- Table of Contents
-
- 12-Security Configuration Guide
- 00-Preface
- 01-Security zone configuration
- 02-AAA configuration
- 03-802.1X configuration
- 04-MAC authentication configuration
- 05-Portal configuration
- 06-Port security configuration
- 07-User profile configuration
- 08-Password control configuration
- 09-Keychain configuration
- 10-Public key management
- 11-PKI configuration
- 12-IPsec configuration
- 13-Group domain VPN configuration
- 14-SSH configuration
- 15-SSL configuration
- 16-SSL VPN configuration
- 17-ASPF configuration
- 18-APR configuration
- 19-Session management
- 20-Connection limit configuration
- 21-Object group configuration
- 22-Object policy configuration
- 23-Attack detection and prevention configuration
- 24-IP source guard configuration
- 25-ARP attack protection configuration
- 26-ND attack defense configuration
- 27-uRPF configuration
- 28-Crypto engine configuration
- 29-FIPS configuration
- 30-mGRE configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 04-MAC authentication configuration | 265.25 KB |
Contents
Configuring MAC authentication
Restrictions: Hardware compatibility with MAC authentication
Restrictions and guidelines: MAC authentication configuration
MAC authentication tasks at a glance
Prerequisites for MAC authentication
Specifying a MAC authentication domain
Configuring the user account format
Configuring MAC authentication timers
Configuring a MAC authentication guest VLAN
Configuring a MAC authentication critical VLAN
Enabling the MAC authentication critical voice VLAN feature
Setting the maximum number of concurrent MAC authentication users on a port
Enabling MAC authentication multi-VLAN mode on a port
Configuring MAC authentication delay
Configuring the keep-online feature
Display and maintenance commands for MAC authentication
MAC authentication configuration examples
Example: Configuring local MAC authentication
Example: Configuring RADIUS-based MAC authentication
Example: Configuring ACL assignment for MAC authentication
Configuring MAC authentication
About MAC authentication
MAC authentication controls network access by authenticating source MAC addresses on a port. The feature does not require client software, and users do not have to enter a username and password for network access. The device initiates a MAC authentication process when it detects an unknown source MAC address on a MAC authentication-enabled port. If the MAC address passes authentication, the user can access authorized network resources. If the authentication fails, the device marks the MAC address as a silent MAC address, drops the packet, and starts a quiet timer. The device drops all subsequent packets from the MAC address within the quiet time. The quiet mechanism avoids repeated authentication during a short time.
User account policies
MAC authentication supports the following user account policies:
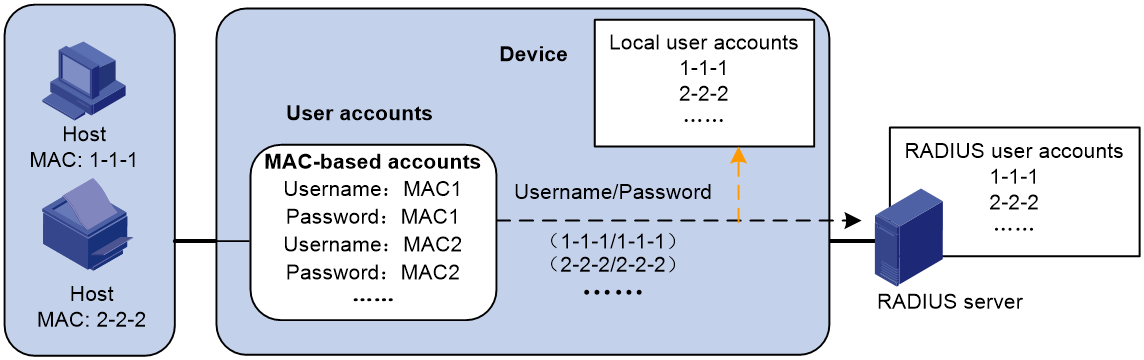
· One MAC-based user account for each user. As shown in Figure 1, the access device uses the source MAC addresses in packets as the usernames and passwords of users for MAC authentication. This policy is suitable for an insecure environment.
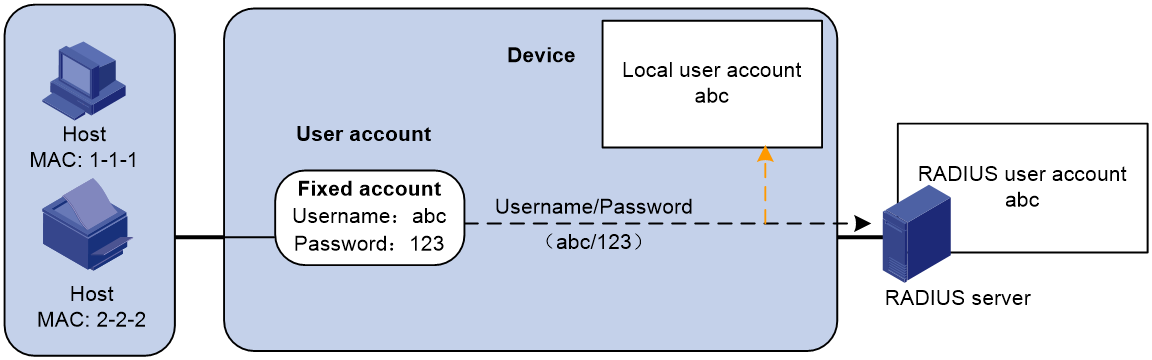
· One shared user account for all users. You specify one username and password, which are not necessarily a MAC address, for all MAC authentication users on the access device. This policy is suitable for a secure environment. See Figure 2.
Figure 1 MAC-based user account policy
Figure 2 Shared user account policy
Authentication methods
You can perform MAC authentication on the access device (local authentication) or through a RADIUS server.
