- Table of Contents
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 01-Mulitcast Overview | 215.28 KB |
Contents
Information transmission techniques
Advantages and applications of multicast
Multicast packet forwarding mechanism
|
|
NOTE: Unless otherwise stated, the term multicast in this document refers to IP multicast. |
Introduction to multicast
As a technique that coexists with unicast and broadcast, the multicast technique effectively addresses the issue of point-to-multipoint data transmission. By enabling high-efficiency point-to-multipoint data transmission over a network, multicast greatly saves network bandwidth and reduces network load.
By using multicast technology, a network operator can easily provide new value-added services, such as live webcasting, web TV, distance learning, telemedicine, web radio, real-time video conferencing, and other bandwidth-critical and time-critical information services.
Information transmission techniques
The information transmission techniques include unicast, broadcast, and multicast.
Unicast
In unicast transmission, the information source must send a separate copy of information to each host that needs the information.
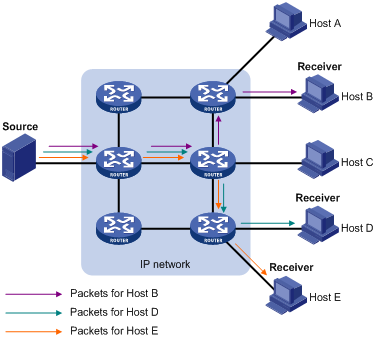
In Figure 1, assume that Host B, Host D and Host E need the information. A separate transmission channel must be established from the information source to each of these hosts.
In unicast transmission, the traffic transmitted over the network is proportional to the number of hosts that need the information. If a large number of hosts need the information, the information source must send a separate copy of the same information to each of these hosts. Sending many copies can place a tremendous pressure on the information source and the network bandwidth.
Unicast is not suitable for batch transmission of information.
Broadcast
In broadcast transmission, the information source sends information to all hosts on the subnet, even if some hosts do not need the information.
Figure 2 Broadcast transmission

In Figure 2, assume that only Host B, Host D, and Host E need the information. If the information is broadcast to the subnet, Host A and Host C also receive it. In addition to information security issues, broadcasting to hosts that do not need the information also causes traffic flooding on the same subnet.
Broadcast is disadvantageous in transmitting data to specific hosts. Moreover, broadcast transmission is a significant waste of network resources.
Multicast
Unicast and broadcast techniques cannot provide point-to-multipoint data transmissions with the minimum network consumption.
Multicast transmission can solve this problem. When some hosts on the network need multicast information, the information sender, or multicast source, sends only one copy of the information. Multicast distribution trees are built through multicast routing protocols, and the packets are replicated only on nodes where the trees branch.
Figure 3 Multicast transmission

The multicast source sends only one copy of the information to a multicast group. Host B, Host D and Host E, which are receivers of the information, must join the multicast group. The routers on the network duplicate and forward the information based on the distribution of the group members. Finally, the information is correctly delivered to Host B, Host D, and Host E.
To summarize, multicast has the following advantages:
· Over unicast—Because multicast traffic flows to the farthest-possible node from the source before it is replicated and distributed, an increase in the number of hosts will not increase the load of the source and will not remarkably add to the usage of network resources.
· Over broadcast—Because multicast data is sent only to the receivers that need it, multicast uses network bandwidth reasonably and enhances network security. In addition, data broadcast is confined to the same subnet, but multicast is not.
Features of multicast
Multicast transmission has the following features:
· A multicast group is a multicast receiver set identified by an IP multicast address. Hosts join a multicast group to become members of the multicast group, before they can receive the multicast data addressed to that multicast group. Typically, a multicast source does not need to join a multicast group.
· An information sender is called a “multicast source”. A multicast source can send data to multiple multicast groups at the same time, and multiple multicast sources can send data to the same multicast group at the same time.
· All hosts that have joined a multicast group become members of the multicast group. The group memberships are dynamic. Hosts can join or leave multicast groups at any time. Multicast groups are not subject to geographic restrictions.
