- Table of Contents
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 03-EVPN VPLS configuration | 356.23 KB |
Contents
Neighbor auto-discovery and PW establishment
MAC address learning, aging, and withdrawal
Traffic forwarding and flooding
EVPN VPLS configuration task list
General configuration restrictions and guidelines
Hardware compatibility restrictions
Feature compatibility requirements
Mapping an Ethernet service instance to a VSI
Configuration restrictions and guidelines
Configuring BGP to advertise BGP EVPN routes
Configuration restrictions and guidelines
Enabling BGP to advertise BGP EVPN routes
Configuring optimal route selection and route advertisement settings
Configuration restrictions and guidelines
Managing remote MAC address entries and remote ARP learning
Disabling MAC address advertisement
Enabling MAC mobility event suppression
Disabling learning of MAC addresses from ARP information
Disabling ARP information advertisement
Confining floods to the local site
Enabling ARP flood suppression
Enabling packet statistics for an AC
Configuration restrictions and guidelines
Enabling packet statistics for an Ethernet service instance
Enabling packet statistics for all PWs in an EVPN instance
Configuration restrictions and guidelines
Enabling SNMP notifications for L2VPN PWs
Testing the connectivity of an EVPN PW
Displaying and maintaining EVPN VPLS
EVPN VPLS configuration examples
Configuration example for EVPN VPLS between singlehomed sites
Configuring EVPN VPLS
Overview
EVPN Virtual Private LAN Service (VPLS) is a Layer 2 VPN technology that uses MP-BGP to advertise EVPN routes in the control plane and uses MPLS for forwarding in the data plane. EVPN VPLS provides point-to-multipoint Layer 2 forwarding services for users with MAC address table lookup in VSIs.
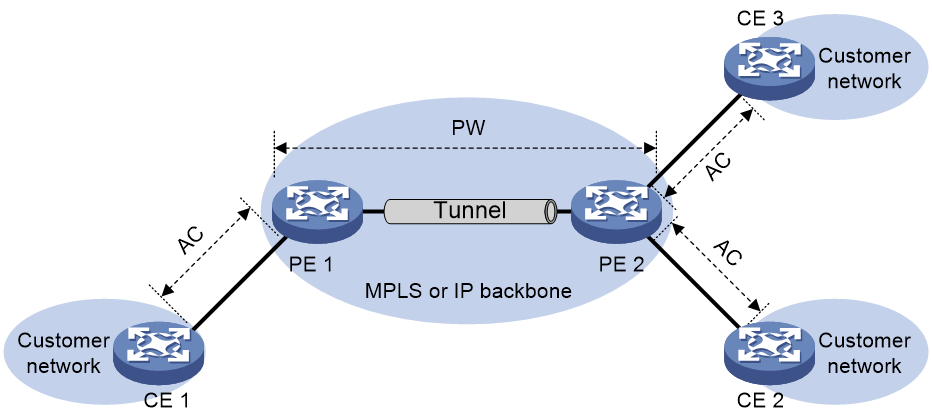
EVPN VPLS network model
As shown in Figure 1, an EVPN VPLS network contains the following devices:
· Customer edge (CE)—Customer device directly connected to the service provider network.
· Provider edge (PE)—Service provider device connected to CEs. PEs provide access to the EVPN VPLS network and forward traffic between customer network sites by using public tunnels.
A PE uses ACs, PWs, tunnels, and VSIs to provide EVPN VPLS services.
· Attachment circuit (AC)—A physical or virtual link between a CE and a PE.
· Pseudowire (PW)—A virtual bidirectional connection between two PEs. A PW contains a pair of virtual links in opposite directions.
· Public tunnel—A connection that carries one or more PWs across the MPLS or IP backbone. A public tunnel can be an LSP, GRE, or MPLS TE tunnel.
· Virtual Switch Instance (VSI)—A virtual switch instance provides Layer 2 switching services for a VPLS instance (EVPN instance) on a PE. A VSI acts as a virtual switch that has all the functions of a conventional Ethernet switch, including source MAC address learning, MAC address aging, and flooding. VPLS uses VSIs to forward Layer 2 data packets in EVPN instances.
Neighbor auto-discovery and PW establishment
A PE uses IMET routes to automatically discover neighbors and establish PWs. When a PE receives an IMET route in a VSI, it compares the export route targets of the route with the import route targets of the EVPN instance associated with the VSI. If they are match, the PE will establish a unidirectional virtual link based on the PE address and PW label information carried in the route. PW establishment is finished when two virtual links in opposite directions are established between two PEs.
MAC address learning, aging, and withdrawal
Source MAC address learning
A PE uses the MAC address table of a VSI to forward Layer 2 unicast traffic for that VSI.
A PE learns source MAC addresses in the following ways:
· Local MAC address learning—When the PE receives a frame from a local CE, it first identifies the VSI of the frame. Then, the PE adds the source MAC address of the frame (the MAC address of the local CE) to the MAC address table of the VSI. The output interface of the MAC address entry is the AC that receives the frame.
· Remote MAC address learning—A PE advertises the MAC addresses of local CEs to remote PEs through BGP EVPN MAC/IP advertisement routes. When a remote PE receives the routes, it adds the received MAC addresses to the MAC address table of the corresponding VSI. The output interface is the PW between the PEs.
MAC address aging
· Local MAC address aging—The MAC address table uses an aging timer for each dynamic MAC address entry. If no packet is received from a MAC address before the aging timer expires, VPLS deletes the MAC address.
· Remote MAC address aging—Remote MAC addresses advertised through MAC/IP advertisement routes are not removed from the MAC address table until routes to withdraw the MAC addresses are received.
MAC address withdrawal
When an AC goes down, the PE deletes MAC addresses on the AC. Then it sends an LDP address withdrawal message to notify all other PEs in the EVPN instance to delete those MAC addresses.
