- Table of Contents
-
- 09-Security Configuration Guide
- 00-Preface
- 01-AAA configuration
- 02-Password control configuration
- 03-Public key management
- 04-PKI configuration
- 05-SSL configuration
- 06-IPsec configuration
- 07-SSH configuration
- 08-IP source guard configuration
- 09-ARP attack protection configuration
- 10-uRPF configuration
- 11-FIPS configuration
- 12-Attack detection and prevention configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 08-IP source guard configuration | 193.89 KB |
Contents
Configuring the IPv4SG feature
Enabling IPv4SG on an interface
Configuring a static IPv4SG binding
Configuring the IPv6SG feature
Enabling IPv6SG on an interface
Configuring a static IPv6SG binding
Displaying and maintaining IPSG
Static IPv4SG configuration example
Dynamic IPv4SG using DHCP snooping configuration example
Dynamic IPv4SG using DHCP relay agent configuration example
Static IPv6SG configuration example
Configuring IP source guard
Overview
IP source guard (IPSG) prevents spoofing attacks by using an IPSG binding table to match legitimate packets. It drops all packets that do not match the table. IPSG is a per-interface packet filter. Configuring the feature on one interface does not affect packet forwarding on another interface.
The IPSG binding table can include global and interface-specific bindings. IPSG first uses the interface-specific bindings to match packets. If no match is found, IPSG uses the global bindings. The IPSG bindings fall into the following types:
· IP.
· MAC.
· IP-MAC.
· IP-VLAN.
· MAC-VLAN.
· IP-MAC-VLAN.
IPSG bindings can be static or dynamic.
· Static bindings—Configured manually. Global IPSG supports only static IP-MAC bindings. For more information about global static IPSG bindings, see "Static IPSG bindings."
· Dynamic bindings—Generated based on information from other modules. For more information about dynamic bindings, see "Dynamic IPSG bindings."
|
|
NOTE: The IPSG feature is available on Layer 2 and Layer 3 Ethernet interfaces and VLAN interfaces. The term "interface" in this chapter collectively refers to these types of interfaces. You can use the port link-mode command to configure an Ethernet port as a Layer 2 or Layer 3 interface (see Layer 2—LAN Switching Configuration Guide). |
As shown in Figure 1, IPSG forwards only the packets that match an IPSG binding.
Figure 1 Diagram for the IPSG feature

Static IPSG bindings
Static IPSG bindings are configured manually. They are suitable for scenarios where few hosts exist on a LAN and their IP addresses are manually configured. For example, you can configure a static IPSG binding on an interface that connects to a server. This binding allows the interface to receive packets only from the server.
Static IPv4SG bindings on an interface implement the following functions:
· Filter IPv4 or IPv6 incoming packets on the interface.
· Cooperate with ARP detection in IPv4 for user validity checking.
For information about ARP detection, see "Configuring ARP attack protection."
Static IPSG bindings can be global or interface-specific.
· Global static binding—Binds the IP address and MAC address in system view. The binding takes effect on all interfaces to filter packets for user spoofing attack prevention.
· Interface-specific static binding—Binds the IP address, MAC address, VLAN, or any combination of the items in interface view. The binding takes effect only on the interface to check the validity of users who are attempting to access the interface.
Dynamic IPSG bindings
IPSG can automatically obtain user information from other modules to generate dynamic bindings. The source modules include DHCP snooping, DHCP relay agent, and DHCP server.
DHCP-based IPSG bindings are suitable for scenarios where hosts on a LAN obtain IP addresses through DHCP. IPSG is configured on the DHCP snooping device or DHCP relay agent. It generates dynamic bindings based on the DHCP snooping entries or DHCP relay entries. IPSG allows only packets from the DHCP clients to pass through.
Dynamic IPv4SG bindings generated based on different source modules are for different usages:
|
Interface types |
Source modules |
Binding usage |
|
Layer 2 Ethernet interface |
DHCP snooping |
Packet filtering. |
|
Layer 3 Ethernet interface VLAN interface |
DHCP relay agent |
Packet filtering. |
|
DHCP server |
For cooperation with modules (such as the ARP detection module) to provide security services. |
For more information about DHCP snooping, DHCP relay, and DHCP server, see Layer 3—IP Services Configuration Guide.
The switch does not support dynamic IPv6SG bindings in the current software version.
