- Table of Contents
-
- 17-Network Management and Monitoring Configuration Guide
- 00-Preface
- 01-System maintenance and debugging configuration
- 02-NQA configuration
- 03-NTP configuration
- 04-PoE configuration
- 05-SNMP configuration
- 06-RMON configuration
- 07-Event MIB configuration
- 08-NETCONF configuration
- 09-SmartMC configuration
- 10-CWMP configuration
- 11-EAA configuration
- 12-Process monitoring and maintenance configuration
- 13-Sampler configuration
- 14-Mirroring configuration
- 15-NetStream configuration
- 16-IPv6 NetStream configuration
- 17-sFlow configuration
- 18-Performance management configuration
- 19-Flow log configuration
- 20-Information center configuration
- 21-Packet capture configuration
- 22-Cloud connection configuration
- Title page
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 19-Flow log configuration | 161.00 KB |
Contents
Restrictions: Hardware compatibility with flow log
NAT flow log tasks at a glance
Prerequisites for NAT flow log
Specifying a NAT flow log export destination
Restrictions and guidelines for NAT flow log export destination configuration
Specifying a log host as the NAT flow log export destination
Specifying the information center as the NAT flow log export destination
Configuring the NAT flow log version
Specifying a source IP address for NAT flow log packets
Configuring the timestamp of NAT flow log entries
Enabling load balancing for NAT flow log entries
Configuring NAT flow log host groups
Prerequisites for log host group configuration
Configuring an IPv4 NAT flow log host group
Configuring an IPv6 NAT flow log host group
Specifying an RIR flow log export destination
Hardware compatibility with RIR flow log export destination configuration
Restrictions and guidelines for RIR flow log export destination configuration
Prerequisites for RIR flow log export destination configuration
Specifying a log host as the flow log export destination
Specifying the information center as the RIR flow log export destination
Display and maintenance commands for flow log
NAT flow log configuration examples
Example: Configuring NAT flow log export
Example: Configuring NAT flow log export to a NAT flow log host group
RIR flow log configuration examples
Example: Configuring RIR flow log export
Configuring flow log
About flow log
Flow log records session information based on flows. Flow log creates entries based on NAT sessions or RIR related sessions.
A flow log entry might contain the following information about a flow:
· Network access quintuple information (source IP address, destination IP address, source port, destination port, and protocol number).
· Statistics about sent and received packet statistics.
· Flow-based link selection information.
Flow log export
You can export flow log entries in the following methods:
· Export flow log entries to log hosts. Flow log entries are sent as binary characters in UDP. One UDP packet can contain multiple log entries.
· Export flow log entries to the information center. Flow log entries are converted to syslog entries in ASCII format, with the informational severity level. The information center specifies the output destinations for the log entries. For more information about the information center, see "Configuring the information center."
Log entries in ASCII format are human readable. However, the log data volume is higher in ASCII format than in binary format. It's recommended to export flow log entries to the information center if the log data volume is small.
NAT flow log versions
NAT flow log has three versions: version 1.0, version 3.0, and version 5.0. Table 1, Table 2, and Table 3 show the fields available in the versions.
