- Table of Contents
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 01-Text | 684.59 KB |
Setting the maximum lifetime for routes and labels in the RIB
Setting the maximum lifetime for routes in the FIB
Setting the maximum number of ECMP routes
Displaying and maintaining a routing table
Displaying and maintaining static routes
Basic static route configuration example
Configuring IPv6 static routing
Configuring an IPv6 static route
Displaying and maintaining IPv6 static routes
Basic IPv6 static route configuration example
Configuring an IPv6 default route
Feature and hardware compatibility
Controlling RIP reception and advertisement on interfaces
Configuring an additional routing metric
Configuring RIPv2 route summarization·
Disabling host route reception
Configuring received/redistributed route filtering
Configuring RIP route redistribution
Tuning and optimizing RIP networks
Enabling split horizon and poison reverse
Setting the maximum number of ECMP routes
Enabling zero field check on incoming RIPv1 messages
Enabling source IP address check on incoming RIP updates
Configuring RIPv2 message authentication
Setting the RIP triggered update interval
Configuring RIP network management
Configuring the RIP packet sending rate·
Setting the maximum length of RIP packets
Displaying and maintaining RIP
Configuring RIP route redistribution
Configuring an additional metric for a RIP interface
Feature and hardware compatibility
Configuring RIPng route control
Configuring an additional routing metric
Configuring RIPng route summarization
Configuring received/redistributed route filtering
Setting a preference for RIPng
Configuring RIPng route redistribution·
Tuning and optimizing the RIPng network
Configuring split horizon and poison reverse
Configuring zero field check on RIPng packets
Setting the maximum number of ECMP routes
Configuring the RIPng packet sending rate·
Setting the interval for sending triggered updates
Displaying and maintaining RIPng
Basic RIPng configuration example
RIPng route redistribution configuration example
RIPng GR configuration example
RIPng IPsec profile configuration example
Configuring basic IP routing
IP routing directs IP packet forwarding on routers based on a routing table. This chapter focuses on unicast routing protocols. For more information about multicast routing protocols, see IP Multicast Configuration Guide.
The term "router" in this document refers to access controllers and access controller modules.
Routing table
A RIB contains the global routing information and related information, including route recursion, route redistribution, and route extension information. The router selects optimal routes from the routing table and puts them into the FIB table. It uses the FIB table to forward packets.
Table 1 categorizes routes by different criteria.
|
Criterion |
Categories |
|
Destination |
· Network route—The destination is a network. The subnet mask is less than 32 bits. · Host route—The destination is a host. The subnet mask is 32 bits. |
|
Whether the destination is directly connected |
· Direct route—The destination is directly connected. · Indirect route—The destination is indirectly connected. |
|
Origin |
· Direct route—A direct route is discovered by the data link protocol on an interface, and is also called an interface route. · Static route—A static route is manually configured by an administrator. |
To view brief information about a routing table, use the display ip routing-table command.
<Sysname> display ip routing-table
Destinations : 19 Routes : 19
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
1.1.1.0/24 Direct 0 0 1.1.1.1 GE1/0/1
1.1.1.0/32 Direct 0 0 1.1.1.1 GE1/0/1
1.1.1.1/32 Direct 0 0 127.0.0.1 InLoop0
1.1.1.255/32 Direct 0 0 1.1.1.1 GE1/0/1
2.2.2.0/24 Static 60 0 12.2.2.2 Vlan1
80.1.1.0/24 Static 10 0 80.1.1.1 Vlan10
...
A route entry includes the following key items:
· Destination—IP address of the destination host or network.
· Mask—Mask length of the IP address.
· Proto—Protocol that installed the route.
· Pre—Preference of the route. Among routes to the same destination, the route with the highest preference is optimal.
· Cost—If multiple routes to a destination have the same preference, the one with the smallest cost is the optimal route.
· NextHop—Next hop.
· Interface—Output interface.
Route preference
By default, both static and direct routing have a preference. If they find multiple routes to the same destination, the router selects the route with the highest preference as the optimal route.
The preference of a direct route is always 0 and cannot be changed. You can configure a preference for each static route. The following table lists the route types and default preferences. The smaller the value, the higher the preference.
Table 2 Route types and default route preferences
|
Route type |
Preference |
|
Direct route |
0 |
|
Multicast static route |
1 |
|
Unicast static route |
60 |
|
Unknown (route from an untrusted source) |
256 |
Load sharing
A routing protocol might find multiple optimal equal-cost routes to the same destination. You can use these routes to implement equal-cost multi-path (ECMP) load sharing.
Static routing and IPv6 static routing support ECMP load sharing.
Route backup
Route backup can improve network availability. Among multiple routes to the same destination, the route with the highest priority is the primary route and others are secondary routes.
The router forwards matching packets through the primary route. When the primary route fails, the route with the highest preference among the secondary routes is selected to forward packets. When the primary route recovers, the router uses it to forward packets.
Route recursion
To use a static route that has an indirectly connected next hop, a router must perform route recursion to find the output interface to reach the next hop.
The RIB records and saves route recursion information, including brief information about related routes, recursive paths, and recursion depth.
Setting the maximum lifetime for routes and labels in the RIB
Perform this task to prevent routes of a certain protocol from being aged out due to slow protocol convergence resulting from a large number of route entries.
The configuration takes effect at the next protocol or RIB process switchover.
To set the maximum lifetime for routes and labels in the RIB (IPv4):
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIB view. |
rib |
N/A |
|
3. Create a RIB IPv4 address family and enter RIB IPv4 address family view. |
address-family ipv4 |
By default, no RIB IPv4 address family is created. |
|
4. Set the maximum lifetime for IPv4 routes and labels in the RIB. |
protocol protocol lifetime seconds |
By default, the maximum lifetime for routes and labels in the RIB is 480 seconds. |
To set the maximum route lifetime for routes and labels in the RIB (IPv6):
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIB view. |
rib |
N/A |
|
3. Create a RIB IPv6 address family and enter RIB IPv6 address family view. |
address-family ipv6 |
By default, no RIB IPv6 address family is created. |
|
4. Set the maximum lifetime for IPv6 routes and labels in the RIB. |
protocol protocol lifetime seconds |
By default, the maximum lifetime for routes and labels in the RIB is 480 seconds. |
Setting the maximum lifetime for routes in the FIB
FIB entries must be retained for some time after a protocol process switchover or RIB process switchover. Perform this task to meet such requirement.
To set the maximum lifetime for routes in the FIB (IPv4):
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIB view. |
rib |
N/A |
|
3. Create a RIB IPv4 address family and enter its view. |
address-family ipv4 |
By default, no RIB IPv4 address family is created. |
|
4. Set the maximum lifetime for IPv4 routes in the FIB. |
fib lifetime seconds |
By default, the maximum lifetime for routes in the FIB is 600 seconds. |
To set the maximum lifetime for routes in the FIB (IPv6):
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIB view. |
rib |
N/A |
|
3. Create a RIB IPv6 address family and enter its view. |
address-family ipv6 |
By default, no RIB IPv6 address family is created. |
|
4. Set the maximum lifetime for IPv6 routes in the FIB. |
fib lifetime seconds |
By default, the maximum lifetime for routes in the FIB is 600 seconds. |
Setting the maximum number of ECMP routes
The following matrix shows the feature and hardware compatibility:
|
Hardware series |
Model |
Setting the maximum number of ECMP routes compatibility |
|
WX1800H series |
WX1804H WX1810H WX1820H WX1840H |
Yes |
|
WX3800H series |
WX3820H WX3840H |
No |
|
WX5800H series |
WX5860H |
No |
This configuration takes effect at reboot. Make sure the reboot does not impact your network.
To set the maximum number of ECMP routes:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Set the maximum number of ECMP routes. |
max-ecmp-num number |
By default, the maximum number of ECMP routes is 4. |
Displaying and maintaining a routing table
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display routing table information. |
display ip routing-table [ verbose ] |
|
Display information about routes permitted by an IPv4 basic ACL. |
display ip routing-table acl acl-number [ verbose ] |
|
Display information about routes to a specific destination address. |
display ip routing-table ip-address [ mask | mask-length ] [ longer-match ] [ verbose ] |
|
Display information about routes to a range of destination addresses. |
display ip routing-table ip-address1 to ip-address2 [ verbose ] |
|
Display information about routes permitted by an IP prefix list. |
display ip routing-table prefix-list prefix-list-name [ verbose ] |
|
Display information about routes installed by a protocol. |
display ip routing-table protocol protocol [ inactive | verbose ] |
|
Display IPv4 route statistics. |
display ip routing-table statistics |
|
Display brief IPv4 routing table information. |
|
|
Display the maximum number of ECMP routes. |
display max-ecmp-num |
|
Display next hop information in the RIB. |
display rib nib [ self-originated ] [ nib-id ] [ verbose ] display rib nib protocol protocol [ verbose ] |
|
Display next hop information for direct routes. |
display route-direct nib [ nib-id ] [ verbose ] |
|
Clear IPv4 route statistics. |
reset ip routing-table statistics protocol { protocol | all } |
|
Display IPv6 routing table information. |
display ipv6 routing-table [ verbose ] |
|
Display information about routes to an IPv6 destination address. |
display ipv6 routing-table ipv6-address [ prefix-length ] [ longer-match ] [ verbose ] |
|
Display information about routes permitted by an IPv6 basic ACL. |
display ipv6 routing-table acl acl6-number [ verbose ] |
|
Display information about routes to a range of IPv6 destination addresses. |
display ipv6 routing-table ipv6-address1 to ipv6-address2 [ verbose ] |
|
Display information about routes permitted by an IPv6 prefix list. |
display ipv6 routing-table prefix-list prefix-list-name [ verbose ] |
|
Display information about routes installed by an IPv6 protocol. |
display ipv6 routing-table protocol protocol [ inactive | verbose ] |
|
Display IPv6 route statistics. |
display ipv6 routing-table statistics |
|
Display brief IPv6 routing table information. |
|
|
Display next hop information in the IPv6 RIB. |
display ipv6 rib nib [ self-originated ] [ nib-id ] [ verbose ] display ipv6 rib nib protocol protocol [ verbose ] |
|
Display next hop information for IPv6 direct routes. |
display ipv6 route-direct nib [ nib-id ] [ verbose ] |
|
Clear IPv6 route statistics. |
reset ipv6 routing-table statistics protocol { protocol | all } |
Configuring static routing
Static routes are manually configured. If a network's topology is simple, you only need to configure static routes for the network to work correctly.
Static routes cannot adapt to network topology changes. If a fault or a topological change occurs in the network, the network administrator must modify the static routes manually.
The term "router" in this document refers to access controllers and access controller modules.
Configuring a static route
Before you configure a static route, complete the following tasks:
· Configure the physical parameters for related interfaces.
· Configure the link-layer attributes for related interfaces.
· Configure the IP addresses for related interfaces.
To configure a static route:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. (Optional.) Create a static route group and enter static route group view. |
ip route-static-group group-name |
By default, no static route group is created. |
|
3. (Optional.) Configure a static route prefix. |
prefix dest-address { mask-length | mask } |
By default, no static route prefix is configured. |
|
4. (Optional.) Return to system view. |
quit |
N/A |
|
5. Configure a static route. |
ip route-static { dest-address { mask-length | mask } | group group-name } { interface-type interface-number [ next-hop-address ] | next-hop-address } [ permanent | track track-entry-number ] [ preference preference-value ] [ tag tag-value ] [ description description-text ] |
By default, no static route is configured. |
|
6. (Optional.) Configure the default preference for static routes. |
ip route-static default-preference default-preference-value |
The default setting is 60. |
|
7. (Optional.) Delete all static routes, including the default route. |
delete static-routes all |
To delete one static route, use the undo ip route-static command. |
Displaying and maintaining static routes
Execute display commands in any view.
|
Task |
Command |
|
Display static route information. |
display ip routing-table protocol static [ inactive | verbose ] |
|
Display static route next hop information. |
display route-static nib [ nib-id ] [ verbose ] |
|
Display static routing table information. |
display route-static routing-table [ ip-address { mask-length | mask } ] |
Basic static route configuration example
Network requirements
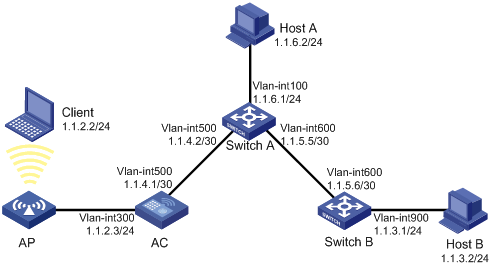
As shown in Figure 1, configure static routes on the switches and the AC for interconnections between each host and the AC.
Configuration procedure
1. Configure IP addresses for interfaces. (Details not shown.)
2. Configure static routes:
# Configure a default route on the AC.
<AC> system-view
[AC] ip route-static 0.0.0.0 0.0.0.0 1.1.4.2
# Configure two static routes on Switch A.
<SwitchA> system-view
[SwitchA] ip route-static 1.1.2.0 255.255.255.0 1.1.4.1
[SwitchA] ip route-static 1.1.3.0 255.255.255.0 1.1.5.6
# Configure a default route on Switch B.
<SwitchB> system-view
[SwitchB] ip route-static 0.0.0.0 0.0.0.0 1.1.5.5
3. Configure the default gateways of and the client, Host A, and Host B as 1.1.2.3, 1.1.6.1, and 1.1.3.1. (Details not shown.)
