- Table of Contents
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 02-IGMP snooping configuration | 318.50 KB |
IGMP snooping configuration task list
Configuring basic IGMP snooping features
Specifying an IGMP snooping version
Setting the maximum number of IGMP snooping forwarding entries
Setting the IGMP last member query interval
Configuring IGMP snooping port features
Setting aging timers for dynamic ports
Configuring a port as a simulated member host
Enabling fast-leave processing
Enabling inner VLAN ID-based forwarding
Configuring the IGMP snooping querier
Enabling the IGMP snooping querier
Configuring parameters for IGMP general queries and responses
Configuring source IP addresses for IGMP messages
Configuring IGMP snooping policies
Configuring a multicast group policy
Enabling multicast source port filtering
Enabling dropping unknown multicast data
Enabling IGMP report suppression
Setting the maximum number of multicast groups on a port
Enabling multicast group replacement
Displaying and maintaining IGMP snooping
IGMP snooping configuration examples
Group policy configuration example
Static port configuration example
IGMP snooping querier configuration example
Layer 2 multicast forwarding cannot function
Multicast group policy does not work
Configuring IGMP snooping
Overview
IGMP snooping runs on a Layer 2 switch as a multicast constraining mechanism to improve multicast forwarding efficiency. It creates Layer 2 multicast forwarding entries from IGMP packets that are exchanged between the hosts and the router.
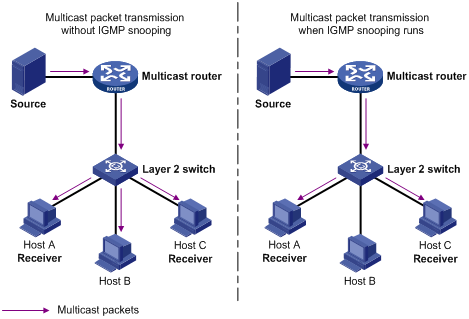
As shown in Figure 1, when IGMP snooping is not enabled, the Layer 2 switch floods multicast packets to all hosts. When IGMP snooping is enabled, the Layer 2 switch forwards multicast packets of known multicast groups to only the receivers.
Figure 1 Multicast packet transmission without and with IGMP snooping
Basic IGMP snooping concepts
IGMP snooping ports
As shown in Figure 2, IGMP snooping runs on Switch A and Switch B, and Host A and Host C are receivers in a multicast group.
Figure 2 IGMP snooping related ports
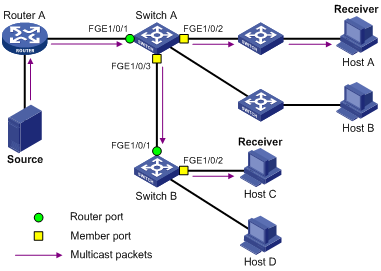
The following describes the ports involved in IGMP snooping:
· Router port—Layer 3 multicast device-side port. Layer 3 multicast devices include DRs and IGMP queriers. In Figure 2, FortyGigE 1/0/1 of Switch A and FortyGigE 1/0/1 of Switch B are the router ports. A switch records all its router ports in a router port list.
Do not confuse the "router port" in IGMP snooping with the "routed interface" commonly known as the "Layer 3 interface." The router port in IGMP snooping is a Layer 2 interface.
· Member port—Multicast receiver-side port. In Figure 2, FortyGigE 1/0/2 and FortyGigE 1/0/3 of Switch A and FortyGigE 1/0/2 of Switch B are the member ports. A switch records all its member ports in the IGMP snooping forwarding table.
Unless otherwise specified, router ports and member ports in this document include both static and dynamic router ports and member ports.
|
|
NOTE: When IGMP snooping is enabled, all ports that receive PIM hello messages or IGMP general queries with the source addresses other than 0.0.0.0 are considered dynamic router ports. For more information about PIM hello messages, see "Configuring PIM." |
Aging timers for dynamic ports in IGMP snooping
The following are aging timers for dynamical ports in IGMP snooping:
· Dynamic router port aging timer—The switch starts this timer for a port that receives an IGMP general query with the source address other than 0.0.0.0 or a PIM hello message. If the port does not receive either of these messages before the timer expires, the switch removes the port from its router port list.
· Dynamic member port aging timer—The switch starts this timer for a port that receives an IGMP report. If the port does not receive reports before the timer expires, the switch removes the port from the IGMP snooping forwarding entries.
|
|
NOTE: In IGMP snooping, only dynamic ports age out. Static ports never age out. |
How IGMP snooping works
The ports in this section are dynamic ports. For information about how to configure and remove static ports, see "Configuring static ports."
IGMP messages types include general query, IGMP report, and leave message. An IGMP snooping-enabled switch performs differently depending on the message.
General query
To check for the existence of multicast group members, the IGMP querier periodically sends IGMP general queries to all hosts and routers on the local subnet. All these hosts and routers are identified by the address 224.0.0.1.
After receiving an IGMP general query, the switch forwards the query to all ports in the VLAN except the port that received the query. The switch also performs one of the following operations:
· If the receiving port is a dynamic router port in the router port list, the switch restarts the aging timer for the port.
· If the receiving port does not exist in the router port list, the switch adds the port to the router port list. It also starts an aging timer for the port.
IGMP report
A host sends an IGMP report to the IGMP querier for the following purposes:
· Responds to queries if the host is a multicast group member.
· Applies for a multicast group membership.
After receiving an IGMP report from the host, the switch forwards it through all the router ports in the VLAN. The switch also resolves the address of the reported multicast group, and looks up the forwarding table for a matching entry.
· If no match is found, the switch creates a forwarding entry for the group with the receiving port as an outgoing interface. It also marks the receiving port as a dynamic member port and starts an aging timer for the port.
· If a match is found but the matching forwarding entry does not contain the receiving port, the switch adds the receiving port to the outgoing interface list. It also marks the receiving port as a dynamic member port and starts an aging timer for the port.
· If a match is found and the matching forwarding entry contains the receiving port, the switch restarts the aging timer for the port.
