
b. Searches the remote SRv6 SID and VPN instance/public instance mapping table to find the VPN instance/public instance mapped to the remote SRv6 SID.
c. Forwards the packet by looking up the routing table of the VPN instance/public instance.
· EVPN VPWS over SRv6 TE policy scenario
a. Removes the outer IPv6 header to obtain the remote SRv6 SID from the inner packet.
b. Searches the remote SRv6 SID and cross-connect mapping table to find the cross-connect mapped to the remote SRv6 SID.
c. Forwards the packet to the AC associated with the cross-connect.
· EVPN VPLS over SRv6 TE policy scenario
a. Removes the outer IPv6 header to obtain the remote SRv6 SID from the inner packet.
b. Searches the remote SRv6 SID and VSI mapping table to find the VSI mapped to the remote SRv6 SID.
c. Forwards the packet according to the MAC address forwarding table of the VSI.
Remote SRv6 SID
As shown in Figure 15, PE 4 receives a BGP route from PE 3. If the SRv6 SID in the BGP route is within the locator protected by the End.M SID on PE 4, PE 4 regards the SRv6 SID as a remote SRv6 SID and generates a mapping between the remote SRv6 SID and the VPN instance/public instance, cross-connect, or VSI.
When the adjacency between PE 4 and PE 3 breaks, PE 4 deletes the BGP route received from PE 3. As a result, the remote SRv6 SID and VPN instance/public instance/cross-connect/VSI mapping will be deleted, resulting in packet loss. To avoid this issue, you can configure the mappings deletion delay time on PE 4 to ensure that traffic is forwarded through PE 4 before PE 1 knows the PE 3 failure and computes a new forwarding path.
Route advertisement
The route advertisement procedure is similar in IP L3VPN, EVPN L3VPN, EVPN VPWS, EVPN VPLS, or IP public network over SRv6 TE policy egress protection scenarios. The following example describes the route advertisement in an IP L3VPN over SRv6 TE policy egress protection scenario.
As shown in Figure 15, the FRR path is generated on P 1 as follows:
1. PE 4 advertises the End.M SID and the protected locator to P 1 through an IS-ISv6 route. Meanwhile, PE 4 generates a local SID entry for the End.M SID.
2. Upon receiving the route that carries the End.M SID and the protected locator, P 1 installs a Mirror FRR backup route into its routing table for the protected locator. The next hop of the route is PE 4. To ensure that traffic can bypass PE 3 and arrive at PE 4 without causing loops, the device must calculate a TI-LFA backup path and append the End.M SID to the TI-LFA backup path's SID list.
On PE 4, a <remote SRv6 SID, VPN instance > mapping entry is generated as follows:
1. Upon receiving the private route from CE 2, PE 3 encapsulates the route as a VPNv4 route and sends it to PE 4. The VPNv4 route carries the SRv6 SID, RT, and RD information.
2. After PE 4 receives the VPNv4 route, it obtains the SRv6 SID and the VPN instance. Then, PE 4 performs longest matching of the SRv6 SID against the locators protected by End.M SIDs. If a match is found, PE 4 uses the SRv6 SID as a remote SRv6 SID and generates a <remote SRv6 SID, VPN instance> mapping entry.
Packet forwarding
The packet forwarding procedure is similar in IP L3VPN, EVPN L3VPN, EVPN VPWS, EVPN VPLS, or IP public network over SRv6 TE policy egress protection scenarios. The following example describes the packet forwarding in an IP L3VPN over SRv6 TE policy egress protection scenario.
Figure 16 Data forwarding in SRv6 egress protection
As shown in Figure 16, traffic is forwarded along the CE 1-PE 1-P 1-PE 3-CE 2 path. When the egress node PE 3 fails, a packet is forwarded as follows:
1. P 1 detects that its next hop (PE 3) is unreachable and thus switches traffic to the Mirror FRR path. In this example, the optimal path between P 1 and PE 4 does not traverse PE 3, and P 1 does not need to encapsulate the TI-LFA FRR SID list into the packet. Therefore, P 1 encapsulates the packet with an IPv6 header whose destination address is the End.M SID, and then forwards the packet to PE 4.
2. PE 4 finds that the packet is destined for its local End.M SID. As instructed by the End.M SID, PE 4 performs the following operations:
a. Removes the outer IPv6 header to obtain the remote SRv6 SID from the inner packet. (The remote SRv6 SID is A100::1 in this example)
b. Searches the remote SRv6 SID and VPN instance mapping table to find the VPN instance mapped to the remote SRv6 SID. (The VPN instance is VPN 1 in this example.)
c. Looks up a route in the routing table of the VPN instance to forward the packet to CE 2.
SRv6 TE policy tasks at a glance
To configure an SRv6 TE policy, perform the following tasks:
1. Configuring an SRv6 TE policy and configure basic settings for the policy:
This task is required when you use PCE to compute SID lists.
c. Configuring a candidate path and the SID lists of the path
d. (Optional.) Enabling strict SID encapsulation for SID lists
e. (Optional.) Configuring dynamic path calculation timers
f. (Optional.) Enabling the device to distribute SRv6 TE policy candidate path information to BGP-LS
g. (Optional.) Shutting down an SRv6 TE policy
2. (Optional.) Configuring BGP to advertise BGP IPv6 SR policy routes
a. Enabling BGP to advertise BGP IPv6 SR policy routes
b. Configuring BGP to redistribute BGP IPv6 SR policy routes
c. (Optional.) Enabling advertising BGP IPv6 SR policy routes to EBGP peers
d. (Optional.) Enabling Router ID filtering
e. (Optional.) Configuring BGP to control BGP IPv6 SR policy route selection and advertisement
f. (Optional.) Maintaining BGP sessions
3. Configuring SRv6 TE policy traffic steering
4. (Optional.) Configuring IPR for SRv6 TE policies
5. (Optional.) Configuring the SRv6 TE policy encapsulation mode
6. (Optional.) Configuring high availability features for SRv6 TE policy
¡ Enabling SBFD for SRv6 TE policies
¡ Configuring the BFD echo packet mode for SRv6 TE policies
¡ Enabling hot standby for SRv6 TE policies
¡ Configuring path switchover and deletion delays for SRv6 TE policies
¡ Setting the delay time for bringing up SRv6 TE policies
¡ Configuring path connectivity verification for SRv6 TE policies
¡ Configuring SRv6 TE policy transit node protection
¡ Configuring SRv6 TE policy egress protection
¡ Configuring candidate path reoptimization for SRv6 TE policies
¡ Configuring flapping suppression for SRv6 TE policies
7. (Optional.) Configuring advanced settings for SRv6 TE policies
¡ Configuring the TTL processing mode of SRv6 TE policies
¡ Configuring SRv6 TE policy CBTS
¡ Configuring a rate limit for an SRv6 TE policy
¡ Enabling the device to drop traffic when an SRv6 TE policy becomes invalid
¡ Specifying the packet encapsulation type preferred in optimal route selection
8. (Optional.) Maintaining an SRv6 TE policy
¡ Enabling SRv6 TE policy logging
¡ Enabling SNMP notifications for SRv6 TE policies
¡ Configuring traffic forwarding statistics for SRv6 TE policies
Creating an SRv6 TE policy
Manually creating an SRv6 TE policy and configuring its attributes
About this task
An SRv6 TE policy is identified by a BSID, color, and end-point.
You can bind a BSID to the policy manually, or set only the color and end-point attributes of the policy so the system automatically assigns a BSID to the policy. If you use both methods, the manually bound BSID takes effect.
Restrictions and guidelines
The configured BSID must be on the locator specified for SRv6 TE policies in SRv6 TE view. Otherwise, the SRv6 TE policy cannot forward packets. For more information about the locator configuration, see "Configuring IPv6 Segment Routing."
Different SRv6 TE policies cannot have the same color and end-point configuration.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Specify a locator for SRv6 TE.
srv6-policy locator locator-name
By default, no locator is specified for SRv6 TE.
5. Enter SRv6 TE policy view.
policy policy-name
6. Configure a BSID for the policy.
binding-sid ipv6 ipv6-address
7. Set the color and end-point attributes.
color color-value end-point ipv6 ipv6-address
By default, the color and end-point attributes of an SRv6 TE policy are not configured.
Automatically creating SRv6 TE policies by using ODN
About this task
When the device receives a BGP route, if the color extended attribute value of the BGP route is the same as the color value of an ODN template, the device automatically creates an SRv6 TE policy and two candidate paths for the policy. The automatically created candidate paths use preferences 100 and 200.
You can specify an IPv6 prefix list to filter BGP routes. The BGP routes permitted by the specified IPv6 prefix list can trigger ODN to create SRv6 TE policies. The BGP routes denied by the specified IPv6 prefix list cannot trigger ODN to create SRv6 TE policies.
An ODN-created SRv6 TE policy is deleted immediately when the matching BGP route is deleted. To avoid packet loss before the new forwarding path is computed, you can configure a proper deletion delay time for the SRv6 TE policy.
Restrictions and guidelines
You need to configure candidate paths for an ODN-created SRv6 TE policy.
· For the ODN-created candidate path preference 200, manually configure the SID lists for the candidate path.
· For the ODN-created candidate path preference 100, use PCE to compute the SID lists for the candidate path.
· Manually create candidate paths that use preferences other than 100 and 200, and then configure the SID lists for the candidate paths.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Specify a locator for SRv6 TE.
srv6-policy locator locator-name
By default, no locator is specified for SRv6 TE.
5. Create an ODN template and enter SRv6-TE-ODN view.
on-demand color color-value
6. (Optional.) Configure the ODN SRv6 TE policy generation policy.
restrict prefix-list-name
By default, a BGP route can trigger ODN to create an SRv6 TE policy when the route's color attribute value is the same as the ODN color.
7. (Optional.) Configure the deletion delay time for ODN-created SRv6 TE policies.
delete-delay delay-time
By default, the deletion delay time for ODN-created SRv6 TE policies is 180000 milliseconds.
Configuring a PCEP session
Restrictions and guidelines
For more information about the PCEP commands, see MPLS commands in MPLS Command Reference.
Discovering PCEs
About this task
You can manually specify a PCE by using the pce static command on a PCC. A PCC sends PCEP connection requests to the discovered PCEs but does not accept requests from the PCEs.
Procedure
1. Enter system view.
system-view
2. Enter PCC view.
pce-client
3. Specify the IP address of the PCE.
pce static ip-address
Enabling the SRv6 capability for a PCC
About this task
To establish a PCEP session that supports SRv6, you need to enable the SRv6 capability on the devices at both sides of the PCEP session.
Procedure
1. Enter system view.
system-view
2. Enter PCC view.
pce-client
3. Enable the SRv6 capability for the PCC device.
pce capability segment-routing ipv6
By default, a PCC device does not have the SRv6 capability.
Configuring PCEP session parameters
About this task
This task allows you to configure parameters for a PCC to establish PCEP sessions to manually specified PCEs.
Procedure
1. Enter system view.
system-view
2. Enter PCC view.
pce-client
3. Set the path computation request timeout time.
pce request-timeout value
By default, the request timeout time is 10 seconds.
4. Set the PCEP session deadtimer.
pce deadtimer value
By default, the PCEP session deadtimer is 120 seconds.
5. Set the keepalive interval for PCEP sessions.
pce keepalive interval
By default, the keepalive interval is 30 seconds.
6. Set the minimum acceptable keepalive interval and the maximum number of allowed unknown messages received from the PCE peer.
pce tolerance { min-keepalive value | max-unknown-messages value }
By default, the minimum acceptable keepalive interval is 10 seconds, and the maximum number of allowed unknown messages in a minute is 5.
7. Configure PCEP session authentication for a peer. Choose one option as needed:
¡ Configure the keychain authentication.
pce peer ip-address keychain keychain-name
¡ Configure the MD5 authentication.
pce peer ip-address md5 { cipher | plain } string
By default, PCEP session authentication is not configured.
For two devices to establish a PCEP session, you must configure the same authentication mode and specify the same key string on both devices.
Configuring a candidate path and the SID lists of the path
Restrictions and guidelines
Do not configure an SRv6 TE policy candidate path to use both manually configured SID lists and PCE-computed SID lists.
Configuring a candidate path to use manually configured SID lists
About this task
Before you specify a SID list for a candidate path, you need to create the SID list and add nodes to the SID list.
After you add nodes to a SID list, the system will sort the nodes in ascending order of node index. The node with the smallest index represents the next hop of the source node on the forwarding path.
To reduce the SRH cost, you can use four 32-bit G-SIDs to represent one normal 128-bit SRv6 SID. In a SID list, you can add a 128-bit SRv6 SID with a COC flavor, indicating that the next node of the current node is a 32-bit G-SID. For more information about G-SIDs, see "Configuring SRv6."
If multiple SRv6 TE policies have a common path, you can configure the common path as an SRv6 TE policy. When you configure the SRv6 TE policies, you can add the BSID of the common SRv6 TE policy to the SID lists of the SRv6 TE policies. In this way, you recurse the SRv6 TE policies to the common SRv6 TE policy, simplifying the SID list configuration.
To use a controller to deploy an SID list that contains G-SID nodes to a forwarding device, perform the following operations on the controller:
· Use the index index-number ipv6 ipv6-address flavor flavor-number lb-length ln-length function-length args-length command on the controller to add the G-SID nodes to the SID list to form an explicit path.
· Deploy the path to the forwarding device through a BGP IPv6 SR policy route.
Then, traffic matching the SID list on the forwarding device will be forwarded to the G-SID nodes in the SID list in sequence.
Restrictions and guidelines
When you add G-SIDs to a SID list, make sure the following conditions are met:
· The SRv6 SID for the previous node of the G-SID must be End(COC32) SID or End.X(COC32) SID.
· The SRv6 SID for the last node does not contain the COC flavor.
If the first SID in the SID list of an SRv6 TE policy is a BSID, note the following restrictions and guidelines:
· Nested SRv6 TE policy recursions are not supported, that is, the first SID in the SID list of the recursion SRv6 TE policy (the SRv6 TE policy with that BSID) cannot be a BSID.
· The first SID cannot be the BSID of this SRv6 TE policy itself.
· Do not configure path connectivity verification for this SRv6 TE policy.
· The BSID cannot be configured as a local BSID or a reverse BSID.
· The traffic statistics, BFD, and SBFD features of this SRv6 TE policy are not affected by the status of those features for the recursion SRv6 TE policy.
· The BFD/SBFD detection time of this SRv6 TE policy cannot be shorter than that of the recursion SRv6 TE policy.
· The path MTU of this SRv6 TE policy cannot be smaller than that of the recursion SRv6 TE policy.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Create a SID list and enter SID list view.
segment-list segment-list-name
5. Add a node to the SID list.
¡ Add a normal 128-bit SRv6 SID.
index index-number ipv6 ipv6-address [ verification ]
¡ Add a 128-bit SRv6 SID with the COC flavor, and specify the common prefix length for the next G_SID.
index index-number coc32 ipv6 ipv6-address common-prefix-length [ verification ]
¡ Add a G-SID node on the controller, and specify the type and flavor of the SRv6 G-SID and the length of each portion in the SRv6 G-SID.
index index-number ipv6 ipv6-address flavor flavor-number lb-length ln-length function-length args-length [ verification ]
6. Return to SRv6 TE view.
quit
7. Enter SRv6 TE policy view.
policy policy-name
8. Create and enter SRv6 TE policy candidate path view.
candidate-paths
9. Set the preference for a candidate path and enter SRv6 TE policy path preference view.
preference preference-value
By default, no candidate path preferences are set.
Each preference represents a candidate path.
10. Specify an explicit path for the candidate path.
explicit segment-list segment-list-name [ local-binding-sid ipv6 ipv6-address | path-mtu mtu-value | reverse-binding-sid ipv6 ipv6-address | weight weight-value ] *
A candidate path can have multiple SID lists.
Configuring a candidate path to create an SID list through affinity attribute-based path calculation
Creating a name-to-bit mapping for an affinity attribute
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Create the constraints mapping and enter its view.
affinity-map
5. Create a name-to-bit mapping for an affinity attribute.
name name bit-position bit-position-number
By default, no name-to-bit mapping is configured for an affinity attribute.
Configuring affinity attribute rules
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enter SRv6 TE policy view.
policy policy-name
5. Enter SRv6 TE policy candidate path view.
candidate-paths
6. Enter SRv6 TE policy candidate path preference view.
preference preference-value
Each preference represents a candidate path.
7. Create SRv6 TE policy constraints and enter constraints view.
constraints
8. Create and enter the affinity attribute view.
affinity
9. Configure affinity attribute rules.
¡ Configure the include-all affinity attribute rule and enter its view.
include-all
¡ Configure the include-any affinity attribute rule and enter its view.
include-any
¡ Configure the exclude-any affinity attribute rule and enter its view.
exclude-any
10. Specify an affinity attribute for an affinity attribute rule.
name name
By default, no affinity attribute is specified for an affinity attribute rule.
Configuring dynamic path calculation based on affinity attribute rule
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enter SRv6 TE policy view.
policy policy-name
5. Enter SRv6 TE policy candidate path view.
candidate-paths
6. Enter SRv6 TE policy candidate path preference view.
preference preference-value
Each preference represents a candidate path.
7. Enable dynamic path calculation and create and enter SRv6 TE policy path preference dynamic view.
dynamic
By default, dynamic path calculation is disabled.
8. Create a metric type and enter its view.
metric
9. Specify a metric.
type { hopcount | igp | latency | te }
By default, no metric is specified. The SRv6 TE policy cannot perform dynamic path calculation.
10. (Optional.) Configure the maximum number of SIDs in an SID list.
sid-limit limit-value
By default, the maximum number of SIDs in an SID list is not configured.
This command limits the number of SIDs in the SID lists for the candidate paths of an SRv6 TE policy during metric-based path calculation.
Configuring a candidate path to create an SID list through Flex-Algo-based path calculation
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enter SRv6 TE policy view.
policy policy-name
5. Enter SRv6 TE policy candidate path view.
candidate-paths
6. Enter SRv6 TE policy candidate path preference view.
preference preference-value
Each preference represents a candidate path.
7. Enable dynamic path calculation and create and enter SRv6 TE policy path preference dynamic view.
dynamic
By default, dynamic path calculation is disabled.
8. Return to SRv6 TE policy candidate path preference view.
quit
9. Create SRv6 TE policy constraints and enter constraints view.
constraints
10. Create the segment constraints and enter its view.
segments
11. Specify a Flex-Algo for an SRv6 TE policy.
sid-algorithm algorithm-id
By default, no Flex-Algo is associated with an SRv6 TE policy.
Configuring a candidate path to use PCE-computed SID lists
Prerequisites
Before you perform this task, configure a PCEP session first.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enter SRv6 TE policy view.
policy policy-name
5. Create and enter SRv6 TE policy candidate path view.
candidate-paths
6. Set the preference for a candidate path and enter SRv6 TE policy path preference view.
preference preference-value
By default, no candidate path preferences are set.
Each preference represents a candidate path.
7. Create and enter SRv6 TE policy path preference dynamic view.
dynamic
8. Enable a candidate path to use PCE to compute the SID lists.
pcep
By default, a candidate path does not use PCE to compute SID lists.
Configuring an ODN-created candidate path to create an SID list through affinity attribute-based path calculation
Creating a name-to-bit mapping for an affinity attribute
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Create the constraints mapping and enter its view.
affinity-map
5. Create a name-to-bit mapping for an affinity attribute.
name name bit-position bit-position-number
By default, no name-to-bit mapping is configured for an affinity attribute.
Configuring affinity attribute rules
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enter SRv6 TE ODN view.
on-demand color color-value
5. Enable dynamic path calculation and create and enter SRv6 TE ODN dynamic view.
dynamic
By default, dynamic path calculation is disabled.
6. Create the affinity attribute rule and enter its view.
affinity { include-all | include-any | exclude-any }
7. Specify an affinity attribute for an affinity attribute rule.
name name
By default, no affinity attribute is specified for an affinity attribute rule.
Configuring dynamic path calculation based on affinity attribute rule
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enter SRv6 TE ODN view.
on-demand color color-value
5. (Optional.) Configure the maximum depth for the SID label stack.
maximum-sid-depth value
By default, the maximum depth of the SID label stack is not configured.
To implement dynamic path calculation for ODN-generated SRv6 TE policies, use this command to control the number of SIDs in the SID lists for the candidate paths of the SRv6 TE policies.
6. Enable dynamic path calculation and create and enter SRv6 TE ODN dynamic view.
dynamic
By default, dynamic path calculation is disabled.
7. Create a metric type and enter its view.
metric
8. Specify a metric.
type { hopcount | igp | latency | te }
By default, no metric is specified. The SRv6 TE policy cannot perform dynamic path calculation.
Configuring an ODN-created candidate path to create an SID list through Flex-Algo-based path calculation
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enter SRv6 TE ODN view.
on-demand color color-value
5. (Optional.) Configure the maximum depth for the SID label stack.
maximum-sid-depth value
By default, the maximum depth of the SID label stack is not configured.
To implement dynamic path calculation for ODN-generated SRv6 TE policies, use this command to control the number of SIDs in the SID lists for the candidate paths of the SRv6 TE policies.
6. Enable dynamic path calculation and create and enter SRv6 TE ODN dynamic view.
dynamic
By default, dynamic path calculation is disabled.
7. Specify a Flex-Algo for an SRv6 TE policy.
sid-algorithm algorithm-id
By default, no Flex-Algo is associated with an SRv6 TE policy.
Configuring an ODN-created candidate path to use PCE-computed SID lists
Prerequisites
Before you perform this task, configure a PCEP session first.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enter SRv6-TE-ODN view.
on-demand color color-value
5. Enter SRv6-TE-ODN dynamic view.
dynamic
6. Enable a candidate path to use PCE to compute the SID lists.
pcep
By default, a candidate path does not use PCE to compute SID lists..
Configuring PCE delegation to create candidate paths and SID lists
About this task
After PCE delegation for an SRv6 TE policy is enabled, the PCC delegates the policy's candidate paths to a PCE. The PCC creates or updates candidate paths according to the creation or update requests received from the PCE.
When the device delegates only part of its SRv6 TE policies to a PCE, the PCE does not have complete SRv6 TE policy candidate path information to calculate global bandwidth information. You can enable the device to report information about the undelegated SRv6 TE policies to the PCE without using the PCE to compute candidate paths for the policies. This feature is referred to as the passive delegation report only feature.
Restrictions and guidelines
You can configure the PCE delegation and passive delegation report only features for all SRv6 TE policies globally in SRv6 TE view or for a specific SRv6 TE policy in SRv6 TE policy view. The policy-specific configuration takes precedence over the global configuration. An SRv6 TE policy uses the global configuration only when it has no policy-specific configuration.
In SRv6 TE view, if you execute both the srv6-policy pce delegation enable command and the srv6-policy pce passive-delegate report-only enable command, the srv6-policy pce passive-delegate report-only enable command takes effect.
In SRv6 TE policy view, if you execute both the pce delegation command and the pce passive-delegate report-only command, the pce passive-delegate report-only command takes effect.
Prerequisites
Before you perform this task, configure a PCEP session first.
Configuring PCE delegation parameters
1. Enter system view.
system-view
2. Enter PCC view.
pce-client
3. Set the delegation priority of a PCE.
pce peer ip-address delegation-priority priority
By default, the delegation priority of a PCE is 65535.
A smaller value represents a higher priority.
4. Set the redelegation timeout interval.
pce redelegation-timeout value
By default, the redelegation timeout interval is 30 seconds.
5. Set the state timeout interval on the PCC.
pce state-timeout value
By default, the state timeout interval is 60 seconds.
Enabling delegation
1. Enter system view.
system-view
2. Enter PCC view.
pce-client
3. Configure the PCEP device type as active stateful or passive stateful.
pcep type { active-stateful | passive-stateful }
By default, the PCEP device type is stateless.
4. Return to system view.
quit
5. Enter SRv6 view.
segment-routing ipv6
6. Enter SRv6 TE view.
traffic-engineering
7. Enable PCE delegation for SRv6 TE policies globally.
srv6-policy pce delegation enable
By default, PCE delegation for SRv6 TE policies is disabled globally.
8. Globally enable the PCC to report candidate information of an SRv6 TE policy to the PCE without delegating the policy to the PCE.
srv6-policy pce passive-delegate report-only enable
By default, this feature is disabled globally.
9. Enter SRv6 TE policy view.
policy policy-name
10. Enable PCE delegation for the SRv6 TE policy.
pce delegation { enable | disable }
By default, an SRv6 TE policy uses the PCE delegation setting configured in SRv6 TE view.
11. Enable the PCC to report candidate information of the SRv6 TE policy to the PCE without delegating the policy to the PCE.
pce passive-delegate report-only { enable | disable }
By default, an SRv6 TE policy uses the passive delegation report only setting configured in SRv6 TE view.
Enabling strict SID encapsulation for SID lists
About this task
The SID list of an SRv6 TE policy can be formed by prefix SIDs and adjacency SIDs. A prefix SID cannot uniquely identify a link. When the links in the network flap frequently, the forwarding paths of the SRv6 TE policy might change. To ensure stability of forwarding paths, perform this task to enable the SRv6 TE policy to include only adjacency SIDs in the calculated SID lists.
Prerequisites
Perform this task on the source node of an SRv6 TE policy.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enable strict SID encapsulation for SID lists.
¡ Execute the following commands in sequence to enable this feature in SRv6 TE policy path preference dynamic view.
policy policy-name
candidate-paths
preference preference-value
dynamic
strict-sid-only enable
¡ Execute the following commands in sequence to enable this feature in SRv6 TE ODN dynamic view.
on-demand color color-value
dynamic
strict-sid-only enable
By default, strict SID encapsulation is disabled for SID lists.
