- Table of Contents
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 01-ARP configuration | 232.56 KB |
Command and hardware compatibility
Configuring a static ARP entry
Setting the maximum number of dynamic ARP entries for a device
Setting the maximum number of dynamic ARP entries for an interface
Setting the aging timer for dynamic ARP entries
Enabling dynamic ARP entry check
Displaying and maintaining ARP
Gratuitous ARP packet learning
Periodic sending of gratuitous ARP packets
Enabling IP conflict notification
Common proxy ARP configuration example
Feature and hardware compatibility
ARP fast-reply configuration example
Configuring ARP
Overview
ARP resolves IP addresses into MAC addresses on Ethernet networks.
ARP message format
ARP uses two types of messages: ARP request and ARP reply. Figure 1 shows the format of ARP request/reply messages. Numbers in the figure refer to field lengths.
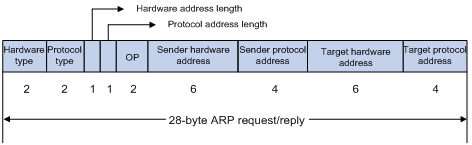
· Hardware type—Hardware address type. The value 1 represents Ethernet.
· Protocol type—Type of the protocol address to be mapped. The hexadecimal value 0x0800 represents IP.
· Hardware address length and protocol address length—Length, in bytes, of a hardware address and a protocol address. For an Ethernet address, the value of the hardware address length field is 6. For an IPv4 address, the value of the protocol address length field is 4.
· OP—Operation code, which describes the type of ARP message. The value 1 represents an ARP request, and the value 2 represents an ARP reply.
· Sender hardware address—Hardware address of the device sending the message.
· Sender protocol address—Protocol address of the device sending the message.
· Target hardware address—Hardware address of the device to which the message is being sent.
· Target protocol address—Protocol address of the device to which the message is being sent.
ARP operating mechanism
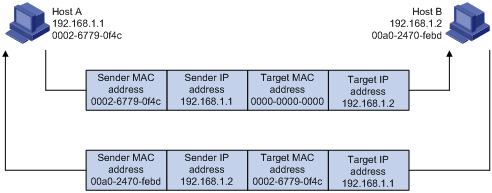
As shown in Figure 2, Host A and Host B are on the same subnet. Host A sends a packet to Host B as follows:
1. Host A looks through the ARP table for an ARP entry for Host B. If one entry is found, Host A uses the MAC address in the entry to encapsulate the IP packet into a data link layer frame. Then Host A sends the frame to Host B.
2. If Host A finds no entry for Host B, Host A buffers the packet and broadcasts an ARP request. The payload of the ARP request contains the following information:
¡ Sender IP address and sender MAC address—Host A's IP address and MAC address.
¡ Target IP address—Host B's IP address.
¡ Target MAC address—An all-zero MAC address.
All hosts on this subnet can receive the broadcast request, but only the requested host (Host B) processes the request.
3. Host B compares its own IP address with the target IP address in the ARP request. If they are the same, Host B operates as follows:
a. Adds the sender IP address and sender MAC address into its ARP table.
b. Encapsulates its MAC address into an ARP reply.
c. Unicasts the ARP reply to Host A.
4. After receiving the ARP reply, Host A operates as follows:
a. Adds the MAC address of Host B into its ARP table.
b. Encapsulates the MAC address into the packet and sends the packet to Host B.
Figure 2 ARP address resolution process
If Host A and Host B are on different subnets, Host A sends a packet to Host B as follows:
1. Host A broadcasts an ARP request where the target IP address is the IP address of the gateway.
2. The gateway responds with its MAC address in an ARP reply to Host A.
3. Host A uses the gateway's MAC address to encapsulate the packet, and then sends the packet to the gateway.
4. If the gateway has an ARP entry for Host B, it forwards the packet to Host B directly. If not, the gateway broadcasts an ARP request, in which the target IP address is the IP address of Host B.
5. After the gateway gets the MAC address of Host B, it sends the packet to Host B.
ARP table
An ARP table stores dynamic and static ARP entries.