For more information about configuring local authentication and RADIUS authentication, see "Configuring AAA."
RADIUS authentication
If MAC-based accounts are used, the access device sends the source MAC address of the packet as the username and password to the RADIUS server for authentication.
If a shared account is used, the access device sends the shared account username and password to the RADIUS server for authentication.
Local authentication
If MAC-based accounts are used, the access device uses the source MAC address of the packet as the username and password to search the local account database for a match.
If a shared account is used, the access device uses the shared account username and password to search the local account database for a match.
VLAN assignment
Authorization VLAN
The authorization VLAN controls the access of a MAC authentication user to authorized network resources. The device supports authorization VLANs assigned locally or by a remote server.
|
IMPORTANT: Only remote servers can assign tagged authorization VLANs. |
Remote VLAN authorization
In remote VLAN authorization, you must configure the authorization VLAN for a user on the remote server. After the user authenticates to the server, the server assigns authorization VLAN information to the device. Then, the device assigns the user access port to the authorization VLAN as a tagged or untagged member.
The device supports assignment of the following authorization VLAN information by the remote server:
· VLAN ID.
· VLAN name, which must be the same as the VLAN description on the access device.
· A string of VLAN IDs and VLAN names.
In the string, some VLANs are represented by their IDs, and some VLANs are represented by their names.
· VLAN group name.
For more information about VLAN groups, see VLAN configuration in Layer 2—LAN Switching Configuration Guide.
· VLAN ID with a suffix of t or u.
The t and u suffixes require the device to assign the access port to the VLAN as a tagged or untagged member, respectively. For example, 2u indicates assigning the port to VLAN 2 as an untagged member.
If a VLAN name or VLAN group name is assigned, the device converts the information into a VLAN ID before VLAN assignment.
|
IMPORTANT: For the VLAN represented by its VLAN name to be assigned successfully, you must make sure the VLAN has been created on the device. To assign VLAN IDs with suffixes, make sure the access port is a hybrid or trunk port. |
To ensure a successful assignment, the authorization VLANs assigned by the remote server cannot be any of the following types:
· Dynamically learned VLANs.
· Reserved VLANs.
· Super VLANs.
· Private VLANs.
If the server assigns a group of VLANs, the access device selects a VLAN as described in Table 1.
Table 1 Authorization VLAN selection from a group of VLANs
|
VLAN information |
Authorization VLAN selection |
|
VLANs by IDs VLANs by names VLAN group name |
On a hybrid port with MAC-based VLAN enabled, the device selects an authorization VLAN from the VLAN group for a user according to the following rules: · If the port does not have online users, the device selects the VLAN with the lowest ID. · If the port has online users, the device selects the VLAN that has the fewest number of online users. If two VLANs have the same number of online 802.1X users, the device selects the VLAN with the lower ID. On an access, trunk or MAC-based VLAN disabled hybrid port, the device selects an authorization VLAN from the VLAN group for a user according to the following rules: · If the port does not have online users, the device selects the VLAN with the lowest ID. · If the port has online users, the device examines whether the VLAN that has online users is in the VLAN group. If the VLAN is found in the group, the VLAN is assigned to the user as the authorization VLAN. If the VLAN is not found in the group, the VLAN authorization fails. |
|
VLAN IDs with suffixes |
1. The device selects the leftmost VLAN ID without a suffix, or the leftmost VLAN ID suffixed by u as an untagged VLAN, whichever is more leftmost. 1. The device assigns the untagged VLAN to the port as the PVID, and it assigns the remaining as tagged VLANs. If no untagged VLAN is assigned, the PVID of the port does not change. The port permits traffic from these tagged and untagged VLANs to pass through. For example, the authentication server sends the string 1u 2t 3 to the access device for a user. The device assigns VLAN 1 as an untagged VLAN and all remaining VLANs (including VLAN 3) as tagged VLANs. VLAN 1 becomes the PVID. |
Local VLAN authorization
To perform local VLAN authorization for a user, specify the VLAN ID in the authorization attribute list of the local user account for that user. For each local user, you can specify only one authorization VLAN ID. The port through which the user accesses the device is assigned to the VLAN as an untagged member.
|
IMPORTANT: Local VLAN authorization does not support assignment of tagged VLANs. |
For more information about local user configuration, see "Configuring AAA."
Authorization VLAN manipulation for a MAC authentication-enabled port
Table 2 describes the way the network access device handles authorization VLANs (except for the VLANs specified with suffixes) for MAC authenticated users.
|
Port type |
VLAN manipulation |
|
· Access port · Trunk port · Hybrid port |
· The device assigns the port to the first authenticated user's authorization VLAN and sets the VLAN as the PVID if that authorization VLAN has the untagged attribute. · If the authorization VLAN has the tagged attribute, the device assigns the port to the authorization VLAN without changing its PVID. |
|
Hybrid port with MAC-based VLAN enabled |
The device maps the MAC address of each user to its own authorization VLAN regardless of whether the port is a tagged member. The PVID of the port does not change. |
|
IMPORTANT: · For users attached to an access port, make sure the authorization VLAN assigned by the server has the untagged attribute. VLAN assignment will fail if the server issues a VLAN that has the tagged attribute. · When you assign VLANs to users attached to a trunk or hybrid port, make sure there is only one untagged VLAN. If a different untagged VLAN is assigned to a subsequent user, the user cannot pass authentication. · As a best practice to enhance network security, do not use the port hybrid vlan command to assign a hybrid port to an authorization VLAN as a tagged member. |
For a MAC authenticated user to access the network on a hybrid port when no authorization VLANs are assigned to the user, perform either of the following tasks:
· If the port receives tagged authentication packets from the user in a VLAN, use the port hybrid vlan command to configure the port as a tagged member in the VLAN.