Configuring dynamic path calculation timers
About this task
Perform this task to avoid excessive resource consumption caused by frequent network changes.
If you specify the maximum-interval, minimum-interval, and incremental-interval settings for the command, the following situations will occur:
· For the first path calculation triggered for the SRv6 TE policy, the minimum-interval setting applies.
· For the nth (n > 1) path calculation triggered for the SRv6 TE policy, the device adds a value of incremental-interval × 2n-2 based on the minimum-interval setting. The total value does not exceed the maximum-interval setting.
If the value of minimum-interval + incremental-interval × 2n-2 is larger than or equal to the value of maximum-interval, the device uses the conservative keyword and SRv6 TE policy flapping condition to adjust the path calculation intervals:
· If the conservative keyword is specified:
¡ If SRv6 TE policy flappings occur, the maximum-interval setting applies.
¡ If no SRv6 TE policy flappings occur, the maximum interval applies for once, and then the minimum interval applies.
· If the conservative keyword is not specified:
¡ If SRv6 TE policy flappings occur, the maximum interval applies for three consecutive times, and then the minimum interval applies.
¡ If no SRv6 TE policy flappings occur, the maximum interval applies for once, and then the minimum interval applies.
Restrictions and guidelines
The value of the minimum-interval or incremental-interval argument cannot be greater than the maximum-interval argument.
To increase path calculation frequency for faster path calculation, configure a fixed interval.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Configure the dynamic path calculation timers.
srv6-policy calc-schedule-interval { maximum-interval [ minimum-interval [ incremental-interval [ conservative ] ] ] | millisecond interval }
By default, the maximum, minimum, and incremental intervals for dynamic path calculation are 5 seconds, 50 milliseconds, and 200 milliseconds, respectively.
Enabling the device to distribute SRv6 TE policy candidate path information to BGP-LS
About this task
After this feature is enabled, the device distributes SRv6 TE policy candidate path information to BGP-LS. BGP-LS advertises the SRv6 TE policy candidate path information in routes to meet application requirements.
Prerequisites
Before you configure this feature, enable the device to exchange LS information with the related peer or peer group. For more information about the LS exchange capability, see the BGP LS configuration in Layer 3—IP Routing Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enable the device to distribute SRv6 TE policy candidate path information to BGP-LS.
distribute bgp-ls
By default, the device cannot distribute SRv6 TE policy candidate path information to BGP-LS
Shutting down an SRv6 TE policy
About this task
This feature controls the administrative state of an SRv6 TE policy.
If multiple SRv6 TE policies exist on the device, you can shut down unnecessary SRv6 TE policies to prevent them from affecting traffic forwarding.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enter SRv6 TE policy view.
policy policy-name
5. Shut down the SRv6 TE policy.
shutdown
By default, an SRv6 TE policy is not administratively shut down.
Configuring BGP to advertise BGP IPv6 SR policy routes
Restrictions and guidelines for BGP IPv6 SR policy routes advertisement
For more information about BGP commands, see Layer 3—IP Routing Commands.
Enabling BGP to advertise BGP IPv6 SR policy routes
1. Enter system view.
system-view
2. Configure a global router ID.
router id router-id
By default, no global router ID is configured.
3. Enable a BGP instance and enter its view.
bgp as-number [ instance instance-name ]
By default, BGP is disabled and no BGP instances exist.
4. Configure a peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } as-number as-number
5. Create the BGP IPv6 SR policy address family and enter its view.
address-family ipv6 sr-policy
6. Enable BGP to exchange BGP IPv6 SR policy routing information with the peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } enable
By default, the device cannot use BGP to exchange BGP IPv6 SR policy routing information with a peer or peer group.
Configuring BGP to redistribute BGP IPv6 SR policy routes
About this task
After you configure BGP to redistribute BGP IPv6 SR policy routes, the system will redistribute the local BGP IPv6 SR policy routes to the BGP routing table and advertise the routes to peers. Then, the peers can forward traffic based on the BGP IPv6 SR policy.
Procedure
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP IPv6 SR policy address family view.
address-family ipv6 sr-policy
4. Enable BGP to redistribute routes from BGP IPv6 SR policies.
import-route sr-policy
By default, BGP does not redistribute BGP IPv6 SR policy routes.
Enabling advertising BGP IPv6 SR policy routes to EBGP peers
About this task
By default, BGP IPv6 SR policy routes are advertised among IBGP peers. To advertise BGP IPv6 SR policy routes to EBGP peers, you must perform this task to enable the advertisement capability.
Procedure
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP IPv6 SR policy address family view.
address-family ipv6 sr-policy
4. Enable advertising BGP IPv6 SR policy routes to EBGP peers.
advertise ebgp enable
By default, BGP IPv6 SR policy routes are not advertised to EBGP peers.
Enabling Router ID filtering
About this task
For the device to process only part of the received BGP IPv6 SR policy routes, you can perform this task to enable filtering the routes by Router ID.
This feature enables the device to check the Route Target attribute of a received BGP IPv6 SR policy route. The device accepts the route only if the Route Target attribute contains the Router ID of the local device.
Restrictions and guidelines
To use Router ID filtering, make sure you add Route Target attributes to BGP IPv6 SR policy routes properly by using routing policy or other methods. Otherwise, Router ID filtering might learn or drop BGP IPv6 SR policy routes incorrectly.
Procedure
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP IPv6 SR policy address family view.
address-family ipv6 sr-policy
4. Enable Router ID filtering.
router-id filter
By default, Router ID filtering is disabled.
Configuring BGP to control BGP IPv6 SR policy route selection and advertisement
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP IPv6 SR policy address family view.
address-family ipv6 sr-policy
4. Configure the NEXT_HOP attribute for routes. Choose one option as needed:
¡ Specify the local router as the next hop for routes sent to a peer or peer group.
peer { group-name | ipv6-address [ mask-length ] } next-hop-local
¡ Configure the device to not change the next hop of routes advertised to peers.
peer { group-name | ipv6-address [ prefix-length ] } next-hop-invariable
By default, BGP sets the local router as the next hop for all routes sent to an EBGP peer or peer group. BGP does not set the local router as the next hop for routes sent to an IBGP peer or peer group.
The peer next-hop-local and peer next-hop-invariable commands are mutually exclusive.
5. Allow a local AS number to exist in the AS_PATH attribute of routes from a peer or peer group, and to set the number of times the local AS number can appear.
peer { group-name | ipv6-address [ prefix-length ] } allow-as-loop [ number ]
By default, the local AS number is not allowed to exist in the AS_PATH attribute of routes from a peer or peer group.
6. Specify a preferred value for routes received from a peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } preferred-value value
By default, the preferred value is 0 for routes received from a peer or peer group.
7. Set the maximum number of routes that can be received from a peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } route-limit prefix-number [ { alert-only | discard | reconnect reconnect-time } | percentage-value ] *
By default, the number of routes that can be received from a peer or peer group is not limited.
8. Configure BGP route reflection:
a. Configure the device as a route reflector and specify a peer or peer group as a client.
peer { group-name | ipv6-address [ prefix-length ] } reflect-client
By default, neither the route reflector nor the client is configured.
b. (Optional.) Enable BGP IPv6 SR policy route reflection between clients.
reflect between-clients
By default, route reflection between clients is enabled.
c. (Optional.) Configure the cluster ID for the RR.
reflector cluster-id { cluster-id | ipv4-address }
By default, the RR uses its own router ID as the cluster ID.
9. Specify an IPv6 prefix list to filter routes received from or advertised to a peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } prefix-list ipv6-prefix-list-name { export | import }
By default, no prefix list based filtering is configured.
10. Apply a routing policy to routes incoming from or outgoing to a peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } route-policy route-policy-name { export | import }
By default, no routing policy is applied to routes incoming from or outgoing to a peer or peer group.
11. Advertise the COMMUNITY attribute to a peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } advertise-community
By default, no COMMUNITY attribute is advertised to any peers or peer groups.
12. Advertise the extended community attribute to a peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } advertise-ext-community
By default, no extended community attribute is advertised to any peers or peer groups.
13. Assign a peer or peer group a high priority in BGP route selection.
peer { group-name | ipv6-address [ prefix-length ] } high-priority
By default, a peer or peer group does not have a high priority in BGP route selection.
14. Configure the optimal route selection delay. Choose the following tasks as needed:
¡ Configure the optimal route selection delay timer for all BGP routes in the address family.
route-select delay delay-value
¡ After the neighbor state changes from Down to Up, delay optimal route selection for BGP routes from that neighbor for a specified duration.
route-select suppress on-peer-up milliseconds
By default, optimal route selection is not delayed.
Maintaining BGP sessions
To maintain BGP sessions, execute the following commands in user view:
· Reset BGP sessions for the BGP IPv6 SR policy address family.
reset bgp [ instance instance-name ] { as-number | ipv6-address [ prefix-length ] | all | external | group group-name | internal } ipv6 sr-policy
· Soft-reset BGP sessions for the BGP IPv6 SR policy address family.
refresh bgp [ instance instance-name ] { ipv6-address [ prefix-length ] | all | external | group group-name | internal } { export | import } ipv6 sr-policy
Configuring SRv6 TE policy traffic steering
Configuring the SRv6 TE policy traffic steering mode
Restrictions and guidelines
This feature does not take effect on L2VPN networks.
Prerequisites
To use color-based traffic steering, you need to add the color extended community to IPv6 unicast routes by using routing policy or other methods. For information about the routing policy configuration, see Layer 3—IP Routing Configuration Guide.
To use tunnel policy-based traffic steering, you need to configure a bound tunnel, preferred tunnel, or load sharing tunnel policy that uses an SRv6 TE policy. For more information about the tunnel policy configuration, see MPLS Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Configure the traffic steering mode for SRv6 TE policies.
sr-policy steering { disable | policy-based }
By default, the device steering data packets to SRv6 TE policies based on colors of the packets.
If you specify the policy-based keyword, the device steers traffic based on the bound policy, color, and tunnel load sharing policy in a descending order of priority.
Configuring color-based traffic steering
About this task
To steer traffic to an SRv6 TE policy based on colors, you can configure a color extended community for routes that do not carry a color extended community in the following methods:
· Configure a routing policy to add a color value to routes.
· Configure a default color value.
The color value specified in the routing policy is preferred.
Restrictions and guidelines
The default color value applies only to the VPN routes or public network routes learned from a remote PE.
The default color value is used only for SRv6 TE policy traffic steering. It does not used in route advertisement.
Configuring a routing policy to add a color value to routes
1. Enter system view.
system-view
2. Enter routing policy node view.
route-policy route-policy-name { deny | permit } node node-number
3. Set the color extended community attribute for BGP routes.
apply extcommunity color color [ additive ]
By default, no color extended community attribute is set for BGP routes.
4. Return to system view.
quit
5. Enter BGP instance view.
bgp as-number [ instance instance-name ]
6. Enter a BGP address family view as needed:
¡ Enter BGP IPv4 unicast address family view.
address-family ipv4 [ unicast ]
¡ Enter BGP IPv6 unicast address family view
address-family ipv6 [ unicast ]
¡ Enter BGP VPNv4 address family view.
address-family vpnv4
¡ Enter BGP VPNv6 address family view.
address-family vpnv6
¡ Enter BGP EVPN address family view.
address-family l2vpn evpn
7. Apply the routing policy to filter routes advertised to or received from a peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } route-policy route-policy-name { export | import }
By default, no routing policy is applied to a peer or peer group.
Configuring a default color value for VPN routes
1. Enter system view.
system-view
2. Enter VPN instance view.
ip vpn-instance vpn-instance-name [ index vpn-index ]
3. Enter IPv4 address family view or IPv6 address family view of the VPN instance.
¡ Enter VPN instance IPv4 address family view.
address-family ipv4
¡ Enter VPN instance IPv6 address family view.
address-family ipv6
4. Configure a default color value for L3VPN route recursion to an SRv6 TE policy.
default-color color-value [ evpn ]
By default, no default color is configured for L3VPN route recursion to an SRv6 TE policy.
Configuring a default color value for public network routes
1. Enter system view.
system-view
2. Enter pubic instance view.
ip public-instance
3. Enter public instance IPv4 or IPv6 address family view.
¡ Enter public instance IPv4 address family view
address-family ipv4
¡ Enter public instance IPv6 address family view.
address-family ipv6
4. Configure a default color value for public network route recursion to an SRv6 TE policy.
default-color color-value
By default, no default color value is configured for public network route recursion to an SRv6 TE policy.
Configuring tunnel policy-based traffic steering
Configuring a tunnel policy
1. Enter system view.
system-view
2. Create a tunnel policy and enter tunnel policy view.
tunnel-policy tunnel-policy-name [ default ]
3. Configure the tunnel policy. Choose the following tasks as needed:
¡ Specify an SRv6 TE policy to be bound with the specified destination IPv6 address.
binding-destination dest-ipv6-address srv6-policy { name policy-name | end-point ipv6 ipv6-address color color-value } [ ignore-destination-check ] [ down-switch ]
By default, no SRv6 TE policy is specified for a tunnel policy.
¡ Specify an SRv6 TE policy as a preferred tunnel of the tunnel policy.
preferred-path srv6-policy name sr-policy-name
By default, no preferred tunnel is specified for a tunnel policy.
¡ Configuring SRv6 TE policy load sharing for the tunnel policy.
select-seq srv6-policy load-balance-number number
By default, no load sharing tunnel policy is configured.
For more information about the tunnel policy commands, see MPLS Command Reference.
Specifying the tunnel policy for a VPN instance
1. Enter system view.
system-view
2. Enter a VPN instance view as needed.
¡ Enter VPN instance view.
ip vpn-instance vpn-instance-name
¡ Execute the following commands in sequence to enter VPN instance IPv4 address family view:
ip vpn-instance vpn-instance-name
address-family ipv4
¡ Execute the following commands in sequence to enter VPN instance IPv6 address family view:
ip vpn-instance vpn-instance-name
address-family ipv6
3. Specify a tunnel policy for the VPN instance.
tnl-policy tunnel-policy-name
By default, no tunnel policy is specified for a VPN instance.
For more information about this command, see MPLS L3VPN commands in MPLS Command Reference.
Specifying the tunnel policy for a PW
1. Enter system view.
system-view
2. Enter cross-connect group view.
xconnect-group group-name
3. Enter cross-connect view.
connection connection-name
4. Create an EVPN PW and specify a tunnel policy for this PW.
evpn local-service-id local-service-id remote-service-id remote-service-id tunnel-policy tunnel-policy-name
Specifying the tunnel policy for an EVPN instance
1. Enter system view.
system-view
2. Enter VSI view.
vsi vsi-name
3. Enter EVPN instance view.
evpn encapsulation srv6
4. Specify a tunnel policy for the EVPN instance.
tunnel-policy tunnel-policy-name
By default, no tunnel policy is specified for an EVPN instance.
For more information about this command, see EVPN Command Reference.
Configuring DSCP-based traffic steering
About this task
Each SRv6 TE policy in an SRv6 TE policy group has a different color attribute value. By configuring color-to-DSCP mappings for an SRv6 TE policy group, you associate DSCP values to SRv6 TE policies. This allows IPv6 packets containing a specific DSCP value to be steered to the corresponding SRv6 TE policy for further forwarding.
Restrictions and guidelines
You can map the color values of only valid SRv6 TE policies to DSCP values.
You can configure color-to-DSCP mappings separately for the IPv4 address family and IPv6 address family. For a specific address family, a DSCP value can be mapped to only one color value.
Use the color match dscp default command to specify the default SRv6 TE policy for an address family. If no SRv6 TE policy in an SRv6 TE policy group matches a specific DSCP value, the default SRv6 TE policy is used to forward packets containing the DSCP value. Only one default SRv6 TE policy can be specified for an address family.
When the device receives an IPv4 or IPv6 packet that does not match any color-to-DSCP mapping, the device selects a valid SRv6 TE policy for the packet in the following order:
1. The default SRv6 TE policy specified for the same address family as the packet.
2. The default SRv6 TE policy specified for the other address family.
3. Handles the packet according to whether the drop-upon-mismatch enable command is used.
¡ If the drop-upon-mismatch enable command is used, the device discards the packet.
¡ If the drop-upon-mismatch enable command is not used but color-to-DSCP mappings are configured in the same address family as the packet, the device searches for the color-to-DSCP mapping with the smallest DSCP value that is mapped to a valid SRv6 TE policy. The device will use that SRv6 TE policy to forward the packet.
¡ If the drop-upon-mismatch enable command is not used but color-to-DSCP mappings are configured in the other address family, the device searches for the color-to-DSCP mapping with the smallest DSCP value that is mapped to a valid SRv6 TE policy. The device will use that SRv6 TE policy to forward the packet.
4. The device performs an IPv6 routing table lookup to forward the packet that does not match any of the previous SRv6 TE policies.
Manually creating an SRv6 TE policy group
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Create an SRv6 TE policy group and enter its view.
policy-group group-id
5. Configure the end-point IPv6 address for the SRv6 TE policy group.
end-point ipv6 ipv6-address
By default, no end-point IPv6 address is configured for the SRv6 TE policy group.
The SRv6 TE policies identified by the colors in the SRv6 TE policy group must use the same end-point IPv6 address as the SRv6 TE policy group.
6. (Optional.) Create the color value for the SRv6 TE policy group.
group-color color-value
By default, the color value is not configured for an SRv6 TE policy group.
7. (Optional.) Configure a BSID for the SRv6 TE policy group.
binding-sid ipv6 ipv6-address
By default, no BSID is configured for an SRv6 TE policy group.
8. (Optional.) Enable the feature of discarding packets that do not match any valid SRv6 TE policy or SRv6 BE path.
drop-upon-mismatch enable
By default, this feature is disabled.
9. Create color-to-DSCP mappings for the SRv6 TE policy group.
color color-value match dscp { ipv4 | ipv6 } dscp-value-list
color color-value match dscp { ipv4 | ipv6 } default
By default, no color-to-DSCP mappings are created for the SRv6 TE policy group.
DSCP-based traffic steering cannot function if no color-to-DSCP mappings are created.
Automatically creating an SRv6 TE policy group by ODN
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Create an ODN template for creating SRv6 TE policy groups and enter SRv6 TE ODN policy group view.
on-demand-group color color-value
5. (Optional.) Configure the description of the SRv6 TE policy group ODN template.
description text
By default, the description of the SRv6 TE policy group ODN template is not configured.
6. (Optional.) Enable the feature of discarding packets that do not match any valid SRv6 TE policy or SRv6 BE path.
drop-upon-mismatch enable
By default, this feature is disabled.
7. Create the DSCP forward type and enter its view.
forward-type dscp
8. Create color-to-DSCP mappings for the SRv6 TE policy group ODN template.
color color-value match dscp { ipv4 | ipv6 } dscp-value-list
color color-value match dscp { ipv4 | ipv6 } default
By default, no color-to-DSCP mappings are created for the SRv6 TE policy group ODN template.
This command is required to implement DSCP-based traffic steering.
Steering traffic to an SRv6 TE policy group
1. Enter system view.
system-view
2. Configure traffic steering to an SRv6 TE policy group.
a. Create a tunnel policy and enter tunnel policy view.
tunnel-policy tunnel-policy-name [ default ]
b. Bind the SRv6 TE policy group to a destination IP address.
binding-destination dest-ip-address sr-policy group sr-policy-group-id [ ignore-destination-check ] [ down-switch ]
By default, a tunnel policy does not bind any SRv6 TE policy group to a destination IP address.
For more information about the command, see tunnel policy commands in MPLS Command Reference.
c. Configure color-based traffic steering.
For more information, see "Configuring color-based traffic steering."
Specify a color value as the color extended community attribute of BGP routes in the routing policy according to the creation method of the SRv6 TE policy group.
- If the SRv6 TE policy group is manually created, the specified color value must be the color value of the SRv6 TE policy group.
- If the SRv6 TE policy group is automatically created by ODN, the specified color value must be the color value of the ODN template.
Configuring 802.1p-based traffic steering
About this task
Each SRv6 TE policy in an SRv6 TE policy group has a different color attribute value. By configuring color-to-802.1p mappings for an SRv6 TE policy group, you associate 802.1p values to SRv6 TE policies. This allows packets containing a specific 802.1p value to be steered to the corresponding SRv6 TE policy for further forwarding.
Use the color match dot1p default command to specify the default SRv6 TE policy for an SRv6 TE policy group. If no SRv6 TE policy in an SRv6 TE policy group matches a specific 802.1p value, the default SRv6 TE policy is used to forward packets containing the 802.1p value.
When the device receives a packet that does not match any color-to-802.1p mapping, the device uses the following procedure to forward the packet:
1. Uses the default SRv6 TE policy to forward the packet if that SRv6 TE policy is valid.
2. Handles the packet depending on whether the drop-upon-mismatch enable command is used.
¡ If the drop-upon-mismatch enable command is used, the device discards the packet.
¡ If the drop-upon-mismatch enable command is not used, the device uses the SRv6 TE policy mapped to the smallest 802.1p value to forward the packet in case that the SRv6 TE policy is valid.
3. The device performs an IPv6 routing table lookup to forward the packet if the packet does not meet any of the previous conditions.
Restrictions and guidelines
You can map the color values of only valid SRv6 TE policies to 802.1p values. For an SRv6 TE policy group, an 802.1p value can be mapped to only one color value.
Only one default SRv6 TE policy can be specified for an SRv6 TE policy group.
Manually creating an SRv6 TE policy group
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Create an SRv6 TE policy group and enter its view.
policy-group group-id
5. Configure the endpoint IPv6 address for the SRv6 TE policy group.
end-point ipv6 ipv6-address
By default, no endpoint IPv6 address is configured for the SRv6 TE policy group.
The SRv6 TE policy associated with each color value in the SRv6 TE policy group must use the same endpoint IPv6 address as the SRv6 TE policy group.
6. (Optional.) Create the color value for the SRv6 TE policy group.
group-color color-value
By default, the color value is not configured for an SRv6 TE policy group.
7. (Optional.) Configure a BSID for the SRv6 TE policy group.
binding-sid ipv6 ipv6-address
By default, no BSID is configured for an SRv6 TE policy group.
8. (Optional.) Enable the feature of discarding packets that do not match any valid SRv6 TE policy or SRv6 BE path.
drop-upon-mismatch enable
By default, this feature is disabled.
9. Specify the Dot1p forward type for the SRv6 TE policy group.
forward-type dot1p
By default, DSCP-based traffic steering is used for packets that match an SRv6 TE policy group.
10. Create color-to-802.1p mappings for the SRv6 TE policy group.
color color-value match dot1p dot1p-value-list
color color-value match dot1p default
By default, no color-to-802.1p mappings are created for an SRv6 TE policy group.
Steering traffic to an SRv6 TE policy group
1. Enter system view.
system-view
2. Configure traffic steering to an SRv6 TE policy group.
a. Create a tunnel policy and enter its view.
tunnel-policy tunnel-policy-name [ default ]
b. Bind the SRv6 TE policy group to a destination IP address.
binding-destination dest-ipv6-address srv6-policy group srv6-policy-group-id [ ignore-destination-check ] [ down-switch ]
By default, a tunnel policy does not bind any SRv6 TE policy group to a destination IP address.
For more information about the command, see tunnel policy commands in MPLS Command Reference.
c. Configure color-based traffic steering.
For more information, see "Configuring color-based traffic steering."
Specify the color value of the SRv6 TE policy group as the color extended community attribute of BGP routes in the routing policy
Configuring service class-based traffic steering
About this task
Service class is a type of local ID on the device. You can use the remark service-class command to assign a service class to traffic. Once the traffic is steered to an SRv6 TE policy group for forwarding, the device matches the service class value of the traffic with the service class mappings in the SRv6 TE policy group. If a matching mapping is found, the device forwards the traffic through the SRv6 TE policy with the color attribute value in the mapping or in SRv6 BE mode.
If the service class value in a packet matches a color-to-service class mapping, and the SRv6 TE policy with the color attribute value in the mapping is valid, the device uses the SRv6 TE policy to forward the packet.
If the service class value in a packet matches an SRv6 BE-to-service class mapping, and the SRv6 BE mode is valid, the device forwards the packet in SRv6 BE mode. In this mode, the device encapsulates a new IPv6 header to the packet, with the destination address in the new IPv6 header set to the VPN SID assigned to public or private network routes by the egress node of the SRv6 TE policy group. Then, the device performs an IPv6 routing table lookup to forward the encapsulated packet.
· If the VPN SID is reachable, the SRv6 BE mode is valid and the packet can be forwarded in SRv6 BE mode.
· If the VPN SID is unreachable, the SRv6 BE mode is invalid and the packet cannot be forwarded in SRv6 BE mode.
You can use the best-effort match service-class default command to specify SRv6 BE mode as a backup for SRv6 TE policies. When none of the specified SRv6 TE policies are valid, the device will forward traffic in SRv6 BE mode.
When service class-based traffic steering is used, the device uses the following process to forward a packet:
1. Matches the service class value in the packet with the mappings configured by using the color match service-class and best-effort match service-class commands. If a match is found, the device uses the matching SRv6 TE policy to forward the packet or forwards the packet in SRv6 BE mode.
2. Uses the default SRv6 TE policy specified by using the color match service-class default command to forward the packet in the following situations:
¡ The service class value in the packet does not match an SRv6 TE policy or the SRv6 BE mode.
¡ The service class value in the packet matches an SRv6 TE policy or the SRv6 BE mode. However, the matching SRv6 TE policy or the SRv6 BE mode is invalid.
3. Forwards the packet in SRv6 BE mode if both of the following requirements are met:
¡ No default SRv6 TE policy is specified by using the color match service-class default command, or the default SRv6 TE policy is invalid.
¡ The best-effort match service-class default command is used and the SRv6 BE mode is valid.
