- Table of Contents
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 02-H3C_Login_Management_Configuration_Examples | 240.55 KB |
|
|
|
H3C Login Management Examples |
|
|
|
|
|
|
Software version: Release 7951P01
Document version: 6W100-20200625
Copyright © 2020 New H3C Technologies Co., Ltd. All rights reserved.
No part of this manual may be reproduced or transmitted in any form or by any means without prior written consent of New H3C Technologies Co., Ltd.
Except for the trademarks of New H3C Technologies Co., Ltd., any trademarks that may be mentioned in this document are the property of their respective owners.
The information in this document is subject to change without notice.
Contents
Example: Configuring console login
Example: Configuring Telnet login
Example: Configuring login user command authorization and accounting
Configuring the HWTACACS server
Introduction
This document provides login configuration examples. It also provides examples for implementing user access control by using command authorization and command accounting.
Prerequisites
The configuration examples in this document were created and verified in a lab environment, and all the devices were started with the factory default configuration. When you are working on a live network, make sure you understand the potential impact of every command on your network.
This document assumes that you have basic knowledge of login management.
Example: Configuring console login
Network configuration
Configure console login so users must pass local authentication to log in to the device through the console port.
Analysis
The port properties for the terminal emulation program must match the console port's default settings.
By default, a local user is assigned the default user role network-operator and is not assigned any service type. To enable the user to log in through the console port, you must assign the terminal service type to the user. To enable the user to manage the device, you must assign the network-admin user role to the user.
Restrictions and guidelines
When you configure console login, follow these restrictions and guidelines:
· Identify the console port carefully to make sure you are connecting to the correct port.
· Prepare a console terminal, for example, a PC. Make sure the console terminal has a terminal emulation program, such as HyperTerminal or PuTTY. For information about how to use terminal emulation programs, see the programs' user guides.
· The required terminal emulation program varies by operating system.
¡ On the Windows Server 2003 or Windows XP operating system, use HyperTerminal.
¡ On the Windows Server 2008, Windows Vista, Windows 7, and other operating systems, use a third-party terminal emulation program. For information about how to use the third-party terminal emulation program, see the user guide or online help for the program.
Procedures
1. Turn off the PC if the PC is on.
2. Connect the DB-9 female connector of the console cable to the serial port of the PC.
3. Identify the console port of the device carefully and connect the RJ-45 connector of the console cable to the console port.
|
IMPORTANT: The serial ports on PCs do not support hot swapping. To connect a PC to an operating device, first connect the PC end. To disconnect a PC from an operating device, first disconnect the device end. |
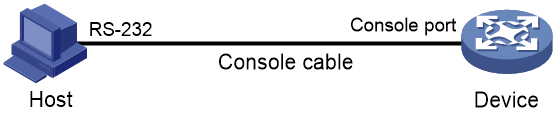
Figure 1 Connecting a configuration terminal to the console port
4. Turn on the PC.
5. On the PC, launch the terminal emulation program and create a connection to the device. Set the port properties so the port properties match the following console port default settings:
¡ Bits per second—9600 bps.
¡ Flow control—None.
¡ Parity—None.
¡ Stop bits—1.
¡ Data bits—8.
6. Power on the device and press Enter as prompted.
The user view prompt appears. To get help, enter a question mark (?).
Line con1 is available.
Press ENTER to get started.
******************************************************************************
* Copyright (c) 2004-2019 New H3C Technologies Co., Ltd. All rights reserved.*
* Without the owner's prior written consent, *
* no decompiling or reverse-engineering shall be allowed. *
******************************************************************************
<Sysname> %Dec 9 17:08:07:804 2014 DeviceD SHELL/5/SHELL_LOGIN: -MDC=1; Console
logged in from con0.
<Sysname>
7. Configure console line 1:
# Enter console line view.
<Sysname> system-view
[Sysname] line console 1
# Enable scheme authentication to use AAA to authenticate the console login user.
[Sysname-line-console1] authentication-mode scheme
[Sysname-line-console1] quit
# Create local user admin.
[Sysname] local-user admin class manage
New local user added.