Verifying the configuration
# Display static routes on the AC.
[AC] display ip routing-table protocol static
Summary Count : 1
Static Routing table Status : <Active>
Summary Count : 1
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/0 Static 60 0 1.1.4.2 Vlan500
Static Routing table Status : <Inactive>
Summary Count : 0
# Display static routes on Switch A.
[SwitchA] display ip routing-table protocol static
Summary Count : 2
Static Routing table Status : <Active>
Summary Count : 2
Destination/Mask Proto Pre Cost NextHop Interface
1.1.2.0/24 Static 60 0 1.1.4.1 Vlan500
Static Routing table Status : <Inactive>
Summary Count : 0
# Use the ping command on Host A to test the reachability of the client (Windows XP runs on the two devices).
C:\Documents and Settings\Administrator>ping 1.1.2.2
Pinging 1.1.2.2 with 32 bytes of data:
Reply from 1.1.2.2: bytes=32 time=1ms TTL=126
Reply from 1.1.2.2: bytes=32 time=1ms TTL=126
Reply from 1.1.2.2: bytes=32 time=1ms TTL=126
Reply from 1.1.2.2: bytes=32 time=1ms TTL=126
Ping statistics for 1.1.2.2:
Packets: Sent = 4, Received = 4, Lost = 0 (0% loss),
Approximate round trip times in milli-seconds:
Minimum = 1ms, Maximum = 1ms, Average = 1ms
# Use the tracert command on Host A to test the reachability of the client.
C:\Documents and Settings\Administrator>tracert 1.1.2.2
Tracing route to 1.1.2.2 over a maximum of 30 hops
1 <1 ms <1 ms <1 ms 1.1.6.1
2 <1 ms <1 ms <1 ms 1.1.4.1
3 1 ms <1 ms <1 ms 1.1.2.2
Trace complete.
Configuring a default route
A default route is used to forward packets that do not match any specific routing entry in the routing table. Without a default route, packets that do not match any routing entries are discarded and an ICMP destination-unreachable packet is sent to the source.
A default route can be configured in either of the following ways:
· The network administrator can configure a default route with both destination and mask being 0.0.0.0. For more information, see "Configuring a static route."
· Some dynamic routing protocols, such RIP, can generate a default route. For example, an upstream router running RIP can generate a default route and advertise it to other routers. These routers install the default route with the next hop being the upstream router. For more information, see the respective chapters on these routing protocols in this configuration guide.
Configuring IPv6 static routing
Static routes are manually configured and cannot adapt to network topology changes. If a fault or a topological change occurs in the network, the network administrator must modify the static routes manually. IPv6 static routing works well in a simple IPv6 network.
The term "router" in this document refers to access controllers and access controller modules.
Configuring an IPv6 static route
Before you configure an IPv6 static route, complete the following tasks:
· Configure parameters for the related interfaces.
· Configure link layer attributes for the related interfaces.
· Make sure the neighboring nodes can reach each other.
To configure an IPv6 static route:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Configure an IPv6 static route. |
ipv6 route-static ipv6-address prefix-length { interface-type interface-number [ next-hop-address ] | next-hop-address } [ permanent ] [ preference preference-value ] [ tag tag-value ] [ description description-text ] |
By default, no IPv6 static route is configured. |
|
3. (Optional.) Set the default preference for IPv6 static routes. |
ipv6 route-static default-preference default-preference-value |
The default setting is 60. |
|
4. (Optional.) Delete all IPv6 static routes, including the default route. |
delete ipv6 static-routes all |
The undo ipv6 route-static command deletes one IPv6 static route. |
Displaying and maintaining IPv6 static routes
Execute display commands in any view.
|
Task |
Command |
|
Display IPv6 static route information. |
display ipv6 routing-table protocol static [ inactive | verbose ] |
|
Display IPv6 static route next hop information. |
display ipv6 route-static nib [ nib-id ] [ verbose ] |
|
Display IPv6 static routing table information. |
display ipv6 route-static routing-table [ ipv6-address prefix-length ] |
Basic IPv6 static route configuration example
Network requirements
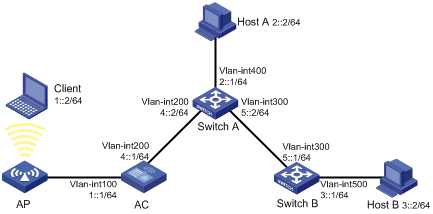
As shown in Figure 2, configure IPv6 static routes so that hosts can reach the AC.
Configuration procedure
1. Configure the IPv6 addresses for all VLAN interfaces. (Details not shown.)
2. Configure IPv6 static routes:
# Configure a default IPv6 static route on the AC.
<AC> system-view
[AC] ipv6 route-static :: 0 4::2
# Configure two IPv6 static routes on Switch A.
<SwitchA> system-view
[SwitchA] ipv6 route-static 1:: 64 4::1
[SwitchA] ipv6 route-static 3:: 64 5::1
# Configure a default IPv6 static route on Switch B.
<SwitchB> system-view
[SwitchB] ipv6 route-static :: 0 5::2
3. Configure the IPv6 addresses for all the hosts, and configure the default gateways of Client, Host A, and Host B as 1::1, 2::1, and 3::1, respectively.
Verifying the configuration
# Display the IPv6 static route information on the AC.
[AC] display ipv6 routing-table protocol static
Summary Count : 1
Static Routing table Status : <Active>
Summary Count : 1
Destination: :: Protocol : Static
NextHop : 4::2 Preference: 60
Interface : Vlan-interface200 Cost : 0
Static Routing table Status : <Inactive>
Summary Count : 0
# Display the IPv6 static route information on Switch A.
[SwitchA] display ipv6 routing-table protocol static
Summary Count : 2
Static Routing table Status : <Active>
Summary Count : 2
Destination: 1::/64 Protocol : Static
NextHop : 4::1 Preference: 60
Interface : Vlan-interface200 Cost : 0
Destination: 3::/64 Protocol : Static
NextHop : 5::1 Preference: 60
Interface : Vlan-interface300 Cost : 0
Static Routing table Status : <Inactive>
Summary Count : 0
# Use the ping command to test the reachability.
[AC] ping ipv6 3::1
Ping6(56 data bytes) 4::1 --> 3::1, press CTRL_C to break
56 bytes from 3::1, icmp_seq=0 hlim=62 time=0.700 ms
56 bytes from 3::1, icmp_seq=1 hlim=62 time=0.351 ms
56 bytes from 3::1, icmp_seq=2 hlim=62 time=0.338 ms
56 bytes from 3::1, icmp_seq=3 hlim=62 time=0.373 ms
56 bytes from 3::1, icmp_seq=4 hlim=62 time=0.316 ms
--- Ping6 statistics for 3::1 ---
5 packets transmitted, 5 packets received, 0.0% packet loss
round-trip min/avg/max/std-dev = 0.316/0.416/0.700/0.143 ms
Configuring an IPv6 default route
A default IPv6 route is used to forward packets that match no entry in the routing table.
A default IPv6 route can be configured in either of the following ways:
· The network administrator can configure a default route with a destination prefix of ::/0. For more information, see "Configuring an IPv6 static route."
· Some dynamic routing protocols, such as RIPng, can generate a default IPv6 route. For example, an upstream router running RIPng can generate a default IPv6 route and advertise it to other routers. These routers install the default IPv6 route with the next hop being the upstream router. For more information, see the respective chapters on those routing protocols in this configuration guide.
Configuring RIP
Overview
Routing Information Protocol (RIP) is a distance-vector IGP suited to small-sized networks. It employs UDP to exchange route information through port 520.
RIP uses a hop count to measure the distance to a destination. The hop count from a router to a directly connected network is 0. The hop count from a router to a directly connected router is 1. To limit convergence time, RIP restricts the value range of the metric from 0 to 15. A destination with a metric value of 16 (or greater) is considered unreachable. For this reason, RIP is not suitable for large-sized networks.
RIP route entries
RIP stores routing entries in a database. Each routing entry contains the following elements:
· Destination address—IP address of a destination host or a network.
· Next hop—IP address of the next hop.
· Egress interface—Egress interface of the route.
· Metric—Cost from the local router to the destination.
· Route time—Time elapsed since the last update. The time is reset to 0 when the routing entry is updated.
· Route tag—Used for route control. For more information, see "Configuring routing policies."
Routing loop prevention
RIP uses the following mechanisms to prevent routing loops:
· Counting to infinity—A destination with a metric value of 16 is considered unreachable. When a routing loop occurs, the metric value of a route will increment to 16 to avoid endless looping.
· Triggered updates—RIP immediately advertises triggered updates for topology changes to reduce the possibility of routing loops and to speed up convergence.
· Split horizon—Disables RIP from sending routes through the interface where the routes were learned to prevent routing loops and save bandwidth.
· Poison reverse—Enables RIP to set the metric of routes received from a neighbor to 16 and sends these routes back to the neighbor. The neighbor can delete such information from its routing table to prevent routing loops.
RIP operation
RIP works as follows:
1. RIP sends request messages to neighboring routers. Neighboring routers return response messages that contain their routing tables.
2. RIP uses the received responses to update the local routing table and sends triggered update messages to its neighbors. All RIP routers on the network do this to learn latest routing information.
3. RIP periodically sends the local routing table to its neighbors. After a RIP neighbor receives the message, it updates its routing table, selects optimal routes, and sends an update to other neighbors. RIP ages routes to keep only valid routes.
RIP versions
There are two RIP versions, RIPv1 and RIPv2.
RIPv1 is a classful routing protocol. It advertises messages only through broadcast. RIPv1 messages do not carry mask information, so RIPv1 can only recognize natural networks such as Class A, B, and C. For this reason, RIPv1 does not support discontiguous subnets.
RIPv2 is a classless routing protocol. It has the following advantages over RIPv1:
· Supports route tags to implement flexible route control through routing policies.
· Supports masks, route summarization, and CIDR.
· Supports designated next hops to select the best ones on broadcast networks.
· Supports multicasting route updates so only RIPv2 routers can receive these updates to reduce resource consumption.
· Supports plain text authentication and MD5 authentication to enhance security.
RIPv2 supports two transmission modes: broadcast and multicast. Multicast is the default mode using 224.0.0.9 as the multicast address. An interface operating in RIPv2 broadcast mode can also receive RIPv1 messages.
Protocols and standards
· RFC 1058, Routing Information Protocol
· RFC 1723, RIP Version 2 - Carrying Additional Information
· RFC 1721, RIP Version 2 Protocol Analysis
· RFC 1722, RIP Version 2 Protocol Applicability Statement
· RFC 1724, RIP Version 2 MIB Extension
· RFC 2082, RIPv2 MD5 Authentication
Feature and hardware compatibility
|
Hardware series |
Model |
Command compatibility |
|
WX1800H series |
WX1804H WX1810H WX1820H WX1840H |
Yes |
|
WX3800H series |
WX3820H WX3840H |
No |
|
WX5800H series |
WX5860H |
No |
RIP configuration task list
Configuring basic RIP
Before you configure basic RIP settings, complete the following tasks:
· Configure the link layer protocol.
· Configure IP addresses for interfaces to ensure IP connectivity between neighboring routers.
Enabling RIP
Follow these guidelines when you enable RIP:
· To enable multiple RIP processes on a router, you must specify an ID for each process. A RIP process ID has only local significance. Two RIP routers having different process IDs can also exchange RIP packets.
· If you configure RIP settings in interface view before enabling RIP, the settings do not take effect until RIP is enabled.
· If a physical interface is attached to multiple networks, you cannot advertise these networks in different RIP processes.
· You cannot enable multiple RIP processes on a physical interface.
· The rip enable command takes precedence over the network command.
Enabling RIP on a network
You can enable RIP on a network and specify a wildcard mask for the network. After that, only the interface attached to the network runs RIP.
To enable RIP on a network:
|
Command |
Remarks |
|
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable RIP and enter RIP view. |
rip [ process-id ] |
By default, RIP is disabled. |
|
3. Enable RIP on a network. |
network network-address [ wildcard-mask ] |
By default, RIP is disabled on a network. The network 0.0.0.0 command can enable RIP on all interfaces in a single process, but does not apply to multiple RIP processes. |
Enabling RIP on an interface
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable RIP and enter RIP view. |
rip [ process-id ] |
By default, RIP is disabled. |
|
3. Return to system view. |
quit |
N/A |
|
4. Enter interface view. |
interface interface-type interface-number |
N/A |
|
5. Enable RIP on the interface. |
rip process-id enable [ exclude-subip ] |
By default, RIP is disabled on an interface. |
Controlling RIP reception and advertisement on interfaces
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIP view. |
rip [ process-id ] |
N/A |
|
3. Disable an interface from sending RIP messages. |
silent-interface { interface-type interface-number | all } |
By default, all RIP-enabled interfaces can send RIP messages. The disabled interface can still receive RIP messages and respond to unicast requests containing unknown ports. |
|
4. Return to system view. |
quit |
N/A |
|
5. Enter interface view. |
interface interface-type interface-number |
N/A |
|
6. Enable an interface to receive RIP messages. |
rip input |
By default, a RIP-enabled interface can receive RIP messages. |
|
7. Enable an interface to send RIP messages. |
rip output |
By default, a RIP-enabled interface can send RIP messages. |
Configuring a RIP version
You can configure a global RIP version in RIP view or an interface-specific RIP version in interface view.
An interface preferentially uses the interface-specific RIP version. If no interface-specific version is specified, the interface uses the global RIP version. If neither a global nor interface-specific RIP version is configured, the interface sends RIPv1 broadcasts and can receive the following:
· RIPv1 broadcasts and unicasts.