· If the port receives untagged authentication packets from the user in a VLAN, use the port hybrid vlan command to configure the port as an untagged member in the VLAN.
Guest VLAN
The MAC authentication guest VLAN on a port accommodates users that have failed MAC authentication for any reason other than server unreachable. For example, the VLAN accommodates users for which invalid passwords are entered.
You can deploy a limited set of network resources in the MAC authentication guest VLAN. For example, a software server for downloading software and system patches.
A hybrid port is always assigned to a MAC authentication guest VLAN as an untagged member. After the assignment, do not reconfigure the port as a tagged member in the VLAN.
The device reauthenticates users in the MAC authentication guest VLAN at a specific interval. Table 3 shows the way that the network access device handles guest VLANs for MAC authentication users.
|
Authentication status |
VLAN manipulation |
|
A user in the MAC authentication guest VLAN fails MAC authentication. |
The user is still in the MAC authentication guest VLAN. |
|
A user in the MAC authentication guest VLAN passes MAC authentication. |
The device remaps the MAC address of the user to the authorization VLAN assigned by the authentication server. If no authorization VLAN is configured for the user on the authentication server, the device remaps the MAC address of the user to the PVID of the port. |
Critical VLAN
The MAC authentication critical VLAN on a port accommodates users that have failed MAC authentication because no RADIUS authentication servers are reachable. Users in a MAC authentication critical VLAN can access only network resources in the critical VLAN.
The critical VLAN feature takes effect when MAC authentication is performed only through RADIUS servers. If a MAC authentication user fails local authentication after RADIUS authentication, the user is not assigned to the critical VLAN. For more information about the authentication methods, see "Configuring AAA."
Table 4 shows the way that the network access device handles critical VLANs for MAC authentication users.
|
Authentication status |
VLAN manipulation |
|
A user fails MAC authentication because all the RADIUS servers are unreachable. |
The device maps the MAC address of the user to the MAC authentication critical VLAN. The user is still in the MAC authentication critical VLAN if the user fails MAC reauthentication because all the RADIUS servers are unreachable. If no MAC authentication critical VLAN is configured, the device maps the MAC address of the user to the PVID of the port. |
|
A user in the MAC authentication critical VLAN fails MAC authentication for any reason other than server unreachable. |
If a guest VLAN has been configured, the device maps the MAC address of the user to the guest VLAN. If no guest VLAN is configured, the device maps the MAC address of the user to the PVID of the port. |
|
A user in the MAC authentication critical VLAN passes MAC authentication. |
The device remaps the MAC address of the user to the authorization VLAN assigned by the authentication server. If no authorization VLAN is configured for the user on the authentication server, the device remaps the MAC address of the user to the PVID of the access port. |
Critical voice VLAN
The MAC authentication critical voice VLAN on a port accommodates MAC authentication voice users that have failed authentication because none of the RADIUS servers in their ISP domain are reachable.
The critical voice VLAN feature takes effect when MAC authentication is performed only through RADIUS servers. If a MAC authentication voice user fails local authentication after RADIUS authentication, the user is not assigned to the critical voice VLAN. For more information about the authentication methods, see "Configuring AAA."
Table 5 shows the way that the network access device handles critical voice VLANs for MAC authentication voice users.
|
Authentication status |
VLAN manipulation |
|
A voice user fails MAC authentication because all the RADIUS servers are unreachable. |
The device maps the MAC address of the voice user to the MAC authentication critical voice VLAN. The voice user is still in the MAC authentication critical voice VLAN if the voice user fails MAC reauthentication because all the RADIUS servers are unreachable. If no MAC authentication critical voice VLAN is configured, the device maps the MAC address of the voice user to the PVID of the port. |
|
A voice user in the MAC authentication critical voice VLAN fails MAC authentication for any reason other than server unreachable. |
If a guest VLAN has been configured, the device maps the MAC address of the voice user to the guest VLAN. If no guest VLAN is configured, the device maps the MAC address of the voice user to the PVID of the port. |
|
A voice user in the MAC authentication critical voice VLAN passes MAC authentication. |
The device remaps the MAC address of the voice user to the authorization VLAN assigned by the authentication server. If no authorization VLAN is configured for the voice user on the authentication server, the device remaps the MAC address of the voice user to the PVID of the access port. |
ACL assignment
You can specify an authorization ACL in the user account for a MAC authentication user on the authentication server to control the user's access to network resources. After the user passes MAC authentication, the authentication server (local or remote) assigns the authorization ACL to the access port of the user. The ACL will filter traffic for this user by permitting or denying matching traffic. You must configure ACL rules for the authorization ACL on the access device for the ACL assignment feature.
To change the access control criteria for the user, you can use one of the following methods:
· Modify ACL rules on the access device.
· Specify another authorization ACL on the authentication server.
The supported authorization ACLs include the following types:
· Basic ACLs, which are numbered in the range of 2000 to 2999.
· Advanced ACLs, which are numbered in the range of 3000 to 3999.
· Layer 2 ACLs, which are numbered in the range of 4000 to 4999.
For an authorization ACL to take effect, make sure the ACL exists with rules and none of the rules contains the counting, established, fragment, source-mac, or logging keyword.
For more information about ACLs, see ACL and QoS Command Reference.
User profile assignment
You can specify a user profile in the user account for a MAC authentication user on the authentication server to control the user's access to network resources. After the user passes MAC authentication, the authentication server assigns the user profile to the user to filter traffic for this user. The authentication server can be the local access device or a RADIUS server. In either case, you must configure the user profile on the access device.