Table 1 NAT flow log 1.0 fields
|
Field |
Description |
|
SrcIP |
Source IP address before NAT. |
|
DestIP |
Destination IP address before NAT. |
|
SrcPort |
Source TCP/UDP port number before NAT. |
|
DestPort |
Destination TCP/UDP port number before NAT. |
|
StartTime |
Start time of the flow, in seconds. |
|
EndTime |
End time of the flow, in seconds. This field is 0 if the Operator field is 6 (regular connectivity check record for the active flow). |
|
Protocol |
Protocol number. |
|
Operator |
Reasons why a NAT flow log entry was generated: · 0—Reserved. · 1—Flow was ended normally. · 2—Flow was aged out because of aging timer expiration. · 3—Flow was aged out because of configuration change or manual deletion. · 4—Flow was aged out because of insufficient resources. · 5—Reserved. · 6—Regular connectivity check record for the active flow. · 7—Flow was deleted because a new flow was created when the flow table was full. · 8—Flow was created. · FE—Other reasons. · 10-FE-1—Reserved for future use. |
|
Reserved |
Reserved for future use. |
Table 2 NAT flow log 3.0 fields
|
Field |
Description |
|
Protocol |
Protocol number. |
|
Operator |
Reasons why a NAT flow log was generated: · 0—Reserved. · 1—Flow was ended normally. · 2—Flow was aged out because of aging timer expiration. · 3—Flow was aged out because of configuration change. · 4—Flow was aged out because of insufficient resources. · 5—Reserved. · 6—Regular connectivity check record for the active flow. · 7—Flow was deleted because a new flow was created when the flow table was full. · 8—Flow was created. · FE—Other reasons. · 10-FE-1—Reserved for future use. |
|
IPVersion |
IP packet version. |
|
TosIPv4 |
ToS field of the IPv4 packet. |
|
SourceIP |
Source IP address before NAT. |
|
SrcNatIP |
Source IP address after NAT. |
|
DestIP |
Destination IP address before NAT. |
|
DestNatIP |
Destination IP address after NAT. |
|
SrcPort |
Source TCP/UDP port number before NAT. |
|
SrcNatPort |
Source TCP/UDP port number after NAT. |
|
DestPort |
Destination TCP/UDP port number before NAT. |
|
DestNatPort |
Destination TCP/UDP port number after NAT. |
|
StartTime |
Start time of the flow, in seconds. |
|
EndTime |
End time of the flow, in seconds. This field is 0 when the Operator field is 6 (regular connectivity check record for the active flow). |
|
InTotalPkg |
Number of packets received for the session. |
|
InTotalByte |
Number of bytes received for the session. |
|
OutTotalPkg |
Number of packets sent for the session. |
|
OutTotalByte |
Number of bytes sent for the session. |
|
InVPNID |
ID of the source VPN instance. |
|
OutVPNID |
ID of the destination VPN instance. |
|
Reserved1 |
Reserved field. |
|
AppID |
Application protocol ID. |
|
Reserved3 |
Reserved field. |
Table 3 NAT flow log 5.0 fields
|
Field |
Description |
|
Protocol |
Protocol number. |
|
Operator |
Reasons why a NAT flow log was generated: · 0—Reserved. · 1—Flow was ended normally. · 2—Flow was aged out because of aging timer expiration. · 3—Flow was aged out because of configuration change. · 4—Flow was aged out because of insufficient resources. · 5—Reserved. · 6—Regular connectivity check record for the active flow. · 7—Flow was deleted because a new flow was created when the flow table was full. · 8—Flow was created. · FE—Other reasons. · 10-FE-1—Reserved for future use. |
|
IPVersion |
IP packet version. |
|
TosIPv4 |
ToS field of the IPv4 packet. |
|
SourceIP |
Source IP address before NAT. |
|
SrcNatIP |
Source IP address after NAT. |
|
DestIP |
Destination IP address before NAT. |
|