· RIPv2 broadcasts, multicasts, and unicasts.
To configure a RIP version:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIP view. |
rip [ process-id ] |
N/A |
|
3. Specify a global RIP version. |
version { 1 | 2 } |
By default, no global version is specified. An interface sends RIPv1 broadcasts, and can receive RIPv1 broadcasts and unicasts, and RIPv2 broadcasts, multicasts, and unicasts. |
|
4. Return to system view. |
quit |
N/A |
|
5. Enter interface view. |
interface interface-type interface-number |
N/A |
|
6. Specify a RIP version for the interface. |
rip version { 1 | 2 [ broadcast | multicast ] } |
By default, no interface-specific RIP version is specified. The interface sends RIPv1 broadcasts, and can receive RIPv1 broadcasts and unicasts, and RIPv2 broadcasts, multicasts, and unicasts. |
Configuring RIP route control
Before you configure RIP route control, complete the following tasks:
· Configure IP addresses for interfaces to ensure IP connectivity between neighboring routers.
· Configure basic RIP.
Configuring an additional routing metric
An additional routing metric (hop count) can be added to the metric of an inbound or outbound RIP route.
An outbound additional metric is added to the metric of a sent route, and it does not change the route's metric in the routing table.
An inbound additional metric is added to the metric of a received route before the route is added into the routing table, and the route's metric is changed. If the sum of the additional metric and the original metric is greater than 16, the metric of the route is 16.
To configure additional routing metrics:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Specify an inbound additional routing metric. |
rip metricin value |
The default setting is 0. |
|
4. Specify an outbound additional routing metric. |
rip metricout value |
The default setting is 1. |
Configuring RIPv2 route summarization
Perform this task to summarize contiguous subnets into a summary network and sends the network to neighbors. The smallest metric among all summarized routes is used as the metric of the summary route.
Enabling RIPv2 automatic route summarization
Automatic summarization enables RIPv2 to generate a natural network for contiguous subnets. For example, suppose there are three subnet routes 10.1.1.0/24, 10.1.2.0/24, and 10.1.3.0/24. Automatic summarization automatically creates and advertises a summary route 10.0.0.0/8 instead of the more specific routes.
To enable RIPv2 automatic route summarization:
|
Command |
Remarks |
|
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIP view. |
rip [ process-id ] |
N/A |
|
3. (Optional.) Enable RIPv2 automatic route summarization. |
summary |
By default, RIPv2 automatic route summarization is enabled. If subnets in the routing table are not contiguous, disable automatic route summarization to advertise more specific routes. |
Advertising a summary route
Perform this task to manually configure a summary route.
For example, suppose contiguous subnets routes 10.1.1.0/24, 10.1.2.0/24, and 10.1.3.0/24 exist in the routing table. You can create a summary route 10.1.0.0/16 on GigabitEthernet 1/0/1 to advertise the summary route instead of the more specific routes.
To configure a summary route:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIP view. |
rip [ process-id ] |
N/A |
|
3. Disable RIPv2 automatic route summarization. |
undo summary |
By default, RIPv2 automatic route summarization is enabled. |
|
4. Return to system view. |
quit |
N/A |
|
5. Enter interface view. |
interface interface-type interface-number |
N/A |
|
6. Configure a summary route. |
rip summary-address ip-address { mask-length | mask } |
By default, no summary route is configured. |
Disabling host route reception
Perform this task to disable RIPv2 from receiving host routes from the same network to save network resources. This feature does not apply to RIPv1.
To disable RIP from receiving host routes:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIP view. |
rip [ process-id ] |
N/A |
|
3. Disable RIP from receiving host routes. |
undo host-route |
By default, RIP receives host routes. |
Advertising a default route
You can advertise a default route on all RIP interfaces in RIP view or on a specific RIP interface in interface view. The interface view setting takes precedence over the RIP view settings.
To disable an interface from advertising a default route, use the rip default-route no-originate command on the interface.
To configure RIP to advertise a default route:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIP view. |
rip [ process-id ] |
N/A |
|
3. Enable RIP to advertise a default route. |
default-route { only | originate } [ cost cost-value ] |
By default, RIP does not advertise a default route. |
|
4. Return to system view. |
quit |
N/A |
|
5. Enter interface view. |
interface interface-type interface-number |
N/A |
|
6. Configure the RIP interface to advertise a default route. |
rip default-route { { only | originate } [ cost cost-value ] | no-originate } |
By default, a RIP interface can advertise a default route if the RIP process is enabled to advertise a default route. |
|
|
NOTE: The router enabled to advertise a default route does not accept default routes from RIP neighbors. |
Configuring received/redistributed route filtering
Perform this task to filter received and redistributed routes by using a filtering policy.
To configure route filtering:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIP view. |
rip [ process-id ] |
N/A |
|
3. Configure the filtering of received routes. |
filter-policy { ipv4-acl-number | gateway prefix-list-name | prefix-list prefix-list-name [ gateway prefix-list-name ] } import [ interface-type interface-number ] |
By default, the filtering of received routes is not configured. This command filters received routes. Filtered routes are not installed into the routing table or advertised to neighbors. |
|
4. Configure the filtering of redistributed routes. |
filter-policy { ipv4-acl-number | prefix-list prefix-list-name } export [ interface-type interface-number | direct | rip [ process-id ] | static ] |
By default, the filtering of redistributed routes is not configured. This command filters redistributed routes, including routes redistributed with the import-route command. |
Setting a preference for RIP
If multiple IGPs find routes to the same destination, the route found by the IGP that has the highest priority is selected as the optimal route. Perform this task to assign a preference to RIP. The smaller the preference value, the higher the priority.
To set a preference for RIP:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIP view. |
rip [ process-id ] |
N/A |
|
3. Set a preference for RIP. |
The default setting is 100. |
Configuring RIP route redistribution
Perform this task to configure RIP to redistribute routes from other routing protocols, including static and direct routes.
To configure RIP route redistribution:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIP view. |
rip [ process-id ] |
N/A |
|
3. Enable RIP to redistribute external routes. |
import-route { direct | static } [ cost cost-value | tag tag ] * import-route rip [ process-id | all-processes ] [ allow-direct | cost cost-value | tag tag ] * |
By default, RIP does not redistribute external routes. This command can redistribute only active routes. To view active routes, use the display ip routing-table protocol command. |
|
4. (Optional.) Set a default cost for redistributed routes. |
default cost cost-value |
The default setting is 0. |
Tuning and optimizing RIP networks
Configuration prerequisites
Before you tune and optimize RIP networks, complete the following tasks:
· Configure IP addresses for interfaces to ensure IP connectivity between neighboring nodes.
· Configure basic RIP.
Setting RIP timers
You can change the RIP network convergence speed by adjusting the following RIP timers:
· Update timer—Specifies the interval between route updates.
· Timeout timer—Specifies the route aging time. If no update for a route is received within the aging time, the metric of the route is set to 16.
· Suppress timer—Specifies how long a RIP route stays in suppressed state. When the metric of a route is 16, the route enters the suppressed state. A suppressed route can be replaced by an updated route that is received from the same neighbor before the suppress timer expires and has a metric less than 16.
· Garbage-collect timer—Specifies the interval from when the metric of a route becomes 16 to when it is deleted from the routing table. RIP advertises the route with a metric of 16. If no update is announced for that route before the garbage-collect timer expires, the route is deleted from the routing table.
|
|
IMPORTANT: To avoid unnecessary traffic or route flapping, configure identical RIP timer settings on RIP routers. |
To set RIP timers:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIP view. |
rip [ process-id ] |
N/A |
|
3. Set RIP timers. |
timers { garbage-collect garbage-collect-value | suppress suppress-value | timeout timeout-value | update update-value } * |
By default: · The garbage-collect timer is 120 seconds. · The suppress timer is 120 seconds. · The timeout timer is 180 seconds. · The update timer is 30 seconds. |
Enabling split horizon and poison reverse
The split horizon and poison reverse functions can prevent routing loops.
If both split horizon and poison reverse are configured, only the poison reverse function takes effect.
Enabling split horizon
Split horizon disables RIP from sending routes through the interface where the routes were learned to prevent routing loops between adjacent routers.
To enable split horizon:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable split horizon. |
rip split-horizon |
By default, split horizon is enabled. |
Enabling poison reverse
Poison reverse allows RIP to send routes through the interface where the routes were learned. The metric of these routes is always set to 16 (unreachable) to avoid routing loops between neighbors.
To enable poison reverse:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable poison reverse. |
rip poison-reverse |
By default, poison reverse is disabled. |
Setting the maximum number of ECMP routes
Perform this task to implement load sharing over ECMP routes.
To set the maximum number of ECMP routes:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIP view. |
rip [ process-id ] |
N/A |
|
3. Set the maximum number of ECMP routes. |
maximum load-balancing number |
By default, the maximum number of RIP ECMP routes is 4. For more information about the max-ecmp-num command, see Layer 3—IP Routing Command Reference. |
Enabling zero field check on incoming RIPv1 messages
Some fields in the RIPv1 message must be set to zero. These fields are called "zero fields." You can enable zero field check on incoming RIPv1 messages. If a zero field of a message contains a non-zero value, RIP does not process the message. If you are certain that all messages are trustworthy, disable zero field check to save CPU resources.
This feature does not apply to RIPv2 packets, because they have no zero fields.
To enable zero field check on incoming RIPv1 messages:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIP view. |
rip [ process-id ] |
N/A |
|
3. Enable zero field check on incoming RIPv1 messages. |
checkzero |
The default setting is enabled. |
Enabling source IP address check on incoming RIP updates
Perform this task to enable source IP address check on incoming RIP updates.
Upon receiving a message on an Ethernet interface, RIP compares the source IP address of the message with the IP address of the interface. If they are not in the same network segment, RIP discards the message.
Upon receiving a message on a PPP interface, RIP checks whether the source address of the message is the IP address of the peer interface. If not, RIP discards the message.
To enable source IP address check on incoming RIP updates:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIP view. |
rip [ process-id ] |
N/A |
|
3. Enable source IP address check on incoming RIP messages. |
validate-source-address |
By default, this function is enabled. |
Configuring RIPv2 message authentication
Perform this task to enable authentication on RIPv2 messages. This feature does not apply to RIPv1 because RIPv1 does not support authentication. Although you can specify an authentication mode for RIPv1 in interface view, the configuration does not take effect.
RIPv2 supports two authentication modes: simple authentication and MD5 authentication.
To configure RIPv2 message authentication:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Configure RIPv2 authentication. |
rip authentication-mode { md5 { rfc2082 { cipher | plain } string key-id | rfc2453 { cipher | plain } string } | simple { cipher | plain } string } |
By default, RIPv2 authentication is not configured. |
Setting the RIP triggered update interval
Perform this task to avoid network overhead and reduce system resource consumption caused by frequent RIP triggered updates.
You can use the timer triggered command to set the maximum interval, minimum interval, and incremental interval for sending RIP triggered updates.
· For a stable network, the minimum-interval is used.
· If network changes become frequent, the triggered update sending interval is incremented by incremental-interval × 2n-2 for each triggered update until the maximum-interval is reached. The value n is the number of triggered update times.
To set the triggered update interval:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
N/A |
|
|
2. Enter RIP view. |
N/A |
|
|
3. Set the RIP triggered update interval. |
timer triggered maximum-interval [ minimum-interval [ incremental-interval ] ] |
By default: · The maximum interval is 5 seconds. · The minimum interval is 50 milliseconds. · The incremental interval is 200 milliseconds. |
Specifying a RIP neighbor
Typically RIP messages are sent in broadcast or multicast. To enable RIP on a link that does not support broadcast or multicast, you must manually specify RIP neighbors.
Follow these guidelines when you specify a RIP neighbor:
· Do not use the peer ip-address command when the neighbor is directly connected. Otherwise, the neighbor might receive both unicast and multicast (or broadcast) messages of the same routing information.
· If the specified neighbor is not directly connected, disable source address check on incoming updates.
To specify a RIP neighbor:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIP view. |
rip [ process-id ] |
N/A |
|
3. Specify a RIP neighbor. |
peer ip-address |
By default, RIP does not unicast updates to any peer. |
|
4. Disable source IP address check on inbound RIP updates |
undo validate-source-address |
By default, source IP address check on inbound RIP updates is enabled. |
Configuring RIP network management
You can use network management software to manage the RIP process to which MIB is bound.
To configure RIP network management:
|
Command |
Remarks |
|
|
1. Enter system view. |
system-view |
N/A |
|
2. Bind MIB to a RIP process. |
rip mib-binding process-id |
By default, MIB is bound to the RIP process with the smallest process ID. |
Configuring the RIP packet sending rate
Perform this task to set the interval for sending RIP packets and the maximum number of RIP packets that can be sent at each interval. This feature can avoid excessive RIP packets from affecting system performance and consuming too much bandwidth.
To configure the RIP packet sending rate:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIP view. |
rip [ process-id ] |
N/A |
|
3. Set the interval for sending RIP packets and the maximum number of RIP packets that can be sent at each interval. |
output-delay time count count |
By default, an interface sends up to three RIP packets every 20 milliseconds. |
|
4. Return to system view. |
quit |
N/A |
|
5. Enter interface view. |
N/A |
|
|
6. Set the interval for sending RIP packets and the maximum number of RIP packets that can be sent at each interval. |
By default, the interface uses the RIP packet sending rate configured for the RIP process that the interface runs. |
Setting the maximum length of RIP packets
|
|
NOTE: The supported maximum length of RIP packets varies by vendor. Use this feature with caution to avoid compatibility issues. |
The packet length of RIP packets determines how many routes can be carried in a RIP packet. Set the maximum length of RIP packets to make good use of link bandwidth.
