- Table of Contents
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 02-User isolation configuration | 246.53 KB |
Contents
Enabling SSID-based user isolation
Configuring VLAN-based user isolation
Display and maintenance commands for user isolation
User isolation configuration examples
Example: Configuring SSID-based user isolation
Example: Configuring VLAN-based user isolation
Configuring user isolation
About user isolation
The user isolation feature isolates packets for users that use the same SSID in the same VLAN or for users that are in the same VLAN. This feature improves user security, relieves the forwarding stress of the device, and reduces consumption of radio resources.
User isolation types
User isolation includes the following types:
· SSID-based user isolation—Isolates wireless users that use the same SSID in the same VLAN.
· VLAN-based user isolation—Isolates wired or wireless users in the same VLAN.
SSID-based user isolation
When SSID-based user isolation is enabled for a service, the AP isolates all wireless users that access the network through the service regardless of their VLANs.
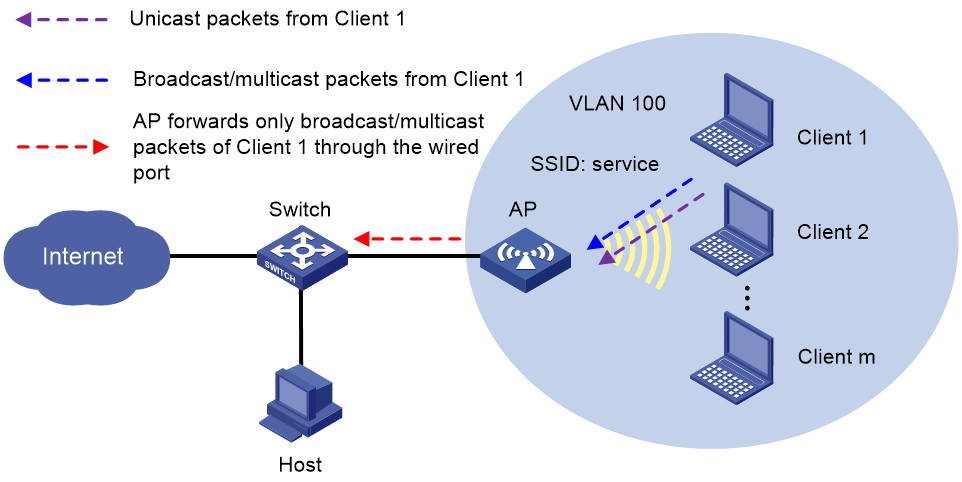
As shown in Figure 1, Client 1 to Client m access the WLAN through the AP by using the service named service. Enable user isolation on the AP for the service.
· Client 1 sends broadcast or multicast packets in VLAN 100. When the AP receives the packets, it does not forward them to any clients in the WLAN. The AP forwards the packets only through the wired port to the switch.
· Client 1 sends unicast packets to Client 2 in VLAN 100. When the AP receives the packets, it discards them instead of forwarding them to Client 2.
Figure 1 Packet forwarding path
VLAN-based user isolation
When user isolation is enabled for a VLAN, the AP processes packets of the users in the VLAN as follows:
· For received unicast packets, the AP discards the packets.
· For broadcast or multicast packets, the AP forwards the packets only to non-local wired and wireless users in the VLAN through wired ports. The AP does not forward the packets to the local wireless users in the VLAN.