Traffic forwarding and flooding
Unicast traffic forwarding
After a PE receives a unicast packet with a known destination MAC address from an AC, the PE searches the MAC address table of the VSI bound to the AC for packet forwarding.
· If the output interface in the entry is a PW, the PE inserts the PW label to the packet, and adds the public tunnel header to the packet. It then forwards the packet to the remote PE over the PW. If the public tunnel is an LSP or MPLS TE tunnel, each packet on the PW contains two labels. The inner label is the PW label, which identifies the PW and ensures that the packet is forwarded to the correct VSI. The outer label is the public LSP or MPLS TE tunnel label, which ensures that the packet is correctly forwarded to the remote PE.
· If the output interface in the entry is a local interface, the PE directly forwards the packet to the local interface.
After a PE receives a unicast packet with a known destination MAC address from a PW, the PE searches the MAC address table of the VSI bound to the PW for packet forwarding. The PE forwards the packet through the output interface in the matching MAC address entry.
Flooding
When a PE receives flood traffic from an AC in a VSI, it will flood the traffic to the following interfaces:
· All ACs in the VSI except for the incoming AC.
· All PWs associated with the VSI.
When a PE receives flood traffic from a PW, it will flood the traffic to all ACs in the VSI bound to the PW.
Full mesh and split horizon
A Layer 2 network requires a loop prevention protocol such as STP to avoid loops. However, a loop prevention protocol on PEs brings management and maintenance difficulties. Therefore, EVPN VPLS uses the following methods to prevent loops:
· Full mesh—Every two PEs in an EVPN instance must establish a PW. The PWs form a full mesh among PEs in the EVPN instance.
· Split horizon—A PE does not forward packets received from a PW to any other PWs in the same VSI but only forwards those packets to ACs.
ARP flood suppression
ARP flood suppression reduces ARP request broadcasts by enabling a PE to reply to ARP requests on behalf of VMs.
As shown in Figure 2, this feature snoops ARP requests, ARP responses, and BGP EVPN routes to populate the ARP flood suppression table with local and remote MAC addresses. If an ARP request has a matching entry, the PE replies to the request on behalf of the VM. If no match is found, the PE floods the request to both local and remote sites.
Figure 2 ARP flood suppression
ARP flood suppression uses the following workflow:
1. CE1 sends an ARP request to obtain the MAC address of CE 2.
2. PE 1 creates a suppression entry for CE 1, floods the ARP request to local CEs and remote PEs (PE 2 and PE 3) in the VSI, and sends the suppression entry to PE 2 and PE 3 through BGP EVPN. Unicast-mode flooding is used to illustrate the workflow.
3. PE 2 and PE 3 de-encapsulate the ARP request and broadcast the request to local CEs in the VSI.
4. CE 2 sends an ARP reply after it receives the ARP request.
5. PE 2 creates a suppression entry for CE 2, forwards the ARP reply to PE 1, and sends the suppression entry to PE 1 and PE 3 through BGP EVPN.
6. PE 1 de-encapsulates the ARP reply and forwards the ARP reply to CE 1.
7. CE 4 sends an ARP request to obtain the MAC address of CE 1.
8. PE 1 creates a suppression entry for CE 4 and replies to the ARP request.
9. CE 3 sends an ARP request to obtain the MAC address of CE 1.
10. PE 3 creates a suppression entry for CE 3 and replies to the ARP request.
Control word
The control word field is between the MPLS label stack and the Layer 2 data. It carries control information for the Layer 2 frame, for example, the sequence number.
The control word feature has the following functions:
· Avoids fragment disorder. In multipath forwarding, fragments received might be disordered. The control word feature reorders the fragments according to the sequence number carried in the control word field.
· Identifies the original payload length for packets that include padding.
The control word field is optional for EVPN VPLS. You can configure whether to carry the control word field in packets sent on PWs. If you enable the control word feature on PEs at both ends of a PW, packets transmitted on the PW carry the control word field. Otherwise, the packets do not carry the control word field.
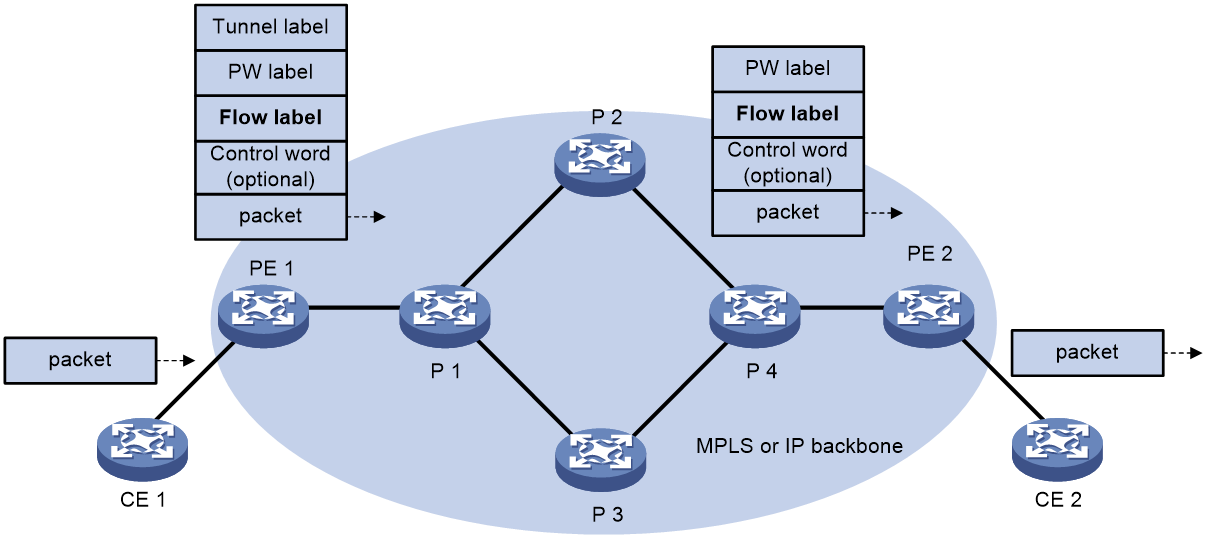
L2VPN flow label
Packets carrying different types of traffic might be transmitted through the same PW and encapsulated with the same PW label. The P devices forward the traffic flows of a PW over the same path even if Equal Cost Multiple Paths (ECMPs) exist.