Dynamic ARP entry
ARP automatically creates and updates dynamic entries. A dynamic ARP entry is removed when its aging timer expires or the output interface goes down. In addition, a dynamic ARP entry can be overwritten by a static ARP entry.
Static ARP entry
A static ARP entry is manually configured and maintained. It does not age out and cannot be overwritten by any dynamic ARP entry.
Static ARP entries protect communication between devices because attack packets cannot modify the IP-to-MAC mapping in a static ARP entry.
The device supports the following types of static ARP entries:
· Long static ARP entry—It contains the IP address, MAC address, VLAN, and output interface.
A long static ARP entry is directly used for forwarding packets.
· Short static ARP entry—It contains only the IP address and MAC address.
¡ If the output interface is a Layer 3 Ethernet interface, the short ARP entry can be directly used to forward packets.
¡ If the output interface is a VLAN interface, the device sends an ARP request whose target IP address is the IP address in the short entry. If the sender IP and MAC addresses in the received ARP reply match the short static ARP entry, the device performs the following operations:
- Adds the interface that received the ARP reply to the short static ARP entry.
- Uses the resolved short static ARP entry to forward IP packets.
To communicate with a host by using a fixed IP-to-MAC mapping, configure a short static ARP entry on the device. To communicate with a host by using a fixed IP-to-MAC mapping through an interface in a VLAN, configure a long static ARP entry on the device.
Command and hardware compatibility
The WX1800H series, WX2500H series, and WX3000H series access controllers do not support the slot keyword or the slot-number argument.
Configuring a static ARP entry
A static ARP entry is effective when the device functions correctly. If a VLAN or VLAN interface is deleted, long static ARP entries in the VLAN are deleted, and resolved short static ARP entries in the VLAN become unresolved.
A resolved short static ARP entry becomes unresolved upon certain events. For example, it becomes unresolved when the resolved output interface goes down.
A long static ARP entry is ineffective in either of the following situations:
· The IP address in the entry conflicts with a local IP address.
· No local interface has an IP address in the same subnet as the IP address in the ARP entry.
To configure a static ARP entry:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Configure a static ARP entry. |
· Configure a long static ARP entry: · Configure a short static ARP entry: |
By default, no static ARP entry is configured. |
Setting the maximum number of dynamic ARP entries for a device
A device can dynamically learn ARP entries. To prevent a device from holding too many ARP entries, you can set the maximum number of dynamic ARP entries that the device can learn. When the maximum number is reached, the device stops learning ARP entries.
If you set a value lower than the number of existing dynamic ARP entries, the device does not remove the existing entries unless they are aged out.
To set the maximum number of dynamic ARP entries for a device:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Set the maximum number of dynamic ARP entries for the device. |
arp max-learning-number number slot slot-number |
By default, the maximum number of dynamic ARP entries varies by device model. For more information, see Layer 3—IP Services Command Reference. To disable the device from learning dynamic ARP entries, set the number to 0. |
Setting the maximum number of dynamic ARP entries for an interface
An interface can dynamically learn ARP entries. To prevent an interface from holding too many ARP entries, you can set the maximum number of dynamic ARP entries that the interface can learn. When the maximum number is reached, the interface stops learning ARP entries.
You can set limits for both a Layer 2 interface and the VLAN interface for a permitted VLAN on the Layer 2 interface. The Layer 2 interface learns an ARP entry only when neither limit is reached.
To set the maximum number of dynamic ARP entries for an interface:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Set the maximum number of dynamic ARP entries for the interface. |
arp max-learning-num number |
By default, the maximum number of dynamic ARP entries varies by device model. For more information, see Layer 3—IP Services Command Reference. To disable the interface from learning dynamic ARP entries, set the number to 0. |
Setting the aging timer for dynamic ARP entries
Each dynamic ARP entry in the ARP table has a limited lifetime, called an aging timer. The aging timer of a dynamic ARP entry is reset each time the dynamic ARP entry is updated. A dynamic ARP entry that is not updated before its aging timer expires is deleted from the ARP table.
