- Table of Contents
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 02-QoS configuration | 887.66 KB |
QoS processing flow in a device
Restrictions and guidelines for applying a QoS policy
Applying the QoS policy to an interface
Applying the QoS policy to VLANs
Applying the QoS policy globally
Applying the QoS policy to a control plane
Display and maintenance commands for QoS policies
Setting the exclusive bandwidth on an interface
About setting the exclusive bandwidth
Display and maintenance commands for exclusive bandwidth
Priority mapping configuration methods
Priority mapping tasks at a glance
Configuring an uncolored priority map
Configuring a colored priority map
Configuring a flexible priority map for an interface
Configuring the priority trust mode
Changing the port priority of an interface
Display and maintenance commands for priority mapping
Priority mapping configuration examples
Example: Configuring a priority trust mode
Example: Configuring priority mapping tables and priority marking
Configuring traffic policing, GTS, and rate limit
About traffic policing, GTS, and rate limit
Traffic evaluation and token buckets
Traffic policing configuration approaches
Configuring traffic policing by using the MQC approach
Configuring traffic policing for a user profile
Configuring traffic policing for a control plane
Configuring GTS for a user group profile
Configuring GTS for a session group profile
Configuring the rate limit for an interface
Configuring traffic permission by using the MQC approach
Display and maintenance commands for traffic policing, GTS, and rate limit
Traffic policing, GTS, and rate limit configuration examples
Example: Configuring traffic policing and GTS
Configuring hardware congestion management
About hardware congestion management
Hardware congestion management tasks at a glance
Configuring queuing on an interface
Configure AF and the minimum guaranteed bandwidth
Configuring EF and the guaranteed bandwidth
Configuring a queue scheduling profile
About queue scheduling profiles
Restrictions and guidelines for queue scheduling profile configuration
Configuring a queue scheduling profile
Applying a queue scheduling profile
Example: Configuring a queue scheduling profile
Display and maintenance commands for hardware congestion management
Configuring congestion avoidance
Relationship between WRED and queuing mechanisms
Configuring and applying a queue-based WRED table
Example: Configuring and applying a queue-based WRED table
Display and maintenance commands for WRED
Restrictions and guidelines: Traffic filtering configuration
Traffic filtering configuration examples
Example: Configuring traffic filtering
Configuring priority marking by using the MQC approach
Priority marking configuration examples
Example: Configuring priority marking
Example: Configuring priority marking and class-based accounting for priority marking verification
Configuring traffic redirecting
Restrictions and guidelines: Traffic redirecting configuration
Traffic redirecting configuration examples
Example: Configuring traffic redirecting to the next hop
Configuring aggregate CAR by using the MQC approach
Display and maintenance commands for global CAR
Global CAR configuration examples
Example: Configuring aggregate CAR
Configuring class-based accounting
Restrictions and guidelines: Class-based accounting configuration
Class-based accounting configuration examples
Example: Configuring class-based accounting
Configuring queue-based accounting
Display and maintenance commands for queue-based accounting
Configuring basic BGP functions
Configuring the route receiver
Configuring basic BGP functions
Enabling QPPB on the route receiving interface
Example: Configuring QPPB in an IPv4 network
Example: Configuring QPPB in an MPLS L3VPN
Example: Configuring QPPB in an IPv6 network
Appendix B Default priority maps
Appendix C Introduction to packet precedence
QoS overview
In data communications, Quality of Service (QoS) provides differentiated service guarantees for diversified traffic in terms of bandwidth, delay, jitter, and drop rate, all of which can affect QoS.
QoS manages network resources and prioritizes traffic to balance system resources.
The following section describes typical QoS service models and widely used QoS techniques.
QoS service models
This section describes several typical QoS service models.
Best-effort service model
The best-effort model is a single-service model. The best-effort model is not as reliable as other models and does not guarantee delay-free delivery.
The best-effort service model is the default model for the Internet and applies to most network applications. It uses the First In First Out (FIFO) queuing mechanism.
IntServ model
The integrated service (IntServ) model is a multiple-service model that can accommodate diverse QoS requirements. This service model provides the most granularly differentiated QoS by identifying and guaranteeing definite QoS for each data flow.
In the IntServ model, an application must request service from the network before it sends data. IntServ signals the service request with the RSVP. All nodes receiving the request reserve resources as requested and maintain state information for the application flow. For more information about RSVP, see MPLS Configuration Guide.
The IntServ model demands high storage and processing capabilities because it requires all nodes along the transmission path to maintain resource state information for each flow. This model is suitable for small-sized or edge networks. However, it is not suitable for large-sized networks, for example, the core layer of the Internet, where billions of flows are present.
DiffServ model
The differentiated service (DiffServ) model is a multiple-service model that can meet diverse QoS requirements. It is easy to implement and extend. DiffServ does not signal the network to reserve resources before sending data, as IntServ does.
QoS techniques in a network
The QoS techniques include the following features:
· Traffic classification.
· Traffic policing.
· Traffic shaping.
· Rate limit.
· Congestion management.
· Congestion avoidance.
The following section briefly introduces these QoS techniques.
All QoS techniques in this document are based on the DiffServ model.
Figure 1 Position of the QoS techniques in a network
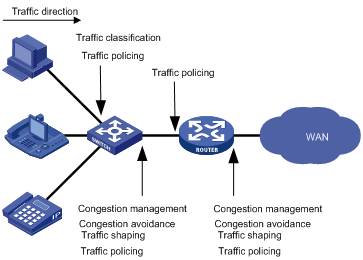
As shown in Figure 1, traffic classification, traffic shaping, traffic policing, congestion management, and congestion avoidance mainly implement the following functions:
· Traffic classification—Uses match criteria to assign packets with the same characteristics to a traffic class. Based on traffic classes, you can provide differentiated services.
· Traffic policing—Polices flows and imposes penalties to prevent aggressive use of network resources. You can apply traffic policing to both incoming and outgoing traffic of a port.
· Traffic shaping—Adapts the output rate of traffic to the network resources available on the downstream device to eliminate packet drops. Traffic shaping usually applies to the outgoing traffic of a port.
· Congestion management—Provides a resource scheduling policy to determine the packet forwarding sequence when congestion occurs. Congestion management usually applies to the outgoing traffic of a port.
· Congestion avoidance—Monitors the network resource usage. It is usually applied to the outgoing traffic of a port. When congestion worsens, congestion avoidance reduces the queue length by dropping packets.
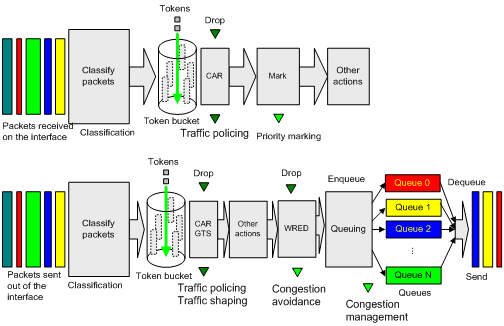
QoS processing flow in a device
Figure 2 briefly describes how the QoS module processes traffic.
1. Traffic classifier identifies and classifies traffic for subsequent QoS actions.
2. The QoS module takes various QoS actions on classified traffic as configured, depending on the traffic processing phase and network status. For example, you can configure the QoS module to perform the following operations:
¡ Traffic policing for incoming traffic.
¡ Traffic shaping for outgoing traffic.
¡ Congestion avoidance before congestion occurs.
¡ Congestion management when congestion occurs.
QoS configuration approaches
You can configure QoS by using the MQC approach or non-MQC approach.
In the modular QoS configuration (MQC) approach, you configure QoS service parameters by using QoS policies. A QoS policy defines QoS actions to take on different classes of traffic and can be applied to an object (such as an interface) to control traffic.
In the non-MQC approach, you configure QoS service parameters without using a QoS policy. For example, you can use the rate limit feature to set a rate limit on an interface without using a QoS policy.
Some features support both approaches, but some support only one.
Configuring a QoS policy
About QoS policies
A QoS policy has the following components:
· Traffic class—Defines criteria to match packets.
· Traffic behavior—Defines QoS actions to take on matching packets.
By associating a traffic class with a traffic behavior, a QoS policy can perform the QoS actions on matching packets.
A QoS policy can have multiple class-behavior associations.
QoS policy tasks at a glance
To configure a QoS policy, perform the following tasks:
2. Defining a traffic behavior
¡ Applying the QoS policy to an interface
¡ Applying the QoS policy to VLANs
¡ Applying the QoS policy globally
¡ Applying the QoS policy to a control plane
Defining a traffic class
1. Enter system view.
system-view
2. Create a traffic class and enter traffic class view.
traffic classifier classifier-name [ operator { and | or } ]
3. Configure a match criterion.
if-match match-criteria
By default, no match criterion is configured.
For more information, see the if-match command in ACL and QoS Command Reference.
Defining a traffic behavior
1. Enter system view.
system-view
2. Create a traffic behavior and enter traffic behavior view.
traffic behavior behavior-name
3. Configure an action in the traffic behavior.
By default, no action is configured for a traffic behavior.
For more information about configuring an action, see the subsequent chapters for traffic policing, traffic filtering, priority marking, class-based accounting, and so on.
Defining a QoS policy
1. Enter system view.
system-view
2. Create a QoS policy and enter QoS policy view.
qos policy policy-name
3. Associate a traffic class with a traffic behavior to create a class-behavior association in the QoS policy.
classifier classifier-name behavior behavior-name [ mode qppb-manipulation | insert-before before-classifier-name ]
By default, a traffic class is not associated with a traffic behavior.
Repeat this step to create more class-behavior associations.
|
Parameter |
Description |
|
qppb-manipulation |
Specifies that a class-behavior association applies only to matching the apply qos-local-id command configuration in a BGP routing policy. For more information, see routing policy configuration in Layer 3—IP Routing Configuration Guide. |
Applying the QoS policy
Application destinations
You can apply a QoS policy to the following destinations:
· Interface—The QoS policy takes effect on the traffic sent or received on the interface.
· VLAN—The QoS policy takes effect on the traffic sent or received on all ports in the VLAN.
· Globally—The QoS policy takes effect on the traffic sent or received on all ports.
· Control plane—The QoS policy takes effect on the traffic received on the control plane.
· User profile—The QoS policy takes effect on the traffic sent or received by the online users of the user profile.
Restrictions and guidelines for applying a QoS policy
You can modify traffic classes, traffic behaviors, and class-behavior associations in a QoS policy even after it is applied (except that it is applied to a user profile). If a traffic class uses an ACL for traffic classification, you can delete or modify the ACL.
Applying the QoS policy to an interface
Restrictions and guidelines
A QoS policy can be applied to multiple interfaces. A maximum of two QoS policies with different priorities and names can be applied to the inbound direction of an interface. Only one QoS policy can be applied to the outbound direction of an interface.
The QoS policy applied to the outgoing traffic on an interface does not regulate local packets. Local packets refer to critical protocol packets sent by the local system for operation maintenance. The most common local packets include link maintenance, IS-IS, OSPF, RIP, BGP, LDP, RSVP, and SSH packets.
You can configure the sharing mode for QoS and ACL resources only if you apply a QoS policy to an interface.
On the following cards, if you apply QoS policies separately to an aggregate interface and a member port of the aggregate interface, the QoS policy applied to the aggregate interface effect:
· CEPC.
· CSPEX.
· CSPC-GE16XP4L-E, CSPC-GE24L-E, and CSPC-GP24GE8XP2L-E.
The QoS policy applied to the member port takes effect after it leaves the aggregation group.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Apply the QoS policy to the interface.
qos apply policy policy-name { inbound | outbound } [ preorder preorder-value ] [ share-mode ]
By default, no QoS policy is applied to an interface.
Applying the QoS policy to VLANs
About QoS policy application to VLANs
You can apply a QoS policy to VLANs to regulate the traffic on all ports of the VLANs.
Restrictions and guidelines
QoS policies cannot be applied to dynamic VLANs, including VLANs created by GVRP.
When you apply a QoS policy to VLANs, the QoS policy is applied to the specified VLANs on all interface cards. If the hardware resources of an interface card are insufficient, applying a QoS policy to VLANs might fail on the interface card. The system does not automatically roll back the QoS policy configuration already applied to the main processing unit or other interface cards. To ensure consistency, use the undo qos vlan-policy command to manually remove the QoS policy configuration applied to them.
Procedure
1. Enter system view.
system-view
2. Apply the QoS policy to VLANs.
qos vlan-policy policy-name vlan vlan-id-list { inbound | outbound }
By default, no QoS policy is applied to a VLAN.
Applying the QoS policy globally
About global QoS policy application
You can apply a QoS policy globally to the inbound or outbound direction of all ports.
Restrictions and guidelines
If the hardware resources of an interface card are insufficient, applying a QoS policy globally might fail on the interface card. The system does not automatically roll back the QoS policy configuration already applied to the main processing unit or other interface cards. To ensure consistency, you must use the undo qos apply policy global command to manually remove the QoS policy configuration applied to them.
Procedure
1. Enter system view.
system-view
2. Apply the QoS policy globally.
qos apply policy policy-name global { inbound | outbound } [ preorder preorder-value ]
By default, no QoS policy is applied globally.
A QoS policy applied in the outbound direction globally does not take effect on CSPC (except CSPC-GE16XP4L-E, CSPC-GE24L-E, and CSPC-GP24GE8XP2L-E) or CMPE-1104 cards.
Applying the QoS policy to a control plane
About the data plane and control plane
A device provides the data plane and the control plane.
· Data plane—The units at the data plane are responsible for receiving, transmitting, and switching (forwarding) packets, such as various dedicated forwarding chips. They deliver super processing speeds and throughput.
· Control plane—The units at the control plane are processing units running most routing and switching protocols. They are responsible for protocol packet resolution and calculation, such as CPUs. Compared with data plane units, the control plane units allow for great packet processing flexibility but have lower throughput.
When the data plane receives packets that it cannot recognize or process, it transmits them to the control plane. If the transmission rate exceeds the processing capability of the control plane, the control plane will be busy handling undesired packets. As a result, the control plane will fail to handle legitimate packets correctly or timely. As a result, protocol performance is affected.
To address this problem, apply a QoS policy to the control plane to take QoS actions, such as traffic filtering or traffic policing, on inbound traffic. This ensures that the control plane can correctly receive, transmit, and process packets.
A predefined control plane QoS policy uses the protocol type or protocol group type to identify the type of packets sent to the control plane. You can use protocol types or protocol group types in if-match commands in traffic class view for traffic classification. Then you can reconfigure traffic behaviors for these traffic classes as required. You can use the display qos policy control-plane pre-defined command to display predefined control plane QoS policies.
Procedure
1. Enter system view.
system-view
2. Enter control plane view.
In standalone mode:
control-plane slot slot-number
In IRF mode:
control-plane chassis chassis-number slot slot-number
3. Apply the QoS policy to the control plane.
qos apply policy policy-name inbound
By default, no QoS policy is applied to a control plane.
Display and maintenance commands for QoS policies
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
(In standalone mode.) Display traffic class configuration. |
display traffic classifier user-defined [ classifier-name ] [ slot slot-number ] |
|
(In IRF mode.) Display traffic class configuration. |
display traffic classifier user-defined [ classifier-name ] [ chassis chassis-number slot slot-number ] |
|
(In standalone mode.) Display traffic behavior configuration. |
display traffic behavior user-defined [ behavior-name ] [ slot slot-number ] |
|
(In IRF mode.) Display traffic behavior configuration. |
display traffic behavior user-defined [ behavior-name ] [ chassis chassis-number slot slot-number ] |
|
(In standalone mode.) Display QoS and ACL resource usage. |
display qos-acl resource [ slot slot-number ] |
|
(In IRF mode.) Display QoS and ACL resource usage. |
display qos-acl resource [ chassis chassis-number slot slot-number ] |
|
(In standalone mode.) Display QoS policy configuration. |
display qos policy user-defined [ policy-name [ classifier classifier-name ] ] [ slot slot-number ] |
|
(In IRF mode.) Display QoS policy configuration. |
display qos policy user-defined [ policy-name [ classifier classifier-name ] ] [ chassis chassis-number slot slot-number ] |
|
(In standalone mode.) Display information about QoS policies applied to interfaces. |
display qos policy interface [ interface-type interface-number ] [ slot slot-number | all ] [ inbound | outbound ] |
|
(In IRF mode.) Display information about QoS policies applied to interfaces. |
display qos policy interface [ interface-type interface-number ] [ chassis chassis-number slot slot-number | all ] [ inbound | outbound ] |
|
(In standalone mode.) Display information about QoS policies applied to user profiles. |
display qos policy user-profile [ name profile-name ] [ user-id user-id ] [ slot slot-number ] [ inbound | outbound ] |
|
(In IRF mode.) Display information about QoS policies applied to user profiles. |
display qos policy user-profile [ name profile-name ] [ user-id user-id ] [ chassis chassis-number slot slot-number ] [ inbound | outbound ] |
|
(In standalone mode.) Display information about QoS policies applied to VLANs. |
display qos vlan-policy { name policy-name | vlan [ vlan-id ] } [ slot slot-number ] [ inbound | outbound ] |
|
(In IRF mode.) Display information about QoS policies applied to VLANs. |
display qos vlan-policy { name policy-name | vlan [ vlan-id ] } [ chassis chassis-number slot slot-number ] [ inbound | outbound ] |
|
(In standalone mode.) Display information about QoS policies applied globally. |
display qos policy global [ slot slot-number ] [ inbound | outbound ] |
|
(In IRF mode.) Display information about QoS policies applied globally. |
display qos policy global [ chassis chassis-number slot slot-number ] [ inbound | outbound ] |
|
(In standalone mode.) Display information about QoS policies applied to a control plane. |
display qos policy control-plane slot slot-number |
|
(In IRF mode.) Display information about QoS policies applied to a control plane. |
display qos policy control-plane chassis chassis-number slot slot-number |
|
(In standalone mode.) Display information about the predefined QoS policy applied to the control plane. |
display qos policy control-plane pre-defined [ slot slot-number ] |
|
(In IRF mode.) Display information about the predefined QoS policy applied to the control plane. |
display qos policy control-plane pre-defined [ chassis chassis-number slot slot-number ] |
|
Clear the statistics of the QoS policy applied in a certain direction of a VLAN. |
reset qos vlan-policy [ vlan vlan-id ] [ inbound | outbound ] |
|
Clear the statistics for a QoS policy applied globally. |
reset qos policy global [ inbound | outbound ] |
|
(In standalone mode.) Clear the statistics for the QoS policy applied to a control plane. |
reset qos policy control-plane slot slot-number |
|
(In IRF mode.) Clear the statistics for the QoS policy applied to a control plane. |
reset qos policy control-plane chassis chassis-number slot slot-number |
Setting the exclusive bandwidth on an interface
About setting the exclusive bandwidth
The exclusive bandwidth on an interface is reserved for specific features and cannot be shared with other features. The amount of exclusive bandwidth is deducted from the interface bandwidth.
Restrictions and guidelines
The exclusive bandwidth feature is mutually exclusive with the HQoS feature. If one feature has been configured on an interface, the other feature cannot be configured successfully.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Set the exclusive bandwidth on the interface.
qos exclusive-bandwidth bandwidth-value
By default, no exclusive bandwidth is set on an interface.
Display and maintenance commands for exclusive bandwidth
Execute display commands in any view.
|
Task |
Command |
|
(Distributed devices in standalone mode.) Display exclusive bandwidth settings for interfaces. |
display qos exclusive-bandwidth interface [ interface-type interface-number ] outbound [ slot slot-number ] |
|
(Distributed devices in IRF mode.) Display exclusive bandwidth settings for interfaces. |
display qos exclusive-bandwidth interface [ interface-type interface-number ] outbound [ chassis chassis-number slot slot-number ] |
Configuring priority mapping
About priority mapping
When a packet arrives, a device assigns a set of QoS priority parameters to the packet based on either of the following:
· A priority field carried in the packet.
· The port priority of the incoming port.
This process is called priority mapping. During this process, the device can modify the priority of the packet according to the priority mapping rules. The set of QoS priority parameters decides the scheduling priority and forwarding priority of the packet.
Priority mapping is implemented with priority maps and involves the following priorities:
· 802.1p priority.
· DSCP.
· EXP.
· IP precedence.
· Local precedence.
· Drop priority.
About priorities
Priorities include the following types: priorities carried in packets, and priorities locally assigned for scheduling only.
Packet-carried priorities include 802.1p priority, DSCP precedence, IP precedence, and EXP. These priorities have global significance and affect the forwarding priority of packets across the network. For more information about these priorities, see "Appendixes."
Locally assigned priorities only have local significance. They are assigned by the device only for scheduling. These priorities include the local precedence, drop priority, and user priority, as follows:
· Local precedence—Used for queuing. A local precedence value corresponds to an output queue. A packet with higher local precedence is assigned to a higher priority output queue to be preferentially scheduled.
· Drop priority—Used for making packet drop decisions. Packets with the highest drop priority are dropped preferentially.
· User priority—Precedence that the device automatically extracts from a priority field of the packet according to its forwarding path. It is a parameter for determining the scheduling priority and forwarding priority of the packet. The user priority represents the following items:
¡ The 802.1p priority for Layer 2 packets.
¡ The IP precedence for Layer 3 packets.
¡ The EXP for MPLS packets.
Priority maps
The device provides various types of priority maps. By looking through a priority map, the device decides which priority value to assign to a packet for subsequent packet processing.
The default priority maps (as shown in Appendix B Default priority maps) are available for priority mapping. They are adequate in most cases. If a default priority map cannot meet your requirements, you can modify the priority map as required.
Priority mapping configuration methods
You can configure priority mapping by using any of the following methods:
· Configuring priority trust mode—In this method, you can configure a port to look up a trusted priority type (802.1p, for example) in incoming packets in the priority maps. Then, the system maps the trusted priority to the target priority types and values.
· Changing port priority—If no packet priority is trusted, the port priority of the incoming port is used. By changing the port priority of a port, you change the priority of the incoming packets on the port.
· Configuring a QoS policy containing the priority mapping (called primap) action with the primap command.