In an application with a group policy configured on an IGMP snooping-enabled switch, when a user requests a multicast program, the user's host initiates an IGMP report. After receiving this report, the switch resolves the multicast group address in the report and performs ACL filtering on the report. If the report passes ACL filtering, the switch creates an IGMP snooping forwarding entry for the multicast group with the receiving port as an outgoing interface. Otherwise, the switch drops this report, in which case the multicast data for the multicast group is not sent to this port, and the user cannot retrieve the program.
A switch does not forward an IGMP report through a non-router port because of the IGMP report suppression mechanism. For more information about the IGMP report suppression mechanism, see "Configuring IGMP."
Leave message
An IGMPv1 host silently leaves a multicast group. The switch is not notified of the leaving and cannot immediately update the status of the port that connects to the receiver host. The switch does not remove the port from the outgoing interface list in the associated forwarding entry until the aging time for the group expires. For a static member port, this mechanism does not take effect.
An IGMPv2 or IGMPv3 host sends an IGMP leave message to the multicast router when it leaves a multicast group.
When the switch receives an IGMP leave message on a dynamic member port, the switch first examines whether a forwarding entry matches the group address in the message.
· If no match is found, the switch discards the IGMP leave message.
· If a match is found but the receiving port is not an outgoing interface in the forwarding entry, the switch discards the IGMP leave message.
· If a match is found and the receiving port is not the only outgoing interface in the forwarding entry, the switch performs the following operations:
¡ Discards the IGMP leave message.
¡ Sends an IGMP group-specific query to identify whether the group has active receivers attached to the receiving port.
¡ Sets the aging timer for the receiving port to twice the IGMP last member query interval.
· If a match is found and the receiving port is the only outgoing interface in the forwarding entry, the switch performs the following operations:
¡ Forwards the IGMP leave message to all router ports in the VLAN.
¡ Sends an IGMP group-specific query to identify whether the group has active receivers attached to the receiving port.
¡ Sets the aging timer for the receiving port to twice the IGMP last member query interval.
After receiving the IGMP leave message on a port, the IGMP querier resolves the multicast group address in the message. Then the IGMP querier sends an IGMP group-specific query to the multicast group through the receiving port.
After receiving the IGMP group-specific query, the switch forwards it through all its router ports in the VLAN and all member ports of the multicast group. Then, it waits for the responding IGMP reports from the directly connected hosts. For the dynamic member port that received the leave message, the switch performs one of the following operations:
· If the port receives an IGMP report before the aging timer expires, the switch resets the aging timer for the port.
· If the port does not receive any IGMP reports when the aging timer expires, the switch removes the port from the forwarding entry for the multicast group.
Protocols and standards
RFC 4541, Considerations for Internet Group Management Protocol (IGMP) and Multicast Listener Discovery (MLD) Snooping Switches
IGMP snooping configuration task list
The IGMP snooping configurations made on Layer 2 aggregate interfaces do not interfere with the configurations made on member ports. In addition, the configurations made on Layer 2 aggregate interfaces do not take part in aggregation calculations. The configuration made on a member port of the aggregate group takes effect after the port leaves the aggregate group.
Configuring basic IGMP snooping features
Before you configure basic IGMP snooping features, complete the following tasks:
· Configure the corresponding VLANs.
· Determine the IGMP snooping version.
· Determine the maximum number of IGMP snooping forwarding entries.
· Determine the IGMP last member query interval.
Enabling IGMP snooping
When you enable IGMP snooping, follow these guidelines:
· You must enable IGMP snooping globally before you enable it for a VLAN.
· IGMP snooping for a VLAN takes effect only on the member ports in that VLAN.
· You can enable IGMP snooping for the specified VLANs in IGMP-snooping view or for a VLAN in VLAN view. For a VLAN, the configuration in VLAN view has the same priority as the configuration in IGMP-snooping view, and the most recent configuration takes effect.
Enabling IGMP snooping in IGMP-snooping view
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable IGMP snooping globally and enter IGMP-snooping view. |
igmp-snooping |
By default, IGMP snooping is disabled. |
|
3. Enable IGMP snooping for the specified VLANs. |
enable vlan vlan-list |
By default, IGMP snooping is disabled for the specified VLANs. |
Enabling IGMP snooping in VLAN view
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable IGMP snooping globally and enter IGMP-snooping view. |
igmp-snooping |
By default, IGMP snooping is disabled. |
|
3. Return to system view. |
quit |
N/A |
|
4. Enter VLAN view. |
vlan vlan-id |
N/A |
|
5. Enable IGMP snooping for the VLAN. |
igmp-snooping enable |
By default, IGMP snooping is disabled for the VLAN. |
Specifying an IGMP snooping version
Different IGMP snooping versions can process different versions of IGMP messages.
· IGMPv2 snooping can process IGMPv1 and IGMPv2 messages, but it floods IGMPv3 messages in the VLAN instead of processing them.
· IGMPv3 snooping can process IGMPv1, IGMPv2, and IGMPv3 messages.
If you change IGMPv3 snooping to IGMPv2 snooping, the device does the following:
· Clears all IGMP snooping forwarding entries that are dynamically added.
· Keeps static IGMPv3 snooping forwarding entries (*, G).
· Clears static IGMPv3 snooping forwarding entries (S, G), which will be restored when IGMP snooping is switched back to IGMPv3 snooping.
For more information about static IGMP snooping forwarding entries, see "Configuring static ports."
You can specify the version for the specified VLANs in IGMP-snooping view or for a VLAN in VLAN view. For a VLAN, the configuration in VLAN view has the same priority as the configuration in IGMP-snooping view, and the most recent configuration takes effect.
Specifying an IGMP snooping version in IGMP-snooping view
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable IGMP snooping globally and enter IGMP-snooping view. |
igmp-snooping |
N/A |
|
3. Specify the IGMP snooping version for the specified VLANs |
version version-number vlan vlan-list |
The default setting is IGMPv2 snooping. |
Specifying an IGMP snooping version in VLAN view
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VLAN view. |
vlan vlan-id |
N/A |
|
3. Specify the version of IGMP snooping. |
igmp-snooping version version-number |
The default setting is IGMPv2 snooping. |
Setting the maximum number of IGMP snooping forwarding entries
You can modify the maximum number of IGMP snooping forwarding entries, including dynamic entries and static entries. When the number of forwarding entries on the device reaches the upper limit, the device does not automatically remove any existing entries. As a best practice, manually remove some entries to allow new entries to be created.
