- Table of Contents
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 05-IP L3VPN over SRv6 configuration | 320.58 KB |
Configuring IP L3VPN over SRv6
Restrictions: Hardware compatibility with IP L3VPN over SRv6
IP L3VPN over SRv6 tasks at a glance
Applying a locator to a BGP VPN instance
Configuring PEs to exchange BGP VPNv4 or VPNv6 routes
Configuring IPv6 peers to exchange SRv6 SIDs
Configuring next hop-based dynamic End.DX4 or End.DX6 SID allocation for BGP routes
Configuring BGP VPNv4 or VPNv6 routes
Restrictions and guidelines for BGP VPNv4 or VPNv6 route configuration
Controlling BGP VPNv4 or VPNv6 route advertisement and reception
Setting a preferred value for received BGP VPNv4 or VPNv6 routes
Configuring BGP VPNv4 or VPNv6 route reflection
Configuring BGP VPNv4 or VPNv6 route attributes
Configuring BGP VPNv4 or VPNv6 route distribution filtering policies
Configuring the route recursion mode
Specifying a source address for the outer IPv6 header of SRv6-encapsulated packets
Enabling SRv6 VPN compatibility with a peer or peer group
Configuring IP L3VPN over SRv6 FRR
Display and maintenance commands for IP L3VPN over SRv6
Displaying and maintaining the running status of IP L3VPN over SRv6 VPN
IP L3VPN over SRv6 configuration examples
Example: Configuring IPv4 L3VPN over SRv6
IP L3VPN over SRv6 configuration examples
Example: Configuring IPv4 L3VPN over SRv6
Configuring IP L3VPN over SRv6
About IP L3VPN over SRv6
IP L3VPN over SRv6 uses SRv6 tunnels to carry IP L3VPN services. This technology establishes SRv6 tunnels among geographically dispersed customer sites over an IPv6 network and transparently forwards Layer 3 customer traffic to remote sites over the IPv6 network through the tunnels.
Basic principle
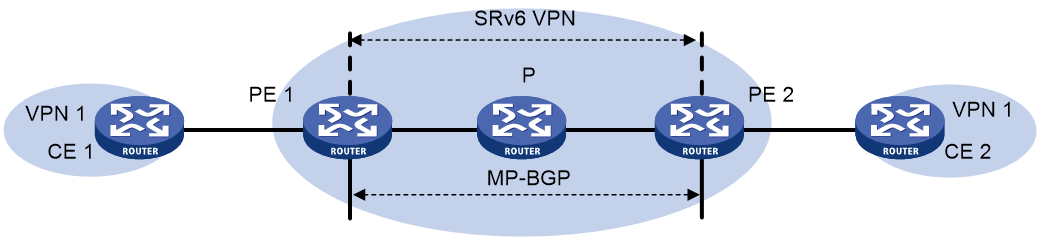
Figure 1 shows a typical IP L3VPN over SRv6 network.
· PE 1 and PE 2 use BGP to advertise IPv4 or IPv6 VPN routes to each other over the IPv6 backbone network. The VPN routes contain private network routing information and SID information.
· The PEs have a single-hop SRv6 tunnel between them and they use the SRv6 tunnel to forward VPN traffic across sites.
· The devices in the IPv6 backbone network forward the SRv6-encapsulated VPN traffic through the optimal path calculated by IGP.
IP L3VPN over SRv6 connects geographically dispersed sites that belong to the same VPN over the IPv6 backbone network.
If the customer sites belong to the public network, IP L3VPN over SRv6 takes the public network as a special VPN. The PEs establish a single-hop SRv6 tunnel between them and use the SRv6 tunnel to forward public network traffic across sites.
Route advertisement
The route advertisement process of IPv4 L3VPN over SRv6 is similar to that of IPv6 L3VPN over SRv6. This section uses IPv4 L3VPN over SRv6 to illustrate the process.
As shown in Figure 1, local routes of CE 1 are advertised to CE 2 by using the following process:
1. CE 1 uses static routing, RIP, OSPF, IS-IS, EBGP, or IBGP to advertise routes of the local site to PE 1.
2. After learning the route information of CE 1, PE 1 stores the private routes to the routing table of the VPN instance. In this example, VPN instance 1 is used. Then, PE 1 converts the routes to BGP VPNv4 routes and advertises the BGP VPNv4 routes to PE 2 by using MP-BGP. The BGP VPNv4 routes carry the RD, RT, and SID attributes (the SID attribute is used as the private network label).
¡ If next hop-based dynamic SID allocation is not used, all private network routes of the VPN instance are allocated the same End.DT4 or End.DT46 SID.
¡ If next hop-based dynamic SID allocation is used, private network routes with the same next hop are allocated the same End.DX4 SID in the VPN instance.
3. When PE 2 receives the routes advertised by PE 1, it adds the routes to the routing table of VPN 1, converts the routes to IPv4 routes, and advertises the IPv4 routes to CE 2.
4. By adding the received IPv4 routes to the routing table, CE 2 learns the private network routes of CE 1.
Packet forwarding
IP L3VPN over SRv6 supports the following route recursion modes:
· SRv6-BE mode.
· SRv6-TE mode.
· SRv6-TE and SRv6-BE hybrid mode.
The packet forwarding process differs by the route recursion mode in use.
SRv6-BE mode
This mode is also called SID-based forwarding mode. In this mode, a PE forwards an SRv6 packet by searching the IPv6 routing table based on the SRv6 SID encapsulated in the packet.
The packet forwarding process is similar for IPv4 L3VPN over SRv6 and IPv6 L3VPN over SRv6 and for VPN sites and public network sites. This section uses IPv4 L3VPN over SRv6 and VPN sites to illustrate the process.
As shown in Figure 1, CE 2 forwards an IPv4 packet to CE 1 as follows:
1. CE 2 sends the IPv4 packet to PE 2.
2. PE 2 receives the packet on an interface associated with VPN 1. PE 2 searches for a route that matches the destination IPv4 address of the packet in the routing table of VPN 1. The corresponding End.DT4, End.DT46, or End.DX4 SID is found. Then, PE 2 encapsulates an outer IPv6 header for the packet. The End.DT4, End.DT46, or End.DX4 SID is encapsulated in the outer IPv6 header as the destination address.
3. PE 2 searches the IPv6 routing table based on the End.DT4, End.DT46, or End.DX4 SID for the optimal IGP route and forwards the packet to P through the route.
4. P searches the IPv6 routing table based on the End.DT4, End.DT46, or End.DX4 SID for the optimal IGP route and forwards the packet to PE 1 through the route.
5. When PE 1 receives the packet, it processes the packet as follows:
¡ If the packet header contains an End.DT4 or End.DT46 SID, PE 1 searches the local SID forwarding table for the SID and removes the outer IPv6 header. Then, PE 1 matches the packet to VPN 1 based on the SID, searches the routing table of VPN 1 for the optimal route, and forwards the packet to CE 1.
¡ If the packet header contains an End.DX4 SID, PE 1 searches the local SID forwarding table for the SID and removes the outer IPv6 header. Then, PE 1 forwards the packet to CE 1 according to the next hop and output interface bound to the SID.
SRv6-TE mode
This mode is also called SRv6 TE policy-based forwarding mode. In this mode, when a PE forwards a customer packet, it first searches for a matching SRv6 TE policy based on the packet attributes. Then, the PE adds an SRH to the packet. The SRH includes the destination SRv6 SID and the SID list of the SRv6 TE policy. Finally, the PE forwards the encapsulated packet based on the SRv6 TE policy.
The following modes are available to steer traffic to an SRv6 TE policy:
· Color—The device searches for an SRv6 TE policy that has the same color and endpoint address as the color and nexthop address of a VPN route. If a matching SRv6 TE policy exists, the device recurses the VPN route to that SRv6 TE policy. When the device receives packets that match the VPN route, it forwards the packets through the SRv6 TE policy.
· Tunnel policy—The device searches the tunnel policies for a matching SRv6 TE policy based on the next hop of a matching route. Configure a preferred tunnel or load sharing tunnel policy that uses the SRv6 TE policy. In this way, the SRv6 TE policy will be used as the public tunnel to forward private network packets.
For more information about tunnel policies, see MPLS Configuration Guide. For more information about SRv6 TE policies, see "Configuring SRv6 TE policies."
SRv6-TE and SRv6-BE hybrid mode
In this mode, the PE preferentially uses the SRv6-TE mode to forward a packet. If no SRv6 TE policy is available for the packet, the PE forwards the packet in SRv6-BE mode.