To change the user's access permissions, you can use one of the following methods:
· Modify the user profile configuration on the access device.
· Specify another user profile for the user on the authentication server.
For more information about user profiles, see "Configuring user profiles."
Restrictions: Hardware compatibility with MAC authentication
This feature is supported only on the following ports:
|
Hardware |
MAC authentication and port compatibility |
|
MSR810, MSR810-W, MSR810-W-DB, MSR810-LM, MSR810-W-LM, MSR810-10-PoE, MSR810-LM-HK, MSR810-W-LM-HK, MSR810-LMS-EA |
Fixed Layer 2 Ethernet ports. |
|
MSR810-LMS, MSR810-LUS |
Fixed Layer 2 Ethernet ports. |
|
MSR2600-6-X1, MSR2600-10-X1 |
Fixed Layer 2 Ethernet ports. |
|
MSR3600-28, MSR3600-51, MSR3600-28-SI, MSR3600-51-SI |
Fixed Layer 2 Ethernet ports. |
|
MSR3600-28-X1, MSR3600-28-X1-DP, MSR3600-51-X1, MSR3600-51-X1-DP |
Fixed Layer 2 Ethernet ports. |
|
MSR3610-I-DP, MSR3610-IE-DP |
Fixed Layer 2 Ethernet ports. |
|
Routers installed with an Ethernet switching module |
Layer 2 Ethernet ports on the following modules: · HMIM-8GSW. · HMIM-8GSWF. · HMIM-24GSW. · HMIM-24GSW-PoE. · SIC-4GSW. For more information about the support of the routers for these modules, see H3C MSR Router Series Comware 7 Interface Module Guide. |
The following routers can function as ACs:
· MSR810/810-W/810-W-DB/810-LM/810-W-LM/810-10-PoE/810-LM-HK/810-W-LM-HK.
· MSR2600-6-X1/2600-10-X1.
· MSR 2630.
· MSR3600-28/3600-51.
· MSR3600-28-X1/3600-28-X1-DP/3600-51-X1/3600-51-X1-DP.
· MSR3610-I-DP/3610-IE-DP.
· MSR3610-X1/3610-X1-DP/3610-X1-DC/3610-X1-DP-DC.
· MSR 3610/3620/3620-DP/3640/3660.
The following routers can function as APs:
· MSR810-W.
· MSR810-W-DB.
· MSR810-W-LM.
· MSR810-W-LM-HK.
Restrictions and guidelines: MAC authentication configuration
Do not change the link type of a port when the MAC authentication guest VLAN or critical VLAN on the port has users.
If the MAC address that has failed authentication is a static MAC address or a MAC address that has passed any security authentication, the device does not mark the MAC address as a silent address.
MAC authentication tasks at a glance
To configure MAC authentication, perform the following tasks:
1. Enabling MAC authentication
2. Configure basic MAC authentication features
¡ Specifying a MAC authentication domain
¡ Configuring the user account format
¡ (Optional.) Configuring MAC authentication timers
3. (Optional.) Configuring MAC authentication VLAN assignment
¡ Configuring a MAC authentication guest VLAN
¡ Configuring a MAC authentication critical VLAN
¡ Enabling the MAC authentication critical voice VLAN feature
4. (Optional.) Configuring other MAC authentication features
¡ Setting the maximum number of concurrent MAC authentication users on a port
¡ Enabling MAC authentication multi-VLAN mode on a port
Perform this task to not reauthenticate online users when VLAN changes occur on a port.
¡ Configuring MAC authentication delay
¡ Configuring the keep-online feature
Prerequisites for MAC authentication
Before you configure MAC authentication, complete the following tasks:
1. Make sure the port security feature is disabled. For more information about port security, see "Configuring port security."
2. Configure an ISP domain and specify an AAA method. For more information, see "Configuring AAA."
¡ For local authentication, you must also create local user accounts (including usernames and passwords) and specify the lan-access service for local users.
¡ For RADIUS authentication, make sure the device and the RADIUS server can reach each other and create user accounts on the RADIUS server. If you are using MAC-based accounts, make sure the username and password for each account are the same as the MAC address of each MAC authentication user.
Enabling MAC authentication
Restrictions and guidelines
For MAC authentication to take effect on a port, you must enable this feature globally and on the port.
You cannot enable MAC authentication on a port that is in a link aggregation group.
Procedure
1. Enter system view.
system-view
2. Enable MAC authentication globally.
mac-authentication
By default, MAC authentication is disabled globally.
3. Enter Layer 2 Ethernet interface view.
interface interface-type interface-number
4. Enable MAC authentication on the port.
mac-authentication
By default, MAC authentication is disabled on a port.
Specifying a MAC authentication domain
About authentication domains for MAC authentication
By default, MAC authentication users are in the system default authentication domain. To implement different access policies for users, you can use one of the following methods to specify authentication domains for MAC authentication users:
· Specify a global authentication domain in system view. This domain setting applies to all ports enabled with MAC authentication.
· Specify an authentication domain for an individual port in Layer 2 Ethernet interface view.
MAC authentication chooses an authentication domain for users on a port in this order: the port-specific domain, the global domain, and the default domain. For more information about authentication domains, see "Configuring AAA."
Procedure
1. Enter system view.
system-view
2. Specify an authentication domain for MAC authentication users.
¡ In system view:
mac-authentication domain domain-name
¡ In Layer 2 Ethernet interface view:
interface interface-type interface-number
mac-authentication domain domain-name
By default, the system default authentication domain is used for MAC authentication users.