The L2VPN flow label feature can enable a P device to perform load sharing on packets based on the flow types.
After you configure this feature, the P and PE devices process packets as follows:
· When the ingress PE encapsulates a packet, it adds a flow label before it adds a PW label, as shown in Figure 3.
The ingress PE adds different flow labels for packets of different traffic types.
· The P devices perform load sharing on packets based on the flow labels.
· The egress PE removes both the PW and flow labels from a packet before forwarding the packet.
Figure 3 L2VPN flow label feature
You can enable the flow label sending, receiving, or both sending and receiving capabilities on a PE.
· The sending capability enables a PE to send packets with flow labels. The PE adds a flow label before it adds a PW label to a packet during encapsulation.
· The receiving capability enables a PE to identify the flow label in a received packet and removes the flow label before forwarding the packet.
For two PEs to successfully negotiate the flow label capabilities, make sure one end has the sending capability and the other end has the receiving capability.
For EVPN VPLS, you must manually configure flow label capabilities for the local and remote PEs.
EVPN VPLS configuration task list
|
Tasks at a glance |
|
b. (Optional.) Configuring VSI parameters |
|
4. Configuring BGP to advertise BGP EVPN routes a. Enabling BGP to advertise BGP EVPN routes b. (Optional.) Configuring optimal route selection and route advertisement settings c. (Optional.) Maintaining BGP sessions |
|
5. (Optional.) Configuring a PW class |
|
6. (Optional.) Managing remote MAC address entries and remote ARP learning ¡ Disabling MAC address advertisement ¡ Enabling MAC mobility event suppression |
|
7. (Optional.) Optimizing and maintaining an EVPN VPLS network: ¡ Confining floods to the local site ¡ Enabling ARP flood suppression ¡ Enabling packet statistics for an AC ¡ Enabling packet statistics for all PWs in an EVPN instance |
|
8. (Optional.) Enabling SNMP notifications for L2VPN PW |
|
9. (Optional.) Testing the connectivity of an EVPN PW |
General configuration restrictions and guidelines
Hardware compatibility restrictions
The site-facing and transport-facing interfaces must reside on the following interface modules:
· FD interface modules.
· FE interface modules.
· SG interface modules.
EVPN VPLS supports L2VPN flow labels (set by using the flow-label command) on a PE only when the site-facing and transport-facing interfaces of the PE reside on the FE interface modules. For more information about the flow-label command, see VPLS commands in MPLS Command Reference.
Feature compatibility requirements
EVPN VPLS is mutually exclusive with EVPN-DCI dualhoming. Do not use the evpn edge group command in an EVPN VPLS network. For more information about EVPN-DCI dualhoming and the evpn edge group command, see "Configuring EVPN-DCI."
Do not use MAC authentication together with EVPN VPLS. For more information about MAC authentication, see Security Configuration Guide.
Configuring a VSI
Creating a VSI
To create a VSI:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable L2VPN. |
l2vpn enable |
By default, L2VPN is disabled. |
|
3. Create a VSI and enter VSI view. |
vsi vsi-name |
N/A |
|
4. Bring up the VSI. |
undo shutdown |
By default, a VSI is not administratively down. |
Configuring VSI parameters
To configure VSI parameters:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VSI view. |
vsi vsi-name |
N/A |
|
3. Configure a VSI description. |
description text |
By default, a VSI does not have a description. |
|
4. Set the MTU of the VSI. |
mtu mtu |
The default MTU for a VSI is 1500 bytes. |
|
5. Enable MAC address learning for the VSI. |
mac-learning enable |
By default, MAC address learning is enabled for a VSI. |
Configuring an EVPN instance
An EVPN instance acts as a VPLS instance in an EVPN VPLS network. The EVPN routes advertised by the PE carry the RD and route targets configured for the EVPN instance associated with a VSI.
To configure an EVPN instance:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VSI view. |
vsi vsi-name |
N/A |
|
3. Create an EVPN instance and enter EVPN instance view. |
evpn encapsulation mpls |
N/A |
|
4. Configure an RD for the EVPN instance. |
route-distinguisher route-distinguisher |
By default, no RD is configured for an EVPN instance. |
|
5. Configure route targets for the EVPN instance. |
vpn-target { vpn-target&<1-8> } [ both | export-extcommunity | import-extcommunity ] |
By default, an EVPN instance does not have route targets. Make sure the following requirements are met: · The import targets of the EVPN instance do not match the export targets of the VPN instance associated with the VSI or the public instance. · The export targets of the EVPN instance do not match the import targets of the VPN instance associated with the VSI or the public instance. |
Mapping an Ethernet service instance to a VSI
Overview
An Ethernet service instance matches a list of VLANs on a site-facing interface by using a frame match criterion. The frame match criterion specifies the characteristics of traffic from the VLANs, such as tagging status and VLAN IDs. The PE assigns traffic from the VLANs to a VSI by mapping the Ethernet service instance to the VSI. The VSI performs Layer 2 forwarding for the VLANs based on its MAC address table.
For more information about the commands in this task, see VPLS in MPLS Command Reference.