# Set the password to 123 (plain text) for the local user.
[Sysname-luser-manage-admin] password simple 123
# Assign the terminal service type and the network-admin user role to the user. Reclaim the default user role.
[Sysname-luser-manage-admin] service-type terminal
[Sysname-luser-manage-admin] authorization-attribute user-role network-admin
[Sysname-luser-manage-admin] undo authorization-attribute user-role network-operator
[Sysname-luser-manage-admin] quit
Verifying the configuration
1. Log in to the device through the console port again and press Enter as prompted.
The prompt for username login: appears.
2. Enter the username admin.
The prompt for password Password: appears.
3. Enter the password 123.
The user view prompt <Sysname> appears.
Line con1 is available.
Press ENTER to get started.
login: admin
Password:
******************************************************************************
* Copyright (c) 2004-2019 New H3C Technologies Co., Ltd. All rights reserved.*
* Without the owner's prior written consent, *
* no decompiling or reverse-engineering shall be allowed. *
******************************************************************************
<Sysname>
Configuration files
#
line console 1
authentication-mode scheme
user-role network-admin
#
local-user admin class manage
password hash $h$6$R1DZqFZrkA93GMAf$th9k1FcsjqRRy1A2reQXQkfmnTBSr/7//80W5gKuyeHYxNor/FVNl4tbBQLhaGeY5XFrVr1+WopPcC+dfaumgg==
service-type terminal
authorization-attribute user-role network-admin
#
Example: Configuring Telnet login
Network configuration
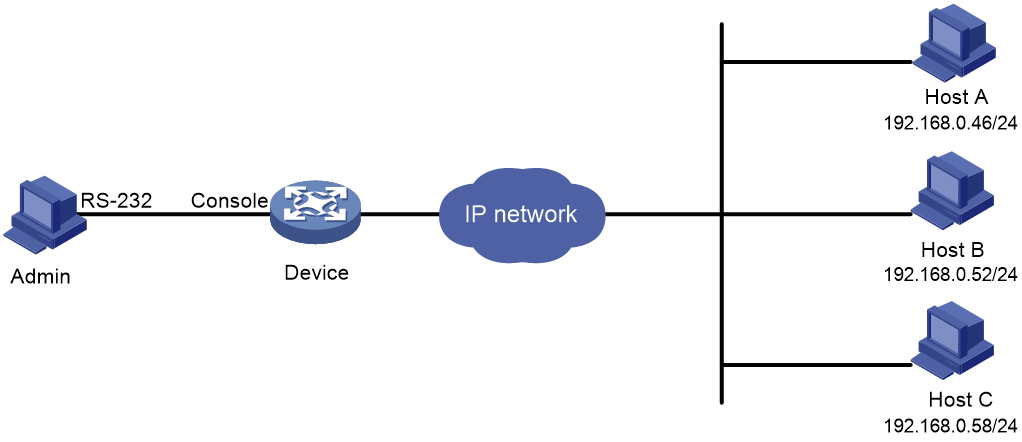
As shown in Figure 2, users need to log in to the device remotely to manage the device.
· Configure Telnet login to enable users to Telnet to the device.
· Configure Telnet user authentication so a Telnet user must provide the correct username and password at login.
· Configure access control so only Telnet users at 192.168.0.46/24 and 192.168.0.52/24 can Telnet to the device.
· Configure two local users.
¡ One local user can manage the device.
¡ One local user can use only the read commands of features.
Analysis
Telnet service is disabled by default. To enable Telnet login, you must enable Telnet service.
To control Telnet login, configure an ACL to permit access only from the specified IP addresses.
By default, a local user is assigned the default user role network-operator. To restrict a local user to read commands, you must create a user role that can access only read commands.
Procedures
# Log in to the device through the console port. (Details not shown.)
# Enable Telnet service.
<Sysname> system-view
[Sysname] telnet server enable
# Enable scheme authentication to use AAA to authenticate the Telnet login user.
[Sysname] line vty 0 63
[Sysname-line-vty0-63] authentication-mode scheme
[Sysname-line-vty0-63] quit
# Create the local user userA. Set the password to 123 (plain text).
[Sysname] local-user userA class manage
New local user added.
