- Table of Contents
-
- H3C S9500 Operation Manual-Release2132[V2.03]-01 Access Volume
- 00-1Cover
- 01-Ethernet Interface Configuration
- 02-POS Interface Configuration
- 03-GVRP Configuration
- 04-Link Aggregation Configuration
- 05-Port Mirroring Configuration
- 06-RPR Configuration
- 07-Ethernet OAM Configuration
- 08-MSTP Configuration
- 09-VLAN Configuration
- 10-QinQ Configuration
- 11-BPDU Tunneling Configuration
- 12-Port Isolation Configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 08-MSTP Configuration | 709.46 KB |
Table of Contents
1.3 Configuring the Root Bridge
1.3.1 Configuring an MST Region
1.3.2 Specifying the Root Bridge or a Secondary Root Bridge
1.3.3 Configuring the Work Mode of MSTP Device
1.3.4 Configuring the Priority of the Current Device
1.3.5 Configuring the Maximum Hops of an MST Region
1.3.6 Configuring the Network Diameter of a Switched Network
1.3.7 Configuring Timers of MSTP
1.3.8 Configuring the Timeout Factor
1.3.9 Configuring the Maximum Transmission Rate of Ports
1.3.10 Configuring Ports as Edge Ports
1.3.11 Configuring Whether Ports Connect to Point-to-Point Links
1.3.12 Configuring the Mode a Port Uses to Recognize/Send MSTP Packets
1.3.13 Enabling the MSTP Feature
1.4.1 Configuring an MST Region
1.4.2 Configuring the Work Mode of MSTP
1.4.3 Configuring the Timeout Factor
1.4.4 Configuring the Maximum Transmission Rate of Ports
1.4.5 Configuring Ports as Edge Ports
1.4.6 Configuring Path Costs of Ports
1.4.7 Configuring Port Priority
1.4.8 Configuring Whether Ports Connect to Point-to-Point Links
1.4.9 Configuring the Mode a Port Uses to Recognize/Send MSTP Packets
1.4.10 Enabling the MSTP Feature
1.6 Configuring the VLAN Ignore Feature
1.6.1 Introduction to the VLAN Ignore Feature
1.7 Configuring Digest Snooping
1.7.1 Configuration Prerequisites
1.8 Configuring No Agreement Check
1.8.1 Configuration Prerequisites
1.9 Configuring Protection Functions
1.9.1 Configuration Prerequisites
1.9.2 Enabling the BPDU Guard Function
1.9.3 Enabling the Root Guard Function
1.9.4 Enabling the Loop Guard Function
1.9.5 Enabling the TC-BPDU Attack Guard Function
1.10 Displaying and Maintaining MSTP
1.11 MSTP Configuration Examples
Chapter 1 MSTP Configuration
When configuring MSTP, go to these sections for information you are interested in:
l Configuring the VLAN Ignore Feature
l Configuring No Agreement Check
l Configuring Protection Functions
l Displaying and Maintaining MSTP
1.1 MSTP Overview
1.1.1 Introduction to STP
I. Functions of STP
The Spanning Tree Protocol (STP) was established based on the 802.1D standard of IEEE to eliminate physical loops at the data link layer in a local area network (LAN). Devices running this protocol detect loops in the network by exchanging information with one another and eliminate loops by selectively blocking certain ports until the loop structure is pruned into a loop-free network structure. This avoids proliferation and infinite recycling of packets that would occur in a loop network and prevents deterioration of device performance caused by duplicate packets received.
In the narrow sense, STP refers to the STP protocol defined in IEEE 802.1d; in the broad sense, it refers to the STP protocol defined in IEEE 802.1d and various enhanced spanning tree protocols derived from the STP protocol.
II. Protocol packets of STP
STP uses bridge protocol data units (BPDUs) for exchanging information. BPDU is also known as configuration packets or configuration messages.
STP identifies the network topology by transmitting BPDUs between STP compliant network devices. BPDUs contain sufficient information for the network devices to complete the spanning tree computing.
In STP, BPDUs come in two types:
l Configuration BPDUs, used to calculate the spanning tree and maintain the spanning tree topology.
l Topology change notification (TCN) BPDUs, used to notify concerned devices of network topology changes, if any.
III. Basic concepts in STP
1) Root bridge
The root of a spanning tree is called the root bridge. In the entire network, there is only one root bridge. Whichever bridge in the network can become the root bridge, depending on the network topology.
Upon network convergence, the root bridge generates and sends out configuration BPDUs at a certain interval and other devices just forward the BPDUs. This mechanism ensures topological stability.