IPSG configuration task list
To configure IPv4SG, perform the following tasks:
|
(Required.) Enabling IPv4SG on an interface |
|
(Optional.) Configuring a static IPv4SG binding |
To configure IPv6SG, perform the following tasks:
|
Tasks at a glance |
|
(Required.) Enabling IPv6SG on an interface |
|
(Optional.) Configuring a static IPv6SG binding |
Configuring the IPv4SG feature
You cannot configure the IPv4SG feature on a service loopback interface. If IPv4SG is enabled on an interface, you cannot assign the interface to a service loopback group.
Enabling IPv4SG on an interface
When you enable IPSG on an interface, the static and dynamic IPSG are both enabled.
· Static IPv4SG uses static bindings configured by using the ip source binding command.
· Dynamic IPv4SG generates dynamic bindings from related source modules. IPv4SG uses the bindings to filter incoming IPv4 packets based on the matching criteria specified in the ip verify source command.
To implement dynamic IPv4SG, make sure the DHCP snooping or DHCP relay agent feature operates correctly on the network.
To enable the IPv4SG feature on an interface:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
The following interface types are supported: · Layer 2 Ethernet interface. · Layer 3 Ethernet interface. · VLAN interface. |
|
3. Enable the IPv4SG feature. |
ip verify source { ip-address | ip-address mac-address | mac-address } |
By default, the feature is disabled on an interface. If you configure this command on an interface multiple times, the most recent configuration takes effect. |
Configuring a static IPv4SG binding
You can configure global static and interface-specific static IPv4SG bindings.
Global static bindings take effect on all interfaces.
Interface-specific bindings take priority over global static bindings. An interface first uses the bindings on the interface to match packets. If no match is found, the interface uses the global bindings.
Configuring a global static IPv4SG binding
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Configure a global static IPv4SG binding. |
ip source binding ip-address ip-address mac-address mac-address |
By default, no global static IPv4SG bindings exist. |
Configuring a static IPv4SG binding on an interface
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
The following interface types are supported: · Layer 2 Ethernet interface. · Layer 3 Ethernet interface. · VLAN interface. |
|
3. Configure a static IPv4SG binding. |
ip source binding { ip-address ip-address | ip-address ip-address mac-address mac-address | mac-address mac-address } [ vlan vlan-id ] |
By default, no static IPv4SG bindings exist on an interface. The vlan vlan-id option is supported only in Layer 2 Ethernet interface view. To configure a static IPv4SG binding for the ARP attack detection feature, make sure the following conditions are met: · The ip-address ip-address option, the mac-address mac-address option, and the vlan vlan-id option must be specified. · ARP detection must be enabled for the specified VLAN. For information about ARP detection, see "Configuring ARP attack protection." You can configure the same static IPv4SG binding on different interfaces. |
Configuring the IPv6SG feature
You cannot configure the IPv6SG feature on a service loopback interface. If IPv6SG is enabled on an interface, you cannot assign the interface to a service loopback group.
Enabling IPv6SG on an interface
When you enable IPv6SG on an interface, IPv6SG uses static bindings configured by using the ipv6 source binding command to filter incoming IPv6 packets.
To enable the IPv6SG feature on an interface:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
The following interface types are supported: · Layer 2 Ethernet interface. · Layer 3 Ethernet interface. · VLAN interface. |
|
3. Enable the IPv6SG feature. |
ipv6 verify source { ip-address | ip-address mac-address | mac-address } |
By default, the IPv6SG feature is disabled on an interface. If you configure this command on an interface multiple times, the most recent configuration takes effect. |
Configuring a static IPv6SG binding
You can configure global static and interface-specific static IPv6SG bindings.
Global static bindings take effect on all interfaces.
Interface-specific static bindings take priority over global static bindings. An interface first uses the bindings on the interface to match packets. If no match is found, the interface uses the global bindings.