Priority mapping process
On receiving an Ethernet packet on a port, the switch marks the scheduling priorities (local precedence and drop precedence) for the Ethernet packet. This procedure is done according to the priority trust mode of the receiving port and the 802.1Q tagging status of the packet, as shown in Figure 3.
Figure 3 Priority mapping process for an Ethernet packet
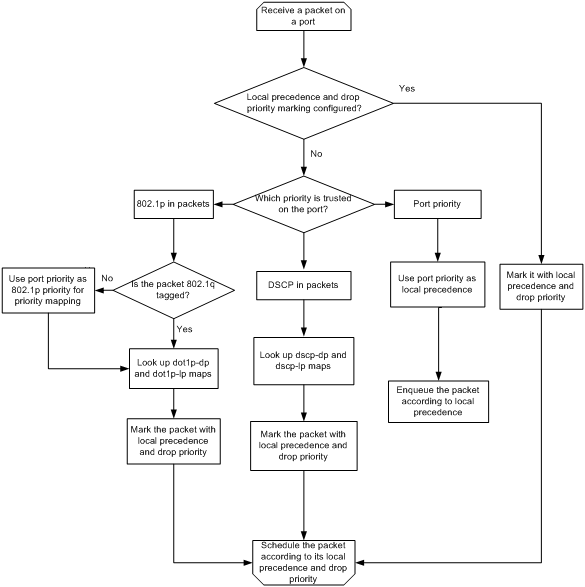
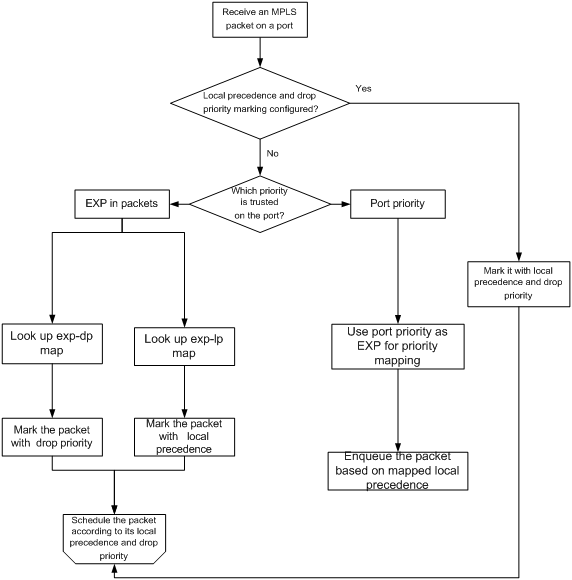
The switch marks a received MPLS packet with a scheduling priority based on the priority trust mode and the packet EXP value, as shown in Figure 4.
Figure 4 Priority mapping process for an MPLS packet
For information about priority marking, see "Configuring priority marking."
Restrictions and guidelines
If all member ports of a Layer 3 aggregate interface are on CSPEX (except CSPEX-1204 and CSPEX-1104-E) and CEPC cards, you can configure a flexible priority map, the auto priority trust mode, and the port priority for the Layer 3 aggregate interface or subinterface. The flexible priority map, the auto priority trust mode, and the port priority settings for the Layer 3 aggregate interface or subinterface takes priority over these settings on its member ports.
Priority mapping tasks at a glance
To configure priority mapping, perform the following tasks:
1. (Optional.) Configuring a priority map
¡ Configuring an uncolored priority map
¡ Configuring a colored priority map
¡ Configuring a flexible priority map for an interface
2. Configure a priority mapping method:
¡ Configuring the priority trust mode
¡ Changing the port priority of an interface
¡ Configuring colored primap
Configuring a priority map
About priority maps
Table 1 shows the priority maps provided by the device. These priority maps can be colored or uncolored.
You can use colored priority maps if the packets are colored by traffic policing. You can use uncolored priority maps if the packets are not colored by traffic policing. For how traffic policing processes and colors packets, see "About traffic policing, GTS, and rate limit."
|
Priority map |
Description |
|
dot1p-dot1p |
802.1p-802.1p priority map. |
|
dot1p-dp |
802.1p-drop priority map. |
|
dot1p-dscp |
802.1p-DSCP priority map. |
|
dot1p-exp |
802.1p-EXP priority map. |
|
dot1p-lp |
802.1p-local priority map. |
|
dscp-dot1p |
DSCP-802.1p priority map. |
|
dscp-dp |
DSCP-drop priority map. |
|
dscp-dscp |
DSCP-DSCP priority map. |
|
dscp-exp |
DSCP-EXP priority map. |
|
dscp-lp |
DSCP-local priority map. |
|
exp-dot1p |
EXP-802.1p priority map. |
|
exp-dp |
EXP-drop priority map. |
|
exp-dscp |
EXP-DSCP priority map. |
|
exp-exp |
EXP-EXP priority map. |
|
exp-lp |
EXP-local priority map. |
|
lp-dot1p |
Local-802.1p priority map. |
|
lp-dp |
Local-drop priority map. |
|
lp-dscp |
Local-DSCP priority map. |
|
lp-exp |
Local-EXP priority map. |
|
lp-phb |
Local-PHP priority map. |
Configuring an uncolored priority map
1. Enter system view.
system-view
2. Enter priority map view.
qos map-table inbound { dot1p-dot1p | dot1p-dp | dot1p-dscp | dot1p-exp | dot1p-lp | dscp-dot1p | dscp-dp | dscp-dscp | dscp-exp | dscp-lp | exp-dot1p | exp-dp | exp-dscp | exp-exp | exp-lp }
CSPC (except CSPC-GE16XP4L-E, CSPC-GE24L-E, and CSPC-GP24GE8XP2L-E) and CMPE-1104 cards do not support the following priority maps:
¡ dot1p-dot1p
¡ dot1p-dscp
¡ dot1p-exp
¡ dscp-exp
¡ dscp-lp
¡ exp-dscp
¡ exp-dp
¡ exp-exp
¡ exp-lp
3. Configure mappings for the priority map.
import import-value-list export export-value
By default, the default priority maps are used. For more information, see "Uncolored priority maps."
If you execute this command multiple times, the most recent configuration takes effect.
Configuring a colored priority map
1. Enter system view.
system-view
2. Enter colored priority map view.
qos map-table color { green | yellow | red } { inbound { dot1p-dot1p | dot1p-dp | dot1p-dscp | dot1p-exp | dot1p-lp | dscp-dot1p | dscp-dp | dscp-dscp | dscp-exp | dscp-lp | exp-dot1p | exp-dp | exp-dscp | exp-exp | exp-lp } | outbound { dot1p-dot1p | dot1p-dscp | dot1p-exp | dscp-dot1p | dscp-dscp | dscp-exp | exp-dot1p | exp-dscp | exp-exp } }
CSPC (except CSPC-GE16XP4L-E, CSPC-GE24L-E, and CSPC-GP24GE8XP2L-E) and CMPE-1104 cards do not support colored priority maps.
3. Configure mappings for the colored priority map.
import import-value-list export export-value
By default, the default colored priority maps are used. For more information, see "Colored priority maps."
If you execute this command multiple times, the most recent configuration takes effect.
Configuring a flexible priority map for an interface
About flexible priority maps
An uncolored or colored priority map takes effect on the device globally. A flexible priority map can be applied on a per-interface basis for controlling packet scheduling and forwarding more accurately.
Restrictions and guidelines
If you both configure a priority map in priority map view and apply a flexible priority map to an interface, the flexible priority map takes effect on the interface.
Procedure
1. Enter system view.
system-view
2. Create a flexible priority map and enter its view.
qos map-table name map-table-name
3. Configure mappings for the flexible priority map.
{ dot1p-dot1p | dot1p-dp | dot1p-dscp | dot1p-exp | dot1p-lp | dscp-dot1p | dscp-dp | dscp-dscp | dscp-exp | dscp-lp | exp-dot1p | exp-dp | exp-dscp | exp-exp | exp-lp | lp-dot1p | lp-dp | lp-dscp | lp-exp | lp-phb } import import-value-list export export-value
By default, no mapping is configured in a flexible priority map.
If you execute this command multiple times and enter the same input values for one priority map, the most recent configuration takes effect.
4. Return to system view.
quit
5. Enter interface view.
interface interface-type interface-number
6. Apply the flexible priority map to the interface.
qos apply map-table map-table-name [ inbound | outbound ]
If you do not specify a direction, the inbound direction applies. Only one priority map can be applied to one direction of an interface.
Only the following priority maps can be applied to the inbound direction of an interface:
¡ dot1p-dot1p
¡ dot1p-dp
¡ dot1p-dscp
¡ dot1p-exp
¡ dot1p-lp
¡ dscp-dot1p
¡ dscp-dp
¡ dscp-dscp
¡ dscp-exp
¡ dscp-lp
¡ exp-dot1p
¡ exp-dp
¡ exp-dscp
¡ exp-exp
¡ exp-lp
Only the following priority maps can be applied to the outbound direction of an interface:
¡ lp-dot1p
¡ lp-dp
¡ lp-dscp
¡ lp-exp
¡ lp-php
Configuring the priority trust mode
About configuring the priority trust mode
You can configure the device to trust priority fields carried in packets for priority mapping. When you configure the trusted packet priority type on an interface, use the following available keywords:
· auto—Automatically selects the priority of each received packet according to packet type for mapping.
¡ On CSPC (except CSPC-GE16XP4L-E, CSPC-GE24L-E, and CSPC-GP24GE8XP2L-E) and CMPE-1104 cards:
- For non-IP packets, the 802.1p priority is used.
- For IP packets, the IP precedence is used.
- For MPLS packets, the EXP value is used.
¡ On CSPC-GE16XP4L-E, CSPC-GE24L-E, CSPC-GP24GE8XP2L-E, CSPEX, and CEPC cards:
- For Layer 2 packets, the 802.1p priority is used.
- For Layer 3 packets, the IP precedence is used.
- For MPLS packets, the EXP value is used.
· dot1p—Uses the 802.1p priority of received packets for mapping.
· dscp—Uses the DSCP precedence of received IP packets for mapping.
· inner-dot1p—Uses the inner 802.1p priority of received QinQ packets for mapping.
Restrictions and guidelines
On CSPC (except CSPC-GE16XP4L-E, CSPC-GE24L-E, and CSPC-GP24GE8XP2L-E) and CMPE-1104 cards, you must specify the override keyword when configuring the qos trust auto command.
The dot1p, dscp, and inner-dot1p keywords are available only on CSPEX (except CSPEX-1204 and CSPEX-1104-E) and CEPC cards.
When an IP packet enters an MPLS network, the device populates the EXP field with the EXP value derived from a priority map even if the override keyword is not specified.
For a Layer 3 packet, the device overwrites the 802.1p priority value in the packet with the 802.1p priority value derived from a priority map even if the override keyword is not specified.
For an MPLS packet that comes from the public network, he device uses the EXP value in the packet for priority mapping instead of trusting the configured 802.1p or DSCP priority.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Configure the priority trust mode.
qos trust { auto | dot1p | dscp | inner-dot1p } [ override ]
By default, a port does not trust any packet priority and uses the port priority based on the packet type for priority mapping.
Changing the port priority of an interface
About port priority
If the auto priority trust mode is not configured, the device uses its port priority to look for priority parameters for the incoming packets. By changing port priority, you can prioritize traffic received on different interfaces.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Set the port priority of the interface.
qos priority { dot1p | dscp | exp } priority-value
The default setting is 0.
The dot1p, dscp, and exp keywords are available only on CSPC-GE16XP4L-E, CSPC-GE24L-E, CSPC-GP24GE8XP2L-E, CSPEX, and CEPC cards.
Configuring colored primap
About primap
To reassign priority parameters for a traffic class according to a priority mapping table, configure a primap traffic behavior and associate it with the traffic class.
Restrictions and guidelines
The device supports the following application destinations for primap:
· Interface.
· VLANs.
· Globally.
· Control plane.
· User profile.
Procedure
1. Enter system view.
system-view
2. Define a traffic class.
a. Create a traffic class and enter traffic class view.
traffic classifier classifier-name [ operator { and | or } ]
b. Configure a match criterion.
if-match match-criteria
By default, no match criterion is configured.
c. Return to system view.
quit
3. Define a traffic behavior.
a. Create a traffic behavior and enter traffic behavior view.
traffic behavior behavior-name
b. Configure a CAR action.
car cir committed-information-rate [ cbs committed-burst-size [ ebs excess-burst-size ] ] [ green action | red action | yellow action ] *
car cir committed-information-rate [ cbs committed-burst-size ] pir peak-information-rate [ ebs excess-burst-size ] [ green action | red action | yellow action ] *
By default, no CAR action is configured.
c. Configure the action of assigning priority values to packets using a specified colored priority mapping table.
primap pre-defined color { dot1p-dot1p | dot1p-dp | dot1p-dscp | dot1p-exp | dot1p-lp | dscp-dot1p | dscp-dp | dscp-dscp | dscp-exp | dscp-lp | exp-dot1p | exp-dp | exp-dscp | exp-exp | exp-lp }
By default, no priority mapping action is configured.
d. (Optional.) Configure the action of assigning drop priority to packets according to packet color.
primap color-map-dp
By default, no priority mapping action is configured.
The packet color-to-drop priority mappings are fixed to red to 2, yellow to 1, and green to 0.
This action can be used only in the outbound direction.
e. Return to system view.
quit
4. Define a QoS policy.
a. Create a QoS policy and enter QoS policy view.
qos policy policy-name
b. Associate the traffic behavior with the traffic class.
classifier classifier-name behavior behavior-name
By default, a traffic class is not associated with a traffic behavior.
c. Return to system view.
quit
5. Apply the QoS policy.
For more information, see "Applying the QoS policy."
By default, no QoS policy is applied.
Display and maintenance commands for priority mapping
Execute display commands in any view.
|
Task |
Command |
|
Display priority map configuration. |
display qos map-table inbound [ dot1p-dot1p | dot1p-dp | dot1p-dscp | dot1p-exp | dot1p-lp | dscp-dot1p | dscp-dp | dscp-dscp | dscp-exp | dscp-lp | exp-dot1p | exp-dp | exp-dscp | exp-exp | exp-lp ] |
|
Display colored priority map configuration. |
display qos map-table color [ green | yellow | red ] { inbound [ dot1p-dot1p | dot1p-dp | dot1p-dscp | dot1p-exp | dot1p-lp | dscp-dot1p | dscp-dp | dscp-dscp | dscp-exp | dscp-lp | exp-dot1p | exp-dp | exp-dscp | exp-exp | exp-lp ] | outbound [ dot1p-dot1p | dot1p-dscp | dot1p-exp | dscp-dot1p | dscp-dscp | dscp-exp | exp-dot1p | exp-dscp | exp-exp ] } |
|
Display flexible priority map configuration. |
display qos map-table name [ map-table-name ] |
|
Display flexible priority maps applied to interfaces. |
display qos map-table interface [ interface-type interface-number ] [ inbound | outbound ] |
|
Display the trusted packet priority type on a port. |
display qos trust interface [ interface-type interface-number ] |
Priority mapping configuration examples
Example: Configuring a priority trust mode
Network configuration
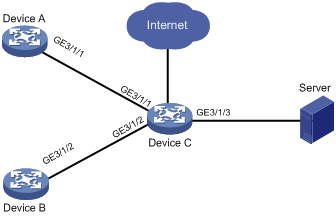
As shown in Figure 5:
· The 802.1p priority of traffic from Device A to Device C is 3.
· The 802.1p priority of traffic from Device B to Device C is 1.
Procedure
# Assign port priority to GigabitEthernet 3/1/1 and GigabitEthernet 3/1/2. Make sure the following requirements are met:
· The priority of GigabitEthernet 3/1/1 is higher than that of GigabitEthernet 3/1/2.
· The auto priority trust mode is not configured on GigabitEthernet 3/1/1 or GigabitEthernet 3/1/2.
<DeviceC> system-view
[DeviceC] interface gigabitethernet 3/1/1
[DeviceC-GigabitEthernet3/1/1] qos priority 3
[DeviceC-GigabitEthernet3/1/1] quit
[DeviceC] interface gigabitethernet 3/1/2
[DeviceC-GigabitEthernet3/1/2] qos priority 1
[DeviceC-GigabitEthernet3/1/2] quit
Example: Configuring priority mapping tables and priority marking
Network configuration
As shown in Figure 6:
· The Marketing department connects to GigabitEthernet 3/1/1 of Device, which sets the DSCP priority of traffic from the Marketing department to 18.
· The R&D department connects to GigabitEthernet 3/1/2 of Device, which sets the DSCP priority of traffic from the R&D department to 55.
· The Management department connects to GigabitEthernet 3/1/3 of Device, which sets the DSCP priority of traffic from the Management department to 38.
Configure port priority, 802.1p-to-local mapping table, and priority marking to implement the plan as described in Table 2.
|
Traffic destination |
Traffic priority order |
Queuing plan |
||
|
Traffic source |
Output queue |
Queue priority |
||
|
Public servers |
R&D department > Management department > Marketing department |
R&D department |
6 |
High |
|
Management department |
4 |
Medium |
||
|
Marketing department |
2 |
Low |
||
|
Internet |
Management department > Marketing department > R&D department |
R&D department |
2 |
Low |
|
Management department |
6 |
High |
||
|
Marketing department |
3 |
Medium |
||
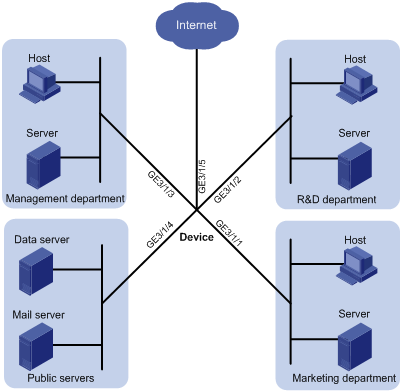
Procedure
1. Configure trusting port priority:
# Set the port priority of GigabitEthernet 3/1/1 to 18.
<Device> system-view
[Device] interface gigabitethernet 3/1/1
[Device-GigabitEthernet3/1/1] qos priority dscp 18
[Device-GigabitEthernet3/1/1] quit
# Set the port priority of GigabitEthernet 3/1/2 to 55.
[Device] interface gigabitethernet 3/1/2
[Device-GigabitEthernet3/1/2] qos priority dscp 55
[Device-GigabitEthernet3/1/2] quit
# Set the port priority of GigabitEthernet 3/1/3 to 38.
[Device] interface gigabitethernet 3/1/3
[Device-GigabitEthernet3/1/3] qos priority dscp 38
[Device-GigabitEthernet3/1/3] quit
According to the default dscp-lp mapping table, DSCP values 18, 55, 38 correspond to to local precedence values 2, 6, and 4, respectively.
This guarantees the R&D department, Management department, and Marketing department decreased priorities to access the public servers.
2. Configure priority marking to mark the packets from Management department, Marketing department, and R&D department to the Internet with local precedence values 6, 3, and 2.
This guarantees the Management department, Marketing department, and R&D department decreased priorities to access the Internet.
# Create ACL 3000, and configure a rule to match HTTP packets.
[Device] acl advanced 3000
[Device-acl-adv-3000] rule permit tcp destination-port eq 80
[Device-acl-adv-3000] quit
# Create a traffic class named http, and use ACL 3000 as a match criterion.
[Device] traffic classifier http
[Device-classifier-http] if-match acl 3000
[Device-classifier-http] quit
# Create a traffic behavior named admin, and configure a marking action for the Management department.
[Device] traffic behavior admin
[Device-behavior-admin] remark local-precedence 6
[Device-behavior-admin] quit
# Create a QoS policy named admin, and associate traffic class http with traffic behavior admin in QoS policy admin.
[Device] qos policy admin
[Device-qospolicy-admin] classifier http behavior admin
[Device-qospolicy-admin] quit
# Apply QoS policy admin to the inbound direction of Gigabitethernet 3/1/3.
[Device] interface gigabitethernet 3/1/3
[Device-Gigabitethernet3/1/3] qos apply policy admin inbound
# Create a traffic behavior named market, and configure a marking action for the Marketing department.
[Device] traffic behavior market
[Device-behavior-market] remark local-precedence 3
[Device-behavior-market] quit
# Create a QoS policy named market, and associate traffic class http with traffic behavior market in QoS policy market.
[Device] qos policy market
[Device-qospolicy-market] classifier http behavior market
[Device-qospolicy-market] quit
# Apply QoS policy market to the inbound direction of Gigabitethernet 3/1/1.
[Device] interface gigabitethernet 3/1/1
[Device-Gigabitethernet3/1/1] qos apply policy market inbound
# Create a traffic behavior named rd, and configure a marking action for the R&D department.
[Device] traffic behavior rd
[Device-behavior-rd] remark local-precedence 2
[Device-behavior-rd] quit
# Create a QoS policy named rd, and associate traffic class http with traffic behavior rd in QoS policy rd.
[Device] qos policy rd
[Device-qospolicy-rd] classifier http behavior rd
[Device-qospolicy-rd] quit
# Apply QoS policy rd to the inbound direction of Gigabitethernet 3/1/2.
[Device] interface gigabitethernet 3/1/2
[Device-Gigabitethernet3/1/2] qos apply policy rd inbound
Configuring traffic policing, GTS, and rate limit
About traffic policing, GTS, and rate limit
Traffic limit helps assign network resources (including bandwidth) and increase network performance. For example, you can configure a flow to use only the resources committed to it in a certain time range. This avoids network congestion caused by burst traffic.
Traffic policing, Generic Traffic Shaping (GTS), and rate limit control the traffic rate and resource usage according to traffic specifications. You can use token buckets for evaluating traffic specifications.
Traffic evaluation and token buckets
Token bucket features
A token bucket is analogous to a container that holds a certain number of tokens. Each token represents a certain forwarding capacity. The system puts tokens into the bucket at a constant rate. When the token bucket is full, the extra tokens cause the token bucket to overflow.
Evaluating traffic with the token bucket
A token bucket mechanism evaluates traffic by looking at the number of tokens in the bucket. If the number of tokens in the bucket is enough for forwarding the packets:
· The traffic conforms to the specification (called conforming traffic).
· The corresponding tokens are taken away from the bucket.
Otherwise, the traffic does not conform to the specification (called excess traffic).