Configuring the user account format
1. Enter system view.
system-view
2. Configure the MAC authentication user account format.
¡ Use one MAC-based user account for each user.
mac-authentication user-name-format mac-address [ { with-hyphen [ six-section | three-section ] | without-hyphen } [ lowercase | uppercase ] ]
¡ Use one shared user account for all users.
mac-authentication user-name-format fixed [ account name ] [ password { cipher | simple } string ]
By default, the device uses the MAC address of a user as the username and password for MAC authentication. The MAC address is in the hexadecimal notation without hyphens, and letters are in lower case.
Configuring MAC authentication timers
About MAC authentication timers
MAC authentication uses the following timers:
· Offline detect timer—Sets the interval that the device waits for traffic from a user before the device determines that the user is idle. If the device has not received traffic from a user before the timer expires, the device logs off that user and requests the accounting server to stop accounting for the user.
· Quiet timer—Sets the interval that the device must wait before the device can perform MAC authentication for a user that has failed MAC authentication. All packets from the MAC address are dropped during the quiet time. This quiet mechanism prevents repeated authentication from affecting system performance.
· Server timeout timer—Sets the interval that the device waits for a response from a RADIUS server before the device determines that the RADIUS server is unavailable. If the timer expires during MAC authentication, the user cannot access the network.
Procedure
1. Enter system view.
system-view
2. Configure MAC authentication timers.
mac-authentication timer { offline-detect offline-detect-value | quiet quiet-value | server-timeout server-timeout-value }
By default, the offline detect timer is 300 seconds, the quiet timer is 60 seconds, and the server timeout timer is 100 seconds.
Configuring a MAC authentication guest VLAN
Restrictions and guidelines
When you configure the MAC authentication guest VLAN on a port, follow the guidelines in Table 6.
Table 6 Relationships of the MAC authentication guest VLAN with other security features
|
Feature |
Relationship description |
Reference |
|
Quiet feature of MAC authentication |
The MAC authentication guest VLAN feature has higher priority. When a user fails MAC authentication, the user can access the resources in the guest VLAN. The user's MAC address is not marked as a silent MAC address. |
|
|
Super VLAN |
You cannot specify a VLAN as both a super VLAN and a MAC authentication guest VLAN. |
See Layer 2—LAN Switching Configuration Guide. |
|
Port intrusion protection |
The guest VLAN feature has higher priority than the block MAC action but lower priority than the shutdown port action of the port intrusion protection feature. |
See "Configuring port security." |
Prerequisites
Before you configure the MAC authentication guest VLAN on a port, complete the following tasks:
· Create the VLAN to be specified as the MAC authentication guest VLAN.
· Configure the port as a hybrid port, and configure the VLAN as an untagged member on the port.
· Enable MAC-based VLAN on the port.
For information about VLAN configuration, see Layer 2—LAN Switching Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enter Layer 2 Ethernet interface view.
interface interface-type interface-number
3. Specify the MAC authentication guest VLAN on the port.
mac-authentication guest-vlan guest-vlan-id
By default, no MAC authentication guest VLAN is specified on a port.
You can configure only one MAC authentication guest VLAN on a port. The MAC authentication guest VLANs on different ports can be different.
4. Set the authentication interval for users in the MAC authentication guest VLAN.
mac-authentication guest-vlan auth-period period-value
The default setting is 30 seconds.
Configuring a MAC authentication critical VLAN
Restrictions and guidelines
When you configure the MAC authentication critical VLAN on a port, follow the guidelines in Table 7.
Table 7 Relationships of the MAC authentication critical VLAN with other security features
|
Feature |
Relationship description |
Reference |
|
Quiet feature of MAC authentication |
The MAC authentication critical VLAN feature has higher priority. When a user fails MAC authentication because no RADIUS authentication server is reachable, the user can access the resources in the critical VLAN. The user's MAC address is not marked as a silent MAC address. |
|
|
Super VLAN |
You cannot specify a VLAN as both a super VLAN and a MAC authentication critical VLAN. |
See Layer 2—LAN Switching Configuration Guide. |
|
Port intrusion protection |
The critical VLAN feature has higher priority than the block MAC action but lower priority than the shutdown port action of the port intrusion protection feature. |
See "Configuring port security." |
Prerequisites
Before you configure the MAC authentication critical VLAN on a port, complete the following tasks:
· Create the VLAN to be specified as the MAC authentication critical VLAN.
· Configure the port as a hybrid port, and configure the VLAN as an untagged member on the port.
For information about VLAN configuration, see Layer 2—LAN Switching Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enter Layer 2 Ethernet interface view.
interface interface-type interface-number
3. Specify the MAC authentication critical VLAN on the port.
mac-authentication critical vlan critical-vlan-id
By default, no MAC authentication critical VLAN is specified on a port.
You can configure only one MAC authentication critical VLAN on a port. The MAC authentication critical VLANs on different ports can be different.
Enabling the MAC authentication critical voice VLAN feature
Prerequisites
Before you enable the MAC authentication critical voice VLAN feature on a port, complete the following tasks:
· Enable LLDP both globally and on the port.
The device uses LLDP to identify voice users. For information about LLDP, see Layer 2—LAN Switching Configuration Guide.
· Enable voice VLAN on the port.
For information about voice VLANs, see Layer 2—LAN Switching Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enter Layer 2 Ethernet interface view.
interface interface-type interface-number
3. Enable the MAC authentication critical voice VLAN feature on a port.
mac-authentication critical-voice-vlan
By default, the MAC authentication critical voice VLAN feature is disabled on a port.
Setting the maximum number of concurrent MAC authentication users on a port
About limiting the number of concurrent MAC authentication users on a port
Perform this task to prevent the system resources from being overused.