IP L3VPN over SRv6 FRR
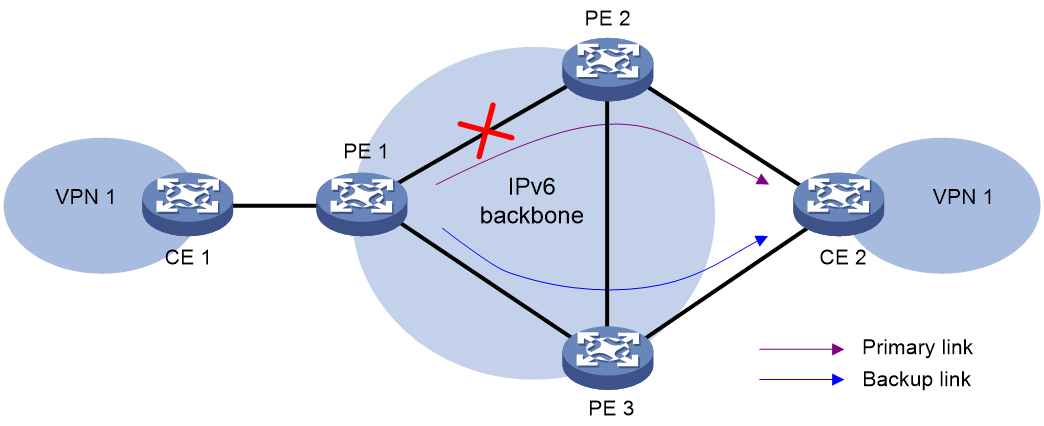
IP L3VPN over SRv6 Fast Reroute (FRR) is applicable to a dualhomed scenario, as shown in Figure 2. By using static BFD to detect the primary link, FRR enables a PE to use the backup link when the primary link fails. The PE then selects a new optimal route, and uses the new optimal route to forward traffic.
IP L3VPN over SRv6 supports VPNv4 route backup for a VPNv4 route and VPNv6 route backup for a VPNv6 route.
Figure 2 Network diagram of VPNv4 route backup for a VPNv4 route
IPv4 L3VPN over SRv6 and IPv6 L3VPN over SRv6 use the same FRR mechanism. This section uses VPNv4 route backup for a VPNv4 route as an example to illustrate the mechanism.
As shown in Figure 2, configure FRR on the ingress node PE 1, and specify the backup next hop for VPN 1 as PE 3. When PE 1 receives a VPNv4 route to CE 2 from both PE 2 and PE 3, it uses the route from PE 2 as the primary link, and the route from PE 3 as the backup link.
Configure static BFD for public tunnels on PE 1 to detect the connectivity of the public tunnel from PE 1 to PE 2. When the tunnel PE 1—PE 2 operates correctly, traffic from CE 1 to CE 2 goes through the path CE 1—PE 1—PE 2—CE 2. When the tunnel fails, the traffic goes through the path CE 1—PE 1—PE 3—CE 2.
In this scenario, PE 1 is responsible for primary link detection and traffic switchover.
For more information about static BFD, see BFD configuration in High Availability Configuration Guide.
Restrictions: Hardware compatibility with IP L3VPN over SRv6
|
Hardware |
IP L3VPN over SRv6 compatibility |
|
MSR810, MSR810-W, MSR810-W-DB, MSR810-LM, MSR810-W-LM, MSR810-10-PoE, MSR810-LM-HK, MSR810-W-LM-HK, MSR810-LM-CNDE-SJK, MSR810-CNDE-SJK |
Yes |
|
MSR810-LMS, MSR810-LUS |
No |
|
MSR810-LMS-EA, MSR810-LME |
Yes |
|
MSR1004S-5G |
Yes |
|
MSR2600-6-X1, MSR2600-10-X1, MSR2600-15-X1 |
Yes |
|
MSR 2630 |
Yes |
|
MSR3600-28, MSR3600-51 |
Yes |
|
MSR3600-28-SI, MSR3600-51-SI |
No |
|
MSR3600-28-X1, MSR3600-28-X1-DP, MSR3600-51-X1, MSR3600-51-X1-DP |
Yes |
|
MSR3610-I-DP, MSR3610-IE-DP, MSR3610-IE-ES, MSR3610-IE-EAD, MSR-EAD-AK770, MSR3610-I-IG, MSR3610-IE-IG |
Yes |
|
MSR3610-X1, MSR3610-X1-DP, MSR3610-X1-DC, MSR3610-X1-DP-DC, MSR3620-X1, MSR3640-X1 |
Yes |
|
MSR3610, MSR3620, MSR3620-DP, MSR3640, MSR3660 |
Yes |
|
MSR3610-G, MSR3620-G |
Yes |
|
MSR3640-X1-HI |
Yes |
|
Hardware |
IP L3VPN over SRv6 compatibility |
|
MSR810-W-WiNet, MSR810-LM-WiNet |
Yes |
|
MSR830-4LM-WiNet |
Yes |
|
MSR830-5BEI-WiNet, MSR830-6EI-WiNet, MSR830-10BEI-WiNet |
Yes |
|
MSR830-6BHI-WiNet, MSR830-10BHI-WiNet |
Yes |
|
MSR2600-6-WiNet, MSR2600-10-X1-WiNet |
Yes |
|
MSR2630-WiNet |
Yes |
|
MSR3600-28-WiNet |
Yes |
|
MSR3610-X1-WiNet |
Yes |
|
MSR3610-WiNet, MSR3620-10-WiNet, MSR3620-DP-WiNet, MSR3620-WiNet, MSR3660-WiNet |
Yes |
|
Hardware |
IP L3VPN over SRv6 compatibility |
|
MSR2630-XS |
Yes |
|
MSR3600-28-XS |
Yes |
|
MSR3610-XS |
Yes |
|
MSR3620-XS |
Yes |
|
MSR3610-I-XS |
Yes |
|
MSR3610-IE-XS |
Yes |
|
MSR3620-X1-XS |
Yes |
|
MSR3640-XS |
Yes |
|
MSR3660-XS |
Yes |
|
Hardware |
IP L3VPN over SRv6 compatibility |
|
MSR810-LM-GL |
Yes |
|
MSR810-W-LM-GL |
Yes |
|
MSR830-6EI-GL |
Yes |
|
MSR830-10EI-GL |
Yes |
|
MSR830-6HI-GL |
Yes |
|
MSR830-10HI-GL |
Yes |
|
MSR1004S-5G-GL |
Yes |
|
MSR2600-6-X1-GL |
Yes |
|
MSR3600-28-SI-GL |
No |
IP L3VPN over SRv6 tasks at a glance
To configure IP L3VPN over SRv6, perform the following tasks:
1. Configuring a VPN instance and associating interfaces connected to CEs with the VPN instance
Perform this task on PEs. For more information, see MPLS L3VPN in MPLS Configuration Guide.
2. Configuring route exchange between a PE and a CE
Configure an IPv4 routing protocol (static routing, RIP, OSPF, IS-IS, EBGP, or IBGP) or an IPv6 routing protocol (IPv6 static routing, RIPng, OSPFv3, IPv6 IS-IS, EBGP, or IBGP) to exchange routes between a PE and a CE
On the CE, configure an IPv4 or IPv6 routing protocol to advertise routes of the local site to the PE. On the PE, associate the routing protocol with the VPN instance. For more information about routing protocol configurations, see Layer 3—IP Routing Configuration Guide.
3. Configuring route exchange between PEs
Perform this task to manually configure an End.DT4, End.DT6, End.DT46, End.DX4, or End.DX6 SID.
b. Applying a locator to a BGP VPN instance
BGP can advertise SRv6 SIDs through BGP routes only after you apply a locator to BGP.
c. Configuring PEs to exchange BGP VPNv4 or VPNv6 routes
d. Configuring IPv6 peers to exchange SRv6 SIDs
This feature enables PEs to exchange End.DT4, End.DT6, End.DT46, End.DX4, or End.DX6 SIDs through BGP VPNv4 or VPNv6 routes.
e. (Optional.) Configuring next hop-based dynamic End.DX4 or End.DX6 SID allocation for BGP routes
This feature enables a PE to dynamically allocate End.DX4 or End.DX6 SIDs to BGP private network routes based on the route next hops.
f. (Optional.) Configuring BGP VPNv4 or VPNv6 routes
4. Configuring the route recursion mode
5. Specifying a source address for the outer IPv6 header of SRv6-encapsulated packets
This feature specifies the source address of the outer IPv6 header for SRv6 packets that are delivered between two private network sites over the backbone network.
6. (Optional.) Enabling SRv6 VPN compatibility with a peer or peer group
7. (Optional.) Configuring IP L3VPN over SRv6 FRR
Configuring an SRv6 SID
Restrictions and guidelines
If PEs advertise BGP VPNv4 or VPNv6 routes to each other, you must specify a VPN instance when configuring an opcode.