A token bucket has the following configurable parameters:
· Mean rate at which tokens are put into the bucket, which is the permitted average rate of traffic. It is usually set to the committed information rate (CIR).
· Burst size or the capacity of the token bucket. It is the maximum traffic size permitted in each burst. It is usually set to the committed burst size (CBS). The set burst size must be greater than the maximum packet size.
Each arriving packet is evaluated.
Complicated evaluation
You can set two token buckets, bucket C and bucket E, to evaluate traffic in a more complicated environment and achieve more policing flexibility. The following are main mechanisms used for complicated evaluation:
· Single rate two color—Uses one token bucket and the following parameters:
¡ CIR—Rate at which tokens are put into bucket C. It sets the average packet transmission or forwarding rate allowed by bucket C.
¡ CBS—Size of bucket C, which specifies the transient burst of traffic that bucket C can forward.
When a packet arrives, the following rules apply:
¡ If bucket C has enough tokens to forward the packet, the packet is colored green.
¡ Otherwise, the packet is colored red.
· Single rate three color—Uses two token buckets and the following parameters:
¡ CIR—Rate at which tokens are put into bucket C. It sets the average packet transmission or forwarding rate allowed by bucket C.
¡ CBS—Size of bucket C, which specifies the transient burst of traffic that bucket C can forward.
¡ EBS—Size of bucket E minus size of bucket C, which specifies the transient burst of traffic that bucket E can forward. The EBS cannot be 0. The size of E bucket is the sum of the CBS and EBS.
When a packet arrives, the following rules apply:
¡ If bucket C has enough tokens, the packet is colored green.
¡ If bucket C does not have enough tokens but bucket E has enough tokens, the packet is colored yellow.
¡ If neither bucket C nor bucket E has sufficient tokens, the packet is colored red.
· Two rate three color—Uses two token buckets and the following parameters:
¡ CIR—Rate at which tokens are put into bucket C. It sets the average packet transmission or forwarding rate allowed by bucket C.
¡ CBS—Size of bucket C, which specifies the transient burst of traffic that bucket C can forward.
¡ PIR—Rate at which tokens are put into bucket E, which specifies the average packet transmission or forwarding rate allowed by bucket E.
¡ EBS—Size of bucket E, which specifies the transient burst of traffic that bucket E can forward.
When a packet arrives, the following rules apply:
¡ If bucket C has enough tokens, the packet is colored green.
¡ If bucket C does not have enough tokens but bucket E has enough tokens, the packet is colored yellow.
¡ If neither bucket C nor bucket E has sufficient tokens, the packet is colored red.
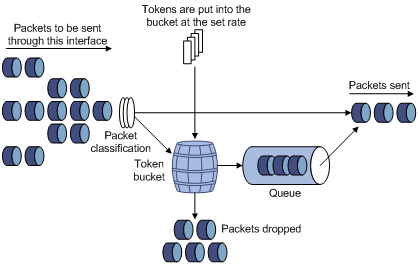
Traffic policing
Traffic policing supports policing the inbound traffic and the outbound traffic.
A typical application of traffic policing is to supervise the specification of traffic entering a network and limit it within a reasonable range. Another application is to "discipline" the extra traffic to prevent aggressive use of network resources by an application. For example, you can limit bandwidth for HTTP packets to less than 50% of the total. If the traffic of a session exceeds the limit, traffic policing can drop the packets or reset the IP precedence of the packets. Figure 7 shows an example of policing outbound traffic on an interface.
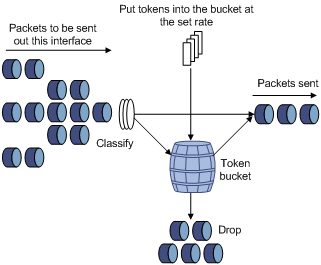
Traffic policing is widely used in policing traffic entering the ISP networks. It can classify the policed traffic and take predefined policing actions on each packet depending on the evaluation result:
· Forwarding the packet if the evaluation result is "conforming."
· Dropping the packet if the evaluation result is "excess."
· Forwarding the packet with its precedence re-marked if the evaluation result is "conforming."
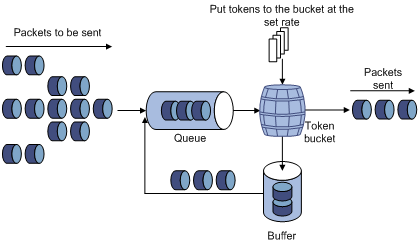
GTS
GTS supports shaping the outbound traffic. GTS limits the outbound traffic rate by buffering exceeding traffic. You can use GTS to adapt the traffic output rate on a device to the input traffic rate of its connected device to avoid packet loss.
The differences between traffic policing and GTS are as follows:
· Packets to be dropped with traffic policing are retained in a buffer or queue with GTS, as shown in Figure 8. When enough tokens are in the token bucket, the buffered packets are sent at an even rate.
· GTS can result in additional delay and traffic policing does not.
For example, in Figure 9, Device B performs traffic policing on packets from Device A and drops packets exceeding the limit. To avoid packet loss, you can perform GTS on the outgoing interface of Device A so that packets exceeding the limit are cached in Device A. Once resources are released, GTS takes out the cached packets and sends them out.

Rate limit
The rate limit of an interface specifies the maximum rate for sending packets (excluding critical packets).
Rate limit also uses token buckets for traffic control. When rate limit is configured on an interface, a token bucket handles all packets to be sent through the interface for rate limiting. If enough tokens are in the token bucket, packets can be forwarded. Otherwise, packets are put into QoS queues for congestion management. In this way, the traffic passing the interface is controlled.
Figure 10 Rate limit implementation
The token bucket mechanism limits traffic rate when accommodating bursts. It allows bursty traffic to be transmitted if enough tokens are available. If tokens are scarce, packets cannot be transmitted until efficient tokens are generated in the token bucket. It restricts the traffic rate to the rate for generating tokens.
Rate limit controls the total rate of all packets on an interface. It is easier to use than traffic policing in controlling the total traffic rate.
Configuring traffic policing
Traffic policing configuration approaches
You can configure traffic policing by using the MQC approach or the non-MQC approach. If both approaches are used, the MQC configuration takes effect.
You can configure the following types of traffic policing by using the non-MQC approach:
· Traffic policing for a user profile.
· Traffic policing for a control plane.
Configuring traffic policing by using the MQC approach
Restrictions and guidelines
The device supports the following application destinations for traffic policing:
· Interface.
· VLANs.
· Globally.
· Control plane.
· User profile.
Procedure
1. Enter system view.
system-view
2. Define a traffic class.
a. Create a traffic class and enter traffic class view.
traffic classifier classifier-name [ operator { and | or } ]
b. Configure a match criterion.
if-match match-criteria
By default, no match criterion is configured.
For more information about the if-match command, see ACL and QoS Command Reference.
c. Return to system view.
quit
3. Define a traffic behavior.
a. Create a traffic behavior and enter traffic behavior view.
traffic behavior behavior-name
b. Configure a traffic policing action.
car cir committed-information-rate [ cbs committed-burst-size [ ebs excess-burst-size ] ] [ green action | red action | yellow action ] *
car cir committed-information-rate [ cbs committed-burst-size ] pir peak-information-rate [ ebs excess-burst-size ] [ green action | red action | yellow action ] *
By default, no traffic policing action is configured.
Only the pass action is supported for green packets and yellow packets on CSPC-GE16XP4L-E, CSPC-GE24L-E, CSPC-GP24GE8XP2L-E, CSPEX, and CEPC cards.
Only the discard and pass actions are supported for red packets on CSPC-GE16XP4L-E, CSPC-GE24L-E, CSPC-GP24GE8XP2L-E, CSPEX, and CEPC cards.
If you set the cir committed-information-rate option to a value in the range of 1 to 8 kbps on , the actual setting takes effect. If you set this option to a value in the range of 1 to 8 kbps on any other card, 8 kbps always takes effect.
In a traffic policing action applied to a control plane, the supported value range for the cir committed-information-rate option is 8 to 10000 kbps.
c. Return to system view.
quit
4. Define a QoS policy.
a. Create a QoS policy and enter QoS policy view.
qos policy policy-name
b. Associate the traffic class with the traffic behavior in the QoS policy.
classifier classifier-name behavior behavior-name
By default, a traffic class is not associated with a traffic behavior.
c. Return to system view.
quit
5. Apply the QoS policy.
For more information, see "Applying the QoS policy."
By default, no QoS policy is applied.
Configuring traffic policing for a user profile
About traffic policing for a user profile
When a user profile is configured, you can perform traffic policing based on users. After a user passes authentication, the authentication server sends the name of the user profile associated with the user to the device. When any user of the user profile logs in, the authentication server automatically applies the CAR parameters configured for the user profile to the user. When the user logs off, the system automatically removes the CAR configuration without manual intervention.
Procedure
1. Enter system view.
system-view
2. Enter user profile view.
user-profile profile-name
3. Configure a CAR policy for the user profile.
qos car { inbound | outbound } any cir committed-information-rate [ cbs committed-burst-size [ ebs excess-burst-size ] ]
qos car { inbound | outbound } any cir committed-information-rate [ cbs committed-burst-size ] pir peak-information-rate [ ebs excess-burst-size ]
By default, no CAR policy is configured for a user profile.
Configuring traffic policing for a control plane
About traffic policing for a control plane
You can configure the following types of traffic policing for a control plane:
· Traffic policing for all traffic—Polices all control plane traffic.
· Online user-based traffic policing—Polices the control plane traffic from all online users.
· Whitelist-based traffic policing—Polices the control plane traffic that matches the dynamic whitelist by using the system-defined traffic policing parameters.
If multiple types of traffic policing for a control plane are configured, they take effect at the same time. When the control plane is congested, the traffic that matches the dynamic whitelist is preferentially sent to the control plane.
This feature is available only on CSPEX (except CSPEX-1204 and CSPEX-1104-E) and CEPC cards.
For more information about control planes, see "Applying the QoS policy to a control plane."
Procedure
1. Enter system view.
system-view
2. Enter control plane view.
In standalone mode:
control-plane slot slot-number
In IRF mode:
control-plane chassis chassis-number slot slot-number
3. (Optional.) Enable whitelist-based traffic policing.
qos car whitelist [ ipv6 ] enable
By default, whitelist-based traffic policing is enabled, and the device uses the default rate limit values to police matching traffic.
4. Configure a CAR policy for the control plane.
¡ Configure a CAR policy for all traffic.
qos car any cir committed-information-rate [ cbs committed-burst-size [ ebs excess-burst-size ] ]
qos car any cir committed-information-rate [ cbs committed-burst-size ] pir peak-information-rate [ ebs excess-burst-size ]
By default, no CAR policy is configured for all traffic.
¡ Configure an online user-based CAR policy.
qos car user cir committed-information-rate [ cbs committed-burst-size [ ebs excess-burst-size ] ]
qos car user cir committed-information-rate [ cbs committed-burst-size ] pir peak-information-rate [ ebs excess-burst-size ]
By default, no online user-based CAR policy is configured.
Configuring GTS
Configuring queue-based GTS
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Configure GTS for a queue.
qos gts queue queue-id cir committed-information-rate [ cbs committed-burst-size ]
By default, GTS is not configured on an interface.
For this command to take effect on a Layer 3 aggregate interface or subinterface, make sure all its member ports are on CSPEX (except CSPEX-1204 and CSPEX-1104-E) and CEPC cards.
On CSPC-GE16XP4L-E, CSPC-GE24L-E, CSPC-GP24GE8XP2L-E, CSPEX-1104-E, and CSPEX-1204 cards, you cannot configure both queue-based GTS and a queue scheduling profile with WRR queuing for the same interface.
Configuring GTS for a user group profile
About traffic policing for a user group profile
When a user group profile is configured, you can perform GTS based on home users. After a user passes authentication, the authentication server sends the name of the user group profile associated with the user to the device. When any home user of the user group profile logs in, the authentication server automatically applies the GTS parameters configured for the user group profile to the user. When the user logs off, the system automatically removes the GTS configuration without manual intervention.
Restrictions and guidelines
Only the outgoing traffic (traffic received by home users) can be policed.
Procedure
1. Enter system view.
system-view
2. Enter user group profile view.
user-group-profile profile-name
3. Configure GTS for the user group profile.
qos gts [ inbound ] any cir committed-information-rate [ cbs committed-burst-size [ ebs excess-burst-size ] ] [ queue-length queue-length ]
qos gts [ inbound ] any cir committed-information-rate [ cbs committed-burst-size ] pir peak-information-rate [ ebs excess-burst-size ] [ queue-length queue-length ]
By default, GTS is not configured for a user group profile.
The configuration in user group profile view takes effect when the home users come online.
Configuring GTS for a session group profile
About GTS for a session group profile
When a session group profile is configured, you can perform GTS based on home users. After a user passes authentication, the authentication server sends the name of the session group profile associated with the user to the device. When any home user of the session group profile logs in, the authentication server automatically applies the GTS parameters configured for the session group profile to the user. When the user logs off, the system automatically removes the GTS configuration without manual intervention.
This feature is available only on CSPEX (except CSPEX-1104-E) and CEPC cards.
Procedure
1. Enter system view.
system-view
2. Enter session group profile view.
user-profile profile-name type session-group
3. Configure GTS for the session group profile.
qos gts { any | queue queue-id } cir committed-information-rate [ cbs committed-burst-size [ ebs excess-burst-size ] ] [ queue-length queue-length ]
qos gts { any | queue queue-id } cir committed-information-rate [ cbs committed-burst-size ] pir peak-information-rate [ ebs excess-burst-size ] [ queue-length queue-length ]
By default, GTS is not configured for a session group profile.
The configuration in session group profile view takes effect when the home users come online.
Configuring the rate limit for an interface
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Configure the rate limit for the interface.
qos lr outbound cir committed-information-rate [ cbs committed-burst-size ]
By default, no rate limit is configured on an interface.
For this command to take effect on a Layer 3 aggregate interface or subinterface, make sure all its member ports are on CSPEX (except CSPEX-1204 and CSPEX-1104-E) and CEPC cards.
Configuring traffic permission by using the MQC approach
About traffic permission
Traffic permission allows matching traffic to pass through without performing rate limiting and accounting on the traffic. Traffic permission is supported only for traffic that passes IPoE, portal, or PPPoE authentication.
The device supports the following application destinations for traffic permission:
· Interface.
· VLANs.
· Globally.
· Control plane.
· User profile.
Procedure
1. Enter system view.
system-view
2. Enter traffic behavior view.
traffic behavior behavior-name
3. Configure the rate limit for the interface.
free account
By default, no traffic permission action is configured.
Display and maintenance commands for traffic policing, GTS, and rate limit
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
(In standalone mode.) Display ACL rules in the dynamic whitelist. |
display acl whitelist [ ipv6 ] slot slot-number |
|
(In IRF mode.) Display ACL rules in the dynamic whitelist. |
display acl whitelist [ ipv6 ] chassis chassis-number slot slot-number |
|
(In standalone mode.) Display whitelist-based control plane CAR configuration and statistics. |
display qos car control-plane whitelist [ ipv6 ] slot slot-number |
|
(In IRF mode.) Display whitelist-based control plane CAR configuration and statistics. |
display qos car control-plane whitelist [ ipv6 ] chassis chassis-number slot slot-number |
|
(In standalone mode.) Display QoS and ACL resource usage. |
display qos-acl resource [ slot slot-number ] |
|
(In IRF mode.) Display QoS and ACL resource usage. |
display qos-acl resource [ chassis chassis-number slot slot-number ] |
|
Display traffic behavior configuration. |
display traffic behavior user-defined [ behavior-name ] |
|
(In standalone mode.) Display GTS configuration and statistics for interfaces. |
display qos gts interface [ interface-type interface-number [ slot slot-number ] ] |
|
(In IRF mode.) Display GTS configuration and statistics for interfaces. |
display qos gts interface [ interface-type interface-number [ chassis chassis-number slot slot-number ] ] |
|
(In standalone mode.) Display queue-based traffic statistics for a home user. |
display qos queue-statistics user-id user-id [ slot slot-number ] outbound |
|
(In IRF mode.) Display queue-based traffic statistics for a home user. |
display qos queue-statistics user-id user-id [ chassis chassis-number slot slot-number ] outbound |
|
(In standalone mode.) Display rate limit configuration and statistics for interfaces. |
display qos lr interface [ interface-type interface-number [ slot slot-number ] ] |
|
(In IRF mode.) Display rate limit configuration and statistics for interfaces. |
display qos lr interface [ interface-type interface-number [ chassis chassis-number slot slot-number ] ] |
|
(In standalone mode.) Clear whitelist-based control plane CAR statistics. |
reset qos car control-plane whitelist [ ipv6 ] slot slot-number |
|
(In IRF mode.) Clear whitelist-based control plane CAR statistics. |
reset qos car control-plane whitelist [ ipv6 ] chassis chassis-number slot slot-number |
Traffic policing, GTS, and rate limit configuration examples
Example: Configuring traffic policing and GTS
Network configuration
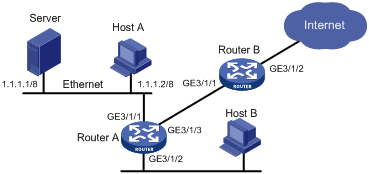
As shown in Figure 11:
· The server, Host A, and Host B can access the Internet through Router A and Router B.
· The server, Host A, and GigabitEthernet 3/1/1 of Router A are in the same network segment.
· Host B and GigabitEthernet 3/1/2 of Router A are in the same network segment.
Perform traffic control for the packets that GigabitEthernet 3/1/1 of Router A receives from the server and Host A using the following guidelines:
· Limit the rate of packets from the server to 10240 kbps. When the traffic rate is below 10240 kbps, the traffic is forwarded. When the traffic rate exceeds 10240 kbps, the excess packets are marked with DSCP value 0 and then forwarded.
· Limit the rate of packets from Host A to 25600 kbps. When the traffic rate is below 25600 kbps, the traffic is forwarded. When the traffic rate exceeds 25600 kbps, the excess packets are dropped.
Perform traffic control on GigabitEthernet 3/1/1 and GigabitEthernet 3/1/2 of Router B using the following guidelines:
· Limit the total incoming traffic rate on GigabitEthernet 3/1/1 to 204800 kbps, and the excess packets are dropped.
· Limit the outgoing HTTP traffic rate on GigabitEthernet 3/1/2 to 102400 kbps, and the excess packets are dropped.
Procedure
1. Configure Router A:
# Configure ACLs to permit the packets from the server and Host A.
[RouterA] acl basic 2001
[RouterA-acl-ipv4-basic-2001] rule permit source 1.1.1.1 0
[RouterA-acl-ipv4-basic-2001] quit
[RouterA] acl basic 2002
[RouterA-acl-ipv4-basic-2002] rule permit source 1.1.1.2 0
[RouterA-acl-ipv4-basic-2002] quit
# Create a traffic class named server, and use ACL 2001 as the match criterion.
[RouterA] traffic classifier server
[RouterA-classifier-server] if-match acl 2001
[RouterA-classifier-server] quit
# Create a traffic class named host, and use ACL 2002 as the match criterion.
[RouterA] traffic classifier host
[RouterA-classifier-host] if-match acl 2002
[RouterA-classifier-host] quit
# Create a traffic behavior named server, and configure a traffic policing action (CIR 102400 kbps).
[RouterA] traffic behavior server
[RouterA-behavior-server] car cir 102400 red remark-dscp-pass 0
[RouterA-behavior-server] quit
# Create a traffic behavior named host, and configure a traffic policing action (CIR 25600 kbps).
[RouterA] traffic behavior host
[RouterA-behavior-host] car cir 25600
[RouterA-behavior-host] quit
# Create a QoS policy named car, and associate traffic classes server and host with traffic behaviors server and host in the QoS policy, respectively.
[RouterA] qos policy car
[RouterA-qospolicy-car] classifier server behavior server
[RouterA-qospolicy-car] classifier host behavior host
[RouterA-qospolicy-car] quit
# Apply QoS policy car to the inbound direction of GigabitEthernet 3/1/1.
[RouterA] interface gigabitethernet 3/1/1
[RouterA-GigabitEthernet3/1/1] qos apply policy car inbound
2. Configure Router B:
# Create ACL 3001, and configure a rule to match HTTP packets.
<RouterB> system-view
[RouterB] acl advanced 3001
[RouterB-acl-ipv4-adv-3001] rule permit tcp destination-port eq 80
[RouterB-acl-ipv4-adv-3001] quit
# Create a traffic class named http, and use ACL 3001 as a match criterion.
[RouterB] traffic classifier http
[RouterB-classifier-http] if-match acl 3001
[RouterB-classifier-http] quit
# Create a traffic class named class, and configure the traffic class to match all packets.
[RouterB] traffic classifier class
[RouterB-classifier-class] if-match any
[RouterB-classifier-class] quit
# Create a traffic behavior named car_inbound, and configure a traffic policing action (CIR 204800 kbps).
[RouterB] traffic behavior car_inbound
[RouterB-behavior-car_inbound] car cir 204800
[RouterB-behavior-car_inbound] quit
# Create a traffic behavior named car_outbound, and configure a traffic policing action (CIR 102400 kbps).
[RouterB] traffic behavior car_outbound
[RouterB-behavior-car_outbound] car cir 102400
[RouterB-behavior-car_outbound] quit
# Create a QoS policy named car_inbound, and associate traffic class class with traffic behavior car_inbound in the QoS policy.
[RouterB] qos policy car_inbound
[RouterB-qospolicy-car_inbound] classifier class behavior car_inbound
[RouterB-qospolicy-car_inbound] quit
# Create a QoS policy named car_outbound, and associate traffic class http with traffic behavior car_outbound in the QoS policy.
