- Table of Contents
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 01-PPP configuration | 280.69 KB |
Contents
PPP link establishment process
Enabling PPP encapsulation on an interface
Configuring PPP authentication
Configuring PAP authentication
Configuring CHAP authentication (authenticator name is configured)
Configuring CHAP authentication (authenticator name is not configured)
Configuring MS-CHAP or MS-CHAP-V2 authentication
Configuring the polling feature
Configuring the PPP negotiation timeout time
Configuring IPv4 address negotiation on the client
Configuring IPv4 address negotiation on the server
Configuring IPv6 address negotiation on the server
Enabling PPP link quality monitoring
Configuring magic number check for PPP
Setting the online PPP session count alarm thresholds on the device
Display and maintenance commands for PPP
Example: Configuring one-way PAP authentication
Example: Configuring two-way PAP authentication
Example: Configuring one-way CHAP authentication
Example: Specifying an IP address for the client on the server interface
Example: Specifying an IP address pool on the server interface
Example: Using the IP address pool associated with an ISP domain
Configuring PPP
About PPP
Point-to-Point Protocol (PPP) is a point-to-point link layer protocol. It provides user authentication, supports synchronous/asynchronous communication, and allows for easy extension.
PPP protocols
PPP includes the following protocols:
· Link control protocol (LCP)—Establishes, tears down, and monitors data links.
· Network control protocol (NCP)—Negotiates the packet format and type for data links.
· Authentication protocols—Authenticate users. Protocols include the following:
¡ Password Authentication Protocol (PAP).
¡ Challenge Handshake Authentication Protocol (CHAP).
¡ Microsoft CHAP (MS-CHAP).
¡ Microsoft CHAP Version 2 (MS-CHAP-V2).
PPP link establishment process
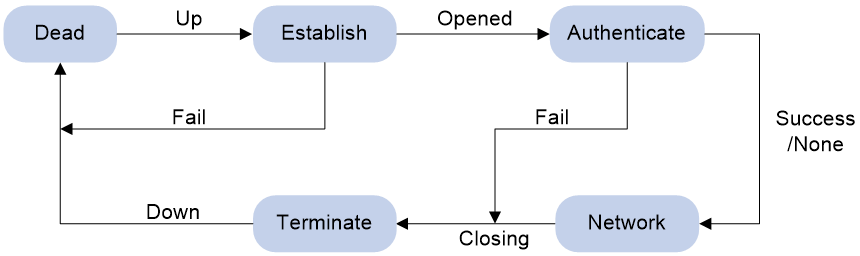
Figure 1 shows the PPP link establishment process.
Figure 1 PPP link establishment process
1. Initially, PPP is in Link Dead phase. After the physical layer goes up, PPP enters the Link Establishment phase (Establish).
2. In the Link Establishment phase, the LCP negotiation is performed. The LCP configuration options include Authentication-Protocol, Maximum-Receive-Unit (MRU), and Magic-Number.
¡ If the negotiation fails, LCP reports a Fail event, and PPP returns to the Dead phase.
¡ If the negotiation succeeds, LCP enters the Opened state and reports an Up event, indicating that the underlying layer link has been established. At this time, the PPP link is not established for the network layer, and network layer packets cannot be transmitted over the link.
3. If authentication is configured, the PPP link enters the Authentication phase, where PAP, CHAP, MS-CHAP, or MS-CHAP-V2 authentication is performed.
¡ If the client fails to pass the authentication, LCP reports a Fail event and enters the Link Termination phase. In this phase, the link is torn down and LCP goes down.
¡ If the client passes the authentication, LCP reports a Success event.
4. If a network layer protocol is configured, the PPP link enters the Network-Layer Protocol phase for NCP negotiation, such as IPCP negotiation and IPv6CP negotiation.
¡ If the NCP negotiation succeeds, the link goes up and becomes ready to carry negotiated network-layer protocol packets.
¡ If the NCP negotiation fails, NCP reports a Down event and enters the Link Termination phase.
If the interface is configured with an IP address, the IPCP negotiation is performed. IPCP configuration options include IP addresses and DNS server IP addresses. After the IPCP negotiation succeeds, the link can carry IP packets.
5. After the NCP negotiation is performed, the PPP link remains active until either of the following events occurs:
¡ Explicit LCP or NCP frames close the link.
¡ Some external events take place (for example, the intervention of a user).
PPP authentication
PPP supports the following authentication methods:
PAP
PAP is a two-way handshake authentication protocol using the username and password. PAP sends username/password pairs in plain text over the network. If authentication packets are intercepted in transit, network security might be threatened. For this reason, it is suitable only for low-security environments.
CHAP
CHAP is a three-way handshake authentication protocol. CHAP transmits usernames but not passwords over the network. It transmits the result calculated from the password and random packet ID by using the MD5 algorithm. It is more secure than PAP. The authenticator may or may not be configured with a username. As a best practice, configure a username for the authenticator, which makes it easier for the peer to verify the identity of the authenticator.
MS-CHAP
MS-CHAP is a three-way handshake authentication protocol. MS-CHAP differs from CHAP in that MS-CHAP provides authentication retry. If the peer fails authentication, it is allowed to retransmit authentication information to the authenticator for reauthentication. The authenticator allows a peer to retransmit a maximum of three times.
MS-CHAP-V2
MS-CHAP-V2 is a three-way handshake authentication protocol.
MS-CHAP-V2 differs from CHAP as follows:
· MS-CHAP-V2 provides two-way authentication by piggybacking a peer challenge on the Response packet and an authenticator response on the Acknowledge packet.
· MS-CHAP-V2 supports authentication retry. If the peer fails authentication, it is allowed to retransmit authentication information to the authenticator for reauthentication. The authenticator allows a peer to retransmit a maximum of three times.
· MS-CHAP-V2 supports password change. If the peer fails authentication because of an expired password, it will send the new password entered by the user to the authenticator for reauthentication.
PPP for IPv4
On IPv4 networks, PPP negotiates the IP address and DNS server address during IPCP negotiation.
IP address negotiation
IP address negotiation enables one end to assign an IP address to the other.
An interface can act as a client or a server during IP address negotiation:
· Client—Obtains an IP address from the server. Use the client mode when the device accesses the Internet through an ISP.
· Server—Assigns an IP address to the client. Before you configure the IP address of the server, you must perform one of the following tasks:
¡ Configure a local address pool and associate the pool with the ISP domain.
¡ Specify an IP address or an address pool for the client on the interface.
When IP address negotiation is enabled on a client, the server selects an IP address for the client in the following sequence:
1. If the AAA server configures an IP address or address pool for the client, the server selects that IP address or an IP address from the pool. The IP address or address pool is configured on the AAA server instead of the PPP server. For information about AAA, see Security Configuration Guide.
2. If an address pool is associated with the ISP domain used during client authentication, the server selects an IP address from the pool.
3. If an IP address or address pool is specified for the client on the interface of the server, the server selects that IP address or an IP address from that pool.
DNS server address negotiation
IPCP negotiation can determine the DNS server IP address.
When the device is connected to a host, configure the device as the server to assign the DNS server IP address to the host.
When the device is connected to an ISP access server, configure the device as the client. Then, the device can obtain the DNS server IP address from the ISP access server.