Configuration restrictions and guidelines
An Ethernet service instance can contain only one match criterion. To change the match criterion, you must remove the original criterion first. When you remove the match criterion in an Ethernet service instance, the mapping between the service instance and the VSI is removed automatically.
Configuration procedure
To map an Ethernet service instance to a VSI:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
· Enter Layer 2 Ethernet interface view. · Enter Layer 2 aggregate interface view. |
N/A |
|
3. Create an Ethernet service instance and enter Ethernet service instance view. |
service-instance instance-id |
N/A |
|
4. Choose one option to configure a frame match criterion. |
· Match frames with the specified inner
VLAN tags. · Match frames with the specified outer
VLAN tags. · Match frames with the specified inner
and outer VLAN tags. · Match any VLAN tagged or untagged
frames. · Match frames that do not match any other
service instance on the interface. |
An interface can contain only one Ethernet service instance that uses the default match criterion. An Ethernet service instance that uses the default match criterion matches any frames if it is the only instance on the interface. By default, an Ethernet service instance does not contain a frame match criterion. |
|
5. Map the Ethernet service instance to a VSI. |
xconnect vsi vsi-name [ access-mode { ethernet | vlan } ] [ track track-entry-number&<1-3> ] |
By default, an Ethernet service instance is not mapped to a VSI. |
Configuring BGP to advertise BGP EVPN routes
Configuration restrictions and guidelines
For more information about BGP commands in this task, see Layer 3—IP Routing Command Reference.
Enabling BGP to advertise BGP EVPN routes
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Configure a global router ID. |
router id router-id |
By default, no global router ID is configured. |
|
3. Enable a BGP instance and enter BGP instance view. |
bgp as-number [ instance instance-name ] |
By default, BGP is disabled and no BGP instances exist. |
|
4. Specify remote PEs as BGP peers. |
peer { group-name | ipv4-address [ mask-length ] } as-number as-number |
N/A |
|
5. Create the BGP EVPN address family and enter BGP EVPN address family view. |
address-family l2vpn evpn |
N/A |
|
6. Enable BGP to exchange BGP EVPN routes with a peer or peer group. |
peer { group-name | ipv4-address [ mask-length ] } enable |
By default, BGP does not exchange BGP EVPN routes with peers. |
Configuring optimal route selection and route advertisement settings
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter BGP instance view. |
bgp as-number [ instance instance-name ] |
N/A |
|
3. Enter BGP EVPN address family view. |
address-family l2vpn evpn |
N/A |
|
4. Permit the local AS number to appear in routes from a peer or peer group and set the number of appearances. |
peer { group-name | ipv4-address [ mask-length ] } allow-as-loop [ number ] |
By default, the local AS number is not allowed in routes from peers. |
|
5. Enable route target filtering for BGP EVPN routes. |
policy vpn-target |
By default, route target filtering is enabled for BGP EVPN routes. |
|
6. (Optional.) Set the optimal route selection delay timer. |
route-select delay delay-value |
By default, the optimal route selection delay timer is 0 seconds, which means optimal route selection is not delayed. |
|
7. Enable the device to filter advertised objects based on the first AS number in EBGP routes. |
peer-as-check enable |
By default, the device advertises a received EBGP route to all BGP peers except the peer that sends the EBGP route. After you execute this command, the device checks the first AS number in the AS_Path attribute of an EBGP route when advertising the EBGP route to EBGP peers. The device will not advertise the EBGP route to the EBGP peers in that AS. |
|
8. Configure the device as an RR and specify a peer or peer group as its client. |
peer { group-name | ipv4-address [ mask-length ] } reflect-client |
By default, no RR or client is configured. |
|
9. (Optional.) Enable BGP EVPN route reflection between clients. |
reflect between-clients |
By default, BGP EVPN route reflection between clients is enabled. |
|
10. (Optional.) Configure the cluster ID of the RR. |
reflector cluster-id { cluster-id | ipv4-address } |
By default, an RR uses its own router ID as the cluster ID. |
|
11. (Optional.) Create a reflection policy for the RR to filter reflected BGP EVPN routes. |
rr-filter ext-comm-list-number |
By default, an RR does not filter reflected BGP EVPN routes. |
|
12. (Optional.) Create a reflection policy for the RR to filter reflected BGP EVPN routes. |
reflect change-path-attribute |
By default, an RR does not filter reflected BGP EVPN routes. |
|
13. Configure the device as a route server and specify a peer or peer group as a client. |
peer { group-name | ipv4-address [ mask-length ] } route-server-client [ external ] |
By default, neither the route server nor the client is configured. The packets advertised to the clients does not carry the AS number of the route server. To avoid peer establishment failures, execute the peer ignore-first-as command on the clients. |
|
14. Configure the device to not change the next hop of routes advertised to an EBGP peer or peer group. |
peer { group-name | ipv4-address [ mask-length ] } next-hop-invariable |
By default, the device uses its address as the next hop of routes advertised to EBGP peers. |
|
15. Apply a routing policy to routes received from or advertised to a peer or peer group. |
peer { group-name | ipv4-address [ mask-length ] } route-policy route-policy-name { export | import } |
By default, no routing policies are applied to routes received from or advertised to peers or peer groups. |
|
16. Configure Layer 2 ACL-based route filtering. |
· Filter routes for a peer or peer group
by using a Layer 2 ACL. · Filter all advertised routes. · Filter all received routes. |
By default, Layer 2 ACL-based route filtering is not configured for a peer or peer group. In a Layer 2 ACL, only the rule [ rule-id ] { deny | permit } dest-mac dest-address dest-mask rule is used to filter MAC/IP advertisement routes that carry the specified MAC addresses. The other rules in a Layer 2 ACL do not take effect in routing filtering. |
|
17. Advertise the COMMUNITY attribute to a peer or peer group. |
peer { group-name | ipv4-address [ mask-length ] } advertise-community |
By default, the device does not advertise the COMMUNITY attribute to peers or peer groups. |
|
18. Configure the BGP Additional Paths capabilities. |
peer { group-name | ipv4-address [ mask-length ] } additional-paths { receive | send } * |
By default, no BGP Additional Paths capabilities are configured. |
|
19. Set the maximum number of Add-Path optimal routes that can be advertised to a peer or peer group. |
peer { group-name | ipv4-address [ mask-length ] } advertise additional-paths best number |
By default, a maximum of one Add-Path optimal route can be advertised to a peer or peer group. |
|
20. Set the maximum number of Add-Path optimal routes that can be advertised to all peers. |
additional-paths select-best best-number |
By default, a maximum of one Add-Path optimal route can be advertised to all peers. |
Maintaining BGP sessions
Perform the following tasks in user view:
|
Task |
Command |
|
Reset BGP sessions of the BGP EVPN address family. |
reset bgp [ instance instance-name ] { as-number | ipv4-address [ mask-length ] | all | external | group group-name | internal } l2vpn evpn |
|
Soft-reset BGP sessions of the BGP EVPN address family. |
refresh bgp [ instance instance-name ] { ipv4-address [ mask-length ] | all | external | group group-name | internal } { export | import } l2vpn evpn |
Configuring a PW class
Overview
In a PW class, you can configure PW attributes such as the PW data encapsulation type, and whether to enable control word. To simplify PW attribute configuration for PWs, you can configure a PW class and apply the PW class to the PWs. For more information about PW class configuration, see VPLS in MPLS Configuration Guide.