[RouterB] qos policy car_outbound
[RouterB-qospolicy-car_outbound] classifier http behavior car_outbound
[RouterB-qospolicy-car_outbound] quit
# Apply QoS policy car_inbound to the inbound direction of Gigabitethernet 3/1/1.
[RouterB] interface gigabitethernet 3/1/1
[RouterB-Gigabitethernet3/1/1] qos apply policy car_inbound inbound
# Apply QoS policy car_outbound to the outbound direction of Gigabitethernet 3/1/2.
[RouterB] interface gigabitethernet 3/1/2
[RouterB-Gigabitethernet3/1/2] qos apply policy car_outbound outbound
Configuring hardware congestion management
About hardware congestion management
Congestion occurs on a link or node when traffic size exceeds the processing capability of the link or node. It is typical of a statistical multiplexing network and can be caused by link failures, insufficient resources, and various other causes.
Figure 12 shows two typical congestion scenarios.
Figure 12 Traffic congestion scenarios
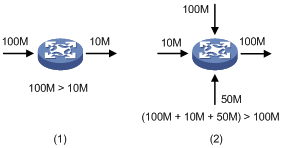
Congestion produces the following negative results:
· Increased delay and jitter during packet transmission.
· Decreased network throughput and resource use efficiency.
· Network resource (memory, in particular) exhaustion and even system breakdown.
Congestion is unavoidable in switched networks and multiuser application environments. To improve the service performance of your network, take measures to manage and control it.
The key to congestion management is defining a resource dispatching policy to prioritize packets for forwarding when congestion occurs.
Congestion management uses queuing and scheduling algorithms to classify and sort traffic leaving a port.
The device supports the following queuing mechanisms:
· SP.
· WRR.
· WFQ.
· CBQ.
SP queuing
SP queuing is designed for mission-critical applications that require preferential service to reduce the response delay when congestion occurs.
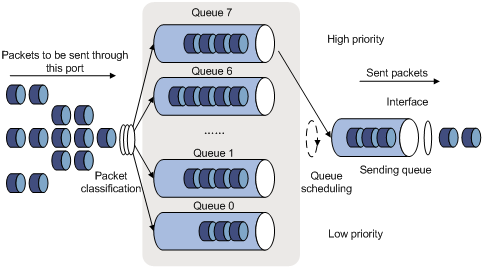
In Figure 13, SP queuing classifies eight queues on a port into eight classes, numbered 7 to 0 in descending priority order.
SP queuing schedules the eight queues in the descending order of priority. SP queuing sends packets in the queue with the highest priority first. When the queue with the highest priority is empty, it sends packets in the queue with the second highest priority, and so on. You can assign mission-critical packets to a high priority queue to make sure they are always served first. Common service packets can be assigned to low priority queues to be transmitted when high priority queues are empty.
The disadvantage of SP queuing is that packets in the lower priority queues cannot be transmitted if packets exist in the higher priority queues. In the worst case, lower priority traffic might never get serviced.
WRR queuing
WRR queuing schedules all the queues in turn to ensure that every queue is served for a certain time, as shown in Figure 14.
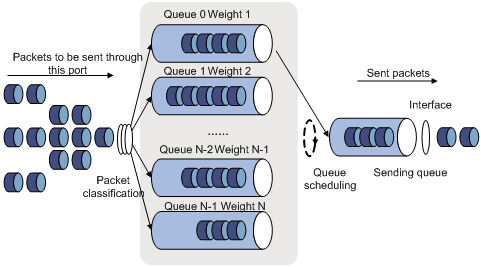
Assume a port provides eight output queues. WRR assigns each queue a weight value (represented by w7, w6, w5, w4, w3, w2, w1, or w0). The weight value of a queue decides the proportion of resources assigned to the queue. On a 100 Mbps port, you can set the weight values to 50, 30, 10, 10, 50, 30, 10, and 10 for w7 through w0. In this way, the queue with the lowest priority can get a minimum of 5 Mbps of bandwidth. WRR solves the problem that SP queuing might fail to serve packets in low-priority queues for a long time.
Another advantage of WRR queuing is that when the queues are scheduled in turn, the service time for each queue is not fixed. If a queue is empty, the next queue will be scheduled immediately. This improves bandwidth resource use efficiency.
On an interface enabled with group-based WRR queuing, you can assign queues to the SP group. Queues in the SP group are scheduled with SP. The SP group has higher scheduling priority than the WRR groups.
WFQ queuing
Figure 15 WFQ queuing

WFQ is similar to WRR. On an interface with group-based WFQ queuing enabled, you can also assign queues to the SP group. Queues in the SP group are scheduled with SP. The SP group has higher scheduling priority than the WFQ groups.
The difference is that WFQ enables you to set guaranteed bandwidth that a WFQ queue can get during congestion.
CBQ queuing
Class-based queuing (CBQ) extends WFQ by supporting user-defined classes and assign a FIFO queue to each class. When network congestion occurs, CBQ uses user-defined traffic match criteria to enqueue packets. Before packets are enqueued, congestion avoidance actions, such as tail drop or WRED and bandwidth restriction check, are performed. When being dequeued, packets are scheduled by WFQ.
CBQ provides the following queues:
· Low Latency Queuing (LLQ)—An EF queue that preferentially transmits delay-sensitive flows like voice packets. To reduce the delay of the other queues except the priority queue, LLQ assigns the maximum available bandwidth to each priority class. The bandwidth value polices traffic during congestion. When no congestion is present, a priority class can use more than the bandwidth assigned to it. During congestion, the packets of each priority class exceeding the assigned bandwidth are discarded.
· Bandwidth queuing (BQ)—An AF queue. The BQ provides guaranteed bandwidth for AF traffic, and schedules the AF classes proportionally.
· WFQ queue—The queue transmits the BE traffic by using the remaining interface bandwidth.
The system matches packets with classification rules in the following order:
· Match packets with classes in the configuration order.
· Match packets with classification rules in a class in the configuration order.
Hardware congestion management tasks at a glance
To configure hardware congestion management, perform the following tasks:
· Configuring queuing on an interface
¡ Configuring SP queuing
¡ Configuring WRR queuing
¡ Configuring WFQ queuing
¡ Configure AF and the minimum guaranteed bandwidth
¡ Configuring EF and the guaranteed bandwidth
· Configuring a queue scheduling profile
Configuring queuing on an interface
WRR and WFQ are available only on CSPC (except CSPC-GE16XP4L-E, CSPC-GE24L-E, and CSPC-GP24GE8XP2L-E) and CMPE-1104 cards.
Configuring SP queuing
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Configure SP queuing.
qos sp
By default, an interface uses SP queuing.
Configuring WRR queuing
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Enable WRR queuing.
qos wrr weight
By default, an interface uses SP queuing.
4. Configure a WRR queue.
qos wrr queue-id group 1 weight schedule-value
By default, all queues on a WRR-enabled interface are in WRR group 1 and have a weight of 1.
Only WRR group 1 is supported in the current software version.
5. (Optional.) Assign a queue to the SP group.
qos wrr queue-id group sp
By default, all queues on a WRR-enabled interface are in WRR group 1.
Configuring WFQ queuing
Restrictions and guidelines
Layer 3 Ethernet subinterfaces on CSPC and CMPE-1104 cards do not support WFQ queuing.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Enable WFQ queuing.
qos wfq weight
By default, an interface uses SP queuing.
4. Configure a WFQ queue.
qos wfq queue-id weight schedule-value
By default, all queues on a WFQ-enabled interface have a weight of 1.
5. (Optional.) Set the minimum guaranteed bandwidth for a WFQ queue.
qos bandwidth queue queue-id min bandwidth-value
By default, no minimum guaranteed bandwidth is provided.
Configuring SP+WRR queuing
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Enable WRR queuing.
qos wrr weight
By default, an interface uses SP queuing.
4. Assign a queue to the SP group.
qos wrr queue-id group sp
By default, all queues on a WRR-enabled interface are in WRR group 1.
5. Assign a queue to the WRR group, and configure a scheduling weight for the queue.
qos wrr queue-id group 1 weight schedule-value
By default, all queues on a WRR-enabled interface have a weight of 1.
Configuring CBQ
Restrictions and guidelines
In a traffic behavior, one one of the following queuing actions can be configured: AF, EF, SP, and WFQ.
This feature is supported only on the following interfaces and cards:
· Layer 3 interfaces on a CMPE-1104 card (except the first four interfaces on the MIC-GP8L card).
· CSPC-GE16XP4L-E, CSPC-GE24L-E, CSPC-GP24GE8XP2L-E, CSPEX, and CEPC cards.
For CBQ to take effect on a Layer 3 aggregate interface or subinterface, make sure all its member ports are on CSPEX (except CSPEX-1204 and CSPEX-1104-E) and CEPC cards.
Configure AF and the minimum guaranteed bandwidth
Restrictions and guidelines
· You can apply this traffic behavior only to the outgoing traffic of an interface.
· You cannot configure the queue af command together with the queue ef or queue wfq command in the same traffic behavior.
· If the total bandwidth for EF, AF and BE traffic exceeds the interface bandwidth, CBQ cannot work as configured.
· The display qos queue-statistics interface command cannot display queue-based traffic statistics for a QoS policy that contains a CBQ action.
Procedure
1. Enter system view.
system-view
2. Define a traffic class.
a. Create a traffic class and enter traffic class view.
traffic classifier classifier-name [ operator { and | or } ]
b. Configure a match criterion.
if-match match-criteria
By default, no match criterion is configured.
For more information about configuring match criteria, see ACL and QoS Command Reference.
c. Return to system view.
quit
3. Define a traffic behavior.
a. Create a traffic behavior and enter traffic behavior view.
traffic behavior behavior-name
b. Configure AF and the minimum guaranteed bandwidth.
queue af bandwidth { bandwidth [ pir peak-information-rate ] | pct percentage }
By default, AF is not configured.
Traffic between the minimum guaranteed bandwidth and PIR is scheduled by using WFQ.
The pir peak-information-rate option does not take effect on a CMPE-1104 card.
c. (Optional.) Configure a WFQ weight for traffic that exceeds the minimum guaranteed bandwidth.
weight weight-value
By default:
- The WFQ weight is 1 on a CMPE-1104 card.
- The WFQ weight is 1 on CSPC-GE16XP4L-E, CSPC-GE24L-E, CSPC-GP24GE8XP2L-E, CSPEX (except CSPEX-1204), and CEPC cards.
- The WFQ weight is 1 for POS interfaces and Ethernet interfaces on the CSPEX-1204 card. SP queuing is used for other interface types and subinterfaces on the CSPEX-1204 card.
d. Return to system view.
quit
4. Define a QoS policy.
a. Create a QoS policy and enter QoS policy view.
qos policy policy-name
b. Associate a traffic behavior with a class in the policy.
classifier classifier-name behavior behavior-name
By default, a class is not associated with a behavior.
c. Return to system view.
quit
d. Apply the QoS policy to an interface.
For more information, see "Applying the QoS policy."
By default, no QoS policy is applied.
Configuring EF and the guaranteed bandwidth
Restrictions and guidelines
· You cannot configure the queue ef command together with the queue af or queue wfq command in one traffic behavior.
· You can apply this traffic behavior only to the outgoing traffic of an interface.
· If the total bandwidth for EF, AF and BE traffic exceeds the interface bandwidth, CBQ cannot work as configured.
· The display qos queue-statistics interface command cannot display queue-based traffic statistics for a QoS policy that contains a CBQ action.
Procedure
1. Enter system view.
system-view
2. Define a traffic class.
a. Create a traffic class and enter traffic class view.
traffic classifier classifier-name [ operator { and | or } ]
b. Configure a match criterion.
if-match match-criteria
By default, no match criterion is configured.
For more information about configuring match criteria, see ACL and QoS Command Reference.
c. Return to system view.
quit
3. Define a traffic behavior.
a. Create a traffic behavior and enter traffic behavior view.
traffic behavior behavior-name
b. Configure EF and the maximum bandwidth.
queue ef bandwidth { bandwidth [ cbs burst ] [ pir peak-information-rate ] | pct percentage [ cbs-ratio ratio ] }
By default, EF is not configured.
The pir peak-information-rate option does not take effect on a CMPE-1104 card.
c. (Optional.) Configure a WFQ weight for traffic that exceeds the guaranteed bandwidth..
weight weight-value
By default:
- The WFQ weight is 1 on a CMPE-1104 card.
- The WFQ weight is 1 on CSPC-GE16XP4L-E, CSPC-GE24L-E, CSPC-GP24GE8XP2L-E, CSPEX (except CSPEX-1204), and CEPC cards.
- The WFQ weight is 1 for POS interfaces and Ethernet interfaces on the CSPEX-1204 card. SP queuing is used for other interface types and subinterfaces on the CSPEX-1204 card.
d. Return to system view.
quit
4. Define a QoS policy.
a. Create a QoS policy and enter QoS policy view.
qos policy policy-name
b. Associate a traffic behavior with a class in the policy.
classifier classifier-name behavior behavior-name
By default, a class is not associated with a behavior.
c. Return to system view.
quit
5. Apply the QoS policy to an interface.
For more information, see "Applying the QoS policy."
By default, no QoS policy is applied.
Configuring WFQ
Restrictions and guidelines
· You cannot configure the queue wfq command together with the queue af or queue ef command in one traffic behavior.
· You can apply this traffic behavior only to the outgoing traffic of an interface.
· If the total bandwidth for EF, AF and BE traffic exceeds the interface bandwidth, CBQ cannot work as configured.
· The display qos queue-statistics interface command cannot display queue-based traffic statistics for a QoS policy that contains a CBQ action.
Procedure
1. Enter system view.
system-view
2. Define a traffic class.
a. Create a traffic class and enter traffic class view.
traffic classifier classifier-name [ operator { and | or } ]
b. Configure a match criterion.
if-match match-criteria
By default, no match criterion is configured.
For more information about configuring match criteria, see ACL and QoS Command Reference.
c. Return to system view.
quit
3. Define a traffic behavior.
a. Create a traffic behavior and enter traffic behavior view.
traffic behavior behavior-name
b. Configure WFQ.
queue wfq
By default, WFQ is not configured.
c. (Optional.) Set the weight of the WFQ queue.
weight weight-value
By default:
- The WFQ weight is 1 on a CMPE-1104 card.
- The WFQ weight is 0 on CSPC-GE16XP4L-E, CSPC-GE24L-E, CSPC-GP24GE8XP2L-E, CSPEX (except CSPEX-1204), and CEPC cards.
- The WFQ weight is 0 for POS interfaces and Ethernet interfaces on the CSPEX-1204 card. SP queuing is used for other interface types and subinterfaces on the CSPEX-1204 card.
d. Return to system view.
quit
4. Define a QoS policy.
a. Create a QoS policy and enter QoS policy view.
qos policy policy-name
b. Associate a traffic behavior with a class in the policy.
classifier classifier-name behavior behavior-name
By default, a class is not associated with a behavior.
c. Return to system view.
quit
5. Apply the QoS policy to an interface.
For more information, see "Applying the QoS policy."
By default, no QoS policy is applied.
Example: Configuring CBQ
Network configuration
As shown in Figure 16, configure a QoS policy on Router A to meet the following requirements:
· Traffic from Router C is classified into three classes based on DSCP values. Perform AF for traffic with DSCP values of AF11 and AF21, and set the minimum guaranteed bandwidth to 5 Mbps for the traffic.
· Perform EF for traffic with a DSCP value of EF and set the maximum bandwidth to 30 Mbps for the traffic.
Before configuring the QoS policy, make sure the following requirements are met:
· The route from Router C to Router D through Router A and Router B is reachable.
· The DSCP fields have been set for the traffic before the traffic enters Router A.
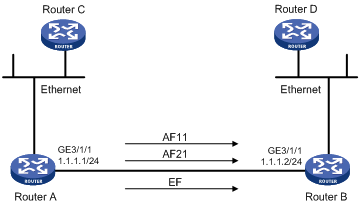
Procedure
# Define three classes to match the IP packets with the DSCP values AF11, AF21, and EF, respectively.
<RouterA> system-view
[RouterA] traffic classifier ef_class
[RouterA-classifier-ef_class] if-match dscp ef
[RouterA-classifier-ef_class] quit
[RouterA] traffic classifier af11_class
[RouterA-classifier-af11_class] if-match dscp af11
[RouterA-classifier-af11_class] quit
[RouterA]traffic classifier af21_class
[RouterA-classifier-af21_class] if-match dscp af21
[RouterA-classifier-af21_class] quit
# Define the default class to match all IP packets.
[RouterA] acl advanced 3000
[RouterA-acl-ipv4-adv-3000] rule 0 permit ip
[RouterA-acl-ipv4-adv-3000] quit
[RouterA] traffic classifier be_class
[RouterA-classifier-be_class] if-match acl 3000
[RouterA-classifier-be_class] quit
# Define two traffic behaviors, and enable AF and set the minimum guaranteed bandwidth to 5 Mbps in each traffic behavior.
[RouterA] traffic behavior af11_behav
[RouterA-behavior-af11_behav] queue af bandwidth 5000
[RouterA-behavior-af11_behav] quit
[RouterA] traffic behavior af21_behav
[RouterA-behavior-af21_behav] queue af bandwidth 5000
[RouterA-behavior-af21_behav] quit
# Define a traffic behavior, and enable EF and set the minimum bandwidth to 30 Mbps in the traffic behavior.
[RouterA] traffic behavior ef_behav
[RouterA-behavior-ef_behav] queue ef bandwidth 30000
[RouterA-behavior-ef_behav] quit
# Define a traffic behavior for the default class.
[RouterA] traffic behavior be_behav
[RouterA-behavior-be_behav] queue wfq
[RouterA-behavior-be_behav] quit
# Define a QoS policy and associate the configured traffic behaviors with classes in the QoS policy.
[RouterA] qos policy dscp
[RouterA-qospolicy-dscp] classifier ef_class behavior ef_behav
[RouterA-qospolicy-dscp] classifier af11_class behavior af11_behav
[RouterA-qospolicy-dscp] classifier af21_class behavior af21_behav
[RouterA-qospolicy-dscp] classifier be_class behavior be_behav
[RouterA-qospolicy-dscp] quit
# Apply the QoS policy to the outgoing traffic of GigabitEthernet 3/1/1.
[RouterA-GigabitEthernet3/1/1] qos apply policy dscp outbound
[RouterA-GigabitEthernet3/1/1] quit
# Display information about the applied QoS policy.
[RouterA] display qos policy interface GigabitEthernet 3/1/1 outbound
Interface: GigabitEthernet3/1/1
Direction: Outbound
Policy: dscp
Classifier: ef_class
Operator: AND
Rule(s) : If-match dscp ef
Behavior: ef_behav
Expedited Forwarding:
Bandwidth 30000 (Kbps), CBS 750000 (Bytes)
Matched : 100/6400 (Packets/Bytes)
Enqueued : 100/6400 (Packets/Bytes)
Discarded: 0/0 (Packets/Bytes)
Classifier: af11_class
Operator: AND
Rule(s) : If-match dscp af11
Behavior: af11_behav
Assured Forwarding:
Bandwidth 5000 (Kbps)
Matched : 50/3200 (Packets/Bytes)
Enqueued : 50/3200 (Packets/Bytes)
Discarded: 0/0 (Packets/Bytes)
Classifier: af21_class
Operator: AND
Rule(s) : If-match dscp af21
Behavior: af21_behav
Assured Forwarding:
Bandwidth 5000 (Kbps)
Matched : 50/3200 (Packets/Bytes)
Enqueued : 50/3200 (Packets/Bytes)
Discarded: 0/0 (Packets/Bytes)
Classifier: be_class
Operator: AND
Rule(s) : If-match acl 3000
Behavior: be_behav
Flow Based Weighted Fair Queuing
Matched : 1000/128000 (Packets/Bytes)
Discard Method: IP Precedence based WRED
The configuration enables EF traffic to be forwarded preferentially when congestion occurs.
Configuring a queue scheduling profile
About queue scheduling profiles
In a queue scheduling profile, you can configure scheduling parameters for each queue. By applying the queue scheduling profile to an interface or session group profile, you can implement congestion management on the interface or session group profile.
Queue scheduling profiles support two queue scheduling algorithms: SP and WRR. In a queue scheduling profile, you can also configure SP+WRR by assigning some queues to the SP group and other queues to WRR groups. A maximum of four WRR groups are supported. SP queues and WRR groups are scheduled according to the SP algorithm. The system compares the lowest queue ID in a WRR group with the SP queue IDs to determine the scheduling priority of the WRR group. In a WRR group, queues are scheduled based on their weights. Figure 17 shows the scheduling order for SP+WRR.
Figure 17 Queue scheduling profile configured with both SP and WRR
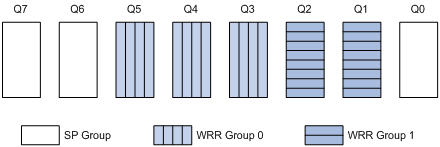
· Queue 7 has the highest priority. Its packets are sent preferentially.
· Queue 6 has the second highest priority. Packets in queue 6 are sent when queue 7 is empty.
· Queue 3, queue 4, and queue 5 are scheduled according to their weights. When both queue 6 and queue 7 are empty, WRR group 1 is scheduled.
· Queue 1 and queue 2 are scheduled according to their weights. WRR group 2 is scheduled when queue 7, queue 6, queue 5, queue 4, and queue 3 are all empty.
· Queue 0 has the lowest priority, and it is scheduled when all other queues are empty.
If the minimum guaranteed bandwidth is set for a queue, the traffic in the queue within the minimum guaranteed bandwidth is scheduled according to the preceding rules. The traffic beyond it is scheduled together with the traffic in queue 0 or the traffic in the WRR group to which queue 0 belongs.
Restrictions and guidelines for queue scheduling profile configuration
When you configure a queue scheduling profile, follow these restrictions and guidelines:
· This feature is available only on CSPC-GE16XP4L-E, CSPC-GE24L-E, CSPC-GP24GE8XP2L-E, CSPEX, and CEPC cards.
· For this feature to take effect on a Layer 3 aggregate interface or subinterface, make sure all its member ports are on CSPEX (except CSPEX-1204 and CSPEX-1104-E) and CEPC cards.
· Only one queue scheduling profile can be applied to an interface, user profile, or session group profile.
· To delete a queue scheduling profile already applied to an interface, user profile, or session group profile, you must remove the queue scheduling profile from the interface, user profile, or session group profile and then delete it.