PPP for IPv6
On IPv6 networks, PPP negotiates only the IPv6 interface identifier instead of the IPv6 address and IPv6 DNS server address during IPv6CP negotiation. All authentication users have to obtain IPv6 global unicast addresses and IPv6 DNS server addresses by using ND or DHCPv6 protocols.
IPv6 address assignment
A host can get an IPv6 global unicast address through the following methods:
· NDRA—The host obtains an IPv6 prefix in an RA message. The host then generates an IPv6 global unicast address by combining the IPv6 prefix and the negotiated IPv6 interface identifier. The IPv6 prefix in the RA message is determined in the following sequence:
a. IPv6 prefix authorized by an AAA server through the Framed-IPv6-Prefix attribute.
b. IPv6 prefix authorized in an ISP domain.
c. Prefix in the ND prefix pool authorized in an ISP domain.
d. Prefix in the 128-bit IPv6 global unicast address authorized by an AAA server through the Framed-IPv6-Address attribute. If an interface identifier has been authorized by an AAA server through the Framed-Interface-Id attribute, skip this step and go to step f.
e. Prefix in the 128-bit IPv6 global unicast address authorized by using the authorization-attribute ipv6 command in local user view. If an interface identifier has been authorized by an AAA server through the Framed-Interface-Id attribute, skip this step and go to step f.
f. RA prefix configured on the interface.
g. Prefix in the IPv6 global unicast address configured on the interface.
The negotiated IPv6 interface identifiers are determined in the following sequence:
a. Interface identifier authorized by an AAA server through the Framed-Interface-Id attribute.
b. Interface identifier in the 128-bit IPv6 global unicast address authorized by an AAA server through the Framed-IPv6-Address attribute. If an IPv6 prefix has been authorized by an AAA server through the Framed-IPv6-Prefix attribute, skip this step and go to step d.
c. Interface identifier in the 128-bit IPv6 global unicast address authorized by using the authorization-attribute ipv6 command in local user view. If an IPv6 prefix has been authorized by an AAA server through the Framed-IPv6-Prefix attribute, skip this step and go to step d.
d. Interface identifier automatically generated for the PPP user when the ipv6cp assign-interface-id command is executed in an ISP domain.
e. Non-zero interface identifier that is carried by the user and does not conflict with any other interface identifier.
f. Interface identifier automatically generated for the PPP user when the interface identifier carried by the user is invalid.
The ND prefix pool authorized by AAA and the IA_NA method are mutually exclusive. For information about the ND protocol, see Layer 3—IP Services Configuration Guide.
· DHCPv6 (IA_NA)—The host requests an IPv6 global unicast address through DHCPv6. The server assigns an IPv6 address to the host from the address pool authorized by AAA. If no AAA-authorized address pool exists, DHCPv6 uses the address pool that matches the server's IPv6 address to assign an IPv6 address to the host. For information about DHCPv6, see Layer 3—IP Services Configuration Guide.
After an IPv6 address pool is authorized to users, IA_NA also supports authorizing the specified 128-bit IPv6 global unicast addresses to PPP users through the following methods:
¡ Authorizing 128-bit IPv6 global unicast addresses by an AAA server through the Framed-IPv6-Address attribute.
¡ Authorizing 128-bit IPv6 global unicast addresses by using the authorization-attribute ipv6 command in local user view.
Make sure the 128-bit IPv6 global unicast addresses authorized by using the two methods above are within the authorized IPv6 address pool. Otherwise, the 128-bit IPv6 global unicast addresses authorized by using the two methods above are not used, and IPv6 addresses in the IPv6 address pool are randomly allocated to users.
· DHCPv6 (IA_PD)—A client-side device requests prefixes through DHCPv6 and assigns them to downstream hosts. The hosts then use the prefixes to generate global IPv6 addresses. This method uses the same principle of selecting address pools as the DHCPv6 (IA_NA) method.
The device can assign a host an IPv6 address in either of the following ways:
· When the host connects to the device directly or through a bridge device, the device can use the NDRA method or the IA_NA method.
· When the host accesses the device through a router, the device can use the IA_PD method to assign an IPv6 prefix to the router. The router assigns the prefix to the host to generate an IPv6 global unicast address.
IPv6 DNS server address assignment
On IPv6 networks, two methods are available for the IPv6 DNS server address assignment:
· AAA authorizes the IPv6 DNS server address and assigns this address to the host through RA messages.
· The DHCPv6 client requests an IPv6 DNS server address from the DHCPv6 server.
Protocols and standards
RFC 1661: The Point-to-Point Protocol (PPP)
PPP tasks at a glance
To configure PPP, perform the following tasks:
1. Enabling PPP encapsulation on an interface
2. Configuring PPP authentication
Choose one of the following tasks:
¡ Configuring PAP authentication
¡ Configuring CHAP authentication (authenticator name is configured)
¡ Configuring CHAP authentication (authenticator name is not configured)
¡ Configuring MS-CHAP or MS-CHAP-V2 authentication
Configure PPP authentication for high-security environments.
3. (Optional.) Configuring the polling feature
4. (Optional.) Configuring PPP negotiation
¡ Configuring the PPP negotiation timeout time
¡ Configuring IPv4 address negotiation on the client
¡ Configuring IPv4 address negotiation on the server
¡ Configuring IPv6 address negotiation on the server
5. (Optional.) Enabling PPP link quality monitoring
6. (Optional.) Configuring magic number check for PPP
7. (Optional.) Enabling PPP user blocking
8. (Optional.) Setting the online PPP session count alarm thresholds on the device
Enabling PPP encapsulation on an interface
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Enable PPP encapsulation on the interface.
link-protocol ppp
By default, all interfaces except Ethernet interfaces use PPP as the link layer protocol.
Configuring PPP authentication
About PPP authentication
You can configure several authentication modes simultaneously. In LCP negotiation, the authenticator negotiates with the peer in the sequence of configured authentication modes until the LCP negotiation succeeds. If the response packet from the peer carries a recommended authentication mode, the authenticator directly uses the authentication mode if it finds the mode configured.
Configuring PAP authentication
Restrictions and guidelines for PAP authentication
For local AAA authentication, the username and password of the peer must be configured on the authenticator.
For remote AAA authentication, the username and password of the peer must be configured on the remote AAA server.
The username and password configured for the peer must be the same as those configured on the peer by using the ppp pap local-user command.
Configuring the authenticator
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Configure the authenticator to authenticate the peer by using PAP.
ppp authentication-mode pap [ domain { isp-name | default enable isp-name } ]
By default, PPP authentication is disabled.
4. Configure local or remote AAA authentication.
For more information about AAA authentication, see Security Configuration Guide.
Configuring the peer
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Configure the PAP username and password sent from the peer to the authenticator when the peer is authenticated by the authenticator by using PAP.
ppp pap local-user username password { cipher | simple } string
By default, when being authenticated by the authenticator by using PAP, the peer sends null username and password to the authenticator.
For security purposes, the password specified in plaintext form and ciphertext form will be stored in encrypted form.
Configuring CHAP authentication (authenticator name is configured)
Restrictions and guidelines for CHAP authentication (authenticator name is configured)
When you configure the authenticator, follow these guidelines:
· For local AAA authentication, the username and password of the peer must be configured on the authenticator.