[Sysname-luser-manage-userA] password simple 123
# Assign the Telnet service type and the network-admin user role to the user. Reclaim the default user role.
[Sysname-luser-manage-userA] authorization-attribute user-role network-admin
[Sysname-luser-manage-userA] service-type telnet
[Sysname-luser-manage-userA] undo authorization-attribute user-role network-operator
[Sysname-luser-manage-userA] quit
# Create user role roleB. Add rule 1 to permit the user role to access read commands of all features.
[Sysname] role name roleB
[Sysname-role-roleB] rule 1 permit read feature
[Sysname-role-roleB] quit
# Create the local user userB. Set the password to 123 (plain text).
[Sysname] local-user userB class manage
New local user added.
[Sysname-luser-manage-userB] password simple 123
# Assign the Telnet service type and the roleB user role to the user. Reclaim the default user role.
[Sysname-luser-manage-userB] authorization-attribute user-role roleB
[Sysname-luser-manage-userB] service-type telnet
[Sysname-luser-manage-userB] undo authorization-attribute user-role network-operator
[Sysname-luser-manage-userB] quit
# Create ACL 2000 and add rules to permit only access from 192.168.0.46 and 192.168.0.52.
[Sysname] acl basic 2000
[Sysname-acl-ipv4-basic-2000] rule 1 permit source 192.168.0.46 0
[Sysname-acl-ipv4-basic-2000] rule 2 permit source 192.168.0.52 0
[Sysname-acl-ipv4-basic-2000] rule 3 deny source any
[Sysname-acl-ipv4-basic-2000] quit
# Apply the ACL to filter Telnet logins.
[Sysname] telnet server acl 2000
Verifying the configuration
1. Telnet to the device from Host A as userA. (Details not shown.)
2. Display the commands available in user view.
The commands for device configuration and management are included in the list.
login: userA
Password:
******************************************************************************
* Copyright (c) 2004-2019 New H3C Technologies Co., Ltd. All rights reserved.*
* Without the owner's prior written consent, *
* no decompiling or reverse-engineering shall be allowed. *
******************************************************************************
<Sysname> ?
User view commands:
archive Archive configuration
arp Address Resolution Protocol (ARP) module
backup Backup operation
bash Enter the bash shell
boot-loader Software image file management
bootrom Update/read/backup/restore bootrom
cd Change current directory
cfd Connectivity Fault Detection (CFD) module
clock Specify the system clock
connectto Connect to target
copy Copy a file
debugging Enable system debugging functions
delete Delete a file
diagnostic Generic OnLine Diagnostics (GOLD) module
diagnostic-logfile Diagnostic log file configuration
dir Display files and directories on the storage media
display Display current system information
erase Alias for 'delete'
exception Exception information configuration
exit Alias for 'quit'
fdisk Partition a storage medium
fixdisk Check and repair a storage medium
format Format a storage medium
free Release a connection
...
3. Telnet to the device from Host B as userB. (Details not shown.)
4. Display the commands available in user view.
Only read commands are displayed.
login: userB
Password:
******************************************************************************
* Copyright (c) 2004-2019 New H3C Technologies Co., Ltd. All rights reserved.*
* Without the owner's prior written consent, *
* no decompiling or reverse-engineering shall be allowed. *
******************************************************************************
<Sysname> ?
User view commands:
dir Display files and directories on the storage media
display Display current system information
erase Alias for 'delete'
exit Alias for 'quit'
md5sum Compute the hash digest of a file using the MD5 algorithm
more Display the contents of a file
no Alias for 'undo'
pwd Display current working directory
quit Exit from current command view
sha256sum Compute the hash digest of a file using the SHA256 algorithm
show Alias for 'display'
system-view Enter System View
write Alias for 'save'
<Sysname>
5. Telnet to the device from Host C. (Details not shown.)
Your access request is rejected.