To set the aging timer for dynamic ARP entries:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Set the aging timer for dynamic ARP entries. |
arp timer aging aging-time |
The default setting is 20 minutes. |
Enabling dynamic ARP entry check
The dynamic ARP entry check feature disables the device from supporting dynamic ARP entries that contain multicast MAC addresses. The device cannot learn dynamic ARP entries containing multicast MAC addresses. You cannot manually add static ARP entries containing multicast MAC addresses.
When dynamic ARP entry check is disabled, ARP entries containing multicast MAC addresses are supported. The device can learn dynamic ARP entries containing multicast MAC addresses obtained from the ARP packets sourced from a unicast MAC address. You can also manually add static ARP entries containing multicast MAC addresses.
To enable dynamic ARP entry check:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable dynamic ARP entry check. |
arp check enable |
By default, dynamic ARP entry check is enabled. |
Enabling ARP logging
This feature enables a device to log ARP events when ARP cannot resolve IP addresses correctly. The device can log the following ARP events:
· On a proxy ARP-disabled interface, the target IP address of a received ARP packet is not one of the following IP addresses:
¡ The IP address of the receiving interface.
¡ The public IP address after NAT.
· The sender IP address of a received ARP reply conflicts with one of the following IP addresses:
¡ The IP address of the receiving interface.
¡ The public IP address after NAT.
The device sends ARP log messages to the information center. You can use the info-center source command to specify the log output rules for the information center. For more information about information center, see Network Management and Monitoring Configuration Guide.
To enable the ARP logging feature:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable the ARP logging feature. |
arp check log enable |
By default, ARP logging is disabled. |
Displaying and maintaining ARP
|
|
IMPORTANT: Clearing ARP entries from the ARP table might cause communication failures. Make sure the entries to be cleared do not affect current communications. |
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display ARP entries. |
display arp [ [ all | dynamic | static ] [ slot slot-number ] | vlan vlan-id | interface interface-type interface-number ] [ count | verbose ] |
|
Display the ARP entry for an IP address. |
display arp ip-address [ slot slot-number ] [ verbose ] |
|
Display the aging timer of dynamic ARP entries. |
display arp timer aging |
|
Clear ARP entries from the ARP table. |
reset arp { all | dynamic | interface interface-type interface-number | slot slot-number | static } |
Configuring gratuitous ARP
Overview
In a gratuitous ARP packet, the sender IP address and the target IP address are the IP address of the sending device.
A device sends a gratuitous ARP packet for either of the following purposes:
· Determine whether its IP address is already used by another device. If the IP address is already used, the device is informed of the conflict by an ARP reply.
· Inform other devices of a MAC address change.
Gratuitous ARP packet learning
This feature enables a device to create or update ARP entries by using the sender IP and MAC addresses in received gratuitous ARP packets.
When this feature is disabled, the device uses received gratuitous ARP packets to update existing ARP entries only. ARP entries are not created based on the received gratuitous ARP packets, which saves ARP table space.
Periodic sending of gratuitous ARP packets
Enabling periodic sending of gratuitous ARP packets helps downstream devices update ARP entries or MAC entries in a timely manner.
This feature can implement the following functions:
· Prevent gateway spoofing.
Gateway spoofing occurs when an attacker uses the gateway address to send gratuitous ARP packets to the hosts on a network. The traffic destined for the gateway from the hosts is sent to the attacker instead. As a result, the hosts cannot access the external network.
To prevent such gateway spoofing attacks, you can enable the gateway to send gratuitous ARP packets at intervals. Gratuitous ARP packets contain the primary IP address and manually configured secondary IP addresses of the gateway, so hosts can learn correct gateway information.
· Prevent ARP entries from aging out.
If network traffic is heavy or if the host CPU usage is high, received ARP packets can be discarded or are not promptly processed. Eventually, the dynamic ARP entries on the receiving host age out. The traffic between the host and the corresponding devices is interrupted until the host re-creates the ARP entries.
To prevent this problem, you can enable the gateway to send gratuitous ARP packets periodically. Gratuitous ARP packets contain the primary IP address and manually configured secondary IP addresses of the gateway, so the receiving hosts can update ARP entries in a timely manner.