· For remote AAA authentication, the username and password of the peer must be configured on the remote AAA server.
· The username and password configured for the peer must meet the following requirements:
¡ The username configured for the peer must be the same as that configured on the peer by using the ppp chap user command.
¡ The passwords configured for the authenticator and peer must be the same.
When you configure the peer, follow these guidelines:
· For local AAA authentication, the username and password of the authenticator must be configured on the peer.
· For remote AAA authentication, the username and password of the authenticator must be configured on the remote AAA server.
· The username and password configured for the authenticator must meet the following requirements:
¡ The username configured for the authenticator must be the same as that configured on the authenticator by using the ppp chap user command.
¡ The passwords configured for the authenticator and peer must be the same.
· The peer does not support the CHAP authentication password configured by using the ppp chap password command. CHAP authentication (authenticator name is configured) will apply even if the authentication name is configured.
Configuring the authenticator
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Configure the authenticator to authenticate the peer by using CHAP.
ppp authentication-mode chap [ domain { isp-name | default enable isp-name } ]
By default, PPP authentication is disabled.
4. Configure a username for the CHAP authenticator.
ppp chap user username
The default setting is null.
5. Configure local or remote AAA authentication.
For more information about AAA authentication, see Security Configuration Guide.
Configuring the peer
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Configure a username for the CHAP peer.
ppp chap user username
The default setting is null.
4. Configure local or remote AAA authentication.
For more information about AAA authentication, see Security Configuration Guide.
Configuring CHAP authentication (authenticator name is not configured)
Restrictions and guidelines for CHAP authentication (authenticator name is not configured)
For local AAA authentication, the username and password of the peer must be configured on the authenticator.
For remote AAA authentication, the username and password of the peer must be configured on the remote AAA server.
The username and password configured for the peer must meet the following requirements:
· The username configured for the peer must be the same as that configured on the peer by using the ppp chap user command.
· The password configured for the peer must be the same as that configured on the peer by using the ppp chap password command.
Configuring the authenticator
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Configure the authenticator to authenticate the peer by using CHAP.
ppp authentication-mode chap [ domain { isp-name | default enable isp-name } ]
By default, PPP authentication is disabled.
4. Configure local or remote AAA authentication.
For more information about AAA authentication, see Security Configuration Guide.
Configuring the peer
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Configure a username for the CHAP peer.
ppp chap user username
The default setting is null.
4. Set the CHAP authentication password.
ppp chap password { cipher | simple } string
The default setting is null.
For security purposes, the password specified in plaintext form and ciphertext form will be stored in encrypted form.
Configuring MS-CHAP or MS-CHAP-V2 authentication
Restrictions and guidelines for MS-CHAP or MS-CHAP-V2 authentication
The device can only act as an authenticator for MS-CHAP or MS-CHAP-V2 authentication.
MS-CHAP-V2 authentication supports password change only when using RADIUS.
As a best practice, do not set the authentication method for PPP users to none when MS-CHAP-V2 authentication is used.
For local AAA authentication, the username and password of the peer must be configured on the authenticator. For remote AAA authentication, the username and password of the peer must be configured on the remote AAA server. The username and password of the peer configured on the authenticator or remote AAA server must be the same as those configured on the peer.
If authentication name is configured, the username configured for the authenticator on the peer must be the same as that configured on the authenticator by using the ppp chap user command.
Configuring MS-CHAP or MS-CHAP-V2 authentication (authenticator name is configured)
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Configure the authenticator to authenticate the peer by using MS-CHAP or MS-CHAP-V2.
ppp authentication-mode { ms-chap | ms-chap-v2 } [ domain { isp-name | default enable isp-name } ]
By default, PPP authentication is disabled.
4. Configure a username for the MS-CHAP or MS-CHAP-V2 authenticator.
ppp chap user username
5. Configure local or remote AAA authentication.
For more information about AAA authentication, see Security Configuration Guide.
Configuring MS-CHAP or MS-CHAP-V2 authentication (authenticator name is not configured)
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Configure the authenticator to authenticate the peer by using MS-CHAP or MS-CHAP-V2.
ppp authentication-mode { ms-chap | ms-chap-v2 } [ domain { isp-name | default enable isp-name } ]
By default, PPP authentication is disabled.
4. Configure local or remote AAA authentication.
For more information about AAA authentication, see Security Configuration Guide.
Configuring the polling feature
About this task
The polling feature checks PPP link state.
On an interface that uses PPP encapsulation, the link layer sends keepalive packets at keepalive intervals to detect the availability of the peer. If the interface has received no response to keepalive packets when the keepalive retry limit is reached, it determines that the link has failed and reports a link layer down event.
To set the keepalive retry limit, use the timer-hold retry command.
The value 0 disables an interface from sending keepalive packets. In this case, the interface can respond to keepalive packets from the peer.
Restrictions and guidelines
On a slow link, increase the keepalive interval to prevent false shutdown of the interface. This situation might occur when keepalive packets are delayed because a large packet is being transmitted on the link.
The keepalive interval must be smaller than the negotiation timeout time.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Set the keepalive interval.
timer-hold seconds
By default, the keepalive interval is 10 seconds.
4. Set the keepalive retry limit.
timer-hold retry retries
By default, the keepalive retry limit is 5.
Configuring PPP negotiation
Configuring the PPP negotiation timeout time
About this task
The device starts the PPP negotiation timeout timer after sending a packet. If no response is received before the timer expires, the device sends the packet again.
Restrictions and guidelines
If two ends of a PPP link vary greatly in the LCP negotiation packet processing rate, configure the delay timer on the end with a higher processing rate. The LCP negotiation delay timer prevents frequent LCP negotiation packet retransmission. After the physical layer comes up, PPP starts LCP negotiation when the delay timer expires. If PPP receives LCP negotiation packets before the delay timer expires, it starts LCP negotiation immediately.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. (Optional.) Configure the LCP negotiation delay timer.
ppp lcp delay milliseconds
By default, PPP starts LCP negotiation after the physical layer comes up.
4. Configure the negotiation timeout time.
ppp timer negotiate seconds
The default setting is 3 seconds.
Configuring IPv4 address negotiation on the client
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Enable IP address negotiation.
ip address ppp-negotiate
By default, IP address negotiation is not enabled.
If you execute this command and the ip address command multiple times, the most recent configuration takes effect. For more information about the ip address command, see Layer 3—IP Services Command Reference.
Configuring IPv4 address negotiation on the server
About this task
Configure the server to assign an IP address to a client by using the following methods:
· Method 1: Specify an IP address for the client on the server interface.
· Method 2: Specify an address pool on the server interface.
· Method 3: Associate an address pool with an ISP domain.
· Method 4: Authorize an IP address to a client by using the AAA server.
Restrictions and guidelines for IP address negotiation on the server
For clients requiring no authentication, you can use either method 1 or method 2. When both method 1 and method 2 are configured, the most recent configuration takes effect.
For clients requiring authentication, you can use one or more of the four methods. When multiple methods are configured, method 4 takes precedence over method 3, and method 3 takes precedence over method 1 or method 2. When both method 1 and method 2 are configured, the most recent configuration takes effect.
When you use method 4, enable DHCP on the AAA server by using the dhcp enable command and authorize an IP address to the client. For more information about the dhcp enable command, see Layer 3—IP Services Command Reference.