DestNatIP |
Destination IP address after NAT. |
|
SrcPort |
Source TCP/UDP port number before NAT. |
|
SrcNatPort |
Source TCP/UDP port number after NAT. |
|
DestPort |
Destination TCP/UDP port number before NAT. |
|
DestNatPort |
Destination TCP/UDP port number after NAT. |
|
StartTime |
Start time of the flow, in seconds. |
|
EndTime |
End time of the flow, in seconds. This field is 0 when the Operator field is 6 (regular connectivity check record for the active flow). |
|
InTotalPkg |
Number of packets received for the session. |
|
InTotalByte |
Number of bytes received for the session. |
|
OutTotalPkg |
Number of packets sent for the session. |
|
OutTotalByte |
Number of bytes sent for the session. |
|
InVPNID |
ID of the source VPN instance. |
|
OutVPNID |
ID of the destination VPN instance. |
|
AppID |
Application protocol ID. |
|
UserName |
Username. |
|
Reserved1 Reserved2 Reserved3 |
Reserved fields. |
Restrictions: Hardware compatibility with flow log
|
Hardware |
Flow log compatibility |
|
MSR810, MSR810-W, MSR810-W-DB, MSR810-LM, MSR810-W-LM, MSR810-10-PoE, MSR810-LM-HK, MSR810-W-LM-HK, MSR810-LM-CNDE-SJK, MSR810-CNDE-SJK |
Yes |
|
MSR810-LMS, MSR810-LUS |
No |
|
MSR810-LMS-EA, MSR810-LME |
Yes |
|
MSR2600-6-X1, MSR2600-10-X1 |
Yes |
|
MSR 2630 |
Yes |
|
MSR3600-28, MSR3600-51 |
Yes |
|
MSR3600-28-SI, MSR3600-51-SI |
No |
|
MSR3600-28-X1, MSR3600-28-X1-DP, MSR3600-51-X1, MSR3600-51-X1-DP |
Yes |
|
MSR3610-I-DP, MSR3610-IE-DP, MSR3610-IE-ES, MSR3610-IE-EAD, MSR3610-I-IG, MSR3610-IE-IG |
Yes |
|
MSR3610-X1, MSR3610-X1-DP, MSR3610-X1-DC, MSR3610-X1-DP-DC |
Yes |
|
MSR 3610, MSR 3620, MSR 3620-DP, MSR 3640, MSR 3660 |
Yes |
|
MSR3610-G, MSR3620-G |
Yes |
|
Hardware |
Flow log compatibility |
|
MSR810-W-WiNe, MSR810-LM-WiNet |
Yes |
|
MSR830-4LM-WiNet |
Yes |
|
MSR830-5BEI-WiNet, MSR830-6EI-WiNet, MSR830-10BEI-WiNet |
Yes |
|
MSR830-6BHI-WiNet, MSR830-10BHI-WiNet |
Yes |
|
MSR2600-6-WiNet, MSR2600-10-X1-WiNet |
Yes |
|
MSR2630-WiNet |
Yes |
|
MSR3600-28-WiNet |
Yes |
|
MSR3610-X1-WiNet |
Yes |
|
MSR3610-WiNet, MSR3620-10-WiNet, MSR3620-DP-WiNet, MSR3620-WiNet, MSR3660-WiNet |
Yes |
|
Hardware |
Flow log compatibility |
|
MSR2630-XS |
Yes |
|
MSR3600-28-XS |
Yes |
|
MSR3610-XS |
Yes |
|
MSR3620-XS |
Yes |
|
MSR3610-I-XS |
Yes |
|
MSR3610-IE-XS |
Yes |
|
Hardware |
Flow log compatibility |
|
MSR810-LM-GL |
Yes |
|
MSR810-W-LM-GL |
Yes |
|
MSR830-6EI-GL |
Yes |
|
MSR830-10EI-GL |
Yes |
|
MSR830-6HI-GL |
Yes |
|
MSR830-10HI-GL |
Yes |
|
MSR2600-6-X1-GL |
Yes |
|
MSR3600-28-SI-GL |
No |
NAT flow log tasks at a glance
To configure NAT flow log, perform the following tasks:
1. Specifying a NAT flow log export destination
Choose one of the following tasks:
¡ Specifying a log host as the NAT flow log export destination
¡ Specifying the information center as the NAT flow log export destination
2. (Optional.) Configuring the NAT flow log version
3. (Optional.) Specifying a source IP address for NAT flow log packets
4. (Optional.) Configuring the timestamp of NAT flow log entries
5. (Optional.) Enabling load balancing for NAT flow log entries
6. (Optional.) Configuring NAT flow log host groups
Prerequisites for NAT flow log
Before you configure the NAT flow log feature, complete the following tasks:
· Enable NAT logging by using the nat log enable command.
· Enable the following NAT logging features as needed:
¡ Logging of active NAT flows.
¡ Logging of NAT session establishment events.
¡ Logging of NAT session removal events.
For more information about the NAT logging commands, see Layer 3—IP Services Command Reference.