Configuration procedure
When you configure gratuitous ARP, follow these restrictions and guidelines:
· You can enable periodic sending of gratuitous ARP packets on a maximum of 1024 interfaces.
· Periodic sending of gratuitous ARP packets takes effect on an interface only when the following conditions are met:
¡ The data link layer state of the interface is up.
¡ The interface has an IP address.
· If you change the sending interval for gratuitous ARP packets, the configuration takes effect at the next sending interval.
· The sending interval for gratuitous ARP packets might be much longer than the specified sending interval in any of the following circumstances:
¡ This feature is enabled on multiple interfaces.
¡ Each interface is configured with multiple secondary IP addresses.
¡ A small sending interval is configured when the previous two conditions exist.
To configure gratuitous ARP:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable learning of gratuitous ARP packets. |
gratuitous-arp-learning enable |
By default, learning of gratuitous ARP packets is enabled. |
|
3. Enable the device to send gratuitous ARP packets upon receiving ARP requests whose sender IP address belongs to a different subnet. |
gratuitous-arp-sending enable |
By default, a device does not send gratuitous ARP packets upon receiving ARP requests whose sender IP address belongs to a different subnet. |
|
4. Enter interface view. |
interface interface-type interface-number |
N/A |
|
5. Enable periodic sending of gratuitous ARP packets. |
arp send-gratuitous-arp [ interval milliseconds ] |
By default, periodic sending of gratuitous ARP packets is disabled. |
Enabling IP conflict notification
By default, if the sender IP address of an ARP packet is being used by the receiving device, the receiving device sends a gratuitous ARP request. It also displays an error message after it receives an ARP reply about the conflict.
You can use this command to enable the device to display error messages before sending a gratuitous ARP reply or request for conflict confirmation.
To enable IP conflict notification:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable IP conflict notification. |
arp ip-conflict log prompt |
By default, IP conflict notification is disabled. |
Configuring proxy ARP
Proxy ARP enables a device on one network to answer ARP requests for an IP address on another network. With proxy ARP, hosts on different broadcast domains can communicate with each other as they would on the same broadcast domain.
Proxy ARP includes common proxy ARP and local proxy ARP.
· Common proxy ARP—Allows communication between hosts that connect to different Layer 3 interfaces and reside in different broadcast domains.
· Local proxy ARP—Allows communication between hosts that connect to the same Layer 3 interface and reside in different broadcast domains.
Enabling common proxy ARP
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
The following interface types are supported: · VLAN interface. · Layer 3 Ethernet interface. · Layer 3 Ethernet subinterface. |
|
3. Enable common proxy ARP. |
proxy-arp enable |
By default, common proxy ARP is disabled. |
Enabling local proxy ARP
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
The following interface types are supported: · VLAN interface. · Layer 3 Ethernet interface. · Layer 3 Ethernet subinterface. |
|
3. Enable local proxy ARP. |
local-proxy-arp enable [ ip-range startIP to endIP ] |
By default, local proxy ARP is disabled. |
Displaying proxy ARP
Execute display commands in any view.
|
Task |
Command |
|
Display common proxy ARP status. |
display proxy-arp [ interface interface-type interface-number ] |
|
Display local proxy ARP status. |
display local-proxy-arp [ interface interface-type interface-number ] |
Common proxy ARP configuration example
Network requirements
As shown in Figure 3, Client 1 and Client 2 have the same IP prefix and mask, but they are located on different subnets separated by the switch. Client 1 belongs to VLAN 10, and Client 2 belongs to VLAN 20. No default gateway is configured on Client 1 and Client 2.
Configure common proxy ARP on the AC to enable communication between the two clients.