Procedure
1. Enter system view.
system-view
2. Enable SRv6 and enter SRv6 view.
segment-routing ipv6
3. Configure a locator and enter SRv6 locator view.
locator locator-name [ ipv6-prefix ipv6-address prefix-length [ args args-length | static static-length ] * ]
4. Configure an opcode. Perform one of the following tasks:
¡ Configure an End.DT4 SID.
opcode opcode end-dt4 [ vpn-instance vpn-instance-name ]
The specified VPN instance must exist. An End.DT4 SID cannot be configured in different VPN instances.
¡ Configure an End.DT6 SID.
opcode opcode end-dt6 [ vpn-instance vpn-instance-name ]
The specified VPN instance must exist. An End.DT6 SID cannot be configured in different VPN instances.
¡ Configure an End.DT46 SID.
opcode opcode end-dt46 [ vpn-instance vpn-instance-name ]
The specified VPN instance must exist. An End.DT46 SID cannot be configured in different VPN instances.
¡ Configure an End.DX4 SID.
opcode opcode end-dx4 interface interface-type interface-number nexthop nexthop-ipv4-address [ vpn-instance vpn-instance-name ]
The specified VPN instance must exist. An End.DX4 SID cannot be configured with different output interfaces or next hops.
¡ Configure an End.DX6 SID.
opcode opcode end-dx6 interface interface-type interface-number nexthop nexthop-ipv6-address [ vpn-instance vpn-instance-name ]
The specified VPN instance must exist. An End.DX6 SID cannot be configured with different output interfaces or next hops.
Applying a locator to a BGP VPN instance
About this task
This feature is applicable to an IP L3VPN over SRv6 network with VPN sites. Use this feature in BGP-VPN IPv4 or IPv6 unicast address family view of a VPN instance to apply for SRv6 SIDs for the private network routes of the VPN instance.
Use this feature if the device will use End.DT4, End.DT6, End.DT46, End.DX4, or End.DX6 SIDs to deliver VPN traffic across sites.
Restrictions and guidelines
The VPN instance of the specified locator must be the same as the VPN instance of the private network. To specify a VPN instance for a locator, use the opcode end-dt4, opcode end-dt6, opcode end-dt46, opcode end-dx4, or opcode end-dx6 command in SRv6 locator view.
Prerequisites
Before you perform this task, you must create the specified locator.
Procedure
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP-VPN instance view.
ip vpn-instance vpn-instance-name
4. Enter BGP-VPN IPv4 unicast address family view or BGP-VPN IPv6 unicast address family view.
¡ Enter BGP-VPN IPv4 unicast address family view.
address-family ipv4 [ unicast ]
¡ Enter BGP-VPN IPv6 unicast address family view.
address-family ipv6 [ unicast ]
5. Apply a locator to the BGP VPN instance.
segment-routing ipv6 locator locator-name [ auto-sid-disable ]
By default, no locator is applied to a BGP VPN instance.
Configuring PEs to exchange BGP VPNv4 or VPNv6 routes
Restrictions and guidelines
For more information about the commands in this section, see BGP in Layer 3—IP Routing Command Reference.
To ensure optimal route selection and SRv6 tunnel traffic forwarding, make sure a pair of PEs are not both IPv4 and IPv6 peers to each other.
Procedure
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Specify a remote PE as an IPv6 peer.
peer { group-name | ipv6-address [ prefix-length ] } as-number as-number
4. Specify a source interface (IPv6 address) for establishing TCP connections to an IPv6 peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } connect-interface interface-type interface-number
By default, BGP uses the output interface in the optimal route destined for a BGP peer or peer group as the source interface for establishing TCP connections.
5. Create the BGP VPNv4 or VPNv6 address family and enter its view.
¡ Create the BGP VPNv4 address family and enter its view.
address-family vpnv4
¡ Create the BGP VPNv6 address family and enter its view.
address-family vpnv6
6. Enable BGP to exchange VPNv4 or VPNv6 routing information with an IPv6 peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } enable
By default, BGP cannot exchange VPNv4 or VPNv6 routing information with an IPv6 peer or peer group.
Configuring IPv6 peers to exchange SRv6 SIDs
About this task
Perform this task to configure IPv6 peers to exchange SRv6 SID information through BGP VPNv4, VPNv6, IPv4 unicast, or IPv6 unicast routes.
Procedure
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP VPNv4 address family view or BGP VPNv6 address family view.
¡ Enter BGP VPNv4 address family view.
address-family vpnv4
¡ Enter BGP VPNv6 address family view.
address-family vpnv6
4. Enable BGP to exchange SRv6 SID information with an IPv6 peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } prefix-sid
By default, BGP cannot exchange SRv6 SID information with an IPv6 peer or peer group.
Configuring next hop-based dynamic End.DX4 or End.DX6 SID allocation for BGP routes
About this task
This task is applicable to an IP L3VPN over SRv6 network with VPN sites. Perform this task to forward an SRv6 decapsulated VPN packet to the next hop without looking up the routing table of the VPN instance.
If you assign an End.DT4 SID, End.DT6 SID, or End.DT46 SID to a BGP VPN instance, all BGP private network routes of the instance are allocated that SID. When a PE removes the SRv6 encapsulation from a received packet, it looks up the routing table of the VPN instance based on the SID for an optimal route. Then, the PE forwards the packet to a CE. To forward the packet to the next hop without looking up the routing table of the VPN instance, perform this task.
This task dynamically allocates End.DX4 or End.DX6 SIDs to all next hops of the BGP private network routes in a VPN instance based on the next hop addresses. When forwarding a packet, the PE searches for the output interface and next hop based on the End.DX4 or End.DX6 SID of the packet. Then, the PE directly forwards the packet out of the output interface to the next hop.
Restrictions and guidelines
Before you perform this task in BGP-VPN IPv4 or IPv6 unicast address family view, execute the segment-routing ipv6 locator command in the same view to apply a locator to the view. This ensures successful dynamic End.DX4 or End.DX6 SID allocation.
This feature does not allocate End.DX4 or End.DX6 SIDs to direct routes.
Procedure
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP-VPN instance view.
ip vpn-instance vpn-instance-name
4. Enter BGP-VPN IPv4 unicast address family view or BGP-VPN IPv6 unicast address family view.
¡ Enter BGP-VPN IPv4 unicast address family view.
address-family ipv4 [ unicast ]
¡ Enter BGP-VPN IPv6 unicast address family view.
address-family ipv6 [ unicast ]
5. Automatically allocate End.DX4 or End.DX6 SIDs to all next hops of BGP private network routes.
segment-routing ipv6 apply-sid all-nexthop
By default, VPN instance-based SID allocation is used for private network routes.
Configuring BGP VPNv4 or VPNv6 routes
Restrictions and guidelines for BGP VPNv4 or VPNv6 route configuration
For more information about the commands in this section, see BGP in Layer 3—IP Routing Command Reference.
Controlling BGP VPNv4 or VPNv6 route advertisement and reception
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP VPNv4 address family view or BGP VPNv6 address family view.
¡ Enter BGP VPNv4 address family view.
address-family vpnv4
¡ Enter BGP VPNv6 address family view.
address-family vpnv6
4. Set the maximum number of routes that BGP can receive from a peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } route-limit prefix-number [ { alert-only | discard | reconnect reconnect-time } | percentage-value ] *
By default, the number of routes that BGP can receive from a peer or peer group is not limited.
5. Save all route updates from a peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } keep-all-routes
By default, route updates from peers and peer groups are not saved.
Setting a preferred value for received BGP VPNv4 or VPNv6 routes
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP VPNv4 address family view or BGP VPNv6 address family view.
¡ Enter BGP VPNv4 address family view.
address-family vpnv4
¡ Enter BGP VPNv6 address family view.
address-family vpnv6
4. Set a preferred value for routes received from a peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } preferred-value value
By default, the preferred value is 0 for routes received from a peer or peer group.
Configuring BGP VPNv4 or VPNv6 route reflection
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP VPNv4 address family view or BGP VPNv6 address family view.
¡ Enter BGP VPNv4 address family view.
address-family vpnv4
¡ Enter BGP VPNv6 address family view.
address-family vpnv6
4. Configure the router as a route reflector (RR) and specify a peer or peer group as its client.
peer { group-name | ipv6-address [ prefix-length ] } reflect-client
By default, no RR or client is configured.
5. (Optional.) Enable route reflection between clients.
reflect between-clients
By default, route reflection between clients is enabled.
6. (Optional.) Configure the cluster ID of the RR.
reflector cluster-id { cluster-id | ip-address }
By default, an RR uses its own router ID as the cluster ID.
7. (Optional.) Create an RR reflection policy.
rr-filter ext-comm-list-number
By default, an RR does not filter reflected routes.
8. (Optional.) Enable the RR to change the attributes of routes to be reflected.
reflect change-path-attribute
By default, the RR cannot change the attributes of routes to be reflected.