Specifying an IP address for the client on the server interface
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Configure the interface to assign an IP address to the peer.
remote address ip-address
By default, an interface does not assign an IP address to the peer.
4. Configure an IP address for the interface.
ip address ip-address
By default, no IP address is configured on an interface.
Specifying an IP address pool on the server interface
1. Enter system view.
system-view
2. Configure DHCP.
¡ If the server acts as a DHCP server, perform the following tasks:
- Configure the DHCP server.
- Configure an IP address pool on the server.
¡ If the server acts as a DHCP relay agent, perform the following tasks:
- Configure the DHCP relay agent on the server.
- Configure an IP address pool on the remote DHCP server.
- Enable the DHCP relay agent to record relay entries.
- Configure a DHCP relay address pool.
For information about configuring a DHCP server and a DHCP relay agent, see Layer 3—IP Services Configuration Guide.
3. Enter interface view.
interface interface-type interface-number
4. Configure the interface to assign an IP address from the configured IP address pool to the peer.
remote address pool pool-name
By default, an interface does not assign an IP address to the peer.
5. (Optional.) Configure the method of generating DHCP client IDs when PPP users act as DHCP clients.
remote address dhcp client-identifier { { callingnum | username } [ session-info ] | session-info }
By default, the method of generating DHCP client IDs when PPP users act as DHCP clients is not configured.
When DHCP client IDs are generated based on PPP usernames, make sure different users use different PPP usernames to come online.
6. Configure an IP address for the interface.
ip address ip-address
By default, no IP address is configured on an interface.
Associating an IP address pool with an ISP domain
1. Enter system view.
system-view
2. Configure DHCP.
¡ If the server acts as a DHCP server, perform the following tasks:
- Configure the DHCP server.
- Configure an IP address pool on the server.
¡ If the server acts as a DHCP relay agent, perform the following tasks:
- Configure the DHCP relay agent on the server.
- Configure an IP address pool on the remote DHCP server.
- Enable the DHCP relay agent to record relay entries.
- Configure a DHCP relay address pool.
For information about configuring a DHCP server and a DHCP relay agent, see Layer 3—IP Services Configuration Guide.
3. Enter ISP domain view.
domain name isp-name
4. Associate the ISP domain with the configured IP address pool or DHCP relay address pool for address assignment.
authorization-attribute ip-pool pool-name
By default, no IP address pool or DHCP relay address pool is associated.
For more information about this command, see Security Command Reference.
5. Return to system view.
quit
6. Enter interface view.
interface interface-type interface-number
7. (Optional.) Configure the method of generating DHCP client IDs when PPP users act as DHCP clients.
remote address dhcp client-identifier { { callingnum | username } [ session-info ] | session-info }
By default, the method of generating DHCP client IDs when PPP users act as DHCP clients is not configured.
When DHCP client IDs are generated based on PPP usernames, make sure different users use different PPP usernames to come online.
8. Configure an IP address for the interface.
ip address ip-address
By default, no IP address is configured on an interface.
Configuring IPv6 address negotiation on the server
Assigning an IPv6 address by using the NDRA method
1. Enter interface view.
interface interface-type interface-number
2. Configure the interface to automatically generate a link-local address.
ipv6 address auto link-local
3. Configure the prefix information in RA messages on the interface.
ipv6 nd ra prefix { ipv6-prefix prefix-length | ipv6-prefix/prefix-length } [ valid-lifetime preferred-lifetime [ no-autoconfig | off-link ] * | no-advertise ]
The IPv6 prefix in the RA message is determined in the following sequence:
¡ IPv6 prefix authorized by AAA.
¡ Prefix in the ND prefix pool authorized by AAA.
¡ RA prefix configured on the interface.
¡ Prefix of the IPv6 global unicast address configured on the interface.
4. Enable the interface to advertise RA messages.
undo ipv6 nd ra halt
5. Set the other stateful configuration flag (O) to 1 in RA advertisements to be sent.
ipv6 nd autoconfig other-flag
6. Enable the DHCPv6 server.
ipv6 dhcp select server
7. Return to system view.
quit
8. Create an ISP domain and enter its view.
domain name isp-name
9. Configure an IPv6 prefix authorized to the user in the ISP domain.
authorization-attribute ipv6-prefix ipv6-prefix prefix-length
Assigning an IPv6 address by using the IA_NA method
1. Enter interface view.
interface interface-type interface-number
2. Configure the interface to automatically generate a link-local address.
ipv6 address auto link-local
3. Configure the prefix information in RA messages on the interface.
ipv6 nd ra prefix { ipv6-prefix prefix-length | ipv6-prefix/prefix-length } [ valid-lifetime preferred-lifetime [ no-autoconfig | off-link ] * | no-advertise ]
The IPv6 prefix in the RA message is determined in the following sequence:
¡ IPv6 prefix authorized by AAA.
¡ Prefix in the ND prefix pool authorized by AAA.
¡ RA prefix configured on the interface.
¡ Prefix of the IPv6 global unicast address configured on the interface.
4. Enable the interface to advertise RA messages.
undo ipv6 nd ra halt
5. Set the managed address configuration flag (M) to 1 in RA advertisements to be sent.
ipv6 nd autoconfig managed-address-flag
6. Set the other stateful configuration flag (O) to 1 in RA advertisements to be sent.
ipv6 nd autoconfig other-flag
7. Enable the DHCPv6 server.
ipv6 dhcp select server
8. Return to system view.
quit
9. Configure an IPv6 address pool and configure an ISP domain to authorize the address pool to users.
For more information, see DHCPv6 configuration in Layer 3—IP Services Configuration Guide and AAA configuration in Security Configuration Guide.
Assigning an IPv6 address by using the IA_PD method
1. Enter interface view.
interface interface-type interface-number
2. Configure the interface to automatically generate a link-local address.
ipv6 address auto link-local
3. Enable the interface to advertise RA messages.
undo ipv6 nd ra halt
4. Enable the DHCPv6 server.
ipv6 dhcp select server
5. Return to system view.
quit
6. Create a prefix pool and specify the prefix and the assigned prefix length for the pool.
ipv6 dhcp prefix-pool prefix-pool-number prefix prefix/prefix-len assign-len assign-len
7. Create an IPv6 address pool and enter its view.
ipv6 pool pool-name
8. Apply a prefix pool to the IPv6 address pool, so the DHCPv6 server can dynamically select a prefix from the prefix pool for the client.
prefix-pool prefix-pool-number [ preferred-lifetime preferred-lifetime valid-lifetime valid-lifetime ]
9. Return to system view.
quit
10. Create an ISP domain and enter its view.
domain name isp-name
11. Configure the user authorization attribute in the ISP domain.
authorization-attribute ipv6-pool pool-name
Enabling IP segment match
About this task
This feature enables the local interface to check whether its IP address and the IP address of the remote interface are in the same network segment. If they are not, IPCP negotiation fails.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Enable IP segment match.
ppp ipcp remote-address match
By default, this feature is disabled.
Enabling PPP link quality monitoring
About this task
PPP link quality monitoring (LQM) monitors the quality (packet loss ratio and packet error ratio) of PPP links in real time.