Configuration files
#
telnet server enable
telnet server acl 2000
#
acl basic 2000
rule 1 permit source 192.168.0.46 0
rule 2 permit source 192.168.0.52 0
rule 3 deny
#
line vty 0 63
authentication-mode scheme
user-role network-operator
#
local-user userA class manage
password hash $h$6$I2Sg4Llj1qVUWQZ3$JA6KkU3zfVVRg48MM92X6cVpdiqR2JF887PKi3GQMwn
XXXcsWBuz7GIeJZeeNFMmMBaV7DPkKblnb0sGT2axvg==
service-type telnet
authorization-attribute user-role network-admin
local-user userB class manage
password hash $h$6$q+c3OcSxrPpDpsDf$BWkgfOyxBLyR5zyYgF/+VvN/1ofy81zoHDlFf80OjDl
a6/EiSJbSBl33PeazilSkWSYcttkg5v5bGecB7oYwAw==
service-type telnet
authorization-attribute user-role roleB
#
role name roleB
rule 1 permit read feature
#
Example: Configuring login user command authorization and accounting
Network configuration
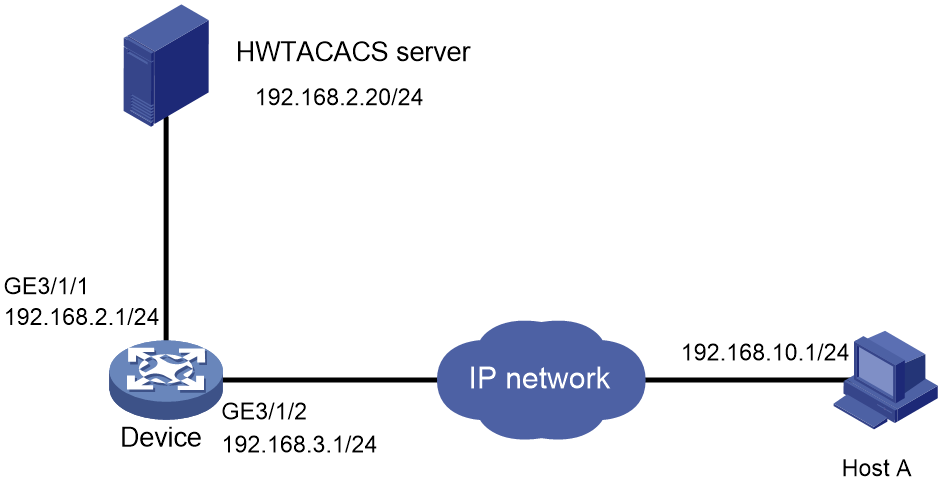
As shown in Figure 3, Host A needs to log in to the device to manage the device.
For device security purposes, configure the device to perform the following tasks:
· Allow Host A to Telnet in after authentication.
· Use the HWTACACS server to control the commands that the user can execute.
· Send commands executed by users to the HWTACACS server to monitor and control user operations on the device.
Analysis
To implement command authorization and accounting, you must perform the following tasks:
· Enable scheme authentication and configure a HWTACACS scheme on the device.
· Configure an account on the HWTACACS server for the Telnet user and assign commands for the user to use.
Restrictions and guidelines
The command authorization function takes effect immediately after you execute the command authorization command. Before executing this command, you must complete the following tasks:
· Configure a user account on the HWTACACS server and specify the commands for the user to use.
· Configure the required HWTACACS scheme on the device.
Procedures
Configuring the HWTACACS server
In this example, the HWTACACS server runs on IMC PLAT 7.1 (E0302) and IMC EIA 7.1 (E0301).
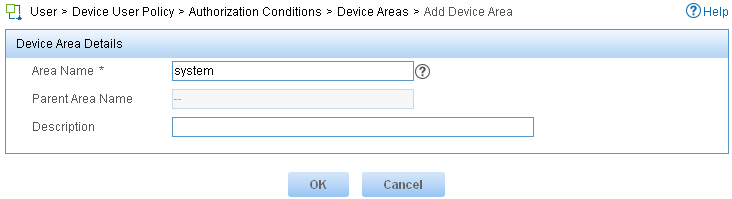
1. Add a device area:
a. Log in to IMC.
b. Click the User tab.
c. From the navigation tree, select Device User Policy > Authorization Conditions > Device Areas.
d. Click Add.
e. Set the area name to system and click OK.