Configuring BGP VPNv4 or VPNv6 route attributes
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP VPNv4 address family view or BGP VPNv6 address family view.
¡ Enter BGP VPNv4 address family view.
address-family vpnv4
¡ Enter BGP VPNv6 address family view.
address-family vpnv6
4. Specify the router as the next hop for routes sent to a peer or peer group.
peer { group-name | ipv4-address [ mask-length ] | ipv6-address [ prefix-length ] } next-hop-local
By default, the router sets itself as the next hop for routes sent to a peer or peer group.
5. Configure the AS_PATH attribute.
¡ Permit the local AS number to appear in routes from a peer or peer group and set the appearance times.
peer { group-name | ipv6-address [ prefix-length ] } allow-as-loop [ number ]
By default, the local AS number is not allowed in routes from a peer or peer group.
This command is available only in BGP VPNv4 address family view.
¡ Remove private AS numbers from the AS_PATH attribute of updates sent to an EBGP peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } public-as-only
By default, BGP updates sent to an EBGP peer or peer group can carry both public and private AS numbers.
6. Advertise the COMMUNITY attribute to a peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } advertise-community
By default, the COMMUNITY attribute is not advertised.
7. Configure the SoO attribute for a peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } soo site-of-origin
By default, no SoO attribute is configured for a peer or peer group.
Configuring BGP VPNv4 or VPNv6 route distribution filtering policies
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP VPNv4 address family view or BGP VPNv6 address family view.
¡ Enter BGP VPNv4 address family view.
address-family vpnv4
¡ Enter BGP VPNv6 address family view.
address-family vpnv6
4. Specify an ACL or IP prefix list to filter advertised BGP routes.
filter-policy { ipv4-acl-number | prefix-list prefix-list-name } export [ protocol process-id ]
By default, no ACL or IP prefix list is specified to filter advertised BGP routes.
5. Specify an ACL or IP prefix list to filter received BGP routes.
filter-policy { ipv4-acl-number | prefix-list prefix-list-name } import
By default, no ACL or IP prefix list is specified to filter received BGP routes.
6. Specify an IP prefix list to filter BGP routes for a peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } prefix-list prefix-list-name { export | import }
By default, no IP prefix list is specified to filter BGP routes for a peer or peer group.
7. Apply a routing policy to routes received from or advertised to a peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } route-policy route-policy-name { export | import }
By default, no routing policy is applied to routes received from or advertised to a peer or peer group.
8. Enable route target filtering of received VPNv4 or VPNv6 routes.
policy vpn-target
By default, the route target filtering feature is enabled for received VPNv4 or VPNv6 routes. BGP adds an VPNv4 or VPNv6 route to the routing table only when the export route targets of the route match the local import route targets.
Configuring the route recursion mode
About this task
After a PE receives a customer packet destined for an SRv6 SID, it forwards the packet according to the route recursion mode.
· SRv6-BE mode—This mode is also called SID-based forwarding mode. In this mode, the PE first encapsulates the End.DT4, End.DT6, or End.DT46 SID into the packet. Then, the PE searches the IPv6 routing table based on the SID encapsulated in the packet to forward the packet.
· SRv6-TE mode—This mode is also called SRv6 TE policy-based forwarding mode. In this mode, the PE first searches for a matching SRv6 TE policy based on the packet attributes. Then, the PE adds an SRH to the packet. The SRH includes the End.DT4, End.DT6, or End.DT46 SID and the SID list of the SRv6 TE policy. Finally, the PE forwards the encapsulated packet through the SRv6 TE policy. For more information, see "Configuring SRv6 TE policies."
· SRv6-TE and SRv6-BE hybrid mode—In this mode, the PE preferentially uses the SRv6-TE mode to forward the packet. If no SRv6 TE policy is available for the packet, the PE forwards the packet in SRv6-BE mode.
Prerequisites
To use the SRv6-TE mode or the SRv6-TE and SRv6-BE hybrid mode, you must configure a tunnel policy and SRv6 TE policy. For more information, see tunnel policy configuration in MPLS Configuration Guide and "Configuring SRv6 TE policies."
Procedure
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP-VPN instance view.
ip vpn-instance vpn-instance-name
4. Enter BGP-VPN IPv4 unicast address family view or BGP-VPN IPv6 unicast address family view.
¡ Enter BGP-VPN IPv4 unicast address family view.
address-family ipv4 [ unicast ]
¡ Enter BGP-VPN IPv6 unicast address family view.
address-family ipv6 [ unicast ]
5. Configure the route recursion mode.
segment-routing ipv6 { best-effort | traffic-engineer | traffic-engineer best-effort }
By default, a PE searches the IPv6 routing table based on the next hop of a matching route to forward traffic.
Specifying a source address for the outer IPv6 header of SRv6-encapsulated packets
Restrictions and guidelines
To ensure correct traffic forwarding in an IP L3VPN over SRv6 network with VPN or public network sites, you must specify a source address for the outer IPv6 header of SRv6-encapsulated packets.
You cannot specify a loopback address, link-local address, multicast address, or unspecified address as the source IPv6 address. You must specify an IPv6 address of the local device as the source IPv6 address, and make sure the IPv6 address has been advertised by a routing protocol. As a best practice, specify a loopback interface address of the local device as the source IPv6 address.
Procedure
1. Enter system view.
system-view
2. Enter SRv6 view.
segment-routing ipv6
3. Specify a source address for the outer IPv6 header of SRv6-encapsulated packets.
encapsulation source-address ipv6-address [ ip-ttl ttl-value ]
By default, no source address is specified for the outer IPv6 header of SRv6-encapsulated packets.
Enabling SRv6 VPN compatibility with a peer or peer group
About this task
This task is applicable to an IP L3VPN over SRv6 network with VPN sites.
PEs from different vendors might define different End.DT4 SID message formats in VPNv4 routes. A PE cannot learn VPNv4 routes from its peers if it uses an End.DT4 SID message format different than its peers. To resolve this issue, perform this task on the PE to enable its SRv6 VPN compatibility with its peers. This task ensures that a Comware PE can communicate with PEs from other vendors in an IP L3VPN over SRv6 network.
Procedure
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP VPNv4 address family view.
address-family vpnv4
4. Enable SRv6 VPN compatibility with a peer or peer group.
peer { group-name | ipv6-address [ prefix-length ] } srv6-vpn compatible
By default, SRv6 compatibility is disabled with a peer or peer group.
Configuring IP L3VPN over SRv6 FRR
About this task
This task is applicable to an IP L3VPN over SRv6 network with VPN sites.
IP L3VPN over SRv6 FRR enables the device to calculate backup routes for all routes of a VPN instance to reduce the traffic interruption caused by link or device failures on the backbone. If the device learns two unequal-cost routes destined for the same network from different peers, the optimal route is backed up by the other route. When the optimal route becomes unavailable, the device uses the backup route to forward traffic. At the same time, the device calculates a new optimal route and then uses it to direct traffic forwarding.
Restrictions and guidelines
This feature might cause routing loops in certain conditions. Make sure you are fully aware of this feature when you use it on a live network.
Procedure
1. Enter system view.
system-view
2. Configure static BFD.
bfd static session-name [ peer-ipv6 ipv6-address [ vpn-instance vpn-instance-name ] source-ipv6 ipv6-address [ discriminator local local-value remote remote-value ] ]
3. Return to system view.
quit
4. Enter BGP instance view.
bgp as-number [ instance instance-name ]
5. Configure BGP FRR to use BFD to detect next hop connectivity for the primary route.
primary-path-detect bfd echo
By default, BGP FRR uses ARP to detect the connectivity to the next hop of the primary route.
For more information about this command, see BGP commands in Layer 3—IP Routing Command Reference.
6. Enter BGP-VPN IPv4 unicast address family view, BGP VPNv4 address family view, BGP-VPN IPv6 unicast address family view, or BGP VPNv6 address family view.
¡ Execute the following commands in sequence to enter BGP-VPN IPv4 unicast address family view:
ip vpn-instance vpn-instance-name
address-family ipv4 [ unicast ]
¡ Enter BGP VPNv4 address family view.
address-family vpnv4
¡ Execute the following commands in sequence to enter BGP-VPN IPv6 unicast address family view:
ip vpn-instance vpn-instance-name
address-family ipv6 [ unicast ]
7. Enable FRR for the address family.
pic
By default, FRR is disabled for a BGP address family.
For more information about this command, see BGP commands in Layer 3—IP Routing Command Reference.