Procedure
1. Enter system view.
system-view
2. Enter Layer 2 Ethernet interface view.
interface interface-type interface-number
3. Set the maximum number of concurrent MAC authentication users on the port.
mac-authentication max-user max-number
The default setting is 4294967295.
Enabling MAC authentication multi-VLAN mode on a port
About the MAC authentication multi-VLAN mode
The MAC authentication multi-VLAN mode prevents an authenticated online user from service interruption caused by VLAN changes on a port. When the port receives a packet sourced from the user in a VLAN not matching the existing MAC-VLAN mapping, the device neither logs off the user nor reauthenticates the user. The device creates a new MAC-VLAN mapping for the user, and traffic transmission is not interrupted. The original MAC-VLAN mapping for the user remains on the device until it dynamically ages out. As a best practice, configure this feature on hybrid or trunk ports.
This feature improves transmission of data that is vulnerable to delay and interference. It is typically applicable to IP phone users.
Procedure
1. Enter system view.
system-view
2. Enter Layer 2 Ethernet interface view.
interface interface-type interface-number
3. Enable MAC authentication multi-VLAN mode.
mac-authentication host-mode multi-vlan
By default, this feature is disabled on a port. When the port receives a packet sourced from an authenticated user in a VLAN not matching the existing MAC-VLAN mapping, the device logs off and reauthenticates the user.
Configuring MAC authentication delay
About MAC authentication delay
When both 802.1X authentication and MAC authentication are enabled on a port, you can delay MAC authentication so that 802.1X authentication is preferentially triggered.
If no 802.1X authentication is triggered or 802.1X authentication fails within the delay period, the port continues to process MAC authentication.
Restrictions and guidelines
Do not set the port security mode to mac-else-userlogin-secure or mac-else-userlogin-secure-ext when you use MAC authentication delay. The delay does not take effect on a port in either of the two modes. For more information about port security modes, see "Configuring port security."
Procedure
1. Enter system view.
system-view
2. Enter Layer 2 Ethernet interface view.
interface interface-type interface-number
3. Enable MAC authentication delay and set the delay timer.
mac-authentication timer auth-delay time
By default, MAC authentication delay is disabled.
Configuring the keep-online feature
About the keep-online feature
Periodic MAC reauthentication tracks the connection status of online users, and updates the authorization attributes assigned by the RADIUS server. The attributes include VLAN, user profile-based QoS, and ACL.
The device reauthenticates an online MAC authentication user periodically only after it receives the termination action Radius-request from the authentication server for this user. The Session-Timeout attribute (session timeout period) assigned by the server is the reauthentication interval. To display the server-assigned Session-Timeout and Termination-Action attributes, use the display mac-authentication connection command. Support for the server configuration and assignment of Session-Timeout and Termination-Action attributes depends on the server model.
The keep-online feature enables the device to keep the MAC authentication users online when no server is reachable for MAC reauthentication.
Restrictions and guidelines
In a fast-recovery network, you can use the keep-online feature to prevent MAC authentication users from coming online and going offline frequently.
Any modification to the MAC authentication domain or user account format setting does not affect the reauthentication of online MAC authentication users. The modified setting takes effect only on MAC authentication users that come online after the modification.
Procedure
1. Enter system view.
system-view
2. Enter Layer 2 Ethernet interface view.
interface interface-type interface-number
3. Enable the keep-online feature for authenticated MAC authentication users on the port.
mac-authentication re-authenticate server-unreachable keep-online
By default, the keep-online feature is disabled. The device logs off online MAC authentication users if no server is reachable for MAC reauthentication.
Display and maintenance commands for MAC authentication
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display MAC authentication information. |
display mac-authentication [ ap ap-name [ radio radio-id ] | interface interface-type interface-number ] |
|
Display MAC authentication connections. |
In standalone mode: display mac-authentication connection [ ap ap-name [ radio radio-id ] | interface interface-type interface-number | user-mac mac-address | user-name user-name ] In IRF mode: display mac-authentication connection [ ap ap-name [ radio radio-id ] | interface interface-type interface-number | slot slot-number | user-mac mac-address | user-name user-name ] |
|
Clear MAC authentication statistics. |
reset mac-authentication statistics [ ap ap-name [ radio radio-id ] | interface interface-type interface-number ] |
|
Remove users from the MAC authentication critical VLAN on a port. |
reset mac-authentication critical-vlan interface interface-type interface-number [ mac-address mac-address ] |
|
Remove users from the MAC authentication guest VLAN on a port. |
reset mac-authentication guest-vlan interface interface-type interface-number [ mac-address mac-address ] |
MAC authentication configuration examples
Example: Configuring local MAC authentication
Network configuration
As shown in Figure 3, the device performs local MAC authentication on GigabitEthernet 1/0/1 to control Internet access of users.
Configure the device to meet the following requirements:
· Detect whether a user has gone offline every 180 seconds.
· Deny a user for 180 seconds if the user fails MAC authentication.
· Authenticate all users in ISP domain bbb.
· Use the MAC address of each user as the username and password for authentication. A MAC address is in the hexadecimal notation with hyphens, and letters are in lower case.
Procedure
# Add a network access local user. In this example, configure both the username and password as Host A's MAC address 00-e0-fc-12-34-56.