4. Handles the packet according to whether the drop-upon-mismatch enable command is used if the best-effort match service-class default command is not used or the SRv6 BE path is invalid.
¡ If the drop-upon-mismatch enable command is used, the device discards the packet.
¡ If the drop-upon-mismatch enable command is not used, the device uses the SRv6 TE policy mapped to the smallest service class value to forward the packet in case that the SRv6 TE policy is valid.
5. The device performs an IPv6 routing table lookup to forward the packet if the packet does not meet any of the previous conditions.
Restrictions and guidelines
Only one default SRv6 TE policy can be specified for an SRv6 TE policy group.
For an SRv6 TE policy group, a service class value can be mapped only to the SRv6 BE mode or to one SRv6 TE policy.
Manually creating an SRv6 TE policy group
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Create an SRv6 TE policy group and enter its view.
policy-group group-id
5. Configure the endpoint IPv6 address for the SRv6 TE policy group.
end-point ipv6 ipv6-address
By default, no endpoint IPv6 address is configured for an SRv6 TE policy group.
The SRv6 TE policy associated with each color value in the SRv6 TE policy group must use the same endpoint IPv6 address as the SRv6 TE policy group.
6. (Optional.) Create the color value for the SRv6 TE policy group.
group-color color-value
By default, the color value is not configured for an SRv6 TE policy group.
7. (Optional.) Configure a BSID for the SRv6 TE policy group.
binding-sid ipv6 ipv6-address
By default, no BSID is configured for an SRv6 TE policy group.
8. (Optional.) Enable the feature of discarding packets that do not match any valid SRv6 TE policy or SRv6 BE path.
drop-upon-mismatch enable
By default, this feature is disabled.
9. Specify the service class forward type for the SRv6 TE policy group.
forward-type service-class
By default, DSCP-based traffic steering is used for packets that match an SRv6 TE policy group.
10. Create color-to-service class mappings for the SRv6 TE policy group.
color color-value match service-class service-class-value-list
color color-value match service-class default
By default, no color-to-service class mappings are created for an SRv6 TE policy group.
11. Specify service class values with which traffic will be forwarded in SRv6 BE mode.
best-effort match service-class service-class-value-list
best-effort match service-class default
By default, no service class values are specified for the device to forward traffic in SRv6 BE mode.
Automatically creating an SRv6 TE policy group by ODN
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Create an ODN template for creating SRv6 TE policy groups and enter SRv6 TE ODN policy group view.
on-demand-group color color-value
5. (Optional.) Configure the description of the SRv6 TE policy group ODN template.
description text
By default, no description is configured for an SRv6 TE policy group ODN template.
6. (Optional.) Enable the feature of discarding packets that do not match any valid SRv6 TE policy or SRv6 BE path.
drop-upon-mismatch enable
By default, this feature is disabled.
7. Create the service class forward type and enter its view.
forward-type service-class
8. Create color-to-service class mappings for the SRv6 TE policy group ODN template.
color color-value match service-class service-class-value-list
color color-value match service-class default
By default, no color-to-service class mappings are created for an SRv6 TE policy group ODN template.
9. Specify service class values with which traffic will be forwarded in SRv6 BE mode.
best-effort match service-class service-class-value-list
best-effort match service-class default
By default, no service class values are specified for the device to forward traffic in SRv6 BE mode.
Steering traffic to an SRv6 TE policy group
1. Enter system view.
system-view
2. Configure traffic steering to an SRv6 TE policy group.
¡ Execute the following commands in sequence to configure a tunnel policy to steer traffic to an SRv6 TE policy group:
- Create a tunnel policy and enter tunnel policy view.
tunnel-policy tunnel-policy-name [ default ]
- Bind an SRv6 TE policy group to a destination IP address.
binding-destination dest-ipv6-address srv6-policy group srv6-policy-group-id [ ignore-destination-check ] [ down-switch ]
By default, a tunnel policy does not bind any SRv6 TE policy group to a destination IP address.
For more information about the commands, see tunnel policy commands in MPLS Command Reference.
¡ Configure color-based traffic steering.
For more information, see "Configuring color-based traffic steering."
Specify a color value as the color extended community attribute of BGP routes in the routing policy according to the creation method of the SRv6 TE policy group.
- If the SRv6 TE policy group is manually created, the specified color value must be the color value of the SRv6 TE policy group.
- If the SRv6 TE policy group is automatically created by ODN, the specified color value must be the color value of the ODN template.
Configuring TE class ID-based traffic steering
About this task
When service packets are steered to an SRv6 TE policy group and the SRv6 TE policy group uses TE class ID-based traffic steering, the device matches the TE class ID in the packets with the mappings between TE class IDs and forwarding policies. If a matching mapping is found, the device forwards the packets according to the matching forwarding policy. The device selects a matching forwarding policy as follows:
· If the TE class ID in a packet is mapped to a color attribute value, the device steers the packet to the SRv6 TE policy containing the color attribute value.
· If the TE class ID in a packet is mapped to an IPR policy, the device uses the path selection policy defined in the IPR policy to steer the packet to the optimal SRv6 TE policy for forwarding.
· If the TE class ID in a packet is mapped to the SRv6 BE mode, the device forwards the packet in SRv6 BE mode. In this mode, the device encapsulates a new IPv6 header in the packet and looks up the IPv6 routing table to forward the packet.
· The device uses the default forwarding policy to forward the following packets after the packets are steered to the SRv6 TE policy group for forwarding:
¡ The packets that do not have a TE class ID.
¡ The packets that have a TE class ID not mapped to any forwarding policy specified by using the index te-class match command.
¡ The packets that have a TE class ID mapped to an invalid forwarding policy.
When packets are forwarded according to the default forwarding policy, the device selects a forwarding method in the following order:
1. If a color attribute value or an IPR policy is specified in the default forwarding policy and the SRv6 TE policy used to forward the packets are valid, the device steers the packets to that SRv6 TE policy for forwarding.
2. If the SRv6 BE mode is specified in the default forwarding policy and the SRv6 BE mode is valid, the device encapsulates a new IPv6 header to the packets and looks up the IPv6 routing table to forward the packets.
3. Handles the packet depending on whether the drop-upon-mismatch enable command is used.
¡ If the drop-upon-mismatch enable command is used, the device discards the packet.
¡ If the drop-upon-mismatch enable command is not used, the device searches for the TE class ID-to-forwarding policy mapping with the smallest index value and a valid forwarding policy. The device will use the SRv6 TE policy pointed by the mapping to forward the packet or forward the packet in SRv6 BE mode. If no mappings are configured between TE class IDs and SRv6 TE policies or IPR policies or between TE class IDs and the SRv6 BE mode in the SRv6 TE policy group, or the mapping with the smallest index value is invalid, the device proceeds to the next step.
4. Performs an IPv6 routing table lookup to forward the packets if the packets do not meet any of the previous conditions.
Restrictions and guidelines
One TE class ID can be associated only with one index value.
If you execute the index te-class match command multiple times to configure mappings with the same index value, only the most recent configuration takes effect.
One TE class ID can be mapped only to one forwarding policy. For example,if TE class ID 10 has been mapped to IPR policy ipr1, it cannot be mapped to any other IPR policy, an SRv6 TE policy, or the SRv6 BE mode. If you map one TE class ID to multiple forwarding policies, only the most recent configuration takes effect.
As a best practice, configure different endpoint addresses for different SRv6 TE policy groups. If you configure the same endpoint address for multiple SRv6 TE policy groups, SRv6 TE policies with that endpoint address will belong to multiple SRv6 TE policy groups.
You can configure a maximum of two forwarding methods in the default forwarding policy. However, IPR forwarding and SRv6 TE policy forwarding cannot coexist.
Manually creating an SRv6 TE policy group
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Create an SRv6 TE policy group and enter its view.
policy-group group-id
5. Configure the endpoint IPv6 address for the SRv6 TE policy group.
end-point ipv6 ipv6-address
By default, no endpoint IPv6 address is configured for an SRv6 TE policy group.
The SRv6 TE policy associated with each color value in the SRv6 TE policy group must use the same endpoint IPv6 address as the SRv6 TE policy group.
6. (Optional.) Create the color value for the SRv6 TE policy group.
group-color color-value
By default, the color value is not configured for an SRv6 TE policy group.
7. (Optional.) Configure the BSID for the SRv6 TE policy group.
binding-sid ipv6 ipv6-address
By default, no BSID is configured for an SRv6 TE policy group.
8. (Optional.) Enable the feature of discarding packets that do not match any valid SRv6 TE policy or SRv6 BE path.
drop-upon-mismatch enable
By default, this feature is disabled.
9. Create the TE class forward type and enter its view.
forward-type te-class
By default, DSCP-based traffic steering is used for packets that match an SRv6 TE policy group.
10. Configure a mapping between a TE class ID and an SRv6 TE policy, an IPR policy, or the SRv6 BE mode.
index index-value te-class te-class-id match { best-effort | ipr-policy ipr-name | srv6-policy color color-value }
By default, no mapping is configured between a TE class ID and an SRv6 TE policy, an IPR policy, or the SRv6 BE mode.
11. (Optional.) Configure the default forwarding policy for TE class ID-based traffic steering.
default match best-effort
default match { ipr-policy ipr-name | srv6-policy color color-value }
By default, the default forwarding policy is not configured for TE class ID-based traffic steering.
Automatically creating an SRv6 TE policy group by ODN
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Create an ODN template for creating SRv6 TE policy groups and enter SRv6 TE ODN policy group view.
on-demand-group color color-value
5. (Optional.) Configure the description of the SRv6 TE policy group ODN template.
description text
By default, no description is configured for an SRv6 TE policy group ODN template.
6. (Optional.) Enable the feature of discarding packets that do not match any valid SRv6 TE policy or SRv6 BE path.
drop-upon-mismatch enable
By default, this feature is disabled.
7. Create the TE class forward type and enter its view.
forward-type te-class
8. Configure a mapping between a TE class ID and an SRv6 TE policy, an IPR policy, or the SRv6 BE mode.
index index-value te-class te-class-id match { best-effort | ipr-policy ipr-name | srv6-policy color color-value }
By default, no mapping is configured between a TE class ID and an SRv6 TE policy, an IPR policy, or the SRv6 BE mode.
9. (Optional.) Configure the default forwarding policy for TE class ID-based traffic steering.
default match best-effort
default match { ipr-policy ipr-name | srv6-policy color color-value }
By default, the default forwarding policy is not configured for TE class ID-based traffic steering.
Steering traffic to an SRv6 TE policy group
1. Enter system view.
system-view
2. Configure traffic steering to an SRv6 TE policy group.
¡ Execute the following commands in sequence to configure a tunnel policy to steer traffic to an SRv6 TE policy group:
- Create a tunnel policy and enter tunnel policy view.
tunnel-policy tunnel-policy-name [ default ]
- Bind an SRv6 TE policy group to a destination IP address.
binding-destination dest-ipv6-address srv6-policy group srv6-policy-group-id [ ignore-destination-check ] [ down-switch ]
By default, a tunnel policy does not bind any SRv6 TE policy group to a destination IP address.
For more information about the commands, see tunnel policy commands in MPLS Command Reference.
¡ Configure color-based traffic steering.
For more information, see "Configuring color-based traffic steering."
Specify a color value as the color extended community attribute of BGP routes in the routing policy according to the creation method of the SRv6 TE policy group.
Configuring static route-based traffic steering
Restrictions and guidelines
After you configure this feature on a public IP over SRv6 network, execute the route-replicate command in public instance IPv4/IPv6 address family view to replicate the routes of the specified VPN instance to the public network. The public network then can use the VPN routes to forward user traffic.
Procedure
1. Enter system view.
system-view
2. Configure static route recursion to an SRv6 TE policy:
¡ Configure IPv4 static route recursion to an SRv6 TE policy:
Public network:
ip route-static dest-address { mask-length | mask } srv6-policy { color color-value end-point ipv6 ipv6-address | name policy-name } [ sid sid ] [ preference preference ] [ tag tag-value ] [ description text ]
VPN:
ip route-static vpn-instance s-vpn-instance-name dest-address { mask-length | mask } srv6-policy { color color-value end-point ipv6 ipv6-address | name policy-name } [ sid sid ] [ preference preference ] [ tag tag-value ] [ description text ]
By default, no IPv4 static route is configured.
For more information, see static routing commands in Layer 3—IP Routing Command Reference.
¡ Configure IPv6 static route recursion to an SRv6 TE policy:
Public network:
ipv6 route-static ipv6-address prefix-length srv6-policy { color color-value end-point ipv6 ipv6-address | name policy-name } [ sid sid ] [ preference preference ] [ tag tag-value ] [ description text ]
VPN:
ipv6 route-static vpn-instance s-vpn-instance-name ipv6-address prefix-length srv6-policy { color color-value end-point ipv6 ipv6-address | name policy-name } [ sid sid ] [ preference preference ] [ tag tag-value ] [ description text ]
By default, no IPv6 static route is configured.
For more information, see IPv6 static routing commands in Layer 3—IP Routing Command Reference.
Configuring QoS policy-based traffic steering
About this task
To resolve congestion for certain IPv6 public network traffic, you can create a traffic class to identify traffic, and redirect matching traffic to an SRv6 TE policy based on endpoint and color. If traffic fails to match the redirection rule or the SRv6 TE policy fails, the traffic class becomes invalid, and the traffic is forwarded according to IPv6 routing table lookup.
Restrictions and guidelines
For more information about QoS policy commands, see QoS commands in ACL and QoS Command Reference.
Procedure
a. Enter system view.
system-view
b. Create a traffic class and enter traffic class view.
traffic classifier classifier-name [ operator { and | or } ]
c. Configure a match criterion.
if-match [ not ] match-criteria
By default, no match criterion is configured.
For more information, see the if-match command in ACL and QoS Command Reference.
a. Create a traffic behavior and enter traffic behavior view.
traffic behavior behavior-name
b. Redirect matching traffic to an SRv6 TE policy.
redirect srv6-policy endpoint color [ { sid | vpnsid } sid ]
By default, no action is configured for a traffic behavior.
a. Create a QoS policy and enter QoS policy view.
qos policy policy-name
b. Associate a traffic class with a traffic behavior to create a class-behavior association in the QoS policy.
classifier classifier-name behavior behavior-name
By default, a traffic class is not associated with a traffic behavior.
c. Return to system view.
quit
d. Apply the QoS policy.
For more information, see QoS policy configuration in ACL and QoS Configuration Guide.
By default, the QoS policy is not applied.
Configuring Flowspec rule-based traffic steering
Creating and activating an IPv6 Flowspec rule
1. Enter system view.
system-view
2. Create an IPv6 Flowspec rule.
flow-route flowroute-name ipv6
3. Configure a match criterion.
if-match match-criteria
4. Redirect packets to an SRv6 TE policy.
apply redirect next-hop ipv6-address color color [ sid sid-value ]
By default, no action is configured.
5. Commit the match criterion and action.
commit
By default, match criteria and actions are not committed.
Applying an IPv6 Flowspec rule to the public network
1. Enter system view.
system-view
2. Enter Flowspec view.
flowspec
3. Create a Flowspec IPv6 address family for the public network and enter its view.
address-family ipv6
4. Apply an IPv6 Flowspec rule to the public network. Choose one option as needed:
¡ Apply an IPv6 Flowspec rule.
flow-route flowroute-name
By default, no IPv6 Flowspec rule is applied to the public network.
¡ Apply an IPv6 Flowspec rule and associate it with a Flowspec interface group.
flow-route flowroute-name flow-interface-group group-id
By default, no Flowspec interface group is associated with an IPv6 Flowspec rule.
Applying an IPv6 Flowspec rule to a VPN instance
1. Enter system view.
system-view
2. Configure a VPN instance.
a. Create a VPN instance and enter VPN instance view.
ip vpn-instance vpn-instance-name
b. Configure an RD for the VPN instance.
route-distinguisher route-distinguisher
By default, no RD is configured for a VPN instance.
c. Configure route targets for the VPN instance.
vpn-target { vpn-target&<1-8> [ both | export-extcommunity | import-extcommunity ] }
By default, no route targets are configured.
For more information about the ip vpn-instance, route-distinguisher, and vpn-target commands, see MPLS L3VPN commands in MPLS Command Reference.
3. Enter the IPv6 Flowspec address family view of the VPN instance.
address-family ipv6 flowspec
4. Configure an RD for the IPv6 Flowspec address family.
route-distinguisher route-distinguisher
By default, no RD is configured for the IPv6 Flowspec address family.
5. Configure route targets for the IPv6 Flowspec address family.
vpn-target vpn-target&<1-8> [ both | export-extcommunity | import-extcommunity ]
By default, no route targets are configured for the IPv6 Flowspec address family.
The route targets configured must be the same as the route targets configured previously for the VPN instance.
6. Execute the quit command twice to return to system view.
7. Enter Flowspec view.
flowspec
8. Create a Flowspec IPv6 address family and associate the address family with the VPN instance.
address-family ipv6 vpn-instance vpn-instance-name
9. Apply an IPv6 Flowspec rule to the Flowspec IPv6 VPN instance address family. Choose one option as needed:
¡ Apply an IPv6 Flowspec rule.
flow-route flowroute-name
By default, no IPv6 Flowspec rule is applied to a Flowspec IPv6 VPN instance address family.
¡ Apply an IPv6 Flowspec rule and associate it with a Flowspec interface group.
flow-route flowroute-name flow-interface-group group-id
By default, no Flowspec interface group is associated with an IPv6 Flowspec rule.
Enabling BGP to distribute IPv6 Flowspec rules
1. Enter system view.
system-view
2. Enter BGP instance view:
bgp as-number [ instance instance-name ]
3. Enter BGP IPv6 Flowspec address family view, BGP-VPN IPv6 Flowspec address family view, or BGP VPNv6 Flowspec address family view:
¡ Enter BGP IPv6 Flowspec address family view to distribute public network IPv6 Flowspec rules:
address-family ipv6 flowspec
¡ Enter BGP-VPN IPv6 Flowspec address family view to distribute private network IPv6 Flowspec rules:
ip vpn-instance vpn-instance-name
address-family ipv6 flowspec
¡ Enter BGP VPNv6 Flowspec address family view to distribute VPNv6 Flowspec rules:
address-family vpnv6 flowspec
4. Enable BGP Flowspec peers to exchange routing information.
peer { group-name | ipv4-address [ mask-length ] | ipv6-address [ prefix-length ] } enable
By default, BGP Flowspec peers cannot exchange routing information.
Enabling automatic route advertisement for an SRv6 TE policy
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enter SRv6 TE policy view.
policy policy-name
5. Enable automatic route advertisement for the SRv6 TE policy.
autoroute enable [ isis | ospfv3 ]
By default, automatic route advertisement is disabled for an SRv6 TE policy.
6. Configure an autoroute metric for the SRv6 TE policy.
autoroute metric { absolute value | relative value }
By default, the autoroute metric of an SRv6 TE policy equals its IGP metric.
7. Return to system view.
quit
quit
quit
8. Include the SRv6 TE policy in IGP computation:
¡ Execute the following commands in sequence to enable automatic route advertisement for IS-IS SRv6 TE policies.
isis [ process-id ] [ vpn-instance vpn-instance-name ]
address-family ipv6 [ unicast ]
srv6-policy autoroute enable [ level-1 | level-2 ]
¡ Execute the following commands in sequence to enable automatic route advertisement for OSPFv3 SRv6 TE policies.
ospfv3 [ process-id | vpn-instance vpn-instance-name ] *
srv6-policy autoroute enable
By default, automatic route advertisement for SRv6 TE policies is disabled for IPv6 IS-IS and OSPFv3.
Configuring the SRv6 TE policy encapsulation mode
About this task
When the device forwards a packet through an SRv6 TE policy, it must encapsulate that packet with the SID list of the SRv6 TE policy. Supported encapsulation modes include:
· Encaps—Normal encapsulation mode. It adds a new IPv6 header and an SRH to the original packets. All SIDs in the SID list of the SRv6 TE policy are encapsulated in the SRH. The destination IPv6 address in the new IPv6 header is the first SID in the SID list of the SRv6 TE policy. The source IPv6 address is the IPv6 address specified by using the encapsulation source-address command.
· Encaps.Red—Reduced mode of normal encapsulation. It adds a new IPv6 header and an SRH to the original packets. The first SID in the SID list of the SRv6 TE policy is not encapsulated in the SRH to reduce the SRH length. All other SIDs in the SID list are encapsulated in the SRH. The destination IPv6 address in the new IPv6 header is the first SID in the SID list of the SRv6 TE policy. The source IPv6 address is the IPv6 address specified by using the encapsulation source-address command.
· Insert—Insertion mode. It inserts an SRH after the original IPv6 header. All SIDs in the SID list of the SRv6 TE policy are encapsulated in the SRH. The destination IPv6 address in the original IPv6 header is changed to the first SID in the SID list of the SRv6 TE policy. The source IPv6 address in the original IPv6 header is not changed.
· Insert.Red—Reduced insertion mode. It inserts an SRH after the original IPv6 header. The first SID in the SID list of the SRv6 TE policy is not encapsulated in the SRH to reduce the SRH length. All other SIDs in the SID list are encapsulated in the SRH. The destination IPv6 address in the original IPv6 header is changed to the first SID in the SID list of the SRv6 TE policy. The source IPv6 address in the original IPv6 header is not changed.
If traffic is steered to an SRv6 TE policy and the SRv6 SID of the ingress node is an End.X SID, the device does not encapsulate the End.X SID into the SRH by default.
To obtain complete SRv6 forwarding path information from the SRH of packets, you can configure the device to encapsulate the local End.X SID in the SRH.
Restrictions and guidelines
You can configure the encapsulation mode for all SRv6 TE policies globally in SRv6 TE view or for a specific SRv6 TE policy in SRv6 TE policy view. The policy-specific configuration takes precedence over the global configuration. An SRv6 TE policy uses the global configuration only when it has no policy-specific configuration.
The normal encapsulation modes are exclusive with the insertion modes. If you configure both a normal encapsulation mode and an insertion mode for an SRv6 TE policy, the most recent configuration takes effect.
If you configure the Insert or Insert.Red mode for an SRv6 TE policy, it uses the Encaps mode to encapsulate received IPv4 packets.
In SRv6 TE view, if you execute both the srv6-policy encapsulation-mode encaps reduced command and the srv6-policy encapsulation-mode encaps include local-end.x command, the srv6-policy encapsulation-mode encaps include local-end.x command takes effect.
In SRv6 TE view, if you execute both the srv6-policy encapsulation-mode insert reduced command and the srv6-policy encapsulation-mode insert include local-end.x command, the srv6-policy encapsulation-mode insert include local-end.x command takes effect.
In SRv6 TE policy view, if you execute both the encapsulation-mode encaps reduced command and the encapsulation-mode encaps include local-end.x command, the encapsulation-mode encaps include local-end.x command takes effect.
In SRv6 TE policy view, if you execute both the encapsulation-mode insert reduced command and the encapsulation-mode insert include local-end.x command, the encapsulation-mode insert include local-end.x command takes effect.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Configure the encapsulation mode globally for all SRv6 TE policies. Choose one option as needed:
¡ Specify the Encaps.Red encapsulation mode globally for all SRv6 TE policies.
srv6-policy encapsulation-mode encaps reduced
¡ Specify the Insert or Insert.Red encapsulation mode globally for all SRv6 TE policies.
srv6-policy encapsulation-mode insert
srv6-policy encapsulation-mode insert reduced
By default, the encapsulation mode for SRv6 TE policies is Encaps.
5. Enable the device to include the local End.X SID in the SRH of the packets forwarded by SRv6 TE policies. Choose one option as needed:
¡ Enable this feature for SRv6 TE policies with a normal encapsulation mode.
srv6-policy encapsulation-mode encaps include local-end.x
¡ Enable this feature for SRv6 TE policies with an insertion encapsulation mode.
srv6-policy encapsulation-mode insert include local-end.x
By default, the device does not include the local End.X SID in the SRH of the packets forwarded by SRv6 TE policies.
6. Enter SRv6 TE policy view.
policy policy-name
7. Configure the encapsulation mode for the SRv6 TE policy. Choose one option as needed:
¡ Specify the Encaps.Red encapsulation mode for the SRv6 TE policy.
encapsulation-mode encaps reduced [ disable ]
¡ Specify the Insert or Insert.Red encapsulation mode globally for all SRv6 TE policies.
encapsulation-mode insert
encapsulation-mode insert reduced [ disable ]
By default, the encapsulation mode is not configured for an SRv6 TE policy, and the encapsulation mode configured in SRv6 TE view applies.
8. Configure local End.X SID encapsulation in the SRH of the packets forwarded by the SRv6 TE policy. Choose one option as needed:
¡ Configure this feature when the SRv6 TE policy uses a normal encapsulation mode.
encapsulation-mode encaps include local-end.x [ disable ]
¡ Configure this feature when the SRv6 TE policy uses an insertion encapsulation mode.
encapsulation-mode insert include local-end.x [ disable ]
By default, local End.X SID encapsulation is not configured for an SRv6 TE policy, and the local End.X SID encapsulation setting configured in SRv6 TE view applies.
Configuring IPR for SRv6 TE policies
Restrictions and guidelines for IPR configuration
For this feature to take effect on an SRv6 TE policy group, you must configure the following settings for that SRv6 TE policy group:
· TE class ID-based traffic steering.
· Mappings between TE class IDs and IPR policies.
For more information, see "Configuring TE class ID-based traffic steering."
Configuring iFIT measurement for SRv6 TE policies
Restrictions and guidelines
· iFIT is an in-situ OAM measurement technology. This technology can measure the packet loss rate, delay, and jitter of an SRv6 TE policy only when data service traffic is being forwarded through that SRv6 TE policy. For more information about iFIT, see Network Management and Monitoring Configuration Guide.