To set the maximum number of IGMP snooping forwarding entries:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter IGMP-snooping view. |
igmp-snooping |
N/A |
|
3. Set the maximum number of IGMP snooping forwarding entries. |
entry-limit limit |
The default setting is 4294967295. |
Setting the IGMP last member query interval
A receiver host starts a report delay timer for a multicast group when it receives an IGMP group-specific query for the group. This timer is set to a random value in the range of 0 to the maximum response time advertised in the query. When the timer value decreases to 0, the host sends an IGMP report to the group.
The IGMP last member query interval defines the maximum response time advertised in IGMP group-specific queries. Set an appropriate value for the IGMP last member query interval to speed up hosts' responses to IGMP group-specific queries and avoid IGMP report traffic bursts.
Configuration restrictions and guidelines
When you set the IGMP last member query interval, follow these restrictions and guidelines:
· If the Layer 2 device receives a leave message from a port enabled with fast-leave processing, the device does not send an IGMP group-specific query to the port.
· You can set the IGMP last member query interval globally for all VLANs in IGMP-snooping view or for a VLAN in VLAN view. For a VLAN, the VLAN-specific configuration takes priority over the global configuration.
Setting the IGMP last member query interval globally
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter IGMP-snooping view. |
igmp-snooping |
N/A |
|
3. Set the IGMP last member query interval globally. |
last-member-query-interval interval |
The default setting is 1 second. |
Setting the IGMP last member query interval in a VLAN
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VLAN view. |
vlan vlan-id |
N/A |
|
3. Set the IGMP last member query interval in the VLAN. |
igmp-snooping last-member-query-interval interval |
The default setting is 1 second. |
Configuring IGMP snooping port features
Before you configure IGMP snooping port features, complete the following tasks:
· Enable IGMP snooping for the VLAN.
· Determine the aging timer for dynamic router ports.
· Determine the aging timer for dynamic member ports.
· Determine the addresses of the multicast group and multicast source.
Setting aging timers for dynamic ports
When you set aging timers for dynamic ports, follow these guidelines:
· If the memberships of multicast groups frequently change, you can set a relatively small value for the aging timer of the dynamic member ports. If the memberships of multicast groups rarely change, you can set a relatively large value.
· If a dynamic router port receives a PIMv2 hello message, the aging timer for the port is specified by the hello message. In this case, the router-aging-time command or the igmp-snooping router-aging-time command does not take effect on the port.
· IGMP group-specific queries originated by the Layer 2 device trigger the aging timer adjustment of dynamic member ports. If a dynamic member port receives such a query, its aging timer is set to twice the IGMP last member query interval. For more information about setting the IGMP last member query interval on the Layer 2 device, see "Setting the IGMP last member query interval."
· You can set the timers globally for all VLANs in IGMP-snooping view or for a VLAN in VLAN view. For a VLAN, the VLAN-specific configuration takes priority over the global configuration.
Setting the aging timers for dynamic ports globally
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter IGMP-snooping view. |
igmp-snooping |
N/A |
|
3. Set the aging timer for dynamic router ports globally. |
router-aging-time interval |
The default setting is 260 seconds. |
|
4. Set the aging timer for dynamic member ports globally. |
host-aging-time interval |
The default setting is 260 seconds. |
Setting the aging timers for dynamic ports in a VLAN
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VLAN view. |
vlan vlan-id |
N/A |
|
3. Set the aging timer for dynamic router ports in the VLAN. |
igmp-snooping router-aging-time interval |
The default setting is 260 seconds. |
|
4. Set the aging timer for dynamic member ports in the VLAN. |
igmp-snooping host-aging-time interval |
The default setting is 260 seconds. |
Configuring static ports
You can configure the following types of static ports:
· Static member port—When you configure a port as a static member port for a multicast group, all hosts attached to the port will receive multicast data for the group.
The static member port does not respond to IGMP queries. When you complete or cancel this configuration on a port, the port does not send an unsolicited IGMP report or leave message.
· Static router port—When you configure a port as a static router port for a multicast group, all multicast data for the group received on the port will be forwarded.
Static member ports and static router ports never age out. To remove such a port, use the undo igmp-snooping static-group or undo igmp-snooping static-router-port command.
To configure static ports:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter Layer 2 Ethernet interface view or Layer 2 aggregate interface view. |
interface interface-type interface-number |
N/A |
|
3. Configure the port as a static port. |
·
Configure the port as a static member port: ·
Configure the port as a static router port. |
By default, a port is not a static member port or a static router port. |
Configuring a port as a simulated member host
When a port is configured as a simulated member host, it is equivalent to an independent host in the following ways:
· It sends an unsolicited IGMP report when you complete the configuration.
· It responds to IGMP general queries with IGMP reports.
· It sends an IGMP leave message when you cancel the configuration.
The version of IGMP running on the simulated member host is the same as the version of IGMP snooping running on the port. The port ages out in the same way as a dynamic member port.
To configure a port as a simulated member host:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter Layer 2 Ethernet interface view or Layer 2 aggregate interface view. |
N/A |
|
|
3. Configure the port as a simulated member host. |
igmp-snooping host-join group-address [ source-ip source-address ] vlan vlan-id |
By default, the port is not a simulated member host. |
Enabling fast-leave processing
This feature enables the switch to immediately remove the port that receives a leave massage from the forwarding entry of the multicast group in the message.
When you enable the IGMP snooping fast-leave processing feature, follow these guidelines:
· Do not enable fast-leave processing on a port that has multiple receiver hosts in a VLAN. If fast-leave processing is enabled, the remaining receivers cannot receive multicast data for a group after a receiver leaves that group.
· You can enable fast-leave processing globally for all ports in IGMP-snooping view or for a port in interface view. For a port, the port-specific configuration takes priority over the global configuration.