<Device> system-view
[Device] local-user 00-e0-fc-12-34-56 class network
[Device-luser-network-00-e0-fc-12-34-56] password simple 00-e0-fc-12-34-56
# Specify the LAN access service for the user.
[Device-luser-network-00-e0-fc-12-34-56] service-type lan-access
[Device-luser-network-00-e0-fc-12-34-56] quit
# Configure ISP domain bbb to perform local authentication for LAN users.
[Device] domain bbb
[Device-isp-bbb] authentication lan-access local
[Device-isp-bbb] quit
# Enable MAC authentication on GigabitEthernet 1/0/1.
[Device] interface gigabitethernet 1/0/1
[Device-GigabitEthernet1/0/1] mac-authentication
[Device-GigabitEthernet1/0/1] quit
# Specify ISP domain bbb as the MAC authentication domain.
[Device] mac-authentication domain bbb
# Configure MAC authentication timers.
[Device] mac-authentication timer offline-detect 180
[Device] mac-authentication timer quiet 180
# Configure MAC authentication to use MAC-based accounts. Each MAC address is in the hexadecimal notation with hyphens, and letters are in lower case.
[Device] mac-authentication user-name-format mac-address with-hyphen lowercase
# Enable MAC authentication globally.
[Device] mac-authentication
Verifying the configuration
# Display MAC authentication settings and statistics to verify your configuration.
<Device> display mac-authentication
Global MAC authentication parameters:
MAC authentication : Enabled
User name format : MAC address in lowercase(xx-xx-xx-xx-xx-xx)
Username : mac
Password : Not configured
Offline detect period : 180 s
Quiet period : 180 s
Server timeout : 100 s
Authentication domain : bbb
Online MAC-auth wired users : 1
Silent MAC users:
MAC address VLAN ID From port Port index
00e0-fc11-1111 8 Gigabitethernet1/0/1 1
Gigabitethernet1/0/1 is link-up
MAC authentication : Enabled
Carry User-IP : Disabled
Authentication domain : Not configured
Auth-delay timer : Disabled
Re-auth server-unreachable : Logoff
Guest VLAN : Not configured
Guest VLAN auth-period : 30 s
Critical VLAN : Not configured
Critical voice VLAN : Disabled
Host mode : Single VLAN
Max online users : 4294967295
Authentication attempts : successful 1, failed 0
Current online users : 1
MAC address Auth state
00e0-fc12-3456 Authenticated
The output shows that Host A has passed MAC authentication and has come online. Host B failed MAC authentication and its MAC address is marked as a silent MAC address.
Example: Configuring RADIUS-based MAC authentication
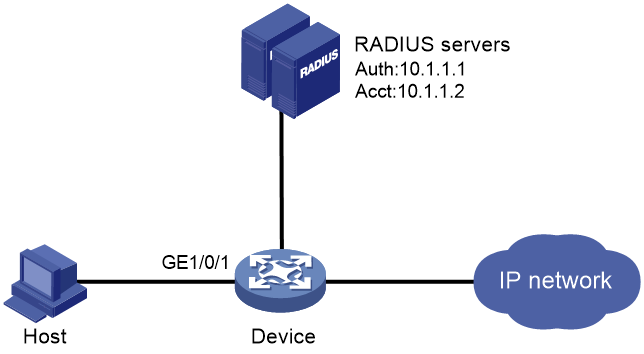
Network configuration
As shown in Figure 4, the device uses RADIUS servers to perform authentication, authorization, and accounting for users.
To control user access to the Internet by MAC authentication, perform the following tasks:
· Enable MAC authentication globally and on GigabitEthernet 1/0/1.
· Configure the device to detect whether a user has gone offline every 180 seconds.
· Configure the device to deny a user for 180 seconds if the user fails MAC authentication.
· Configure all users to belong to ISP domain bbb.
· Use a shared user account for all users, with username aaa and password 123456.
Procedure
Make sure the RADIUS server and the access device can reach each other.
1. Configure the RADIUS servers to provide authentication, authorization, and accounting services. Create a shared account with username aaa and password 123456 for MAC authentication users. (Details not shown.)
2. Configure RADIUS-based MAC authentication on the device:
# Configure a RADIUS scheme.
<Device> system-view
[Device] radius scheme 2000
[Device-radius-2000] primary authentication 10.1.1.1 1812
[Device-radius-2000] primary accounting 10.1.1.2 1813
[Device-radius-2000] key authentication simple abc
[Device-radius-2000] key accounting simple abc
[Device-radius-2000] user-name-format without-domain
[Device-radius-2000] quit
# Apply the RADIUS scheme to ISP domain bbb for authentication, authorization, and accounting.
[Device] domain bbb
[Device-isp-bbb] authentication default radius-scheme 2000
[Device-isp-bbb] authorization default radius-scheme 2000
[Device-isp-bbb] accounting default radius-scheme 2000
[Device-isp-bbb] quit
# Enable MAC authentication on GigabitEthernet 1/0/1.
[Device] interface gigabitethernet 1/0/1
[Device-GigabitEthernet1/0/1] mac-authentication
[Device-GigabitEthernet1/0/1] quit
# Specify the MAC authentication domain as ISP domain bbb.
[Device] mac-authentication domain bbb
# Set MAC authentication timers.
[Device] mac-authentication timer offline-detect 180
[Device] mac-authentication timer quiet 180
# Specify username aaa and password 123456 in plain text for the account shared by MAC authentication users.
[Device] mac-authentication user-name-format fixed account aaa password simple 123456