If PPP LQM is not enabled, each end of a PPP link periodically sends keepalives to its peer. If PPP LQM is enabled, Link Quality Reports (LQRs) packets replace keepalives to monitor the link.
The system uses received LQR packets to measure the link quality. If two consecutive measured results are below the close-percentage, the system shuts down the link. Then the system measures the link quality at an interval that is ten times the LQR interval. If three consecutive measured results are higher than the PPP LQM resume-percentage, the system brings up the link.
Restrictions and guidelines
A shut-down link must experience a minimum of 30 keepalive intervals before it can come up again. As a best practice, do not set the keepalive interval to a large value.
If you enable PPP LQM on both sides of a PPP link, make sure both sides have the same PPP LQM settings. Typically, there is no need to enable PPP LQM on both sides of a PPP link.
This feature does not affect existing users.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Enable PPP LQM.
ppp lqm close-percentage close-percentage [ resume-percentage resume-percentage ]
By default, PPP LQM is disabled.
Configuring magic number check for PPP
About this task
In the PPP link establishment process, the magic number is negotiated. After the negotiation, both the local end and the peer end save their magic numbers locally.
The local end sends Echo-Request packets carrying its own magic number. When magic number check is enabled on both the local end and the peer end, the peer end will compare its own magic number with the magic number in the received Echo-Request packets. If they are the same, the link status is considered as normal, and the peer end replies with Echo-Reply packets carrying its own magic number. The local end also compares its own magic number with the magic number carried in the received Echo-Reply packets. On either end, if the magic number check fails for five consecutive Echo-Request or Echo-Reply packets, the link is disconnected, and LCP negotiation is restarted.
Only the end with magic number check enabled can check the magic number in received Echo-Request or Echo-Reply packets.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Enable magic number check for PPP.
ppp magic-number-check
By default, magic number check is disabled for PPP.
Enabling PPP user blocking
About this task
This feature blocks a PPP user for a period if the user fails authentication consecutively for the specified number of times within the detection period. This feature helps prevent illegal users from using the method of exhaustion to obtain the password, and reduces authentication packets sent to the authentication server. Packets from the blocked users will be discarded during the blocking period, and will be processed when the blocking period expires.
Restrictions and guidelines
This feature identify users by username and domain name. Users that have the same username but belong to different domains are processes as different users.
Procedure
1. Enter system view.
system-view
2. Enable PPP user blocking.
ppp authentication chasten auth-failure auth-period blocking-period
By default, PPP user blocking is disabled.
Setting the online PPP session count alarm thresholds on the device
About this task
The online PPP session count on the device refers to the total number of online PPP sessions on the whole IRF system.
You can use this command to set the upper alarm threshold and lower alarm threshold for the PPP session count. When the PPP session count exceeds the upper alarm threshold or drops below the lower threshold, an alarm is triggered automatically. Then, the administrator can promptly know the online user conditions of the network. Additionally, the administrator can use the display access-user command to view the total number of online PPP sessions.
The maximum number of PPP sessions that can be established depends on the device specifications.
Suppose the maximum number of online PPP sessions allowed is a, the upper alarm threshold is b, and the lower alarm threshold is c. The following rules apply:
· When the online PPP session count exceeds a×b or drops below a×c, the corresponding alarm information is output.
· When the online PPP session count returns between the upper alarm threshold and lower alarm threshold, the alarm clearing information is output.
In some special cases, the online PPP session count frequently changes in the critical range, which causes frequent output of alarm information and alarm clearing information. To avoid this problem, the system introduces a buffer area when the online PPP session count recovers from the upper or lower threshold. The buffer area size is 10% of the difference between the upper threshold and the lower threshold. Suppose the buffer area size is d. Then, d=a×(b-c)÷10. When the online PPP session count drops below a×b-d or exceeds a×c+d, the alarm clearing information is output.
For example, suppose a is 1000, b is 80%, and c is 20%. Then, d= a×(b-c)÷10=1000×(80%-20%)÷10=1000×60%÷10=600÷10=60.
When the online PPP session count exceeds the upper threshold a×b=1000×80%=800, the upper threshold alarm is output. When the online PPP session count restores to be smaller than a×b-d=800-60=740, the alarm clearing information is output.
When the online PPP session count drops below the lower threshold a×c=1000×20%=200, the lower threshold alarm is output. When the online PPP session count restores to be greater than a×c+d=200+60=260, the alarm clearing information is output.
Restrictions and guidelines
The upper alarm threshold must be greater than the lower alarm threshold.
Procedure
1. Enter system view.
system-view
2. Configure the upper and lower online PPP session count alarm thresholds on the device.
ppp session-threshold { lower-limit lower-limit-value | upper-limit upper-limit-value }
By default, the upper online PPP session count alarm threshold is 100, and the lower online PPP session count alarm threshold is 0.
Display and maintenance commands for PPP
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display statistics about PPP user blocking. |
display ppp chasten statistics |
|
Display blocking information about PPP users. |
display ppp chasten user { auth-failed | blocked } [ username user-name ] |
|
Display PPP negotiation packet statistics. |
display ppp packet statistics [ chassis chassis-number slot slot-number [ cpu cpu-number ] ] |
|
Unblock PPP users. |
reset ppp chasten blocked-user [ username user-name ] |
|
Clear PPP negotiation packet statistics. |
reset ppp packet statistics [ chassis chassis-number slot slot-number [ cpu cpu-number ] ] |
PPP configuration examples
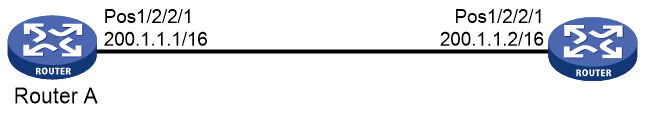
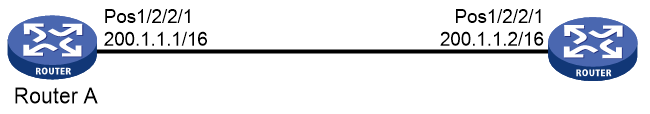
Example: Configuring one-way PAP authentication
Network configuration
As shown in Figure 2, configure Router A to authenticate Router B by using PAP, but Router B not to authenticate Router A.
Procedure
1. Configure Router A:
# Create a user account for Router B.
<RouterA> system-view
[RouterA] local-user userb class network
# Set a password for the user account.
[RouterA-luser-network-userb] password simple passb
# Set the service type of the user account to PPP.
[RouterA-luser-network-userb] service-type ppp
[RouterA-luser-network-userb] quit
# Enable PPP encapsulation on Pos 1/2/2/1. By default, an interface uses PPP encapsulation.
[RouterA] interface pos 1/2/2/1
[RouterA-Pos1/2/2/1] link-protocol ppp
# Set the authentication mode to PAP.
[RouterA-Pos1/2/2/1] ppp authentication-mode pap domain system
# Assign an IP address to Pos 1/2/2/1.
[RouterA-Pos1/2/2/1] ip address 200.1.1.1 16
[RouterA-Pos1/2/2/1] quit
# Configure local authentication for the PPP users in the default ISP domain (system).
[RouterA] domain name system
[RouterA-isp-system] authentication ppp local
[RouterA-isp-system] quit
2. Configure Router B:
# Enable PPP encapsulation on Pos 1/2/2/1. By default, an interface uses PPP encapsulation.
<RouterB> system-view
[RouterB] interface pos 1/2/2/1
[RouterB-Pos1/2/2/1] link-protocol ppp
# On Pos 1/2/2/1, configure the PAP username and password sent from Router B to Router A when Router B is authenticated by Router A using PAP.