Display and maintenance commands for IP L3VPN over SRv6
Resetting BGP sessions
For BGP setting changes to take effect, you must reset or soft-reset BGP sessions. Soft-resetting BGP sessions updates BGP routing information without tearing down the BGP sessions. Resetting BGP sessions updates BGP routing information by tearing down and re-establishing the BGP sessions. Soft-reset requires that both the local router and the peer support ROUTE-REFRESH messages.
Execute the commands in this section in user view. For more information about the commands, see BGP in Layer 3—IP Routing Command Reference.
|
Task |
Command |
|
Soft-reset BGP sessions of the BGP VPNv4 address family. |
refresh bgp [ instance instance-name ] ipv6-address [ prefix-length ] { export | import } vpnv4 |
|
Reset BGP sessions of the BGP VPNv4 address family. |
reset bgp [ instance instance-name ] ipv6-address [ prefix-length ] vpnv4 |
Displaying and maintaining the running status of IP L3VPN over SRv6 VPN
Execute display commands in any view and reset commands in user view.
For more information about the commands in this section, see BGP in Layer 3—IP Routing Command Reference.
|
Task |
Command |
|
Display BGP VPNv4 peer or peer group information. |
display bgp [ instance instance-name ] peer vpnv4 { ipv6-address prefix-length | ipv6-address { log-info | verbose } } |
|
Display BGP VPNv6 peer or peer group information. |
display bgp [ instance instance-name ] peer vpnv6 [ vpn-instance vpn-instance-name ] [ ipv6-address prefix-length | { ipv6-address | group-name group-name } log-info | [ ipv6-address ] verbose ] |
|
Display BGP update group information for VPNv4 address family. |
display bgp [ instance instance-name ] update-group vpnv4 ipv6-address |
|
Display BGP update group information for VPNv6 address family. |
display bgp [ instance instance-name ] update-group vpnv6 [ vpn-instance vpn-instance-name ] [ ipv6-address ] |
|
Clear flap statistics for BGP VPNv4 routes. |
reset bgp [ instance instance-name ] flap-info vpnv4 [ ipv4-address [ mask | mask-length ] | as-path-acl as-path-acl-number | peer ipv6-address [ prefix-length ] ] |
IP L3VPN over SRv6 configuration examples
Example: Configuring IPv4 L3VPN over SRv6
Network configuration
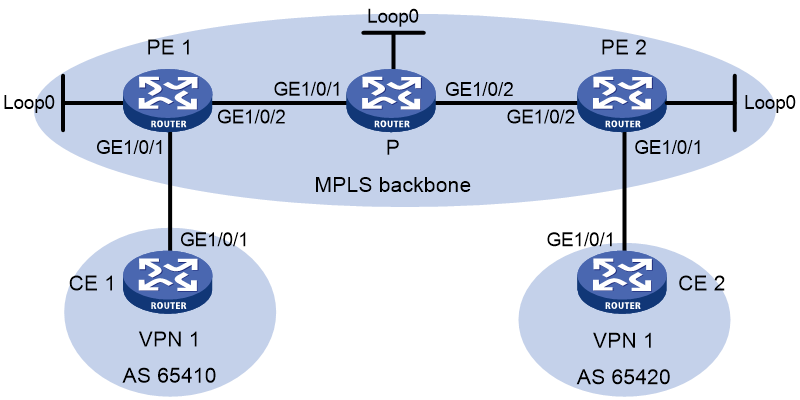
As shown in Figure 3, the backbone network is an IPv6 network, and VPN 1 is an IPv4 network. Deploy IP L3VPN over SRv6 between PE 1 and PE 2 and use an SRv6 tunnel to transmit VPNv4 traffic between the PEs.
· Configure EBGP to exchange VPN routing information between the CEs and PEs.
· Configure IPv6 IS-IS on the PEs in the same AS to realize IPv6 network connectivity.
· Configure MP-IBGP to exchange VPNv4 routing information between the PEs.