Enabling IGMP snooping fast-leave processing globally
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter IGMP-snooping view. |
igmp-snooping |
N/A |
|
3. Enable fast-leave processing globally. |
fast-leave [ vlan vlan-list ] |
By default, fast-leave processing is disabled globally. |
Enabling IGMP snooping fast-leave processing on a port
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter Layer 2 Ethernet interface view or Layer 2 aggregate interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable IGMP snooping fast-leave processing on the port. |
igmp-snooping fast-leave [ vlan vlan-list ] |
By default, fast-leave processing is disabled on a port. |
Enabling inner VLAN ID-based forwarding
Use this feature to enable a port to create and maintain IGMP snooping entries based on the inner VLAN IDs of the received double-tagged IGMP packets.
To enable inner VLAN ID-based forwarding:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter Layer 2 Ethernet interface view or Layer 2 aggregate interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable inner VLAN ID-based forwarding. |
igmp-snooping cvid-forward |
By default, inner VLAN ID-based forwarding is disabled on a port. The port performs outer VLAN ID-based forwarding. |
Configuring the IGMP snooping querier
This section describes how to configure the IGMP snooping querier.
Configuration prerequisites
Before you configure the IGMP snooping querier, complete the following tasks:
· Enable IGMP snooping for the VLAN.
· Determine the IGMP general query interval.
· Determine the maximum response time for IGMP general queries.
Enabling the IGMP snooping querier
Configuration restrictions and guidelines
When you enable the IGMP snooping querier, follow these restrictions and guidelines:
· Do not enable the IGMP snooping querier on a multicast network that runs IGMP. The IGMP snooping querier does not take part in IGMP querier elections. However, it might affect IGMP querier elections if it sends IGMP general queries with a low source IP address. For more information about the IGMP querier election, see "Configuring IGMP."
· Assume that an RB acts as both the IGMP snooping querier and the AVF of a VLAN on a TRILL network. As a best practice, configure the appointed port of the VLAN as a static router port to ensure that IGMP snooping forwarding entries can be created. For more information about TRILL, RBs, AVFs, and appointed ports, see TRILL Configuration Guide.
Configuration procedure
To enable the IGMP snooping querier:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VLAN view. |
vlan vlan-id |
N/A |
|
3. Enable the IGMP snooping querier. |
igmp-snooping querier |
By default, the IGMP snooping querier is disabled. |
Configuring parameters for IGMP general queries and responses
|
|
CAUTION: To avoid mistakenly deleting multicast group members, make sure the IGMP general query interval is greater than the maximum response time for IGMP general queries. |
You can modify the IGMP general query interval based on the actual network condition.
A receiver host starts a timer for each multicast group that it has joined when it receives an IGMP general query. This timer is initialized to a random value in the range of 0 to the maximum response time advertised in the query. When the timer decreases to 0, the host sends an IGMP report to the multicast group.
Set an appropriate value for the maximum response time for IGMP general queries to speed up hosts' responses to IGMP general queries and avoid IGMP report traffic bursts.
You can configure the maximum response time for IGMP general queries globally for all VLANs in IGMP-snooping view or for a VLAN in VLAN view. For a VLAN, the VLAN-specific configuration takes priority over the global configuration.
Setting the maximum response time for IGMP general queries globally
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter IGMP-snooping view. |
igmp-snooping |
N/A |
|
3. Set the maximum response time for IGMP general queries. |
max-response-time interval |
The default setting is 10 seconds. |
Configuring parameters for IGMP general queries and responses in a VLAN
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VLAN view. |
vlan vlan-id |
N/A |
|
3. Set the IGMP general query interval in the VLAN. |
igmp-snooping query-interval interval |
The default setting is 125 seconds. |
|
4. Set the maximum response time for IGMP general queries in the VLAN. |
igmp-snooping max-response-time interval |
The default setting is 10 seconds. |
Configuring source IP addresses for IGMP messages
The IGMP snooping querier might send IGMP general queries with the source IP address 0.0.0.0. The port that receives such queries will not be maintained as a dynamic router port. This might cause the associated dynamic IGMP snooping forwarding entry unable to be correctly created at the data link layer and eventually cause multicast traffic forwarding failures.
To avoid this problem, you can configure a non-all-zero IP address as the source IP address of the IGMP queries on the IGMP snooping querier. This configuration might affect the IGMP querier election within the subnet.
You can also change the source IP address of IGMP reports or leave messages sent by a simulated member host or an IGMP snooping proxy.
To configure source IP addresses for IGMP messages in a VLAN:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VLAN view. |
vlan vlan-id |
N/A |
|
3. Configure the source IP address for IGMP general queries. |
igmp-snooping general-query source-ip ip-address |
By default, the source IP address of IGMP general queries is the IP address of the current VLAN interface. If the current VLAN interface does not have an IP address, the source IP address is 0.0.0.0. |
|
4. Configure the source IP address for IGMP group-specific queries. |
igmp-snooping special-query source-ip ip-address |
By default, the source IP address of IGMP group-specific queries is one of the following: · The source address of IGMP group-specific queries if the IGMP snooping querier has received IGMP general queries. · The IP address of the current VLAN interface if the IGMP snooping querier does not receive an IGMP general query. · 0.0.0.0 if the IGMP snooping querier does not receive an IGMP general query and the current VLAN interface does not have an IP address. |
|
5. Configure the source IP address for IGMP reports. |
By default, the source IP address of IGMP reports is the IP address of the current VLAN interface. If the current VLAN interface does not have an IP address, the source IP address is 0.0.0.0. |
|
|
6. Configure the source IP address for IGMP leave messages. |
By default, the source IP address of IGMP leave messages is the IP address of the current VLAN interface. If the current VLAN interface does not have an IP address, the source IP address is 0.0.0.0. |
Configuring IGMP snooping policies
Before you configure IGMP snooping policies, complete the following tasks:
· Enable IGMP snooping for the VLAN.
· Determine the ACL used as the multicast group policy.
· Determine the maximum number of multicast groups that a port can join.