[RouterB-Pos1/2/2/1] ppp pap local-user userb password simple passb
# Assign an IP address to Pos 1/2/2/1 of Router B.
[RouterB-Pos1/2/2/1] ip address 200.1.1.2 16
[RouterB-Pos1/2/2/1] quit
Verifying the configuration
# Use the display interface pos command to display information about Pos 1/2/2/1 of Router B.
[RouterB] display interface pos 1/2/2/1
Pos1/2/2/1
Current state: UP
Line protocol state: UP
Description: Pos1/2/2/1 Interface
Bandwidth: 64kbps
Maximum transmission unit: 1500
Hold timer: 10 seconds, retry times: 5
Internet address: 200.1.1.2/16 (primary)
Link layer protocol: PPP
LCP: opened, IPCP: opened
...
The output shows that:
· The physical layer status and link layer status of the interface are both up.
· The states of LCP and IPCP are both Opened, indicating that PPP negotiation has succeeded.
# Verify that Router A and Router B can ping each other.
[RouterB] ping 200.1.1.1
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss Ping 200.1.1.1 (200.1.1.1): 56 data bytes, press CTRL+C to break
56 bytes from 200.1.1.1: icmp_seq=0 ttl=128 time=3.197 ms
56 bytes from 200.1.1.1: icmp_seq=1 ttl=128 time=2.594 ms
56 bytes from 200.1.1.1: icmp_seq=2 ttl=128 time=2.739 ms
56 bytes from 200.1.1.1: icmp_seq=3 ttl=128 time=1.738 ms
56 bytes from 200.1.1.1: icmp_seq=4 ttl=128 time=1.744 ms
--- Ping statistics for 200.1.1.1 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 1.738/2.402/3.197/0.576 ms
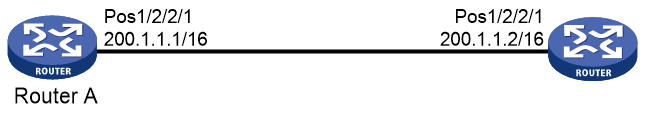
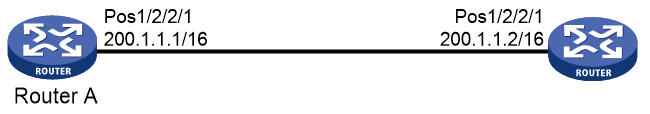
Example: Configuring two-way PAP authentication
Network configuration
As shown in Figure 3, configure Router A and Router B to authenticate each other.
Procedure
1. Configure Router A:
# Create a user account for Router B.
<RouterA> system-view
[RouterA] local-user userb class network
# Set a password for the user account.
[RouterA-luser-network-userb] password simple passb
# Set the service type of the user account to PPP.
[RouterA-luser-network-userb] service-type ppp
[RouterA-luser-network-userb] quit
# Enable PPP encapsulation on Pos 1/2/2/1. By default, an interface uses PPP encapsulation.
[RouterA] interface pos 1/2/2/1
[RouterA-Pos1/2/2/1] link-protocol ppp
# Set the authentication mode to PAP.
[RouterA-Pos1/2/2/1] ppp authentication-mode pap domain system
# Configure the PAP username and password sent from Router A to Router B when Router A is authenticated by Router B using PAP.
[RouterA-Pos1/2/2/1] ppp pap local-user usera password simple passa
# Assign an IP address to Pos 1/2/2/1 of Router A.
[RouterA-Pos1/2/2/1] ip address 200.1.1.1 16
[RouterA-Pos1/2/2/1] quit
# Configure local authentication for the PPP users in the default ISP domain (system).
[RouterA] domain name system
[RouterA-isp-system] authentication ppp local
[RouterA-isp-system] quit
2. Configure Router B:
# Create a user account for Router A on Router B.
<RouterB> system-view
[RouterB] local-user usera class network
# Set a password for the user account.
[RouterB-luser-network-usera] password simple passa
# Set the service type of the user account to PPP.
[RouterB-luser-network-usera] service-type ppp
[RouterB-luser-network-usera] quit
# Enable PPP encapsulation on Pos 1/2/2/1. By default, an interface uses PPP encapsulation.
[RouterB] interface pos 1/2/2/1
[RouterB-Pos1/2/2/1] link-protocol ppp
# Set the authentication mode to PAP on Pos 1/2/2/1.
[RouterB-Pos1/2/2/1] ppp authentication-mode pap domain system
# On Pos 1/2/2/1, configure the PAP username and password sent from Router B to Router A when Router B is authenticated by Router A using PAP.
[RouterB-Pos1/2/2/1] ppp pap local-user userb password simple passb
# Assign an IP address to Pos 1/2/2/1.
[RouterB-Pos1/2/2/1] ip address 200.1.1.2 16
[RouterB-Pos1/2/2/1] quit
# Configure local authentication for the PPP users in the default ISP domain (system).
[RouterB] domain name system
[RouterB-isp-system] authentication ppp local
[RouterB-isp-system] quit
Verifying the configuration
# Use the display interface pos command to display information about Pos 1/2/2/1 of Router B.
[RouterB] display interface pos 1/2/2/1
Pos1/2/2/1
Current state: UP
Line protocol state: UP
Description: Pos1/2/2/1 Interface
Bandwidth: 64kbps
Maximum transmission unit: 1500
Hold timer: 10 seconds, retry times: 5
Internet address: 200.1.1.2/16 (primary)
Link layer protocol: PPP
LCP opened, IPCP opened
...
The output shows that:
· The physical layer status and link layer status of the interface are both up.
· The states of LCP and IPCP are both Opened, indicating that PPP negotiation has succeeded.
# Verify that Router B can successfully ping Router A.
[RouterB] ping 200.1.1.1
Ping 200.1.1.1 (200.1.1.1): 56 data bytes, press CTRL+C to break
56 bytes from 200.1.1.1: icmp_seq=0 ttl=128 time=3.197 ms
56 bytes from 200.1.1.1: icmp_seq=1 ttl=128 time=2.594 ms
56 bytes from 200.1.1.1: icmp_seq=2 ttl=128 time=2.739 ms
56 bytes from 200.1.1.1: icmp_seq=3 ttl=128 time=1.738 ms
56 bytes from 200.1.1.1: icmp_seq=4 ttl=128 time=1.744 ms
--- Ping statistics for 200.1.1.1 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 1.738/2.402/3.197/0.576 ms
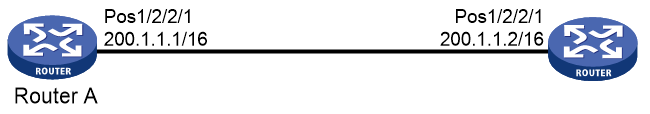
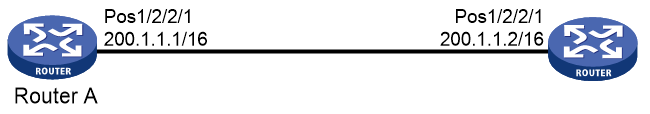
Example: Configuring one-way CHAP authentication
Network configuration
As shown in Figure 4, configure Router A to authenticate Router B by using CHAP.