Configuring a global static IPv6SG binding
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Configure a global static IPv6SG binding. |
ipv6 source binding ip-address ipv6-address mac-address mac-address |
By default, no global static IPv6SG bindings exist. |
Configuring a static IPv6SG binding on an interface
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
The following interface types are supported: · Layer 2 Ethernet interface. · Layer 3 Ethernet interface. · VLAN interface. |
|
3. Configure a static IPv6SG binding. |
ipv6 source binding { ip-address ipv6-address | ip-address ipv6-address mac-address mac-address | mac-address mac-address } [ vlan vlan-id ] |
By default, no static IPv6SG bindings exist on an interface. The vlan vlan-id option is supported only in Layer 2 Ethernet interface view. You can configure the same static IPv6SG binding on different interfaces. |
Displaying and maintaining IPSG
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display IPv4SG bindings (in standalone mode). |
display ip source binding [ static | [ vpn-instance vpn-instance-name ] [ dhcp-relay | dhcp-server | dhcp-snooping ] ] [ ip-address ip-address ] [ mac-address mac-address ] [ vlan vlan-id ] [ interface interface-type interface-number ] [ slot slot-number ] |
|
Display IPv4SG bindings (in IRF mode). |
display ip source binding [ static | [ vpn-instance vpn-instance-name ] [ dhcp-relay | dhcp-server | dhcp-snooping ] ] [ ip-address ip-address ] [ mac-address mac-address ] [ vlan vlan-id ] [ interface interface-type interface-number ] [ chassis chassis-number slot slot-number ] |
|
Display IPv6SG bindings (in standalone mode). |
|
|
Display IPv6SG bindings (in IRF mode). |
display ipv6 source binding [ static ] [ ip-address ipv6-address ] [ mac-address mac-address ] [ vlan vlan-id ] [ interface interface-type interface-number ] [ chassis chassis-number slot slot-number ] |
IPSG configuration examples
Static IPv4SG configuration example
Network requirements
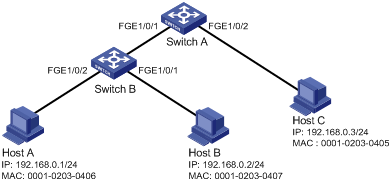
As shown in Figure 2, all hosts use static IP addresses.
Configure static IPv4SG bindings on Switch A and Switch B to meet the following requirements:
· FortyGigE 1/0/2 of Switch A allows only IP packets from Host C to pass.
· FortyGigE 1/0/1 of Switch A allows only IP packets from Host A to pass.
· All interfaces of Switch B allow IP packets from Host A to pass.
· FortyGigE 1/0/1 of Switch B allows IP packets from Host B to pass.
Configuration procedure
1. Configure Switch A:
# Configure IP addresses for the interfaces. (Details not shown.)
# Enable IPv4SG on FortyGigE 1/0/2.
<SwitchA> system-view
[SwitchA] interface fortygige 1/0/2
[SwitchA-FortyGigE1/0/2] ip verify source ip-address mac-address
# On FortyGigE 1/0/2, configure a static IPv4SG binding for Host C.
[SwitchA-FortyGigE1/0/2] ip source binding ip-address 192.168.0.3 mac-address 0001-0203-0405
[SwitchA-FortyGigE1/0/2] quit
# Enable IPv4SG on FortyGigE 1/0/1.
[SwitchA] interface fortygige 1/0/1
[SwitchA-FortyGigE1/0/1] ip verify source ip-address mac-address
# On FortyGigE 1/0/1, configure a static IPv4SG binding for Host A.
[SwitchA-FortyGigE1/0/1] ip source binding ip-address 192.168.0.1 mac-address 0001-0203-0406
[SwitchA-FortyGigE1/0/1] quit
2. Configure Switch B:
# Configure an IP address for each interface. (Details not shown.)
# Enable IPv4SG on FortyGigE 1/0/2.
<SwitchB> system-view
[SwitchB] interface fortygige 1/0/2
[SwitchB-FortyGigE1/0/2] ip verify source ip-address mac-address
[SwitchB-FortyGigE1/0/2] quit
# Configure a static IPv4SG binding for Host A.
[SwitchB] ip source binding ip-address 192.168.0.1 mac-address 0001-0203-0406
# Enable IPv4SG on FortyGigE 1/0/1.
[SwitchB] interface fortygige 1/0/1
[SwitchB-FortyGigE1/0/1] ip verify source ip-address mac-address
# On FortyGigE 1/0/1, configure a static IPv4SG binding for Host B.
[SwitchB-FortyGigE1/0/1] ip source binding mac-address 0001-0203-0407
[SwitchB-FortyGigE1/0/1] quit
Verifying the configuration
# Verify that the static IPv4SG bindings are configured successfully on Switch A.
<SwitchA> display ip source binding static
Total entries found: 2
IP Address MAC Address Interface VLAN Type
192.168.0.1 0001-0203-0405 FGE1/0/2 N/A Static
192.168.0.3 0001-0203-0406 FGE1/0/1 N/A Static
# Verify that the static IPv4SG bindings are configured successfully on Switch B.
<SwitchB> display ip source binding static
Total entries found: 2
IP Address MAC Address Interface VLAN Type
192.168.0.1 0001-0203-0406 N/A N/A Static
N/A 0001-0203-0407 FGE1/0/1 N/A Static
Dynamic IPv4SG using DHCP snooping configuration example
Network requirements
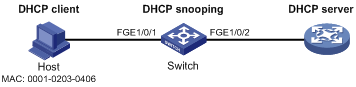
As shown in Figure 3, the host (the DHCP client) obtains an IP address from the DHCP server. Perform the following tasks:
· Enable DHCP snooping on the switch to make sure the DHCP client obtains an IP address from the authorized DHCP server. To generate a DHCP snooping entry for the DHCP client, enable recording of client information in DHCP snooping entries.