For a better understanding of the multicast concept, you can compare multicast transmission to the transmission of TV programs.
Table 1 An analogy between TV transmission and multicast transmission
|
TV transmission |
Multicast transmission |
|
A TV station transmits a TV program through a channel. |
A multicast source sends multicast data to a multicast group. |
|
A user tunes the TV set to the channel. |
A receiver joins the multicast group. |
|
The user starts to watch the TV program transmitted by the TV station via the channel. |
The receiver starts to receive the multicast data that the source is sending to the multicast group. |
|
The user turns off the TV set or tunes to another channel. |
The receiver leaves the multicast group or joins another group. |
Common notations in multicast
The following notations are commonly used in multicast transmission:
· (*, G)—Indicates a rendezvous point tree (RPT), or a multicast packet that any multicast source sends to multicast group G. Here, the asterisk represents any multicast source, and “G” represents a specific multicast group.
· (S, G)—Indicates a shortest path tree (SPT), or a multicast packet that multicast source S sends to multicast group G. Here, “S” represents a specific multicast source, and “G” represents a specific multicast group.
Advantages and applications of multicast
Advantages of multicast
Advantages of the multicast technique include the following:
· Enhanced efficiency—Reduces the CPU load of information source servers and network devices
· Optimal performance—Reduces redundant traffic
· Distributed application—Enables point-to-multipoint applications at the price of minimum network resources
Applications of multicast
The scenarios in which the multicast technique can be effectively applied are:
· Multimedia and streaming applications, such as web TV, web radio, and real-time video/audio conferencing
· Communication for training and cooperative operations, such as distance learning and telemedicine
· Data warehouse and financial applications (stock quotes)
· Any other point-to-multipoint application for data distribution
Multicast models
Based on how the receivers treat the multicast sources, the multicast models include any-source multicast (ASM), source-filtered multicast (SFM), and source-specific multicast (SSM).
ASM model
In the ASM model, any sender can send information to a multicast group as a multicast source, and receivers can join a multicast group identified by a group address, and obtain multicast information addressed to that multicast group. In this model, receivers do not know the positions of the multicast sources in advance. However, they can join or leave the multicast group at any time.
SFM model
The SFM model is derived from the ASM model. To a sender, the two models appear to have the same multicast membership architecture.
The SFM model functionally extends the ASM model. The upper-layer software checks the source address of received multicast packets and permits or denies multicast traffic from specific sources. Therefore, receivers can receive the multicast data from only part of the multicast sources. To a receiver, multicast sources are not all valid; they are filtered.
SSM model
Users might be interested in the multicast data from only certain multicast sources. The SSM model provides a transmission service that enables users to specify the multicast sources that they are interested in at the client side.
The main difference between the SSM model and the ASM model is that in the SSM model, receivers have already determined the locations of the multicast sources by some other means. In addition, the SSM model uses a multicast address range that is different from that of the ASM/SFM model, and dedicated multicast forwarding paths are established between receivers and the specified multicast sources.
Multicast architecture
IP multicast addresses the following questions:
· Where should the multicast source transmit information to? (multicast addressing)
· What receivers exist on the network? (host registration)
· Where is the multicast source that will provide data to the receivers? (multicast source discovery)
· How should information be transmitted to the receivers? (multicast routing)
IP multicast is an end-to-end service. The multicast architecture involves the following parts:
1. Addressing mechanism—A multicast source sends information to a group of receivers through a multicast address.
2. Host registration—Receiver hosts can join and leave multicast groups dynamically. This mechanism is the basis for management of group memberships.
3. Multicast routing—A multicast distribution tree (namely, a forwarding path tree for multicast data on the network) is constructed for delivering multicast data from a multicast source to receivers.
4. Multicast applications—A software system that supports multicast applications, such as video conferencing, must be installed on multicast sources and receiver hosts. The TCP/IP stack must support reception and transmission of multicast data.