The settings in a PW class applied to an EVPN instance will apply to all PWs in the EVPN instance.
Configuration restrictions and guidelines
Make sure the same data encapsulation type is configured for the two PEs that are connected by the same PW.
Configuration procedure
To apply a PW class to an EVPN instance:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VSI view. |
vsi vsi-name |
N/A |
|
3. Enter EVPN instance view. |
evpn encapsulation mpls |
N/A |
|
4. Apply a PW class to the EVPN instance. |
pw-class class-name |
By default, no PW class is applied to an EVPN instance. |
Managing remote MAC address entries and remote ARP learning
Disabling MAC address advertisement
The MAC information and ARP or ND information advertised by the PE overlap. To avoid duplication, disable MAC address advertisement and withdraw the MAC addresses advertised to remote PEs.
To disable MAC address advertisement and withdraw advertised MAC addresses:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VSI view. |
vsi vsi-name |
N/A |
|
3. Enter EVPN instance view. |
evpn encapsulation mpls |
N/A |
|
4. Disable MAC address advertisement and withdraw advertised MAC addresses. |
mac-advertising disable |
By default, MAC address advertisement is enabled. |
Enabling MAC mobility event suppression
Overview
On an EVPN VPLS network, misconfiguration of MAC addresses might cause two sites to contain the same MAC address. In this condition, the PEs at the two sites constantly synchronize and update EVPN MAC address entries and determine that MAC mobility events occur. As a result, an inter-site loop might occur, and the bandwidth is occupied by MAC entry synchronization traffic. To eliminate loops and suppress those MAC mobility events, enable MAC mobility event suppression on the PEs.
This feature allows a MAC address to move at most the specified number of times (MAC mobility suppression threshold) out of a site within a MAC mobility detection cycle. If the suppression threshold has been reached for a MAC address within a detection cycle, the PE at the site suppresses the subsequent move after the MAC address moves back to the site. In addition, the PE learns the MAC address but does not advertise the MAC address.
Configuration restrictions and guidelines
After you execute the undo evpn route mac-mobility suppression command or when the MAC mobility suppression time expires, a PE acts as follows:
· Advertises MAC address entries immediately for the suppressed MAC address entries that have not aged out.
· Relearns the MAC addresses for the suppressed MAC address entries that have aged out and advertises the MAC address entries.
Configuration procedure
To enable MAC mobility event suppression:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable MAC mobility event suppression. |
evpn route mac-mobility suppression[ detect-cycle detect-time | detect-threshold move-times | suppression-time [ suppression-time | permanent ] ] * |
By default, MAC mobility event suppression is disabled. |
Disabling learning of MAC addresses from ARP information
The MAC information and ARP information advertised by a remote PE overlap. To avoid duplication, disable the learning of MAC addresses from ARP information. EVPN will learn remote MAC addresses only from the MAC information advertised from remote sites.
To disable an EVPN instance from learning MAC addresses from ARP information:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VSI view. |
vsi vsi-name |
N/A |
|
3. Enter EVPN instance view. |
evpn encapsulation mpls |
N/A |
|
4. Disable the EVPN instance from learning MAC addresses from ARP information. |
arp mac-learning disable |
By default, an EVPN instance learns MAC addresses from ARP information. |
Disabling ARP information advertisement
In an EVPN VPLS network, you can disable ARP information advertisement for an EVPN instance to save resources if all user terminals in the EVPN instance are attached to one PE. The EVPN instance will stop advertising ARP information through MAC/IP advertisement routes and withdraw advertised ARP information.
To disable ARP information advertisement for an EVPN instance:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VSI view. |
vsi vsi-name |
N/A |
|
3. Enter EVPN instance view. |
evpn encapsulation mpls |
N/A |
|
4. Disable ARP information advertisement for the EVPN instance. |
arp-advertising disable |
By default, ARP information advertisement is enabled for an EVPN instance. |
Confining floods to the local site
By default, the PE floods broadcast, unknown unicast, and unknown multicast frames received from the local site to the following interfaces in the frame's VSI:
· All site-facing interfaces except for the incoming interface.
· All PWs.
To confine a kind of flood traffic to the site-facing interfaces, disable flooding for that kind of flood traffic on the VSI. The VSI will not flood the corresponding frames to PWs.