Configuring a multicast group policy
This feature enables the switch to filter IGMP reports by using an ACL that specifies the multicast groups and the optional sources. Use this feature to control the multicast groups that receiver hosts can join.
When you configure a multicast group policy, follow these guidelines:
· This configuration takes effect only on the multicast groups that a port joins dynamically.
· You can configure a multicast group policy globally for all ports in IGMP-snooping view or for a port in interface view. For a port, the port-specific configuration takes priority over the global configuration.
Configuring a multicast group policy globally
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter IGMP-snooping view. |
igmp-snooping |
N/A |
|
3. Configure a multicast group policy globally. |
group-policy acl-number [ vlan vlan-list ] |
By default, no multicast group policies exist. Hosts can join any multicast groups. |
Configuring a multicast group policy on a port
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter Layer 2 Ethernet interface view or Layer 2 aggregate interface view. |
interface interface-type interface-number |
N/A |
|
3. Configure a multicast group policy on the port. |
igmp-snooping group-policy acl-number [ vlan vlan-list ] |
By default, no multicast group policies exist. Hosts attached to the port can join any multicast groups. |
Enabling multicast source port filtering
This feature enables the switch to discard all multicast data packets and to accept multicast protocol packets. You can enable this feature on ports that connect only to multicast receivers.
You can enable this feature for the specified ports in IGMP-snooping view or for a port in interface view. For a port, the configuration in interface view has the same priority as the configuration in IGMP-snooping view, and the most recent configuration takes effect.
Enabling multicast source port filtering globally
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter IGMP-snooping view. |
igmp-snooping |
N/A |
|
3. Enable multicast source port filtering. |
source-deny port interface-list |
By default, multicast source port filtering is disabled. |
Enabling multicast source port filtering on a port
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter Layer 2 Ethernet interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable multicast source port filtering on the port. |
igmp-snooping source-deny |
By default, multicast source port filtering is disabled on the port. |
Enabling dropping unknown multicast data
This feature enables the switch to drop all unknown multicast data. Unknown multicast data refers to multicast data for which no forwarding entries exist in the IGMP snooping forwarding table.
If you do not enable this feature, unknown multicast data is flooded in the VLAN to which the data belongs.
To enable dropping unknown multicast data for a VLAN:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VLAN view. |
vlan vlan-id |
N/A |
|
3. Enable dropping unknown multicast data for the VLAN. |
igmp-snooping drop-unknown |
By default, dropping unknown multicast data is disabled. Unknown multicast data is flooded. |
Enabling IGMP report suppression
The feature enables the switch to forward only the first IGMP report for a multicast group to its directly connected Layer 3 device. Other reports for the same group in the same query interval are discarded. Use this feature to reduce multicast traffic.
To enable IGMP report suppression:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter IGMP-snooping view. |
igmp-snooping |
N/A |
|
3. Enable IGMP report suppression. |
report-aggregation |
By default, IGMP report suppression is disabled. |
Setting the maximum number of multicast groups on a port
You can set the maximum number of multicast groups on a port to regulate the port traffic.
When you set the maximum number of multicast groups on a port, follow these guidelines:
· This configuration takes effect only on the multicast groups that a port joins dynamically.
· If the number of multicast groups on a port exceeds the limit, the system removes all the forwarding entries related to that port. The receiver hosts attached to that port can join multicast groups again before the number of multicast groups on the port reaches the limit.
To set the maximum number of multicast groups on a port:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter Layer 2 Ethernet interface view or Layer 2 aggregate interface view. |
interface interface-type interface-number |
N/A |
|
3. Set the maximum number of multicast groups on a port. |
igmp-snooping group-limit limit [ vlan vlan-list ] |
The default setting is 4294967295. |
Enabling multicast group replacement
This feature enables the switch to replace an existing group with a newly joined group when the number of groups exceeds the upper limit. This feature is typically used in channel switching applications. Without this feature, the Layer 2 device discards IGMP reports for new groups, and the user cannot change to a new channel.
Configuration restrictions and guidelines
When you enable multicast group replacement, follow these guidelines:
· This configuration takes effect only on the multicast groups that a port joins dynamically.
· You can enable this feature globally for all ports in IGMP-snooping view or for a port in interface view. For a port, the port-specific configuration takes priority over the global configuration.
Enabling multicast group replacement globally
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter IGMP-snooping view. |
igmp-snooping |
N/A |
|
3. Enable multicast group replacement globally. |
overflow-replace [ vlan vlan-list ] |
By default, multicast group replacement is disabled. |
Enabling multicast group replacement on a port
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter Layer 2 Ethernet interface view or Layer 2 aggregate interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable multicast group replacement on a port. |
igmp-snooping overflow-replace [ vlan vlan-list ] |
By default, multicast group replacement is disabled on a port. |
Displaying and maintaining IGMP snooping
Execute display commands in any view and reset commands in user view.