Specifying a NAT flow log export destination
Restrictions and guidelines for NAT flow log export destination configuration
You can export NAT flow log entries to a log host or to the information center, but not both. If you configure both methods, the system exports NAT flow log entries to the information center.
NAT flow log entries exported to the information center has the informational severity level.
Specifying a log host as the NAT flow log export destination
1. Enter system view.
system-view
2. Specify a log host as the destination for NAT flow log export.
userlog flow export [ vpn-instance vpn-instance-name ] host { hostname | ipv4-address | ipv6 ipv6-address } port udp-port
By default, no log hosts are specified.
You can specify multiple log hosts.
Specifying the information center as the NAT flow log export destination
1. Enter system view.
system-view
2. Specify the information center as the destination for NAT flow log export.
userlog flow syslog
By default, NAT flow log entries are not exported to the information center.
Configuring the NAT flow log version
Restrictions and guidelines
Make sure the specified NAT flow log version is supported on the log host.
If you configure the NAT flow log version multiple times, the most recent configuration takes effect.
Procedure
1. Enter system view.
system-view
2. Configure the NAT flow log version.
userlog flow export version version-number
The default NAT flow log version is 1.0.
Specifying a source IP address for NAT flow log packets
About this task
By default, the source IP address for NAT flow log packets is the IP address of their outgoing interface. For the log hosts to filter log entries by log sender, specify a source IP address for all NAT flow log packets.
Restrictions and guidelines
As a best practice, use a Loopback interface's address as the source IP address for NAT flow log packets. A Loopback interface is always up. The setting avoids export failure on interfaces that might go down.
Procedure
1. Enter system view.
system-view
2. Specify a source IP address for NAT flow log packets.
userlog flow export source-ip { ipv4-address | ipv6 ipv6-address }
By default, the source IP address for NAT flow log packets is the IP address of their outgoing interface.
Configuring the timestamp of NAT flow log entries
About this task
The device uses either the local time or the UTC time in the timestamp of NAT flow logs.
· UTC time—Standard Greenwich Mean Time (GMT).
· Local time—Standard GMT plus or minus the time zone offset.
The time zone offset can be configured by using the clock timezone command. For more information, see device management in Fundamentals Command Reference.
Procedure
1. Enter system view.
system-view
2. Configure the device to use the local time in the NAT flow log timestamp.
userlog flow export timestamp localtime
By default, the UTC time is used in the NAT flow log timestamp.
Enabling load balancing for NAT flow log entries
About this task
By default, the device sends a copy of each NAT flow log entry to all configured log hosts. When one log host fails, other log hosts still have complete NAT flow log entries.
In load balancing mode, NAT flow log entries are distributed among log hosts based on the source IP addresses (before NAT) that are recorded in the entries. The NAT flow log entries generated for the same source IP address are sent to the same log host.
Restrictions and guidelines
In load balancing mode, NAT flow log entries are load balanced among all configured log hosts, regardless of whether the log hosts are reachable. If a log host is unreachable, the NAT flow log entries sent to it will be lost.
Procedure
1. Enter system view.
system-view
2. Enable load balancing for NAT flow log entries.
userlog flow export load-balancing
By default, load balancing is disabled.
Configuring NAT flow log host groups
About NAT flow log host group
By default, the device sends a copy of each NAT flow log entry to all available log hosts. To filter logs and reduce the log sending and processing workload of the device, configure the NAT flow log host group feature.
The NAT flow log host group feature allows you to classify NAT flow log hosts into groups and specify an ACL for each group. A NAT flow log matches a log host group if it matches the group's ACL, and it is sent only to the log hosts in the matching group.
If a NAT flow log matches multiple log host groups, the device sends the log to the group that comes first in alphabetical order of the matching group names.
If a NAT flow log does not match any log host groups, the device ignores the log host group configuration and sends the log to all configured log hosts.
If load balancing is enabled, NAT flow logs sent to a log host group will be load-shared among the log hosts in the group. NAT flow logs generated for the same source IP address are sent to the same log host.
Prerequisites for log host group configuration
Before you configure NAT flow log host groups, complete the following tasks:
· Configure the ACLs to be used by the NAT flow log host groups.