· If the optimal candidate path of an SRv6 TE policy has multiple forwarding paths represented by multiple SID lists, and traffic exists in each forwarding path, iFIT will measure the packet loss rate, delay, and jitter of all the forwarding paths corresponding to the SID lists. Then, it will calculate the packet loss rate, delay, and jitter of the SRv6 TE policy based on the weights of the SID lists.
· If both the source and egress nodes of an SRv6 TE policy are H3C devices, set the iFIT measurement mode to end-to-end mode for the SRv6 TE policy as a best practice. In this mode, the egress node feeds back the iFIT measurement results to the source node of the SRv6 TE policy for calculating the network quality of the SRv6 TE policy. Even if the transit nodes along the forwarding path of a target flow have enabled iFIT and detected iFIT packets, they will not feed back the iFIT measurement results to the source node of the SRv6 TE policy. This mechanism reduces device processing complexity.
· If the egress node of an SRv6 TE policy is not an H3C device, you must set the iFIT measurement mode to hop-by-hop mode for the SRv6 TE policy. In this case, enable iFIT and set the iFIT operating mode to collector on the penultimate hop (an H3C device along the forwarding path). This H3C device will act as the data receiver to collect packet statistics, establish a UDP session with the source node, and feed the packet statistics back to the source node to fulfill the functions of the egress node. Typically, hop-by-hop mode is applicable to scenarios where the egress node of an SRv6 TE policy is not an H3C device.
· If multiple nodes feed back measurement data to the source node, the source node handles the data as follows:
¡ If the egress node and multiple other nodes feed back measurement data to the source node, the source node prefers the data fed back from the egress node for calculating the network quality.
¡ If multiple non-egress nodes feed back measurement data to the source node, the source node prefers the data fed back from the node closest to the egress node for calculating the network quality.
· To ensure that iFIT measurement can correctly operate, make sure the clock on all devices participating in iFIT measurement has been synchronized. A violation causes the iFIT calculation results to be inaccurate. You can use NTP and PTP to synchronize clock between devices.
· You can configure iFIT packet loss measurement, iFIT delay and jitter measurement, iFIT measurement mode, and iFIT measurement interval both in SRv6 TE view and SRv6 TE policy view. The configuration in SRv6 TE view takes effect on all SRv6 TE policies and the configuration in SRv6 TE policy view takes effect only on a specific SRv6 TE policy. For an SRv6 TE policy, the policy-specific configuration takes precedence over the configuration in SRv6 TE view.
· To have an iFIT measurement feature take effect on an SRv6 TE policy, make sure the source node of that SRv6 TE policy uses the normal (encaps) encapsulation mode for packet encapsulation. If the source node encapsulates packets in insertion mode, the outer source IP address of encapsulated packets are not the source address specified for iFIT measurement. As a result, the endpoint node returns information to an incorrect node rather than the source node, which causes iFIT measurement to fail.
Prerequisites
For iFIT measurement to take effect on an SRv6 TE policy, you must complete the following tasks:
· On the source node of the SRv6 TE policy, enable iFIT, configure the iFIT device ID, set the iFIT operating mode to analyzer, and execute the service-type srv6-segment-list command.
· On the egress node or transit nodes of the SRv6 TE policy, enable iFIT, set the iFIT operating mode to collector, and execute the service-type srv6-segment-list command.
Configuring iFIT measurement for SRv6 TE policies on the source node
1. Enter system view
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Globally enable iFIT packet loss measurement or iFIT delay and jitter measurement for SRv6 TE policies.
¡ Globally enable iFIT packet loss measurement for SRv6 TE policies.
srv6-policy ifit loss-measure enable
By default, iFIT packet loss measurement is disabled globally for SRv6 TE policies.
¡ Globally enable iFIT delay and jitter measurement for SRv6 TE policies.
srv6-policy ifit delay-measure enable
By default, iFIT delay and jitter measurement is disabled globally for SRv6 TE policies.
5. Globally specify an iFIT measurement mode for SRv6 TE policies.
srv6-policy ifit measure mode { e2e | trace }
By default, the iFIT measurement mode is end-to-end mode for SRv6 TE policis.
6. Globally set the iFIT measurement interval for SRv6 TE policies.
srv6-policy ifit interval time-value
By default, the global iFIT measurement interval is 30 seconds for SRv6 TE policies.
7. Enter SRv6 TE policy view.
policy policy-name
8. Configure iFIT packet loss measurement or iFIT delay and jitter measurement for the SRv6 TE policy.
¡ Configure iFIT packet loss measurement for the SRv6 TE policy.
ifit loss-measure { disable | enable }
By default, iFIT packet loss measurement is not configured in an SRv6 TE policy. The SRv6 TE policy uses the configuration in SRv6 TE view.
¡ Configure iFIT delay and jitter measurement for the SRv6 TE policy.
ifit delay-measure { disable | enable }
By default, iFIT delay and jitter measurement is not configured for an SRv6 TE policy. The SRv6 TE policy uses the configuration in SRv6 TE view.
9. Specify an iFIT measurement mode for the SRv6 TE policy.
ifit measure mode { e2e | trace }
By default, no iFIT measurement mode is specified for an SRv6 TE policy. The SRv6 TE policy uses the configuration in SRv6 TE view.
10. Set the iFIT measurement interval for the SRv6 TE policy.
ifit interval time-value
By default, no iFIT measurement interval is set for an SRv6 TE policy. The SRv6 TE policy uses the configuration in SRv6 TE view.
Configuring IPR path calculation for SRv6 TE policies
About this task
When service packets are steered to an SRv6 TE policy group configured with TE class ID-based traffic steering, the device matches the TE class ID in the packets with the mappings between TE class IDs and IPR policies in the SRv6 TE policy group. To configure the mappings, use the index te-class match command. If a matching mapping is found, the device selects an SRv6 TE policy to forward the packets according to the path selection policy defined in the matching IPR policy.
An IPR policy must cooperate with the iFIT packet loss measurement and iFIT delay and jitter measurement features of SRv6 TE policies for intelligent forwarding path selection. The cooperative mechanism between an IPR policy and the iFIT measurement features of SRv6 TE policies is as follows:
1. iFIT measures the network quality.
You can enable iFIT packet loss measurement and iFIT delay and jitter measurement for SRv6 TE policies on the source node of an SRv6 TE policy group. iFIT then performs the following operations:
a. Measures the link quality of different SRv6 TE policies in the SRv6 TE policy group.
b. Sends the SLA measurement data to IPR on the source node for path calculation and selection according to the iFIT measurement interval.
2. The source node calculates candidate paths.
The source node of SRv6 TE policies calculates the optimal SRv6 TE policy based on the optimal path calculation period set by using the refresh-period command. If the source node finds that any value of the delay, packet loss rate, jitter, and CMI values obtained from the most recent iFIT measurement data for an SRv6 TE policy crosses a threshold set in an IPR policy, that SRv6 TE policy does not comply with the SLA requirements. As a result, the source node does not use that SRv6 TE policy as a candidate path for service traffic forwarding. If iFIT fails to measure the delay, packet loss rate, jitter, and CMI values of an SRv6 TE policy, but the SRv6 TE policy is valid, the source node still uses this SRv6 TE policy as a candidate path for service traffic forwarding.
3. The source node selects the optimal path.
The source node selects the SRv6 TE policy with the highest priority as the optimal forwarding path according to the priority order defined in the IPR policy, and steers service traffic to this SRv6 TE policy. When multiple SRv6 TE policies have the same priority, traffic can be load-balanced among these SRv6 TE policies.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enable IPR and enter SRv6 TE IPR view.
intelligent-policy-route
By default, IPR is disabled.
5. (Optional.) Set the interval at which IPR calculates the optimal path.
refresh-period time-value
By default, IPR calculates the optimal path at intervals of 60 seconds.
6. (Optional.) Specify the data calculation mode for IPR.
measure count { one-way | two-way-average }
By default, the one-way mode is used.
7. Create an IPR policy and enter SRv6 TE IPR policy view.
ipr-policy ipr-name
By default, no IPR policies exist.
8. Configure a mapping between the color attribute value of an SRv6 TE policy and a path selection priority in the IPR policy.
srv6-policy color color-value priority priority-value
By default, no mapping is configured between the color attribute value of an SRv6 TE policy and a path selection priority in an IPR policy.
9. (Optional.) Set the delay threshold in the IPR policy.
delay threshold time-value
By default, the delay threshold is 5000 milliseconds in an IPR policy.
10. (Optional.) Set the jitter threshold in the IPR policy.
jitter threshold time-value
By default, the jitter threshold is 3000 milliseconds in an IPR policy.
11. (Optional.) Set the packet loss rate threshold in the IPR policy.
loss threshold threshold-value
By default, the packet loss rate threshold is 1000‰ in an IPR policy.
12. (Optional.) Set the CMI threshold in the IPR policy.
cmi threshold threshold-value
By default, the CMI threshold in an IPR policy is 9000.
13. (Optional.) Set the switchover period between SRv6 TE policies in the IPR policy.
switch-period time-value
By default, the switchover period between SRv6 TE policies is 6 seconds in an IPR policy.
14. (Optional.) Set the WTR period in the IPR policy.
wait-to-restore-period time-value
By default, the WTR period is 6 seconds in an IPR policy.
Enabling SBFD for SRv6 TE policies
About this task
By default, the returning SBFD packets used for SRv6 TE policy connectivity detection are forwarded based on the IP forwarding path. If a transit node fails, the returning packets will be discarded, the SBFD session will go down, and the SID list will be mistakenly considered as faulty.
To resolve this issue, you can enable the returning SBFD packets to be forwarded based on the specified SID list to ensure connectivity as follows:
1. Configure a reverse BSID in SID list view on the ingress node, and configure a local BSID with the same value in SID list view on the egress node.
2. When the ingress node forwards an SBFD packet, it encapsulates the Aux Path TLV in the packet. This TLV contains the reverse BSID.
3. When the egress node receives the SBFD packet, it compares the reverse BSID in the packet with the configured local BSID. If the values are the same, the egress node encapsulates an SRH for the returning SBFD packet and forwards the packet based on the SID list associated with the local BSID.
To use SBFD to detect an SRv6 TE policy, the device needs to encapsulate the SID list of the SRv6 TE policy for the SBFD packets. The following encapsulation modes are available:
· Encaps—Normal encapsulation mode. It adds a new IPv6 header and an SRH to the original packets.
¡ The destination IPv6 address in the new IPv6 header is the first SID in the SID list of the SRv6 TE policy. The source IPv6 address is the IPv6 address specified by using the encapsulation source-address command.
¡ All SIDs in the SID list of the SRv6 TE policy are encapsulated in the SRH.
· Insert—Insertion mode. It inserts an SRH after the original IPv6 header.
¡ The destination IPv6 address in the original IPv6 header is changed to the first SID in the SID list of the SRv6 TE policy. The source IPv6 address does not change.
¡ All SIDs in the SID list of the SRv6 TE policy and the endpoint of the SRv6 TE policy are encapsulated in the SRH. The endpoint is the last one in the SID list.
· Insert no-endpoint—Insert no-endpoint mode. It inserts an SRH without an endpoint after the original IPv6 header. The last SID in the SID list and the endpoint in the SRv6 TE policy represent the same node.
¡ The destination IPv6 address in the original IPv6 header changes to the first IPv6 address in the SID list of the SRv6 TE policy. The source IPv6 address does not change.
¡ All SIDs in the SID list of the SRv6 TE policy are encapsulated in the SRH. The endpoint of the SRv6 TE policy is not encapsulated in the SRH.
Restrictions and guidelines
You can enable SBFD for all SRv6 TE policies globally in SRv6 TE view or for a specific SRv6 TE policy in SRv6 TE policy view. The policy-specific configuration takes precedence over the global configuration. An SRv6 TE policy uses the global configuration only when it has no policy-specific configuration.
The remote discriminator specified in this command must be the same as that specified in the sbfd local-discriminator command on the reflector. Otherwise, the reflector will not send responses to the initiator.
The device supports the echo packet mode BFD and the SBFD for an SRv6 TE policy. If both modes are configured for the same SRv6 TE policy, the SBFD takes effect.
For an SBFD session, the device selects a source address for SBFD packets in the following order:
1. The packet source address specified by using the source-address command.
2. The address specified by using the sbfd source-ipv6 command.
Procedure
1. Enter system view.
system-view
2. Configure the encapsulation mode for the SBFD packets used for SRv6 forwarding paths connectivity detection.
bfd srv6-encapsulation-mode insert [ no-endpoint ]
By default, the Encap mode is used to encapsulate BFD or SBFD packets. A new IPv6 header and an SRH are added to the original packets. The SRH contains the SID list of an SRv6 TE policy. If the length of the SID list is 0, no SRH is added to the original packets.
3. Configure the source IPv6 address used by the initiator to send SBFD packets.
sbfd source-ipv6 ipv6-address
By default, no source IPv6 address is configured for SBFD packets.
4. Enter SRv6 view.
segment-routing ipv6
5. Enter SRv6 TE view.
traffic-engineering
6. Enable SBFD for all SRv6 TE policies and configure the SBFD session parameters.
srv6-policy sbfd [ remote remote-id ] [ template template-name ] [ backup-template backup-template-name ] [ reverse-path reverse-binding-sid ]
By default, SBFD is disabled for all SRv6 TE policies.
7. (Optional.) Configure the local BSID and reverse BSID for an SID list.
a. Enter SID list view.
segment-list segment-list-name
b. On the egress node of an SRv6 TE policy, configure the local BSID.
local-binding-sid ipv6 ipv6-address
c. On the ingress node of an SRv6 TE policy, configure the reverse BSID.
reverse-binding-sid ipv6 ipv6-address
d. Return to SRv6 TE view.
quit
The specified local BSID or reverse BSID cannot be the same as the BSID of the SRv6 TE policy. If they are the same, the SID list becomes invalid and cannot be used to forward packets.
The specified local BSID or reverse BSID must be within the static length of the locator specified in SRv6 TE view. If this condition is not met, the SID list associated with the BSID cannot be used to forward packets.
8. (Optional.) Enable BFD session down events to trigger SRv6 TE policy path switchover globally.
srv6-policy bfd trigger path-down enable
By default, the feature for triggering SRv6 TE policy path switchover with BFD session down events is disabled globally.
9. (Optional.) Configure the timer that delays reporting the first BFD or SBFD session establishment failure to an SRv6 TE policy.
srv6-policy bfd first-fail-timer seconds
By default, the timer that delays reporting the first BFD or SBFD session establishment failure to an SRv6 TE policy is 60 seconds.
10. Enter SRv6 TE policy view.
policy policy-name
11. (Optional.) Specify a source address for SBFD packets in the SRv6 TE policy.
source-address ipv6 ipv6-address
By default, no source address is specified for SBFD packets in an SRv6 TE policy.
12. Configure SBFD for the SRv6 TE policy.
sbfd { disable | enable [ remote remote-id ] [ template template-name ] [ backup-template backup-template-name ] [ oam-sid sid ] [ encaps | insert [ no-endpoint ] [ reverse-path reverse-binding-sid ] ] }
By default, SBFD is not configured for an SRv6 TE policy.
If you do not specify the encaps or insert keyword, the encapsulation mode configured by the bfd srv6-encapsulation-mode command applies.
13. (Optional.) Enable BFD session down events to trigger SRv6 TE policy path switchover.
bfd trigger path-down { disable | enable }
By default, the feature for triggering SRv6 TE policy path switchover by BFD session down events is not configured. The configuration in SRv6 TE view applies.
Configuring the BFD echo packet mode for SRv6 TE policies
About this task
By default, the returning BFD echo packets used for SRv6 TE policy connectivity detection are forwarded based on the IP forwarding path. If a transit node fails, the returning packets will be discarded, the BFD session will go down, and the SID list will be mistakenly considered as faulty.
To resolve this issue, you can enable the returning BFD packets to be forwarded based on the specified SID list to ensure connectivity as follows:
1. Configure a reverse BSID in SID list view on the ingress node, and configure a local BSID with the same value in SID list view on the egress node.
2. When the ingress node forwards a BFD packet, it encapsulates an SID list in the SRH. In addition, it encapsulates the reverse BSID associated with the SID list to the SL=1 location.
3. When the egress node receives the BFD packet, it compares the SID at the SL=1 location in the SRH with the configured local BSID. If the values are the same, the egress node encapsulates an SRH for the returning BFD packet and forwards the packet based on the SID list associated with the local BSID.
To use echo BFD to detect the connectivity of an SRv6 TE policy, the device needs to encapsulate the SID list of the SRv6 TE policy for the SBFD packets. The following encapsulation modes are available:
· Encaps—Normal encapsulation mode. It adds a new IPv6 header and an SRH to the original packets.
¡ The destination IPv6 address in the new IPv6 header is the first SID in the SID list of the SRv6 TE policy. The source IPv6 address is the IPv6 address specified by using the encapsulation source-address command.
¡ All SIDs in the SID list of the SRv6 TE policy are encapsulated in the SRH.
· Insert—Insertion mode. It inserts an SRH after the original IPv6 header.
¡ The destination IPv6 address in the original BFD echo packet header is changed to the first SID in the SID list of the SRv6 TE policy. The source IPv6 address in the original BFD echo packet does not change.
¡ All SIDs in the SID list of the SRv6 TE policy are encapsulated in the SRH.
Restrictions and guidelines
You can configure the echo packet mode BFD for all SRv6 TE policies globally in SRv6 TE view or for a specific SRv6 TE policy in SRv6 TE policy view. The policy-specific configuration takes precedence over the global configuration. An SRv6 TE policy uses the global configuration only when it does not have policy-specific configuration.
For a BFD session in echo packet mode, the device selects a source address for BFD echo packets in the following order:
1. The packet source address specified by using the source-address command.
2. The packet source address specified by using the bfd echo-source-ipv6 command.
3. The BFD session source address specified by using the bfd echo command.
4. The BFD session source address specified by using the srv6-policy bfd echo command.
On the source node in an SRv6 TE policy, the BFD session source address specified by using the bfd echo or srv6-policy bfd echo command is also the destination address of BFD echo packets. BFD echo packets might use the same IP address as the source address and destination address. In this case, BFD echo session establishment will fail if the network is deployed with security devices that have features such as uRPF, because the features falsely treat the BFD echo packets as illegal packets and intercept them. To resolve this issue, you can configure a source address for BFD echo packets. Make sure the source and destination addresses of BFD echo packets are different.
If you do not specify the source-ipv6 ipv6-address option in the bfd echo command for an SRv6 TE policy, you must enable the echo packet mode BFD globally in SRv6 TE view. Otherwise, the device cannot establish a BFD session for the SRv6 TE policy.
The device supports the echo packet mode BFD and the SBFD for an SRv6 TE policy. If both modes are configured for the same SRv6 TE policy, the SBFD takes effect.
Before you execute this command, execute the bfd echo-source-ipv6 command on the local device to specify the source IPv6 address for echo packets.
Procedure
1. Enter system view.
system-view
2. Configure the encapsulation mode for the BFD packets used for SRv6 forwarding paths connectivity detection.
bfd srv6-encapsulation-mode insert [ no-endpoint ]
By default, the Encap mode is used to encapsulate BFD or SBFD packets. A new IPv6 header and an SRH are added to the original packets. The SRH contains the SID list of an SRv6 TE policy. If the length of the SID list is 0, no SRH is added to the original packets.
3. Enter SRv6 view.
segment-routing ipv6
4. Enter SRv6 TE view.
traffic-engineering
5. Enable echo packet mode BFD for all SRv6 TE policies and configure the BFD session parameters.
srv6-policy bfd echo source-ipv6 ipv6-address [ template template-name ] [ backup-template backup-template-name ] [ reverse-path reverse-binding-sid ]
By default, the echo packet mode BFD is disabled for all SRv6 TE policies.
6. (Optional.) Configure the local BSID and reverse BSID for an SID list.
a. Enter SID list view.
segment-list segment-list-name
b. On the egress node of an SRv6 TE policy, configure the local BSID.
local-binding-sid ipv6 ipv6-address
c. On the ingress node of an SRv6 TE policy, configure the reverse BSID.
reverse-binding-sid ipv6 ipv6-address
d. Return to SRv6 TE view.
quit
The specified local BSID or reverse BSID cannot be the same as the BSID of the SRv6 TE policy. If they are the same, the SID list becomes invalid and cannot be used to forward packets.
The specified local BSID or reverse BSID must be within the static length of the locator specified in SRv6 TE view. If this condition is not met, the SID list associated with the BSID cannot be used to forward packets.
7. (Optional.) Enable BFD session down events to trigger SRv6 TE policy path switchover globally.
srv6-policy bfd trigger path-down enable
By default, the feature for triggering SRv6-TE policy path switchover with BFD session down events is disabled globally.
8. (Optional.) Configure the timer that delays reporting the first BFD or SBFD session establishment failure to an SRv6 TE policy.
srv6-policy bfd first-fail-timer seconds
By default, the timer that delays reporting the first BFD or SBFD session establishment failure to an SRv6 TE policy is 60 seconds.
9. Enter SRv6 TE policy view.
policy policy-name
10. (Optional.) Specify a source address for BFD echo packets in an SRv6 TE policy.
source-address ipv6 ipv6-address
By default, no source address is specified for BFD echo packets in an SRv6 TE policy.
11. Configure the echo packet mode BFD for the SRv6 TE policy.
bfd echo { disable | enable [ source-ipv6 ipv6-address ] [ template template-name ] [ backup-template backup-template-name ] [ oam-sid sid ] [ encaps | insert ] [ reverse-path reverse-binding-sid ] }
By default, the echo packet mode BFD is not configured for an SRv6 TE policy. An SRv6 TE policy uses the echo BFD settings configured in SRv6 TE view.
If you do not specify the encaps or insert keyword, the encapsulation mode configured by the bfd srv6-encapsulation-mode command applies.
After the reverse-path keyword is specified, BFD packets can be encapsulated only in Insert mode. The encaps keyword does not take effect.
12. (Optional.) Enable BFD session down events to trigger SRv6 TE policy path switchover.
bfd trigger path-down { disable | enable }
By default, the feature for triggering SRv6-TE policy path switchover by BFD session down events is not configured. The configuration in SRv6 TE view applies.
13. Specify the local BSID and reverse BSID for BFD detection of an SID list.
a. Enter SRv6 TE policy candidate path view.
candidate-paths
b. Enter SRv6 TE policy path preference view.
preference preference-value
Each preference represents a candidate path.
c. Specify the local BSID and reverse BSID for BFD detection of an SID list.
explicit segment-list segment-list-name [ local-binding-sid ipv6 ipv6-address | reverse-binding-sid ipv6 ipv6-address ] *
For the local BSID:
- The specified BSID cannot be the same as the BSID configured with the local-binding-sid command for the SID list.
- The specified BSID takes precedence over the BSID configured with the local-binding-sid command for the SID list.
For the reverse BSID:
- The specified BSID cannot be the same as the BSID configured with the reverse-binding-sid command for the SID list.
- The specified BSID takes precedence over the BSID configured with the reverse-binding-sid command for the SID list.
Enabling hot standby for SRv6 TE policies
About this task
When the hot standby feature is enabled, the numbers of the main and backup paths are as follows if multiple candidate paths exist.
· One main path one backup path—The candidate path with the greatest preference value in the SRv6 TE policy is the main path and that with the second greatest preference value is the backup path. When all SID lists of the main path fail, the backup path immediately takes over the service to minimize service interruption.
· One main path two backup paths—A secondary backup path is also provided for the main path besides the backup path. The secondary backup path is the candidate path with the third highest preference in the SR-MPLS TE policy. When all SID lists of the main path fail, the backup path immediately takes over the service. If the backup path fails, too, the secondary backup path takes over the service to minimize service interruption.
Restrictions and guidelines
You can enable hot standby for all SRv6 TE policies globally in SRv6 TE view or for a specific SRv6 TE policy in SRv6 TE policy view. The policy-specific configuration takes precedence over the global configuration. An SRv6 TE policy uses the global configuration only when it has no policy-specific configuration.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enable hot standby for all SRv6 TE policies.
srv6-policy backup hot-standby enable
By default, hot standby is disabled for all SRv6 TE policies.
5. Enter SRv6 TE policy view.
policy policy-name
6. Configure hot standby for the SRv6 TE policy.
backup hot-standby { disable | enable }
By default, hot standby is not configured for an SRv6 TE policy, and the hot standby configuration in SRv6 TE view applies.
Configuring path switchover and deletion delays for SRv6 TE policies
About this task
The switchover delay and deletion delay mechanism is used to avoid traffic forwarding failure during a forwarding path (SID list) switchover.
When updating an SRv6 TE policy forwarding path, the device first establishes the new forwarding path before it deletes the old one. During the new path setup process, the device uses the old path to forward traffic until the switchover delay timer expires. When the switchover delay timer expires, the device switches traffic to the new path. The old path is deleted when the deletion delay timer expires.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Configure the switchover delay time and deletion delay time for the SRv6 TE policy forwarding path.
srv6-policy switch-delay switch-delay-time delete-delay delete-delay-time
By default, the switchover delay time and deletion delay time for the SRv6 TE policy forwarding path is 5000 milliseconds and 20000 milliseconds, respectively.
Setting the delay time for bringing up SRv6 TE policies
About this task
After an SRv6 TE policy recovers from a fault, the device waits for the delay time before bringing up the SRv6 TE policy. This is to ensure that the fault is completely removed so as to avoid packet loss caused by SRv6 TE policy flapping.
After this command is executed, the device starts different delay timers for an SRv6 TE policy according to the BFD/SBFD configuration for the SRv6 TE policy.
· If BFD/SBFD is not enabled, the device starts an LSP delay timer when the SID list state changes from Down to Up.
· If BFD/SBFD is enabled, the device starts a BFD delay timer when the BFD/SBFD session state changes from Down to Up.