Multicast addresses
Network-layer multicast addresses—namely, multicast IP addresses—enables communication between multicast sources and multicast group members. In addition, a technique must be available to map multicast IP addresses to link-layer multicast MAC addresses.
IP multicast addresses
1. IPv4 multicast addresses
Internet Assigned Numbers Authority (IANA) assigned the Class D address space (224.0.0.0 to 239.255.255.255) for IPv4 multicast.
Table 2 Class D IP address blocks and description
|
Address block |
Description |
|
224.0.0.0 to 224.0.0.255 |
Reserved permanent group addresses. The IP address 224.0.0.0 is reserved. Other IP addresses can be used by routing protocols and for topology searching, protocol maintenance, and so on. Table 3 lists common permanent group addresses. A packet destined for an address in this block will not be forwarded beyond the local subnet regardless of the Time to Live (TTL) value in the IP header. |
|
224.0.1.0 to 238.255.255.255 |
Globally scoped group addresses. This block includes the following types of designated group addresses: · 232.0.0.0/8—SSM group addresses, and · 233.0.0.0/8—Glop group addresses. |
|
239.0.0.0 to 239.255.255.255 |
Administratively scoped multicast addresses. These addresses are considered locally unique rather than globally unique, and can be reused in domains administered by different organizations without causing conflicts. For more information, see RFC 2365. |
|
|
NOTE: · The membership of a group is dynamic. Hosts can join or leave multicast groups at any time. · “Glop” is a mechanism for assigning multicast addresses between different autonomous systems (ASs). By filling an AS number into the middle two bytes of 233.0.0.0, you get 255 multicast addresses for that AS. For more information, see RFC 2770. |
Table 3 Some reserved multicast addresses
|
Address |
Description |
|
224.0.0.1 |
All systems on this subnet, including hosts and routers |
|
224.0.0.2 |
All multicast routers on this subnet |
|
224.0.0.3 |
Unassigned |
|
224.0.0.4 |
Distance Vector Multicast Routing Protocol (DVMRP) routers |
|
224.0.0.5 |
Open Shortest Path First (OSPF) routers |
|
224.0.0.6 |
OSPF designated routers/backup designated routers |
|
224.0.0.7 |
Shared Tree (ST) routers |
|
224.0.0.8 |
ST hosts |
|
224.0.0.9 |
Routing Information Protocol version 2 (RIPv2) routers |
|
224.0.0.11 |
Mobile agents |
|
224.0.0.12 |
Dynamic Host Configuration Protocol (DHCP) server/relay agent |
|
224.0.0.13 |
All Protocol Independent Multicast (PIM) routers |
|
224.0.0.14 |
Resource Reservation Protocol (RSVP) encapsulation |
|
224.0.0.15 |
All Core-Based Tree (CBT) routers |
|
224.0.0.16 |
Designated Subnetwork Bandwidth Management (SBM) |
|
224.0.0.17 |
All SBMs |
|
224.0.0.18 |
Virtual Router Redundancy Protocol (VRRP) |
2. IPv6 multicast addresses
Figure 4 IPv6 multicast format

The meanings of the fields of an IPv6 multicast address are as follows:
· 0xFF—The most significant eight bits are 11111111, which indicates that this address is an IPv6 multicast address.
· Flags—The Flags field contains four bits.
Figure 5 Format of the Flags field
![]()
Table 4 Description on the bits of the Flags field
|
Bit |
Description |
|
0 |
Reserved, set to 0 |
|
R |
· When set to 0, it indicates that this address is an IPv6 multicast address without an embedded RP address · When set to 1, it indicates that this address is an IPv6 multicast address with an embedded RP address (the P and T bits must also be set to 1) |
|
P |
· When set to 0, it indicates that this address is an IPv6 multicast address not based on a unicast prefix · When set to 1, it indicates that this address is an IPv6 multicast address based on a unicast prefix (the T bit must also be set to 1) |
|
T |
· When set to 0, it indicates that this address is an IPv6 multicast address permanently-assigned by IANA · When set to 1, it indicates that this address is a transient, or dynamically assigned IPv6 multicast address |
· Scope—The Scope filed contains four bits, which indicate the scope of the IPv6 internetwork for which the multicast traffic is intended.