· Use the userlog flow export host command to configure the log hosts to be assigned to the NAT flow log host groups.
Configuring an IPv4 NAT flow log host group
1. Enter system view.
system-view
2. Create an IPv4 NAT flow log host group and enter its view.
userlog host-group host-group-name acl { name acl-name | number acl-number }
By default, no IPv4 NAT flow log host groups exist.
3. Assign an IPv4 log host to the NAT flow log host group.
userlog host-group [ vpn-instance vpn-instance-name ] host flow { hostname | ipv4-address }
By default, an IPv4 NAT flow log host group does not contain any log hosts.
Configuring an IPv6 NAT flow log host group
1. Enter system view.
system-view
2. Create an IPv6 NAT flow log host group and enter its view.
userlog host-group ipv6 host-group-name acl { name acl-name | number acl-number }
By default, no IPv6 NAT flow log host groups exist.
3. Assign an IPv6 log host to the NAT flow log host group.
userlog host-group [ vpn-instance vpn-instance-name ] host flow ipv6 { hostname | ipv6-address }
By default, an IPv6 NAT flow log host group does not contain any log hosts.
Specifying an RIR flow log export destination
Hardware compatibility with RIR flow log export destination configuration
|
Hardware |
Feature Compatibility |
|
MSR810, MSR810-W, MSR810-W-DB, MSR810-LM, MSR810-W-LM, MSR810-10-PoE, MSR810-LM-HK, MSR810-W-LM-HK, MSR810-LM-CNDE-SJK, MSR810-CNDE-SJK |
Yes |
|
MSR810-LMS, MSR810-LUS |
Yes |
|
MSR810-LMS-EA, MSR810-LME |
Yes |
|
MSR2600-6-X1, MSR2600-10-X1 |
Yes |
|
MSR 2630 |
Yes |
|
MSR3600-28, MSR3600-51 |
Yes |
|
MSR3600-28-SI, MSR3600-51-SI |
No |
|
MSR3600-28-X1, MSR3600-28-X1-DP, MSR3600-51-X1, MSR3600-51-X1-DP |
Yes |
|
MSR3610-I-DP, MSR3610-IE-DP, MSR3610-IE-ES, MSR3610-IE-EAD |
Yes |
|
MSR3610-X1, MSR3610-X1-DP, MSR3610-X1-DC, MSR3610-X1-DP-DC |
Yes |
|
MSR 3610, MSR3620, MSR3620-DP, MSR3640, MSR3660 |
Yes |
|
MSR3610-G, MSR3620-G |
Yes |
|
Hardware |
Feature Compatibility |
|
MSR810-W-WiNet, MSR810-LM-WiNet |
Yes |
|
MSR830-4LM-WiNet |
Yes |
|
MSR830-5BEI-WiNet, MSR830-6EI-WiNet, MSR830-10BEI-WiNet |
Yes |
|
MSR830-6BHI-WiNet, MSR830-10BHI-WiNet |
No |
|
MSR2600-6-WiNet, MSR2600-10-X1-WiNet |
Yes |
|
MSR2630-WiNet |
Yes |
|
MSR3600-28-WiNet |
Yes |
|
MSR3610-X1-WiNet |
Yes |
|
MSR3610-WiNet, MSR3620-10-WiNet, MSR3620-DP-WiNet, MSR3620-WiNet, MSR3660-WiNet |
Yes |
|
Hardware |
Feature Compatibility |
|
MSR2630-XS |
Yes |
|
MSR3600-28-XS |
Yes |
|
MSR3610-XS |
Yes |
|
MSR3620-XS |
Yes |
|
MSR3610-I-XS |
Yes |
|
MSR3610-IE-XS |
Yes |
|
MSR2630-XS |
Yes |
|
MSR3600-28-XS |
Yes |
|
Hardware |
Feature Compatibility |
|
MSR810-LM-GL |
Yes |
|
MSR810-W-LM-GL |
Yes |
|
MSR830-6EI-GL |
Yes |
|
MSR830-10EI-GL |
Yes |
|
MSR830-6HI-GL |
No |
|
MSR830-10HI-GL |
No |
|
MSR2600-6-X1-GL |
Yes |
|
MSR3600-28-SI-GL |
Yes |
Restrictions and guidelines for RIR flow log export destination configuration
You can export RIR flow log entries to a log host or to the information center, but not both. If you configure both methods, the system exports flow log entries to the information center.