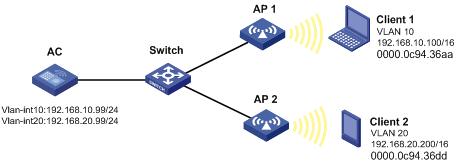
Configuration procedure
# Create VLAN 10 and VLAN 20.
<AC> system-view
[AC] vlan 10
[AC-vlan10] quit
[AC] vlan 20
[AC-vlan20] quit
# Configure the IP address of VLAN-interface 10.
[AC] interface vlan-interface 10
[AC-Vlan-interface10] ip address 192.168.10.99 255.255.255.0
# Enable common proxy ARP on VLAN-interface 10.
[AC-Vlan-interface10] proxy-arp enable
[AC-Vlan-interface10] quit
# Configure the IP address of VLAN-interface 20.
[AC] interface vlan-interface 20
[AC-Vlan-interface20] ip address 192.168.20.99 255.255.255.0
# Enable common proxy ARP on VLAN-interface 20.
[AC-Vlan-interface20] proxy-arp enable
Verifying the configuration
# Verify that Client 1 and Client 2 can ping each other.
Configuring ARP fast-reply
Overview
ARP fast-reply enables a device to directly answer ARP requests according to DHCP snooping entries. ARP fast-reply functions in a VLAN. For information about DHCP snooping, see "Configuring DHCP snooping."
If the target IP address of a received ARP request is the IP address of the VLAN interface, the device delivers the request to the ARP module. If not, the device takes the following steps to process the packet:
1. Search the DHCP snooping table for a match by using the target IP address.
2. If a match is found, whether the device returns a reply depends on the type of interface in the matching entry.
¡ If the interface is the Ethernet interface that received the ARP request, the device does not return any reply.
¡ If the interface is a wireless interface or an Ethernet interface other than the receiving interface, the device returns a reply according to the matching entry.
3. If no matching DHCP snooping entry is found, the ARP request is forwarded to other interfaces except the receiving interface in the VLAN, or delivered to other modules.
Feature and hardware compatibility
|
Hardware series |
Model |
ARP fast-reply compatibility |
|
WX1800H series |
WX1804H WX1810H WX1820H |
Yes |
|
WX2500H series |
WX2510H WX2540H WX2560H |
Yes |
|
WX3000H series |
WX3010H WX3010H-L WX3010H-X WX3024H WX3024H-L |
Yes: · WX3010H-X No: · WX3010H · WX3010H-L · WX3024H · WX3024H-L |
|
WX3500H series |
WX3508H WX3510H WX3520H WX3540H |
Yes |
|
WX5500E series |
WX5510E WX5540E |
Yes |
|
WX5500H series |
WX5540H WX5560H WX5580H |
Yes |
|
Access controller modules |
EWPXM1MAC0F EWPXM1WCME0 EWPXM2WCMD0F LSQM1WCMX20 LSQM1WCMX40 LSUM1WCME0 LSUM1WCMX20RT LSUM1WCMX40RT |
Yes |
Configuration procedure
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VLAN view. |
vlan vlan-id |
N/A |
|
3. Enable ARP fast-reply. |
arp fast-reply enable |
By default, ARP fast-reply is disabled. |
ARP fast-reply configuration example
Network requirements
As shown in Figure 4, all clients are in VLAN 2, and access the network through the switch. APs are connected to VLAN 2. They have obtained IP addresses through DHCP.
Enable ARP fast-reply for VLAN 2. The AC directly returns an ARP reply without broadcasting received ARP requests to other APs upon receiving an ARP request from a client.
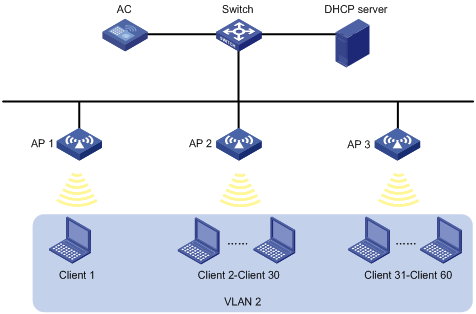
Configuration procedure
1. Configure basic functions on the AC. For more information about the configuration, see WLAN Configuration Guide.
2. Enable ARP fast-reply for VLAN 2 on the AC.
[AC] vlan 2
[AC-vlan2] arp fast-reply enable
[AC-vlan2] quit