Table 5 Values of the Scope field
|
Meaning |
|
|
0, F |
Reserved |
|
1 |
Interface-local scope |
|
2 |
Link-local scope |
|
3 |
Subnet-local scope |
|
4 |
Admin-local scope |
|
5 |
Site-local scope |
|
6, 7, 9 through D |
Unassigned |
|
8 |
Organization-local scope |
|
E |
Global scope |
· Group ID—The Group ID field contains 112 bits. It uniquely identifies an IPv6 multicast group in the scope that the Scope field defines.
Ethernet multicast MAC addresses
A multicast MAC address identifies a group of receivers at the data link layer.
1. IPv4 multicast MAC addresses
As defined by IANA, the most significant 24 bits of an IPv4 multicast MAC address are 0x01005E. Bit 25 is 0, and the other 23 bits are the least significant 23 bits of a multicast IPv4 address.
Figure 6 IPv4-to-MAC address mapping

The most significant four bits of a multicast IPv4 address are 1110, which indicates that this address is a multicast address. Only 23 bits of the remaining 28 bits are mapped to a MAC address, so five bits of the multicast IPv4 address are lost. As a result, 32 multicast IPv4 addresses map to the same IPv4 multicast MAC address. Therefore, in Layer 2 multicast forwarding, a device might receive some multicast data destined for other IPv4 multicast groups. The upper layer must filter such redundant data.
2. IPv6 multicast MAC addresses
The most significant 16 bits of an IPv6 multicast MAC address are 0x3333. The least significant 32 bits are the least significant 32 bits of a multicast IPv6 address.
Figure 7 An example of IPv6-to-MAC address mapping

Multicast protocols
|
|
NOTE: · Generally, Layer 2 multicast refers to IP multicast working at the data link layer. The corresponding multicast protocols are Layer 2 multicast protocols, which include IGMP snooping, MLD snooping and multicast VLAN. · IGMP snooping and multicast VLAN are for IPv4, and MLD snooping is for IPv6. |
Layer 2 multicast protocols include IGMP snooping, MLD snooping and multicast VLAN.
Figure 8 Positions of Layer 2 multicast protocols

1. IGMP snooping and MLD snooping
IGMP snooping and MLD snooping are multicast constraining mechanisms that run on Layer 2 devices. They manage and control multicast groups by listening to and analyzing IGMP or MLD messages exchanged between the hosts and Layer 3 multicast devices, effectively controlling the flooding of multicast data in a Layer 2 network.
2. Multicast VLAN
In the traditional multicast-on-demand mode, when users in different VLANs on a Layer 2 device need multicast information, the upstream Layer 3 device must forward a separate copy of the multicast data to each VLAN of the Layer 2 device. When the multicast VLAN feature is enabled on the Layer 2 device, the Layer 3 multicast device sends only one copy of multicast to the multicast VLAN on the Layer 2 device. This approach avoids waste of network bandwidth and extra burden on the Layer 3 device.
Multicast packet forwarding mechanism
In a multicast model, a multicast source sends information to the host group identified by the multicast group address in the destination address field of IP multicast packets. To deliver multicast packets to receivers located at different positions of the network, multicast routers on the forwarding paths usually need to forward multicast packets that an incoming interface receives to multiple outgoing interfaces. Compared with a unicast model, a multicast model is more complex in the following aspects:
· To ensure multicast packet transmission in the network, unicast routing tables or multicast routing tables (for example, the MBGP routing table) specially provided for multicast must be used as guidance for multicast forwarding.
· To process the same multicast information from different peers received on different interfaces of the same device, every multicast packet undergoes a reverse path forwarding (RPF) check on the incoming interface. The result of the RPF check determines whether the packet will be forwarded or discarded. The RPF check mechanism is the basis for most multicast routing protocols to implement multicast forwarding.