Figure 4 Adding a device area
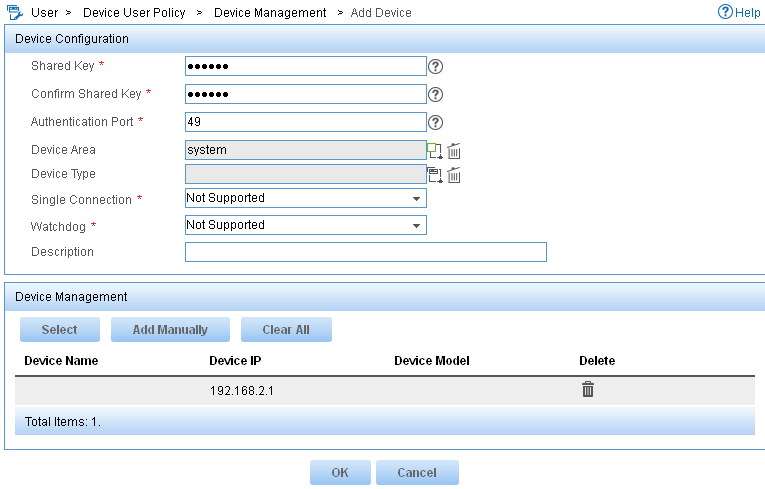
2. Add a device:
a. From the navigation tree, select Device User Policy > Device Management.
b. Click Add.
c. Enter expert for both Shared Key and Confirm Shared Key.
d. Set the authentication port to 49.
e. Select the device area system.
f. Select Not Supported for Single Connection to disable establishing multiple sessions over a single TCP connection.
g. Select Not Supported for Watchdog to disable the device from sending watchdog packets while the user is online.
h. In the Device Management area, click Add Manually.
i. Enter the IP address 192.168.2.1 and click OK.
j. Click OK.
Figure 5 Adding a device
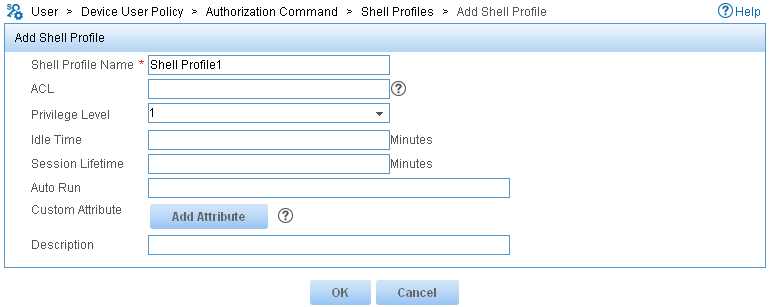
3. Add a shell profile:
a. From the navigation tree, select Device User Policy > Authorization Command > Shell Profiles.
b. Click Add.
c. Enter the profile name Shell Profile1.
d. Select the privilege Level 1.
e. Click OK.
Figure 6 Adding a shell profile
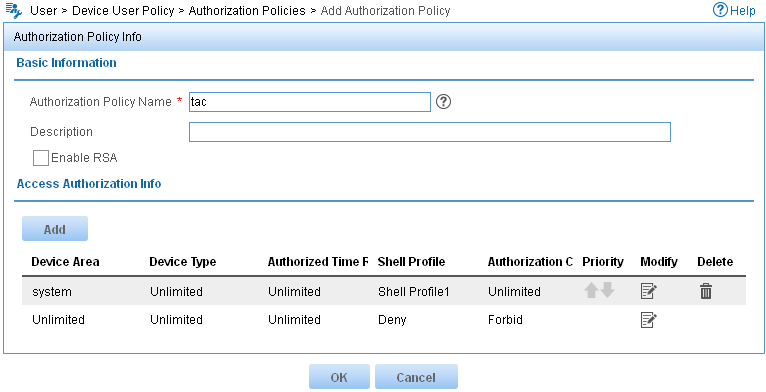
4. Add an authorization policy:
a. From the navigation tree, select Device User Policy > Authorization Policies.
b. Click Add.
c. Enter the policy name tac.