Table 1 Interface and IP address assignment
|
Device |
Interface |
IP address |
Device |
Interface |
IP address |
|
CE 1 |
GE1/0/1 |
10.1.1.2/24 |
PE 2 |
Loop0 |
3::3/128 |
|
PE 1 |
Loop0 |
1::1/128 |
|
GE1/0/1 |
10.2.1.1/24 |
|
|
GE1/0/1 |
10.1.1.1/24 |
|
GE1/0/2 |
2002::1/96 |
|
|
GE1/0/2 |
2001::1/96 |
CE 2 |
GE1/0/1 |
10.2.1.2/24 |
|
P |
Loop0 |
2::2/128 |
|
|
|
|
|
GE1/0/1 |
2001::2/96 |
|
|
|
|
|
GE1/0/2 |
2002::2/96 |
|
|
|
Procedure
1. Configure IPv6 IS-IS on the PEs and device P for network connectivity between the devices:
# Configure PE 1.
<PE1> system-view
[PE1] isis 1
[PE1-isis-1] is-level level-1
[PE1-isis-1] cost-style wide
[PE1-isis-1] network-entity 10.1111.1111.1111.00
[PE1-isis-1] address-family ipv6 unicast
[PE1-isis-1-ipv6] quit
[PE1-isis-1] quit
[PE1] interface loopback 0
[PE1-LoopBack0] ipv6 address 1::1 128
[PE1-LoopBack0] isis ipv6 enable 1
[PE1-LoopBack0] quit
[PE1] interface gigabitethernet 1/0/2
[PE1-GigabitEthernet1/0/2] ipv6 address 2001::1 96
[PE1-GigabitEthernet1/0/2] isis ipv6 enable
[PE1-GigabitEthernet1/0/2] quit
# Configure P.
<P> system-view
[P] isis
[P-isis-1] is-level level-1
[P-isis-1] cost-style wide
[P-isis-1] network-entity 10.2222.2222.2222.00
[P-isis-1] address-family ipv6 unicast
[P-isis-1-ipv6] quit
[P-isis-1] quit
[P] interface loopback 0
[P-LoopBack0] ipv6 address 2::2 128
[P-LoopBack0] isis ipv6 enable
[P-LoopBack0] quit
[P] interface gigabitethernet 1/0/1
[P-GigabitEthernet1/0/1] ipv6 address 2001::2 96
[P-GigabitEthernet1/0/1] isis ipv6 enable
[P-GigabitEthernet1/0/1] quit
[P] interface gigabitethernet 1/0/2
[P-GigabitEthernet1/0/2] ipv6 address 2002::2 96
[P-GigabitEthernet1/0/2] isis ipv6 enable
[P-GigabitEthernet1/0/2] quit
# Configure PE 2.
<PE2> system-view
[PE2] isis
[PE2-isis-1] is-level level-1
[PE2-isis-1] cost-style wide
[PE2-isis-1] network-entity 10.3333.3333.3333.00
[PE2-isis-1] address-family ipv6 unicast
[PE2-isis-1-ipv6] quit
[PE2-isis-1] quit
[PE2] interface loopback 0
[PE2-LoopBack0] ipv6 address 3::3 128
[PE2-LoopBack0] isis ipv6 enable
[PE2-LoopBack0] quit
[PE2] interface gigabitethernet 1/0/2
[PE2-GigabitEthernet1/0/2] ipv6 address 2002::1 96
[PE2-GigabitEthernet1/0/2] isis ipv6 enable
[PE2-GigabitEthernet1/0/2] quit
# Verify that PE 1, P, and PE 2 have established IPv6 IS-IS neighbor relationships and the neighbor state is up.
[PE1] display isis peer
[P] display isis peer
[PE2] display isis peer
# Verify that PE 1 and PE 2 each learn a route destined for the loopback interface of each other.
[PE1] display isis route ipv6
[PE2] display isis route ipv6
2. Configure VPN instance settings on PE 1 and PE 2 and verify that each CE can access its local PE:
# Configure PE 1.
[PE1] ip vpn-instance vpn1
[PE1-vpn-instance-vpn1] route-distinguisher 100:1
[PE1-vpn-instance-vpn1] vpn-target 111:1
[PE1-vpn-instance-vpn1] quit
[PE1] interface gigabitethernet 1/0/1
[PE1-GigabitEthernet1/0/1] ip binding vpn-instance vpn1
[PE1-GigabitEthernet1/0/1] ip address 10.1.1.1 24
[PE1-GigabitEthernet1/0/1] quit
# Configure PE 2.
[PE2] ip vpn-instance vpn1
[PE2-vpn-instance-vpn1] route-distinguisher 100:1
[PE2-vpn-instance-vpn1] vpn-target 111:1
[PE2-vpn-instance-vpn1] quit
[PE2] interface gigabitethernet 1/0/1
[PE2-GigabitEthernet1/0/1] ip binding vpn-instance vpn1
[PE2-GigabitEthernet1/0/1] ip address 10.2.1.1 24
[PE2-GigabitEthernet1/0/1] quit
# Configure IP addresses for the interfaces on the CEs, as shown in Figure 3. (Details not shown.)
# Display VPN instance settings on each PE. This step uses PE 1 as an example.
[PE1] display ip vpn-instance
Total VPN-Instances configured : 1
Total IPv4 VPN-Instances configured : 1
Total IPv6 VPN-Instances configured : 1
VPN-Instance Name RD Address family Create time
vpn1 100:1 IPv4/IPv6 2019/08/12 13:59:39
# Verify that each PE can ping its local CE. This step uses PE 1 and CE 1 as an example.
[PE1] ping -vpn-instance vpn1 10.1.1.2
Ping 10.1.1.2 (10.1.1.2): 56 data bytes, press CTRL+C to break
56 bytes from 10.1.1.2: icmp_seq=0 ttl=255 time=2.000 ms
56 bytes from 10.1.1.2: icmp_seq=1 ttl=255 time=0.000 ms
56 bytes from 10.1.1.2: icmp_seq=2 ttl=255 time=1.000 ms
56 bytes from 10.1.1.2: icmp_seq=3 ttl=255 time=0.000 ms
56 bytes from 10.1.1.2: icmp_seq=4 ttl=255 time=0.000 ms
--- Ping statistics for 10.1.1.2 in VPN instance vpn1 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 0.000/0.600/2.000/0.800 ms
3. Set up an EBGP peer relationship between each PE and its local CE and distribute VPN routes to EBGP:
# Configure CE 1.
<CE1> system-view
[CE1] bgp 65410
[CE1-bgp-default] peer 10.1.1.1 as-number 100
[CE1-bgp-default] address-family ipv4 unicast
[CE1-bgp-default-ipv4] peer 10.1.1.1 enable
[CE1-bgp-default-ipv4] import-route direct
[CE1-bgp-default-ipv4] quit
[CE1-bgp-default] quit
# Configure CE 2 in the same way as CE 1 is configured. (Details not shown.)
# Configure PE 1.
[PE1] bgp 100
[PE1-bgp-default] router-id 1.1.1.1
[PE1-bgp-default] ip vpn-instance vpn1
[PE1-bgp-default-vpn1] peer 10.1.1.2 as-number 65410
[PE1-bgp-default-vpn1] address-family ipv4 unicast
[PE1-bgp-default-ipv4-vpn1] peer 10.1.1.2 enable
[PE1-bgp-default-ipv4-vpn1] quit
[PE1-bgp-default-vpn1] quit
# Configure PE 2 in the same way PE 1 is configured. (Details not shown.)
# Verify that the PEs have established BGP peer relationships with their local CEs and the peers are in established state.
[PE1] display bgp peer ipv4 vpn-instance
[PE2] display bgp peer ipv4 vpn-instance
4. Set up an MP-IBGP peer relationship between PE 1 and PE 2:
# Configure PE 1.
[PE1] bgp 100
[PE1-bgp-default] peer 3::3 as-number 100
[PE1-bgp-default] peer 3::3 connect-interface loopback 0
[PE1-bgp-default] address-family vpnv4
[PE1-bgp-default-vpnv4] peer 3::3 enable
[PE1-bgp-default-vpnv4] quit
[PE1-bgp-default] quit
# Configure PE 2.
[PE2] bgp 100
[PE2-bgp-default] peer 1::1 as-number 100
[PE2-bgp-default] peer 1::1 connect-interface loopback 0
[PE2-bgp-default] address-family vpnv4
[PE2-bgp-default-vpnv4] peer 1::1 enable
[PE2-bgp-default-vpnv4] quit
[PE2-bgp-default] quit
# Verify that the PEs have established a BGP peer relationship and the peers are in established state.
[PE1] display bgp peer vpnv4
[PE2] display bgp peer vpnv4
5. Specify a source address for the outer IPv6 header of SRv6-encapsulated IP L3VPN packets on PE 1 and PE 2:
# Configure PE 1.
[PE1] segment-routing ipv6
[PE1-segment-routing-ipv6] encapsulation source-address 1::1
# Configure PE 2.
[PE2] segment-routing ipv6
[PE2-segment-routing-ipv6] encapsulation source-address 3::3
6. Configure the destination address (End.DT4 SID) of the outer IPv6 header for SRv6-encapsulated IP L3VPN packets:
# Configure PE 1.
[PE1-segment-routing-ipv6] locator aaa ipv6-prefix 1:2::1:0 96 static 8
[PE1-segment-routing-ipv6-locator-aaa] quit
[PE1-segment-routing-ipv6] quit
[PE1] isis 1
[PE1-isis-1] address-family ipv6 unicast
[PE1-isis-1-ipv6] segment-routing ipv6 locator aaa
[PE1-isis-1-ipv6] quit
[PE1-isis-1] quit
# Configure PE 2.
[PE2-segment-routing-ipv6] locator bbb ipv6-prefix 6:5::1:0 96 static 8
[PE2-segment-routing-ipv6-locator-bbb] quit
[PE2-segment-routing-ipv6] quit
[PE2] isis 1
[PE2-isis-1] address-family ipv6 unicast
[PE2-isis-1-ipv6] segment-routing ipv6 locator bbb
[PE2-isis-1-ipv6] quit
[PE2-isis-1] quit
# Verify that the PEs have distributed the End.DT4 SIDs to the routing table and generated SRv6 routes. This step uses PE 1 as an example.
[PE1] display ipv6 routing-table protocol srv6
Summary count : 1
SRv6 Routing table status : <Active>
Summary count : 1
Destination: 1:2::101/128 Protocol : SRv6
NextHop : ::1 Preference: 4
Interface : InLoop0 Cost : 0
SRv6 Routing table status : <Inactive>
Summary count : 0
7. Add End.DT4 SIDs to private network routes on PE 1 and PE 2:
# Configure PE 1.
[PE1] bgp 100
[PE1-bgp-default] ip vpn-instance vpn1
[PE1-bgp-default-vpn1] address-family ipv4 unicast
[PE1-bgp-default-ipv4-vpn1] segment-routing ipv6 locator aaa
[PE1-bgp-default-ipv4-vpn1] quit
[PE1-bgp-default-vpn1] quit
[PE1-bgp-default] quit
# Configure PE 2.
[PE2] bgp 100
[PE2-bgp-default] ip vpn-instance vpn1
[PE2-bgp-default-vpn1] address-family ipv4 unicast
[PE2-bgp-default-ipv4-vpn1] segment-routing ipv6 locator bbb
[PE2-bgp-default-ipv4-vpn1] quit
[PE2-bgp-default-vpn1] quit
[PE2-bgp-default] quit
8. Enable IPv6 peers on the PEs to exchange End.DT4 SIDs and enable the SID-route-recursion feature:
# Configure PE 1.
[PE1] bgp 100
[PE1-bgp-default] address-family vpnv4
[PE1-bgp-default-vpnv4] peer 3::3 prefix-sid
[PE1-bgp-default-vpnv4] quit
[PE1-bgp-default] ip vpn-instance vpn1
[PE1-bgp-default-vpn1] address-family ipv4 unicast
[PE1-bgp-default-ipv4-vpn1] segment-routing ipv6 best-effort
[PE1-bgp-default-ipv4-vpn1] quit
[PE1-bgp-default-vpn1] quit
[PE1-bgp-default] quit
# Configure PE 2.
[PE2] bgp 100
[PE2-bgp-default] address-family vpnv4
[PE2-bgp-default-vpnv4] peer 1::1 prefix-sid
[PE2-bgp-default-vpnv4] quit
[PE2-bgp-default] ip vpn-instance vpn1
[PE2-bgp-default-vpn1] address-family ipv4 unicast
[PE2-bgp-default-ipv4-vpn1] segment-routing ipv6 best-effort
[PE2-bgp-default-ipv4-vpn1] quit
[PE2-bgp-default-vpn1] quit
[PE2-bgp-default] quit
# Display BGP VPNv4 routing information on each PE and verify that the routes advertised by the PEs have the SID attribute. This step uses PE 1 as an example.
[PE1] display bgp routing-table vpnv4 10.2.1.0
BGP local router ID: 1.1.1.1
Local AS number: 100
Route distinguisher: 100:1(vpn1)
Total number of routes: 1
Paths: 1 available, 1 best
BGP routing table information of 10.2.1.0/24:
From : 3::3 (3.3.3.3)
Rely nexthop : FE80::2A96:34FF:FE9D:216
Original nexthop: 3::3
Out interface : GigabitEthernet1/0/2
Route age : 00h14m23s
OutLabel : 3
Ext-Community : <RT: 111:1>
RxPathID : 0x0
TxPathID : 0x0
PrefixSID : End.DT4 SID <6:5::101>
AS-path : 65420
Origin : incomplete
Attribute value : MED 0, localpref 100, pref-val 0
State : valid, internal, best
IP precedence : N/A
QoS local ID : N/A
Traffic index : N/A
Tunnel policy : NULL
Rely tunnel IDs : N/A
Verifying the configuration
# Display IPv4 routing table information on the PEs and verify that each PE has a route destined for the remote CE and the next hop of the route is the End.DT4 SID of the route. This step uses PE 1 as an example.