For packets received from wireless users
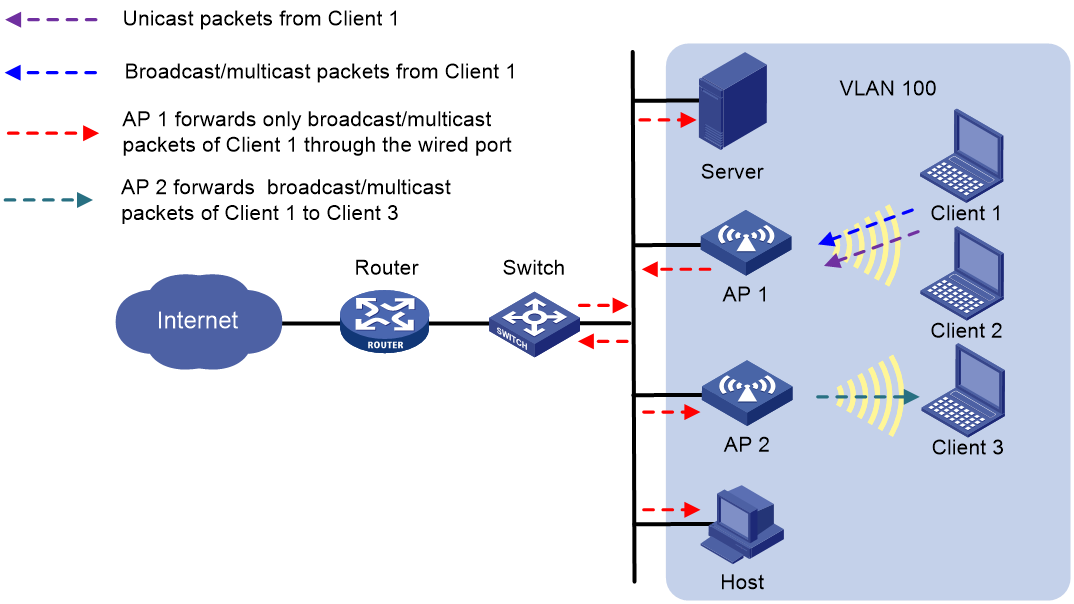
As shown in Figure 2, enable user isolation on AP 1 for VLAN 100.
· Client 1 sends broadcast or multicast packets in VLAN 100.
¡ When AP 1 receives the packets, it forwards them to the server, AP 2, and the host in VLAN 100 through the wired port. However, AP 1 does not forward the packets to Client 2.
¡ When AP 2 receives the packets, it forwards them to Client 3 since user isolation is not enabled on AP 2.
· Client 1 sends unicast packets to Client 3 in VLAN 100. When AP 1 receives the packets, it discards them instead of forwarding them to AP 2.
Figure 2 Packet forwarding path
For packets received from wired users
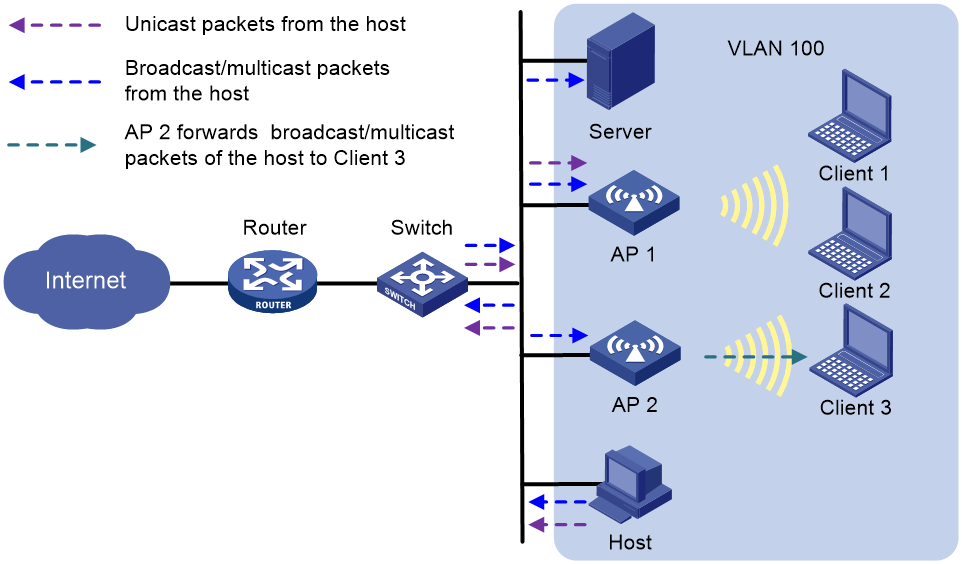
As shown in Figure 3, enable user isolation on AP 1 for VLAN 100.
· The host sends broadcast or multicast packets in VLAN 100. The server, AP 1, and AP 2 can receive the packets.