To disable flooding for a VSI:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VSI view. |
vsi vsi-name |
N/A |
|
3. Disable flooding for the VSI. |
flooding disable { all | { broadcast | unknown-multicast | unknown-unicast } * } |
By default, flooding is enabled for a VSI. |
Enabling ARP flood suppression
Use ARP flood suppression to reduce ARP request broadcasts.
The aging timer is fixed at 25 minutes for ARP flood suppression entries. If the flooding disable command is configured, set the MAC aging timer to a higher value than the aging timer for ARP flood suppression entries on all PEs. This setting prevents the traffic blackhole that occurs when a MAC address entry ages out before its ARP flood suppression entry ages out. To set the MAC aging timer, use the mac-address timer command.
To enable ARP flood suppression:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VSI view. |
vsi vsi-name |
N/A |
|
3. Enable ARP flood suppression. |
arp suppression enable |
By default, ARP flood suppression is disabled. |
Enabling packet statistics for an AC
Configuration restrictions and guidelines
For the statistics enable command to take effect on an Ethernet service instance, you must configure a frame match criterion for the Ethernet service instance and map it to a VSI. When you modify the frame match criterion or VSI mapping, the packet statistics of the instance are cleared. To display the statistics, use the display l2vpn service-instance verbose command.
To clear packet statistics for ACs (Ethernet service instances), use the reset l2vpn statistics ac command.
Enabling packet statistics for an Ethernet service instance
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
· Enter Layer 2 Ethernet interface view. · Enter Layer 2 aggregate interface view. |
N/A |
|
3. Enter Ethernet service instance view. |
service-instance instance-id |
N/A |
|
4. Enable packet statistics for the Ethernet service instance. |
statistics enable |
By default, the packet statistics feature is disabled for all Ethernet service instances. |
Enabling packet statistics for all PWs in an EVPN instance
Configuration restrictions and guidelines
To display the total number of packets received by PWs, use the display evpn mpls statistics inbound command. This command does not display incoming packet statistics about a specific PW.
To display outgoing packet statistics about PWs, use the display l2vpn pw command.
To clear packet statistics for PWs, use the reset l2vpn statistics pw command.
Configuration procedure
To enable packet statistics for all PWs in an EVPN instance:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VSI view. |
vsi vsi-name |
N/A |
|
3. Enter VSI EVPN instance view. |
evpn encapsulation mpls |
N/A |
|
4. Enable packet statistics for all PWs. |
statistics enable |
By default, packet statistics is disabled for all PWs in an EVPN instance. |
Enabling SNMP notifications for L2VPN PWs
This task enables L2VPN to generate SNMP notifications when PW deletions, PW switchovers, or PW status changes occur. For L2VPN event notifications to be sent correctly, you must also configure SNMP on the device. For more information about SNMP configuration, see Network Management and Monitoring Configuration Guide.
To enable SNMP notifications for L2VPN PWs:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable SNMP notifications for L2VPN PWs. |
snmp-agent trap enable l2vpn [ pw-delete | pw-switch | pw-up-down ] * |
By default, SNMP notifications for L2VPN PWs are disabled. |
Testing the connectivity of an EVPN PW
Overview
Perform this task to test the connectivity of a PW when the PW has traffic loss or interruption issues in an EVPN VPLS network. The process of a ping operation is as follows:
1. The PW source PE sends MPLS echo requests that contain the PW labels of the PW to the PW destination PE based on the destination MAC address and VSI you specify.
2. The PW destination PE looks up the routing table and responds to the PW source PE with MPLS echo replies.
3. The PW source PE outputs packet statistics and the test result based on whether and when it receives MPLS echo replies.
Configuration procedure
To test the connectivity of a PW, execute the following command in any view:
|
Task |
Command |
|
Test the connectivity of a PW in any view. |
ping evpn vsi vsi-name mac mac-address [ -a source-ip | -c count | -exp exp-value | -h ttl-value | -m wait-time | -r reply-mode | -rtos tos-value | -s packet-size | -t time-out | -v ] * |
Displaying and maintaining EVPN VPLS
Execute display commands in any view and reset commands in user view.
For more information about the following BGP commands, see Layer 3—IP Routing Command Reference:
· display bgp group.
· display bgp peer.
· display bgp update-group.
For more information about the reset l2vpn statistics ac command, see VPLS in MPLS Command Reference.
|
Task |
Command |
|
Display BGP peer group information. |
display bgp [ instance instance-name ] group l2vpn evpn [ group-name group-name ] |
|
Display BGP EVPN routes. |
display bgp [ instance instance-name ] l2vpn evpn [ peer ipv4-address { advertised-routes | received-routes } [ statistics ] | [ route-distinguisher route-distinguisher | route-type { auto-discovery | es | imet | ip-prefix | mac-ip } ] * [ { evpn-route route-length | evpn-prefix } [ advertise-info ] | { ipv4-address | ipv6-address | mac-address } [ verbose ] ] | statistics ] |
|
Display BGP peer or peer group information. |
display bgp [ instance instance-name ] peer l2vpn evpn [ ipv4-address mask-length | { ipv4-address | group-name group-name } log-info | [ ipv4-address ] verbose ] |
|
Display information about BGP update groups. |
display bgp [ instance instance-name ] update-group l2vpn evpn [ ipv4-address ] |
|
Display information about peers that are automatically discovered through BGP. |
display evpn auto-discovery { { imet | mac-ip } [ mpls | vxlan ] [ peer ip-address] [ vsi vsi-name ] | macip-prefix [ nexthop next-hop ] [ count ] } |
|
Display statistics about PW inbound packets. |
display evpn mpls statistics inbound [ vsi vsi-name ] |
|
Display EVPN ARP entries. |
display evpn route arp [ local | remote ] [ public-instance | vpn-instance vpn-instance-name ] [ count ] |
|
Display ARP flood suppression entries. |
display evpn route arp suppression [ mpls | vxlan ] [ local | remote ] [ vsi vsi-name ] [ count ] |
|
Display EVPN MAC address entries. |
display evpn route mac [ mpls | vxlan ] [ local | remote ] [ vsi vsi-name ] [ count ] |
|
Display EVPN MAC mobility information. |
display evpn [ ipv6 ] route mac-mobility [ vsi vsi-name ] [ mac-address mac-address ] |
|
Display EVPN ND entries. |
display evpn route nd [ local | remote ] [ public-instance | vpn-instance vpn-instance-name ] [ count ] |
|
Display the routing table for a VPN instance. |
display evpn routing-table { public-instance | vpn-instance vpn-instance-name } [ count ] |
|
Clear packet statistics for ACs. |
reset l2vpn statistics ac [ interface interface-type interface-number [ service-instance instance-id ] ] |
EVPN VPLS configuration examples
Configuration example for EVPN VPLS between singlehomed sites
Network requirements
As shown in Figure 4, set up a path between PE 1 and PE 2 for the CEs in VLAN 10 of site 1 and site 2 to communicate through EVPN VPLS over the MPLS or IP backbone network.