2) Root port
The root port takes charge of communicating with the root bridge. A non-root-bridge device has one and only one root port. The root bridge has no root port.
3) Designated bridge and designated port
Refer to the following table for the description of designated bridge and designated port.
Table 1-1 Description of designated bridge and designated port
|
Classification |
Designated bridge |
Designated port |
|
For a device |
The device directly connected with this device and responsible for forwarding configuration BPDUs |
The port through which the designated bridge forwards configuration BPDUs to this device |
|
For a LAN |
The device responsible for forwarding configuration BPDUs to this LAN segment |
The port through which the designated bridge forwards configuration BPDUs to this LAN segment |

Figure 1-1 A schematic diagram of designated bridges and designated ports
As shown in Figure 1-1, AP1 and AP2, BP1 and BP2, and CP1 and CP2 are ports on Switch A, Switch B, and Switch C.
l If Switch A forwards configuration BPDUs to Switch B through AP1, the designated bridge for Switch B is Switch A, and the designated port is AP1 on Switch A.
l Two Switches are connected to the LAN: Switch B and Switch C. If Switch B forwards configuration BPDUs to the LAN, the designated bridge for the LAN is Switch B, and the designated port is BP2 on Switch B.
& Note:
All the ports on the root bridge are designated ports.
4) Path cost
Path cost is a reference value used for link selection in STP. By calculating the path cost, STP selects relatively “robust” links and blocks redundant links, and finally prunes the network into a loop-free tree structure.
IV. How STP works
STP identifies the network topology by transmitting configuration BPDUs between network devices.
Configuration BPDUs contain sufficient information for network devices to complete the spanning tree computing. A configuration BPDU mainly contains the following information:
l Root bridge ID: formed by root bridge priority and MAC address
l Root path cost
l Designated bridge ID: formed by designated bridge priority and MAC address
l Designated port ID: formed by designated port priority and port name
l Message age: age of the configuration BPDU while it is propagating in the network
l Max age: maximum time that a received configuration BPDU can be maintained on the device
l Hello time: interval to send configuration BPDUs
l Forward delay: state transition delay of the port
1) A simplified STP computing model
& Note:
For the convenience of description, the description and examples below involve only four parts of a configuration BPDU:
l Root bridge ID (in the form of device priority)
l Root path cost
l Designated bridge ID (in the form of device priority)
l Designated port ID (in the form of port ID)
l Initial state
l Selection of the optimum configuration BPDU
Each device sends out its configuration BPDU and receives configuration BPDUs from other devices.
The process of selecting the optimum configuration BPDU is as follows:
Table 1-2 Selection of the optimum configuration BPDU
|
Step |
Description |
|
1 |
Upon receiving a configuration BPDU on a port, the device performs the following processing: l If the received configuration BPDU has a lower priority than that of the configuration BPDU generated by the port, the device will discard the received configuration BPDU without doing any processing on the configuration BPDU of this port. l If the received configuration BPDU has a higher priority than that of the configuration BPDU generated by the port, the device will replace the content of the configuration BPDU generated by the port with the content of the received configuration BPDU. |
|
2 |
The device compares the configuration BPDUs of all the ports and chooses the optimum configuration BPDU. |
& Note:
Rules for configuration BPDU comparison:
l The configuration BPDU that has the lowest root bridge ID has the highest priority.
l For configuration BPDUs with the same root bridge ID, they will be compared by their root path costs. If the root path cost in a configuration BPDU plus the path cost corresponding to this port is S, the configuration BPDU with the smallest S value has the highest priority.
l For configuration BPDUs with the same root bridge ID and the same root path cost, they will be compared by their designated bridge IDs, then their designated port IDs, and then the IDs of the ports through which they are received. The smaller the ID, the higher the message priority.
l Selection of the root bridge
At network initialization, each STP-compliant device on the network assumes itself to be the root bridge, with the root bridge ID being its own device ID. By exchanging configuration BPDUs, the devices compare one another’s root bridge ID. The device with the smallest root bridge ID is elected as the root bridge.
l Selection of the root port and designated ports
The process of selecting the root port and designated ports is as follows:
Table 1-3 Selection of the root port and designated ports
|
Step |
Description |
|
1 |
The root port is the port through which the optimum configuration BPDU was received. |
|
2 |
Based on the configuration BPDU and the path cost of the root port, the device generates a designated port configuration BPDU for each of the rest ports as follows: l Using the root bridge ID of the configuration BPDU of the root port as the root bridge ID. l Using the sum of the root path cost of the configuration BPDU of the root port and the path cost corresponding to the root port as the root path cost. l Using the local device ID as the designated bridge ID. l Using the local port ID as the designated port ID. |
|
3 |
The device compares the calculated configuration BPDU with the configuration BPDU on the port of which the port role is to be defined, and does the following according to the comparison result: l If the calculated configuration BPDU is superior, the device considers this port as the designated port, and replaces the original configuration BPDU with the calculated configuration BPDU. The new configuration BPDU will be sent out periodically. l If the configuration BPDU on the port is superior, the device blocks this port without updating its configuration BPDU. As a result, the port can receive BPDUs, but cannot send BPDUs or forward data. |
& Note:
When the network topology is stable, only the root port and designated ports forward traffic, while other ports are all in the blocked state – they only receive STP packets but do not forward user traffic.