¡ When AP 1 receives the packets, it discards them instead of forwarding them to Client 1 and Client 2.
¡ When AP 2 receives the packets, it forwards them to Client 3 since user isolation is not enabled on AP 2.
· The host sends unicast packets to Client 1 in VLAN 100. When AP 1 receives the packets, it discards them instead of forwarding them to Client 1.
Figure 3 Packet forwarding path
Enabling SSID-based user isolation
1. Enter system view.
system-view
2. Enter service template view.
wlan service-template service-template-name
3. Enable SSID-based user isolation.
user-isolation enable
By default, SSID-based user isolation is disabled.
Configuring VLAN-based user isolation
Restrictions and guidelines
To enable users in a VLAN to access the external network, assign the VLAN gateway MAC address to the permitted MAC address list before you enable VLAN-based user isolation.
Procedure
1. Enter system view.
system-view
2. Configure permitted MAC address list for a list of VLANs.
user-isolation vlan vlan-list permit-mac mac-list
By default, no permitted MAC addresses are configured for a VLAN.
The device can forward unicast, multicast, and broadcast traffic sent by the users of permitted MAC addresses in the specified VLANs. In addition, the device can forward unicast traffic sent from other users to these users.
3. Enable user isolation for a list of VLANs.
user-isolation vlan vlan-list enable [ permit-unicast ]
By default, user isolation is disabled for a VLAN.
4. (Optional.) Permit broadcast and multicast traffic sent from wired users to wireless users.
user-isolation permit-broadcast
By default, the device does not forward broadcast or multicast traffic sent from wired users to wireless users in the VLANs where user isolation is enabled.
5. (Optional.) Permit wireless users in the specified VLANs to receive broadcast and multicast traffic that matches an ACL.
user-isolation vlan vlan-list permit-bmc acl [ ipv6 ] acl-number
By default, wireless users in a VLAN cannot receive broadcast or multicast traffic.
Display and maintenance commands for user isolation
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display user isolation statistics for a VLAN or for all VLANs. |
display user-isolation statistics [ vlan vlan-id ] |
|
Clear user isolation statistics for a VLAN or for all VLANs. |
reset user-isolation statistics [ vlan vlan-id ] |
User isolation configuration examples
Example: Configuring SSID-based user isolation
Network configuration
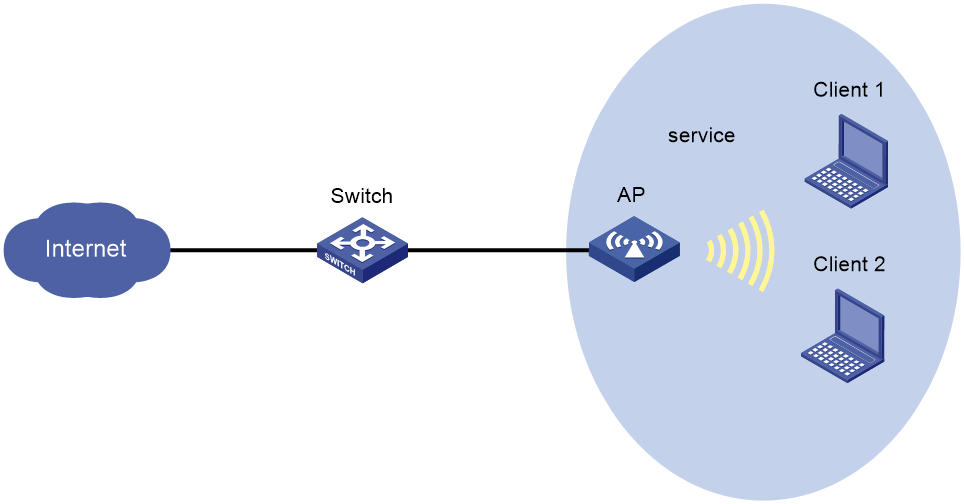
As shown in Figure 4, Client 1 and Client 2 use the same SSID to access the Internet.
Configure user isolation on the AP to isolate the clients from each other while providing Internet access for the clients.