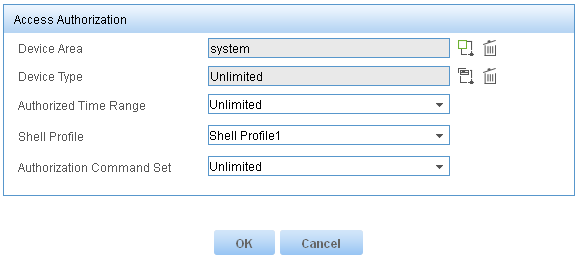
d. In the Access Authorization Info area, click Add to configure access authorization information.
e. Select system for Device Area.
f. Select Unlimited for Device Type and Authorized Time Range.
g. Select the shell profile Shell Profile1.
h. Select Unlimited for Authorization Command Set and click OK.
i. Click OK.
Figure 7 Configuring access authorization information
Figure 8 Adding an authorization policy
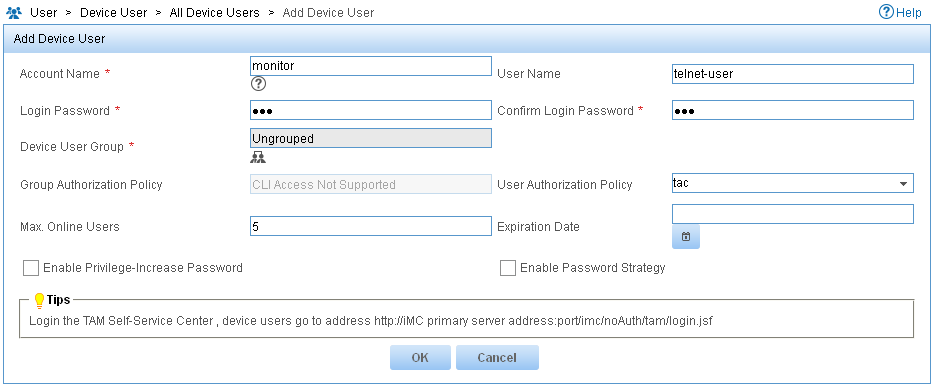
5. Add a device user:
a. From the navigation tree, select Device User > All Device Users.
b. Click Add.
c. Enter the account name monitor and username telnet-user.
d. Enter the login password 123 and confirm the password.
e. Select the user authorization policy tac.
f. Enter 5 for Max. Online Users to limit the number of online users that use the account.
g. Click OK.
Figure 9 Adding a device user
Configuring the device
# Assign IP addresses to relevant interfaces. Make sure the device and the HWTACACS server can reach each other, and the device and Host A can reach each other. (Details not shown.)
# Enable Telnet service.
<Sysname> system-view
[Sysname] telnet server enable
# Create the HWTACACS scheme tac.
[Sysname] hwtacacs scheme tac
# Configure the scheme to use the HWTACACS server at 192.168.2.20:49 for authentication, authorization, and accounting.
[Sysname-hwtacacs-tac] primary authentication 192.168.2.20 49
[Sysname-hwtacacs-tac] primary authorization 192.168.2.20 49
[Sysname-hwtacacs-tac] primary accounting 192.168.2.20 49
# Set the shared keys to expert.
[Sysname-hwtacacs-tac] key authentication simple expert
[Sysname-hwtacacs-tac] key authorization simple expert
[Sysname-hwtacacs-tac] key accounting simple expert
# Remove domain names from usernames sent to the HWTACACS server.
[Sysname-hwtacacs-tac] user-name-format without-domain
[Sysname-hwtacacs-tac] quit
# Configure the system-predefined domain system.
[Sysname] domain name system
# Use the HWTACACS scheme tac for login user authentication, authorization, and accounting. Use local authentication, authorization, and accounting as the backup method.
[Sysname-isp-system] authentication login hwtacacs-scheme tac local
[Sysname-isp-system] authorization login hwtacacs-scheme tac local
[Sysname-isp-system] accounting login hwtacacs-scheme tac local
# Use the HWTACACS scheme tac for command authorization and accounting. Use local authorization as the backup command authorization method.