Configuring a queue scheduling profile
1. Enter system view.
system-view
2. Create a queue scheduling profile and enter queue scheduling profile view.
qos qmprofile profile-name [ basic ]
3. Configure queue scheduling parameters.
¡ Configure a queue to use SP.
queue queue-id sp [ max-bandwidth bandwidth-value ]
¡ Configure a queue to use WRR.
queue queue-id wrr group group-id weight schedule-value [ max-bandwidth bandwidth-value ]
By default, all queues in a queue scheduling profile are SP queues.
One queue can use only one queue scheduling algorithm. In a queue scheduling profile, you can configure different queue scheduling algorithms for different queues.
Only CSPEX (except CSPEX-1204 and CSPEX-1104-E) and CEPC cards support the max-bandwidth bandwidth-value option.
4. (Optional.) Set the minimum guaranteed bandwidth for a queue.
bandwidth queue queue-id min bandwidth-value
By default, the minimum guaranteed bandwidth is not set.
On CSPEX (except CSPEX-1204 and CSPEX-1104-E) and CEPC cards, the minimum guaranteed bandwidth takes effect only on SP queues.
Applying a queue scheduling profile
1. Enter system view.
system-view
2. Enter queue scheduling profile view.
qos qmprofile profile-name
3. Apply the queue scheduling profile.
¡ Apply the queue scheduling profile to the switching fabric module.
qos apply qmprofile profile-name fabric
By default, no queue scheduling profile is applied to the switching fabric module.
¡ Execute the following commands in sequence to apply the queue scheduling profile to an interface.
interface interface-type interface-number
qos apply qmprofile profile-name [ inbound ]
By default, an interface uses SP queuing.
On the CSPEX-1204 card, you cannot configure both queue-based GTS and a queue scheduling profile with WRR queuing for the same interface.
¡ Execute the following commands in sequence to apply the queue scheduling profile to a user group profile:
user-group-profile profile-name
qos apply qmprofile profile-name
By default, no queue scheduling profile is applied to a user group profile.
The configuration in user group profile view takes effect when the users come online.
¡ Execute the following commands in sequence to apply the queue scheduling profile to a session group profile.
user-profile profile-name type session-group
qos apply qmprofile profile-name
By default, no queue scheduling profile is applied to a session group profile.
The configuration in session group profile view takes effect when the users come online.
Applying a queue scheduling profile to a session group profile is available only on CSPEX (except CSPEX-1204 and CSPEX-1104-E) and CEPC cards.
Example: Configuring a queue scheduling profile
Network configuration
Configure a queue scheduling profile to meet the following requirements on GigabitEthernet 3/1/1:
· Queue 7 has the highest priority, and its packets are sent preferentially.
· Queue 4, queue 5, and queue 6 are in WRR group 1 and scheduled according to their weights, which are 1, 5, and 10, respectively. When queue 7 is empty, WRR group 1 is scheduled.
· Queue 1, queue 2, and queue 3 are in WRR group 2 and scheduled according to their weights, which are 1, 10, and 20, respectively. When queue 4, queue 5, queue 6, and queue 7 are all empty, WRR group 2 is scheduled.
· Queue 0 has the lowest priority. Queue 0 is scheduled when all the other queues are empty.
Procedure
# Enter system view.
<Sysname> system-view
# Create a queue scheduling profile named qm1.
[Sysname] qos qmprofile qm1
[Sysname-qmprofile-qm1]
# Configure queue 7 to use SP queuing.
[Sysname-qmprofile-qm1] queue 7 sp
# Assign queue 4, queue 5, and queue 6 to WRR group 1, with the weight of 1, 5, and 10, respectively.
[Sysname-qmprofile-qm1] queue 4 wrr group 1 weight 1
[Sysname-qmprofile-qm1] queue 5 wrr group 1 weight 5
[Sysname-qmprofile-qm1] queue 6 wrr group 1 weight 10
# Assign queue 1, queue 2, and queue 3 to WRR group 2, with the weight of 1, 10, and 20, respectively.
[Sysname-qmprofile-qm1] queue 1 wrr group 2 weight 1
[Sysname-qmprofile-qm1] queue 2 wrr group 2 weight 10
[Sysname-qmprofile-qm1] queue 3 wrr group 2 weight 20
# Configure queue 0 to use SP queuing.
[Sysname-qmprofile-qm1] queue 0 sp
[Sysname-qmprofile-qm1] quit
# Apply queue scheduling profile qm1 to GigabitEthernet 3/1/1.
[Sysname] interface gigabitethernet 3/1/1
[Sysname-GigabitEthernet3/1/1] qos apply qmprofile qm1
After the configuration is completed, GigabitEthernet 3/1/1 performs queue scheduling as specified in queue scheduling profile qm1.
Display and maintenance commands for hardware congestion management
Execute display commands in any view.
|
Task |
Command |
|
Display queuing configuration. |
display qos queue interface [ interface-type interface-number ] |
|
Display SP queuing configuration. |
display qos queue sp interface [ interface-type interface-number ] |
|
Display WRR queuing configuration. |
display qos queue wrr interface [ interface-type interface-number ] |
|
Display WFQ queuing configuration. |
display qos queue wfq interface [ interface-type interface-number ] |
|
(In standalone mode.) Display the configuration of queue scheduling profiles. |
display qos qmprofile configuration [ profile-name ] [ slot slot-number ] |
|
(In IRF mode.) Display the configuration of queue scheduling profiles. |
display qos qmprofile configuration [ profile-name ] [ chassis chassis-number slot slot-number ] |
|
(In standalone mode.) Display the queue scheduling profiles applied to interfaces. |
display qos qmprofile interface [ interface-type interface-number [ slot slot-number ] ] [ inbound ] |
|
(In IRF mode.) Display the queue scheduling profiles applied to interfaces. |
display qos qmprofile interface [ interface-type interface-number [ chassis chassis-number slot slot-number ]] [ inbound ] |
|
(In standalone mode.) Display QoS and ACL resource usage. |
display qos-queue resource slot slot-number { inbound | outbound } |
|
(In IRF mode.) Display QoS and ACL resource usage. |
display qos-queue resource chassis chassis-number slot slot-number { inbound | outbound } |
Configuring congestion avoidance
About congestion avoidance
Avoiding congestion before it occurs is a proactive approach to improving network performance. As a flow control mechanism, congestion avoidance:
· Actively monitors network resources (such as queues and memory buffers).
· Drops packets when congestion is expected to occur or deteriorate.
When dropping packets from a source end, congestion avoidance cooperates with the flow control mechanism at the source end to regulate the network traffic size. The combination of the local packet drop policy and the source-end flow control mechanism implements the following functions:
· Maximizes throughput and network use efficiency.
· Minimizes packet loss and delay.
Tail drop
Congestion management techniques drop all packets that are arriving at a full queue. This tail drop mechanism results in global TCP synchronization. If packets from multiple TCP connections are dropped, these TCP connections go into the state of congestion avoidance and slow start to reduce traffic. However, traffic peak occurs later. Consequently, the network traffic jitters all the time.
RED and WRED
You can use Random Early Detection (RED) or Weighted Random Early Detection (WRED) to avoid global TCP synchronization.
Both RED and WRED avoid global TCP synchronization by randomly dropping packets. When the sending rates of some TCP sessions slow down after their packets are dropped, other TCP sessions remain at high sending rates. Link bandwidth is efficiently used, because TCP sessions at high sending rates always exist.
The RED or WRED algorithm sets an upper threshold and lower threshold for each queue, and processes the packets in a queue as follows:
· When the queue size is shorter than the lower threshold, no packet is dropped.
· When the queue size reaches the upper threshold, all subsequent packets are dropped.
· When the queue size is between the lower threshold and the upper threshold, the received packets are dropped at random. The drop probability in a queue increases along with the queue size under the maximum drop probability.
If the current queue size is compared with the upper threshold and lower threshold to determine the drop policy, burst traffic is not fairly treated. To solve this problem, WRED compares the average queue size with the upper threshold and lower threshold to determine the drop probability.
The average queue size reflects the queue size change trend but is not sensitive to burst queue size changes, and burst traffic can be fairly treated.
When WFQ queuing is used, you can set the following parameters for packets with different precedence values to provide differentiated drop policies:
· Exponent for average queue size calculation.
· Upper threshold.
· Lower threshold.
· Drop probability.
When FIFO, PQ, or CQ is used, you can set the following parameters for each queue to provide differentiated drop policies:
· Exponent for average queue size calculation.
· Upper threshold.
· Lower threshold.
· Drop probability.
Relationship between WRED and queuing mechanisms
Figure 18 Relationship between WRED and queuing mechanisms
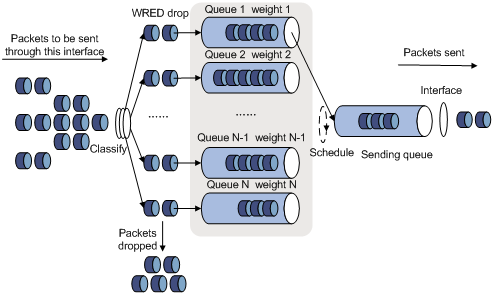
· A flow with a smaller queue size has a lower packet drop probability.
· A flow with a larger queue size has a higher packet drop probability.
In this way, the benefits of the flow with a smaller queue size are protected.
ECN
By dropping packets, WRED alleviates the influence of congestion on the network. However, the network resources for transmitting packets from the sender to the device which drops the packets are wasted. When congestion occurs, it is a better idea to perform the following actions:
· Inform the sender of the congestion status.
· Have the sender proactively slow down the packet sending rate or decrease the window size of packets.
This better utilizes the network resources.
RFC 2482 defined an end-to-end congestion notification mechanism named Explicit Congestion Notification (ECN). ECN uses the DS field in the IP header to mark the congestion status along the packet transmission path. An ECN-capable terminal can determine whether congestion occurs on the transmission path according to the packet contents. Then, it adjusts the packet sending speed to avoid deteriorating congestion. ECN defines the last two bits (ECN field) in the DS field of the IP header as follows:
· Bit 6 indicates whether the sending terminal device supports ECN, and is called the ECN-Capable Transport (ECT) bit.
· Bit 7 indicates whether the packet has experienced congestion along the transmission path, and is called the Congestion Experienced (CE) bit.
For more information about the DS field, see "Appendixes."
In actual applications, the following packets are considered as packets that an ECN-capable endpoint transmits:
· Packets with ECT set to 1 and CE set to 0.
· Packets with ECT set to 0 and CE set to 1.
After you enable ECN on a device, congestion management processes packets as follows:
· When the average queue size is below the lower threshold, no packet is dropped, and the ECN fields of packets are not identified or marked.
· When the average queue size is between the lower threshold and the upper threshold, the device performs the following operations:
a. Picks out packets to be dropped according to the drop probability.
b. Examines the ECN fields of these packets and determines whether to drop these packets.
¡ If the ECN field shows that the packet is sent out of ECN-capable terminal, the device performs the following operations:
- Sets both the ECT bit and the CE bit to 1.
- Forwards the packet.
¡ If both the ECT bit and the CE bit are 1 in the packet, the device forwards the packet without modifying the ECN field. The combination of ECT bit 1 and CE bit 1 indicates that the packet has experienced congestion along the transmission path.
¡ If both the ECT bit and the CE bit is 0 in the packet, the device drops the packet.
· When the average queue size exceeds the upper threshold, the device drops the packet, regardless of whether the packet is sent from an ECN-capable terminal.
WRED parameters
Determine the following parameters before configuring WRED:
· Upper threshold and lower threshold—When the average queue size is smaller than the lower threshold, packets are not dropped. When the average queue size is between the lower threshold and the upper threshold, the packets are dropped at random. The longer the queue, the higher the drop probability. When the average queue size exceeds the upper threshold, subsequent packets are dropped.
· Drop precedence—A parameter used for packet drop. The value 0 corresponds to green packets, the value 1 corresponds to yellow packets, and the value 2 corresponds to red packets. Red packets are dropped preferentially.
· Exponent for average queue size calculation—The greater the exponent, the less sensitive the average queue size is to real-time queue size changes. The formula for calculating the average queue size is:
Average queue size = ( previous average queue size x (1 – 2–n) ) + (current queue size x 2–n), where n is the exponent.
Configuring and applying a queue-based WRED table
Restrictions and guidelines
One WRED table can be applied to multiple interfaces. You can modify the parameters of a WRED table applied to an interface, but you cannot delete the WRED table.
Procedure
1. Enter system view.
system-view
2. Create a WRED table and enter its view.
qos wred queue table table-name
3. (Optional.) Set the WRED exponent for average queue size calculation.
queue queue-id weighting-constant exponent
The default setting is 9.
This command does not take effect on CSPC-GE16XP4L-E, CSPC-GE24L-E, CSPC-GP24GE8XP2L-E, oCSPEX, or CEPC cards.
4. (Optional.) Configure the other WRED parameters.
queue queue-id [ drop-level drop-level ] low-limit low-limit high-limit high-limit [ discard-probability discard-prob ]
By default, the low-limit argument is 100, the discard-prob argument is 10, and the high-limit argument is 1000.
The discard-probability discard-prob option is not configurable on CSPC-GE16XP4L-E, CSPC-GE24L-E, CSPC-GP24GE8XP2L-E, CSPEX, or CEPC cards.
5. (Optional.) Enable ECN for a queue.
queue queue-id ecn
By default, ECN is disabled for a queue.
CSPC-GE16XP4L-E, CSPC-GE24L-E, CSPC-GP24GE8XP2L-E, CSPEX, and CEPC cards do not support this command.
6. Return to system view.
quit
7. Enter interface view.
interface interface-type interface-number
8. Apply the WRED table to the interface.
qos wred apply [ table-name ]
By default, no WRED table is applied to an interface, and tail drop is used on an interface.
For this command to take effect on a Layer 3 aggregate interface or subinterface, make sure all its member ports are on CSPEX (except CSPEX-1204 and CSPEX-1104-E) and CEPC cards.
Example: Configuring and applying a queue-based WRED table
Network configuration
Apply a WRED table to GigabitEthernet 3/1/2, so that the packets are dropped as follows when congestion occurs:
· For the interface to preferentially forward higher-priority traffic, set a lower drop probability for a queue with a greater queue number. Set different drop parameters for queue 0, queue 3, and queue 7.
· Drop packets according to their colors.
¡ In queue 0, set the drop probability to 25%, 50%, and 75% for green, yellow, and red packets, respectively.
¡ In queue 3, set the drop probability to 5%, 10%, and 25% for green, yellow, and red packets, respectively.
¡ In queue 7, set the drop probability to 1%, 5%, and 10% for green, yellow, and red packets, respectively.
· Enable ECN for queue 7.
Procedure
# Configure a queue-based WRED table, and set different drop parameters for packets with different drop levels in different queues.
<Sysname> system-view
[Sysname] qos wred queue table queue-table1
[Sysname-wred-table-queue-table1] queue 0 drop-level 0 low-limit 128 high-limit 512 discard-probability 25
[Sysname-wred-table-queue-table1] queue 0 drop-level 1 low-limit 128 high-limit 512 discard-probability 50
[Sysname-wred-table-queue-table1] queue 0 drop-level 2 low-limit 128 high-limit 512 discard-probability 75
[Sysname-wred-table-queue-table1] queue 3 drop-level 0 low-limit 256 high-limit 640 discard-probability 5
[Sysname-wred-table-queue-table1] queue 3 drop-level 1 low-limit 256 high-limit 640 discard-probability 10
[Sysname-wred-table-queue-table1] queue 3 drop-level 2 low-limit 256 high-limit 640 discard-probability 25
[Sysname-wred-table-queue-table1] queue 7 drop-level 0 low-limit 512 high-limit 1024 discard-probability 1
[Sysname-wred-table-queue-table1] queue 7 drop-level 1 low-limit 512 high-limit 1024 discard-probability 5
[Sysname-wred-table-queue-table1] queue 7 drop-level 2 low-limit 512 high-limit 1024 discard-probability 10
[Sysname-wred-table-queue-table1] queue 7 ecn
[Sysname-wred-table-queue-table1] quit
# Apply the queue-based WRED table to GigabitEthernet 3/1/2.
[Sysname] interface gigabitethernet 3/1/2
[Sysname-GigabitEthernet3/1/2] qos wred apply queue-table1
[Sysname-GigabitEthernet3/1/2] quit
Display and maintenance commands for WRED
Execute display commands in any view.
|
Task |
Command |
|
(In standalone mode.) Display WRED configuration and statistics for an interface. |
display qos wred interface [ interface-type interface-number [ slot slot-number ] ] |
|
(In IRF mode.) Display WRED configuration and statistics for an interface. |
display qos wred interface [ interface-type interface-number [ chassis chassis-number slot slot-number ] ] |
|
(In standalone mode.) Display the configuration of a WRED table or all WRED tables. |
display qos wred table [ name table-name ] [ slot slot-number ] |
|
(In IRF mode.) Display the configuration of a WRED table or all WRED tables. |
display qos wred table [ name table-name ] [ chassis chassis-number slot slot-number ] |
Configuring traffic filtering
About traffic filtering
You can filter in or filter out traffic of a class by associating the class with a traffic filtering action. For example, you can filter packets sourced from an IP address according to network status.
Restrictions and guidelines: Traffic filtering configuration
The device supports the following application destinations for traffic filtering:
· Interface.
· VLANs.
· Globally.
· Control plane.
· User profile.
Procedure
1. Enter system view.
system-view
2. Define a traffic class.
a. Create a traffic class and enter traffic class view.
traffic classifier classifier-name [ operator { and | or } ]
b. Configure a match criterion.
if-match match-criteria
By default, no match criterion is configured.
For more information about configuring match criteria, see ACL and QoS Command Reference.
c. Return to system view.
quit
3. Define a traffic behavior.
a. Create a traffic behavior and enter traffic behavior view.
traffic behavior behavior-name
b. Configure the traffic filtering action.
filter { deny | permit }
By default, no traffic filtering action is configured.
c. Return to system view.
quit
4. Define a QoS policy.
a. Create a QoS policy and enter QoS policy view.
qos policy policy-name
b. Associate the traffic class with the traffic behavior in the QoS policy.
classifier classifier-name behavior behavior-name
By default, a traffic class is not associated with a traffic behavior.
c. Return to system view.
quit
5. Apply the QoS policy.
For more information, see "Applying the QoS policy."
By default, no QoS policy is applied.
6. (Optional.) Display the traffic filtering configuration.
display traffic behavior user-defined [ behavior-name ]
This command is available in any view.
Traffic filtering configuration examples
Example: Configuring traffic filtering
Network configuration
As shown in Figure 19, configure traffic filtering on GigabitEthernet 3/1/1 to deny the incoming packets with a source port number other than 21.
Procedure
# Create advanced ACL 3000, and configure a rule to match packets whose source port number is not 21.
<Device> system-view
[Device] acl advanced 3000
[Device-acl-ipv4-adv-3000] rule 0 permit tcp source-port neq 21
[Device-acl-ipv4-adv-3000] quit
# Create a traffic class named classifier_1, and use ACL 3000 as the match criterion in the traffic class.
[Device] traffic classifier classifier_1
[Device-classifier-classifier_1] if-match acl 3000
[Device-classifier-classifier_1] quit
# Create a traffic behavior named behavior_1, and configure the traffic filtering action to drop packets.
[Device] traffic behavior behavior_1
[Device-behavior-behavior_1] filter deny
[Device-behavior-behavior_1] quit
# Create a QoS policy named policy, and associate traffic class classifier_1 with traffic behavior behavior_1 in the QoS policy.
[Device] qos policy policy
[Device-qospolicy-policy] classifier classifier_1 behavior behavior_1
[Device-qospolicy-policy] quit
# Apply QoS policy policy to the incoming traffic of GigabitEthernet 3/1/1.
[Device] interface gigabitethernet 3/1/1
[Device-GigabitEthernet3/1/1] qos apply policy policy inbound
Configuring priority marking
About priority marking
Priority marking sets the priority fields or flag bits of packets to modify the priority of packets. For example, you can use priority marking to set IP precedence or DSCP for a class of IP packets to control the forwarding of these packets.
1. Configure a traffic behavior with a priority marking action.
2. Associate the traffic class with the traffic behavior.
Priority marking can be used together with priority mapping. For more information, see "Configuring priority mapping."
Configuring priority marking by using the MQC approach
Restrictions and guidelines
· The device supports the following application destinations for priority marking:
¡ Interface.
¡ VLANs.
¡ Globally.
¡ Control plane.
¡ User profile.
· The remark tunnel-dscp command is mutually exclusive with the remark dscp or remark ip-precedence command in one traffic behavior.
Procedure
1. Enter system view.
system-view
2. Define a traffic class.
a. Create a traffic class and enter traffic class view.
traffic classifier classifier-name [ operator { and | or } ]
b. Configure a match criterion.
if-match match-criteria
By default, no match criterion is configured.
For more information about the if-match command, see ACL and QoS Command Reference.
c. Return to system view.
quit
3. Define a traffic behavior.
a. Create a traffic behavior and enter traffic behavior view.
traffic behavior behavior-name
b. Configure a priority marking action.
For configurable priority marking actions, see the remark commands in ACL and QoS Command Reference.
c. Return to system view.
quit
4. Define a QoS policy.
a. Create a QoS policy and enter QoS policy view.
qos policy policy-name
b. Associate the traffic class with the traffic behavior in the QoS policy.
classifier classifier-name behavior behavior-name
By default, a traffic class is not associated with a traffic behavior.
c. Return to system view.
quit
5. Apply the QoS policy.
For more information, see "Applying the QoS policy."
By default, no QoS policy is applied.
6. (Optional.) Display the priority marking configuration.
display traffic behavior user-defined [ behavior-name ]
This command is available in any view.