# Enable MAC authentication globally.
[Device] mac-authentication
Verifying the configuration
# Verify the MAC authentication configuration.
<Device> display mac-authentication
Global MAC authentication parameters:
MAC authentication : Enabled
Username format : Fixed account
Username : aaa
Password : ******
Offline detect period : 180 s
Quiet period : 180 s
Server timeout : 100 s
Authentication domain : bbb
Online MAC-auth wired users : 1
Silent MAC users:
MAC address VLAN ID From port Port index
GigabitEthernet1/0/1 is link-up
MAC authentication : Enabled
Carry User-IP : Disabled
Authentication domain : Not configured
Auth-delay timer : Disabled
Re-auth server-unreachable : Logoff
Guest VLAN : Not configured
Guest VLAN auth-period : 30 s
Critical VLAN : Not configured
Critical voice VLAN : Disabled
Host mode : Single VLAN
Max online users : 4294967295
Authentication attempts : successful 1, failed 0
Current online users : 1
MAC address Auth state
00e0-fc12-3456 Authenticated
Example: Configuring ACL assignment for MAC authentication
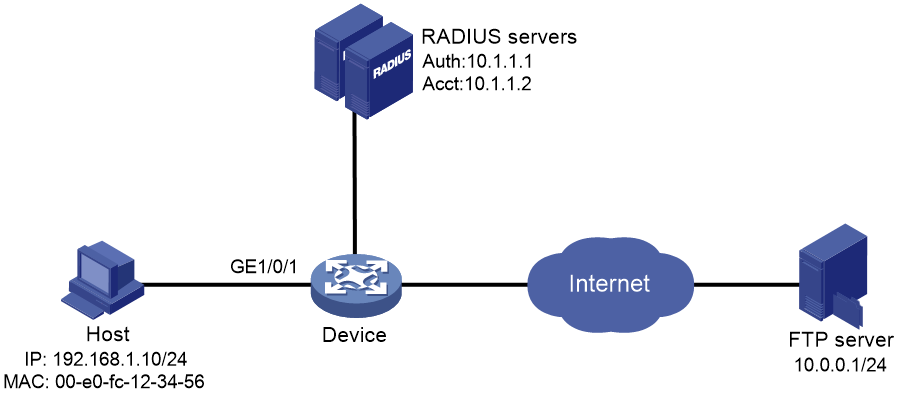
Network configuration
As shown in Figure 5, configure the device to meet the following requirements:
· Use RADIUS servers to perform authentication, authorization, and accounting for users.
· Perform MAC authentication on GigabitEthernet 1/0/1 to control Internet access.
· Use MAC-based user accounts for MAC authentication users. Each MAC address is in the hexadecimal notation with hyphens, and letters are in lower case.
· Use an ACL to deny authenticated users to access the FTP server at 10.0.0.1.
Procedure
Make sure the RADIUS servers and the access device can reach each other.
1. Configure the RADIUS servers:
# Configure the RADIUS servers to provide authentication, authorization, and accounting services. (Details not shown.)
# Add a user account with 00-e0-fc-12-34-56 as both the username and password on each RADIUS server. (Details not shown.)
# Specify ACL 3000 as the authorization ACL for the user account. (Details not shown.)
2. Configure ACL 3000 to deny packets destined for 10.0.0.1 on the device.
<Device> system-view
[Device] acl advanced 3000
[Device-acl-ipv4-adv-3000] rule 0 deny ip destination 10.0.0.1 0
[Device-acl-ipv4-adv-3000] quit
3. Configure RADIUS-based MAC authentication on the device:
# Configure a RADIUS scheme.
[Device] radius scheme 2000
[Device-radius-2000] primary authentication 10.1.1.1 1812
[Device-radius-2000] primary accounting 10.1.1.2 1813
[Device-radius-2000] key authentication simple abc
[Device-radius-2000] key accounting simple abc
[Device-radius-2000] user-name-format without-domain
[Device-radius-2000] quit
# Apply the RADIUS scheme to an ISP domain for authentication, authorization, and accounting.
[Device] domain bbb
[Device-isp-bbb] authentication default radius-scheme 2000
[Device-isp-bbb] authorization default radius-scheme 2000
[Device-isp-bbb] accounting default radius-scheme 2000
[Device-isp-bbb] quit
# Specify the ISP domain for MAC authentication.
[Device] mac-authentication domain bbb
# Configure the device to use MAC-based user accounts. Each MAC address is in the hexadecimal notation with hyphens, and letters are in lower case.
[Device] mac-authentication user-name-format mac-address with-hyphen lowercase
# Enable MAC authentication on GigabitEthernet 1/0/1.
[Device] interface gigabitethernet 1/0/1
[Device-GigabitEthernet1/0/1] mac-authentication
[Device-GigabitEthernet1/0/1] quit
# Enable MAC authentication globally.
[Device] mac-authentication
Verifying the configuration
# Verify the MAC authentication configuration.
<Device> display mac-authentication
Global MAC authentication parameters:
MAC authentication : Enable
Username format : MAC address in lowercase(xx-xx-xx-xx-xx-xx)
Username : mac
Password : Not configured
Offline detect period : 300 s
Quiet period : 60 s
Server timeout : 100 s
Authentication domain : bbb
Online MAC-auth wired users : 1
Silent MAC users:
MAC address VLAN ID From port Port index
GigabitEthernet1/0/1 is link-up
MAC authentication : Enabled
Carry User-IP : Disabled
Authentication domain : Not configured
Auth-delay timer : Disabled
Re-auth server-unreachable : Logoff
Guest VLAN : Not configured
Guest VLAN auth-period : 30 s
Critical VLAN : Not configured
Critical voice VLAN : Disabled
Host mode : Single VLAN
Max online users : 4294967295
Authentication attempts : successful 1, failed 0
Current online users : 1
MAC address Auth state
00e0-fc12-3456 Authenticated
# Verify that you cannot ping the FTP server from the host.
C:\>ping 10.0.0.1
Pinging 10.0.0.1 with 32 bytes of data:
Request timed out.
Request timed out.
Request timed out.
Request timed out.
Ping statistics for 10.0.0.1:
Packets: Sent = 4, Received = 0, Lost = 4 (100% loss),
The output shows that ACL 3000 has been assigned to GigabitEthernet 1/0/1 to deny access to the FTP server.