Procedure
# Configure Client 1 and Client 2 to access the Internet through service template service. For more information, see WLAN Access Configuration Guide. (Details not shown.)
# Enable SSID-based user isolation for service template service.
<AP> system-view
[AP] wlan service-template service
[AP-wlan-st-service] user-isolation enable
[AP-wlan-st-service] quit
Verifying the configuration
# Verify that Client 1 and Client 2 can use service service to access the Internet but cannot access each other. (Details not shown.)
Example: Configuring VLAN-based user isolation
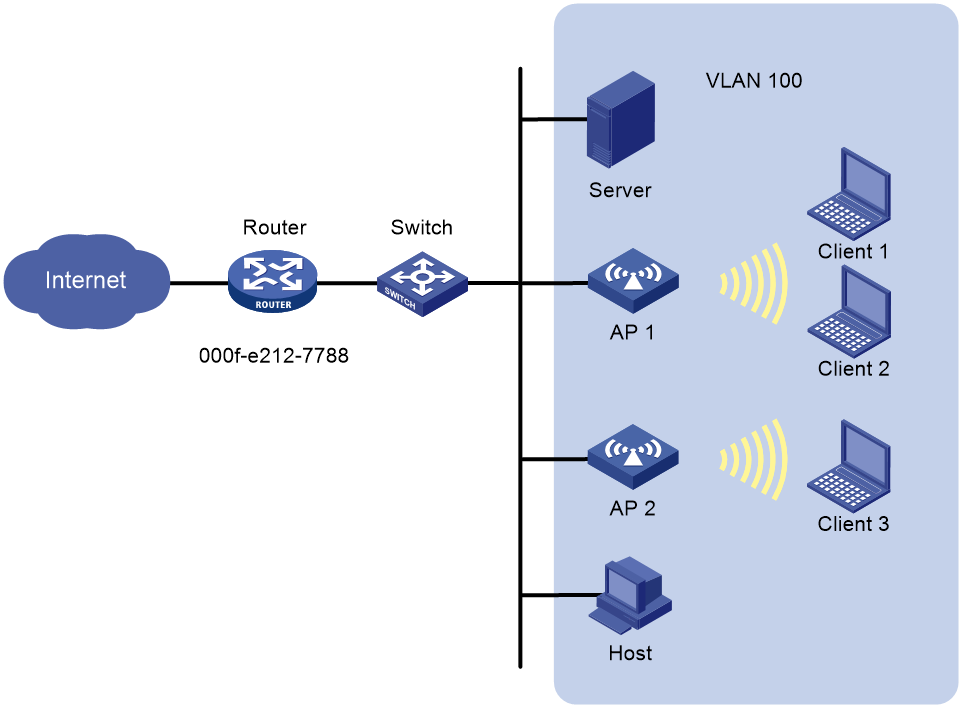
Network configuration
As shown in Figure 5, the router acts as the gateway of the devices in VLAN 100. The MAC address of the gateway is 000f-e212-7788.
Configure user isolation for VLAN 100 on AP 1 to meet the following requirements:
· Client 1, Client 2, Client 3, the host, and the server can access the Internet. For this purpose, add the MAC address of the gateway to the permitted MAC address list.
· When Client 1 forwards broadcast packets, only the host, the server, and Client 3 can receive the packets.
· Client 1 cannot forward unicast packets to Client 2, Client 3, the host, and the server.
Procedure
# Configure Client 1, Client 2, and Client 3 to access the Internet through WLAN. For more information, see WLAN Access Configuration Guide. (Details not shown.)
# Assign the MAC address of the gateway to the permitted MAC address list.
<AP1> system-view
[AP1] user-isolation vlan 100 permit-mac 000f-e212-7788
# Enable VLAN-based user isolation for VLAN 100.
[AP1] user-isolation vlan 100 enable
Verifying the configuration
# Verify that Client 1, Client 2, Client 3, the host, and the server in VLAN 100 can access the Internet. (Details not shown.)
# Verify that only the host, the server, and Client 3 can receive broadcast packets from Client 1. (Details not shown.)
# Verify that Client 1 cannot forward unicast packets to Client 2, Client 3, the host, and the server. (Details not shown.)