|
Command |
|
|
Display IGMP snooping status. |
display igmp-snooping [ global | vlan vlan-id ] |
|
Display dynamic IGMP snooping forwarding entries (in standalone mode). |
display igmp-snooping group [ group-address | source-address ] * [ vlan vlan-id ] [ verbose ] [ slot slot-number ] |
|
Display dynamic IGMP snooping forwarding entries (in IRF mode). |
display igmp-snooping group [ group-address | source-address ] * [ vlan vlan-id ] [ verbose ] [ chassis chassis-number slot slot-number ] |
|
Display static IGMP snooping forwarding entries (in standalone mode). |
display igmp-snooping static-group [ group-address | source-address ] * [ vlan vlan-id ] [ verbose ] [ slot slot-number ] |
|
Display static IGMP snooping forwarding entries (in IRF mode). |
display igmp-snooping static-group [ group-address | source-address ] * [ vlan vlan-id ] [ verbose ] [ chassis chassis-number slot slot-number ] |
|
Display dynamic router port information (in standalone mode). |
display igmp-snooping router-port [ vlan vlan-id ] [ slot slot-number ] |
|
Display dynamic router port information (in IRF mode). |
display igmp-snooping router-port [ vlan vlan-id ] [ chassis chassis-number slot slot-number ] |
|
Display static router port information (in standalone mode). |
display igmp-snooping static-router-port [ vlan vlan-id ] [ slot slot-number ] |
|
Display static router port information (in IRF mode). |
display igmp-snooping static-router-port [ vlan vlan-id ] [ chassis chassis-number slot slot-number ] |
|
Display statistics for the IGMP messages learned through IGMP snooping. |
display igmp-snooping statistics |
|
Display information about Layer 2 IP multicast groups (in standalone mode). |
display l2-multicast ip [ group group-address | source source-address ] * [ vlan vlan-id ] [ slot slot-number ] |
|
Display information about Layer 2 IP multicast groups (in IRF mode). |
display l2-multicast ip [ group group-address | source source-address ] * [ vlan vlan-id ] [ chassis chassis-number slot slot-number ] |
|
Display Layer 2 IP multicast group entries (in standalone mode). |
display l2-multicast ip forwarding [ group group-address | source source-address ] * [ vlan vlan-id ] [ slot slot-number ] |
|
Display Layer 2 IP multicast group entries (in IRF mode). |
display l2-multicast ip forwarding [ group group-address | source source-address ] * [ vlan vlan-id ] [ chassis chassis-number slot slot-number ] |
|
Display information about Layer 2 MAC multicast groups (in standalone mode). |
display l2-multicast mac [ mac-address ] [ vlan vlan-id ] [ slot slot-number ] |
|
Display information about Layer 2 MAC multicast groups (in IRF mode). |
display l2-multicast mac [ mac-address ] [ vlan vlan-id ] [ chassis chassis-number slot slot-number ] |
|
Display Layer 2 MAC multicast group entries (in standalone mode). |
display l2-multicast mac forwarding [ mac-address ] [ vlan vlan-id ] [ slot slot-number ] |
|
Display Layer 2 MAC multicast group entries (in IRF mode). |
display l2-multicast mac forwarding [ mac-address ] [ vlan vlan-id ] [ chassis chassis-number slot slot-number ] |
|
Clear dynamic IGMP snooping forwarding entries. |
reset igmp-snooping group { group-address [ source-address ] | all } [ vlan vlan-id ] |
|
Clear dynamic router port information. |
reset igmp-snooping router-port { all | vlan vlan-id } |
|
Clear statistics for the IGMP messages learned through IGMP snooping. |
reset igmp-snooping statistics |
IGMP snooping configuration examples
Group policy configuration example
Network requirements
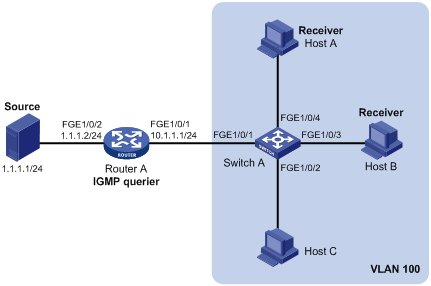
As shown in Figure 3, Router A runs IGMPv2 and acts as the IGMP querier. Switch A runs IGMPv2 snooping.
Configure a multicast group policy and simulate joining to meet the following requirements:
· Host A and Host B receive only the multicast data addressed to multicast group 224.1.1.1.
· Switch A drops unknown multicast data instead of flooding it in VLAN 100.
Configuration procedure
1. Assign an IP address and subnet mask to each interface according to Figure 3. (Details not shown.)
2. On Router A:
# Enable IP multicast routing.
<RouterA> system-view
[RouterA] multicast routing
[RouterA-mrib] quit
# Enable IGMP and PIM-DM on FortyGigE 1/0/1.
[RouterA] interface fortygige 1/0/1
[RouterA-FortyGigE1/0/1] igmp enable
[RouterA-FortyGigE1/0/1] pim dm
[RouterA-FortyGigE1/0/1] quit
# Enable PIM-DM on FortyGigE 1/0/2.
[RouterA] interface fortygige 1/0/2
[RouterA-FortyGigE1/0/2] pim dm
[RouterA-FortyGigE1/0/2] quit
3. Configure Switch A:
# Enable IGMP snooping globally.
<SwitchA> system-view
[SwitchA] igmp-snooping
[SwitchA-igmp-snooping] quit
# Create VLAN 100, and assign FortyGigE 1/0/1 through FortyGigE 1/0/4 to the VLAN.
[SwitchA] vlan 100
[SwitchA-vlan100] port fortygige 1/0/1 to fortygige 1/0/4
# Enable IGMP snooping, and enable dropping unknown multicast data for VLAN 100.
[SwitchA-vlan100] igmp-snooping enable
[SwitchA-vlan100] igmp-snooping drop-unknown
[SwitchA-vlan100] quit
# Configure a multicast group policy so that the hosts in VLAN 100 can join only multicast group 224.1.1.1.
[SwitchA] acl number 2001
[SwitchA-acl-basic-2001] rule permit source 224.1.1.1 0
[SwitchA-acl-basic-2001] quit
[SwitchA] igmp-snooping
[SwitchA-igmp-snooping] group-policy 2001 vlan 100
[SwitchA-igmp-snooping] quit
Verifying the configuration
# Send IGMP reports from Host A and Host B to join multicast groups 224.1.1.1 and 224.2.2.2. (Details not shown.)
# Display information about dynamic IGMP snooping forwarding entries in VLAN 100 on Switch A.
[SwitchA] display igmp-snooping group vlan 100
Total 1 entries.
VLAN 100: Total 1 entries.
(0.0.0.0, 224.1.1.1)
Host slots (1 in total):
1
Host ports (2 in total):
FGE1/0/3
FGE1/0/4
The output shows the following information:
· Host A and Host B have joined multicast group 224.1.1.1 through the member ports FortyGigE 1/0/4 and FortyGigE 1/0/3 on Switch A, respectively.
· Host A and Host B have failed to join multicast group 224.2.2.2. This means that the multicast group policy has taken effect.
Static port configuration example
Network requirements
As shown in Figure 4:
· Router A runs IGMPv2 and serves as the IGMP querier. Switch A, Switch B, and Switch C run IGMPv2 snooping.