[Sysname-isp-system] authorization command hwtacacs-scheme tac local
[Sysname-isp-system] accounting command hwtacacs-scheme tac
[Sysname-isp-system] quit
# Create the local user monitor. Set the password to 123 (plain text).
[Sysname] local-user monitor class manage
[Sysname-luser-manage-monitor] password simple 123
# Assign the Telnet service type and the level-1 user role to the user. Reclaim the default user role.
[Sysname-luser-manage-monitor] service-type telnet
[Sysname-luser-manage-monitor] authorization-attribute user-role level-1
[Sysname-luser-manage-monitor] undo authorization-attribute user-role network-operator
[Sysname-luser-manage-monitor] quit
# Enable scheme authentication to use AAA to authenticate the Telnet login user.
[Sysname] line vty 0 63
[Sysname-line-vty0-63] authentication-mode scheme
# Enable command authorization and command accounting.
[Sysname-line-vty0-63] command authorization
[Sysname-line-vty0-63] command accounting
[Sysname-line-vty0-63] quit
Verifying the configuration
1. Verify the command authorization feature:
# Telnet to the device and enter the username monitor and password 123.
C:\Documents and Settings\Administrator> telnet 192.168.1.1
login: monitor
Password:
******************************************************************************
* Copyright (c) 2004-2019 New H3C Technologies Co., Ltd. All rights reserved.*
* Without the owner's prior written consent, *
* no decompiling or reverse-engineering shall be allowed. *
******************************************************************************
<Sysname>
# Enter a question mark (?) to display commands available in user view and system view. Only commands permitted by the level-1 user role are displayed.
<Sysname> ?
User view commands:
display Display current system information
erase Alias for 'delete'
exit Alias for 'quit'
no Alias for 'undo'
ping Ping function
quit Exit from current command view
show Alias for 'display'
ssh2 Establish an Stelnet connection to an Stelnet server
super Switch to a user role
system-view Enter the System View
telnet Establish a telnet connection
tracert Tracert function
write Alias for 'save'
<Sysname> system-view
System View: return to User View with Ctrl+Z.
[Sysname] ?
System view commands:
access-list Alias for 'acl'
display Display current system information
end Alias for 'return'
erase Alias for 'delete'
exit Alias for 'quit'
hostname Alias for 'sysname'
logging Alias for 'info-center'
no Alias for 'undo'
ping Ping function
quit Exit from current command view
return Exit to User View
show Alias for 'display'
tracert Tracert function
write Alias for 'save'
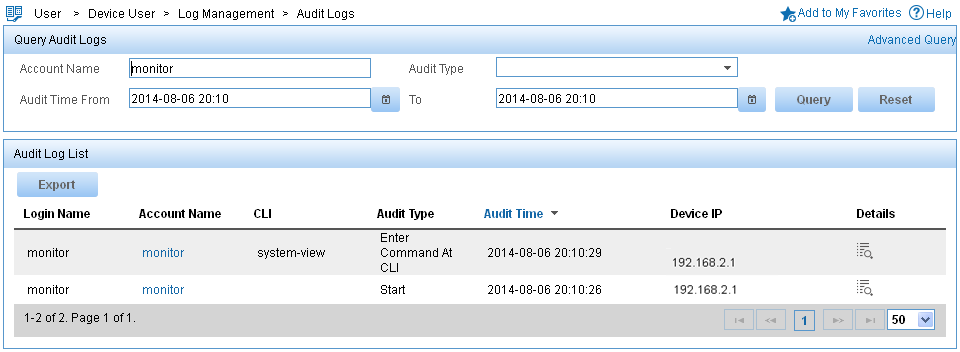
2. Verify the command accounting feature:
a. Log in to IMC.
b. Click the User tab.
c. From the navigation tree, select Device User > Log Management > Audit Logs.
d. In the Query Audit Logs area, enter the account name monitor, select the audit time range, and click Query.
A log for user monitor shows that the user executed the system-view command.