RIR flow log entries exported to the information center has the informational severity level.
Prerequisites for RIR flow log export destination configuration
Before you configure RIR flow log, enable RIR logging by using the log enable command in RIR view. For more inforamtion about this command, see RIR commands in Layer 3—IP Routing Command Reference.
Specifying a log host as the flow log export destination
1. Enter system view.
system-view
2. Specify a log host as the destination for RIR flow log export.
userlog flow export [ vpn-instance vpn-instance-name ] host { hostname | ipv4-address | ipv6 ipv6-address } port udp-port
By default, no log hosts are specified.
Specifying the information center as the RIR flow log export destination
1. Enter system view.
system-view
2. Specify the information center as the destination for RIR flow log export.
userlog flow syslog
By default, RIR flow log entries are not exported to the information center.
Display and maintenance commands for flow log
Execute display commands in any view.
|
Task |
Command |
|
Display flow log configuration and statistics. |
display userlog export |
|
Display flow log host group information. |
display userlog host-group [ ipv6 ] [ host-group-name ] |
|
Clear flow log statistics. |
reset userlog flow export |
NAT flow log configuration examples
Example: Configuring NAT flow log export
Network configuration
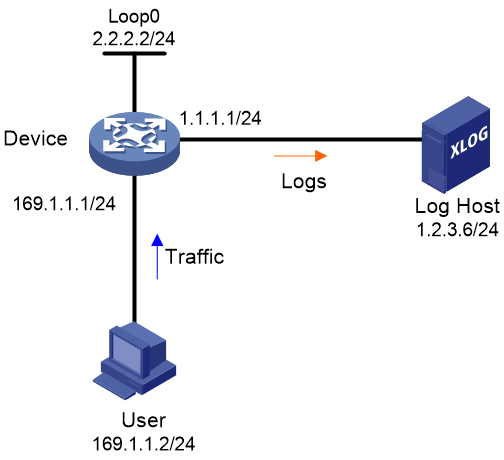
As shown in Figure 1, configure NAT flow log on the device to send NAT flow log entries generated for the user to the log host.
Procedure
# Configure IP addresses, as shown in Figure 1. Make sure the device, user, and the log host can reach one another. (Details not shown.)
# Enable NAT logging.
<Device> system-view
[Device] nat log enable
# Enable NAT logging for session establishment events, session removal events, and active flows.
[Device] nat log flow-begin
[Device] nat log flow-end
[Device] nat log flow-active 10
# Set the NAT flow log version to 3.0.
[Device] userlog flow export version 3
# Specify the log host at 1.2.3.6 as the destination for NAT flow log export. Set the UDP port number to 2000.
[Device] userlog flow export host 1.2.3.6 port 2000
# Specify 2.2.2.2 as the source IP address for NAT flow log packets.
[Device] userlog flow export source-ip 2.2.2.2
[Device] quit
Verifying the configuration
# Display the NAT flow log configuration and statistics.
<Device> display userlog export
Flow:
Export flow log as UDP Packet.
Version: 3.0
Source ipv4 address: 2.2.2.2
Log load balance function: Disabled
Local time stamp: Disabled
Number of log hosts: 1
Log host 1:
Host/Port: 1.2.3.6/2000
Total logs/UDP packets exported: 112/87
Example: Configuring NAT flow log export to a NAT flow log host group
Network configuration
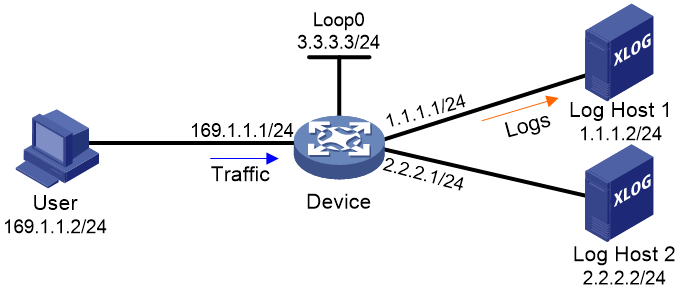
As shown in Figure 2, configure a NAT flow log host group on the device to send NAT flow log entries generated for the user only to Log Host 1.