· Host A and host C are permanent receivers of multicast group 224.1.1.1.
Configure static ports to meet the following requirements:
· To enhance the reliability of multicast traffic transmission, configure FortyGigE 1/0/3 and FortyGigE 1/0/5 on Switch C as static member ports for multicast group 224.1.1.1.
· Suppose the STP runs on the network. The forwarding path from Switch A to Switch C is blocked to avoid data loops. Multicast data flows to the receivers attached to Switch C only along the path of Switch A—Switch B—Switch C. When this path is blocked, a maximum of one IGMP query-response cycle must be completed before multicast data flows to the receivers along the path of Switch A—Switch C. In this case, the multicast delivery is interrupted. For more information about the STP, see Layer 2—LAN Switching Configuration Guide.
Configure FortyGigE 1/0/3 on Switch A as a static router port. Then, multicast data can flow to the receivers nearly uninterruptedly along the path of Switch A—Switch C when the path of Switch A—Switch B—Switch C is blocked.
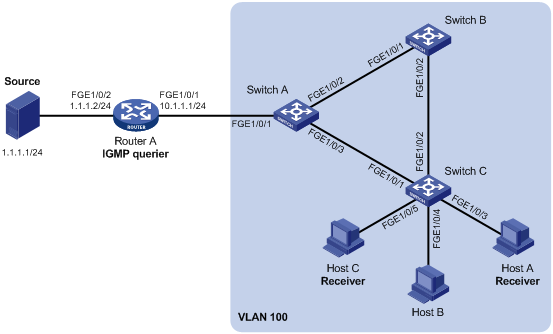
Configuration procedure
1. Assign an IP address and subnet mask to each interface according to Figure 4. (Details not shown.)
2. Configure Router A:
# Enable IP multicast routing.
<RouterA> system-view
[RouterA] multicast routing
[RouterA-mrib] quit
# Enable IGMP and PIM-DM on FortyGigE 1/0/1.
[RouterA] interface fortygige 1/0/1
[RouterA-FortyGigE1/0/1] igmp enable
[RouterA-FortyGigE1/0/1] pim dm
[RouterA-FortyGigE1/0/1] quit
# Enable PIM-DM on FortyGigE 1/0/2.
[RouterA] interface fortygige 1/0/2
[RouterA-FortyGigE1/0/2] pim dm
[RouterA-FortyGigE1/0/2] quit
3. Configure Switch A:
# Enable IGMP snooping globally.
<SwitchA> system-view
[SwitchA] igmp-snooping
[SwitchA-igmp-snooping] quit
# Create VLAN 100, assign FortyGigE 1/0/1 through FortyGigE 1/0/3 to the VLAN, and enable IGMP snooping for the VLAN.
[SwitchA] vlan 100
[SwitchA-vlan100] port fortygige 1/0/1 to fortygige 1/0/3
[SwitchA-vlan100] igmp-snooping enable
[SwitchA-vlan100] quit
# Configure FortyGigE 1/0/3 as a static router port.
[SwitchA] interface fortygige 1/0/3
[SwitchA-FortyGigE1/0/3] igmp-snooping static-router-port vlan 100
[SwitchA-FortyGigE1/0/3] quit
4. Configure Switch B:
# Enable IGMP snooping globally.
<SwitchB> system-view
[SwitchB] igmp-snooping
[SwitchB-igmp-snooping] quit
# Create VLAN 100, assign FortyGigE 1/0/1 and FortyGigE 1/0/2 to the VLAN, and enable IGMP snooping for the VLAN.
[SwitchB] vlan 100
[SwitchB-vlan100] port fortygige 1/0/1 fortygige 1/0/2
[SwitchB-vlan100] igmp-snooping enable
[SwitchB-vlan100] quit
5. Configure Switch C:
# Enable IGMP snooping globally.
<SwitchC> system-view
[SwitchC] igmp-snooping
[SwitchC-igmp-snooping] quit
# Create VLAN 100, assign FortyGigE 1/0/1 through FortyGigE 1/0/5 to the VLAN, and enable IGMP snooping for the VLAN.
[SwitchC] vlan 100
[SwitchC-vlan100] port fortygige 1/0/1 to fortygige 1/0/5
[SwitchC-vlan100] igmp-snooping enable
[SwitchC-vlan100] quit
# Configure FortyGigE 1/0/3 and FortyGigE 1/0/5 as static member ports for multicast group 224.1.1.1.
[SwitchC] interface fortygige 1/0/3
[SwitchC-FortyGigE1/0/3] igmp-snooping static-group 224.1.1.1 vlan 100
[SwitchC-FortyGigE1/0/3] quit
[SwitchC] interface fortygige 1/0/5
[SwitchC-FortyGigE1/0/5] igmp-snooping static-group 224.1.1.1 vlan 100
[SwitchC-FortyGigE1/0/5] quit
Verifying the configuration
# Display information about static router ports in VLAN 100 on Switch A.
[SwitchA] display igmp-snooping static-router-port vlan 100
VLAN 100:
Router slots (1 in total):
1
Router ports (1 in total):
1
FGE1/0/3
The output shows that FortyGigE 1/0/3 on Switch A has become a static router port.
# Display information about static IGMP snooping forwarding entries in VLAN 100 on Switch C.
[SwitchC] display igmp-snooping static-group vlan 100
Total 1 entries.
VLAN 100: Total 1 entries.
(0.0.0.0, 224.1.1.1)
Host slots (1 in total):
1
Host ports (2 in total):
FGE1/0/3
FGE1/0/5
The output shows that FortyGigE 1/0/3 and FortyGigE 1/0/5 on Switch C have become static member ports of multicast group 224.1.1.1.
IGMP snooping querier configuration example
Network requirements
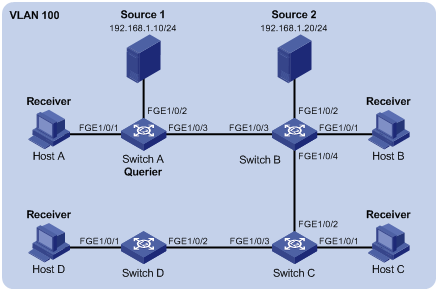
As shown in Figure 5:
· The network is a Layer 2-only network.