Restrictions and guidelines
To view the BFD/SBFD configuration, SID list state, and SBFD session state, execute the display segment-routing ipv6 te policy command.
Set a proper SRv6 TE policy up delay time according to your network conditions. A very long delay time will cause an SRv6 TE policy to be unable to process user traffic for a long time.
You can set the delay time for all SRv6 TE policies globally in SR TE view or for a specific SRv6 TE policy in SRv6 TE policy view. The policy-specific configuration takes precedence over the global configuration. An SRv6 TE policy uses the global configuration only when it has no policy-specific configuration.
If you execute this command for multiple times, the most recent configuration takes effect. A new delay time setting does not apply to the SRv6 TE policies that are already in a policy-up delay process.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Set the policy-up delay time for all SRv6 TE policies.
srv6-policy up-delay delay-time
By default, the device does not delay bringing up SRv6 TE policies.
5. Enter SRv6 TE policy view.
policy policy-name
6. Set the policy-up delay time for the SRv6 TE policy.
up-delay delay-time
By default, no policy-up delay time is set for an SRv6 TE policy and the policy-up delay time set in SR TE view applies.
Configuring path connectivity verification for SRv6 TE policies
About this task
Typically, the controller deploys the SID list of an SRv6 TE policy. Without BFD configured, the first node cannot immediately detect path failures in the SRv6 TE policy. It only changes the SID list of the SRv6 TE policy as instructed by the controller that completes path recalculation upon detecting a topology change. If the controller or the link to the controller fails, the first node will be unable to detect failures and change SID lists, resulting in traffic loss.
For fast traffic switchover and high availability, you can enable path connectivity verification for the first node of the SRv6 TE policy. This feature enables the first node to collect network topology information, and verify all SID lists in the SRv6 TE policy as follows:
· If all SRv6 SIDs exist in the topology and the associated locator prefixes are routable, the SID list is valid.
· If any SRv6 SIDs do not exist in the topology or any of the associated locator prefixes are not routable, the SID list is invalid.
Upon detecting an invalid SID list (SID list failure), the first node changes paths as follows:
· If the valid candidate paths of the SRv6 TE policy contain multiple SID lists, and one of the SID list fails, traffic is distributed to other valid SID lists.
· If the SRv6 TE policy has valid primary and backup candidate paths, and all SID lists for the primary candidate path fail, traffic is distributed to the backup candidate path.
· If all valid candidate paths of the SRv6 TE policy fail, the SRv6 TE policy is faulty and an associated protection action is taken (for example, MPLS L3VPN FRR).
After path connectivity verification is enabled for an SRv6 TE policy, the device verifies the validity of all SIDs in the SID list. If the SID list contains an inter-AS SID (for example, the BGP Peer SID allocated by BGP EPE) or contains the BSID of another SRv6 TE policy, the path connectivity verification will fail. This is because a BSID or BGP Peer SID cannot be flooded in the IGP topology.
To resolve this issue, you can execute the following commands to configure the path connectivity verification only verifies the validity of specific SIDs:
· Use the index command to specify the verification keyword for the SIDs to be verified. Do not specify this keyword for a BSID or BGP EPE SID in the SID list.
· Specify the specified-sid keyword when you execute the path verification command in SRv6 TE policy view or the srv6-policy path verification enable command in SRv6 TE view.
Restrictions and guidelines
You must perform this task on the first node of the SRv6 TE policy.
You can configure SRv6 TE policy path connectivity verification in both SRv6 TE view and SRv6 TE policy view. The configuration in SRv6 TE policy view takes precedence over the configuration in SRv6 TE view. If path connectivity verification is not configured for an SRv6 TE policy, the configuration in SRv6 TE applies.
The first node must have all SRv6 SIDs and routes in the IGP domain to detect their status through the following settings:
· Enable the IGP domain to forward routing information through IPv6 IS-IS.
· Configure the distribute link-state command in IS-IS view for the first node to report link status.
If a BSID exists in the segment list path, path connectivity verification will fail because the BSID cannot be flooded in the IGP topology. Do not perform this task in the scenario where BSID is deployed.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enable path connectivity verification for all SRv6 TE policies.
srv6-policy path verification [ specified-sid ] enable [ rib-check-only ]
By default, path connectivity verification is disabled for all SRv6 TE policies.
5. Enter SRv6 TE policy view.
policy policy-name
6. Configure path connectivity verification for an SRv6 TE policy.
path verification { [ specified-sid ] enable [ rib-check-only ] | disable }
By default, path connectivity verification is not configured for an SRv6 TE policy. The setting configured in SRv6 TE view applies.
Configuring SRv6 TE policy transit node protection
About this task
The transit node protection technology is referred to as SRv6 TE FRR. After SRv6 TE FRR is enabled, when a transit node of an SRv6 TE policy fails, the upstream node of the faulty node can take over to forward packets. The upstream node is called a proxy forwarding node that bypasses the faulty transit node to implement node failure protection.
Restrictions and guidelines
In a complex network, any node might act as a transit node. As a best practice to improve the whole network security, enable SRv6 TE FRR on all nodes.
Transit node failure protection might fail if SRv6 compression is also enabled. Traffic cannot bypass the SRv6 SID of the faulty node, because the SRv6 SIDs in the SID list of the SRv6 TE policy are related with each another. To address this issue, configure the sr-te frr enable command with the downgrade keyword specified, and make sure the last SRv6 SID in the SID list is not compressed. The proxy forwarding node can then use the last SRv6 SID in the SID list as the destination address for forwarding to implement transit node failure protection.
Suppose you configure the sr-te frr enable command with the downgrade keyword specified for the transit node. Then, a transit node failure occurs and triggers transit node failure protection. To enable echo packet mode BFD for the SRv6 TE policy, you must use the bfd echo command to enable the normal encapsulation mode.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enable SRv6 TE FRR.
sr-te frr enable [ downgrade ]
4. Enter SRv6 TE view.
traffic-engineering
5. Enter SRv6 TE policy view.
policy policy-name
6. Enable the bypass feature for the SRv6 TE policy.
bypass enable
By default, the SRv6 TE policy bypass feature is disabled.
Execute this command only on the source node.
Configuring SRv6 TE policy egress protection
Restrictions and guidelines for SRv6 TE policy egress protection configuration
To configure SRv6 TE policy egress protection, all nodes that the packets will traverse must support SRv6.
Configuring an End.M SID
Restrictions and guidelines
Perform this task on protection node for the egress node.
For more information about the commands used in this task, see SRv6 commands in Segment Routing Command Reference.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Create a locator and enter SRv6 locator view.
locator locator-name [ ipv6-prefix ipv6-address prefix-length [ args args-length | static static-length ] * ]
4. Configure an End.M SID and specify the locator to be protected by the End.M SID.
opcode opcode end-m mirror-locator ipv6-address prefix-length
Enabling egress protection
About this task
This task enables the SRv6 node to compute a backup path (mirror FRR path) for the egress node based on the End.M SID carried in a received IS-ISv6 or OSPFv3 route. When the egress node fails, the transit node can forward traffic to the node that protects the egress node according to the End.M SID.
In an egress protection scenario, the transit node deletes the mirror FRR path after completing route convergence. If the deletion occurs before the ingress node switches traffic back from the mirror FRR path, the traffic will be dropped because of no mirror FRR path.
To resolve this issue, you can configure a proper mirror FRR deletion delay time on the transit node to delay the deletion of the mirror FRR route. So, packets can be forwarded over the mirror FRR path before the ingress finishes the path switchover.
Enabling IS-IS egress protection
1. Enter system view.
system-view
2. Enter IS-IS view.
isis [ process-id ] [ vpn-instance vpn-instance-name ]
3. Enter IS-IS IPv6 address family view.
address-family ipv6 [ unicast ]
4. Enable IS-IS egress protection.
fast-reroute mirror enable
By default, IS-IS egress protection is disabled.
5. (Optional.) Configure the mirror FRR deletion delay time.
fast-reroute mirror delete-delay delete-delay-time
By default, the mirror FRR deletion delay time is 60 seconds.
Enabling OSPFv3 egress protection
1. Enter system view.
system-view
2. Enter OSPFv3 view.
ospfv3 [ process-id | vpn-instance vpn-instance-name ] *
3. Enable OSPFv3 egress protection.
fast-reroute mirror enable
By default, OSPFv3 egress protection is disabled.
4. (Optional.) Configure the mirror FRR deletion delay time.
fast-reroute mirror delete-delay delete-delay-time
By default, the mirror FRR deletion delay time is 60 seconds.
Configuring the deletion delay time for remote SRv6 SID mappings with VPN instances/public instance/cross-connects/VSIs
About this task
In an egress protection scenario, if the egress node and the egress node's protection node are disconnected, the protection node will delete the BGP routes received from the egress node. The remote SRv6 SID and VPN instance/public instance/cross-connect/VSI mappings will then be deleted as a result. To avoid this issue, you can configure the mappings deletion delay time on the protection node. This ensures that traffic is forwarded through the protection node before the ingress detects the egress failure and computes a new forwarding path.
Restrictions and guidelines
Perform this task on the protection node for the egress node.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Configure the deletion delay time for remote SRv6 SID mappings with VPN instances/public instance/cross-connects/VSIs.
mirror remote-sid delete-delay delete-delay-time
By default, the deletion delay time for remote SRv6 SID and VPN instance/public instance/cross-connect/VSI mappings is 60 seconds.
Configuring candidate path reoptimization for SRv6 TE policies
About this task
This feature enables the PCE to periodically compute paths and notify the PCC to update path information, so that SRv6 TE policies can use the optimal path to establish the candidate path.
For example, an SRv6 TE policy uses a path other than the optimal path to establish the candidate path because the optimal path does not have sufficient link bandwidth. This feature enables the SRv6 TE policy to switch the candidate path to the optimal path when the link bandwidth becomes sufficient.
Restrictions and guidelines
You can configure candidate path reoptimization for all SRv6 TE policies globally in SRv6 TE view or for a specific SRv6 TE policy in SRv6 TE policy view. The policy-specific configuration takes precedence over the global configuration. An SRv6 TE policy uses the global configuration only when it has no policy-specific configuration.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view
traffic-engineering
4. Enable candidate path reoptimization for SRv6 TE policies globally.
srv6-policy reoptimization [ frequency seconds ]
By default, candidate path reoptimization is disabled for SRv6 TE policies globally.
5. Enter SRv6 TE policy view.
policy policy-name
6. Configure candidate path reoptimization for the SRv6 TE policy.
reoptimization { disable | enable [ frequency seconds ] }
By default, candidate path reoptimization is not configured for an SRv6 TE policy, and the configuration in SRv6 TE view applies.
7. Return to user view.
quit
quit
quit
quit
8. Immediately reoptimize all SRv6 TE policies enabled with candidate path reoptimization.
srv6-policy immediate-reoptimization
Configuring flapping suppression for SRv6 TE policies
About this task
After SRv6 TE policy flapping suppression is enabled, the device starts a counter for an SRv6 TE policy to count the SID list flapping events for the policy.
· If the state of a SID list changes from down to up within the flapping detection interval, an SID list flapping event occurs, and the flapping count increases by 1.
· If the time for a SID list to change from down to up is longer than the resumption interval, the flapping counter is cleared.
· If the flapping count exceeds the flapping suppression threshold, the SRv6 TE policy enters flapping suppression state. In this state, the SRv6 TE policy does not update the SID list state but keep the SID list in down state, and the flapping counter is not cleared.
· When the suppression state lasts for the resumption interval, the device ends the suppression state of the SRv6 TE policy and clears the flapping counter.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view
traffic-engineering
4. Disable flapping suppression for SRv6 TE policies globally.
srv6-policy suppress-flapping disable
By default, candidate path reoptimization is disabled for SRv6 TE policies globally.
5. Configure flapping suppression parameters for the SRv6 TE policy.
srv6-policy suppress-flapping { detect-interval detect-interval | threshold threshold | resume-interval resume-interval } *
By default, the SRv6 TE policy flapping detection interval is 60 seconds, the flapping suppression threshold is 10, and the flapping suppression resumption interval is 120 seconds.
Configuring the TTL processing mode of SRv6 TE policies
About this task
An SRv6 TE policy used as a public tunnel supports the following TTL processing modes:
· Uniform—When the ingress node adds a new IPv6 header to an IP packet, it copies the TTL value of the original IP packet to the Hop Limit field of the new IPv6 header. Each node on the SRv6 TE policy forwarding path decreases the Hop Limit value in the new IPv6 header by 1. The node that de-encapsulates the packet copies the remaining Hop Limit value back to the TTL field of the original IP packet when it removes the new IPv6 header. The TTL value can reflect how many hops the packet has traversed in the public network. The tracert facility can show the real path along which the packet has traveled.
· Pipe—When the ingress node adds a new IPv6 header to an IP packet, it does not copy the TTL value of the original IP packet to the Hop Limit field of the new IPv6 header. It sets the Hop Limit value in the new IPv6 header to 255. Each node on the SRv6 TE policy forwarding path decreases the Hop Limit value in the new IPv6 header by 1. The node that de-encapsulates the packet does not change the IPv6 Hop Limit value. Therefore, the public network nodes are invisible to user networks, and the tracert facility cannot show the real path in the public network.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Configure the TTL processing mode of SRv6 TE policies.
ttl-mode { pipe | uniform }
By default, the TTL processing mode of SRv6 TE policies is pipe.
Configuring SRv6 TE policy CBTS
Prerequisites
Before configuring CBTS, you must create QoS traffic behaviors to mark the MPLS TE service class values for packets. For more information, see QoS configuration in ACL and QoS Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enter SRv6 TE policy view.
policy policy-name
5. Set a service class value for the SRv6 TE policy.
service-class service-class-value
By default, no service class value is set for an SRv6 TE policy.
Configuring a rate limit for an SRv6 TE policy
About this task
When the rate of the packets forwarded by an SRv6 TE policy exceeds the rate limit, the device drops the packets that exceed the rate limit.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enter SRv6 TE policy view.
policy policy-name
5. Set a rate limit for the SRv6 TE policy.
rate-limit kbps
By default, no rate limit is set for an SRv6 TE policy.
Enabling the device to drop traffic when an SRv6 TE policy becomes invalid
About this task
Enable this feature for an SRv6 TE policy if you want to use only the SRv6 TE policy to forward traffic.
By default, if all forwarding paths of an SRv6 TE policy become invalid, the device forwards the packets through IPv6 routing table lookup based on the packet destination IPv6 addresses.
After you execute the drop-upon-invalid enable command, the device drops the packets if all forwarding paths of the SRv6 TE policy become invalid.
Restrictions and guidelines
The drop-upon-invalid enable command does not take effect if the SRv6 TE policy is invalid. To check the SRv6 TE policy validity, see the Forwarding index field in the display segment-routing ipv6 te policy command output. If the value is 0, the SRv6 TE policy is invalid.
The drop-upon-invalid command configured on the remote device does not affect an SRv6 TE policy generated based on a BGP IPv6 SR-TE policy route. The SRv6 TE policy is controlled by only the drop-upon-invalid command configured on the local device.
You can configure the drop-upon-invalid feature globally in SRv6 TE view or for a specific SRv6 TE policy in SRv6 TE policy view. The policy-specific configuration takes precedence over the global configuration. An SRv6 TE policy uses the global configuration only when it has no policy-specific configuration.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Globally enable the feature of dropping traffic when SRv6 TE policies become invalid.
srv6-policy drop-upon-invalid enable
By default, the drop-upon-invalid feature is disabled globally.
5. Enter SRv6 TE policy view.
policy policy-name
6. Configure the device to drop traffic when an SRv6 TE policy becomes invalid.
drop-upon-invalid { disable | enable }
By default, the drop-upon-invalid feature is disabled for an SRv6-TE policy. The device does not drop traffic when the SRv6-TE policy becomes invalid.
Enabling SRv6 TE policies to forward packets without using the last SID in the SID list
About this task
In an SRv6 VPN scenario, to forward a public network packet through the SRv6 TE policy, the device encapsulates an SRH into the packet. The SRH contains the SID list of the SRv6 TE policy and the SID assigned to the VPN instance or public network instance (End.DT4 SID, for example). Both the last SID in the SID list and the End.DT4 SID are used to identify the egress node. To reduce the SRv6 packet size, you can configure this command to use only the End.DT4 SID to identify the egress node.
Restrictions and guidelines
You can configure this feature for all SRv6 TE policies globally in SRv6 TE view or for a specific SRv6 TE policy in SRv6 TE policy view. The policy-specific configuration takes precedence over the global configuration. An SRv6 TE policy uses the global configuration only when it has no policy-specific configuration.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enable all SRv6 TE policies to forward packets without using the last SID in the SID list.
srv6-policy forwarding ignore-last-sid
By default, the feature is disabled..
5. Enter SRv6 TE policy view.
policy policy-name
6. Enable the SRv6 TE policy to forward packets without using the last SID in the SID list.
forwarding ignore-last-sid { disable | enable }
By default, the feature is not configured. The configuration in SRv6 TE view applies.
Specifying the packet encapsulation type preferred in optimal route selection
About this task
As shown in Figure 17, PE 4 is the RR, and it establishes an IBGP connection with PE 1, PE 2, and PE 3, respectively. PE 1 and PE 3 support SRv6. PE 2 does not support SRv6. Both an MPLS L3VPN connection and an EVPN L3VPN over SRv6 connection exist between PE 1 and PE 3.
In this case, you can perform this task to specify the preferred encapsulation type (SRv6 encapsulation or MPLS encapsulation) for BGP optimal route selection in the L3VPN.
Figure 17 MPLS L3VPN and EVPN L3VPN over SRv6 coexist
If you specify the preferred keyword in the bestroute encap-type command, BGP prefers the routes with specified encapsulation type (SRv6 or MPLS) when multiple routes have the same Preferred-value attribute value. The subsequent route selection steps are the same as those in the original BGP route select procedure.
If you do not specify the preferred keyword in the bestroute encap-type command, BGP prefers the routes with the specified encapsulation type (SRv6 or MPLS) when multiple routes have the same Preferred-value and LOCAL_PREF attribute values. The subsequent route selection steps are the same as those in the original BGP route select procedure.
For more information about BGP route selection, see BGP overview in Layer 3—IP Routing Configuration Guide.
Restrictions and guidelines
If you configure both the bestroute encap-type preferred command and the bestroute nexthop-type preferred command, BGP selects the optimal route in the VPN instance by using the following procedure:
1. Drops the route with an unreachable NEXT_HOP.
2. Selects the route with the highest Preferred-value.
3. Uses the optimal route selection rule configured by the bestroute encap-type command: prefers to use an MPLS-encapsulated or SRv6-encapsulated route.
4. Uses the optimal route selection rule configured by the bestroute nexthop-type command: prefers to use a route whose next hop is an IP address or a tunnel.
5. Selects the route with the highest LOCAL_PREF.
6. Proceeds with the subsequent steps in the original BGP route select procedure.
For more information about the bestroute nexthop-type command, see BGP commands in Layer 3—IP Routing Command Reference.
Procedure
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP-VPN instance view.
ip vpn-instance vpn-instance-name
4. Specify the packet encapsulation type preferred in optimal route selection.
bestroute encap-type { mpls | srv6 } [ preferred ]
By default, BGP does not select optimal routes according to the packet encapsulation type.
Enabling SRv6 TE policy logging
About this task
This feature enables the device to generate logs for SRv6 TE policy state changes and resource usage anomalies. The administrator can use the logging information to audit SRv6 TE policies. The device delivers logs to its information center. The information center processes the logs according to user-defined output rules (whether to output logs and where to output). For more information about the information center, see information center configuration in System Management Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enable SRv6 TE policy logging.
srv6-policy log enable
By default, SRv6 TE policy logging is disabled.
Enabling SNMP notifications for SRv6 TE policies
About this task
This feature enables the device to send SNMP notifications about state changes and resource usage anomalies of SRv6 TE policies. For SNMP notifications to be sent correctly, you must also configure SNMP on the device. For more information about SNMP configuration, see the network management and monitoring configuration guide for the device.
Procedure
1. Enter system view.
system-view
2. Enable SNMP notifications for SRv6 TE policies.
snmp-agent trap enable srv6-policy
By default, SNMP notifications for SRv6 TE policies are disabled.
Configuring traffic forwarding statistics for SRv6 TE policies
About this task
This feature collects statistics on the traffic forwarded by SRv6 TE policies.
Restrictions and guidelines
You can configure traffic forwarding statistics for all SRv6 TE policies globally in SRv6 TE view or for a specific SRv6 TE policy in SRv6 TE policy view. The policy-specific configuration takes precedence over the global configuration. An SRv6 TE policy uses the global configuration only when it has no policy-specific configuration.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Enter SRv6 TE view.
traffic-engineering
4. Enable traffic forwarding statistics for all SRv6 TE policies.
srv6-policy forwarding statistics [ service-class ] enable
By default, traffic forwarding statistics is disabled for all SRv6 TE policies.
If you specify the service-class keyword, the device collects statistics on the total traffic as well as the traffic of each service class that are forwarded by SRv6 TE policies.
5. (Optional.) Set the traffic forwarding statistics interval for all SRv6 TE policies.
srv6-policy forwarding statistics interval interval
By default, the SRv6 TE policy forwarding statistics interval is 30 seconds.
6. Enter SRv6 TE policy view.
policy policy-name
7. Configure traffic forwarding statistics for the SRv6 TE policy.
forwarding statistics { disable | [ service-class ] enable }
By default, an SRv6 TE policy uses the traffic forwarding statistics configuration in SRv6 TE view.
If you specify the service-class keyword, the device collects statistics on the total traffic as well as the traffic of each service class that are forwarded by the SRv6 TE policy.
Verifying and maintaining SRv6 TE policies
Verifying the SRv6 TE policy operation status and configuration
Perform display tasks in any view:
· Display SRv6 TE policy information.
display segment-routing ipv6 te policy [ name policy-name | down | up | { color color-value | end-point ipv6 ip-address } * ]
· Display status information about SRv6 TE policies.
display segment-routing ipv6 te policy status [ policy-name policy-name ]
· Display SRv6 TE policy statistics.
display segment-routing ipv6 te policy statistics
· Display information about the most recent down event for SRv6 TE policies.
display segment-routing ipv6 te policy last-down-reason [ binding-sid bsid | color color-value endpoint ipv6 ipv6-address | policy-name policy-name ]
· Display SRv6-TE SID list information.
display segment-routing ipv6 te segment-list [ name seglist-name | id id-value ]
· Display SRv6 TE policy database information.
display segment-routing ipv6 te database [ link | node | prefix | srv6-sid ]
· Display information about SRv6 SIDs collected from the LS database.
display segment-routing ipv6 te source-sid [ end | end-x | sid ]
Verifying the SRv6 TE policy group operation status and configuration
Perform display tasks in any view:
· Display SRv6 TE policy group information:
display segment-routing ipv6 te policy-group [ group-id ] [ verbose ]
· Display information about the most recent down event for SRv6 TE policies:
display segment-routing ipv6 te policy-group last-down-reason [ group-id | endpoint ipv6-address color color-value ]
· Display SRv6 TE policy group statistics:
display segment-routing ipv6 te policy-group statistics
Verifying the BGP IPv6 SR policy routing configuration
Perform display tasks in any view:
· Display BGP IPv6 SR policy routing information.
display bgp [ instance instance-name ] routing-table ipv6 sr-policy [ sr-policy-prefix [ advertise-info | as-path | cluster-list | community | ext-community ] | { color color-value | end-point ipv6 ipv6-address } * | peer ipv6-address { advertised-routes | received-routes } [ statistics ] { color color-value | end-point ipv6 ipv6-address } * | statistics { color color-value | end-point ipv6 ipv6-address } * ]
display bgp [ instance instance-name ] routing-table ipv6 sr-policy [ statistics ] community [ community-number&<1-32> | aa:nn&<1-32> ] [ internet | no-advertise | no-export | no-export-subconfed ] [ whole-match ]
display bgp [ instance instance-name ] routing-table ipv6 sr-policy [ statistics ] community-list { basic-community-list-number | comm-list-name | adv-community-list-number } [ whole-match ]
display bgp [ instance instance-name ] routing-table ipv6 sr-policy [ statistics ] ext-community [ bandwidth link-bandwidth-value | color color | rt route-target | soo site-of-origin ]&<1-32> [ whole-match ]
· Display status and statistics information about a BGP IPv6 SR policy peer or peer group.
display bgp [ instance instance-name ] peer ipv6 sr-policy [ ipv6-address prefix-length | { ipv6-address | group-name group-name } log-info | [ ipv6-address ] verbose ]
· Display information about a BGP IPv6 SR policy peer group.
display bgp [ instance instance-name ] group ipv6 sr-policy [ group-name group-name ]
· Display information about a BGP IPv6 SR policy update group.
display bgp [ instance instance-name ] update-group ipv6 sr-policy [ ipv6-address ]
Verifying the SRv6 TE policy BFD and SBFD operation status
Perform display tasks in any view:
· Display BFD information for SRv6 TE policies.
display segment-routing ipv6 te bfd [ down | policy { { color color-value | end-point ipv6 ipv6-address } * | name policy-name } | up ]
· Display SBFD information for SRv6 TE policies.
display segment-routing ipv6 te sbfd [ down | policy { { color color-value | end-point ipv6 ipv6-address } * | name policy-name } | up ]
Verifying the SRv6 TE policy egress protection configuration
Perform display tasks in any view:
· Display remote SRv6 SIDs protected by mirror SIDs.
display bgp [ instance instance-name ] mirror remote-sid [ end-dt4 | end-dt46 | end-dt6 ] [ sid ]
· Display remote SRv6 SIDs protected by mirror SIDs on EVPN VPWS over SRv6 networks.
display evpn srv6 mirror remote-sid [ sid | type { end-dt2u | end-dx2 } ]
Displaying and clearing SRv6 TE policy forwarding statistics
To display SRv6 TE forwarding information, execute the following command in any view:
display segment-routing ipv6 te forwarding [ policy { name policy-name | { color color-value | end-point ipv6 ipv6-address } * } ] [ verbose ]
To clear traffic forwarding statistics of SRv6 TE policies, execute the following command in user view:
reset segment-routing ipv6 te forwarding statistics [ binding-sid binding-sid | color color-value endpoint endpoint-ipv6 | name name-value ]
Displaying SRv6 TE policy information for the PCE process
Perform display tasks in any view:
· Display SRv6 TE policy information stored in the PCE process.
display pce segment-routing ipv6 policy database [ color color-value endpoint ipv6 ipv6-address | policyname policy-name] [ verbose ]
· Display information about the SRv6 TE policy Initiate messages cached in the PCE process.
display pce segment-routing ipv6 policy initiate-cache
Displaying IPR-related information for SRv6 TE policies
Perform display tasks in any view:
· Display IPR policy information.
display segment-routing ipv6 te ipr [ name ipr-name ]
· Display iFIT measurement information for SRv6 TE policies.
display segment-routing ipv6 te policy ifit [ name policy-name | { color color-value | end-point ipv6 ipv6-address } * ]
SRv6 TE policy configuration examples
Example: Configuring SRv6 TE policy-based forwarding
Network configuration
As shown in Figure 18, perform the following tasks on the devices to implement SRv6 TE policy-based forwarding over a specific path:
· Configure Device A through Device D to run IS-IS to implement Layer 3 connectivity.