When authentication is enabled, follow these guidelines to ensure packet forwarding:
· For simple authentication, the maximum length of RIP packets must be no less than 52 bytes.
· For MD5 authentication (with packet format defined in RFC 2453), the maximum length of RIP packets must be no less than 56 bytes.
· For MD5 authentication (with packet format defined in RFC 2082), the maximum length of RIP packets must be no less than 72 bytes.
To set the maximum length of RIP packets:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Set the maximum length of RIP packets. |
rip max-packet-length value |
By default, the maximum length of RIP packets is 512 bytes. |
Configuring RIP GR
GR ensures forwarding continuity when a routing protocol restarts.
Two routers are required to complete a GR process. The following are router roles in a GR process:
· GR restarter—Graceful restarting router. It must have GR capability.
· GR helper—A neighbor of the GR restarter. It helps the GR restarter to complete the GR process.
After RIP restarts on a router, the router must learn RIP routes again and update its FIB table, which causes network disconnections and route reconvergence.
With the GR feature, the restarting router (known as the GR restarter) can notify the event to its GR capable neighbors. GR capable neighbors (known as GR helpers) maintain their adjacencies with the router within a GR interval. During this process, the FIB table of the router does not change. After the restart, the router contacts its neighbors to retrieve its FIB.
By default, a RIP-enabled device acts as the GR helper. Perform this task on the GR restarter.
To configure GR on the GR restarter:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIP view. |
rip [ process-id ] |
N/A |
|
3. Enable GR for RIP. |
graceful-restart |
By default, RIP GR is disabled. |
|
4. (Optional.) Set the GR interval. |
By default, the GR interval is 60 seconds. |
Displaying and maintaining RIP
Execute display commands in any view and execute reset commands in user view.
|
Command |
|
|
Display RIP current status and configuration information. |
display rip [ process-id ] |
|
Display active routes in the RIP database. |
display rip process-id database [ ip-address { mask-length | mask } ] |
|
Display RIP GR information. |
|
|
Display RIP interface information. |
display rip process-id interface [ interface-type interface-number ] |
|
Display neighbor information for a RIP process. |
display rip process-id neighbor [ interface-type interface-number ] |
|
Display routing information for a RIP process. |
display rip process-id route [ ip-address { mask-length | mask } [ verbose ] | peer ip-address | statistics ] |
|
Reset a RIP process. |
reset rip process-id process |
|
Clear the statistics for a RIP process. |
reset rip process-id statistics |
RIP configuration examples
Configuring basic RIP
Network requirements
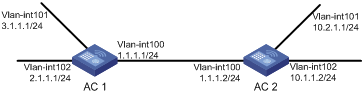
As shown in Figure 3, enable RIPv2 on all interfaces on AC 1 and AC 2. Configure AC 2 to not advertise route 10.2.1.0/24 to AC 1, and to accept only route 2.1.1.0/24 from AC 1.
Configuration procedure
1. Configure IP addresses for interfaces. (Details not shown.)
2. Configure basic RIP by using either of the following methods:
(Method 1) # Enable RIP on the specified networks on AC 1.
<AC1> system-view
[AC1] rip
[AC1-rip-1] network 1.0.0.0
[AC1-rip-1] network 2.0.0.0
[AC1-rip-1] network 3.0.0.0
[AC1-rip-1] quit
(Method 2) # Enable RIP on the specified interfaces on AC 2.
<AC2> system-view
[AC2] rip
[AC2-rip-1] quit
[AC2] interface vlan-interface 100
[AC2-Vlan-interface100] rip 1 enable
[AC2-Vlan-interface100] quit
[AC2] interface vlan-interface 101
[AC2-Vlan-interface101] rip 1 enable
[AC2-Vlan-interface101] quit
[AC2] interface vlan-interface 102
[AC2-Vlan-interface102] rip 1 enable
[AC2-Vlan-interface102] quit
# Display the RIP routing table of AC 1.
[AC1] display rip 1 route
Route Flags: R - RIP, T - TRIP
P - Permanent, A - Aging, S - Suppressed, G - Garbage-collect
D - Direct, O - Optimal, F - Flush to RIB
----------------------------------------------------------------------------
Peer 1.1.1.2 on Vlan-interface100
Destination/Mask Nexthop Cost Tag Flags Sec
10.0.0.0/8 1.1.1.2 1 0 RAOF 11
Local route
Destination/Mask Nexthop Cost Tag Flags Sec
1.1.1.0/24 0.0.0.0 0 0 RDOF -
2.1.1.0/24 0.0.0.0 0 0 RDOF -
3.1.1.0/24 0.0.0.0 0 0 RDOF -
The output shows that RIPv1 uses a natural mask.
3. Configure a RIP version:
# Configure RIPv2 on AC 1.
[AC1] rip
[AC1-rip-1] version 2
[AC1-rip-1] undo summary
[AC1-rip-1] quit
# Configure RIPv2 on AC 2.
[AC2] rip
[AC2-rip-1] version 2
[AC2-rip-1] undo summary
[AC2-rip-1] quit
# Display the RIP routing table on AC 1.
[AC1] display rip 1 route
Route Flags: R - RIP, T - TRIP
P - Permanent, A - Aging, S - Suppressed, G - Garbage-collect
D - Direct, O - Optimal, F - Flush to RIB
----------------------------------------------------------------------------
Peer 1.1.1.2 on Vlan-interface100
Destination/Mask Nexthop Cost Tag Flags Sec
10.0.0.0/8 1.1.1.2 1 0 RAOF 50
10.2.1.0/24 1.1.1.2 1 0 RAOF 16
10.1.1.0/24 1.1.1.2 1 0 RAOF 16
Local route
Destination/Mask Nexthop Cost Tag Flags Sec
1.1.1.0/24 0.0.0.0 0 0 RDOF -
2.1.1.0/24 0.0.0.0 0 0 RDOF -
3.1.1.0/24 0.0.0.0 0 0 RDOF -
The output shows that RIPv2 uses classless subnet masks.
|
|
NOTE: After RIPv2 is configured, RIPv1 routes might still exist in the routing table until they are aged out. |
# Display the RIP routing table on AC 2.
[AC2] display rip 1 route
Route Flags: R - RIP, T - TRIP
P - Permanent, A - Aging, S - Suppressed, G - Garbage-collect
D - Direct, O - Optimal, F - Flush to RIB
----------------------------------------------------------------------------
Peer 1.1.1.1 on Vlan-interface100
Destination/Mask Nexthop Cost Tag Flags Sec
2.1.1.0/24 1.1.1.1 1 0 RAOF 19
3.1.1.0/24 1.1.1.1 1 0 RAOF 19
Local route
Destination/Mask Nexthop Cost Tag Flags Sec
1.1.1.0/24 0.0.0.0 0 0 RDOF -
10.1.1.0/24 0.0.0.0 0 0 RDOF -
10.2.1.0/24 0.0.0.0 0 0 RDOF -
4. Configure route filtering:
# Reference IP prefix lists on AC 2 to filter received and redistributed routes.
[AC2] ip prefix-list aaa index 10 permit 2.1.1.0 24
[AC2] ip prefix-list bbb index 10 deny 10.2.1.0 24
[AC2] ip prefix-list bbb index 11 permit 0.0.0.0 0 less-equal 32
[AC2] rip 1
[AC2-rip-1] filter-policy prefix-list aaa import
[AC2-rip-1] filter-policy prefix-list bbb export
[AC2-rip-1] quit
# Display the RIP routing table on AC 1.
[AC1] display rip 100 route
Route Flags: R - RIP, T - TRIP
P - Permanent, A - Aging, S - Suppressed, G - Garbage-collect
----------------------------------------------------------------------------
Peer 1.1.1.2 on Vlan-interface100
Destination/Mask Nexthop Cost Tag Flags Sec
10.1.1.0/24 1.1.1.2 1 0 RAOF 19
Local route
Destination/Mask Nexthop Cost Tag Flags Sec
1.1.1.0/24 0.0.0.0 0 0 RDOF -
2.1.1.0/24 0.0.0.0 0 0 RDOF -
3.1.1.0/24 0.0.0.0 0 0 RDOF -
# Display the RIP routing table on AC 2.
[AC2] display rip 1 route
Route Flags: R - RIP, T - TRIP
P - Permanent, A - Aging, S - Suppressed, G - Garbage-collect
D - Direct, O - Optimal, F - Flush to RIB
----------------------------------------------------------------------------
Peer 1.1.1.1 on Vlan-interface100
Destination/Mask Nexthop Cost Tag Flags Sec
2.1.1.0/24 1.1.1.1 1 0 RAOF 19
Local route
Destination/Mask Nexthop Cost Tag Flags Sec
1.1.1.0/24 0.0.0.0 0 0 RDOF -
10.1.1.0/24 0.0.0.0 0 0 RDOF -
10.2.1.0/24 0.0.0.0 0 0 RDOF -
Configuring RIP route redistribution
Network requirements
As shown in Figure 4, AC 2 communicates with AC 1 through RIP 100 and with AC 3 through RIP 200.
Configure RIP 200 to redistribute direct routes and routes from RIP 100 on AC 2 so AC 3 can learn routes destined for 10.2.1.0/24 and 11.1.1.0/24. AC 1 cannot learn routes destined for 12.3.1.0/24 and 16.4.1.0/24.
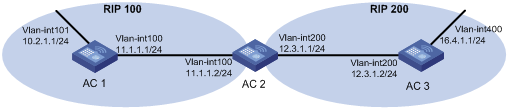
Configuration procedure
1. Configure IP addresses for interfaces. (Details not shown.)
2. Configure basic RIP:
# Enable RIP 100, and configure RIPv2 on AC 1.
<AC1> system-view
[AC1] rip 100
[AC1-rip-100] network 10.0.0.0
[AC1-rip-100] network 11.0.0.0
[AC1-rip-100] version 2
[AC1-rip-100] undo summary
[AC1-rip-100] quit
# Enable RIP 100 and RIP 200, and configure RIPv2 on AC 2.
<AC2> system-view
[AC2] rip 100
[AC2-rip-100] network 11.0.0.0
[AC2-rip-100] version 2
[AC2-rip-100] undo summary
[AC2-rip-100] quit
[AC2] rip 200
[AC2-rip-200] network 12.0.0.0
[AC2-rip-200] version 2
[AC2-rip-200] undo summary
[AC2-rip-200] quit
# Enable RIP 200, and configure RIPv2 on AC 3.
<AC3> system-view
[AC3] rip 200
[AC3-rip-200] network 12.0.0.0
[AC3-rip-200] network 16.0.0.0
[AC3-rip-200] version 2
[AC3-rip-200] undo summary
[AC3-rip-200] quit
# Display the IP routing table on AC 3.
[AC3] display ip routing-table
Destinations : 13 Routes : 13
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
12.3.1.0/24 Direct 0 0 12.3.1.2 Vlan200
12.3.1.0/32 Direct 0 0 12.3.1.2 Vlan200
12.3.1.2/32 Direct 0 0 127.0.0.1 InLoop0
12.3.1.255/32 Direct 0 0 12.3.1.2 Vlan200
16.4.1.0/24 Direct 0 0 16.4.1.1 Vlan400
16.4.1.0/32 Direct 0 0 16.4.1.1 Vlan400
16.4.1.1/32 Direct 0 0 127.0.0.1 InLoop0
16.4.1.255/32 Direct 0 0 16.4.1.1 Vlan400
127.0.0.0/8 Direct 0 0 127.0.0.1 InLoop0
127.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
127.0.0.1/32 Direct 0 0 127.0.0.1 InLoop0
127.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
3. Configure route redistribution:
# Configure RIP 200 to redistribute routes from RIP 100 and direct routes on AC 2.
[AC2] rip 200
[AC2-rip-200] import-route rip 100
[AC2-rip-200] import-route direct
[AC2-rip-200] quit
# Display the IP routing table on AC 3.
[AC3] display ip routing-table
Destinations : 15 Routes : 15
Destination/Mask Proto Pre Cost NextHop Interface
0.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
10.2.1.0/24 RIP 100 1 12.3.1.1 Vlan200
11.1.1.0/24 RIP 100 1 12.3.1.1 Vlan200
12.3.1.0/24 Direct 0 0 12.3.1.2 Vlan200
12.3.1.0/32 Direct 0 0 12.3.1.2 Vlan200
12.3.1.2/32 Direct 0 0 127.0.0.1 InLoop0
12.3.1.255/32 Direct 0 0 12.3.1.2 Vlan200
16.4.1.0/24 Direct 0 0 16.4.1.1 Vlan400
16.4.1.0/32 Direct 0 0 16.4.1.1 Vlan400
16.4.1.1/32 Direct 0 0 127.0.0.1 InLoop0
16.4.1.255/32 Direct 0 0 16.4.1.1 Vlan400
127.0.0.0/8 Direct 0 0 127.0.0.1 InLoop0
127.0.0.0/32 Direct 0 0 127.0.0.1 InLoop0
127.0.0.1/32 Direct 0 0 127.0.0.1 InLoop0
127.255.255.255/32 Direct 0 0 127.0.0.1 InLoop0
Configuring an additional metric for a RIP interface
Network requirements
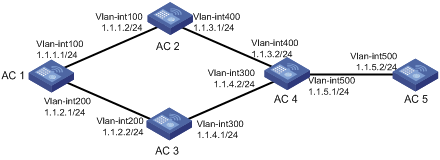
As shown in Figure 5, run RIPv2 on all the interfaces of AC 1, AC 2, AC 3, AC 4, and AC 5.