[PE1] display ip routing-table vpn-instance vpn1
Destinations : 11 Routes : 11
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
10.1.1.0/24 Direct 0 0 10.1.1.1 GE1/0/1
10.1.1.0/32 Direct 0 0 10.1.1.1 GE1/0/1
10.1.1.1/32 Direct 0 0 127.0.0.1 InLoop0
10.1.1.255/32 Direct 0 0 10.1.1.1 GE1/0/1
10.2.1.0/24 BGP 255 0 6:5::101 GE1/0/2
127.0.0.0/8 Direct 0 0 127.0.0.1 InLoop0
127.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
127.0.0.1/32 Direct 0 0 127.0.0.1 InLoop0
127.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
255.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
# Verify that CE 1 and CE 2 can ping each other. (Details not shown.)
IP L3VPN over SRv6 configuration examples
Example: Configuring IPv4 L3VPN over SRv6
Network configuration
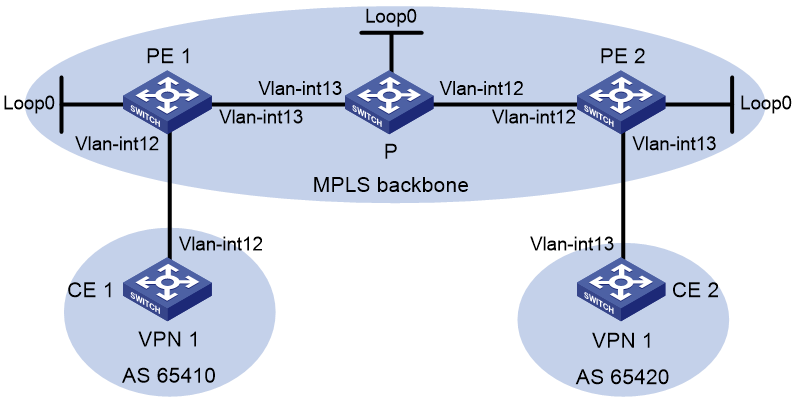
As shown in Figure 4, the backbone network is an IPv6 network, and VPN 1 is an IPv4 network. Deploy IP L3VPN over SRv6 between PE 1 and PE 2 and use an SRv6 tunnel to transmit VPNv4 traffic between the PEs.
· Configure EBGP to exchange VPN routing information between the CEs and PEs.
· Configure IPv6 IS-IS on the PEs in the same AS to realize IPv6 network connectivity.
· Configure MP-IBGP to exchange VPNv4 routing information between the PEs.
Table 2 Interface and IP address assignment
|
Device |
Interface |
IP address |
Device |
Interface |
IP address |
|
CE 1 |
VLAN-interface 12 |
10.1.1.2/24 |
PE 2 |
Loopback 0 |
3::3/128 |
|
PE 1 |
Loopback 0 |
1::1/128 |
|
VLAN-interface 13 |
10.2.1.1/24 |
|
|
VLAN-interface 12 |
10.1.1.1/24 |
|
VLAN-interface 12 |
2002::1/96 |
|
|
VLAN-interface 13 |
2001::1/96 |
CE 2 |
VLAN-interface 13 |
10.2.1.2/24 |
|
P |
Loopback 0 |
2::2/128 |
|
|
|
|
|
VLAN-interface 13 |
2001::2/96 |
|
|
|
|
|
VLAN-interface 12 |
2002::2/96 |
|
|
|
Procedure
1. Configure IPv6 IS-IS on the PEs and device P for network connectivity between the devices:
# Configure PE 1.
<PE1> system-view
[PE1] isis 1
[PE1-isis-1] is-level level-1
[PE1-isis-1] cost-style wide
[PE1-isis-1] network-entity 10.1111.1111.1111.00
[PE1-isis-1] address-family ipv6 unicast
[PE1-isis-1-ipv6] quit
[PE1-isis-1] quit
[PE1] interface loopback 0
[PE1-LoopBack0] ipv6 address 1::1 128
[PE1-LoopBack0] isis ipv6 enable 1
[PE1-LoopBack0] quit
[PE1] interface vlan-interface 13
[PE1-Vlan-interface13] ipv6 address 2001::1 96
[PE1-Vlan-interface13] isis ipv6 enable
[PE1-Vlan-interface13] quit
# Configure P.
<P> system-view
[P] isis
[P-isis-1] is-level level-1
[P-isis-1] cost-style wide
[P-isis-1] network-entity 10.2222.2222.2222.00
[P-isis-1] address-family ipv6 unicast
[P-isis-1-ipv6] quit
[P-isis-1] quit
[P] interface loopback 0
[P-LoopBack0] ipv6 address 2::2 128
[P-LoopBack0] isis ipv6 enable
[P-LoopBack0] quit
[P] interface vlan-interface 13
[P-Vlan-interface13] ipv6 address 2001::2 96
[P-Vlan-interface13] isis ipv6 enable
[P-Vlan-interface13] quit
[P] interface vlan-interface 12
[P-Vlan-interface12] ipv6 address 2002::2 96
[P-Vlan-interface12] isis ipv6 enable
[P-Vlan-interface12] quit
# Configure PE 2.
<PE2> system-view
[PE2] isis
[PE2-isis-1] is-level level-1
[PE2-isis-1] cost-style wide
[PE2-isis-1] network-entity 10.3333.3333.3333.00
[PE2-isis-1] address-family ipv6 unicast
[PE2-isis-1-ipv6] quit
[PE2-isis-1] quit
[PE2] interface loopback 0
[PE2-LoopBack0] ipv6 address 3::3 128
[PE2-LoopBack0] isis ipv6 enable
[PE2-LoopBack0] quit
[PE2] interface vlan-interface 12
[PE2-Vlan-interface12] ipv6 address 2002::1 96
[PE2-Vlan-interface12] isis ipv6 enable
[PE2-Vlan-interface12] quit
# Verify that PE 1, P, and PE 2 have established IPv6 IS-IS neighbor relationships and the neighbor state is up.
[PE1] display isis peer
[P] display isis peer
[PE2] display isis peer
# Verify that PE 1 and PE 2 each learn a route destined for the loopback interface of each other.
[PE1] display isis route ipv6
[PE2] display isis route ipv6
2. Configure VPN instance settings on PE 1 and PE 2 and verify that each CE can access its local PE:
# Configure PE 1.
[PE1] ip vpn-instance vpn1
[PE1-vpn-instance-vpn1] route-distinguisher 100:1
[PE1-vpn-instance-vpn1] vpn-target 111:1
[PE1-vpn-instance-vpn1] quit
[PE1] interface vlan-interface 12
[PE1-Vlan-interface12] ip binding vpn-instance vpn1
[PE1-Vlan-interface12] ip address 10.1.1.1 24
[PE1-Vlan-interface12] quit
# Configure PE 2.
[PE2] ip vpn-instance vpn1
[PE2-vpn-instance-vpn1] route-distinguisher 100:1
[PE2-vpn-instance-vpn1] vpn-target 111:1
[PE2-vpn-instance-vpn1] quit
[PE2] interface vlan-interface 13
[PE2-Vlan-interface13] ip binding vpn-instance vpn1
[PE2-Vlan-interface13] ip address 10.2.1.1 24
[PE2-Vlan-interface13] quit
# Configure IP addresses for the interfaces on the CEs, as shown in Figure 4. (Details not shown.)
# Display VPN instance settings on each PE. This step uses PE 1 as an example.
[PE1] display ip vpn-instance
Total VPN-Instances configured : 1
Total IPv4 VPN-Instances configured : 1
Total IPv6 VPN-Instances configured : 1
VPN-Instance Name RD Address family Create time
vpn1 100:1 IPv4/IPv6 2019/08/12 13:59:39
# Verify that each PE can ping its local CE. This step uses PE 1 and CE 1 as an example.
[PE1] ping -vpn-instance vpn1 10.1.1.2
Ping 10.1.1.2 (10.1.1.2): 56 data bytes, press CTRL+C to break
56 bytes from 10.1.1.2: icmp_seq=0 ttl=255 time=2.000 ms
56 bytes from 10.1.1.2: icmp_seq=1 ttl=255 time=0.000 ms
56 bytes from 10.1.1.2: icmp_seq=2 ttl=255 time=1.000 ms
56 bytes from 10.1.1.2: icmp_seq=3 ttl=255 time=0.000 ms
56 bytes from 10.1.1.2: icmp_seq=4 ttl=255 time=0.000 ms
--- Ping statistics for 10.1.1.2 in VPN instance vpn1 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 0.000/0.600/2.000/0.800 ms