Once the root bridge, the root port on each non-root bridge and designated ports have been successfully elected, the entire tree-shaped topology has been constructed.
The following is an example of how the STP algorithm works. The specific network diagram is shown in Figure 1-2, where the priority of Switch A is 0, the priority of Switch B is 1, the priority of Switch C is 2, and the path costs of the links are 5, 10 and 4.
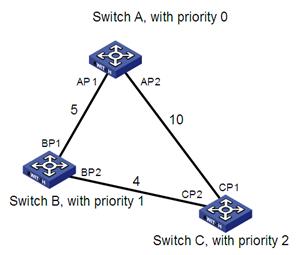
Figure 1-2 Network diagram for STP algorithm
l Initial state of each device
The following table shows the initial state of each device.
Table 1-4 Initial state of each device
|
Device |
Port ID |
BPDU of the port |
|
Switch A |
AP1 |
{0, 0, 0, AP1} |
|
AP2 |
{0, 0, 0, AP2} |
|
|
Switch B |
BP1 |
{1, 0, 1, BP1} |
|
BP2 |
{1, 0, 1, BP2} |
|
|
Switch C |
CP1 |
{2, 0, 2, CP1} |
|
CP2 |
{2, 0, 2, CP2} |
l Comparison process and result on each device
The following table shows the comparison process and result on each device.
Table 1-5 Comparison process and result on each device
|
Device |
Comparison process |
BPDU of the port after comparison |
|
Switch A |
l Port AP1 receives a configuration BPDU from Switch B (that is, {1, 0, 1, BP1}). As the configuration BPDU of the local port (that is, {0, 0, 0, AP1}) is superior to the received configuration BPDU, the received configuration BPDU is discarded. l Port AP2 receives a configuration BPDU from Switch C (that is, {2, 0, 2, CP1}). As the BPDU of the local port (that is, {0, 0, 0, AP2}) is superior to the received configuration BPDU, the received configuration BPDU is discarded. l Switch A finds that both the root bridge and designated bridge in the configuration BPDUs of all its ports are Switch A itself, so it assumes itself to be the root bridge. In this case, it does not make any change to the configuration BPDU of each port, and starts sending out configuration BPDUs periodically. |
AP1: {0, 0, 0, AP1} AP2: {0, 0, 0, AP2} |
|
Switch B |
l Port BP1 receives a configuration BPDU from Switch A (that is, {0, 0, 0, AP1}). As the received configuration BPDU is superior to that of the local port (that is, {1, 0, 1, BP1}), Switch B uses the received configuration BPDU as the configuration BPDU of BP1. l Port BP2 receives a configuration BPDU from Switch C (that is, {2, 0, 2, CP2}). As the configuration BPDU of the local port (that is, {1, 0, 1, BP2}) is superior to the received configuration BPDU, Switch B discards the received configuration BPDU. |
BP1: {0, 0, 0, AP1} BP2: {1, 0, 1, BP2} |
|
l Switch B compares the configuration BPDUs of all its ports, and determines that the configuration BPDU of BP1 is the optimum one. So, BP1 acts as the root port, the configuration BPDUs of which remains unchanged. l Based on the configuration BPDU of BP1 and the path cost of the root port (5), Switch B generates a designated port configuration BPDU for BP2 (that is, {0, 5, 1, BP2}). l Switch B compares the generated configuration BPDU (that is, {0, 5, 1, BP2}) with the configuration BPDU of BP2. As the former is superior, BP2 acts as a designated port, and Switch B sends the generated configuration BPDU through BP2 periodically. |
Root port BP1: {0, 0, 0, AP1} Designated port BP2: {0, 5, 1, BP2} |
|
|
Switch C |
l Port CP1 receives a configuration BPDU from Switch A (that is, {0, 0, 0, AP2}). As the received configuration BPDU is superior to that of the local port (that is, {2, 0, 2, CP1}), Switch C uses the received configuration BPDU as the configuration BPDU of CP1. l Port CP2 receives a configuration BPDU from Switch B (that is, {1, 0, 1, BP2}) before the configuration BPDU is updated on BP2. As the received configuration BPDU is superior to that of the local port (that is, {2, 0, 2, CP2}), Switch C uses the received configuration BPDU as the configuration BPDU of CP2. |
CP1: {0, 0, 0, AP2} CP2: {1, 0, 1, BP2} |
|
By comparison: l The configuration BPDUs of CP1 is the optimum configuration BPDU, so CP1 acts as the root port, the configuration BPDUs of which remains unchanged. l Switch C generates a designated port configuration BPDU (that is, {0, 10, 2, CP2}) and compare it with the configuration BPDU of CP2. As the former is superior, CP2 acts as a designated port and Switch C sends the generated configuration BPDU through CP2 periodically. |
Root port CP1: {0, 0, 0, AP2} Designated port CP2: {0, 10, 2, CP2} |