AC 1 has two links to AC 4. The link from AC 2 to AC 4 is more stable than that from AC 3 to AC 4. Configure an additional metric for RIP routes received from VLAN-interface 200 on AC 1 so AC 1 prefers route 1.1.5.0/24 learned from AC 2.
Configuration procedure
1. Configure IP addresses for interfaces. (Details not shown.)
2. Configure basic RIP:
# Configure AC 1.
<AC1> system-view
[AC1] rip 1
[AC1-rip-1] network 1.0.0.0
[AC1-rip-1] version 2
[AC1-rip-1] undo summary
[AC1-rip-1] quit
# Configure AC 2.
<AC2> system-view
[AC2] rip 1
[AC2-rip-1] network 1.0.0.0
[AC2-rip-1] version 2
[AC2-rip-1] undo summary
# Configure AC 3.
<AC3> system-view
[AC2] rip 1
[AC3-rip-1] network 1.0.0.0
[AC3-rip-1] version 2
[AC3-rip-1] undo summary
# Configure AC 4.
<AC4> system-view
[AC4] rip 1
[AC4-rip-1] network 1.0.0.0
[AC4-rip-1] version 2
[AC4-rip-1] undo summary
# Configure AC 5.
<AC5> system-view
[AC5] rip 1
[AC5-rip-1] network 1.0.0.0
[AC5-rip-1] version 2
[AC5-rip-1] undo summary
# Display all active routes in the RIP database on AC 1.
[AC1] display rip 1 database
1.0.0.0/8, auto-summary
1.1.1.0/24, cost 0, nexthop 1.1.1.1, RIP-interface
1.1.2.0/24, cost 0, nexthop 1.1.2.1, RIP-interface
1.1.3.0/24, cost 1, nexthop 1.1.1.2
1.1.4.0/24, cost 1, nexthop 1.1.2.2
1.1.5.0/24, cost 2, nexthop 1.1.1.2
1.1.5.0/24, cost 2, nexthop 1.1.2.2
The output shows two RIP routes destined for network 1.1.5.0/24, with the next hops as AC 2 (1.1.1.2) and AC 3 (1.1.2.2), and with the same cost of 2.
3. Configure an additional metric for a RIP interface:
# Configure an inbound additional metric of 3 for RIP-enabled interface VLAN-interface 200 on AC 1.
[AC1] interface vlan-interface 200
[AC1-Vlan-interface200] rip metricin 3
# Display all active routes in the RIP database on AC 1.
[AC1-Vlan-interface200] display rip 1 database
1.0.0.0/8, auto-summary
1.1.1.0/24, cost 0, nexthop 1.1.1.1, RIP-interface
1.1.2.0/24, cost 0, nexthop 1.1.2.1, RIP-interface
1.1.3.0/24, cost 1, nexthop 1.1.1.2
1.1.4.0/24, cost 2, nexthop 1.1.1.2
1.1.5.0/24, cost 2, nexthop 1.1.1.2
The output shows that only one RIP route reaches network 1.1.5.0/24, with the next hop as AC 2 (1.1.1.2) and a cost of 2.
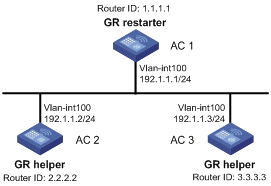
Configuring RIP GR
Network requirements
As shown in Figure 6, AC 1, AC 2, and AC 3 all run RIPv2.
· Enable GR on AC 1. AC 1 acts as the GR restarter.
· AC 2 and AC 3 act as GR helpers to synchronize their routing tables with AC 1 by using GR.
Configuration procedure
1. Configure IP addresses and subnet masks for interfaces on the AC5s. (Details not shown.)
2. Configure RIPv2 on the AC5s to ensure the following: (Details not shown.)
? AC 1, AC 2, and AC 3 can communicate with each other at Layer 3.
? Dynamic route update can be implemented among them with RIPv2.
3. Enable RIP GR on AC 1.
[AC1] rip
[AC1-rip-1] graceful-restart
Verifying the configuration
# Restart RIP or trigger an active/standby switchover, and then display GR status on AC 1.
<AC1> display rip graceful-restart
RIP process: 1
Graceful Restart capability : Enabled
Current GR state : Normal
Graceful Restart period : 60 seconds
Graceful Restart remaining time : 0 seconds
Configuring RIPng
Overview
RIP next generation (RIPng) is an extension of RIP-2 for support of IPv6. Most RIP concepts are applicable to RIPng.
RIPng is a distance vector routing protocol. It employs UDP to exchange route information through port 521. RIPng uses a hop count to measure the distance to a destination. The hop count is the metric or cost. The hop count from a router to a directly connected network is 0. The hop count between two directly connected routers is 1. When the hop count is greater than or equal to 16, the destination network or host is unreachable.
By default, the routing update is sent every 30 seconds. If the router receives no routing updates from a neighbor within 180 seconds, the routes learned from the neighbor are considered unreachable. If no routing update is received within another 240 seconds, the router removes these routes from the routing table.
RIPng for IPv6 has the following differences from RIP:
· UDP port number—RIPng uses UDP port 521 to send and receive routing information.
· Multicast address—RIPng uses FF02::9 as the link-local-router multicast address.
· Destination Prefix—128-bit destination address prefix.
· Next hop—128-bit IPv6 address.
· Source address—RIPng uses FE80::/10 as the link-local source address.
RIPng route entries
RIPng stores route entries in a database. Each route entry contains the following elements:
· Destination address—IPv6 address of a destination host or a network.
· Next hop address—IPv6 address of the next hop.
· Egress interface—Egress interface of the route.
· Metric—Cost from the local router to the destination.
· Route time—Time elapsed since the most recent update. The time is reset to 0 every time the route entry is updated.
· Route tag—Used for route control. For more information, see "Configuring routing policies."
RIPng packets
RIPng uses request and response packets to exchange routing information as follows:
1. When RIPng starts or needs to update some route entries, it sends a multicast request packet to neighbors.
2. When a RIPng neighbor receives the request packet, it sends back a response packet that contains the local routing table. RIPng can also advertise route updates in response packets periodically or advertise a triggered update caused by a route change.
3. After RIPng receives the response, it checks the validity of the response before adding routes to its routing table, including the following details:
? Whether the source IPv6 address is the link-local address.
? Whether the port number is correct.
4. A response packet that fails the check is discarded.
Protocols and standards
· RFC 2080, RIPng for IPv6
· RFC 2081, RIPng Protocol Applicability Statement
Feature and hardware compatibility
|
Hardware series |
Model |
Command compatibility |
|
WX1800H series |
WX1804H WX1810H WX1820H WX1840H |
Yes |
|
WX3800H series |
WX3820H WX3840H |
No |
|
WX5800H series |
WX5860H |
No |
RIPng configuration task list
|
Tasks at a glance |
|
(Required.) Configuring basic RIPng |
|
(Optional.) Configuring RIPng route control: · Configuring an additional routing metric · Configuring RIPng route summarization · Configuring received/redistributed route filtering |
|
(Optional.) Tuning and optimizing the RIPng network: · Configuring split horizon and poison reverse · Configuring zero field check on RIPng packets · Setting the maximum number of ECMP routes |
|
(Optional.) Configuring RIPng GR |
|
(Optional.) Applying an IPsec profile |
Configuring basic RIPng
Before you configure basic RIPng, configure IPv6 addresses for interfaces to ensure IPv6 connectivity between neighboring nodes.
To configure basic RIPng:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable RIPng and enter its view. |
ripng [ process-id ] |
By default, RIPng is disabled. |
|
3. Return to system view. |
quit |
N/A |
|
4. Enter interface view. |
interface interface-type interface-number |
N/A |
|
5. Enable RIPng on the interface. |
ripng process-id enable |
By default, RIPng is disabled. If RIPng is not enabled on an interface, the interface does not send or receive any RIPng route. |
Configuring RIPng route control
Before you configure RIPng, complete the following tasks:
· Configure IPv6 addresses for interfaces to ensure IPv6 connectivity between neighboring nodes.
· Configure basic RIPng.
Configuring an additional routing metric
An additional routing metric (hop count) can be added to the metric of an inbound or outbound RIPng route.
An outbound additional metric is added to the metric of a sent route, and it does not change the route's metric in the routing table.
An inbound additional metric is added to the metric of a received route before the route is added into the routing table, and the route's metric is changed.
To configure an inbound or outbound additional routing metric:
|
Command |
Remarks |
|
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Specify an inbound additional routing metric. |
ripng metricin value |
The default setting is 0. |
|
4. Specify an outbound additional routing metric. |
ripng metricout value |
The default setting is 1. |
Configuring RIPng route summarization
Configure route summarization on an interface, so RIPng advertises a summary route based on the longest match.
RIPng route summarization improves network scalability, reduces routing table size, and increases routing table lookup efficiency.
RIPng advertises a summary route with the smallest metric of all the specific routes.
For example, RIPng has two specific routes to be advertised through an interface: 1:11:11::24 with a metric of a 2 and 1:11:12::34 with a metric of 3. Configure route summarization on the interface, so RIPng advertises a single route 11::0/16 with a metric of 2.
To configure RIPng route summarization:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Advertise a summary IPv6 prefix. |
ripng summary-address ipv6-address prefix-length |
By default, the summary IPv6 prefix is not configured. |
Advertising a default route
You can configure RIPng to advertise a default route with the specified cost to its neighbors.
To configure RIPng to advertise a default route:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Configure RIPng to advertise a default route. |
ripng default-route { only | originate } [ cost cost-value ] |
By default, RIPng does not advertise a default route. This command advertises a default route on the current interface regardless of whether the default route exists in the local IPv6 routing table. |
Configuring received/redistributed route filtering
Perform this task to filter received or redistributed routes by using an IPv6 ACL or IPv6 prefix list. You can also configure RIPng to filter routes redistributed from other routing protocols and routes from a specified neighbor.
To configure a RIPng route filtering policy:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIPng view. |
ripng [ process-id ] |
N/A |
|
3. Configure a filter policy to filter received routes. |
filter-policy { ipv6-acl-number | prefix-list prefix-list-name } import |
By default, RIPng does not filter received routes. |
|
4. Configure a filter policy to filter redistributed routes. |
filter-policy { ipv6-acl-number | prefix-list prefix-list-name } export [ protocol [ process-id ] ] |
By default, RIPng does not filter redistributed routes. |
Setting a preference for RIPng
Routing protocols each have a preference. When they find routes to the same destination, the route found by the routing protocol with the highest preference is selected as the optimal route. You can manually set a preference for RIPng. The smaller the value, the higher the preference.
To set a preference for RIPng:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIPng view. |
ripng [ process-id ] |
N/A |
|
3. Set a preference for RIPng. |
preference preference |
By default, the preference of RIPng is 100. |
Configuring RIPng route redistribution
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIPng view. |
ripng [ process-id ] |
N/A |
|
3. Redistribute routes from other routing protocols. |
import-route protocol [ process-id ] [ allow-direct | cost cost-value ] * |
By default, RIPng does not redistribute routes from other routing protocols. |
|
4. (Optional.) Set a default routing metric for redistributed routes. |
default cost cost-value |
The default metric of redistributed routes is 0. |
Tuning and optimizing the RIPng network
This section describes how to tune and optimize the performance of the RIPng network as well as applications under special network environments.
Before you tune and optimize the RIPng network, complete the following tasks:
· Configure IPv6 addresses for interfaces to ensure IPv6 connectivity between neighboring nodes.
· Configure basic RIPng.
Setting RIPng timers
You can adjust RIPng timers to optimize the performance of the RIPng network.
When you adjust RIPng timers, consider the network performance, and perform unified configurations on routers running RIPng to avoid unnecessary network traffic or route oscillation.
To set RIPng timers:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIPng view. |
ripng [ process-id ] |
N/A |
|
3. Set RIPng timers. |
timers { garbage-collect garbage-collect-value | suppress suppress-value | timeout timeout-value | update update-value } * |
By default: · The update timer is 30 seconds. · The timeout timer is 180 seconds. · The suppress timer is 120 seconds. · The garbage-collect timer is 120 seconds. |
Configuring split horizon and poison reverse
If both split horizon and poison reverse are configured, only the poison reverse function takes effect.
Configuring split horizon
Split horizon disables RIPng from sending routes through the interface where the routes were learned to prevent routing loops between neighbors.
As a best practice, enable split horizon to prevent routing loops in normal cases.
To configure split horizon:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable split horizon. |
ripng split-horizon |
By default, split horizon is enabled. |
Configuring poison reverse
Poison reverse enables a route learned from an interface to be advertised through the interface. However, the metric of the route is set to 16, which means the route is unreachable.
To configure poison reverse:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Enable poison reverse. |
ripng poison-reverse |
By default, poison reverse is disabled. |
Configuring zero field check on RIPng packets
Some fields in the RIPng packet header must be zero. These fields are called zero fields. You can enable zero field check on incoming RIPng packets. If a zero field of a packet contains a non-zero value, RIPng does not process the packets. If you are certain that all packets are trustworthy, disable the zero field check to save CPU resources.