3. Set up an EBGP peer relationship between each PE and its local CE and distribute VPN routes to EBGP:
# Configure CE 1.
<CE1> system-view
[CE1] bgp 65410
[CE1-bgp-default] peer 10.1.1.1 as-number 100
[CE1-bgp-default] address-family ipv4 unicast
[CE1-bgp-default-ipv4] peer 10.1.1.1 enable
[CE1-bgp-default-ipv4] import-route direct
[CE1-bgp-default-ipv4] quit
[CE1-bgp-default] quit
# Configure CE 2 in the same way as CE 1 is configured. (Details not shown.)
# Configure PE 1.
[PE1] bgp 100
[PE1-bgp-default] router-id 1.1.1.1
[PE1-bgp-default] ip vpn-instance vpn1
[PE1-bgp-default-vpn1] peer 10.1.1.2 as-number 65410
[PE1-bgp-default-vpn1] address-family ipv4 unicast
[PE1-bgp-default-ipv4-vpn1] peer 10.1.1.2 enable
[PE1-bgp-default-ipv4-vpn1] quit
[PE1-bgp-default-vpn1] quit
# Configure PE 2 in the same way PE 1 is configured. (Details not shown.)
# Verify that the PEs have established BGP peer relationships with their local CEs and the peers are in established state.
[PE1] display bgp peer ipv4 vpn-instance
[PE2] display bgp peer ipv4 vpn-instance
4. Set up an MP-IBGP peer relationship between PE 1 and PE 2:
# Configure PE 1.
[PE1] bgp 100
[PE1-bgp-default] peer 3::3 as-number 100
[PE1-bgp-default] peer 3::3 connect-interface loopback 0
[PE1-bgp-default] address-family vpnv4
[PE1-bgp-default-vpnv4] peer 3::3 enable
[PE1-bgp-default-vpnv4] quit
[PE1-bgp-default] quit
# Configure PE 2.
[PE2] bgp 100
[PE2-bgp-default] peer 1::1 as-number 100
[PE2-bgp-default] peer 1::1 connect-interface loopback 0
[PE2-bgp-default] address-family vpnv4
[PE2-bgp-default-vpnv4] peer 1::1 enable
[PE2-bgp-default-vpnv4] quit
[PE2-bgp-default] quit
# Verify that the PEs have established a BGP peer relationship and the peers are in established state.
[PE1] display bgp peer vpnv4
[PE2] display bgp peer vpnv4
5. Specify a source address for the outer IPv6 header of SRv6-encapsulated IP L3VPN packets on PE 1 and PE 2:
# Configure PE 1.
[PE1] segment-routing ipv6
[PE1-segment-routing-ipv6] encapsulation source-address 1::1
# Configure PE 2.
[PE2] segment-routing ipv6
[PE2-segment-routing-ipv6] encapsulation source-address 3::3
6. Configure the destination address (End.DT4 SID) of the outer IPv6 header for SRv6-encapsulated IP L3VPN packets:
# Configure PE 1.
[PE1-segment-routing-ipv6] locator aaa ipv6-prefix 1:2::1:0 96 static 8
[PE1-segment-routing-ipv6-locator-aaa] quit
[PE1-segment-routing-ipv6] quit
[PE1] isis 1
[PE1-isis-1] address-family ipv6 unicast
[PE1-isis-1-ipv6] segment-routing ipv6 locator aaa
[PE1-isis-1-ipv6] quit
[PE1-isis-1] quit
# Configure PE 2.
[PE2-segment-routing-ipv6] locator bbb ipv6-prefix 6:5::1:0 96 static 8
[PE2-segment-routing-ipv6-locator-bbb] quit
[PE2-segment-routing-ipv6] quit
[PE2] isis 1
[PE2-isis-1] address-family ipv6 unicast
[PE2-isis-1-ipv6] segment-routing ipv6 locator bbb
[PE2-isis-1-ipv6] quit
[PE2-isis-1] quit
# Verify that the PEs have distributed the End.DT4 SIDs to the routing table and generated SRv6 routes. This step uses PE 1 as an example.
[PE1] display ipv6 routing-table protocol srv6
Summary count : 1
SRv6 Routing table status : <Active>
Summary count : 1
Destination: 1:2::101/128 Protocol : SRv6
NextHop : ::1 Preference: 4
Interface : InLoop0 Cost : 0
SRv6 Routing table status : <Inactive>
Summary count : 0
7. Add End.DT4 SIDs to private network routes on PE 1 and PE 2:
# Configure PE 1.
[PE1] bgp 100
[PE1-bgp-default] ip vpn-instance vpn1
[PE1-bgp-default-vpn1] address-family ipv4 unicast
[PE1-bgp-default-ipv4-vpn1] segment-routing ipv6 locator aaa
[PE1-bgp-default-ipv4-vpn1] quit
[PE1-bgp-default-vpn1] quit
[PE1-bgp-default] quit
# Configure PE 2.
[PE2] bgp 100
[PE2-bgp-default] ip vpn-instance vpn1
[PE2-bgp-default-vpn1] address-family ipv4 unicast
[PE2-bgp-default-ipv4-vpn1] segment-routing ipv6 locator bbb
[PE2-bgp-default-ipv4-vpn1] quit
[PE2-bgp-default-vpn1] quit
[PE2-bgp-default] quit
8. Enable IPv6 peers on the PEs to exchange End.DT4 SIDs and enable the SID-route-recursion feature:
# Configure PE 1.
[PE1] bgp 100
[PE1-bgp-default] address-family vpnv4
[PE1-bgp-default-vpnv4] peer 3::3 prefix-sid
[PE1-bgp-default-vpnv4] quit
[PE1-bgp-default] ip vpn-instance vpn1
[PE1-bgp-default-vpn1] address-family ipv4 unicast
[PE1-bgp-default-ipv4-vpn1] segment-routing ipv6 best-effort
[PE1-bgp-default-ipv4-vpn1] quit
[PE1-bgp-default-vpn1] quit
[PE1-bgp-default] quit
# Configure PE 2.
[PE2] bgp 100
[PE2-bgp-default] address-family vpnv4
[PE2-bgp-default-vpnv4] peer 1::1 prefix-sid
[PE2-bgp-default-vpnv4] quit
[PE2-bgp-default] ip vpn-instance vpn1
[PE2-bgp-default-vpn1] address-family ipv4 unicast
[PE2-bgp-default-ipv4-vpn1] segment-routing ipv6 best-effort
[PE2-bgp-default-ipv4-vpn1] quit
[PE2-bgp-default-vpn1] quit
[PE2-bgp-default] quit
# Display BGP VPNv4 routing information on each PE and verify that the routes advertised by the PEs have the SID attribute. This step uses PE 1 as an example.
[PE1] display bgp routing-table vpnv4 10.2.1.0
BGP local router ID: 1.1.1.1
Local AS number: 100
Route distinguisher: 100:1(vpn1)
Total number of routes: 1
Paths: 1 available, 1 best
BGP routing table information of 10.2.1.0/24:
From : 3::3 (3.3.3.3)
Rely nexthop : FE80::2A96:34FF:FE9D:216
Original nexthop: 3::3
Out interface : Vlan-interface13
Route age : 00h14m23s
OutLabel : 3
Ext-Community : <RT: 111:1>
RxPathID : 0x0
TxPathID : 0x0
PrefixSID : End.DT4 SID <6:5::101>
AS-path : 65420
Origin : incomplete
Attribute value : MED 0, localpref 100, pref-val 0
State : valid, internal, best
IP precedence : N/A
QoS local ID : N/A
Traffic index : N/A
Tunnel policy : NULL
Rely tunnel IDs : N/A
Verifying the configuration
# Display IPv4 routing table information on the PEs and verify that each PE has a route destined for the remote CE and the next hop of the route is the End.DT4 SID of the route. This step uses PE 1 as an example.
[PE1] display ip routing-table vpn-instance vpn1
Destinations : 11 Routes : 11
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
10.1.1.0/24 Direct 0 0 10.1.1.1 Vlan12
10.1.1.0/32 Direct 0 0 10.1.1.1 Vlan12
10.1.1.1/32 Direct 0 0 127.0.0.1 InLoop0
10.1.1.255/32 Direct 0 0 10.1.1.1 Vlan12
10.2.1.0/24 BGP 255 0 6:5::101 Vlan13
127.0.0.0/8 Direct 0 0 127.0.0.1 InLoop0
127.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
127.0.0.1/32 Direct 0 0 127.0.0.1 InLoop0
127.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
255.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
# Verify that CE 1 and CE 2 can ping each other. (Details not shown.)