· Configure basic SRv6 on Device A through Device D.
· Configure an SRv6 TE policy on Device A to forward user packets along path Device A > Device B > Device C > Device D.
|
Device |
Interface |
IP address |
Device |
Interface |
IP address |
|
Device A |
Loop1 |
1::1/128 |
Device B |
Loop1 |
2::2/128 |
|
|
GE1/0/1 |
1000::1/64 |
|
GE1/0/1 |
1000::2/64 |
|
|
GE1/0/2 |
4000::1/64 |
|
GE1/0/2 |
2000::2/64 |
|
Device C |
Loop1 |
3::3/128 |
Device D |
Loop1 |
4::4/128 |
|
|
GE1/0/1 |
3000::3/64 |
|
GE1/0/1 |
3000::4/64 |
|
|
GE1/0/2 |
2000::3/64 |
|
GE1/0/2 |
4000::4/64 |
Procedure
1. Configure IP addresses and masks for interfaces. (Details not shown.)
2. Configure Device A:
# Configure an SRv6 SID list.
[DeviceA] segment-routing ipv6
[DeviceA-segment-routing-ipv6] encapsulation source-address 1::1
[DeviceA-segment-routing-ipv6] locator a ipv6-prefix 5000:: 64 static 32
[DeviceA-segment-routing-ipv6-locator-a] opcode 1 end no-flavor
[DeviceA-segment-routing-ipv6-locator-a] quit
[DeviceA-segment-routing-ipv6] traffic-engineering
[DeviceA-srv6-te] srv6-policy locator a
[DeviceA-srv6-te] segment-list s1
[DeviceA-srv6-te-sl-s1] index 10 ipv6 6000::1
[DeviceA-srv6-te-sl-s1] index 20 ipv6 7000::1
[DeviceA-srv6-te-sl-s1] index 30 ipv6 8000::1
[DeviceA-srv6-te-sl-s1] quit
# Create an SRv6 TE policy and set the attributes.
[DeviceA-srv6-te] policy p1
[DeviceA-srv6-te-policy-p1] binding-sid ipv6 5000::2
[DeviceA-srv6-te-policy-p1] color 10 end-point ipv6 4::4
[DeviceA-srv6-te-policy-p1] candidate-paths
[DeviceA-srv6-te-policy-p1-path] preference 10
[DeviceA-srv6-te-policy-p1-path-pref-10] explicit segment-list s1
[DeviceA-srv6-te-policy-p1-path-pref-10] quit
[DeviceA-srv6-te-policy-p1-path] quit
[DeviceA-srv6-te-policy-p1] quit
[DeviceA-srv6-te] quit
[DeviceA-segment-routing-ipv6] quit
# Configure IS-IS and set the IS-IS cost style to wide.
<DeviceA> system-view
[DeviceA] isis 1
[DeviceA-isis-1] network-entity 00.0000.0000.0001.00
[DeviceA-isis-1] cost-style wide
[DeviceA-isis-1] address-family ipv6 unicast
[DeviceA-isis-1-ipv6] segment-routing ipv6 locator a
[DeviceA-isis-1-ipv6] quit
[DeviceA-isis-1] quit
[DeviceA] interface gigabitethernet 1/0/1
[DeviceA-GigabitEthernet1/0/1] isis ipv6 enable 1
[DeviceA-GigabitEthernet1/0/1] quit
[DeviceA] interface gigabitethernet 1/0/2
[DeviceA-GigabitEthernet1/0/2] isis ipv6 enable 1
[DeviceA-GigabitEthernet1/0/2] quit
[DeviceA] interface loopback 1
[DeviceA-LoopBack1] isis ipv6 enable 1
[DeviceA-LoopBack1] quit
3. Configure Device B:
# Configure the SRv6 End.SID.
[DeviceB] segment-routing ipv6
[DeviceB-segment-routing-ipv6] locator b ipv6-prefix 6000:: 64 static 32
[DeviceB-segment-routing-ipv6-locator-b] opcode 1 end no-flavor
[DeviceB-segment-routing-ipv6-locator-b] quit
[DeviceB-segment-routing-ipv6] quit
# Configure IS-IS and set the IS-IS cost style to wide.
<DeviceB> system-view
[DeviceB] isis 1
[DeviceB-isis-1] network-entity 00.0000.0000.0002.00
[DeviceB-isis-1] cost-style wide
[DeviceB-isis-1] address-family ipv6 unicast
[DeviceB-isis-1-ipv6] segment-routing ipv6 locator b
[DeviceB-isis-1-ipv6] quit
[DeviceB-isis-1] quit
[DeviceB] interface gigabitethernet 1/0/1
[DeviceB-GigabitEthernet1/0/1] isis ipv6 enable 1
[DeviceB-GigabitEthernet1/0/1] quit
[DeviceB] interface gigabitethernet 1/0/2
[DeviceB-GigabitEthernet1/0/2] isis ipv6 enable 1
[DeviceB-GigabitEthernet1/0/2] quit
[DeviceB] interface loopback 1
[DeviceB-LoopBack1] isis ipv6 enable 1
[DeviceB-LoopBack1] quit
4. Configure Device C:
# Configure the SRv6 End.SID.
[DeviceC] segment-routing ipv6
[DeviceC-segment-routing-ipv6] locator c ipv6-prefix 7000:: 64 static 32
[DeviceC-segment-routing-ipv6-locator-c] opcode 1 end no-flavor
[DeviceC-segment-routing-ipv6-locator-c] quit
[DeviceC-segment-routing-ipv6] quit
# Configure IS-IS and set the IS-IS cost style to wide.
<DeviceC> system-view
[DeviceC] isis 1
[DeviceC-isis-1] network-entity 00.0000.0000.0003.00
[DeviceC-isis-1] cost-style wide
[DeviceC-isis-1] address-family ipv6 unicast
[DeviceC-isis-1-ipv6] segment-routing ipv6 locator c
[DeviceC-isis-1-ipv6] quit
[DeviceC-isis-1] quit
[DeviceC] interface gigabitethernet 1/0/1
[DeviceC-GigabitEthernet1/0/1] isis ipv6 enable 1
[DeviceC-GigabitEthernet1/0/1] quit
[DeviceC] interface gigabitethernet 1/0/2
[DeviceC-GigabitEthernet1/0/2] isis ipv6 enable 1
[DeviceC-GigabitEthernet1/0/2] quit
[DeviceC] interface loopback 1
[DeviceC-LoopBack1] isis ipv6 enable 1
[DeviceC-LoopBack1] quit
5. Configure Device D:
# Configure the SRv6 End.SID.
[DeviceD] segment-routing ipv6
[DeviceD-segment-routing-ipv6] locator d ipv6-prefix 8000:: 64 static 32
[DeviceD-segment-routing-ipv6-locator-d] opcode 1 end no-flavor
[DeviceD-segment-routing-ipv6-locator-d] quit
[DeviceD-segment-routing-ipv6] quit
# Configure IS-IS and set the IS-IS cost style to wide.
<DeviceD> system-view
[DeviceD] isis 1
[DeviceD-isis-1] network-entity 00.0000.0000.0004.00
[DeviceD-isis-1] cost-style wide
[DeviceD-isis-1] address-family ipv6 unicast
[DeviceD-isis-1-ipv6] segment-routing ipv6 locator d
[DeviceD-isis-1-ipv6] quit
[DeviceD-isis-1] quit
[DeviceD] interface gigabitethernet 1/0/1
[DeviceD-GigabitEthernet1/0/1] isis ipv6 enable 1
[DeviceD-GigabitEthernet1/0/1] quit
[DeviceD] interface gigabitethernet 1/0/2
[DeviceD-GigabitEthernet1/0/2] isis ipv6 enable 1
[DeviceD-GigabitEthernet1/0/2] quit
[DeviceD] interface loopback 1
[DeviceD-LoopBack1] isis ipv6 enable 1
[DeviceD-LoopBack1] quit
Verifying the configuration
# Display SRv6 TE policy information on Device A.
[DeviceA] display segment-routing ipv6 te policy
Name/ID: p1/0
Color: 10
Endpoint: 4::4
Name from BGP:
BSID:
Mode: Explicit Type: Type_2 Request state: Succeeded
Current BSID: 5000::2 Explicit BSID: 5000::2 Dynamic BSID: -
Reference counts: 4
Flags: A/BS/NC
Status: Up
AdminStatus: Up
Up time: 2020-04-02 16:08:03
Down time: 2020-04-02 16:03:48
Hot backup: Disabled
Statistics: Disabled
Statistics by service class: Disabled
Path verification: Disabled
Forwarding ignore last SID: Disabled
Drop-upon-invalid: Disabled
BFD trigger path-down: Disabled
SBFD: Disabled
BFD Echo: Disabled
Forwarding index: 2150629377
Association ID: 1
Service-class: -
Rate-limit: 15000 kbps
PCE delegation: Disabled
PCE delegate report-only: Disabled
Encaps reduced: Disabled
Encaps include local End.X: Disabled
Candidate paths state: Configured
Candidate paths statistics:
CLI paths: 1 BGP paths: 0 PCEP paths: 0
Candidate paths:
Preference : 10
CPathName:
ProtoOrigin: CLI Discriminator: 30
Instance ID: 0 Node address: 0.0.0.0
Originator: 0, ::
Optimal: Y Flags: V/A
Dynamic: Not configured
PCEP: Not configured
Explicit SID list:
ID: 1 Name: s1
Weight: 1 Forwarding index: 2149580801
State: Up State(-): -
Verification State: -
Active path MTU: 1280 bytes
The output shows that the SRv6 TE policy is in up state. The device can use the SRv6 TE policy to forward packets.
# Display SRv6 TE forwarding information on Device A.
[DeviceA] display segment-routing ipv6 te forwarding verbose
Total forwarding entries: 1
Policy name/ID: p1/0
Binding SID: 5000::2
Policy forwarding index: 2150629377
Main path:
Seglist Name/ID: 1
Seglist forwarding index: 2149580801
Weight: 1
Outgoing forwarding index: 2148532225
Interface: GE1/0/1
Nexthop: FE80::54CB:70FF:FE86:316
Path ID: 0
SID list: {6000::1, 7000::1, 8000::1}
# Display SRv6 forwarding information on Device A.
[DeviceA] display segment-routing ipv6 forwarding
Total SRv6 forwarding entries: 3
Flags: T - Forwarded through a tunnel
N - Forwarded through the outgoing interface to the nexthop IP address
A - Active forwarding information
B - Backup forwarding information
ID FWD-Type Flags Forwarding info
--------------------------------------------------------------------------------
2148532225 SRv6PSIDList NA GE1/0/1
FE80::54CB:70FF:FE86:316
{6000::1, 7000::1, 8000::1}
2149580801 SRv6PCPath TA 2148532225
2150629377 SRv6Policy TA 2149580801
Example: Configuring SRv6 TE policy egress protection
Network configuration
As shown in Figure 19, deploy an SRv6 TE policy in both directions between PE 1 and PE 2 to carry the L3VPN service. PE 2 is the egress node of the SRv6 TE policy. To improve the forwarding reliability, configure PE 3 to protect PE 2.
Table 1 Interface and IP address
|
Device |
Interface |
IP Address |
Device |
Interface |
IP Address |
|
CE 1 |
GE1/0/1 |
10.1.1.2/24 |
PE 2 |
Loop0 |
3::3/128 |
|
PE 1 |
Loop0 |
1::1/128 |
|
GE1/0/1 |
10.2.1.1/24 |
|
|
GE1/0/1 |
10.1.1.1/24 |
|
GE1/0/2 |
2002::1/64 |
|
|
GE1/0/2 |
2001::1/96 |
|
GE1/0/3 |
2004::2/96 |
|
P |
Loop0 |
2::2/128 |
PE 3 |
Loop0 |
4::4/128 |
|
|
GE1/0/1 |
2001::2/96 |
|
GE1/0/1 |
10.3.1.1/24 |
|
|
GE1/0/2 |
2002::2/64 |
|
GE1/0/2 |
2003::1/96 |
|
|
GE1/0/3 |
2003::2/96 |
|
GE1/0/3 |
2004::1/96 |
|
|
|
|
CE 2 |
GE1/0/1 |
10.2.1.2/24 |
|
|
|
|
|
GE1/0/2 |
10.3.1.2/24 |
Prerequisites
Configure interface addresses as shown in Table 1.