To configure RIPng zero field check:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIPng view. |
ripng [ process-id ] |
N/A |
|
3. Enable the zero field check on incoming RIPng packets. |
checkzero |
By default, zero field check is enabled for incoming RIPng packets. |
Setting the maximum number of ECMP routes
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIPng view. |
ripng [ process-id ] |
N/A |
|
3. Set the maximum number of ECMP routes. |
maximum load-balancing number |
By default, the maximum number of ECMP routes is 4. |
Configuring the RIPng packet sending rate
Perform this task to specify the interval for sending RIPng packets and the maximum number of RIPng packets that can be sent at each interval. This feature can avoid excessive RIPng packets from affecting system performance and consuming too much bandwidth.
To configure the RIPng packet sending rate:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIPng view. |
ripng [ process-id ] |
N/A |
|
3. Set the interval for sending RIPng packets and the maximum number of RIPng packets that can be sent at each interval. |
output-delay time count count |
By default, a RIPng process sends a maximum of three RIPng packets every 20 milliseconds. |
|
4. Return to system view. |
quit |
N/A |
|
5. Enter interface view. |
N/A |
|
|
6. Set the interval for sending RIPng packets and the maximum number of RIPng packets that can be sent at each interval. |
By default, an interface uses the RIPng packet sending rate configured for the RIPng process that the interface runs. |
Setting the interval for sending triggered updates
Perform this task to avoid network overhead and reduce system resource consumption caused by frequent RIPng triggered updates.
You can use the timer triggered command to set the maximum interval, minimum interval, and incremental interval for sending RIPng triggered updates.
For a stable network, the minimum interval is used. If network changes become frequent, the triggered update sending interval is incremented by the incremental interval × 2n-2 for each triggered update until the maximum interval is reached. The value n is the number of triggered update times.
To set the interval for sending triggered updates:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIPng view. |
N/A |
|
|
3. Set the interval for sending triggered updates. |
timer triggered maximum-interval [ minimum-interval [ incremental-interval ] ] |
By default: · The maximum interval is 5 seconds. · The minimum interval is 50 milliseconds. · The incremental interval is 200 milliseconds. |
Configuring RIPng GR
GR ensures forwarding continuity when a routing protocol restarts.
Two routers are required to complete a GR process. The following are router roles in a GR process:
· GR restarter—Graceful restarting router. It must have GR capability.
· GR helper—A neighbor of the GR restarter. It helps the GR restarter to complete the GR process.
After RIPng restarts on a router, the router must learn RIPng routes again and updates its FIB table, which causes network disconnections and route reconvergence.
With the GR feature, the restarting router (known as the GR restarter) can notify the event to its GR capable neighbors. GR capable neighbors (known as GR helpers) maintain their adjacencies with the router within a configurable GR interval. During this process, the FIB table of the router does not change. After the restart, the router contacts its neighbors to retrieve its FIB.
By default, a RIPng-enabled device acts as the GR helper. Perform this task on the GR restarter.
To configure GR on the GR restarter:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable RIPng and enter RIPng view. |
ripng [ process-id ] |
N/A |
|
3. Enable the GR capability for RIPng. |
graceful-restart |
By default, RIPng GR is disabled. |
|
4. (Optional.) Set the GR interval. |
By default, the GR interval is 60 seconds. |
Applying an IPsec profile
The following matrix shows the feature and hardware compatibility:
|
Hardware series |
Model |
Command compatibility |
|
WX1800H series |
WX1804H WX1810H WX1820H WX1840H |
Yes: · WX1804H · WX1810H · WX1820H No: · WX1840H |
|
WX3800H series |
WX3820H WX3840H |
No |
|
WX5800H series |
WX5860H |
No |
To protect routing information and prevent attacks, RIPng supports using an IPsec profile to authenticate protocol packets. For more information about IPsec profiles, see Security Configuration Guide.
Outbound RIPng packets carry the Security Parameter Index (SPI) defined in the relevant IPsec profile. A device compares the SPI carried in a received packet with the configured IPsec profile. If they match, the device accepts the packet. If they do not match, the device discards the packet and does not establish a neighbor relationship with the sending device.
You can configure an IPsec profile for a RIPng process or interface. The IPsec profile configured for a process applies to all packets in the process. The IPsec profile configured for an interface applies to packets on the interface. If an interface and its process each have an IPsec profile configured, the interface uses its own IPsec profile.
To apply an IPsec profile to a process:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter RIPng view. |
ripng [ process-id ] |
N/A |
|
3. Apply an IPsec profile to the process. |
enable ipsec-profile profile-name |
By default, no IPsec profile is applied. |
To apply an IPsec profile to an interface:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Apply an IPsec profile to the interface. |
ripng ipsec-profile profile-name |
By default, no IPsec profile is applied. |
Displaying and maintaining RIPng
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display configuration information for a RIPng process. |
display ripng [ process-id ] |
|
Display routes in the RIPng database. |
display ripng process-id database [ ipv6-address prefix-length ] |
|
Display RIPng GR information. |
|
|
Display interface information for a RIPng process. |
display ripng process-id interface [ interface-type interface-number ] |
|
Display neighbor information for a RIPng process. |
display ripng process-id neighbor [ interface-type interface-number ] |
|
Display the routing information for a RIPng process. |
display ripng process-id route [ ipv6-address prefix-length [ verbose ] | peer ipv6-address | statistics ] |
|
Restart a RIPng process. |
reset ripng process-id process |
|
Clear statistics for a RIPng process. |
reset ripng process-id statistics |
RIPng configuration examples
Basic RIPng configuration example
Network requirements
As shown in Figure 7, AC 1, AC 2, and AC 3 run RIPng. Configure AC 2 to filter the route 2::/64 learned from AC 1 and to forward only the route 4::/64 to AC 1.

Configuration procedure
1. Configure IPv6 addresses for interfaces. (Details not shown.)
2. Configure basic RIPng:
# Configure AC 1.
<AC1> system-view
[AC1] ripng 1
[AC1-ripng-1] quit
[AC1] interface vlan-interface 100
[AC1-Vlan-interface100] ripng 1 enable
[AC1-Vlan-interface100] quit
[AC1] interface vlan-interface 400
[AC1-Vlan-interface400] ripng 1 enable
[AC1-Vlan-interface400] quit
# Configure AC 2.
<AC1> system-view
[AC1] ripng 1
[AC1-ripng-1] quit
[AC1] interface vlan-interface 100
[AC1-Vlan-interface100] ripng 1 enable
[AC1-Vlan-interface100] quit
[AC1] interface vlan-interface 400
[AC1-Vlan-interface400] ripng 1 enable
[AC1-Vlan-interface400] quit
# Configure AC 3.
<AC3> system-view
[AC3] ripng 1
[AC3-ripng-1] quit
[AC3] interface vlan-interface 200
[AC3-Vlan-interface200] ripng 1 enable
[AC3-Vlan-interface200] quit
[AC3] interface vlan-interface 500
[AC3-Vlan-interface500] ripng 1 enable
[AC3-Vlan-interface500] quit
[AC3] interface vlan-interface 600
[AC3-Vlan-interface600] ripng 1 enable
[AC3-Vlan-interface600] quit
# Display the RIPng routing table on AC 2.
Route Flags: A - Aging, S - Suppressed, G - Garbage-collect, D – Direct
O - Optimal, F - Flush to RIB
----------------------------------------------------------------
Peer FE80::20F:E2FF:FE23:82F5 on Vlan-interface100
Destination 2::/64,
via FE80::20F:E2FF:FE23:82F5, cost 1, tag 0, AOF, 6 secs
Peer FE80::20F:E2FF:FE00:100 on Vlan-interface200
Destination 4::/64,
via FE80::20F:E2FF:FE00:100, cost 1, tag 0, AOF, 11 secs
Destination 5::/64,
via FE80::20F:E2FF:FE00:100, cost 1, tag 0, AOF, 11
Local route
Destination 1::/64,
via ::, cost 0, tag 0, DOF
Destination 3::/64,
via ::, cost 0, tag 0, DOF
# Display the RIPng routing table on AC 1.
Route Flags: A - Aging, S - Suppressed, G - Garbage-collect, D – Direct
O - Optimal, F - Flush to RIB
----------------------------------------------------------------
Peer FE80::200:2FF:FE64:8904 on Vlan-interface100
Destination 3::/64,
via FE80::200:2FF:FE64:8904, cost 1, tag 0, AOF, 31 secs
Destination 4::/64,
via FE80::200:2FF:FE64:8904, cost 2, tag 0, AOF, 31 secs
Destination 5::/64,
via FE80::200:2FF:FE64:8904, cost 2, tag 0, AOF, 31 secs
Local route
Destination 2::/64,
via ::, cost 0, tag 0, DOF
Destination 1::/64,
via ::, cost 0, tag 0, DOF
3. Configure route filtering:
# Use IPv6 prefix lists on AC 2 to filter received and redistributed routes.
[AC2] ipv6 prefix-list aaa permit 4:: 64
[AC2] ipv6 prefix-list bbb deny 2:: 64
[AC2] ipv6 prefix-list bbb permit :: 0 less-equal 128
[AC2] ripng 1
[AC2-ripng-1] filter-policy prefix-list aaa export
[AC2-ripng-1] filter-policy prefix-list bbb import
[AC2-ripng-1] quit
# Display RIPng routing tables on AC 2 and AC 1.
Route Flags: A - Aging, S - Suppressed, G - Garbage-collect, D – Direct
O - Optimal, F - Flush to RIB
----------------------------------------------------------------
Peer FE80::1:100 on Vlan-interface100
Peer FE80::3:200 on Vlan-interface200
Destination 4::/64,
via FE80::2:200, cost 1, tag 0, AOF, 11 secs
Destination 5::/64,
via FE80::2:200, cost 1, tag 0, AOF, 11 secs
Local route
Destination 1::/64,
via ::, cost 0, tag 0, DOF
Destination 3::/64,
via ::, cost 0, tag 0, DOF
[AC1] display ripng 1 route
Route Flags: A - Aging, S - Suppressed, G - Garbage-collect, D – Direct
O - Optimal, F - Flush to RIB
----------------------------------------------------------------
Peer FE80::2:100 on Vlan-interface100
Destination 4::/64,
via FE80::1:100, cost 2, tag 0, AOF, 2 secs
RIPng route redistribution configuration example
Network requirements
As shown in Figure 8, AC 2 communicates with AC 1 through RIPng 100 and with AC 3 through RIPng 200.
Configure route redistribution on AC 2, so the two RIPng processes can redistribute routes from each other.
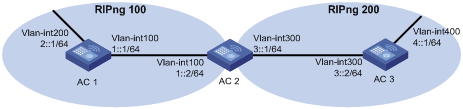
Configuration procedure
1. Configure IPv6 addresses for interfaces. (Details not shown.)
2. Configure basic RIPng:
# Enable RIPng 100 on AC 1.
<AC1> system-view
[AC1] ripng 100
[AC1-ripng-100] quit
[AC1] interface vlan-interface 100
[AC1-Vlan-interface100] ripng 100 enable
[AC1-Vlan-interface100] quit
[AC1] interface vlan-interface 200
[AC1-Vlan-interface200] ripng 100 enable
[AC1-Vlan-interface200] quit
# Enable RIPng 100 and RIPng 200 on AC 2.
<AC2> system-view
[AC2] ripng 100
[AC2-ripng-100] quit
[AC2] interface vlan-interface 100
[AC2-Vlan-interface100] ripng 100 enable
[AC2-Vlan-interface100] quit
[AC2] ripng 200
[AC2-ripng-200] quit
[AC2] interface vlan-interface 300
[AC2-Vlan-interface300] ripng 200 enable
[AC2-Vlan-interface300] quit
# Enable RIPng 200 on AC 3.
<AC3> system-view
[AC3] ripng 200
[AC3] interface vlan-interface 300
[AC3-Vlan-interface300] ripng 200 enable
[AC3-Vlan-interface300] quit
[AC3] interface vlan-interface 400
[AC3-Vlan-interface400] ripng 200 enable
[AC3-Vlan-interface400] quit
# Display the routing table on AC 1.
[AC1] display ipv6 routing-table
Destinations : 7 Routes : 7
Destination: ::1/128 Protocol : Direct
NextHop : ::1 Preference: 0
Interface : InLoop0 Cost : 0
Destination: 1::/64 Protocol : Direct
NextHop : 1::1 Preference: 0
Interface : Vlan100 Cost : 0
Destination: 1::1/128 Protocol : Direct
NextHop : ::1 Preference: 0
Interface : InLoop0 Cost : 0
Destination: 2::/64 Protocol : Direct
NextHop : 2::1 Preference: 0
Interface : Vlan200 Cost : 0
Destination: 2::1/128 Protocol : Direct
NextHop : ::1 Preference: 0
Interface : InLoop0 Cost : 0
Destination: FE80::/10 Protocol : Direct
NextHop : :: Preference: 0
Interface : NULL0 Cost : 0
Destination: FF00::/8 Protocol : Direct
NextHop : :: Preference: 0
Interface : NULL0 Cost : 0
3. Configure RIPng route redistribution:
# Configure route redistribution between the two RIPng processes on AC 2.
[AC2] ripng 100
[AC2-ripng-100] import-route ripng 200
[AC2-ripng-100] quit
[AC2] ripng 200
[AC2-ripng-200] import-route ripng 100
[AC2-ripng-200] quit
# Display the routing table on AC 1.
[AC1] display ipv6 routing-table
Destinations : 8 Routes : 8
Destination: ::1/128 Protocol : Direct
NextHop : ::1 Preference: 0
Interface : InLoop0 Cost : 0
Destination: 1::/64 Protocol : Direct
NextHop : 1::1 Preference: 0
Interface : Vlan100 Cost : 0
Destination: 1::1/128 Protocol : Direct
NextHop : ::1 Preference: 0
Interface : InLoop0 Cost : 0
Destination: 2::/64 Protocol : Direct
NextHop : 2::1 Preference: 0
Interface : Vlan200 Cost : 0
Destination: 2::1/128 Protocol : Direct
NextHop : ::1 Preference: 0
Interface : InLoop0 Cost : 0
Destination: 4::/64 Protocol : RIPng
NextHop : FE80::200:BFF:FE01:1C02 Preference: 100
Interface : Vlan100 Cost : 1
Destination: FE80::/10 Protocol : Direct
NextHop : :: Preference: 0
Interface : NULL0 Cost : 0
Destination: FF00::/8 Protocol : Direct
NextHop : :: Preference: 0
Interface : NULL0 Cost : 0
RIPng GR configuration example
Network requirements
As shown in Figure 9, AC 1, AC 2, and AC 3 learn IPv6 routing information through RIPng.