· Source 1 and Source 2 send multicast data to multicast groups 224.1.1.1 and 225.1.1.1, respectively.
· Host A and Host C are receivers of multicast group 224.1.1.1, and Host B and Host D are receivers of multicast group 225.1.1.1.
· All host receivers run IGMPv2, and all switches run IGMPv2 snooping. Switch A (which is close to the multicast sources) acts as the IGMP snooping querier.
Configure the switches to meet the following requirements:
· To prevent the switches from flooding unknown packets in VLAN 100, enable all the switches to drop unknown multicast packets.
· A switch does not mark a port that receives an IGMP query with source IP address 0.0.0.0 as a dynamic router port. To ensure the establishment of Layer 2 forwarding entries and multicast traffic forwarding, configure the source IP addresses of IGMP queries as non-zero IP addresses.
Configuration procedure
1. Configure Switch A:
# Enable IGMP snooping globally.
[SwitchA] igmp-snooping
[SwitchA-igmp-snooping] quit
# Create VLAN 100, and assign FortyGigE 1/0/1 through FortyGigE 1/0/3 to the VLAN.
[SwitchA-vlan100] port fortygige 1/0/1 to fortygige 1/0/3
# In VLAN 100, enable IGMP snooping, and enable dropping unknown multicast packets.
[SwitchA-vlan100] igmp-snooping enable
[SwitchA-vlan100] igmp-snooping drop-unknown
# In VLAN 100, configure Switch A as the IGMP snooping querier.
[SwitchA-vlan100] igmp-snooping querier
[SwitchA-vlan100] quit
# In VLAN 100, configure the source IP addresses of IGMP general queries and IGMP group-specific queries as 192.168.1.1.
[SwitchA-vlan100] igmp-snooping general-query source-ip 192.168.1.1
[SwitchA-vlan100] igmp-snooping special-query source-ip 192.168.1.1
[SwitchA-vlan100] quit
2. Configure Switch B:
# Enable IGMP snooping globally.
[SwitchB] igmp-snooping
[SwitchB-igmp-snooping] quit
# Create VLAN 100, and assign FortyGigE 1/0/1 through FortyGigE 1/0/4 to the VLAN.
[SwitchB-vlan100] port fortygige 1/0/1 to fortygige 1/0/4
# In VLAN 100, enable IGMP snooping, and enable dropping unknown multicast packets.
[SwitchB-vlan100] igmp-snooping enable
[SwitchB-vlan100] igmp-snooping drop-unknown
[SwitchB-vlan100] quit
3. Configure Switch C:
# Enable IGMP snooping globally.
[SwitchC] igmp-snooping
[SwitchC-igmp-snooping] quit
# Create VLAN 100, and assign FortyGigE 1/0/1 through FortyGigE 1/0/3 to the VLAN.
[SwitchC-vlan100] port fortygige 1/0/1 to fortygige 1/0/3
# In VLAN 100, enable IGMP snooping, and enable dropping unknown multicast packets.
[SwitchC-vlan100] igmp-snooping enable
[SwitchC-vlan100] igmp-snooping drop-unknown
[SwitchC-vlan100] quit
4. Configure Switch D:
# Enable IGMP snooping globally.
[SwitchD] igmp-snooping
[SwitchD-igmp-snooping] quit
# Create VLAN 100, and assign FortyGigE 1/0/1 and FortyGigE 1/0/2 to the VLAN.
[SwitchD-vlan100] port fortygige 1/0/1 to fortygige 1/0/2
# In VLAN 100, enable IGMP snooping, and enable dropping unknown multicast packets.
[SwitchD-vlan100] igmp-snooping enable
[SwitchD-vlan100] igmp-snooping drop-unknown
[SwitchD-vlan100] quit
Verifying the configuration
# Display statistics for IGMP messages learned through IGMP snooping on Switch B.
[SwitchB] display igmp-snooping statistics
Received IGMP general queries: 3
Received IGMPv1 reports: 0
Received IGMPv2 reports: 12
Received IGMP leaves: 0
Received IGMPv2 specific queries: 0
Sent IGMPv2 specific queries: 0
Received IGMPv3 reports: 0
Received IGMPv3 reports with right and wrong records: 0
Received IGMPv3 specific queries: 0
Received IGMPv3 specific sg queries: 0
Sent IGMPv3 specific queries: 0
Sent IGMPv3 specific sg queries: 0
Received error IGMP messages: 0
The output shows that all switches except Switch A can receive the IGMP general queries after Switch A acts as the IGMP snooping querier.
Troubleshooting IGMP snooping
Layer 2 multicast forwarding cannot function
Symptom
Layer 2 multicast forwarding cannot function on the switch.
Solution
To resolve the problem:
1. Use the display igmp-snooping command to display IGMP snooping status.
2. If IGMP snooping is not enabled, use the igmp-snooping command in system view to enable IGMP snooping globally. Then, use the igmp-snooping enable command in VLAN view to enable IGMP snooping for the VLAN.
3. If IGMP snooping is enabled globally but not enabled for the VLAN, use the igmp-snooping enable command in VLAN view to enable IGMP snooping for the VLAN.
4. If the problem persists, contact H3C Support.
Multicast group policy does not work
Symptom
Hosts can receive multicast data from multicast groups that are not permitted by the multicast group policy.
Solution
To resolve the problem:
1. Use the display acl command to verify that the configured ACL meets the multicast group policy requirements.
2. Use the display this command in IGMP-snooping view or in a corresponding interface view to verify that the correct multicast group policy has been applied. If the applied multicast group policy is not correct, use the group-policy or igmp-snooping group-policy command to apply the correct multicast group policy.
3. Use the display igmp-snooping command to verify that dropping unknown multicast data is enabled. If dropping unknown multicast data is not enabled, use the igmp-snooping drop-unknown command to enable dropping unknown multicast data.
4. If the problem persists, contact H3C Support.