Procedure (authenticator name is configured)
1. Configure Router A:
# Create a user account for Router B.
<RouterA> system-view
[RouterA] local-user userb class network
# Set a password for the user account.
[RouterA-luser-network-userb] password simple hello
# Set the service type of the user account to PPP.
[RouterA-luser-network-userb] service-type ppp
[RouterA-luser-network-userb] quit
# Enable PPP encapsulation on Pos 1/2/2/1. By default, an interface uses PPP encapsulation.
[RouterA] interface pos 1/2/2/1
[RouterA-Pos1/2/2/1] link-protocol ppp
# On Pos 1/2/2/1, configure the username for Router A when Router A authenticates Router B.
[RouterA-Pos1/2/2/1] ppp chap user usera
# Set the authentication mode to CHAP on Pos 1/2/2/1.
[RouterA-Pos1/2/2/1] ppp authentication-mode chap domain system
# Assign an IP address to Pos 1/2/2/1.
[RouterA-Pos1/2/2/1] ip address 200.1.1.1 16
[RouterA-Pos1/2/2/1] quit
# Configure local authentication for the PPP users in the default ISP domain (system).
[RouterA] domain name system
[RouterA-isp-system] authentication ppp local
[RouterA-isp-system] quit
2. Configure Router B:
# Create a user account for Router A on Router B.
<RouterB> system-view
[RouterB] local-user usera class network
# Set a password for the user account.
[RouterB-luser-network-usera] password simple hello
# Set the service type of the user account to PPP.
[RouterB-luser-network-usera] service-type ppp
[RouterB-luser-network-usera] quit
# Enable PPP encapsulation on Pos 1/2/2/1. By default, an interface uses PPP encapsulation.
[RouterB] interface pos 1/2/2/1
[RouterB-Pos1/2/2/1] link-protocol ppp
# Configure the username for Router B when Router B is authenticated.
[RouterB-Pos1/2/2/1] ppp chap user userb
# Assign an IP address to Pos 1/2/2/1 of Router B.
[RouterB-Pos1/2/2/1] ip address 200.1.1.2 16
[RouterB-Pos1/2/2/1] quit
Procedure (authenticator name is not configured)
1. Configure Router A:
# Create a user account for Router B.
<RouterA> system-view
[RouterA] local-user userb class network
# Set a password for the user account.
[RouterA-luser-network-userb] password simple hello
# Set the service type of the user account to PPP.
[RouterA-luser-network-userb] service-type ppp
[RouterA-luser-network-userb] quit
# Set the authentication mode to CHAP on Pos 1/2/2/1.
[RouterA] interface pos 1/2/2/1
[RouterA-Pos1/2/2/1] ppp authentication-mode chap domain system
# Assign an IP address to Pos 1/2/2/1.
[RouterA-Pos1/2/2/1] ip address 200.1.1.1 16
[RouterA-Pos1/2/2/1] quit
# Configure local authentication for the PPP users in the default ISP domain (system).
[RouterA] domain name system
[RouterA-isp-system] authentication ppp local
[RouterA-isp-system] quit
2. Configure Router B:
# On Pos 1/2/2/1, configure the username of Router B when Router B is authenticated.
<RouterB> system-view
[RouterB] interface pos 1/2/2/1
[RouterB-Pos1/2/2/1] ppp chap user userb
# Set the default CHAP password on Pos 1/2/2/1.
[RouterB-Pos1/2/2/1] ppp chap password simple hello
# Assign an IP address to Pos 1/2/2/1.
[RouterB-Pos1/2/2/1] ip address 200.1.1.2 16
[RouterB-Pos1/2/2/1] quit
Verifying the configuration
# Use the display interface pos command to display information about Pos 1/2/2/1 of Router B.
[RouterB] display interface pos 1/2/2/1
Pos1/2/2/1
Current state: UP
Line protocol state: UP
Description: Pos1/2/2/1 Interface
Bandwidth: 64kbps
Maximum transmission unit: 1500
Hold timer: 10 seconds, retry times: 5
Internet address: 200.1.1.2/16 (primary)
Link layer protocol: PPP
LCP opened, IPCP opened
...
The output shows that:
· The physical layer status and link layer status of the interface are both up.
· The states of LCP and IPCP are both Opened, indicating that PPP negotiation has succeeded.
# Verify that Router A and Router B can ping each other.
[RouterB] ping 200.1.1.1
Ping 200.1.1.1 (200.1.1.1): 56 data bytes, press CTRL+C to break
56 bytes from 200.1.1.1: icmp_seq=0 ttl=128 time=3.197 ms
56 bytes from 200.1.1.1: icmp_seq=1 ttl=128 time=2.594 ms
56 bytes from 200.1.1.1: icmp_seq=2 ttl=128 time=2.739 ms
56 bytes from 200.1.1.1: icmp_seq=3 ttl=128 time=1.738 ms
56 bytes from 200.1.1.1: icmp_seq=4 ttl=128 time=1.744 ms
--- Ping statistics for 200.1.1.1 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 1.738/2.402/3.197/0.576 ms
Example: Specifying an IP address for the client on the server interface
Network configuration
As shown in Figure 5, configure Router A to allocate an IP address to Pos 1/2/2/1 of Router B through PPP negotiation. The IP address is specified on an interface of Router A.
Procedure
1. Configure Router A:
# Configure an IP address to be assigned to the peer interface on Pos 1/2/2/1.
<RouterA> system-view
[RouterA] interface pos 1/2/2/1
[RouterA-Pos1/2/2/1] remote address 200.1.1.10
# Configure an IP address for Pos 1/2/2/1.
[RouterA-Pos1/2/2/1] ip address 200.1.1.1 16
[RouterA-Pos1/2/2/1] quit
2. Enable IP address negotiation on Pos 1/2/2/1 of Router B.
<RouterB> system-view
[RouterB] interface pos 1/2/2/1
[RouterB-Pos1/2/2/1] ip address ppp-negotiate
[RouterB-Pos1/2/2/1] quit
Verifying the configuration
# Display summary information about Pos 1/2/2/1 on Router B.
[RouterB] display interface pos 1/2/2/1 brief
Brief information on interfaces in route mode:
Link: ADM - administratively down; Stby - standby
Protocol: (s) - spoofing
Interface Link Protocol Primary IP Description
Pos1/2/2/1 UP UP 200.1.1.10
The output shows Pos 1/2/2/1 obtains IP address 200.1.1.10 through PPP negotiation.
# Verify that Router B can ping Pos 1/2/2/1 of Router A.
[RouterB] ping 200.1.1.1
Ping 200.1.1.1 (200.1.1.1): 56 data bytes, press CTRL+C to break
56 bytes from 200.1.1.1: icmp_seq=0 ttl=128 time=3.197 ms
56 bytes from 200.1.1.1: icmp_seq=1 ttl=128 time=2.594 ms
56 bytes from 200.1.1.1: icmp_seq=2 ttl=128 time=2.739 ms
56 bytes from 200.1.1.1: icmp_seq=3 ttl=128 time=1.738 ms
56 bytes from 200.1.1.1: icmp_seq=4 ttl=128 time=1.744 ms
--- Ping statistics for 200.1.1.1 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 1.738/2.402/3.197/0.576 ms
Example: Specifying an IP address pool on the server interface
Network configuration
As shown in Figure 6, configure Router A to allocate an IP address from the IP address pool on an interface of Router A to Pos 1/2/2/1 of Router B through PPP negotiation.