· Enable dynamic IPv4SG on FortyGigE 1/0/1 to filter incoming packets by using the IPv4SG bindings generated based on DHCP snooping entries. Only packets from the DHCP client are allowed to pass.
Configuration procedure
1. Configure the DHCP server:
For information about DHCP server configuration, see Layer 3—IP Services Configuration Guide.
2. Configure the device:
# Configure IP addresses for the interfaces. (Details not shown.)
# Enable DHCP snooping.
<Switch> system-view
[Switch] dhcp snooping enable
# Configure FortyGigE 1/0/2 as a trusted interface.
[Switch] interface fortygige 1/0/2
[Switch-FortyGigE1/0/2] dhcp snooping trust
[Switch-FortyGigE1/0/2] quit
# Enable IPv4SG on FortyGigE 1/0/1 and verify the source IP address and MAC address for dynamic IPSG.
[Switch] interface fortygige 1/0/1
[Switch-FortyGigE1/0/1] ip verify source ip-address mac-address
# Enable recording of client information in DHCP snooping entries on FortyGigE 1/0/1.
[Switch-FortyGigE1/0/1] dhcp snooping binding record
[Switch-FortyGigE1/0/1] quit
Verifying the configuration
# Verify that a dynamic IPv4SG binding is generated based on a DHCP snooping entry.
[Switch] display ip source binding dhcp-snooping
Total entries found: 1
IP Address MAC Address Interface VLAN Type
192.168.0.1 0001-0203-0406 FGE1/0/1 1 DHCP snooping
Dynamic IPv4SG using DHCP relay agent configuration example
Network requirements
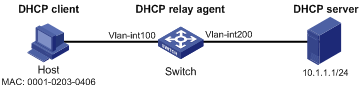
As shown in Figure 4, DHCP relay is enabled on the switch. The host obtains an IP address from the DHCP server through the DHCP relay agent.
Enable dynamic IPv4SG on VLAN-interface 100 to filter received packets based on the DHCP relay entry generated on the switch.
Configuration procedure
1. Configure dynamic IPv4SG:
# Configure IP addresses for the interfaces. (Details not shown.)
# Enable IPv4SG on VLAN-interface 100 and verify the source IP address and MAC address for dynamic IPSG.
<Switch> system-view
[Switch] interface vlan-interface 100
[Switch-Vlan-interface100] ip verify source ip-address mac-address
[Switch-Vlan-interface100] quit
2. Configure the DHCP relay agent:
# Enable the DHCP service.
[Switch] dhcp enable
# Enable recording DHCP relay client entries.
[Switch] dhcp relay client-information record
# Configure VLAN-interface 100 to work in DHCP relay mode.
[Switch] interface vlan-interface 100
[Switch-Vlan-interface100] dhcp select relay
# Specify the IP address of the DHCP server.
[Switch-Vlan-interface100] dhcp relay server-address 10.1.1.1
[Switch-Vlan-interface100] quit
Verifying the configuration
# Verify that a dynamic IPv4SG binding is generated based on a DHCP relay entry.
[Switch] display ip source binding dhcp-relay
Total entries found: 1
IP Address MAC Address Interface VLAN Type
192.168.0.1 0001-0203-0406 Vlan100 100 DHCP relay
Static IPv6SG configuration example
Network requirements
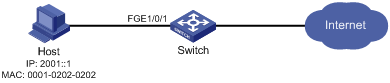
As shown in Figure 5, configure a static IPv6SG binding for FortyGigE 1/0/1 of the device to allow only IPv6 packets from the host to pass.
Configuration procedure
# Enable IPv6SG on FortyGigE 1/0/1.
<Switch> system-view
[Switch] interface fortygige 1/0/1
[Switch-FortyGigE1/0/1] ipv6 verify source ip-address mac-address
# On FortyGigE1/0/1, configure a static IPv6SG binding for the host.
[Switch-FortyGigE1/0/1] ipv6 source binding ip-address 2001::1 mac-address 0001-0202-0202
[Switch-FortyGigE1/0/1] quit
Verifying the configuration
# Verify that the static IPv6SG binding is configured successfully on the switch.
[Switch] display ipv6 source binding static
Total entries found: 1
IPv6 Address MAC Address Interface VLAN Type
2001::1 0001-0202-0202 FGE1/0/1 N/A Static