Procedure
1. Configure CE 1:
# Establish an EBGP peer relationship with PE 1 and redistribute the VPN routes.
<CE1> system-view
[CE1] bgp 65410
[CE1-bgp-default] peer 10.1.1.1 as-number 100
[CE1-bgp-default] address-family ipv4 unicast
[CE1-bgp-default-ipv4] peer 10.1.1.1 enable
[CE1-bgp-default-ipv4] import-route direct
[CE1-bgp-default-ipv4] quit
[CE1-bgp-default] quit
2. Configure PE 1:
# Configure IPv6 IS-IS for backbone network connectivity.
<PE1> system-view
[PE1] isis 1
[PE1-isis-1] is-level level-1
[PE1-isis-1] cost-style wide
[PE1-isis-1] network-entity 10.1111.1111.1111.00
[PE1-isis-1] address-family ipv6 unicast
[PE1-isis-1-ipv6] quit
[PE1-isis-1] quit
[PE1] interface loopback 0
[PE1-LoopBack0] ipv6 address 1::1 128
[PE1-LoopBack0] isis ipv6 enable 1
[PE1-LoopBack0] quit
[PE1] interface gigabitethernet 1/0/2
[PE1-GigabitEthernet1/0/2] ipv6 address 2001::1 96
[PE1-GigabitEthernet1/0/2] isis ipv6 enable 1
[PE1-GigabitEthernet1/0/2] quit
# Configure a VPN instance and bind it to the CE-facing interface.
[PE1] ip vpn-instance vpn1
[PE1-vpn-instance-vpn1] route-distinguisher 100:1
[PE1-vpn-instance-vpn1] vpn-target 111:1
[PE1-vpn-instance-vpn1] quit
[PE1] interface gigabitethernet 1/0/1
[PE1-GigabitEthernet1/0/1] ip binding vpn-instance vpn1
[PE1-GigabitEthernet1/0/1] ip address 10.1.1.1 24
[PE1-GigabitEthernet1/0/1] quit
# Establish an EBGP peer relationship with the connected CE to redistribute the VPN routes.
[PE1] bgp 100
[PE1-bgp-default] router-id 1.1.1.1
[PE1-bgp-default] ip vpn-instance vpn1
[PE1-bgp-default-vpn1] peer 10.1.1.2 as-number 65410
[PE1-bgp-default-vpn1] address-family ipv4 unicast
[PE1-bgp-default-ipv4-vpn1] peer 10.1.1.2 enable
[PE1-bgp-default-ipv4-vpn1] quit
[PE1-bgp-default-vpn1] quit
# Establish MP-IBGP peer relationships with the peer PEs.
[PE1] bgp 100
[PE1-bgp-default] peer 3::3 as-number 100
[PE1-bgp-default] peer 4::4 as-number 100
[PE1-bgp-default] peer 3::3 connect-interface loopback 0
[PE1-bgp-default] peer 4::4 connect-interface loopback 0
[PE1-bgp-default] address-family vpnv4
[PE1-bgp-default-vpnv4] peer 3::3 enable
[PE1-bgp-default-vpnv4] peer 4::4 enable
[PE1-bgp-default-vpnv4] quit
[PE1-bgp-default] quit
# Configure L3VPN over SRv6 TE policy.
[PE1] segment-routing ipv6
[PE1-segment-routing-ipv6] encapsulation source-address 1::1
[PE1-segment-routing-ipv6] locator aaa ipv6-prefix 1:2::1:0 96 static 8
[PE1-segment-routing-ipv6-locator-aaa] opcode 1 end-dt4 vpn-instance vpn1
[PE1-segment-routing-ipv6-locator-aaa] quit
[PE1-segment-routing-ipv6] quit
[PE1] bgp 100
[PE1-bgp-default] address-family vpnv4
[PE1-bgp-default-vpnv4] peer 3::3 prefix-sid
[PE1-bgp-default-vpnv4] peer 4::4 prefix-sid
[PE1-bgp-default-vpnv4] quit
[PE1-bgp-default] ip vpn-instance vpn1
[PE1-bgp-default-vpn1] address-family ipv4 unicast
[PE1-bgp-default-ipv4-vpn1] segment-routing ipv6 traffic-engineering best-effort
[PE1-bgp-default-ipv4-vpn1] segment-routing ipv6 locator aaa
[PE1-bgp-default-ipv4-vpn1] quit
[PE1-bgp-default-vpn1] quit
[PE1-bgp-default] quit
[PE1] isis 1
[PE1-isis-1] address-family ipv6 unicast
[PE1-isis-1-ipv6] segment-routing ipv6 locator aaa
[PE1-isis-1-ipv6] quit
[PE1-isis-1] quit
# Configure an SRv6 TE policy.
[PE1] segment-routing ipv6
[PE1-segment-routing-ipv6] traffic-engineering
[PE1-srv6-te] srv6-policy locator aaa
[PE1-srv6-te] segment-list s1
[PE1-srv6-te-s1-s1] index 10 ipv6 100:abc:1::1
[PE1-srv6-te-s1-s1] index 20 ipv6 6:5::1:2
[PE1-srv6-te-s1-s1] quit
[PE1-srv6-te] policy p1
[PE1-srv6-te-policy-p1] binding-sid ipv6 1:2::1:2
[PE1-srv6-te-policy-p1] color 10 end-point ipv6 3::3
[PE1-srv6-te-policy-p1] candidate-paths
[PE1-srv6-te-policy-p1-path] preference 10
[PE1-srv6-te-policy-p1-path-pref-10] explicit segment-list s1
[PE1-srv6-te-policy-p1-path-pref-10] quit
[PE1-srv6-te-policy-p1-path] quit
[PE1-srv6-te-policy-p1] quit
[PE1-srv6-te] quit
[PE1-segment-routing-ipv6] quit
3. Configure the P device:
# Configure IPv6 IS-IS for backbone network connectivity.
<P> system-view
[P] isis 1
[P-isis-1] is-level level-1
[P-isis-1] cost-style wide
[P-isis-1] network-entity 10.2222.2222.2222.00
[P-isis-1] address-family ipv6 unicast
[P-isis-1-ipv6] quit
[P-isis-1] quit
[P] interface loopback 0
[P-LoopBack0] ipv6 address 2::2 128
[P-LoopBack0] isis ipv6 enable 1
[P-LoopBack0] quit
[P] interface gigabitethernet 1/0/1
[P-GigabitEthernet1/0/1] ipv6 address 2001::2 96
[P-GigabitEthernet1/0/1] isis ipv6 enable 1
[P-GigabitEthernet1/0/1] quit
[P] interface gigabitethernet 1/0/2
[P-GigabitEthernet1/0/2] ipv6 address 2002::2 96
[P-GigabitEthernet1/0/2] isis ipv6 enable 1
[P-GigabitEthernet1/0/2] quit
[P] interface gigabitethernet 1/0/3
[P-GigabitEthernet1/0/3] ipv6 address 2003::2 96
[P-GigabitEthernet1/0/3] isis ipv6 enable 1
[P-GigabitEthernet1/0/3] quit
# Configure SRv6.
[P] segment-routing ipv6
[P-segment-routing-ipv6] locator p ipv6-prefix 100:abc:1::0 96 static 8
[P-segment-routing-ipv6-locator-p] opcode 1 end no-flavor
[P-segment-routing-ipv6-locator-p] quit
[P-segment-routing-ipv6] quit
[P] isis 1
[P-isis-1] address-family ipv6 unicast
[P-isis-1-ipv6] segment-routing ipv6 locator p
# Configure the FRR backup nexthop information and enable egress protection.
[P-isis-1-ipv6] fast-reroute lfa level-1
[P-isis-1-ipv6] fast-reroute ti-lfa
[P-isis-1-ipv6] fast-reroute mirror enable
[P-isis-1-ipv6] quit
[P-isis-1] quit
4. Configure PE 2:
# Configure IPv6 IS-IS for backbone network connectivity.
<PE2> system-view
[PE2] isis 1
[PE2-isis-1] is-level level-1
[PE2-isis-1] cost-style wide
[PE2-isis-1] network-entity 10.3333.3333.3333.00
[PE2-isis-1] address-family ipv6 unicast
[PE2-isis-1-ipv6] quit
[PE2-isis-1] quit
[PE2] interface loopback 0
[PE2-LoopBack0] ipv6 address 3::3 128
[PE2-LoopBack0] isis ipv6 enable 1
[PE2-LoopBack0] quit
[PE2] interface gigabitethernet 1/0/2
[PE2-GigabitEthernet1/0/2] ipv6 address 2002::1 96
[PE2-GigabitEthernet1/0/2] isis ipv6 enable 1
[PE2-GigabitEthernet1/0/2] quit
[PE2] interface gigabitethernet 1/0/3
[PE2-GigabitEthernet1/0/3] ipv6 address 2004::2 96
[PE2-GigabitEthernet1/0/3] isis ipv6 enable 1
[PE2-GigabitEthernet1/0/3] quit
# Configure a VPN instance and bind it to the CE-facing interface.
[PE2] ip vpn-instance vpn1
[PE2-vpn-instance-vpn1] route-distinguisher 100:1
[PE2-vpn-instance-vpn1] vpn-target 111:1
[PE2-vpn-instance-vpn1] quit
[PE2] interface gigabitethernet 1/0/1
[PE2-GigabitEthernet1/0/1] ip binding vpn-instance vpn1
[PE2-GigabitEthernet1/0/1] ip address 10.2.1.1 24
[PE2-GigabitEthernet1/0/1] quit
# Establish an EBGP peer relationship with the connected CE to redistribute the VPN routes.
[PE2] bgp 100
[PE2-bgp-default] router-id 2.2.2.2
[PE2-bgp-default] ip vpn-instance vpn1
[PE2-bgp-default-vpn1] peer 10.2.1.2 as-number 65420
[PE2-bgp-default-vpn1] address-family ipv4 unicast
[PE2-bgp-default-ipv4-vpn1] peer 10.2.1.2 enable
[PE2-bgp-default-ipv4-vpn1] quit
[PE2-bgp-default-vpn1] quit
# Establish MP-IBGP peer relationships with the peer PEs.
[PE2] bgp 100
[PE2-bgp-default] peer 1::1 as-number 100
[PE2-bgp-default] peer 4::4 as-number 100
[PE2-bgp-default] peer 1::1 connect-interface loopback 0
[PE2-bgp-default] peer 4::4 connect-interface loopback 0
[PE2-bgp-default] address-family vpnv4
[PE2-bgp-default-vpnv4] peer 1::1 enable
[PE2-bgp-default-vpnv4] peer 4::4 enable
[PE2-bgp-default-vpnv4] quit
[PE2-bgp-default] quit
# Configure L3VPN over SRv6 TE policy.
[PE2] segment-routing ipv6
[PE2-segment-routing-ipv6] encapsulation source-address 3::3
[PE2-segment-routing-ipv6] locator bbb ipv6-prefix 6:5::1:0 96 static 8
[PE2-segment-routing-ipv6-locator-bbb] opcode 1 end-dt4 vpn-instance vpn1
[PE2-segment-routing-ipv6-locator-bbb] opcode 2 end no-flavor
[PE2-segment-routing-ipv6-locator-bbb] quit
[PE2-segment-routing-ipv6] quit
[PE2] bgp 100
[PE2-bgp-default] address-family vpnv4
[PE2-bgp-default-vpnv4] peer 1::1 prefix-sid
[PE2-bgp-default-vpnv4] peer 4::4 prefix-sid
[PE2-bgp-default-vpnv4] quit
[PE2-bgp-default] ip vpn-instance vpn1
[PE2-bgp-default-vpn1] address-family ipv4 unicast
[PE2-bgp-default-ipv4-vpn1] segment-routing ipv6 traffic-engineering best-effort
[PE2-bgp-default-ipv4-vpn1] segment-routing ipv6 locator bbb
[PE2-bgp-default-ipv4-vpn1] quit
[PE2-bgp-default-vpn1] quit
[PE2-bgp-default] quit
[PE2] isis 1
[PE2-isis-1] address-family ipv6 unicast
[PE2-isis-1-ipv6] segment-routing ipv6 locator bbb
[PE2-isis-1-ipv6] quit
[PE2-isis-1] quit
5. Configure PE 3:
# Configure IPv6 IS-IS for backbone network connectivity.
<PE3> system-view
[PE3] isis 1
[PE3-isis-1] is-level level-1
[PE3-isis-1] cost-style wide
[PE3-isis-1] network-entity 10.4444.4444.4444.00
[PE3-isis-1] address-family ipv6 unicast
[PE3-isis-1-ipv6] quit
[PE3-isis-1] quit
[PE3] interface loopback 0
[PE3-LoopBack0] ipv6 address 4::4 128
[PE3-LoopBack0] isis ipv6 enable 1
[PE3-LoopBack0] quit
[PE3] interface gigabitethernet 1/0/2
[PE3-GigabitEthernet1/0/2] ipv6 address 2003::1 96
[PE3-GigabitEthernet1/0/2] isis ipv6 enable 1
[PE3-GigabitEthernet1/0/2] quit
[PE3] interface gigabitethernet 1/0/3
[PE3-GigabitEthernet1/0/3] ipv6 address 2004::1 96
[PE3-GigabitEthernet1/0/3] isis ipv6 enable 1
[PE3-GigabitEthernet1/0/3] quit
# Configure a VPN instance and bind it to the CE-facing interface.
[PE3] ip vpn-instance vpn1
[PE3-vpn-instance-vpn1] route-distinguisher 100:1
[PE3-vpn-instance-vpn1] vpn-target 111:1
[PE3-vpn-instance-vpn1] quit
[PE3] interface gigabitethernet 1/0/1
[PE3-GigabitEthernet1/0/1] ip binding vpn-instance vpn1
[PE3-GigabitEthernet1/0/1] ip address 10.3.1.1 24
[PE3-GigabitEthernet1/0/1] quit
# Establish an EBGP peer relationship with the connected CE to redistribute the VPN routes.
[PE3] bgp 100
[PE3-bgp-default] router-id 3.3.3.3
[PE3-bgp-default] ip vpn-instance vpn1
[PE3-bgp-default-vpn1] peer 10.3.1.2 as-number 65420
[PE3-bgp-default-vpn1] address-family ipv4 unicast
[PE3-bgp-default-ipv4-vpn1] peer 10.3.1.2 enable
[PE3-bgp-default-ipv4-vpn1] quit
[PE3-bgp-default-vpn1] quit
# Establish MP-IBGP peer relationships with the peer PEs.
[PE3] bgp 100
[PE3-bgp-default] peer 1::1 as-number 100
[PE3-bgp-default] peer 3::3 as-number 100
[PE3-bgp-default] peer 1::1 connect-interface loopback 0
[PE3-bgp-default] peer 3::3 connect-interface loopback 0
[PE3-bgp-default] address-family vpnv4
[PE3-bgp-default-vpnv4] peer 1::1 enable
[PE3-bgp-default-vpnv4] peer 3::3 enable
[PE3-bgp-default-vpnv4] quit
[PE3-bgp-default] quit
# Configure the source address in the outer IPv6 header of SRv6 VPN packets.
[PE3] segment-routing ipv6
[PE3-segment-routing-ipv6] encapsulation source-address 4::4
# Configure an End.M SID to protect PE 2.
[PE3-segment-routing-ipv6] locator ccc ipv6-prefix 9:7::1:0 96 static 8
[PE3-segment-routing-ipv6-locator-ccc] opcode 1 end-m mirror-locator 6:5::1:0 120
[PE3-segment-routing-ipv6-locator-ccc] quit
[PE3-segment-routing-ipv6] quit
# Recurse the VPN routes to the End.M SID route.
[PE3] bgp 100
[PE3-bgp-default] address-family vpnv4
[PE3-bgp-default-vpnv4] peer 1::1 prefix-sid
[PE3-bgp-default-vpnv4] peer 3::3 prefix-sid
[PE3-bgp-default-vpnv4] quit
[PE3-bgp-default] ip vpn-instance vpn1
[PE3-bgp-default-vpn1] address-family ipv4 unicast
[PE3-bgp-default-ipv4-vpn1] segment-routing ipv6 locator ccc
[PE3-bgp-default-ipv4-vpn1] quit
[PE3-bgp-default-vpn1] quit
[PE3-bgp-default] quit
[PE3] isis 1
[PE3-isis-1] address-family ipv6 unicast
[PE3-isis-1-ipv6] segment-routing ipv6 locator ccc
[PE3-isis-1-ipv6] quit
[PE3-isis-1] quit
6. Configure CE 2:
# Establish an EBGP peer relationship with PEs and redistribute the VPN routes.
<CE2> system-view
[CE2] bgp 65420
[CE2-bgp-default] peer 10.2.1.1 as-number 100
[CE2-bgp-default] peer 10.3.1.1 as-number 100
[CE2-bgp-default] address-family ipv4 unicast
[CE2-bgp-default-ipv4] peer 10.2.1.1 enable
[CE2-bgp-default-ipv4] peer 10.3.1.1 enable
[CE2-bgp-default-ipv4] import-route direct
[CE2-bgp-default-ipv4] quit
[CE2-bgp-default] quit
Verifying the configuration
# Display the SRv6 TE policy configuration. The output shows that the SRv6 TE policy is up for traffic forwarding.
[PE1] display segment-routing ipv6 te policy
Name/ID: p1/0
Color: 10
End-point: 3::3
Name from BGP:
BSID:
Mode: Explicit Type: Type_2 Request state: Succeeded
Current BSID: 1:2::1:2 Explicit BSID: 1:2::1:2 Dynamic BSID: -
Reference counts: 4
Flags: A/BS/NC
Status: Up
AdminStatus: Up
Up time: 2020-10-28 09:10:33
Down time: 2020-10-28 09:09:32
Hot backup: Disabled
Statistics: Disabled
Statistics by service class: Disabled
Path verification: Disabled
Forwarding ignore last SID: Disabled
Drop-upon-invalid: Disabled
BFD trigger path-down: Disabled
SBFD: Disabled
BFD Echo: Disabled
Forwarding index: 2150629377
Association ID: 1
Service-class: -
Rate-limit: -
PCE delegation: Disabled
PCE delegate report-only: Disabled
Encaps reduced: Disabled
Encaps include local End.X: Disabled
Candidate paths state: Configured
Candidate paths statistics:
CLI paths: 1 BGP paths: 0 PCEP paths: 0 ODN paths: 0
Candidate paths:
Preference : 10
CPathName:
ProtoOrigin: CLI Discriminator: 30
Instance ID: 0 Node address: 0.0.0.0
Originator: 0, ::
Optimal: Y Flags: V/A
Dynamic: Not configured
PCEP: Not configured
Explicit SID list:
ID: 1 Name: s1
Weight: 1 Forwarding index: 2149580801
State: Up State(-): -
Verification State: -
Active path MTU: 1280 bytes
# Display SRv6 TE policy forwarding information on PE 1.
[PE1] display segment-routing ipv6 te forwarding verbose
Total forwarding entries: 1
Policy name/ID: p1/0
Binding SID: 1:2::1:2
Forwarding index: 2150629377
Main path:
Seglist Name/ID: 1
Seglist forwarding index: 2149580801
Weight: 1
Outgoing forwarding index: 2148532225
Interface: GE1/0/2
Nexthop: FE80::988A:B5FF:FED9:316
Path ID: 0
SID list: {100:ABC:1::1, 6:5::1:1}
# Display SRv6 TE policy forwarding path information on PE 1.
[PE1] display segment-routing ipv6 forwarding
Total SRv6 forwarding entries: 3
Flags: T - Forwarded through a tunnel
N - Forwarded through the outgoing interface to the nexthop IP address
A - Active forwarding information
B - Backup forwarding information
ID FWD-Type Flags Forwarding info
Attri-Val Attri-Val
--------------------------------------------------------------------------------
2148532225 SRv6PSIDList NA GE1/0/2
FE80::988A:B5FF:FED9:316
{100:ABC:1::1, 6:5::1:1}
2149580801 SRv6PCPath TA 2148532225
2150629377 SRv6Policy TA 2149580801
p1
# Display remote SRv6 SIDs protected by End.M SIDs on PE 3.
[PE3] display bgp mirror remote-sid
Remote SID: 6:5::1:1
Remote SID type: End.DT4
Mirror locator: 6:5::1:0/120
Vpn instance name: vpn1
# Display the End.M SID carried in the IS-IS IPv6 route on the P device.
[P] display isis route ipv6 6:5::1:0 120 verbose
Route information for IS-IS(1)
------------------------------
Level-1 IPv6 forwarding table
-----------------------------
IPv6 dest : 6:5::1:0/120
Flag : R/-/- Cost : 10
Admin tag : - Src count : 3
Nexthop : FE80::988A:BDFF:FEB6:417
Interface : GE1/0/2
Mirror FRR:
Interface : GE1/0/3
BkNextHop : FE80::988A:C6FF:FE0D:517
LsIndex : 0x80000001
Backup label stack(top->bottom): {9:7::1:1}
Nib ID : 0x24000006
Flags: D-Direct, R-Added to Rib, L-Advertised in LSPs, U-Up/Down Bit Set
Typically, VPN traffic from CE 1 to CE 2 is forwarded over the CE 1-PE 1-P-PE 2-CE 2 path. When PE 2 fails, the P device switches traffic to the mirror FRR path for the SRv6 TE policy when it detects that the next hop (PE 2) is unreachable.
# Shut down the interface that connects P to PE 2.
[P] interface gigabitethernet 1/0/2
[P-GigabitEthernet1/0/2] shut
[P-GigabitEthernet1/0/2] quit
# Display the IS-IS IPv6 route information. The output shows that the nexthop interface becomes the backup interface.
[P] display isis route ipv6 6:5::1:0 120 verbose
Route information for IS-IS(1)
------------------------------
Level-1 IPv6 forwarding table
-----------------------------
IPv6 dest : 6:5::1:0/120
Flag : R/-/- Cost : 20
Admin tag : - Src count : 3
Nexthop : FE80::988A:BDFF:FEB6:417
Interface : GE1/0/2
Mirror FRR:
Interface : GE1/0/3
BkNextHop : FE80::988A:C6FF:FE0D:517
LsIndex : 0x80000001
Backup label stack(top->bottom): {9:7::1:1}
Nib ID : 0x24000006
Flags: D-Direct, R-Added to Rib, L-Advertised in LSPs, U-Up/Down Bit Set
# Display SRv6 TE policy information on PE 1. The output shows that the SRv6 TE policy is still up.
[PE1] display segment-routing ipv6 te policy
Name/ID: p1/0
Color: 10
End-point: 3::3
Name from BGP:
BSID:
Mode: Explicit Type: Type_2 Request state: Succeeded
Current BSID: 1:2::1:2 Explicit BSID: 1:2::1:2 Dynamic BSID: -
Reference counts: 4
Flags: A/BS/NC
Status: Up
AdminStatus: Up
Up time: 2020-10-28 09:10:33
Down time: 2020-10-28 09:09:32
Hot backup: Disabled
Statistics: Disabled
Statistics by service class: Disabled
Path verification: Disabled
Forwarding ignore last SID: Disabled
Drop-upon-invalid: Disabled
BFD trigger path-down: Disabled
SBFD: Disabled
BFD Echo: Disabled
Forwarding index: 2150629377
Association ID: 1
Service-class: -
Rate-limit: -
PCE delegation: Disabled
PCE delegate report-only: Disabled
Encaps reduced: Disabled
Encaps include local End.X: Disabled
Candidate paths state: Configured
Candidate paths statistics:
CLI paths: 1 BGP paths: 0 PCEP paths: 0 ODN paths: 0
Candidate paths:
Preference : 10
CPathName:
ProtoOrigin: CLI Discriminator: 30
Instance ID: 0 Node address: 0.0.0.0
Originator: 0, ::
Optimal: Y Flags: V/A
Dynamic: Not configured
PCEP: Not configured
Explicit SID list:
ID: 1 Name: s1
Weight: 1 Forwarding index: 2149580801
State: Up State(-): -
Verification State: -
Active path MTU: 1280 bytes
Example: Configuring SRv6 TE policy through ODN
Network configuration
As shown in Figure 20, configuring automatic creation of SRv6 TE policies between Device B and Device E by using ODN to forward the traffic between Device A and Device F.
Table 2 Interface and IP address assignment
|
Device |
Interface |
IP Address |
Device |
Interface |
IP Address |
|
Device A |
GE1/0/1 |
1000::1/64 |
Device F |
GE1/0/1 |
6000::2/64 |
|
Device B |
Loop0 |
1::1/128 |
Device E |
Loop0 |
3::3/128 |
|
|
GE1/0/1 |
1000::2/64 |
|
GE1/0/1 |
6000::1/64 |
|
|
GE1/0/2 |
2000::1/64 |
|
GE1/0/2 |
4000::/64 |
|
|
GE1/0/3 |
3000::1/64 |
|
GE1/0/3 |
5000::1/64 |
|
Device C |
GE1/0/1 |
4000::2/64 |
Device D |
GE1/0/1 |
5000::2/64 |
|
|
GE1/0/2 |
2002::2/64 |
|
GE1/0/2 |
3000::2/64 |
Prerequisites
Configure interface addresses as shown in Table 2.
Proedure
1. Configure Device A:
# Configure IS-IS and set the IS-IS cost style to wide.
<DeviceA> system-view
[DeviceA] isis 1
[DeviceA-isis-1] cost-style wide
[DeviceA-isis-1] network-entity 00.0000.0000.0001.00
[DeviceA-isis-1] address-family ipv6 unicast
[DeviceA-isis-1-ipv6] quit
[DeviceA-isis-1] quit
[DeviceA] interface gigabitethernet 1/0/1
[DeviceA-GigabitEthernet1/0/1] isis ipv6 enable 1
[DeviceA-GigabitEthernet1/0/1] quit
2. Configure Device B:
# Configure IS-IS and set the IS-IS cost style to wide.
<DeviceB> system-view
[DeviceB] isis 1
[DeviceB-isis-1] cost-style wide
[DeviceB-isis-1] network-entity 00.0000.0000.0002.00
[DeviceB-isis-1] address-family ipv6 unicast
[DeviceB-isis-1-ipv6] quit
[DeviceB-isis-1] quit
[DeviceB] interface gigabitethernet 1/0/1
[DeviceB-GigabitEthernet1/0/1] isis ipv6 enable 1
[DeviceB-GigabitEthernet1/0/1] quit
[DeviceB] interface gigabitethernet 1/0/2
[DeviceB-GigabitEthernet1/0/2] isis ipv6 enable 1
[DeviceB-GigabitEthernet1/0/2] quit
[DeviceB] interface gigabitethernet 1/0/3
[DeviceB-GigabitEthernet1/0/3] isis ipv6 enable 1
[DeviceB-GigabitEthernet1/0/3] quit
[DeviceB] interface loopback 0
[DeviceB-LoopBack0] isis ipv6 enable 1
[DeviceB-LoopBack0] quit
# Establish a BGP peer relationship with Device E.
[DeviceB] bgp 100
[DeviceB-bgp-default] router-id 1.1.1.1
[DeviceB-bgp-default] peer 3::3 as-number 100
[DeviceB-bgp-default] peer 3::3 connect-interface loopback 0
[DeviceB-bgp-default] address-family ipv6
[DeviceB-bgp-default-ipv6] peer 3::3 enable
[DeviceB-bgp-default-ipv6] quit
[DeviceB-bgp-default] address-family ipv6 sr-policy
[DeviceB-bgp-default-srpolicy-ipv6] peer 3::3 enable
[DeviceB-bgp-default-srpolicy-ipv6] quit
[DeviceB-bgp-default] quit
# Configure an SRv6 locator.
[DeviceB] segment-routing ipv6
[DeviceB-segment-routing-ipv6] encapsulation source-address 1::1
[DeviceB-segment-routing-ipv6] locator b ipv6-prefix 20:1:: 96 static 24
[DeviceB-segment-routing-ipv6-locator-b] opcode 1 end no-flavor
[DeviceB-segment-routing-ipv6-locator-b] quit
[DeviceB-segment-routing-ipv6] quit
# Configure ODN to create an SRv6 TE policy automatically.
[DeviceB] segment-routing ipv6
[DeviceB-segment-routing-ipv6] traffic-engineering
[DeviceB-srv6-te] srv6-policy locator b
[DeviceB-srv6-te] on-demand color 1
# Enable path computation using PCE.
[DeviceB-srv6-te-odn-1] dynamic
[DeviceB-srv6-te-odn-1-dynamic] pcep
[DeviceB-srv6-te-odn-1] quit
[DeviceB-srv6-te] quit
[DeviceB-segment-routing-ipv6] quit
[DeviceB] isis 1
[DeviceB-isis-1] address-family ipv6 unicast
[DeviceB-isis-1-ipv6] segment-routing ipv6 locator b
[DeviceB-isis-1-ipv6] quit
[DeviceB-isis-1] quit
3. Configure Device C:
# Configure IS-IS and set the IS-IS cost style to wide.
<DeviceC> system-view
[DeviceC] isis 1
[DeviceC-isis-1] cost-style wide
[DeviceC-isis-1] network-entity 00.0000.0000.0003.00
[DeviceC-isis-1] address-family ipv6 unicast
[DeviceC-isis-1-ipv6] quit
[DeviceC-isis-1] quit
[DeviceC] interface gigabitethernet 1/0/1
[DeviceC-GigabitEthernet1/0/1] isis ipv6 enable 1
[DeviceC-GigabitEthernet1/0/1] quit
[DeviceC] interface gigabitethernet 1/0/2
[DeviceC-GigabitEthernet1/0/2] isis ipv6 enable 1
[DeviceC-GigabitEthernet1/0/2] quit
[DeviceC] interface loopback 0
[DeviceC-LoopBack1] isis ipv6 enable 1
[DeviceC-LoopBack1] quit
4. Configure Device D:
# Configure IS-IS and set the IS-IS cost style to wide.
<DeviceD> system-view
[DeviceD] isis 1
[DeviceD-isis-1] cost-style wide
[DeviceD-isis-1] network-entity 00.0000.0000.0004.00
[DeviceD-isis-1] address-family ipv6 unicast
[DeviceD-isis-1-ipv6] quit
[DeviceD-isis-1] quit
[DeviceD] interface gigabitethernet 1/0/1
[DeviceD-GigabitEthernet1/0/1] isis ipv6 enable 1
[DeviceD-GigabitEthernet1/0/1] quit
[DeviceD] interface gigabitethernet 1/0/2
[DeviceD-GigabitEthernet1/0/2] isis ipv6 enable 1
[DeviceD-GigabitEthernet1/0/2] quit
[DeviceD] interface loopback 0
[DeviceD-LoopBack0] isis ipv6 enable 1
[DeviceD-LoopBack0] quit
5. Configure Device E:
# Configure IS-IS and set the IS-IS cost style to wide.
<DeviceE> system-view
[DeviceE] isis 1
[DeviceE-isis-1] cost-style wide
[DeviceE-isis-1] network-entity 00.0000.0000.0005.00
[DeviceE-isis-1] address-family ipv6 unicast
[DeviceE-isis-1-ipv6] quit
[DeviceE-isis-1] quit
[DeviceE] interface gigabitethernet 1/0/1
[DeviceE-GigabitEthernet1/0/1] isis ipv6 enable 1
[DeviceE-GigabitEthernet1/0/1] quit
[DeviceE] interface gigabitethernet 1/0/2
[DeviceE-GigabitEthernet1/0/2] isis ipv6 enable 1
[DeviceE-GigabitEthernet1/0/2] quit
[DeviceE] interface gigabitethernet 1/0/3
[DeviceE-GigabitEthernet1/0/3] isis ipv6 enable 1
[DeviceE-GigabitEthernet1/0/3] quit
[DeviceE] interface loopback 0
[DeviceE-LoopBack0] isis ipv6 enable 1
[DeviceE-LoopBack0] quit
[DeviceE] interface loopback 1
[DeviceE-LoopBack1] ipv6 address 2::2 128
[DeviceE-LoopBack1] quit
# Establish a BGP peer relationship with Device B.
[DeviceE] bgp 100
[DeviceE-bgp-default] router-id 3.3.3.3
[DeviceE-bgp-default] peer 1::1 as-number 100
[DeviceE-bgp-default] peer 1::1 connect-interface loopback 0
[DeviceE-bgp-default] address-family ipv6
[DeviceE-bgp-default-ipv6] peer 1::1 enable
[DeviceE-bgp-default-ipv6] network 2::2 128
[DeviceE-bgp-default-ipv6] quit
[DeviceE-bgp-default] address-family ipv6 sr-policy
[DeviceE-bgp-default-srpolicy-ipv6] peer 1::1 enable
[DeviceE-bgp-default-srpolicy-ipv6] quit
[DeviceE-bgp-default] quit
# Configure a route policy to add a color attribute to the export routes.
[DeviceE] route-policy 1 permit node 10
[DeviceE-route-policy-1-10] apply extcommunity color 01:1
[DeviceE-route-policy-1-10] quit
[DeviceE] bgp 100
[DeviceE-bgp-default] address-family ipv6 unicast
[DeviceE-bgp-default-ipv6] peer 1::1 route-policy 1 export
[DeviceE-bgp-default-ipv6] peer 1::1 advertise-community
[DeviceE-bgp-default-ipv6] peer 1::1 advertise-ext-community
[DeviceE-bgp-default-ipv6] quit
[DeviceE-bgp-default] quit
6. Configure Device F:
# Configure IS-IS and set the IS-IS cost style to wide.
<DeviceF> system-view
[DeviceF] isis 1
[DeviceF-isis-1] network-entity 00.0000.0000.0006.00
[DeviceF-isis-1] cost-style wide
[DeviceF-isis-1] address-family ipv6 unicast
[DeviceF-isis-1-ipv6] quit
[DeviceF-isis-1] quit
[DeviceF] interface gigabitethernet 1/0/1
[DeviceF-GigabitEthernet1/0/1] isis ipv6 enable 1
[DeviceF-GigabitEthernet1/0/1] quit
Verifying the configuration
# Display information about the ODN-created SRv6 TE policy on Device B.
[DeviceB] display segment-routing ipv6 te policy
Name/ID: sr-1-3::3/0
Color: 1
End-point: 3::3
Name from BGP: sr-1-3::3
Name from PCE:
BSID:
Mode: Dynamic Type: Type_2 Request state: Succeeded
Current BSID: 20:1::100:0 Explicit BSID: - Dynamic BSID: 20:1::100:0
Reference counts: 4
Flags: A/BS/NC
Status: Up
AdminStatus: Up
Up time: 2020-12-01 15:58:12
Down time: 2020-12-01 15:58:12
Hot backup: Disabled
Statistics: Disabled
Statistics by service class: Disabled
Path verification: Disabled
Forwarding ignore last SID: Disabled
Drop-upon-invalid: Disabled
BFD trigger path-down: Disabled
SBFD: Disabled
BFD Echo: Disabled
Forwarding index: 2150629377
Association ID: 1
Service-class: -
Rate-limit: -
PCE delegation: Disabled
PCE delegate report-only: Disabled
Encaps reduced: Disabled
Encaps include local End.X: Disabled
Candidate paths state: Not configured
Candidate paths statistics:
CLI paths: 0 BGP paths: 0 PCEP paths: 0 ODN paths: 2
Candidate paths:
Preference : 100
CPathName: sr-1-3::3
ProtoOrigin: BGP Discriminator: 100
Instance ID: 0 Node address: 0.0.0.0
Originator: 0, ::
Optimal: N Flags: None
Dynamic: Configured
PCEP: Configured
Candidate paths:
Preference : 200
CPathName: sr-1-3::3
ProtoOrigin: BGP Discriminator: 200
Instance ID: 0 Node address: 0.0.0.0
Originator: 0, ::
Optimal: N Flags: BN
Dynamic: Not configured
PCEP: Not configured
# Display the forwarding path information of the SRv6 TE policy.
[DeviceB] display segment-routing ipv6 forwarding
Total SRv6 forwarding entries: 1
Flags: T - Forwarded through a tunnel
N - Forwarded through the outgoing interface to the nexthop IP address
A - Active forwarding information
B - Backup forwarding information
ID FWD-Type Flags Forwarding info
--------------------------------------------------------------------------------
2150630377 SRv6Policy TA 2149581800
# Display the forwarding information of the SRv6 TE policy.
[DeviceB] display segment-routing ipv6 te forwarding verbose
Total forwarding entries: 1
Policy name/ID: sr-1-3::3/1001
Binding SID: 20:1::100:0
Forwarding index: 2150630377
Main path:
Seglist Name/ID: 4369
Seglist forwarding index: 2149581800
Weight: 1
Outgoing forwarding index: 2148533223
Interface: GE1/0/3
Nexthop: FE80::7AAA:12FF:FED8:309
Path ID: 0
SID list: {6:5::1:5}
# Display BGP route information for the SRv6 TE policy.
[DeviceB] display bgp routing-table ipv6 3::3 128
BGP local router ID: 1.1.1.1
Local AS number: 100
Paths: 1 available, 1 best
BGP routing table information of 3::3/128:
From : 3::3 (2.2.2.2)
Rely nexthop : FE80::7AAA:12FF:FED8:309
Original nexthop: 3::3
Out interface : GigabitEthernet1/0/3
Route age : 00h17m00s
OutLabel : NULL
Ext-Community : <CO-Flag:Color(01:1)>
RxPathID : 0x0
TxPathID : 0xffffffff
AS-path : (null)
Origin : incomplete
Attribute value : MED 0, localpref 100, pref-val 0
State : valid, internal, not preferred for igp-cost, not ECMP for igp-cost
IP precedence : N/A
QoS local ID : N/A
Traffic index : N/A
Tunnel policy : gw
Rely tunnel IDs : 2150630377
Example: Configuring SRv6 TE policy-based forwarding with IPR
Network configuration
As shown in Figure 21:
· AS 100 is an IPv6 network and the private networks are IPv4 networks.