Figure 10 Querying audit logs
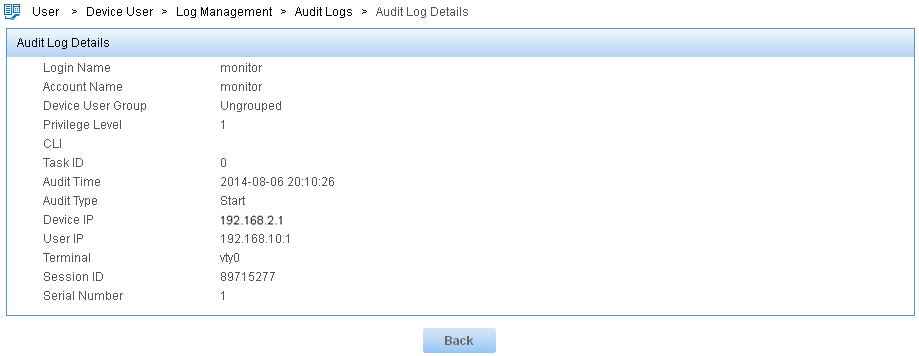
e. Click the Details icon ![]() for
the log of the Start audit type.
for
the log of the Start audit type.
Figure 11 Displaying details about the log of the Start audit type
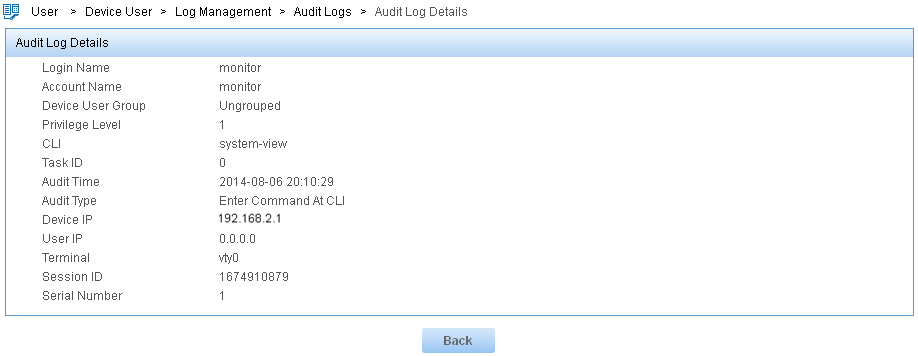
f. Click the Details icon ![]() for
the log of the Enter Command At
CLI audit type.
for
the log of the Enter Command At
CLI audit type.
Figure 12 Displaying details about the log of the Enter Command At CLI audit type
Configuration files
#
telnet server enable
#
hwtacacs scheme tac
primary authentication 192.168.2.20
primary authorization 192.168.2.20
primary accounting 192.168.2.20
key authentication cipher $c$3$Fl1Mn3wBsh+vH6otPvoz+AdE7VaNS3c0Pw==
key authorization cipher $c$3$2x6XI5xU7UGX6VqWFXNp2n3FG07uTNjiQw==
key accounting cipher $c$3$2oKsuCOAZX1+3ibvTPxnJ1YvJ1MHqv73Lw==
user-name-format without-domain
#
domain name system
authentication login hwtacacs-scheme tac local
authorization login hwtacacs-scheme tac local
accounting login hwtacacs-scheme tac local
authorization command hwtacacs-scheme tac local
accounting command hwtacacs-scheme tac
#
local-user monitor class manage
password hash $h$6$5BqWnAJTpBbU5NbY$PbdgF+43eE5WMvj2iHPySfd5nGqj5AhDCDOXTiUMJvR
FFVsZaF8EW1tgpsQPRSq7SDKaGqwHTy9nsabAoGNaYg==
service-type telnet
authorization-attribute user-role level-1
#
line vty 0 63
authentication-mode scheme
user-role network-operator
idle-timeout 0 0
command authorization
command accounting
#
Related documentation
· H3C CR16000-F Routers Fundamentals Configuration Guide-R7951P01
· H3C CR16000-F Routers Fundamentals Command Reference-R7951P01