|
Device |
Interface |
IP address |
Device |
Interface |
IP address |
|
CE 1 |
Vlan-int10 |
10.1.1.10/24 |
P |
Loop0 |
3.3.3.3/32 |
|
PE 1 |
Loop0 |
1.1.1.1/32 |
|
Vlan-int23 |
11.1.1.2/24 |
|
|
Vlan-int23 |
11.1.1.1/24 |
|
Vlan-int26 |
11.1.2.2/24 |
|
CE 2 |
Vlan-int10 |
10.1.1.20/24 |
PE 2 |
Loop0 |
2.2.2.2/32 |
|
|
|
|
|
Vlan-int26 |
11.1.2.1/24 |
Configuration procedure
1. Create VLANs on all devices and assign interfaces to the VLANs. (Details not shown.)
2. Configure CE 1.
<CE1> system-view
[CE1] interface vlan-interface 10
[CE1-Vlan-interface10] ip address 10.1.1.10 24
[CE1-Vlan-interface10] quit
3. Configure PE 1:
# Configure the LSR ID.
<PE1> system-view
[PE1] interface loopback 0
[PE1-LoopBack0] ip address 1.1.1.1 32
[PE1-LoopBack0] quit
[PE1] mpls lsr-id 1.1.1.1
# Enable L2VPN.
[PE1] l2vpn enable
# Enable global LDP.
[PE1] mpls ldp
[PE1-ldp] quit
# Configure VLAN-interface 23 (the interface connected to the P device), and enable LDP on the interface.
[PE1] interface vlan-interface 23
[PE1-Vlan-interface23] ip address 11.1.1.1 24
[PE1-Vlan-interface23] mpls enable
[PE1-Vlan-interface23] mpls ldp enable
[PE1-Vlan-interface23] undo shutdown
[PE1-Vlan-interface23] quit
# Configure OSPF for LDP to create LSPs.
[PE1] ospf
[PE1-ospf-1] area 0
[PE1-ospf-1-area-0.0.0.0] network 11.1.1.0 0.0.0.255
[PE1-ospf-1-area-0.0.0.0] network 1.1.1.1 0.0.0.0
[PE1-ospf-1-area-0.0.0.0] quit
[PE1-ospf-1] quit
# Create an IBGP connection to PE 2, and enable BGP to advertise L2VPN information to PE 2.
[PE1] bgp 100
[PE1-bgp-default] peer 2.2.2.2 as-number 100
[PE1-bgp-default] peer 2.2.2.2 connect-interface loopback 0
[PE1-bgp-default] address-family l2vpn evpn
[PE1-bgp-default-evpn] peer 2.2.2.2 enable
[PE1-bgp-default-evpn] quit
[PE1-bgp-default] quit
# Create VSI vpna, create an EVPN instance on the VSI, enable MPLS encapsulation, and configure an RD and route targets for the EVPN instance.
[PE1] vsi vpna
[PE1-vsi-vpna] evpn encapsulation mpls
[PE1-vsi-vpna-evpn-mpls] route-distinguisher 1:1
[PE1-vsi-vpna-evpn-mpls] vpn-target 1:1 export-extcommunity
[PE1-vsi-vpna-evpn-mpls] vpn-target 1:1 import-extcommunity
[PE1-vsi-vpna-evpn-mpls] quit
[PE1-vsi-vpna] quit
# Configure Ethernet service instance 1000 to match VLAN 10 on Ten-GigabitEthernet 1/0/1 (the interface connected to CE 1).