Priority marking configuration examples
Example: Configuring priority marking
Network configuration
As shown in Figure 20, configure priority marking on the device to meet the following requirements:
|
Traffic source |
Destination |
Processing priority |
|
Host A, B |
Data server |
High |
|
Host A, B |
Mail server |
Medium |
|
Host A, B |
File server |
Low |
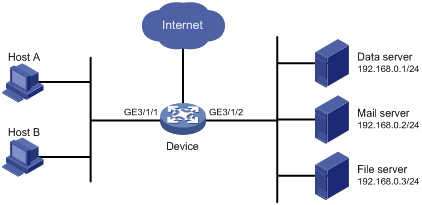
Procedure
# Create advanced ACL 3000, and configure a rule to match packets with destination IP address 192.168.0.1.
<Device> system-view
[Device] acl advanced 3000
[Device-acl-ipv4-adv-3000] rule permit ip destination 192.168.0.1 0
[Device-acl-ipv4-adv-3000] quit
# Create advanced ACL 3001, and configure a rule to match packets with destination IP address 192.168.0.2.
[Device] acl advanced 3001
[Device-acl-ipv4-adv-3001] rule permit ip destination 192.168.0.2 0
[Device-acl-ipv4-adv-3001] quit
# Create advanced ACL 3002, and configure a rule to match packets with destination IP address 192.168.0.3.
[Device] acl advanced 3002
[Device-acl-ipv4-adv-3002] rule permit ip destination 192.168.0.3 0
[Device-acl-ipv4-adv-3002] quit
# Create a traffic class named classifier_dbserver, and use ACL 3000 as the match criterion in the traffic class.
[Device] traffic classifier classifier_dbserver
[Device-classifier-classifier_dbserver] if-match acl 3000
[Device-classifier-classifier_dbserver] quit
# Create a traffic class named classifier_mserver, and use ACL 3001 as the match criterion in the traffic class.
[Device] traffic classifier classifier_mserver
[Device-classifier-classifier_mserver] if-match acl 3001
[Device-classifier-classifier_mserver] quit
# Create a traffic class named classifier_fserver, and use ACL 3002 as the match criterion in the traffic class.
[Device] traffic classifier classifier_fserver
[Device-classifier-classifier_fserver] if-match acl 3002
[Device-classifier-classifier_fserver] quit
# Create a traffic behavior named behavior_dbserver, and configure the action of setting the local precedence value to 4.
[Device] traffic behavior behavior_dbserver
[Device-behavior-behavior_dbserver] remark local-precedence 4
[Device-behavior-behavior_dbserver] quit
# Create a traffic behavior named behavior_mserver, and configure the action of setting the local precedence value to 3.
[Device] traffic behavior behavior_mserver
[Device-behavior-behavior_mserver] remark local-precedence 3
[Device-behavior-behavior_mserver] quit
# Create a traffic behavior named behavior_fserver, and configure the action of setting the local precedence value to 2.
[Device] traffic behavior behavior_fserver
[Device-behavior-behavior_fserver] remark local-precedence 2
[Device-behavior-behavior_fserver] quit
# Create a QoS policy named policy_server, and associate traffic classes with traffic behaviors in the QoS policy.
[Device] qos policy policy_server
[Device-qospolicy-policy_server] classifier classifier_dbserver behavior behavior_dbserver
[Device-qospolicy-policy_server] classifier classifier_mserver behavior behavior_mserver
[Device-qospolicy-policy_server] classifier classifier_fserver behavior behavior_fserver
[Device-qospolicy-policy_server] quit
# Apply QoS policy policy_server to the incoming traffic of GigabitEthernet 3/1/1.
[Device] interface gigabitethernet 3/1/1
[Device-GigabitEthernet3/1/1] qos apply policy policy_server inbound
[Device-GigabitEthernet3/1/1] quit
Example: Configuring priority marking and class-based accounting for priority marking verification
Network configuration
As shown in Figure 21, the source IP address of incoming packets on GigabitEthernet 3/1/1 of Device A is 192.168.0.1, and the DSCP value of the packets is 11.
Configure priority marking and class-based accounting on GigabitEthernet 3/1/2 of Device B to verify that priority marking works correctly.

Procedure
# Create basic ACL 2000, and configure a rule to match packets with source IP address 192.168.0.1.
<DeviceB> system-view
[DeviceB] acl basic 2000
[DeviceB-acl-ipv4-basic-2000] rule permit source 192.168.0.1 0
[DeviceB-acl-ipv4-basic-2000] quit
# Create a traffic class named sip, and use ACL 2000 as the match criterion in the traffic class.
[DeviceB] traffic classifier sip
[DeviceB-classifier-sip] if-match acl 2000
[DeviceB-classifier-sip] quit
# Create a traffic class named dscp50, and use DSCP 50 as the match criterion in the traffic class.
[DeviceB] traffic classifier dscp50
[DeviceB-classifier-dscp50] if-match dscp 50
[DeviceB-classifier-dscp50] quit
# Create a traffic behavior named r, and configure the action of setting the DSCP value to 50.
[DeviceB] traffic behavior r
[DeviceB-behavior-r] remark dscp 50
[DeviceB-behavior-r] quit
# Create a traffic behavior named a, and configure a class-based accounting action.
[DeviceB] traffic behavior a
[DeviceB-behavior-a] accounting packet
[DeviceB-behavior-a] quit
# Create a QoS policy named policy_r, and associate traffic class sip with traffic behavior r in the QoS policy.
[DeviceB] qos policy policy_r
[DeviceB-qospolicy-policy_r] classifier sip behavior r
[DeviceB-qospolicy-policy_r] quit
# Create a QoS policy named policy_a, and associate traffic class dscp50 with traffic behavior a in the QoS policy.
[DeviceB] qos policy policy_a
[DeviceB-qospolicy-policy_a] classifier dscp50 behavior a
[DeviceB-qospolicy-policy_a] quit
# Apply QoS policy policy_r to the incoming traffic of GigabitEthernet 3/1/1.
[DeviceB] interface gigabitethernet 3/1/1
[DeviceB-GigabitEthernet3/1/1] qos apply policy policy_r inbound
[DeviceB-GigabitEthernet3/1/1] quit
# Apply QoS policy policy_a to the outgoing traffic of GigabitEthernet 3/1/2.
[DeviceB] interface gigabitethernet 3/1/2
[DeviceB-GigabitEthernet3/1/2] qos apply policy policy_a outbound
[DeviceB-GigabitEthernet3/1/2] quit
Verifying the configuration
# Display information about the marking QoS policy.
[DeviceB] display qos policy interface GigabitEthernet 3/1/1 inbound
Interface: GigabitEthernet3/1/1
Direction: Inbound
Policy: policy_r
Classifier: sip
Operator: AND
Rule(s) :
If-match acl 2000
Behavior: r
Marking:
Remark dscp 50
# Display information about the accounting QoS policy.
[DeviceB] display qos policy interface GigabitEthernet 3/1/2 outbound
Interface: GigabitEthernet3/1/2
Direction: Outbound
Policy: policy_a
Classifier: dscp50
Operator: AND
Rule(s) :
If-match dscp 50
Behavior: a
Accounting enable:
74107375 (Packets)
The output shows that the accounting action works correctly.
Configuring traffic redirecting
About traffic redirecting
Traffic redirecting redirects packets matching the specified match criteria to a location for processing.
You can redirect packets to the following destinations:
· VPN instance.
· CPU.
· Interface.
· Card.
· Next hop.
If the next hop is in an MPLS network, IP TTL is always copied to the inner label TTL for packets redirected to the next hop. For more information about TTL propagation, see basic MPLS in MPLS Configuration Guide.
· NAT instance.
You can redirecting traffic to a NAT instance by binding the NAT instance. For more information about NAT, see Layer 3—IP Services Configuration Guide.
Restrictions and guidelines: Traffic redirecting configuration
· The device supports the following application destinations for traffic redirecting:
¡ Interface.
¡ VLANs.
¡ Globally.
¡ Control plane.
¡ User profile.
· If you execute the redirect command multiple times in the same traffic behavior, all configured actions take effect at the same time. The following exceptions exist:
¡ Any two of the redirect cpu, redirect http-to-cpu, and redirect https-to-cpu commands are mutually exclusive.
¡ The redirect failover-group and bind nat-instance commands are mutually exclusive.
· For IPoE Web authentication, you must configure the redirect http-to-cpu or redirect https-to-cpu command. If a user performs IPoE Web authentication through the Web browser but the HTTP request is not destined for the portal Web server, the access device redirects the request to the CPU. The CPU pushes the Web authentication page to the user.
· To prevent the CPU from receiving a large number of HTTP requests during IPoE Web authentication, use the ip subscriber http-fast-reply enable command to enable the HTTP request fast reply function. This function reduces the CPU load by identifying HTTP requests in hardware and automatically replying with HTTP responses. For more information about the ip subscriber http-fast-reply enable command, see IPoE commands in see BRAS Services Command Reference.
· Only CSPEX (except CSPEX-1204 and CSPEX-1104-E) and CEPC cards support redirecting traffic to Layer 3 Ethernet interfaces and loopback interfaces, and they do not support redirecting traffic to Layer 3 aggregate interfaces.
Procedure
1. Enter system view.
system-view
2. Define a traffic class.
a. Create a traffic class and enter traffic class view.
traffic classifier classifier-name [ operator { and | or } ]
b. Configure a match criterion.
if-match match-criteria
By default, no match criterion is configured for a traffic class.
For more information about the match criteria, see the if-match command in ACL and QoS Command Reference.
c. Return to system view.
quit
3. Define a traffic behavior.
a. Create a traffic behavior and enter traffic behavior view.
traffic behavior behavior-name
b. Configure a traffic redirecting action. Choose one option as needed:
In standalone mode:
redirect { access-vpn vpn-instance vpn-instance-name | cpu | failover-group group-name | http-to-cpu | https-to-cpu | interface interface-type interface-number | next-hop [ vpn-instance vpn-instance-name ] { ipv4-add1 [ track track-entry-number ] [ ipv4-add2 [ track track-entry-number ] ] | ipv6-add1 [ track track-entry-number ] [ ipv6-add2 [ track track-entry-number ] ] } | slot slot-number }
bind nat-instance instance-name
In IRF mode:
redirect { access-vpn vpn-instance vpn-instance-name | cpu | failover-group group-name | http-to-cpu | https-to-cpu | interface interface-type interface-number | next-hop [ vpn-instance vpn-instance-name ] { ipv4-add1 [ track track-entry-number ] [ ipv4-add2 [ track track-entry-number ] ] | ipv6-add1 [ track track-entry-number ] [ ipv6-add2 [ track track-entry-number ] ] } | chassis chassis-number slot slot-number }
bind nat-instance instance-name
By default, no traffic redirecting action is configured for a traffic behavior.
c. Return to system view.
quit
4. Define a QoS policy.
a. Create a QoS policy and enter QoS policy view.
qos policy policy-name
b. Associate the traffic class with the traffic behavior in the QoS policy.
classifier classifier-name behavior behavior-name
By default, a traffic class is not associated with a traffic behavior.
c. Return to system view.
quit
5. Apply the QoS policy.
For more information, see "Applying the QoS policy."
By default, no QoS policy is applied.
6. (Optional.) Display traffic redirecting configuration.
display traffic behavior user-defined [ behavior-name ]
This command is available in any view.
Traffic redirecting configuration examples
Example: Configuring traffic redirecting to the next hop
Network configuration
As shown in Figure 22:
· Device A is connected to Device B through two links. Device A and Device B are each connected to other devices.
· GigabitEthernet 3/1/1 of Device A is a trunk port and belongs to VLAN 200 and VLAN 201.
· GigabitEthernet 3/1/2 of Device A and GigabitEthernet 3/1/2 of Device B belong to VLAN 200.
· GigabitEthernet 3/1/3 of Device A and GigabitEthernet 3/1/3 of Device B belong to VLAN 201.
· On Device A, the IP address of VLAN-interface 200 is 200.1.1.1/24, and that of VLAN-interface 201 is 201.1.1.1/24.
· On Device B, the IP address of VLAN-interface 200 is 200.1.1.2/24, and that of VLAN-interface 201 is 201.1.1.2/24.
Configure the actions of redirecting traffic to the next hop to meet the following requirements:
· Packets with source IP address 2.1.1.1 received on GigabitEthernet 3/1/1 of Device A are forwarded to the next hop, with primary and secondary next-hop IPv4 addresses as 200.1.1.1/24 and 201.1.1.1/24, respectively.
· Packets with source IP address 2.1.1.2 received on GigabitEthernet 3/1/1 of Device A are forwarded to the next hop, with primary and secondary next-hop IPv4 addresses as 201.1.1.1/24 and 200.1.1.1/24, respectively.
· Other packets received on GigabitEthernet 3/1/1 of Device A are forwarded according to the routing table.
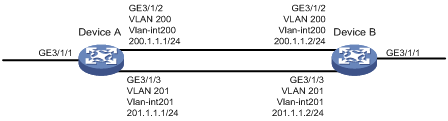
Procedure
# Create basic ACL 2000, and configure a rule to match packets with source IP address 2.1.1.1.
<DeviceA> system-view
[DeviceA] acl basic 2000
[DeviceA-acl-ipv4-basic-2000] rule permit source 2.1.1.1 0
[DeviceA-acl-ipv4-basic-2000] quit
# Create basic ACL 2001, and configure a rule to match packets with source IP address 2.1.1.2.
[DeviceA] acl basic 2001
[DeviceA-acl-ipv4-basic-2001] rule permit source 2.1.1.2 0
[DeviceA-acl-ipv4-basic-2001] quit
# Create a traffic class named classifier_1, and use ACL 2000 as the match criterion in the traffic class.
[DeviceA] traffic classifier classifier_1
[DeviceA-classifier-classifier_1] if-match acl 2000
[DeviceA-classifier-classifier_1] quit
# Create a traffic class named classifier_2, and use ACL 2001 as the match criterion in the traffic class.
[DeviceA] traffic classifier classifier_2
[DeviceA-classifier-classifier_2] if-match acl 2001
[DeviceA-classifier-classifier_2] quit
# Create a traffic behavior named behavior_1, and configure the action of redirecting traffic to the next hop, with primary and secondary next-hop IPv4 addresses as 200.1.1.1/24 and 201.1.1.1/24, respectively.
[DeviceA] traffic behavior behavior_1
[DeviceA-behavior-behavior_1] redirect next-hop 200.1.1.1 201.1.1.1
[DeviceA-behavior-behavior_1] quit
# Create a traffic behavior named behavior_2, and configure the action of redirecting traffic to the next hop, with primary and secondary next-hop IPv4 addresses as 201.1.1.1/24 and 200.1.1.1/24, respectively.
[DeviceA] traffic behavior behavior_2
[DeviceA-behavior-behavior_2] redirect next-hop 201.1.1.1 200.1.1.1
[DeviceA-behavior-behavior_2] quit
# Create a QoS policy named policy.
[DeviceA] qos policy policy
# Associate traffic class classifier_1 with traffic behavior behavior_1 in the QoS policy.
[DeviceA-qospolicy-policy] classifier classifier_1 behavior behavior_1
# Associate traffic class classifier_2 with traffic behavior behavior_2 in the QoS policy.
[DeviceA-qospolicy-policy] classifier classifier_2 behavior behavior_2
[DeviceA-qospolicy-policy] quit
# Apply QoS policy policy to the incoming traffic of GigabitEthernet 3/1/1.
[DeviceA] interface gigabitethernet 3/1/1
[DeviceA-GigabitEthernet3/1/1] qos apply policy policy inbound
Configuring global CAR
About global CAR
Global committed access rate (CAR) is an approach to policing traffic flows globally. It adds flexibility to common CAR where traffic policing is performed only on a per-traffic class or per-interface basis. In this approach, CAR actions are created in system view and each can be used to police multiple traffic flows as a whole.
Global CAR includes aggregate CAR and hierarchical CAR. Only aggregate CAR is supported in the current software version.
An aggregate CAR action is created globally. It can be directly applied to interfaces or used in the traffic behaviors associated with different traffic classes to police multiple traffic flows as a whole. The total rate of the traffic flows must conform to the traffic policing specifications set in the aggregate CAR action.
Configuring aggregate CAR by using the MQC approach
1. Enter system view.
system-view
2. Define a traffic class.
a. Create a traffic class and enter traffic class view.
traffic classifier classifier-name [ operator { and | or } ]
b. Configure a match criterion.
if-match match-criteria
By default, no match criterion is configured.
For configurable match criteria, see the if-match command in ACL and QoS Command Reference.
c. Return to system view.
quit
3. Configure an aggregate CAR action.
qos car car-name aggregative cir committed-information-rate [ cbs committed-burst-size [ ebs excess-burst-size ] ] [ green action | red action | yellow action ] *
qos car car-name aggregative cir committed-information-rate [ cbs committed-burst-size ] pir peak-information-rate [ ebs excess-burst-size ] [ green action | red action | yellow action ] *
By default, no aggregate CAR action is configured.
If you set the cir committed-information-rate option to a value in the range of 1 to 8 kbps on CSPEX cards (except CSPEX-1204 and CSPEX-1104-E) and CEPC cards, the actual setting takes effect. If you set this option to a value in the range of 1 to 8 kbps on any other card, 8 kbps always takes effect.
On CSPC (except CSPC-GE16XP4L-E, CSPC-GE24L-E, and CSPC-GP24GE8XP2L-E) and CMPE-1104 cards, an aggregate CAR action does not take effect if it is applied to the outbound direction.
4. Define a traffic behavior.
a. Enter traffic behavior view.
traffic behavior behavior-name
b. Use the aggregate CAR in the traffic behavior.
car name car-name
By default, no aggregate CAR action is used in a traffic behavior.
5. Apply the QoS policy.
For more information, see "Applying the QoS policy."
By default, no QoS policy is applied.
Display and maintenance commands for global CAR
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display statistics for global CAR actions. |
display qos car name [ car-name ] |
|
Clear statistics for global CAR actions. |
reset qos car name [ car-name ] |
Global CAR configuration examples
Example: Configuring aggregate CAR
Network configuration
As shown in Figure 23, configure aggregate CAR to rate-limit the traffic of VLAN 10 and VLAN 100 received on GigabitEthernet 3/1/1 by using these parameters: CIR 2560 kbps and CBS 20000 bytes.
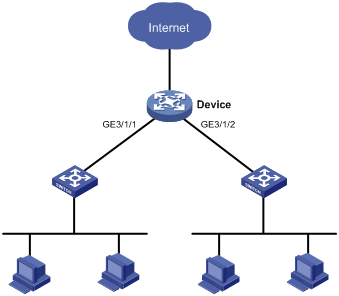
Procedure
# Configure an aggregate CAR action named aggcar-1 according to the rate limit requirements.
<Device> system-view
[Device] qos car aggcar-1 aggregative cir 2560 cbs 20000
# Create class 1 to match traffic of VLAN 10. Create behavior 1 and use aggregate CAR action aggcar-1 in the behavior.
[Device] traffic classifier 1
[Device-classifier-1] if-match service-vlan-id 10
[Device-classifier-1] quit
[Device] traffic behavior 1
[Device-behavior-1] car name aggcar-1
[Device-behavior-1] quit
# Create class 2 to match traffic of VLAN 100. Create behavior 2 and use aggregate CAR action aggcar-1 in the behavior.
[Device] traffic classifier 2
[Device-classifier-2] if-match service-vlan-id 100
[Device-classifier-2] quit
[Device] traffic behavior 2
[Device-behavior-2] car name aggcar-1
[Device-behavior-2] quit
# Create a QoS policy named car, associate class 1 with behavior 1, and associate class 2 with behavior 2.
[Device] qos policy car
[Device-qospolicy-car] classifier 1 behavior 1
[Device-qospolicy-car] classifier 2 behavior 2
[Device-qospolicy-car] quit
# Apply QoS policy car to the incoming traffic of GigabitEthernet 3/1/1.
[Device] interface gigabitethernet 3/1/1
[Device-GigabitEthernet3/1/1]qos apply policy car inbound
Configuring class-based accounting
About class-based accounting
Class-based accounting collects statistics (in packets or bytes) on a per-traffic class basis. For example, you can define the action to collect statistics for traffic sourced from a certain IP address. By analyzing the statistics, you can determine whether anomalies have occurred and what action to take.
Restrictions and guidelines: Class-based accounting configuration
The device supports the following application destinations for class-based accounting:
· Interface.
· VLANs.
· Control plane.
· User profile.
Procedure
1. Enter system view.
system-view
2. Define a traffic class.
a. Create a traffic class and enter traffic class view.
traffic classifier classifier-name [ operator { and | or } ]
b. Configure a match criterion.
if-match match-criteria
By default, no match criterion is configured.
For more information about the if-match command, see ACL and QoS Command Reference.
c. Return to system view.
quit
3. Define a traffic behavior.
a. Create a traffic behavior and enter traffic behavior view.
traffic behavior behavior-name
b. Configure an accounting action.
accounting { byte | packet }
By default, no traffic accounting action is configured.
c. Return to system view.
quit
4. Define a QoS policy.
a. Create a QoS policy and enter QoS policy view.
qos policy policy-name
b. Associate the traffic class with the traffic behavior in the QoS policy.
classifier classifier-name behavior behavior-name
By default, a traffic class is not associated with a traffic behavior.
c. Return to system view.
quit
5. Apply the QoS policy.
For more information, see "Applying the QoS policy."
By default, no QoS policy is applied.
6. (Optional.) Display the class-based accounting configuration.
display traffic behavior user-defined [ behavior-name ]
Class-based accounting configuration examples
Example: Configuring class-based accounting
Network configuration
As shown in Figure 24, configure class-based accounting on GigabitEthernet 3/1/1 to collect statistics for incoming traffic from 1.1.1.1/24.

Procedure
# Create basic ACL 2000, and configure a rule to match packets with source IP address 1.1.1.1.
<Device> system-view
[Device] acl basic 2000
[Device-acl-ipv4-basic-2000] rule permit source 1.1.1.1 0
[Device-acl-ipv4-basic-2000] quit
# Create a traffic class named classifier_1, and use ACL 2000 as the match criterion in the traffic class.
[Device] traffic classifier classifier_1
[Device-classifier-classifier_1] if-match acl 2000
[Device-classifier-classifier_1] quit
# Create a traffic behavior named behavior_1, and configure the class-based accounting action.
[Device] traffic behavior behavior_1
[Device-behavior-behavior_1] accounting
[Device-behavior-behavior_1] quit
# Create a QoS policy named policy, and associate traffic class classifier_1 with traffic behavior behavior_1 in the QoS policy.