|
|
l Next, port CP2 receives the updated configuration BPDU of Switch B (that is, {0, 5, 1, BP2}). As the received configuration BPDU is superior to the local one, Switch C launches a BPDU update process. l At the same time, port CP1 receives configuration BPDUs periodically from Switch A. Switch C does not launch an update process after comparison. |
CP1: {0, 0, 0, AP2} CP2: {0, 5, 1, BP2} |
|
|
By comparison: l Because the root path cost of CP2 ( which is 9) is smaller than the root path cost of CP1 (which is 10), the configuration BPDU of CP2 is the optimum BPDU, and CP2 acts as the root port, the configuration BPDUs of which remains unchanged. l After the comparison between the configuration BPDU of CP1 and the generated designated port configuration BPDU, port CP1 is blocked, with the configuration BPDU of the port remaining unchanged, and the port will not receive data from Switch A until a spanning tree computing process is triggered by a new condition, for example, the link between Switch B and Switch C becomes down. |
Blocked port CP1: {0, 0, 0, AP2} Root port CP2: {0, 5, 1, BP2} |
After the comparison processes described in the table above, a spanning tree with Switch A as the root bridge is stabilized, as shown in Figure 1-3.
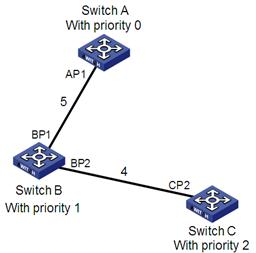
Figure 1-3 A spanning tree with Switch A as the root bridge
& Note:
To facilitate description, the spanning tree computing process in this example is simplified, while the actual process is more complicated.
2) The BPDU forwarding mechanism in STP
l Upon network initiation, every switch regards itself as the root bridge, generates configuration BPDUs with itself as the root, and sends the configuration BPDUs at a regular interval of hello time.
l If it is the root port that received the configuration BPDU and the received configuration BPDU is superior to the configuration BPDU of the port, the device will increase message age carried in the configuration BPDU by a certain rule and start a timer to time the configuration BPDU while it sends out this configuration BPDU through the designated port.
l If the configuration BPDU received on the designated port is inferior to the configuration BPDU of the local port, the port will immediately send out its superior configuration BPDU in response.
l If a path becomes faulty, the root port on this path will no longer receive new configuration BPDUs and the old configuration BPDUs will be discarded due to timeout. In this case, the device will generate a configuration BPDU with itself as the root and send out the BPDU. This triggers a new spanning tree computing process so that a new path is established to restore the network connectivity.
However, the newly computed configuration BPDU will not be propagated throughout the network immediately, so the old root ports and designated ports that have not detected the topology change continue forwarding data through the old path. If the new root port and designated port begin to forward data as soon as they are elected, a temporary loop may occur.
3) STP timers
STP calculation involves three timing parameters: forward delay, hello time, and max age.
l Forward delay is the delay for port state transition. A path failure can cause re-calculation of the spanning tree, and hence topology change. As it takes time for the new configuration BPDU to propagate throughout the network, forwarding data on the root port or designated port immediately upon its selection can cause a temporary loop. To avoid this, STP defines that a newly elected root port or designated port must wait twice the forward delay time before it begins to forward data. The delay ensures that the new configuration BPDU has been propagated throughout the network.
l Hello time is the time interval at which a device sends hello packets to the adjacent devices to ensure that the paths are fault-free.
l Max age determines how long a configuration BPDU can be held by the device. The device discards a configuration BPDU once its age reaches the max age.
1.1.2 Introduction to MSTP
I. Why MSTP
1) Disadvantages of STP and RSTP
STP does not support rapid state transition of ports. A newly elected root port or designated port must wait twice the forward delay time before transitioning to the forwarding state, even if it is a port on a point-to-point link or it is an edge port.