Procedure
1. Configure Router A:
# Enable DHCP.
<RouterA> system-view
[RouterA] dhcp enable
# Create IP address pool pool1, and specify the subnet for dynamic allocation and a gateway address in the address pool.
[RouterA] ip pool pool1
[RouterA-ip-pool-pool1] network 200.1.1.0 24
[RouterA-ip-pool-pool1] gateway-list 200.1.1.1
# Exclude IP address 200.1.1.1 from dynamic allocation in the address pool.
[RouterA-ip-pool-pool1] forbidden-ip 200.1.1.1
[RouterA-ip-pool-pool1] quit
# Configure Pos 1/2/2/1 to assign an IP address from IP address pool pool1 to the peer interface.
[RouterA] interface pos 1/2/2/1
[RouterA-Pos1/2/2/1] remote address pool pool1
# Configure an IP address for Pos 1/2/2/1.
[RouterA-Pos1/2/2/1] ip address 200.1.1.1 16
[RouterA-Pos1/2/2/1] quit
2. Enable IP address negotiation on Pos 1/2/2/1 of Router B.
<RouterB> system-view
[RouterB] interface pos 1/2/2/1
[RouterB-Pos1/2/2/1] ip address ppp-negotiate
[RouterB-Pos1/2/2/1] quit
Verifying the configuration
# Display summary information about Pos 1/2/2/1 on Router B.
[RouterB] display interface pos 1/2/2/1 brief
Brief information on interfaces in route mode:
Link: ADM - administratively down; Stby - standby
Protocol: (s) - spoofing
Interface Link Protocol Primary IP Description
Pos1/2/2/1 UP UP 200.1.1.2
The output shows that Pos 1/2/2/1 has obtained IP address 200.1.1.2 through PPP negotiation.
# Verify that Router B can ping Pos 1/2/2/1 of Router A.
[RouterB] ping 200.1.1.1
Ping 200.1.1.1 (200.1.1.1): 56 data bytes, press CTRL+C to break
56 bytes from 200.1.1.1: icmp_seq=0 ttl=128 time=3.197 ms
56 bytes from 200.1.1.1: icmp_seq=1 ttl=128 time=2.594 ms
56 bytes from 200.1.1.1: icmp_seq=2 ttl=128 time=2.739 ms
56 bytes from 200.1.1.1: icmp_seq=3 ttl=128 time=1.738 ms
56 bytes from 200.1.1.1: icmp_seq=4 ttl=128 time=1.744 ms
--- Ping statistics for 200.1.1.1 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 1.738/2.402/3.197/0.576 ms
# Display binding information about assigned IP addresses on Router A.
[RouterA] display dhcp server ip-in-use
IP address Client identifier/ Lease expiration Type
Hardware address
200.1.1.2 0030-3030-302e-3030- Unlimited Auto(C)
3030-2e30-3030-362d
The output shows that one IP address of the IP address pool has been assigned.
Example: Using the IP address pool associated with an ISP domain
Network configuration
As shown in Figure 7, configure Router A to allocate an IP address from the IP address pool associated with the ISP domain to Pos 1/2/2/1 of Router B through PPP negotiation.
Procedure
1. Configure Router A:
# Enable DHCP.
<RouterA> system-view
[RouterA] dhcp enable
# Create IP address pool pool1, and specify the subnet for dynamic allocation and a gateway address in the address pool.
[RouterA] ip pool pool1
[RouterA-ip-pool-pool1] network 200.1.1.0 24
[RouterA-ip-pool-pool1] gateway-list 200.1.1.1
# Exclude IP address 200.1.1.1 from dynamic allocation in the address pool.
[RouterA-ip-pool-pool1] forbidden-ip 200.1.1.1
[RouterA-ip-pool-pool1] quit
# Create a local user for Router B.
[RouterA] local-user userb class network
# Set a password for the local user.
[RouterA-luser-network-userb] password simple 123
# Set the service type to PPP for the local user.
[RouterA-luser-network-userb] service-type ppp
[RouterA-luser-network-userb] quit
# Create ISP domain dm1 and associate the ISP domain with IP address pool pool1.
[RouterA] domain name dm1
[RouterA-isp-dm1] authorization-attribute ip-pool pool1
[RouterA-isp-dm1] quit
# Configure Pos 1/2/2/1 to authenticate the peer interface in ISP domain dm1 by using PAP.
[RouterA] interface pos 1/2/2/1
[RouterA-Pos1/2/2/1] ppp authentication-mode pap domain dm1
# Configure an IP address for Pos 1/2/2/1.
[RouterA-Pos1/2/2/1] ip address 200.1.1.1 16
[RouterA-Pos1/2/2/1] quit
2. Configure Router B:
# On Pos 1/2/2/1, configure the username and password for PAP authentication by Router A.
<RouterB> system-view
[RouterB] interface pos 1/2/2/1
[RouterB-Pos1/2/2/1] ppp pap local-user userb password simple 123
# Enable IP address negotiation on Pos 1/2/2/1.
<RouterB> system-view
[RouterB] interface pos 1/2/2/1
[RouterB-Pos1/2/2/1] ip address ppp-negotiate
[RouterB-Pos1/2/2/1] quit
Verifying the configuration
# Display summary information about Pos 1/2/2/1 on Router B.
[RouterB] display interface pos 1/2/2/1 brief
Brief information on interfaces in route mode:
Link: ADM - administratively down; Stby - standby
Protocol: (s) - spoofing
Interface Link Protocol Primary IP Description
Pos1/2/2/1 UP UP 200.1.1.2
The output shows that Pos 1/2/2/1 has obtained IP address 200.1.1.2 through PPP negotiation.
# Verify that Router B can ping Pos 1/2/2/1 of Router A.
[RouterB-Pos1/2/2/1] ping 200.1.1.1
Ping 200.1.1.1 (200.1.1.1): 56 data bytes, press CTRL+C to break
56 bytes from 200.1.1.1: icmp_seq=0 ttl=128 time=3.197 ms
56 bytes from 200.1.1.1: icmp_seq=1 ttl=128 time=2.594 ms
56 bytes from 200.1.1.1: icmp_seq=2 ttl=128 time=2.739 ms
56 bytes from 200.1.1.1: icmp_seq=3 ttl=128 time=1.738 ms
56 bytes from 200.1.1.1: icmp_seq=4 ttl=128 time=1.744 ms
--- Ping statistics for 200.1.1.1 ---
5 packet(s) transmitted, 5 packet(s) received, 0.0% packet loss
round-trip min/avg/max/std-dev = 1.738/2.402/3.197/0.576 ms
# Display binding information about assigned IP addresses on Router A.
[RouterA] display dhcp server ip-in-use
IP address Client identifier/ Lease expiration Type
Hardware address
200.1.1.2 0030-3030-302e-3030- Unlimited Auto(C)
3030-2e30-3030-362d
The output shows that one IP address of the IP address pool has been assigned.