[Device] qos policy policy
[Device-qospolicy-policy] classifier classifier_1 behavior behavior_1
[Device-qospolicy-policy] quit
# Apply QoS policy policy to the incoming traffic of GigabitEthernet 3/1/1.
[Device] interface gigabitethernet 3/1/1
[Device-GigabitEthernet3/1/1] qos apply policy policy inbound
[Device-GigabitEthernet3/1/1] quit
# Display traffic statistics to verify the configuration.
[Device] display qos policy interface gigabitethernet 3/1/1
Interface: GigabitEthernet3/1/1
Direction: Inbound
Policy: policy
Classifier: classifier_1
Operator: AND
Rule(s) :
If-match acl 2000
Behavior: behavior_1
Accounting enable:
28529 (Packets)
Configuring queue-based accounting
About queue-based accounting
Queue-based accounting collects queue-based traffic statistics for interfaces, such as:
· The total length of a queue.
· The current queue length.
· The total number of packets forwarded.
· The number of per-color packets forwarded.
Procedure
1. Enter system view.
system-view
2. Enable queue-based accounting.
qos queue-statistics { inbound | outbound }
By default, queue-based accounting is enabled.
You can configure the inbound keyword, but it does not take effect.
Display and maintenance commands for queue-based accounting
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
(In standalone mode.) Display queue-based traffic statistics for interfaces. |
display qos queue-statistics interface [ interface-type interface-number [ slot slot-number ] ] outbound |
|
(In IRF mode.) Display queue-based traffic statistics for interfaces. |
display qos queue-statistics interface [ interface-type interface-number [ chassis chassis-number slot slot-number ] ] outbound |
|
Clear queue-based traffic statistics for interfaces (see Interface Command Reference). |
reset counters interface [ interface-type [ interface-number ] ] |
Configuring QPPB
About QPPB
The QoS Policy Propagation Through the Border Gateway Protocol (QPPB) feature enables you to classify IP packets based on the following attributes:
· BGP community lists.
· Prefix lists.
· BGP AS paths.
Application scenarios
QPPB minimizes the QoS policy configuration and management efforts on the BGP route receiver when the network topology changes. It is suitable for a large-scaled complex network.
The QPPB feature is implemented as follows:
· The BGP route sender preclassifies routes before advertising them.
· The BGP route receiver performs the following operations:
¡ Sets the IP precedence and local QoS ID for the routes.
¡ Takes appropriate QoS actions on the packets that match the routes.
QPPB is used in the following scenarios:
· Traffic classification based on source or destination IP addresses.
· Traffic classification based on IBGP and EBGP within an autonomous system or across multiple autonomous systems.
QPPB fundamentals
QPPB works on the BGP receiver by applying a QoS policy to BGP routes with the same IP precedence or local QoS ID. It depends on the BGP route sender to preclassify routes.
The BGP route sender uses a routing policy to set route attributes for BGP routes before advertising them.
The BGP sender performs the following operations:
· Uses a routing policy to match routes based on these route attributes.
· Sets IP precedence and local QoS ID for the matching routes.
The BGP receiver performs the following operations:
1. Compares the routes with the incoming route policy based on their BGP AS path, prefix, or community attributes.
2. Applies the IP precedence and local QoS ID to the matching routes.
3. Adds the BGP routes and their associated IP precedence and local QoS ID to the routing table.
4. Applies the IP precedence and local QoS ID to the packets sourced from or destined to the IP address in the route.
5. Takes QoS actions on the packets according to the QoS priority settings.
QPPB tasks at a glance
To configure QPPB, perform the following tasks:
1. Configuring the route sender
a. Configuring basic BGP functions
b. (Optional.) Creating a routing policy
2. Configuring the route receiver
a. Configuring basic BGP functions
b. Configuring a routing policy
c. Enabling QPPB on the route receiving interface
Configuring the route sender
Configure the BGP route sender to set route attributes for routes before advertising them.
Configuring basic BGP functions
For more information, see Layer 3—IP Routing Configuration Guide.
Creating a routing policy
Configuring the route receiver
Configure the BGP route receiver to match the route attributes set by the router sender and set the QPPB-related attributes.
Configuring basic BGP functions
For more information, see Layer 3—IP Routing Configuration Guide.
Configuring a routing policy
Configure a routing policy to perform the following operations:
· Match the route attributes set by the route sender.
· Set the IP precedence, local QoS ID, or both for the matching routes.
For more information, see Layer 3—IP Routing Configuration Guide.
Enabling QPPB on the route receiving interface
Hardware and feature compatibility
This feature is available only on CSPEX (except CSPEX-1204 and CSPEX-1104-E) and CEPC cards.
Restrictions and guidelines
For QPPB to work correctly, you must configure the QoS policy as follows:
· Use the IP precedence or local QoS ID set in the routing policy to match packets.
· Specify the mode qppb-manipulation keyword when associating a traffic behavior with a traffic class.
For more information about QoS policies, see "Configuring a QoS policy."
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Enable QPPB on the interface.
bgp-policy { destination | source } ip-prec-map ip-qos-map
By default, QPPB is disabled.
This command applies only to incoming traffic.
4. Apply a QoS policy to the interface.
qos apply policy policy-name { inbound | outbound }
By default, no QoS policy is applied to an interface.
QPPB configuration examples
Example: Configuring QPPB in an IPv4 network
Network configuration
As shown in Figure 25, all devices run BGP.
Configure QPPB so that Device B can perform the following operations:
· Receive routes.
· Set IP precedence values and local QoS IDs according to the routing policy.
· Use the QoS policy to limit the traffic rate to 512000 kbps.
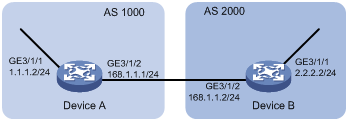
Procedure
1. Configure IP addresses for each interface. (Details not shown.)
2. Configure a BGP connection to Device B, and add the network 1.1.1.0/8 to the BGP routing table on Device A.
<DeviceA> system-view
[DeviceA] bgp 1000
[DeviceA-bgp] peer 168.1.1.2 as-number 2000
[DeviceA-bgp] peer 168.1.1.2 connect-interface gigabitethernet 3/1/2
[DeviceA-bgp] address-family ipv4
[DeviceA-bgp-ipv4] import-route direct
[DeviceA-bgp-ipv4] peer 168.1.1.2 enable
[DeviceA-bgp-ipv4] quit
[DeviceA-bgp] quit
3. Configure Device B:
# Configure a BGP connection to Device A.
<DeviceB> system-view
[DeviceB] bgp 2000
[DeviceB-bgp] peer 168.1.1.1 as-number 1000
[DeviceB-bgp] peer 168.1.1.1 connect-interface gigabitethernet 3/1/2
[DeviceB-bgp] address-family ipv4
[DeviceB-bgp-ipv4] peer 168.1.1.1 enable
[DeviceB-bgp-ipv4] peer 168.1.1.1 route-policy qppb import
[DeviceB-bgp-ipv4] quit
[DeviceB-bgp] quit
# Configure the routing policy qppb.
[DeviceB] route-policy qppb permit node 0
[DeviceB-route-policy-qppb-0] apply ip-precedence 1
[DeviceB-route-policy-qppb-0] apply qos-local-id 3
[DeviceB-route-policy-qppb-0] quit
# Enable QPPB on GigabitEthernet 3/1/2.
[DeviceB] interface gigabitethernet 3/1/2
[DeviceB-GigabitEthernet3/1/2] bgp-policy source ip-prec-map ip-qos-map
[DeviceB-GigabitEthernet3/1/2] quit
# Configure a QoS policy.
[DeviceB] traffic classifier qppb
[DeviceB-classifier-qppb] if-match ip-precedence 1
[DeviceB-classifier-qppb] if-match qos-local-id 3
[DeviceB-classifier-qppb] quit
[DeviceB] traffic behavior qppb
[DeviceB-behavior-qppb] car cir 512000 green pass red discard
[DeviceB-behavior-qppb] quit
[DeviceB] qos policy qppb
[DeviceB-qospolicy-qppb] classifier qppb behavior qppb mode qppb-manipulation
[DeviceB-qospolicy-qppb] quit
# Apply the QoS policy to incoming traffic on GigabitEthernet 3/1/2.
[DeviceB] interface gigabitethernet 3/1/2
[DeviceB-GigabitEthernet3/1/2] qos apply policy qppb inbound
[DeviceB-GigabitEthernet3/1/2] quit
Verifying the configuration
# Verify that the related route on Device B takes effect.
[DeviceB] display ip routing-table 1.1.1.0 24 verbose
Summary Count : 1
Destination: 1.1.1.0/24
Protocol: BGP Process ID: 0
SubProtID: 0x2 Age: 00h00m33s
Cost: 0 Preference: 255
IpPre: 1 QosLocalID: 3
Tag: 0 State: Active Adv
OrigTblID: 0x0 OrigVrf: default-vrf
TableID: 0x2 OrigAs: 1000
NibID: 0x15000000 LastAs: 1000
AttrID: 0x0 Neighbor: 168.1.1.1
Flags: 0x10060 OrigNextHop: 168.1.1.1
Label: NULL RealNextHop: 168.1.1.1
BkLabel: NULL BkNextHop: N/A
SRLabel: NULL BkSRLabel: NULL
SIDIndex: NULL InLabel: NULL
Tunnel ID: Invalid Interface: GigabitEthernet3/1/2
BkTunnel ID: Invalid BkInterface: N/A
FtnIndex: 0x0 TrafficIndex: N/A
Connector: N/A VpnPeerId:
N/A
Dscp: N/A
# Display the QoS policy configuration on GigabitEthernet3/1/2 of Device B.
[DeviceB] display qos policy interface gigabitethernet 3/1/2
Interface: GigabitEthernet3/1/2
Direction: Inbound
Policy: qppb
Classifier: default-class
Mode: qppb-manipulation
Matched : 51 (Packets) 4022 (Bytes)
5-minute statistics:
Forwarded: 0/28 (pps/bps)
Dropped : 0/0 (pps/bps)
Operator: AND
Rule(s) :
If-match any
Behavior: be
-none-
Classifier: qppb
Mode: qppb-manipulation
Matched : 0 (Packets) 0 (Bytes)
5-minute statistics:
Forwarded: 0/0 (pps/bps)
Dropped : 0/0 (pps/bps)
Operator: AND
Rule(s) :
If-match ip-precedence 1
If-match qos-local-id 3
Behavior: qppb
Committed Access Rate:
CIR 512000 (kbps), CBS 32000000 (Bytes), EBS 0 (Bytes)
Green action : pass
Yellow action : pass
Red action : discard
Green packets : 0 (Packets) 0 (Bytes)
Yellow packets: 0 (Packets) 0 (Bytes)
Red packets : 0 (Packets) 0 (Bytes)
Example: Configuring QPPB in an MPLS L3VPN
Network configuration
As shown in Figure 26, all devices run BGP.
Configure QPPB so that Device C can perform the following operations:
· Receive routes.
· Set the QPPB local QoS IDs.
· Use the QoS policy to limit the traffic rate to 200000 kbps in each direction.