The rapid spanning tree protocol (RSTP) is an optimized version of STP. RSTP allows a newly elected root port or designated port to enter the forwarding state much quicker under certain conditions than in STP. As a result, it takes a shorter time for the network to reach the final topology stability.
& Note:
l In RSTP, a newly elected root port can enter the forwarding state rapidly if this condition is met: The old root port on the device has stopped forwarding data and the upstream designated port has started forwarding data.
l In RSTP, a newly elected designated port can enter the forwarding state rapidly if this condition is met: The designated port is an edge port (a port is an edge port if it is not connected to the other devices directly or indirectly) or a port connected with a point-to-point link. If the designated port is an edge port, it can enter the forwarding state directly; if the designated port is connected with a point-to-point link, it can enter the forwarding state immediately after the device undergoes handshake with the downstream device and gets a response.
Although RSTP support rapid network convergence, it has the same drawback as STP does: All bridges within a LAN share the same spanning tree, so redundant links cannot be blocked based on VLANs, and the packets of all VLANs are forwarded along the same spanning tree.
2) Features of MSTP
The multiple spanning tree protocol (MSTP) overcomes the shortcomings of STP and RSTP. In addition to support for rapid network convergence, it also allows data flows of different VLANs to be forwarded along their own paths, thus providing a better load sharing mechanism for redundant links. For description about VLANs, refer to VLAN Configuration in the Access Volume.
MSTP features the following:
l MSTP maintains a VLAN-to-MSTI mapping table that maps VLANs to MST instances (MSTIs). MSTP can save communication overheads and resource usage by mapping multiple VLANs to one MSTI.
l MSTP divides a switched network into multiple regions, each containing multiple spanning trees that are independent of one another.
l MSTP prunes loop networks into a loop-free tree, thus avoiding proliferation and endless recycling of packets in a loop network. In addition, it provides multiple redundant paths for data forwarding, thus supporting load balancing of VLAN data.
l MSTP is compatible with STP and RSTP.
II. Basic concepts in MSTP
As shown in Figure 1-4, there are four multiple spanning tree (MST) regions, each made up of four switches running MSTP. The following explains some basic MSTP concepts based on this figure.
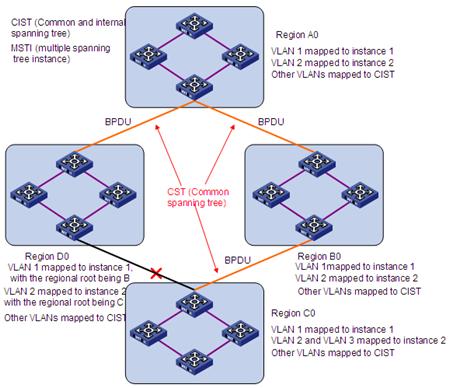
Figure 1-4 Basic concepts in MSTP
1) MST region
An MST region is composed of multiple devices in a switched network and network segments among them. These devices have the following characteristics:
l All are MSTP-enabled.
l They have the same region name.
l They have the same VLAN-to-MSTI mapping configuration.
l They have the same MSTP revision level configuration.
l They are physically linked with one another.
In area A0 in Figure 1-4, for example, all devices have the same MST region configuration:
l The same region name.
l The same VLAN-to-MSTI mapping (VLAN 1 is mapped to MSTI 1, VLAN 2 to MSTI 2, and the rest to the common and internal spanning tree (CIST), that is, MSTI 0).
l The same MSTP revision level (not shown in the figure).
& Note:
Multiple MST regions can exist in a switched network. You can use an MSTP command to group multiple devices to the same MST region.
2) VLAN-to-MSTI mapping table
As an attribute of an MST region, the VLAN-to-MSTI mapping table describes the mapping relationships between VLANs and MSTIs. In Figure 1-4, for example, the VLAN-to-MSTI mapping table of region A0 describes that the same region name, the same VLAN-to-MSTI mapping (VLAN 1 is mapped to MSTI 1, VLAN 2 to MSTI 2, and the rest to CIST.
3) IST
Internal spanning tree (IST) is a spanning tree that runs in an MST region. ISTs in all MST regions and the common spanning tree (CST) jointly constitute the common and internal spanning tree (CIST) of the entire network. An IST is a section of the CIST in an MST region. In Figure 1-4, for example, the CIST has a section in each MST region, and this section is the IST in each MST region.