Configure AC 1 as the GR restarter. Configure AC 2 and AC 3 as the GR helpers to synchronize their routing tables with AC 1 by using GR.
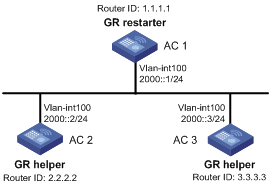
Configuration procedure
1. Configure IPv6 addresses for interfaces. (Details not shown.)
2. Configure RIPng on the ACs to ensure the following: (Details not shown.)
? AC 1, AC 2, and AC 3 can communicate with each other at Layer 3.
? Dynamic route update can be implemented among them with RIPng.
3. Enable RIPng GR on AC 1.
<AC1> system-view
[AC1] ripng 1
[AC1-ripng-1] graceful-restart
Verifying the configuration
# Restart RIPng or trigger an active/standby switchover, and then display GR status on AC 1.
<AC1> display ripng 1 graceful-restart
RIPng process: 1
Graceful Restart capability : Enabled
Current GR state : Normal
Graceful Restart period : 60 seconds
Graceful Restart remaining time: 0 seconds
RIPng IPsec profile configuration example
Network requirements
As shown in Figure 10, configure RIPng on the ACs, and configure IPsec profiles on the ACs to authenticate and encrypt protocol packets.

Configuration procedure
1. Configure IPv6 addresses for interfaces. (Details not shown.)
2. Configure RIPng basic functions:
# Configure AC 1.
<AC1> system-view
[AC1] ripng 1
[AC1-ripng-1] quit
[AC1] interface vlan-interface 100
[AC1-Vlan-interface100] ripng 1 enable
[AC1-Vlan-interface100] quit
# Configure AC 2.
<AC2> system-view
[AC2] ripng 1
[AC2-ripng-1] quit
[AC2] interface vlan-interface 200
[AC2-Vlan-interface200] ripng 1 enable
[AC2-Vlan-interface200] quit
[AC2] interface vlan-interface 100
[AC2-Vlan-interface100] ripng 1 enable
[AC2-Vlan-interface100] quit
# Configure AC 3.
<AC3> system-view
[AC3] ripng 1
[AC3-ripng-1] quit
[AC3] interface vlan-interface 200
[AC3-Vlan-interface200] ripng 1 enable
[AC3-Vlan-interface200] quit
3. Configure RIPng IPsec profiles:
? On AC 1:
# Create an IPsec transform set named protrf1.
[AC1] ipsec transform-set protrf1
# Specify the ESP encryption and authentication algorithms.
[AC1-ipsec-transform-set-protrf1] esp encryption-algorithm 3des-cbc
[AC1-ipsec-transform-set-protrf1] esp authentication-algorithm md5
# Specify the encapsulation mode as transport.
[AC1-ipsec-transform-set-protrf1] encapsulation-mode transport
[AC1-ipsec-transform-set-protrf1] quit
# Create a manual IPsec profile named profile001.
[AC1] ipsec profile profile001 manual
# Reference IPsec transform set protrf1.
[AC1-ipsec-profile-profile001-manual] transform-set protrf1
# Configure the inbound and outbound SPIs for ESP.
[AC1-ipsec-profile-profile001-manual] sa spi inbound esp 256
[AC1-ipsec-profile-profile001-manual] sa spi outbound esp 256
# Configure the inbound and outbound SA keys for ESP.
[AC1-ipsec-profile-profile001-manual] sa string-key inbound esp simple abc
[AC1-ipsec-profile-profile001-manual] sa string-key outbound esp simple abc
[AC1-ipsec-profile-profile001-manual] quit
? On AC 2:
# Create an IPsec transform set named protrf1.
[AC2] ipsec transform-set protrf1
# Specify the ESP encryption and authentication algorithms.
[AC2-ipsec-transform-set-protrf1] esp encryption-algorithm 3des-cbc
[AC2-ipsec-transform-set-protrf1] esp authentication-algorithm md5
# Specify the encapsulation mode as transport.
[AC2-ipsec-transform-set-protrf1] encapsulation-mode transport
[AC2-ipsec-transform-set-protrf1] quit
# Create a manual IPsec profile named profile001.
[AC2] ipsec profile profile001 manual
# Reference IPsec transform set protrf1.
[AC2-ipsec-profile-profile001-manual] transform-set protrf1
# Configure the inbound and outbound SPIs for ESP.
[AC2-ipsec-profile-profile001-manual] sa spi inbound esp 256
[AC2-ipsec-profile-profile001-manual] sa spi outbound esp 256
# Configure the inbound and outbound SA keys for ESP.
[AC2-ipsec-profile-profile001-manual] sa string-key inbound esp simple abc
[AC2-ipsec-profile-profile001-manual] sa string-key outbound esp simple abc
[AC2-ipsec-profile-profile001-manual] quit
? On AC 3:
# Create an IPsec transform set named protrf1.
[AC3] ipsec transform-set protrf1
# Specify the ESP encryption and authentication algorithms.
[AC3-ipsec-transform-set-protrf1] esp encryption-algorithm 3des-cbc
[AC3-ipsec-transform-set-protrf1] esp authentication-algorithm md5
# Specify the encapsulation mode as transport.
[AC3-ipsec-transform-set-protrf1] encapsulation-mode transport
[AC3-ipsec-transform-set-protrf1] quit
# Create a manual IPsec profile named profile001.
[AC3] ipsec profile profile001 manual
# Reference IPsec transform set protrf1.
[AC3-ipsec-profile-profile001-manual] transform-set protrf1
# Configure the inbound and outbound SPIs for ESP.
[AC3-ipsec-profile-profile001-manual] sa spi inbound esp 256
[AC3-ipsec-profile-profile001-manual] sa spi outbound esp 256
# Configure the inbound and outbound SA keys for ESP.
[AC3-ipsec-profile-profile001-manual] sa string-key inbound esp simple abc
[AC3-ipsec-profile-profile001-manual] sa string-key outbound esp simple abc
[AC3-ipsec-profile-profile001-manual] quit
4. Apply the IPsec profiles to the RIPng process:
# Configure AC 1.
[AC1] ripng 1
[AC1-ripng-1] enable ipsec-profile profile001
[AC1-ripng-1] quit
# Configure AC 2.
[AC2] ripng 1
[AC2-ripng-1] enable ipsec-profile profile001
[AC2-ripng-1] quit
# Configure AC 3.
[AC3] ripng 1
[AC3-ripng-1] enable ipsec-profile profile001
[AC3-ripng-1] quit
Verifying the configuration
# Verify that RIPng packets between ACs A, B and C are protected by IPsec. (Details not shown.)
A
advertising
RIP default route, 21
RIP on interface, 18
RIPng default route, 40
RIPv2 summary route, 20
applying
RIPng IPsec profile, 44
authenticating
RIPng IPsec profile application, 44
RIPv2 message authentication configuration, 25
automatic
RIPv2 automatic route summarization enable, 20
B
backing up
IP routing route backup, 2
C
configuring
IP routing, 1
IPv6 default route, 14
IPv6 static route, 11
IPv6 static routing, 11
IPv6 static routing basics, 12
RIP, 15, 17, 29
RIP additional routing metric, 19
RIP basics, 17, 29
RIP GR, 28, 36
RIP interface additional metric, 34
RIP network management, 27
RIP packet send rate, 27
RIP poison reverse, 24
RIP received/redistributed route filtering, 22
RIP route control, 19
RIP route redistribution, 22, 32
RIP split horizon, 24
RIP timers, 23
RIP version, 19
RIPng, 37, 38, 46
RIPng basics, 38, 46
RIPng GR, 44, 51
RIPng IPsec profile configuration, 52
RIPng packet send rate, 43
RIPng packet zero field check, 42
RIPng poison reverse, 42
RIPng received/redistributed route filtering, 40
RIPng route control, 39
RIPng route redistribution, 41, 48
RIPng route summarization, 39
RIPng routing metric, 39
RIPng split horizon, 42
RIPv2 message authentication, 25
RIPv2 route summarization, 20
static routing, 6, 6
static routing basics, 7
static routing default route, 10
controlling
RIP additional routing metric configuration, 19
RIP interface advertisement, 18
RIP interface reception, 18, 18
RIP route control configuration, 19
RIPng route control, 39
D
default
IPv6 default route configuration, 14
RIP default route advertisement, 21
RIPng default route advertisement, 40
static routing configuration. See under static routing
device
RIP basic configuration, 29
RIP configuration, 29
RIP GR configuration, 36
RIP interface additional metric configuration, 34
RIP route redistribution, 32
RIPng basic configuration, 46
RIPng configuration, 46
RIPng GR configuration, 51
RIPng IPsec profile configuration, 52
RIPng route redistribution, 48
disabling
RIP host route reception, 21
displaying
IP routing table, 4
IPv6 static routing, 11
RIP, 29
RIPng, 45
static routing, 7
distributing
RIPng received/redistributed route filtering, 40
RIPng route redistribution, 41, 48
E
ECMP
IP routing ECMP route max number, 4
RIP ECMP route max number, 24
RIPng ECMP route max, 43
enabling
RIP, 17
RIP poison reverse, 24
RIP split horizon, 24
RIP update source IP address check, 25
RIPv1 incoming message zero field check, 25
RIPv2 automatic route summarization, 20
F
FIB
IP routing table, 1
filtering
RIP received/redistributed route filtering, 22
RIPng received/redistributed route filtering, 40
G
garbage-collect timer (RIP), 23
Graceful Restart (GR)
RIP configuration, 28, 36
RIP GR helper configuration, 28
RIP GR restarter configuration, 28
RIPng configuration, 44, 51
H
host route reception, 21
I
IGP
RIP configuration, 15, 17, 29
RIP neighbor specification, 26
interval
RIP triggered update interval, 26
RIPng triggered update send interval, 43
IP addressing
RIP configuration, 15, 17, 29
RIP update source IP address check, 25
IP routing
configuration, 1
displaying IPv6 static routing, 11
displaying routing table, 4
displaying static routes, 7
ECMP route max number configuration, 4
FIB route max lifetime, 3
IPv6 default route. See under IPv6 static routing
IPv6 static routing. See IPv6 static routing
load sharing, 2
maintaining routing table, 4
RIB label max lifetime, 3
RIB route max lifetime, 3
RIP additional routing metric configuration, 19
RIP basic configuration, 17, 29
RIP configuration, 15, 17, 29
RIP default route advertisement, 21
RIP ECMP route max number, 24
RIP GR configuration, 28, 36
RIP host route reception disable, 21
RIP interface additional metric configuration, 34
RIP interface advertisement control, 18
RIP interface reception control, 18
RIP neighbor specification, 26
RIP network management configuration, 27
RIP network optimization, 23
RIP network tuning, 23
RIP operation, 15
RIP packet max length, 28
RIP packet send rate configuration, 27
RIP poison reverse configuration, 24
RIP preference configuration, 22
RIP received/redistributed route filtering, 22
RIP route control configuration, 19
RIP route entries, 15
RIP route redistribution, 32
RIP route redistribution configuration, 22
RIP routing loop prevention, 15
RIP split horizon configuration, 24
RIP timer configuration, 23
RIP triggered update interval configuration, 26
RIP update source IP address check, 25
RIP version configuration, 19
RIP versions, 16
RIPng basic configuration, 38, 46
RIPng configuration, 37, 38, 46
RIPng default route advertisement, 40
RIPng display, 45
RIPng ECMP route max, 43
RIPng GR configuration, 44, 51
RIPng IPsec profile application, 44
RIPng IPsec profile configuration, 52
RIPng maintain, 45
RIPng network optimization, 41
RIPng network tuning, 41
RIPng packet, 37
RIPng packet send rate, 43
RIPng packet zero field check configuration, 42
RIPng poison reverse configuration, 42
RIPng preference, 41
RIPng protocols and standards, 38
RIPng received/redistributed route filtering, 40
RIPng route control, 39
RIPng route entry, 37
RIPng route redistribution, 41, 48
RIPng route summarization, 39
RIPng routing metric configuration, 39
RIPng split horizon configuration, 42
RIPng timer configuration, 41
RIPng triggered update send interval, 43
RIPv1 message zero field check, 25
RIPv2 message authentication configuration, 25
RIPv2 route summarization configuration, 20
route backup, 2
route preference, 2
route recursion, 2
routing table, 1
static routing basic configuration, 7
static routing configuration, 6, 6
static routing default route configuration, 10
IPsec
RIPng IPsec profile application, 44
RIPng IPsec profile configuration, 52
IPv4
IP routing FIB route max lifetime, 3
IP routing RIB label max lifetime, 3
IP routing RIB route max lifetime, 3
IPv6
IP routing FIB route max lifetime, 3
IP routing RIB label max lifetime, 3
IP routing RIB route max lifetime, 3
RIP, 37, See also RIPng
RIPng GR configuration, 51
basic configuration, 12
configuration, 11
default route configuration, 14
displaying, 11
route configuration, 11
L
label
IP routing RIB label max lifetime, 3
load balancing
IP routing ECMP route max number, 4
RIPng ECMP route max, 43
load sharing
IP routing load sharing, 2
RIP ECMP route max number, 24
loop
RIP routing loop prevention, 15
M
maintaining
IP routing table, 4
RIP, 29
RIPng, 45
message
RIPv1 message zero field check enable, 25
RIPv2 message authentication configuration, 25
metric
RIP additional routing metric configuration, 19
RIP interface additional metric configuration, 34
RIPng routing metric configuration, 39
multicast
RIPng basic configuration, 38
RIPng configuration, 37, 38
N
neighbor
RIP neighbor specification, 26
network
IP routing ECMP route max number, 4
IP routing FIB route max lifetime, 3
IP routing load sharing, 2
IP routing RIB label max lifetime, 3