· PE 1, P 1, P 2, P 3, and PE 2 belong to one AS, and they run IS-IS for IPv6 network connectivity.
· An SRv6 TE policy group is created between PE 1 and PE 2. The SRv6 TE policy group contains three SRv6 TE policies with different forwarding paths to carry IPv4 L3VPN service traffic.
· Routing policies are configured on PE 1 and PE 2 to match color attribute values in VPNv4 routes and steer VPN traffic to the SRv6 TE policy group between PE 1 and PE 2.
· An IPR policy is configured for dynamic forwarding path selection.
The SRv6 TE policies are configured as follows:
· SRv6 TE policy A has one candidate path. The forwarding path represented by the SID list is PE 1 > P 1 > PE 2.
· SRv6 TE policy B has one candidate path. The forwarding path represented by the SID list is PE 1 > P 2 > PE 2.
· SRv6 TE policy C has one candidate path. The forwarding path represented by the SID list is PE 1 > P 3 > PE 2.
The IPR policy contains the following settings:
· The packet loss rate threshold is 5‰, delay threshold is 100 ms, jitter threshold is 10 ms, and CMI threshold is 110.
· The path selection priority is 1 for SRv6 TE policy A, 2 for SRv6 TE policy B, and 3 for SRv6 TE policy C.
|
Device |
Interface |
IP address |
Device |
Interface |
IP address |
|
CE 1 |
GE1/0/1 |
10.1.1.1/24 |
CE 2 |
GE1/0/2 |
20.1.1.1/24 |
|
|
Loop0 |
11.11.11.11/32 |
|
Loop0 |
22.22.22.22/32 |
|
PE 1 |
Loop1 |
1::1/128 |
P 1 |
Loop1 |
2::2/128 |
|
|
GE1/0/1 |
10.1.1.2/24 |
|
GE1/0/1 |
5001::2/96 |
|
|
GE1/0/2 |
2001::1/96 |
|
GE1/0/2 |
2001::2/96 |
|
|
GE1/0/3 |
3001::1/96 |
P 2 |
Loop1 |
4::4/128 |
|
|
GE1/0/4 |
4001::1/96 |
|
GE1/0/1 |
6001::2/96 |
|
PE 2 |
Loop1 |
3::3/128 |
|
GE1/0/2 |
3001::2/96 |
|
|
GE1/0/1 |
5001::1/96 |
P 3 |
Loop1 |
5::5/128 |
|
|
GE1/0/2 |
20.1.1.2/24 |
|
GE1/0/1 |
7001::2/96 |
|
|
GE1/0/3 |
6001::1/96 |
|
GE1/0/2 |
4001::2/96 |
|
|
GE1/0/4 |
7001::1/96 |
|
|
|
Procedure
1. Configure IPv6 addresses and prefix lengths for interfaces as shown in Figure 21. (Details not shown.)
2. Configure CE 1:
# Configure EBGP to advertise private routes to PE 1.
<CE1> system-view
[CE1] bgp 200
[CE1-bgp-default] router-id 11.11.11.11
[CE1-bgp-default] peer 10.1.1.2 as-number 100
[CE1-bgp-default] address-family ipv4 unicast
[CE1-bgp-default-ipv4] peer 10.1.1.2 enable
[CE1-bgp-default-ipv4] import-route direct
[CE1-bgp-default-ipv4] quit
[CE1-bgp-default] quit
3. Configure CE 2:
# Configure EBGP to advertise private routes to PE 2.
[CE2] bgp 300
[CE2-bgp-default] router-id 22.22.22.22
[CE2-bgp-default] peer 20.1.1.2 as-number 100
[CE2-bgp-default] address-family ipv4 unicast
[CE2-bgp-default-ipv4] peer 20.1.1.2 enable
[CE2-bgp-default-ipv4] import-route direct
[CE2-bgp-default-ipv4] quit
[CE2-bgp-default] quit
4. Configure PE 1:
# Configure IPv6 IS-IS for backbone network connectivity.
<PE1> system-view
[PE1] isis 1
[PE1-isis-1] cost-style wide
[PE1-isis-1] network-entity 00.0000.0000.0001.00
[PE1-isis-1] address-family ipv6 unicast
[PE1-isis-1-ipv6] quit
[PE1-isis-1] quit
[PE1] interface loopback 1
[PE1-LoopBack1] isis ipv6 enable 1
[PE1-LoopBack1] quit
[PE1] interface gigabitethernet 1/0/2
[PE1-GigabitEthernet1/0/2] isis ipv6 enable 1
[PE1-GigabitEthernet1/0/2] quit
[PE1] interface gigabitethernet 1/0/3
[PE1-GigabitEthernet1/0/3] isis ipv6 enable 1
[PE1-GigabitEthernet1/0/3] quit
[PE1] interface gigabitethernet 1/0/4
[PE1-GigabitEthernet1/0/4] isis ipv6 enable 1
[PE1-GigabitEthernet1/0/4] quit
# Configure a VPN instance to attach CE 1 to PE 1.
[PE1] ip vpn-instance vpn1
[PE1-vpn-instance-vpn1] route-distinguisher 100:1
[PE1-vpn-instance-vpn1] vpn-target 100:1
[PE1-vpn-instance-vpn1] quit
[PE1] interface gigabitethernet 1/0/1
[PE1-GigabitEthernet1/0/1] ip binding vpn-instance vpn1
[PE1-GigabitEthernet1/0/1] ip address 10.1.1.2 24
[PE1-GigabitEthernet1/0/1] quit
# Establish an EBGP peer relationship with CE 1 and import VPN routes.
[PE1] bgp 100
[PE1-bgp-default] router-id 1.1.1.1
[PE1-bgp-default] ip vpn-instance vpn1
[PE1-bgp-default-vpn1] peer 10.1.1.1 as-number 200
[PE1-bgp-default-vpn1] address-family ipv4 unicast
[PE1-bgp-default-ipv4-vpn1] peer 10.1.1.1 enable
[PE1-bgp-default-ipv4-vpn1] import-route direct
[PE1-bgp-default-ipv4-vpn1] quit
[PE1-bgp-default-vpn1] quit
# Establish an MP-IBGP peer relationship with PE 2.
[PE1-bgp-default] peer 3::3 as-number 100
[PE1-bgp-default] peer 3::3 connect-interface loopback 1
[PE1-bgp-default] address-family vpnv4
[PE1-bgp-default-vpnv4] peer 3::3 enable
[PE1-bgp-default-vpnv4] quit
[PE1-bgp-default] quit
# Recurse VPN routes between PE 1 and PE 2 to the SRv6 TE policy group.
[PE1] segment-routing ipv6
[PE1-segment-routing-ipv6] encapsulation source-address 1::1
[PE1-segment-routing-ipv6] locator abc ipv6-prefix 100:1:: 64 static 16
[PE1-segment-routing-ipv6-locator-abc] opcode 1 end no-flavor
[PE1-segment-routing-ipv6-locator-abc] quit
[PE1-segment-routing-ipv6] quit
[PE1] isis 1
[PE1-isis-1] address-family ipv6 unicast
[PE1-isis-1-ipv6] segment-routing ipv6 locator abc
[PE1-isis-1-ipv6] quit
[PE1-isis-1] quit
[PE1] bgp 100
[PE1-bgp-default] address-family vpnv4
[PE1-bgp-default-vpnv4] peer 3::3 prefix-sid
[PE1-bgp-default-vpnv4] quit
[PE1-bgp-default] ip vpn-instance vpn1
[PE1-bgp-default-vpn1] address-family ipv4 unicast
[PE1-bgp-default-ipv4-vpn1] segment-routing ipv6 locator abc
[PE1-bgp-default-ipv4-vpn1] segment-routing ipv6 traffic-engineering
[PE1-bgp-default-ipv4-vpn1] quit
[PE1-bgp-default-vpn1] quit
[PE1-bgp-default] quit
# Configure SRv6 TE policy A.
[PE1] segment-routing ipv6
[PE1-segment-routing-ipv6] traffic-engineering
[PE1-srv6-te] srv6-policy locator abc
[PE1-srv6-te] segment-list s1
[PE1-srv6-te-sl-s1] index 10 ipv6 200:1::1
[PE1-srv6-te-sl-s1] index 20 ipv6 300:1::1
[PE1-srv6-te-sl-s1] quit
[PE1-srv6-te] policy A
[PE1-srv6-te-policy-A] color 10 end-point ipv6 3::3
[PE1-srv6-te-policy-A] candidate-paths
[PE1-srv6-te-policy-A-path] preference 10
[PE1-srv6-te-policy-A-path-pref-10] explicit segment-list s1
[PE1-srv6-te-policy-A-path-pref-10] quit
[PE1-srv6-te-policy-A-path] quit
[PE1-srv6-te-policy-A] quit
[PE1-srv6-te] quit
[PE1-segment-routing-ipv6] quit
# Configure SRv6 TE policy B.
[PE1] segment-routing ipv6
[PE1-segment-routing-ipv6] traffic-engineering
[PE1-srv6-te] srv6-policy locator abc
[PE1-srv6-te] segment-list s2
[PE1-srv6-te-sl-s1] index 10 ipv6 400:1::1
[PE1-srv6-te-sl-s1] index 20 ipv6 300:1::1
[PE1-srv6-te-sl-s1] quit
[PE1-srv6-te] policy B
[PE1-srv6-te-policy-B] color 20 end-point ipv6 3::3
[PE1-srv6-te-policy-B] candidate-paths
[PE1-srv6-te-policy-B-path] preference 10
[PE1-srv6-te-policy-B-path-pref-10] explicit segment-list s2
[PE1-srv6-te-policy-B-path-pref-10] quit
[PE1-srv6-te-policy-B-path] quit
[PE1-srv6-te-policy-B] quit
[PE1-srv6-te] quit
[PE1-segment-routing-ipv6] quit
# Configure SRv6 TE policy C.
[PE1] segment-routing ipv6
[PE1-segment-routing-ipv6] traffic-engineering
[PE1-srv6-te] srv6-policy locator abc
[PE1-srv6-te] segment-list s3
[PE1-srv6-te-sl-s1] index 10 ipv6 500:1::1
[PE1-srv6-te-sl-s1] index 20 ipv6 300:1::1
[PE1-srv6-te-sl-s1] quit
[PE1-srv6-te] policy C
[PE1-srv6-te-policy-C] color 30 end-point ipv6 3::3
[PE1-srv6-te-policy-C] candidate-paths
[PE1-srv6-te-policy-C-path] preference 10
[PE1-srv6-te-policy-C-path-pref-10] explicit segment-list s3
[PE1-srv6-te-policy-C-path-pref-10] quit
[PE1-srv6-te-policy-C-path] quit
[PE1-srv6-te-policy-C] quit
[PE1-srv6-te] quit
[PE1-segment-routing-ipv6] quit
# Enable iFIT, configure the iFIT device ID, set the iFIT operating mode to analyzer, and globally enable iFIT packet loss measurement and iFIT delay and jitter measurement for SRv6 TE policies.
[PE1] ifit enable
[PE1-ifit] device-id 100
[PE1-ifit] work-mode analyzer
[PE1-ifit-analyzer] service-type srv6-segment-list
[PE1-ifit-analyzer] quit
[PE1-ifit] quit
[PE1] segment-routing ipv6
[PE1-segment-routing-ipv6] traffic-engineering
[PE1-srv6-te] srv6-policy ifit loss-measure enable
[PE1-srv6-te] srv6-policy ifit delay-measure enable
[PE1-srv6-te] srv6-policy ifit interval 10
# Globally enable SBFD for SRv6 TE policies.
[PE1] sbfd source-ipv6 1::1
[PE1] bfd multi-hop detect-multiplier 5
[PE1] bfd multi-hop min-transmit-interval 50
[PE1] segment-routing ipv6
[PE1-segment-routing-ipv6] traffic-engineering
[PE1-srv6-te] srv6-policy sbfd remote 101
[PE1-srv6-te] quit
[PE1-segment-routing-ipv6] quit
# Configure IPR policy ipr1 and configure parameters in the IPR policy.
[PE1] segment-routing ipv6
[PE1-segment-routing-ipv6] traffic-engineering
[PE1-srv6-te] intelligent-policy-route
[PE1-srv6-te-ipr] refresh-period 30
[PE1-srv6-te-ipr] ipr-policy ipr1
[PE1-srv6-ipr-policy-ipr1] delay threshold 100
[PE1-srv6-ipr-policy-ipr1] jitter threshold 10
[PE1-srv6-ipr-policy-ipr1] loss threshold 5
[PE1-srv6-ipr-policy-ipr1] cmi threshold 110
[PE1-srv6-ipr-policy-ipr1] srv6-policy color 10 priority 1
[PE1-srv6-ipr-policy-ipr1] srv6-policy color 20 priority 2
[PE1-srv6-ipr-policy-ipr1] srv6-policy color 30 priority 3
[PE1-srv6-ipr-policy-ipr1] quit
[PE1-srv6-te-ipr] quit
[PE1-srv6-te] quit
[PE1-segment-routing-ipv6] quit
# In the inbound direction of GigabitEthernet 1/0/1, mark the private network service traffic from CE 1 to CE 2, with a source address of 11.11.11.11/32 and a destination address of 22.22.22.22/32, with TE class ID 10.
[PE1] acl advanced 3000
[PE1-acl-ipv4-adv-3000] rule 10 permit ip source 11.11.11.11 0 destination 22.22.22.22 0
[PE1-acl-ipv4-adv-3000] quit
[PE1] traffic classifier aaa
[PE1-classifier-aaa] if-match acl 3000
[PE1-classifier-aaa] quit
[PE1] traffic behavior aaa
[PE1-behavior-aaa] remark te-class 10
[PE1-behavior-aaa] quit
[PE1] qos policy aaa
[PE1-qospolicy-aaa] classifier aaa behavior aaa
[PE1-qospolicy-aaa] quit
[PE1] interface gigabitethernet 1/0/1
[PE1-GigabitEthernet1/0/1] qos apply policy aaa inbound
[PE1-GigabitEthernet1/0/1] quit
# Configure SRv6 TE policy group 10. In the SRv6 TE policy group, use TE class ID-based traffic steering, configure a mapping between TE class ID 10 and IPR policy ipr1, and specify the SRv6 BE mode in the default forwarding policy.
[PE1] segment-routing ipv6
[PE1-segment-routing-ipv6] traffic-engineering
[PE1-srv6-te] policy-group 10
[PE1-srv6-te-policy-group-10] end-point ipv6 3::3
[PE1-srv6-te-policy-group-10] group-color 100
[PE1-srv6-te-policy-group-10] forward-type te-class
[PE1-srv6-te-policy-group-10] index 1 te-class 10 match ipr-policy ipr1
[PE1-srv6-te-policy-group-10] default match best-effort
# Configure a routing policy and tunnel policy to steer VPN service traffic to the SRv6 TE policy group through the routing policy and preferentially select the SRv6 TE policy group for traffic forwarding.
[PE1] route-policy a permit node 10
[PE1-route-policy-a-10] apply extcommunity color 00:100
[PE1-route-policy-a-10] quit
[PE1] bgp 100
[PE1-bgp-default] address-family vpnv4
[PE1-bgp-default-vpnv4] peer 3::3 route-policy a import
[PE1-bgp-default-vpnv4] quit
[PE1-bgp-default] quit
[PE1] tunnel-policy a
[PE1-tunnel-policy-a] select-seq srv6-policy-group load-balance-number 1
[PE1-tunnel-policy-a] quit
[PE1] ip vpn-instance vpn1
[PE1-vpn-instance-vpn1] tnl-policy a
[PE1-vpn-instance-vpn1] quit
5. Configure P 1:
# Configure IPv6 IS-IS for backbone network connectivity.
<P1> system-view
[P1] isis 1
[P1-isis-1] cost-style wide
[P1-isis-1] network-entity 00.0000.0000.0002.00
[P1-isis-1] address-family ipv6 unicast
[P1-isis-1-ipv6] quit
[P1-isis-1] quit
[P1] interface loopback 1
[P1-LoopBack1] isis ipv6 enable 1
[P1-LoopBack1] quit
[P1] interface gigabitethernet 1/0/2
[P1-GigabitEthernet1/0/2] isis ipv6 enable 1
[P1-GigabitEthernet1/0/2] quit
[P1] interface gigabitethernet 1/0/1
[P1-GigabitEthernet1/0/1] isis ipv6 enable 1
[P1-GigabitEthernet1/0/1] quit
# Configure a locator and use IS-IS to advertise the locator.
[P1] segment-routing ipv6
[P1-segment-routing-ipv6] locator abc ipv6-prefix 200:1:: 64 static 16
[P1-segment-routing-ipv6-locator-abc] opcode 1 end no-flavor
[P1-segment-routing-ipv6-locator-abc] quit
[P1-segment-routing-ipv6] quit
[P1] isis 1
[P1-isis-1] address-family ipv6 unicast
[P1-isis-1-ipv6] segment-routing ipv6 locator abc
[P1-isis-1-ipv6] quit
[P1-isis-1] quit
6. Configure P 2:
# Configure IPv6 IS-IS for backbone network connectivity.
<P2> system-view
[P2] isis 1
[P2-isis-1] cost-style wide
[P2-isis-1] network-entity 00.0000.0000.0003.00
[P2-isis-1] address-family ipv6 unicast
[P2-isis-1-ipv6] quit
[P2-isis-1] quit
[P2] interface loopback 1
[P2-LoopBack1] isis ipv6 enable 1
[P2-LoopBack1] quit
[P2] interface gigabitethernet 1/0/2
[P2-GigabitEthernet1/0/2] isis ipv6 enable 1
[P2-GigabitEthernet1/0/2] quit
[P2] interface gigabitethernet 1/0/1
[P2-GigabitEthernet1/0/1] isis ipv6 enable 1
[P2-GigabitEthernet1/0/1] quit
# Configure a locator and use IS-IS to advertise the locator.
[P2] segment-routing ipv6
[P2-segment-routing-ipv6] locator abc ipv6-prefix 400:1:: 64 static 16
[P2-segment-routing-ipv6-locator-abc] opcode 1 end no-flavor
[P2-segment-routing-ipv6-locator-abc] quit
[P2-segment-routing-ipv6] quit
[P2] isis 1
[P2-isis-1] address-family ipv6 unicast
[P2-isis-1-ipv6] segment-routing ipv6 locator abc
[P2-isis-1-ipv6] quit
[P2-isis-1] quit
7. Configure P 3:
# Configure IPv6 IS-IS for backbone network connectivity.
<P3> system-view
[P3] isis 1
[P3-isis-1] cost-style wide
[P3-isis-1] network-entity 00.0000.0000.0004.00
[P3-isis-1] address-family ipv6 unicast
[P3-isis-1-ipv6] quit
[P3-isis-1] quit
[P3] interface loopback 1
[P3-LoopBack1] isis ipv6 enable 1
[P3-LoopBack1] quit
[P3] interface gigabitethernet 1/0/2
[P3-GigabitEthernet1/0/2] isis ipv6 enable 1
[P3-GigabitEthernet1/0/2] quit
[P3] interface gigabitethernet 1/0/1
[P3-GigabitEthernet1/0/1] isis ipv6 enable 1
[P3-GigabitEthernet1/0/1] quit
# Configure a locator and use IS-IS to advertise the locator.
[P3] segment-routing ipv6
[P3-segment-routing-ipv6] locator abc ipv6-prefix 500:1:: 64 static 16
[P3-segment-routing-ipv6-locator-abc] opcode 1 end no-flavor
[P3-segment-routing-ipv6-locator-abc] quit
[P3-segment-routing-ipv6] quit
[P3] isis 1
[P3-isis-1] address-family ipv6 unicast
[P3-isis-1-ipv6] segment-routing ipv6 locator abc
[P3-isis-1-ipv6] quit
[P3-isis-1] quit
8. Configure PE 2:
# Configure IPv6 IS-IS for backbone network connectivity.
<PE2> system-view
[PE2] isis 1
[PE2-isis-1] cost-style wide
[PE2-isis-1] network-entity 00.0000.0000.0005.00
[PE2-isis-1] address-family ipv6 unicast
[PE2-isis-1-ipv6] quit
[PE2-isis-1] quit
[PE2] interface loopback 1
[PE2-LoopBack1] isis ipv6 enable 1
[PE2-LoopBack1] quit
[PE2] interface gigabitethernet 1/0/1
[PE2-GigabitEthernet1/0/1] isis ipv6 enable 1
[PE2-GigabitEthernet1/0/1] quit
[PE2] interface gigabitethernet 1/0/3
[PE2-GigabitEthernet1/0/3] isis ipv6 enable 1
[PE2-GigabitEthernet1/0/3] quit
[PE2] interface gigabitethernet 1/0/4
[PE2-GigabitEthernet1/0/4] isis ipv6 enable 1
[PE2-GigabitEthernet1/0/4] quit
# Configure a VPN instance to attach CE 2 to PE 2.
[PE2] ip vpn-instance vpn1
[PE2-vpn-instance-vpn1] route-distinguisher 100:1
[PE2-vpn-instance-vpn1] vpn-target 100:1
[PE2-vpn-instance-vpn1] quit
[PE2] interface gigabitethernet 1/0/2
[PE2-GigabitEthernet1/0/2] ip binding vpn-instance vpn1
[PE2-GigabitEthernet1/0/2] ip address 20.1.1.2 24
[PE2-GigabitEthernet1/0/2] quit
# Establish an EBGP peer relationship with CE 2 and import VPN routes.
[PE2] bgp 100
[PE2-bgp-default] router-id 3.3.3.3
[PE2-bgp-default] ip vpn-instance vpn1
[PE2-bgp-default-vpn1] peer 20.1.1.1 as-number 300
[PE2-bgp-default-vpn1] address-family ipv4 unicast
[PE2-bgp-default-ipv4-vpn1] peer 20.1.1.1 enable
[PE2-bgp-default-ipv4-vpn1] import-route direct
[PE2-bgp-default-ipv4-vpn1] quit
[PE2-bgp-default-vpn1] quit
# Establish an MP-IBGP peer relationship with PE 1.
[PE2-bgp-default] peer 1::1 as-number 100
[PE2-bgp-default] peer 1::1 connect-interface loopback 1
[PE2-bgp-default] address-family vpnv4
[PE2-bgp-default-vpnv4] peer 1::1 enable
[PE2-bgp-default-vpnv4] peer 1::1 prefix-sid
[PE2-bgp-default-vpnv4] quit
[PE2-bgp-default] ip vpn-instance vpn1
[PE2-bgp-default-vpn1] address-family ipv4 unicast
[PE2-bgp-default-ipv4-vpn1] segment-routing ipv6 locator abc
[PE2-bgp-default-ipv4-vpn1] segment-routing ipv6 best-effort
[PE2-bgp-default-ipv4-vpn1] quit
[PE2-bgp-default-vpn1] quit
[PE2-bgp-default] quit
# Configure a locator and use IS-IS to advertise the locator.
[PE2] segment-routing ipv6
[PE2-segment-routing-ipv6] encapsulation source-address 3::3
[PE2-segment-routing-ipv6] locator abc ipv6-prefix 300:1:: 64 static 16
[PE2-segment-routing-ipv6-locator-abc] opcode 1 end no-flavor
[PE2-segment-routing-ipv6-locator-abc] quit
[PE2-segment-routing-ipv6] quit
[PE2] isis 1
[PE2-isis-1] address-family ipv6 unicast
[PE2-isis-1-ipv6] segment-routing ipv6 locator abc
[PE2-isis-1-ipv6] quit
[PE2-isis-1] quit
# Enable iFIT and set the iFIT operating mode to collector.
[PE2] ifit enable
[PE2-ifit] work-mode collector
[PE2-ifit-collector] service-type srv6-segment-list
[PE2-ifit-collector] quit
[PE2-ifit] quit
# Specify 101 as the local discriminator for the reflector of the SBFD session.
[PE2] sbfd local-discriminator 101
Verifying the configuration
# On PE 1, display SRv6 TE policy group information. Verify that the SRv6 TE policy group is in up state, traffic with TE class ID 10 is forwarded through the forwarding policy defined in IPR policy ipr1. In addition, the IPR policy is in active state and the color attribute value of the optimal SRv6 TE policy calculated by IPR is 10.
<Sysname> display segment-routing ipv6 te policy-group verbose
Total number of policy groups: 1
GroupID: 10 GroupState: Up
GroupNID: 2151677963 Best-effort NID: 2156920832
Referenced: 1 Flags: A
Group type: Static TE Class
Group color: 100
StateChangeTime: 2022-11-11 01:50:17
Endpoint: 3::3
UP/Total Mappings: 1/1
Default Match Type: SRv6 BE
Default SRv6 TE Policy Color: -
Default IPR Policy : -
Index : 1 TE Class : 10
Match Type : IPR Policy(active)
SRv6 TE Policy Color : 10
IPR Policy : ipr1
Color : 10 Priority : 1
Color : 20 Priority : 2
Color : 30 Priority : 3
# On PE 1, display forwarding information for SRv6 TE policies.
[PE1] display segment-routing ipv6 te forwarding verbose
Total forwarding entries: 1
Policy name/ID: A/0
Binding SID: 100:1::10:1
Policy forwarding index: 2150629377
Main path:
Seglist Name/ID: 1
Seglist forwarding index: 2149580801
Weight: 1
Outgoing forwarding index: 2148532225
Interface: GE1/0/2
Nexthop: FE80::54CB:70FF:FE86:316
Path ID: 0
SID list: {200:1::1, 300:1::1}