4) CST
The CST is a single spanning tree that connects all MST regions in a switched network. If you regard each MST region as a “device”, the CST is a spanning tree computed by these devices through STP or RSTP. The red lines in Figure 1-4 describe the CST.
5) CIST
Jointly constituted by ISTs and the CST, the CIST is a single spanning tree that connects all devices in a switched network. In Figure 1-4, for example, the ISTs in all MST regions plus the inter-MST-region CST constitute the CIST of the entire network.
6) MSTI
Multiple spanning trees can be generated in an MST region through MSTP, one spanning tree being independent of another. Each spanning tree is referred to as a multiple spanning tree instance (MSTI). In Figure 1-4, for example, multiple spanning tree can exist in each MST region, each spanning tree corresponding to a VLAN. These spanning trees are called MSTIs.
7) Regional root bridge
The root bridge of the IST or an MSTI within an MST region is the regional root bridge of the MST or that MSTI. Based on the topology, different spanning trees in an MST region may have different regional roots. For example, in region D0 in Figure 1-4, the regional root of instance 1 is device B, while that of instance 2 is device C.
8) Common root bridge
The common root bridge is the root bridge of the CIST.
In Figure 1-4, for example, the common root bridge is a device in region A0.
9) Boundary port
A boundary port is a port that connects an MST region to another MST configuration, or to a single spanning-tree region running STP, or to a single spanning-tree region running RSTP.
During MSTP computing, a boundary port assumes the same role on the CIST and on MSTIs. Namely, if a boundary port is master port on the CIST, it is also the master port on all MSTIs within this region. In Figure 1-4, for example, if a device in region A0 is interconnected with the first port of a device in region D0 and the common root bridge of the entire switched network is located in region A0, the first port of that device in region D0 is the boundary port of region D0.
& Note:
Currently, the S9500 series routing switches are not capable of recognizing boundary ports. When an S9500 series routing switch is connected to a third party’s device that supports boundary port recognition, the third party’s device may malfunction in recognizing a boundary port.
10) Roles of ports
MSTP calculation involves these port roles: root port, designated port, master port, alternate port, and backup port.
l Root port: a port responsible for forwarding data to the root bridge.
l Designated port: a port responsible for forwarding data to the downstream network segment or device.
l Master port: A port on the shortest path from the entire region to the common root bridge, connecting the MST region to the common root bridge.
l Alternate port: The standby port for the root port or master port. When the root port or master port is blocked, the alternate port becomes the new root port or master port.
l Backup port: The backup port of designated ports. When a designated port is blocked, the backup port becomes the new designated port and starts forwarding data without delay. When a loop occurs while two ports of the same MSTP device are interconnected, the device blocks either of the two ports, whichever is the backup port.
A port can assume different roles in different MSTIs.

In Figure 1-5,
l Devices A, B, C, and D constitute an MST region.
l Port 1 and port 2 of device A connect to the common root bridge.
l Port 5 and port 6 of device C form a loop.
l Port 3 and port 4 of device D connect downstream to other MST regions.
11) Port states
In MSTP, port states fall into the following tree:
l Forwarding: the port learns MAC addresses and forwards user traffic;
l Learning: the port learns MAC addresses but does not forwards user traffic;
l Discarding: the port neither learns MAC addresses nor forwards user traffic.
& Note:
When in different MSTIs, a port can be in different states.
A port state is not exclusively associated with a port role. Table 1-6 lists the port state(s) supported by each port role (“√” indicates that the port supports this state, while “-“ indicates that the port does not support this state).
Table 1-6 Ports states supported by different port roles
|
Role State |
Root port/Master port |
Designated port |
Alternate port |
Backup port |
|
Forwarding |
√ |
√ |
— |
— |
|
Learning |
√ |
√ |
— |
— |
|
Discarding |
√ |
√ |
√ |
√ |
III. How MSTP works
MSTP divides an entire Layer 2 network into multiple MST regions, which are interconnected by a computed CST. Inside an MST region, multiple spanning trees are generated through computing, each spanning tree called an MSTI. Among these MSTIs, instance 0 is the IST, while all the others are MSTIs. Similar to STP, MSTP uses configuration BPDUs to compute spanning trees. The only difference between the two protocols being in that what is carried in an MSTP BPDU is the MSTP configuration on the device from which this BPDU is sent.
1) CIST calculation
By comparison of configuration BPDUs, one device with the highest priority is elected as the root bridge of the CIST. MSTP generates an IST within each MST region through computing, and, at the same time, MSTP regards each MST region as a single device and generates a CST among these MST regions through computing. The CST and ISTs constitute the CIST of the entire network.
2) MSTI calculation
Within an MST region, MSTP generates different MSTIs for different VLANs based on the VLAN-to-MSTI mappings.