Table 3 Interfaces and IP address assignment
|
Device |
Interface |
IP address |
Device |
Interface |
IP address |
|
Device A |
GE3/1/1 |
192.168.1.2/24 |
Device B |
GE3/1/1 |
167.1.1.2/24 |
|
GE3/1/2 |
167.1.1.1/24 |
GE3/1/2 |
168.1.1.2/24 |
||
|
Device C |
GE3/1/1 |
169.1.1.2/24 |
Device D |
GE3/1/2 |
169.1.1.1/24 |
|
GE3/1/2 |
168.1.1.1/24 |
GE3/1/1 |
192.168.3.2/24 |
Procedure
1. Configure IP addresses for each interface. (Details not shown.)
2. Configure a BGP connection on Device A.
<DeviceA> system-view
[DeviceA] bgp 100
[DeviceA-bgp] peer 167.1.1.2 as-number 200
[DeviceA-bgp] peer 167.1.1.2 connect-interface gigabitethernet 3/1/2
[DeviceA-bgp] address-family ipv4
[DeviceA-bgp-ipv4] import-route direct
[DeviceA-bgp-ipv4] peer 167.1.1.2 enable
[DeviceA-bgp-ipv4] quit
[DeviceA-bgp] quit
3. Configure Device B:
# Configure a VPN instance.
<DeviceB> system-view
[DeviceB] ip vpn-instance vpn1
[DeviceB-vpn-instance-vpn1] route-distinguisher 200:1
[DeviceB-vpn-instance-vpn1] vpn-target 200:1 export-extcommunity
[DeviceB-vpn-instance-vpn1] vpn-target 200:1 import-extcommunity
[DeviceB-vpn-instance-vpn1] quit
# Configure a BGP connection.
[DeviceB] router id 1.1.1.1
[DeviceB] bgp 200
[DeviceB-bgp] peer 2.2.2.2 as-number 200
[DeviceB-bgp] peer 2.2.2.2 connect-interface loopback 0
[DeviceB-bgp] ip vpn-instance vpn1
[DeviceB-bgp-vpn1] peer 167.1.1.1 as-number 100
[DeviceB-bgp-vpn1] address-family ipv4
[DeviceB-bgp-ipv4-vpn1] peer 167.1.1.1 enable
[DeviceB-bgp-ipv4-vpn1] quit
[DeviceB-bgp] address-family vpnv4
[DeviceB-bgp-vpnv4] peer 2.2.2.2 enable
[DeviceB-bgp-vpnv4] quit
[DeviceB-bgp] quit
# Configure MPLS.
[DeviceB] mpls lsr-id 1.1.1.1
[DeviceB] mpls ldp
[DeviceB-mpls-ldp] quit
# Configure OSPF.
[DeviceB] ospf
[DeviceB-ospf-1] area 0
[DeviceB-ospf-1-area-0.0.0.0] network 1.1.1.1 0.0.0.0
[DeviceB-ospf-1-area-0.0.0.0] network 168.1.1.0 0.0.0.255
[DeviceB-ospf-1-area-0.0.0.0] quit
[DeviceB-ospf-1] quit
# Bind GigabitEthernet 3/1/1 to VPN instance vpn1.
[DeviceB] interface gigabitethernet 3/1/1
[DeviceB-GigabitEthernet3/1/1] ip binding vpn-instance vpn1
[DeviceB-GigabitEthernet3/1/1] ip address 167.1.1.2 24
[DeviceB-GigabitEthernet3/1/1] quit
# Enable MPLS on GigabitEthernet 3/1/2.
[DeviceB] interface gigabitethernet 3/1/2
[DeviceB-GigabitEthernet3/1/2] mpls enable
[DeviceB-GigabitEthernet3/1/2] mpls ldp enable
[DeviceB-GigabitEthernet3/1/2] quit
4. Configure Device C:
# Configure a VPN instance.
<DeviceC> system-view
[DeviceC] ip vpn-instance vpn1
[DeviceC-vpn-instance-vpn1] route-distinguisher 200:1
[DeviceC-vpn-instance-vpn1] vpn-target 200:1 export-extcommunity
[DeviceC-vpn-instance-vpn1] vpn-target 200:1 import-extcommunity
[DeviceC-vpn-instance-vpn1] quit
# Configure a BGP connection.
[DeviceC] router id 2.2.2.2
[DeviceC] bgp 200
[DeviceC-bgp] peer 1.1.1.1 as-number 200
[DeviceC-bgp] peer 1.1.1.1 connect-interface loopback 0
[DeviceC-bgp] ip vpn-instance vpn1
[DeviceC-bgp-vpn1] peer 169.1.1.1 as-number 300
[DeviceC-bgp-vpn1] address-family ipv4
[DeviceC-bgp-ipv4-vpn1] peer 169.1.1.1 enable
[DeviceC-bgp-ipv4-vpn1] peer 169.1.1.1 route-policy qppb import
[DeviceC-bgp-ipv4-vpn1] quit
[DeviceC-bgp-vpn1] quit
[DeviceC-bgp] address-family vpnv4
[DeviceC-bgp-vpnv4] peer 1.1.1.1 enable
[DeviceC-bgp-vpnv4] peer 1.1.1.1 route-policy qppb import
[DeviceC-bgp-vpnv4] quit
[DeviceC-bgp] quit
# Configure a routing policy.
[DeviceC] route-policy qppb permit node 0
[DeviceC-route-policy-qppb-0] apply qos-local-id 3
[DeviceC-route-policy-qppb-0] quit
# Configure MPLS.
[DeviceC] mpls lsr-id 2.2.2.2
[DeviceC] mpls ldp
[DeviceC-mpls-ldp] quit
# Configure OSPF.
[DeviceC] ospf
[DeviceC-ospf-1] area 0
[DeviceC-ospf-1-area-0.0.0.0] network 2.2.2.2 0.0.0.0
[DeviceC-ospf-1-area-0.0.0.0] network 168.1.1.0 0.0.0.255
[DeviceC-ospf-1-area-0.0.0.0] quit
[DeviceC-ospf-1] quit
# Configure a QoS policy.
[DeviceC] traffic classifier qppb
[DeviceC-classifier-qppb] if-match qos-local-id 3
[DeviceC-classifier-qppb] quit
[DeviceC] traffic behavior qppb
[DeviceC-behavior-qppb] car cir 200000 green pass red discard
[DeviceC-behavior-qppb] quit
[DeviceC] qos policy qppb
[DeviceC-qospolicy-qppb] classifier qppb behavior qppb mode qppb-manipulation
[DeviceC-qospolicy-qppb] quit
# Enable MPLS on GigabitEthernet 3/1/2.
[DeviceC] interface gigabitethernet 3/1/2
[DeviceC-GigabitEthernet3/1/2] mpls enable
[DeviceC-GigabitEthernet3/1/2] mpls ldp enable
# Enable QPPB on GigabitEthernet 3/1/1 and GigabitEthernet 3/1/2.
[DeviceC-GigabitEthernet3/1/2] bgp-policy destination ip-qos-map
[DeviceC-GigabitEthernet3/1/2] quit
[DeviceC] interface gigabitethernet 3/1/1
[DeviceC-GigabitEthernet3/1/1] bgp-policy destination ip-qos-map
[DeviceC-GigabitEthernet3/1/1] quit
# Bind GigabitEthernet 3/1/1 to VPN instance vpn1.
[DeviceC] interface gigabitethernet 3/1/1
[DeviceC-GigabitEthernet3/1/1] ip binding vpn-instance vpn1
[DeviceC-GigabitEthernet3/1/1] ip address 169.1.1.2 24
# Apply QoS policy qppb to the incoming traffic of GigabitEthernet 3/1/1.
[DeviceC-GigabitEthernet3/1/1] qos apply policy qppb inbound
[DeviceC-GigabitEthernet3/1/1] quit
# Apply QoS policy qppb to the incoming traffic of GigabitEthernet 3/1/2.
[DeviceC] interface gigabitethernet 3/1/2
[DeviceC-GigabitEthernet3/1/2] qos apply policy qppb inbound
5. Configure a BGP connection on Device D.
<DeviceD> system-view
[DeviceD] bgp 300
[DeviceD-bgp] peer 169.1.1.2 as-number 200
[DeviceD-bgp] peer 169.1.1.2 connect-interface gigabitethernet 3/1/2
[DeviceD-bgp] address-family ipv4
[DeviceD-bgp-ipv4] peer 169.1.1.2 enable
[DeviceD-bgp-ipv4] import-route direct
[DeviceD-bgp-ipv4] quit
Verifying the configuration
# Verify that the related routes on Device A take effect.
[DeviceA] display ip routing-table
Destinations : 16 Routes : 16
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
127.0.0.0/8 Direct 0 0 127.0.0.1 InLoop0
127.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
127.0.0.1/32 Direct 0 0 127.0.0.1 InLoop0
127.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
167.1.1.0/24 Direct 0 0 167.1.1.1 GE3/1/2
167.1.1.0/32 Direct 0 0 167.1.1.1 GE3/1/2
167.1.1.1/32 Direct 0 0 127.0.0.1 InLoop0
167.1.1.255/32 Direct 0 0 167.1.1.1 GE3/1/2
169.1.1.0/24 BGP 255 0 167.1.1.2 GE3/1/2
192.168.1.0/24 Direct 0 0 192.168.1.2 GE3/1/1
192.168.1.0/32 Direct 0 0 192.168.1.2 GE3/1/1
192.168.1.2/32 Direct 0 0 127.0.0.1 InLoop0
192.168.1.255/32 Direct 0 0 192.168.1.2 GE3/1/1
192.168.3.0/24 BGP 255 0 167.1.1.2 GE3/1/2
255.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
# Verify that the related routes on Device B take effect.
[DeviceB] display ip routing-table
Destinations : 12 Routes : 12
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
1.1.1.1/32 Direct 0 0 127.0.0.1 InLoop0
2.2.2.2/32 OSPF 10 1 168.1.1.1 GE3/1/2
127.0.0.0/8 Direct 0 0 127.0.0.1 InLoop0
127.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
127.0.0.1/32 Direct 0 0 127.0.0.1 InLoop0
127.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
168.1.1.0/24 Direct 0 0 168.1.1.2 GE3/1/2
168.1.1.0/32 Direct 0 0 168.1.1.2 GE3/1/2
168.1.1.2/32 Direct 0 0 127.0.0.1 InLoop0
168.1.1.255/32 Direct 0 0 168.1.1.2 GE3/1/2
255.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
[DeviceB] display ip routing-table vpn-instance vpn1
Destinations : 14 Routes : 14
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
127.0.0.0/8 Direct 0 0 127.0.0.1 InLoop0
127.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
127.0.0.1/32 Direct 0 0 127.0.0.1 InLoop0
127.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
167.1.1.0/24 Direct 0 0 167.1.1.2 GE3/1/1
167.1.1.0/32 Direct 0 0 167.1.1.2 GE3/1/1
167.1.1.2/32 Direct 0 0 127.0.0.1 InLoop0
167.1.1.255/32 Direct 0 0 167.1.1.2 GE3/1/1
169.1.1.0/24 BGP 255 0 2.2.2.2 GE3/1/2
192.168.1.0/24 BGP 255 0 167.1.1.1 GE3/1/1
192.168.2.0/24 BGP 255 0 167.1.1.1 GE3/1/1
192.168.3.0/24 BGP 255 0 2.2.2.2 GE3/1/2
255.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
# Verify that the related routes on Device C take effect.
[DeviceC] display ip routing-table
Destinations : 12 Routes : 12
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
1.1.1.1/32 OSPF 10 1 168.1.1.2 GE3/1/2
2.2.2.2/32 Direct 0 0 127.0.0.1 InLoop0
127.0.0.0/8 Direct 0 0 127.0.0.1 InLoop0
127.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
127.0.0.1/32 Direct 0 0 127.0.0.1 InLoop0
127.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
168.1.1.0/24 Direct 0 0 168.1.1.1 GE3/1/2
168.1.1.0/32 Direct 0 0 168.1.1.1 GE3/1/2
168.1.1.1/32 Direct 0 0 127.0.0.1 InLoop0
168.1.1.255/32 Direct 0 0 168.1.1.1 GE3/1/2
224.0.0.0/4 Direct 0 0 0.0.0.0 NULL0
224.0.0.0/24 Direct 0 0 0.0.0.0 NULL0
255.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
[DeviceC] display ip routing-table vpn-instance vpn1
Destinations : 14 Routes : 14
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
127.0.0.0/8 Direct 0 0 127.0.0.1 InLoop0
127.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
127.0.0.1/32 Direct 0 0 127.0.0.1 InLoop0
127.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
167.1.1.0/24 BGP 255 0 1.1.1.1 GE3/1/2
169.1.1.0/24 Direct 0 0 169.1.1.2 GE3/1/1
169.1.1.0/32 Direct 0 0 169.1.1.2 GE3/1/1
169.1.1.2/32 Direct 0 0 127.0.0.1 InLoop0
169.1.1.255/32 Direct 0 0 169.1.1.2 GE3/1/1
192.168.1.0/24 BGP 255 0 1.1.1.1 GE3/1/2
192.168.2.0/24 BGP 255 0 169.1.1.1 GE3/1/1
192.168.3.0/24 BGP 255 0 169.1.1.1 GE3/1/1
255.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
# Verify that the related routes on Device D take effect.
[DeviceD] display ip routing-table
Destinations : 16 Routes : 16
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
127.0.0.0/8 Direct 0 0 127.0.0.1 InLoop0
127.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
127.0.0.1/32 Direct 0 0 127.0.0.1 InLoop0
127.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
167.1.1.0/24 BGP 255 0 169.1.1.2 GE3/1/2
169.1.1.0/24 Direct 0 0 169.1.1.1 GE3/1/2
169.1.1.0/32 Direct 0 0 169.1.1.1 GE3/1/2
169.1.1.1/32 Direct 0 0 127.0.0.1 InLoop0
169.1.1.255/32 Direct 0 0 169.1.1.1 GE3/1/2
192.168.1.0/24 BGP 255 0 169.1.1.2 GE3/1/2
192.168.3.0/24 Direct 0 0 192.168.3.2 GE3/1/1
192.168.3.0/32 Direct 0 0 192.168.3.2 GE3/1/1
192.168.3.2/32 Direct 0 0 127.0.0.1 InLoop0
192.168.3.255/32 Direct 0 0 192.168.3.2 GE3/1/1
255.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
# Display the QoS policy configuration in the inbound direction on Device C.
[DeviceC] display qos policy interface inbound
Interface: GigabitEthernet3/1/1
Direction: Inbound
Policy: qppb
Classifier: default-class
Mode: qppb-manipulation
Matched : 312 (Packets) 18916 (Bytes)
5-minute statistics:
Forwarded: 0/24 (pps/bps)
Dropped : 0/0 (pps/bps)
Operator: AND
Rule(s) :
If-match any
Behavior: be
-none-
Classifier: qppb
Mode: qppb-manipulation
Matched : 0 (Packets) 0 (Bytes)
5-minute statistics:
Forwarded: 0/0 (pps/bps)
Dropped : 0/0 (pps/bps)
Operator: AND
Rule(s) :
If-match qos-local-id 3
Behavior: qppb
Committed Access Rate:
CIR 200000 (kbps), CBS 1250000 (Bytes), EBS 0 (Bytes)
Green action : pass
Yellow action : pass
Red action : discard
Green packets : 0 (Bytes) 0 (bps)
Yellow packets: 0 (Bytes) 0 (bps)
Red packets : 0 (Bytes) 0 (bps)
Interface: GigabitEthernet3/1/2
Direction: Inbound
Policy: qppb
Classifier: default-class
Mode: qppb-manipulation
Matched : 311 (Packets) 23243 (Bytes)
5-minute statistics:
Forwarded: 0/24 (pps/bps)
Dropped : 0/0 (pps/bps)
Operator: AND
Rule(s) :
If-match any
Behavior: be
-none-
Classifier: qppb
Mode: qppb-manipulation
Matched : 0 (Packets) 0 (Bytes)
5-minute statistics:
Forwarded: 0/0 (pps/bps)
Dropped : 0/0 (pps/bps)
Operator: AND
Rule(s) :
If-match qos-local-id 3
Behavior: qppb
Committed Access Rate:
CIR 200000 (kbps), CBS 12500480 (Bytes), EBS 0 (Bytes)
Green action : pass
Yellow action : pass
Red action : discard
Green packets : 0 (Bytes) 0 (bps)
Yellow packets: 0 (Bytes) 0 (bps)
Red packets : 0 (Bytes) 0 (bps)
Example: Configuring QPPB in an IPv6 network
Network configuration
As shown in Figure 27, all devices run BGP.
Configure QPPB so that Device B can perform the following operations:
· Receive routes.
· Set the QPPB IP precedence value.
· Use the QoS policy to limit the rate of traffic with the IP precedence value to 512000 kbps.

Procedure
1. Configure IPv6 addresses for each interface. (Details not shown.)
2. Configure BGP on Device A.
<DeviceA> system-view
[DeviceA] bgp 1000
[DeviceA] peer 168::2 as-number 2000
[DeviceA] peer 168::2 connect-interface gigabitethernet 3/1/2
[DeviceA-bgp] address-family ipv6
[DeviceA-bgp-ipv6] peer 168::2 enable
[DeviceA-bgp-ipv6] import-route direct
[DeviceA-bgp-ipv6] quit
[DeviceA-bgp] quit
3. Configure Device B:
# Configure BGP.
<DeviceB> system-view
[DeviceB] bgp 2000
[DeviceB] peer 168::1 as-number 1000
[DeviceB] peer 168::1 connect-interface gigabitethernet 3/1/2
[DeviceB-bgp] address-family ipv6
[DeviceB-bgp-ipv6] peer 168::1 enable
[DeviceB-bgp-ipv6] peer 168::1 route-policy qppb import
[DeviceB-bgp-ipv6] quit
[DeviceB-bgp] quit
# Configure a routing policy.
[DeviceB] route-policy qppb permit node 0
[DeviceB-route-policy-qppb-0] apply ip-precedence 4
[DeviceB-route-policy-qppb-0] quit
# Enable QPPB on GigabitEthernet 3/1/1.
[DeviceB] interface gigabitethernet 3/1/1
[DeviceB-GigabitEthernet3/1/1] bgp-policy destination ip-prec-map
# Configure a QoS policy.
[DeviceB] traffic classifier qppb
[DeviceB-classifier-qppb] if-match ip-precedence 4
[DeviceB-classifier-qppb] quit
[DeviceB] traffic behavior qppb
[DeviceB-behavior-qppb] car cir 512000 red discard
[DeviceB-behavior-qppb] quit
[DeviceB] qos policy qppb
[DeviceB-qospolicy-qppb] classifier qppb behavior qppb mode qppb-manipulation
[DeviceB-qospolicy-qppb] quit
# Apply the QoS policy to the incoming traffic of GigabitEthernet 3/1/1.
[DeviceB] interface gigabitethernet 3/1/1
[DeviceB-GigabitEthernet3/1/1] qos apply policy qppb inbound
[DeviceB-GigabitEthernet3/1/1] quit
Verifying the configuration
# Verify that the related routes on Device A take effect.
[DeviceA] display ipv6 routing-table
Destinations : 6 Routes : 6
Destination: ::1/128 Protocol : Direct
NextHop : ::1 Preference: 0
Interface : InLoop0 Cost : 0
Destination: 1::/64 Protocol : Direct
NextHop : :: Preference: 0
Interface : GE3/1/1 Cost : 0
Destination: 1::1/128 Protocol : Direct
NextHop : ::1 Preference: 0
Interface : InLoop0 Cost : 0
Destination: 168::/64 Protocol : Direct
NextHop : :: Preference: 0
Interface : GE3/1/2 Cost : 0
Destination: 168::1/128 Protocol : Direct
NextHop : ::1 Preference: 0
Interface : InLoop0 Cost : 0
Destination: FE80::/10 Protocol : Direct
NextHop : :: Preference: 0
Interface : NULL0 Cost : 0
# Verify that the related routes on Device B take effect.
[DeviceB] display ipv6 routing-table
Destinations : 8 Routes : 8
Destination: ::1/128 Protocol : Direct
NextHop : ::1 Preference: 0
Interface : InLoop0 Cost : 0
Destination: 1::/64 Protocol : BGP4+
NextHop : 168::1 Preference: 255
Interface : GE3/1/2 Cost : 0
Destination: 2::/64 Protocol : Direct
NextHop : :: Preference: 0
Interface : GE3/1/1 Cost : 0
Destination: 2::1/128 Protocol : Direct
NextHop : ::1 Preference: 0
Interface : InLoop0 Cost : 0
Destination: 2::2/128 Protocol : Direct
NextHop : ::1 Preference: 0
Interface : InLoop0 Cost : 0
Destination: 168::/64 Protocol : Direct
NextHop : :: Preference: 0
Interface : GE3/1/2 Cost : 0
Destination: 168::2/128 Protocol : Direct
NextHop : ::1 Preference: 0
Interface : InLoop0 Cost : 0
Destination: FE80::/10 Protocol : Direct
NextHop : :: Preference: 0
Interface : NULL0 Cost : 0
# Display the configuration and statistics for the QoS policy applied to GigabitEthernet 3/1/1 on Device C.
[DeviceC] display qos policy interface gigabitethernet 3/1/1
Interface: GigabitEthernet3/1/1
Direction: Inbound
Policy: qppb
Classifier: default-class
Mode: qppb-manipulation
Matched : 0 (Packets) 0 (Bytes)
5-minute statistics:
Forwarded: 0/0 (pps/bps)
Dropped : 0/0 (pps/bps)
Operator: AND
Rule(s) :
If-match any
Behavior: be
-none-
Classifier: qppb
Mode: qppb-manipulation
Matched : 0 (Packets) 0 (Bytes)
5-minute statistics:
Forwarded: 0/0 (pps/bps)
Dropped : 0/0 (pps/bps)
Operator: AND
Rule(s) :
If-match ip-precedence 4
Behavior: qppb
Committed Access Rate:
CIR 512000 (kbps), CBS 32000000 (Bytes), EBS 0 (Bytes)
Green action : pass
Yellow action : pass
Red action : discard
Green packets : 0 (Bytes) 0 (bps)
Yellow packets: 0 (Bytes) 0 (bps)
Red packets : 0 (Bytes) 0 (bps)
Appendixes
Appendix A Acronyms
Table 4 Appendix A Acronyms
|
Acronym |
Full spelling |
|
AF |
Assured Forwarding |
|
BE |
Best Effort |
|
BQ |
Bandwidth Queuing |
|
CAR |
Committed Access Rate |
|
CBS |
Committed Burst Size |
|
CBQ |
Class Based Queuing |
|
CE |
Congestion Experienced |
|
CIR |
Committed Information Rate |
|
DiffServ |
Differentiated Service |
|
DSCP |
Differentiated Services Code Point |
|
EBS |
Excess Burst Size |
|
ECN |
Explicit Congestion Notification |
|
EF |
Expedited Forwarding |
|
FIFO |
First in First out |
|
FQ |
Fair Queuing |
|
GTS |
Generic Traffic Shaping |
|
IntServ |
Integrated Service |
|
ISP |
Internet Service Provider |
|
LLQ |
Low Latency Queuing |
|
LSP |
Label Switched Path |
|
MPLS |
Multiprotocol Label Switching |
|
PE |
Provider Edge |
|
PHB |
Per Hop Behavior |
|
PIR |
Peak Information Rate |
|
PQ |
Priority Queuing |
|
QoS |
Quality of Service |
|
QPPB |
QoS Policy Propagation Through the Border Gateway Protocol |
|
RED |
Random Early Detection |
|
RSVP |
Resource Reservation Protocol |
|
RTP |
Real-Time Transport Protocol |
|
SP |
Strict Priority |
|
ToS |
Type of Service |
|
VoIP |
Voice over IP |
|
VPN |
Virtual Private Network |
|
WFQ |
Weighted Fair Queuing |
|
WRED |
Weighted Random Early Detection |
|
WRR |
Weighted Round Robin |
Appendix B Default priority maps
Uncolored priority maps
For the default dot1p-dot1p, dot1p-exp, dscp-dscp, exp-lp, exp-dot1p, and exp-exp priority maps, an input value yields a target value equal to it.
Table 5 Default dot1p-lp, dot1p-dp, and dot1p-dscp priority maps
|
Input priority value |
dot1p-lp map |
dot1p-dp map |
dot1p-dscp map |
|
dot1p |
lp |
dp |
dscp |
|
0 |
2 |
0 |
0 |
|
1 |
0 |
0 |
8 |
|
2 |
1 |
0 |
16 |
|
3 |
3 |
0 |
24 |
|
4 |
4 |
0 |
32 |
|
5 |
5 |
0 |
40 |
|
6 |
6 |
0 |
48 |
|
7 |
7 |
0 |
56 |
Table 6 Default dscp-lp, dscp-dp, dscp-dot1p, and dscp-exp priority maps
|
Input priority value |
dscp-lp map |
dscp-dp map |
dscp-dot1p map |
dscp-exp map |
|
dscp |
lp |
dp |
dot1p |
exp |
|
0 to 7 |
0 |
0 |
0 |
0 |
|
8 to 15 |
1 |
0 |
1 |
1 |
|
16 to 23 |
2 |
0 |
2 |
2 |
|
24 to 31 |
3 |
0 |
3 |
3 |
|
32 to 39 |
4 |
0 |
4 |
4 |
|
40 to 47 |
5 |
0 |
5 |
5 |
|
48 to 55 |
6 |
0 |
6 |
6 |
|
56 to 63 |
7 |
0 |
7 |
7 |
Table 7 Default exp-dscp and exp-dp priority maps
|
Input priority value |
exp-dscp map |
exp-dp map |
|
EXP value |
dscp |
dp |
|
0 |
0 |
0 |
|
1 |
8 |
0 |
|
2 |
16 |
0 |
|
3 |
24 |
0 |
|
4 |
32 |
0 |
|
5 |
40 |
0 |
|
6 |
48 |
0 |
|
7 |
56 |
0 |
Colored priority maps
An input value yields a target value equal to it for the following default colored priority maps for green/yellow/red packets:
· dot1p-dot1p.
· dot1p-exp.
· dscp-dscp.
· exp-lp.
· exp-dot1p.
· exp-exp.
· lp-lp.
· lp-exp.
Table 8 Default dscp-dot1p, dscp-dp, dscp-exp, and dscp-lp priority maps for green packets
|
Input priority value |
dscp-dot1p map |
dscp-dp map |
dscp-exp map |
dscp-lp map |
|
DSCP of green packets |
dot1p |
dp |
exp |
lp |
|
0 to 7 |
0 |
0 |
0 |
0 |
|
8 to 15 |
1 |
0 |
1 |
1 |
|
16 to 23 |
2 |
0 |
2 |
2 |
|
24 to 31 |
3 |
0 |
3 |
3 |
|
32 to 39 |
4 |
0 |
4 |
4 |
|
40 to 47 |
5 |
0 |
5 |
5 |
|
48 to 55 |
6 |
0 |
6 |
6 |
|
56 to 63 |
7 |
0 |
7 |
7 |
Table 9 Default dscp-dot1p, dscp-dp, dscp-exp, and dscp-lp priority maps for yellow packets
|
Input priority value |
dscp-dot1p map |
dscp-dp map |
dscp-exp map |
dscp-lp map |
|
DSCP of yellow packets |
dot1p |
dp |
exp |
lp |
|
0 to 7 |
0 |
1 |
0 |
0 |
|
8 to 15 |
1 |
1 |
1 |
1 |
|
16 to 23 |
2 |
1 |
2 |
2 |
|
24 to 31 |
3 |
1 |
3 |
3 |
|
32 to 39 |
4 |
1 |
4 |
4 |
|
40 to 47 |
5 |
1 |
5 |
5 |
|
48 to 55 |
6 |
1 |
6 |
6 |
|
56 to 63 |
7 |
1 |
7 |
7 |
Table 10 Default dscp-dot1p, dscp-dp, dscp-exp, and dscp-lp priority maps for red packets
|
Input priority value |
dscp-dot1p map |
dscp-dp map |
dscp-exp map |
dscp-lp map |
|
DSCP of red packets |
dot1p |
dp |
exp |
lp |
|
0 to 7 |
0 |
2 |
0 |
0 |
|
8 to 15 |
1 |
2 |
1 |
1 |
|
16 to 23 |
2 |
2 |
2 |
2 |
|
24 to 31 |
3 |
2 |
3 |
3 |
|
32 to 39 |
4 |
2 |
4 |
4 |
|
40 to 47 |
5 |
2 |
5 |
5 |
|
48 to 55 |
6 |
2 |
6 |
6 |
|
56 to 63 |
7 |
2 |
7 |
7 |
Table 11 Default exp-dp and exp-dscp priority maps for green packets
|
Input priority value |
exp-dp map |
exp-dscp map |
|
EXP of green packets |
dp |
DSCP |
|
0 |
0 |
0 |
|
1 |
0 |
8 |
|
2 |
0 |
16 |
|
3 |
0 |
24 |
|
4 |
0 |
32 |
|
5 |
0 |
40 |
|
6 |
0 |
48 |
|
7 |
0 |
56 |
Table 12 Default exp-dp and exp-dscp priority maps for yellow packets
|
Input priority value |
exp-dp map |
exp-dscp map |
|
EXP of yellow packets |
dp |
DSCP |
|
0 |
1 |
0 |
|
1 |
1 |
8 |
|
2 |
1 |
16 |
|
3 |
1 |
24 |
|
4 |
1 |
32 |
|
5 |
1 |
40 |
|
6 |
1 |
48 |
|
7 |
1 |
56 |
Table 13 Default exp-dp and exp-dscp priority maps for red packets
|
Input priority value |
exp-dp map |
exp-dscp map |
|
EXP of red packets |
dp |
DSCP |
|
0 |
2 |
0 |
|
1 |
2 |
8 |
|
2 |
2 |
16 |
|
3 |
2 |
24 |
|
4 |
2 |
32 |
|
5 |
2 |
40 |
|
6 |
2 |
48 |
|
7 |
2 |
56 |
Appendix C Introduction to packet precedence
IP precedence and DSCP values
As shown in Figure 28, the ToS field in the IP header contains 8 bits. The first 3 bits (0 to 2) represent IP precedence from 0 to 7. According to RFC 2474, the ToS field is redefined as the differentiated services (DS) field. A DSCP value is represented by the first 6 bits (0 to 5) of the DS field and is in the range 0 to 63. The remaining 2 bits (6 and 7) are reserved.

Table 14 IP precedence
|
IP precedence (decimal) |
IP precedence (binary) |
Description |
|
0 |
000 |
Routine |
|
1 |
001 |
priority |
|
2 |
010 |
immediate |
|
3 |
011 |
flash |
|
4 |
100 |
flash-override |
|
5 |
101 |
critical |
|
6 |
110 |
internet |
|
7 |
111 |
network |
Table 15 DSCP values
|
DSCP value (decimal) |
DSCP value (binary) |
Description |
|
46 |
101110 |
ef |
|
10 |
001010 |
af11 |
|
12 |
001100 |
af12 |
|
14 |
001110 |
af13 |
|
18 |
010010 |
af21 |
|
20 |
010100 |
af22 |
|
22 |
010110 |
af23 |
|
26 |
011010 |
af31 |
|
28 |
011100 |
af32 |
|
30 |
011110 |
af33 |
|
34 |
100010 |
af41 |
|
36 |
100100 |
af42 |
|
38 |
100110 |
af43 |
|
8 |
001000 |
cs1 |
|
16 |
010000 |
cs2 |
|
24 |
011000 |
cs3 |
|
32 |
100000 |
cs4 |
|
40 |
101000 |
cs5 |
|
48 |
110000 |
cs6 |
|
56 |
111000 |
cs7 |
|
0 |
000000 |
be (default) |
802.1p priority
802.1p priority lies in the Layer 2 header. It applies to occasions where Layer 3 header analysis is not needed and QoS must be assured at Layer 2.
As shown in Figure 29, the 4-byte 802.1Q tag header contains the 2-byte tag protocol identifier (TPID) and the 2-byte tag control information (TCI). The value of the TPID is 0x8100. Figure 30 shows the format of the 802.1Q tag header. The Priority field in the 802.1Q tag header is called 802.1p priority, because its use is defined in IEEE 802.1p. Table 16 shows the values for 802.1p priority.
Figure 29 An Ethernet frame with an 802.1Q tag header
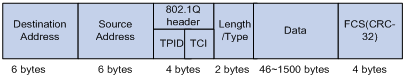

Table 16 Description on 802.1p priority
|
802.1p priority (decimal) |
802.1p priority (binary) |
Description |
|
0 |
000 |
best-effort |
|
1 |
001 |
background |
|
2 |
010 |
spare |
|
3 |
011 |
excellent-effort |
|
4 |
100 |
controlled-load |
|
5 |
101 |
video |
|
6 |
110 |
voice |
|
7 |
111 |
network-management |
EXP values
The EXP field is in MPLS labels for MPLS QoS purposes. As shown in Figure 31, the EXP field is 3-bit long and is in the range of 0 to 7.
Figure 31 MPLS label structure
![]()