Procedure
# Configure IP addresses, as shown in Figure 2. Make sure the device, user, and the log host can reach one another. (Details not shown.)
# Enable NAT logging.
<Device> system-view
[Device] nat log enable
# Enable NAT logging for session establishment events, session removal events, and active flows.
[Device] nat log flow-begin
[Device] nat log flow-end
[Device] nat log flow-active 10
# Specify Log Host 1 and Log Host 2 for NAT flow log export.
[Device] userlog flow export host 1.1.1.2 port 2000
[Device] userlog flow export host 2.2.2.2 port 2000
# Specify 3.3.3.3 as the source IP address for NAT flow log packets.
[Device] userlog flow export source-ip 3.3.3.3
# Create ACL 2000 to match packets sent by the user.
[Device] acl basic 2000
[Device-acl-ipv4-basic-2000] rule 1 permit source 169.1.1.2 0.0.0.0
[Device-acl-ipv4-basic-2000] quit
# Create an IPv4 NAT flow log host group named test and specify ACL 2000 for it.
[Device] userlog host-group test acl number 2000
# Assign Log Host 1 to NAT flow log host group test.
[Device-userlog-host-group-test] userlog host-group host flow 1.1.1.2
[Device-userlog-host-group-test] quit
Verifying the configuration
# Display information about NAT flow log host group test.
[Device] display userlog host-group test
Userlog host-group test:
ACL number: 2000
Flow log host numbers: 1
Log host 1:
Host/port: 1.1.1.2/2000
# After the user comes online, display NAT flow log export statistics.
[Device] display userlog export
Flow:
Export flow log as UDP Packet.
Version: 1.0
Source ipv4 address: 3.3.3.3
Log load balance function: Disabled
Local time stamp: Disabled
Number of log hosts: 2
Log host 1:
Host/Port: 1.1.1.2/2000
Total logs/UDP packets exported: 13/13
Log host 2:
Host/Port: 2.2.2.2/2000
Total logs/UDP packets exported: 0/0
RIR flow log configuration examples
Example: Configuring RIR flow log export
Network configuration
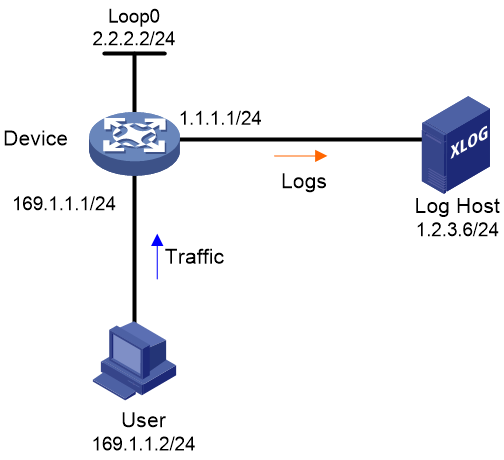
As shown in Figure 3, configure NAT flow log on the device to send NAT flow log entries generated for the user to the log host.
Procedure
# Configure IP addresses, as shown in Figure 3. Make sure the device, user, and the log host can reach one another. (Details not shown.)
# Enable RIR logging.
<Device> system-view
[Device] rir
[Device-rir] log enable
[Device-rir] quit
# Export RIR flow log entries to the log host at 1.2.3.6 and UDP port 2000.
[Device] userlog flow export host 1.2.3.6 port 2000
Verifying the configuration
# Verify that when link selection events occur on the device, the log host can receive RIR flow log entries for the events.