MSTP performs a separate computing process, which is similar to spanning tree computing in STP, for each spanning tree. For details, refer to How STP works in section 1.1.1.
In MSTP, a VLAN packet is forwarded along the following paths:
l Within an MST region, the packet is forwarded along the corresponding MSTI.
l Between two MST regions, the packet is forwarded along the CST.
IV. Implementation of MSTP on devices
MSTP is compatible with STP and RSTP. STP and RSTP protocol packets can be recognized by devices running MSTP and used for spanning tree computing.
In addition to basic MSTP functions, many management-facilitating special functions are provided, as follows:
l Root bridge hold
l Root bridge backup
l Root guard
l BPDU guard
l TC-BPDU guard
l Support for hot swapping of interface cards and active/standby changeover.
1.1.3 Protocols and Standards
MSTP is documented in:
l IEEE 802.1D: Spanning Tree Protocol
l IEEE 802.1w: Rapid Spanning Tree Protocol
l IEEE 802.1s: Multiple Spanning Tree Protocol
1.2 Configuration Task List
Before configuration, you need to know the position of each device in each MSTI: root bridge or leave node. In each instance, one, and only one device acts as the root bridge, while all others as leaf nodes.
|
Task |
Remarks |
|
|
Required |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Configuring the Mode a Port Uses to Recognize/Send MSTP Packets |
Optional |
|
|
Required |
||
|
Required |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Configuring the Mode a Port Uses to Recognize/Send MSTP Packets |
Optional |
|
|
Required |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
& Note:
If both GVRP and MSTP are enabled on a device at the same time, GVRP packets will be forwarded along the CIST. Therefore, if both GVRP and MSTP are running on the same device and you wish to advertise a certain VLAN within the network through GVRP, make sure that this VLAN is mapped to the CIST (instance 0) when configuring the VLAN-to-MSTI mapping table. For detailed information of GVRP, refer to GVRP Configuration of the Access Volume.
1.3 Configuring the Root Bridge
1.3.1 Configuring an MST Region
I. Configuration procedure
Follow these steps to configure an MST region:
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Enter MST region view |
stp region-configuration |
— |
|
Configure the MST region name |
region-name name |
Optional By default, the name of an MST region is the bridge MAC address. |
|
Configure the VLAN-to-MSTI mapping table |
instance instance-id vlan vlan-list |
Optional Use either command. By default, all VLANs in an MST region are mapped to MSTI 0. |
|
vlan-mapping modulo modulo |
||
|
Configure the MSTP revision level of the MST region |
revision-level level |
Optional 0 by default |
|
Activate MST region configuration manually |
active region-configuration |
Required |
|
Display the configuration of the current MST region |
check region-configuration |
Optional |
|
Display the currently effective MST region configuration information |
display stp region-configuration |
Optional Available in any view |
Two or multiple devices belong to the same MST region only when they are configured to have the same MST region name, the same VLAN-to-MSTI mapping entries in the MST region and the same MST region revision level, and they are interconnected via a physical link.
The configuration of MST region–related parameters, especially the VLAN-to-MSTI mapping table, will cause MSTP to launch a new spanning tree computing process, which may result in network topology instability. To reduce the possibility of topology instability caused by configuration, MSTP will not immediately launch a new spanning tree computing process when processing MST region–related configurations; instead, such configurations will take effect only if you:
l activate the MST region–related parameters suing the active region-configuration command, or
l enable MSTP using the stp enable command.
II. Configuration example
# Configure the MST region name to be info, the MSTP revision level to be 1, and VLAN 2 through VLAN 10 to be mapped to instance 1, and VLAN 20 through VLAN 30 to instance 2.
<Sysname> system-view
[Sysname] stp region-configuration
[Sysname-mst-region] region-name info
[Sysname-mst-region] instance 1 vlan 2 to 10
[Sysname-mst-region] instance 2 vlan 20 to 30
[Sysname-mst-region] revision-level 1
[Sysname-mst-region] active region-configuration
1.3.2 Specifying the Root Bridge or a Secondary Root Bridge
MSTP can determine the root bridge of a spanning tree through MSTP computing. Alternatively, you can specify the current device as the root bridge using the commands provided by the system.