[PE1] interface ten-gigabitethernet 1/0/1
[PE1-Ten-GigabitEthernet1/0/1] port link-type trunk
[PE1-Ten-GigabitEthernet1/0/1] port trunk permit vlan 10
[PE1-Ten-GigabitEthernet1/0/1] service-instance 1000
[PE1-Ten-GigabitEthernet1/0/1-srv1000] encapsulation s-vid 10
# Map Ethernet service instance 1000 to VSI vpna.
[PE1-Ten-GigabitEthernet1/0/1-srv1000] xconnect vsi vpna
[PE1-Ten-GigabitEthernet1/0/1-srv1000] quit
[PE1-Ten-GigabitEthernet1/0/1] quit
4. Configure the P device:
# Configure the LSR ID.
<P> system-view
[P] interface loopback 0
[P-LoopBack0] ip address 3.3.3.3 32
[P-LoopBack0] quit
[P] mpls lsr-id 3.3.3.3
# Enable global LDP.
[P] mpls ldp
[P-ldp] quit
# Configure VLAN-interface 23 (the interface connected to PE 1), and enable LDP on the interface.
[P] interface vlan-interface 23
[P-Vlan-interface23] ip address 11.1.1.2 24
[P-Vlan-interface23] mpls enable
[P-Vlan-interface23] mpls ldp enable
[P-Vlan-interface23] undo shutdown
[P-Vlan-interface23] quit
# Configure VLAN-interface 26 (the interface connected to PE 2), and enable LDP on the interface.
[P] interface vlan-interface 26
[P-Vlan-interface26] ip address 11.1.2.2 24
[P-Vlan-interface26] mpls enable
[P-Vlan-interface26] mpls ldp enable
[P-Vlan-interface26] undo shutdown
[P-Vlan-interface26] quit
# Configure OSPF for LDP to create LSPs.
[P] ospf
[P-ospf-1] area 0
[P-ospf-1-area-0.0.0.0] network 11.1.1.0 0.0.0.255
[P-ospf-1-area-0.0.0.0] network 11.1.2.0 0.0.0.255
[P-ospf-1-area-0.0.0.0] network 3.3.3.3 0.0.0.0
[P-ospf-1-area-0.0.0.0] quit
[P-ospf-1] quit
5. Configure PE 2:
# Configure the LSR ID.
<PE2> system-view
[PE2] interface loopback 0
[PE2-LoopBack0] ip address 2.2.2.2 32
[PE2-LoopBack0] quit
[PE2] mpls lsr-id 2.2.2.2
# Enable L2VPN.
[PE2] l2vpn enable
# Enable global LDP.
[PE2] mpls ldp
[PE2-ldp] quit
# Configure VLAN-interface 26 (the interface connected to the P device), and enable LDP on the interface.
[PE2] interface vlan-interface 26
[PE2-Vlan-interface26] ip address 11.1.2.1 24
[PE2-Vlan-interface26] mpls enable
[PE2-Vlan-interface26] mpls ldp enable
[PE2-Vlan-interface26] undo shutdown
[PE2-Vlan-interface26] quit
# Configure OSPF for LDP to create LSPs.
[PE2] ospf
[PE2-ospf-1] area 0
[PE2-ospf-1-area-0.0.0.0] network 2.2.2.2 0.0.0.0
[PE2-ospf-1-area-0.0.0.0] network 11.1.2.0 0.0.0.255
[PE2-ospf-1-area-0.0.0.0] quit
[PE2-ospf-1] quit
# Create an IBGP connection to PE 1, and enable BGP to advertise L2VPN information to PE 1.
[PE2] bgp 100
[PE2-bgp-default] peer 1.1.1.1 as-number 100
[PE2-bgp-default] peer 1.1.1.1 connect-interface loopback 0
[PE2-bgp-default] address-family l2vpn evpn
[PE2-bgp-default-evpn] peer 1.1.1.1 enable
[PE2-bgp-default-evpn] quit
[PE2-bgp-default] quit
# Create VSI vpna, create an EVPN instance on the VSI, enable MPLS encapsulation, and configure an RD and route targets for the EVPN instance.
[PE2] vsi vpna
[PE2-vsi-vpna] evpn encapsulation mpls
[PE2-vsi-vpna-evpn-mpls] route-distinguisher 1:1
[PE2-vsi-vpna-evpn-mpls] vpn-target 1:1 export-extcommunity
[PE2-vsi-vpna-evpn-mpls] vpn-target 1:1 import-extcommunity
[PE2-vsi-vpna-evpn-mpls] quit
[PE2-vsi-vpna] quit
# Configure Ethernet service instance 1000 to match VLAN 10 on Ten-GigabitEthernet 1/0/1 (the interface connected to CE 2).
[PE2] interface ten-gigabitethernet 1/0/1
[PE2-Ten-GigabitEthernet1/0/1] port link-type trunk
[PE2-Ten-GigabitEthernet1/0/1] port trunk permit vlan 10
[PE2-Ten-GigabitEthernet1/0/1] service-instance 1000
[PE2-Ten-GigabitEthernet1/0/1-srv1000] encapsulation s-vid 10
# Map Ethernet service instance 1000 to VSI vpna.
[PE2-Ten-GigabitEthernet1/0/1-srv1000] xconnect vsi vpna
[PE2-Ten-GigabitEthernet1/0/1-srv1000] quit
[PE2-Ten-GigabitEthernet1/0/1] quit
6. Configure CE 2.
<CE2> system-view
[CE2] interface vlan-interface 10
[CE2-Vlan-interface10] ip address 10.1.1.20 24
[CE2-Vlan-interface10] quit
Verifying the configuration
# Verify that an EVPN PW has been established between PE 1 and PE 2.
[PE1] display l2vpn pw
Flags: M - main, B - backup, E - ecmp, BY - bypass, H - hub link, S - spoke link
N - no split horizon, A - administration, ABY - ac-bypass
PBY - pw-bypass
Total number of PWs: 1
1 up, 0 blocked, 0 down, 0 defect, 0 idle, 0 duplicate
VSI name: vpna
Peer PWID/RmtSite/SrvID In/Out Label Proto Flag Link ID State
2.2.2.2 - 775127/775127 EVPN M 8 Up
# Verify that the PW is created on PE 2.
<PE2> display l2vpn pw
Flags: M - main, B - backup, E - ecmp, BY - bypass, H - hub link, S - spoke link
N - no split horizon, A - administration, ABY - ac-bypass
PBY - pw-bypass
Total number of PWs: 1
1 up, 0 blocked, 0 down, 0 defect, 0 idle, 0 duplicate
VSI name: vpna
Peer PWID/RmtSite/SrvID In/Out Label Proto Flag Link ID State
1.1.1.1 - 775127/775127 EVPN M 8 Up
# Verify that CE 1 and CE 2 can ping each other. (Details not shown.)