IP routing RIB route max lifetime, 3
IP routing route backup, 2
IP routing route preference, 2
IP routing route recursion, 2
IPv6 static route configuration, 11
RIP additional routing metric configuration, 19
RIP basic configuration, 17, 29
RIP default route advertisement, 21
RIP ECMP route max number, 24
RIP GR configuration, 28, 36
RIP host route reception disable, 21
RIP interface additional metric configuration, 34
RIP interface advertisement control, 18
RIP interface reception control, 18
RIP network management configuration, 27
RIP network optimization, 23
RIP network tuning, 23
RIP operation, 15
RIP packet max length, 28
RIP packet send rate configuration, 27
RIP poison reverse configuration, 24
RIP preference configuration, 22
RIP received/redistributed route filtering, 22
RIP route control configuration, 19
RIP route entries, 15
RIP route redistribution, 32
RIP route redistribution configuration, 22
RIP routing loop prevention, 15
RIP split horizon configuration, 24
RIP timer configuration, 23
RIP triggered update interval configuration, 26
RIP update source IP address check, 25
RIP version configuration, 19
RIP versions, 16
RIPng basic configuration, 38, 46
RIPng default route advertisement, 40
RIPng ECMP route max, 43
RIPng GR configuration, 44, 51
RIPng IPsec profile application, 44
RIPng IPsec profile configuration, 52
RIPng network optimization, 41
RIPng network tuning, 41
RIPng packet, 37
RIPng packet send rate, 43
RIPng packet zero field check, 42
RIPng poison reverse, 42
RIPng preference, 41
RIPng received/redistributed route filtering, 40
RIPng route control, 39
RIPng route entry, 37
RIPng route redistribution, 41, 48
RIPng route summarization, 39
RIPng routing metric configuration, 39
RIPng split horizon, 42
RIPng timer configuration, 41
RIPng triggered update send interval, 43
RIPv1 message zero field check, 25
RIPv2 message authentication configuration, 25
RIPv2 route summarization configuration, 20
static routing configuration, 6
network management
IP routing configuration, 1
IPv6 default route configuration, 14
IPv6 static routing basic configuration, 12
IPv6 static routing configuration, 11
RIP configuration, 15, 17, 29
RIPng configuration, 37, 38, 46
static routing basic configuration, 7
static routing configuration, 6
static routing default route configuration, 10
O
optimal
IP routing FIB table optimal routes, 1
optimizing
RIP networks, 23
RIPng network, 41
P
packet
IP routing configuration, 1
IP routing load sharing, 2
IP routing route backup, 2
IP routing route preference, 2
IP routing route recursion, 2
RIP network management configuration, 27
RIP packet max length, 28
RIP packet send rate configuration, 27
RIPng, 37
RIPng packet send rate, 43
RIPng packet zero field check, 42
RIPng triggered update send interval, 43
poison reverse, 24, 24
RIPng configuration, 42
preference
IP routing route preference, 2
RIP configuration, 22
preferring
RIPng preference, 41
procedure
advertising RIP default route, 21
advertising RIPng default route, 40
advertising RIPv2 summary route, 20
applying RIPng IPsec profile, 44
configuring IP routing RIP GR, 36
configuring IPv6 static route, 11
configuring IPv6 static routing basics, 12
configuring RIP, 17, 29
configuring RIP additional routing metric, 19
configuring RIP basics, 17, 29
configuring RIP GR, 28
configuring RIP interface additional metric, 34
configuring RIP network management, 27
configuring RIP packet send rate, 27
configuring RIP poison reverse, 24
configuring RIP received/redistributed route filtering, 22
configuring RIP route control, 19
configuring RIP route redistribution, 22, 32
configuring RIP split horizon, 24
configuring RIP timers, 23
configuring RIP version, 19
configuring RIPng, 38
configuring RIPng basics, 38, 46
configuring RIPng GR, 44, 51
configuring RIPng IPsec profile configuration, 52
configuring RIPng packet send rate, 43
configuring RIPng packet zero field check, 42
configuring RIPng poison reverse, 42
configuring RIPng received/redistributed route filtering, 40
configuring RIPng route control, 39
configuring RIPng route redistribution, 41, 48
configuring RIPng route summarization, 39
configuring RIPng routing metric, 39
configuring RIPng split horizon, 42
configuring RIPv2 message authentication, 25
configuring RIPv2 route summarization, 20
configuring static route, 6
configuring static routing basics, 7
configuring static routing default route, 10
controlling RIP interface advertisement, 18
controlling RIP interface reception, 18
disabling RIP host route reception, 21
displaying IP routing table, 4
displaying IPv6 static routing, 11
displaying RIP, 29
displaying RIPng, 45
displaying static routing, 7
enabling RIP, 17
enabling RIP poison reverse, 24
enabling RIP split horizon, 24
enabling RIP update source IP address check, 25
enabling RIPv1 message zero field check, 25
enabling RIPv2 automatic route summarization, 20
maintaining IP routing table, 4
maintaining RIP, 29
maintaining RIPng, 45
optimizing RIP networks, 23
optimizing RIPng network, 41
setting IP routing ECMP route max number, 4
setting IP routing FIB route max lifetime, 3
setting IP routing RIB label max lifetime, 3
setting IP routing RIB route max lifetime, 3
setting RIP ECMP route max number, 24
setting RIP packet max length, 28
setting RIP preference, 22
setting RIP triggered update interval, 26
setting RIPng ECMP route max, 43
setting RIPng preference, 41
setting RIPng timer, 41
setting RIPng triggered update send interval, 43
specifying RIP neighbor, 26
tuning IP routing RIP networks, 23
tuning RIPng network, 41
protocols and standards
RIP, 16
RIPng, 38
triggered RIP (TRIP), 16
R
receiving
RIPng received/redistributed route filtering, 40
recursion
IP routing route recursion, 2
redistributing
RIP received/redistributed route filtering, 22
RIP route redistribution, 32
RIP routes, 22
RIPng received/redistributed route filtering, 40
RIPng route redistribution, 41, 48
RIB
IP routing FIB route max lifetime, 3
IP routing RIB label max lifetime, 3
IP routing RIB route max lifetime, 3
additional routing metric configuration, 19
basic configuration, 17, 29
configuration, 15, 17, 29
default route advertisement, 21
displaying, 29
ECMP route max number, 24
enabling, 17
GR configuration, 28, 36
GR helper configuration, 28
GR restarter configuration, 28
host route reception disable, 21
interface additional metric configuration, 34
interface advertisement control, 18
interface reception control, 18
IPv6. See RIPng
maintaining, 29
neighbor specification, 26
network management configuration, 27
network optimization, 23
network tuning, 23
operation, 15
packet max length, 28
packet send rate configuration, 27
poison reverse configuration, 24
poison reverse enable, 24
preference configuration, 22
protocols and standards, 16
received/redistributed route filtering, 22
RIPv1 message zero field check enable, 25
RIPv2 message authentication configuration, 25
RIPv2 route summarization configuration, 20
route control configuration, 19
route entries, 15
route redistribution, 32
route redistribution configuration, 22
routing loop prevention, 15
split horizon configuration, 24
split horizon enable, 24
timer configuration, 23
triggered update interval configuration, 26
update source IP address check, 25
version configuration, 19
versions, 16
basic configuration, 38, 46
configuration, 37, 38, 46
default route advertisement, 40
display, 45
ECMP route max, 43
GR configuration, 44, 51
IPsec profile application, 44
IPsec profile configuration, 52
maintain, 45
network optimization, 41
network tuning, 41
packet, 37
packet send rate configuration, 43
packet zero field check, 42
poison reverse configuration, 42
preference configuration, 41
protocols and standards, 38
received/redistributed route filtering, 40
route control, 39
route entry, 37
route redistribution, 48
route redistribution configuration, 41
route summarization, 39
routing metric configuration, 39
split horizon configuration, 42
timer configuration, 41
triggered update send interval configuration, 43
RIPv1
message zero field check enable, 25
protocols and standards, 16
RIP basic configuration, 17
RIP configuration, 15, 17, 29
RIP versions, 16
version configuration, 19
RIPv2
automatic route summarization enable, 20
message authentication configuration, 25
protocols and standards, 16
RIP basic configuration, 17
RIP configuration, 15, 17, 29
RIP versions, 16
route summarization configuration, 20
summary route advertisement, 20
version configuration, 19
route
IP routing ECMP route max number, 4
IP routing FIB route max lifetime, 3
IP routing FIB table optimal routes, 1
IP routing load sharing, 2
IP routing RIB label max lifetime, 3
IP routing RIB route max lifetime, 3
IP routing route backup, 2
IP routing route preference, 2
IP routing route recursion, 2
IPv6 default route configuration, 14
IPv6 static route configuration, 11
IPv6 static routing basic configuration, 12
IPv6 static routing configuration, 11
RIP default route advertisement, 21
RIP ECMP route max number, 24
RIP host route reception disable, 21
RIP poison reverse configuration, 24
RIP preference configuration, 22
RIP received/redistributed route filtering, 22
RIP route control configuration, 19
RIP route entries, 15
RIP route redistribution, 32
RIP route redistribution configuration, 22
RIP split horizon configuration, 24
RIP update source IP address check, 25
RIPng default route advertisement, 40
RIPng ECMP route max, 43
RIPng preference, 41
RIPng received/redistributed route filtering, 40
RIPng route control, 39
RIPng route entry, 37
RIPng route redistribution, 41, 48
RIPng route summarization, 39
RIPv1 message zero field check, 25
RIPv2 summary route advertisement, 20
static routing basic configuration, 7
static routing configuration, 6, 6
static routing default route configuration, 10
routing
IPv6 default route. See under IPv6 static routing
IPv6 static routing. See IPv6 static routing
Routing Information Protocol. Use RIP
S
security
RIPng IPsec profile application, 44
RIPng IPsec profile configuration, 52
sending
RIPng packet send rate, 43
RIPng triggered update send interval, 43
setting
IP routing ECMP route max number, 4
IP routing FIB route max lifetime, 3
IP routing RIB label max lifetime, 3
IP routing RIB route max lifetime, 3
RIP ECMP route max number, 24
RIP packet max length, 28
RIP preference, 22
RIP triggered update interval, 26
RIPng ECMP route max, 43
RIPng preference, 41
RIPng timer, 41
RIPng triggered update send interval, 43
source
RIP source IP address check, 25
specifying
RIP neighbor, 26
split horizon, 24, 24
RIPng configuration, 42
static
routing. See static routing
basic configuration, 7
configuration, 6
default route configuration, 10
display, 7
IPv6. See IPv6 static routing
routing configuration, 6
summarizing
RIPng route summarization, 39
RIPv2 automatic route summarization enable, 20
RIPv2 route summarization configuration, 20
RIPv2 summary route advertisement, 20
suppressing
RIP suppress timer, 23
switch
RIP basic configuration, 29
RIP configuration, 29
RIP GR configuration, 36
RIP interface additional metric configuration, 34
RIP route redistribution, 32
RIPng basic configuration, 46
RIPng configuration, 46
RIPng configuration GR, 51
RIPng IPsec profile configuration, 52
RIPng route redistribution, 48
T
table
IP routing, 1
timeout
RIP timeout timer, 23
timer
RIP garbage-collect timer, 23
RIP suppress timer, 23
RIP timeout timer, 23
RIP update timer, 23
RIPng timer configuration, 41
topology
IPv6 default route configuration, 14
IPv6 static route configuration, 11
IPv6 static routing basic configuration, 12
IPv6 static routing configuration, 11
Track
static routing configuration, 6
triggered RIP
protocols and standards, 16
triggering
RIP triggered update interval, 26
RIPng triggered update send interval, 43
tuning
RIP networks, 23
RIPng network, 41
U
UDP
RIP configuration, 15, 17, 29
RIPng basic configuration, 38, 46
RIPng configuration, 37, 38, 46
RIPng GR configuration, 44
RIPng IPsec profile configuration, 52
RIPng route redistribution, 48
unicast
IP routing configuration, 1
IP routing load sharing, 2
IP routing route backup, 2
IP routing route preference, 2
IP routing route recursion, 2
updating
RIP source IP address check, 25
RIP triggered update interval, 26
RIP update timer, 23
RIPng triggered update send interval, 43
Z
zero field check
RIPng packet, 42
zero field check (RIPv1), 25