I. Specifying the current device as the root bridge of a specific spanning tree
Follow these steps to specify the current device as the root bridge of a specific spanning tree:
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Specify the current device as the root bridge of a specific spanning tree |
stp [ instance instance-id ] root primary [ bridge-diameter bridgenum [ hello-time centi-seconds ] ] |
Required The device does not function as the root bridge by default. |
II. Specifying the current device as a secondary root bridge of a specific spanning tree
Follow these steps to specify the current device as a secondary root bridge of a specific spanning tree:
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Specify the current device as a secondary root bridge of a specific spanning tree |
stp [ instance instance-id ] root secondary [ bridge-diameter bridgenum [ hello-time centi-seconds ] ] |
Required By default, a device does not function as a secondary root bridge. |
Note that:
l Upon specifying the current device as the root bridge or a secondary root bridge, you cannot change the priority of the device.
l You can configure the current device as the root bridge or a secondary root bridge of an MSTI, which is specified by instance instance-id in the command. If you set instance-id to 0, the current device will be the root bridge or a secondary root bridge of the CIST.
l The current device has independent roles in different instances. It can act as the root bridge or a secondary root bridge of one instance while it can also act as the root bridge or a secondary root bridge of another instance. However, the same device cannot be the root bridge and a secondary root bridge in the same instance at the same time.
l There is one and only one root bridge in effect in a spanning tree instance. If two or more devices have been designated to be root bridges of the same spanning tree instance, MSTP will select the device with the lowest MAC address as the root bridge.
l You can specify multiple secondary root bridges for the same instance. Namely, you can specify secondary root bridges for the same instance on two or more than two device.
l When the root bridge of an instance fails or is shut down, the secondary root bridge (if you have specified one) can take over the role of the instance. However, if you specify a new root bridge for the instance at this time, the secondary root bridge will not become the root bridge. If you have specified multiple secondary root bridges for an instance, when the root bridge fails, MSTP will select the secondary root bridge with the lowest MAC address as the new root bridge.
l When specifying the root bridge or a secondary root bridge, you can specify the network diameter and hello time. However, these two options are effective only for MSTI 0, namely the CIST. If you include these two options in your command for any other instance, the configuration can succeed, but they will not actually work. For the description of network diameter and hello time, refer to Configuring the Network Diameter of a Switched Network and Configuring Timers of MSTP.
l Alternatively, you can also specify the current device as the root bridge by setting by priority of the device to 0. For the device priority configuration, refer to Configuring the Priority of the Current Device.
III. Configuration example
# Specify the current device as the root bridge of MSTI 1 and a secondary root bridge of MSTI 2.
<Sysname> system-view
[Sysname] stp instance 1 root primary
[Sysname] stp instance 2 root secondary
1.3.3 Configuring the Work Mode of MSTP Device
MSTP and RSTP can recognize each other’s protocol packets, so they are mutually compatible. However, STP is unable to recognize MSTP packets. For hybrid networking with legacy STP devices and full interoperability with RSTP-compliant devices, MSTP supports three work modes: STP-compatible mode, RSTP mode, and MSTP mode.
l In STP-compatible mode, all ports of the device send out STP BPDUs,
l In RSTP mode, all ports of the device send out RSTP BPDUs. If the device detects that it is connected with a legacy STP device, the port connecting with the legacy STP device will automatically migrate to STP-compatible mode.
l In MSTP mode, all ports of the device send out MSTP BPDUs. If the device detects that it is connected with a legacy STP device, the port connecting with the legacy STP device will automatically migrate to STP-compatible mode.
I. Configuration procedure
Follow these steps to configure the MSTP work mode:
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Configure the work mode of MSTP |
stp mode { stp | rstp | mstp } |
Optional MSTP mode by default |
II. Configuration example
# Configure MSTP to work in STP-compatible mode.
<Sysname> system-view
[Sysname] stp mode stp
# Configure MSTP to work in RSTP mode.
<Sysname> system-view
[Sysname] stp mode rstp
1.3.4 Configuring the Priority of the Current Device
The priority of a device determines whether it can be elected as the root bridge of a spanning tree. A lower value indicates a higher priority. By setting the priority of a device to a low value, you can specify the device as the root bridge of spanning tree. An MSTP-compliant device can have different priorities in different MSTIs.
I. Configuration procedure
Follow these steps to configure the priority of the current device:
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Configure the priority of the current device |
stp [ instance instance-id ] priority priority |
Optional 32768 by default |
![]() Caution:
Caution:
l Upon specifying the current device as the root bridge or a secondary root bridge, you cannot configure the priority of the device.
l During root bridge selection, if all devices in a spanning tree have the same priority, the one with the lowest MAC address will be selected as the root bridge of the spanning tree.
II. Configuration example
# Set the device priority in MSTI 1 to 4096.
<Sysname> system-view
[Sysname] stp instance 1 priority 4096
1.3.5 Configuring the Maximum Hops of an MST Region
By setting the maximum hops of an MST region, you can restrict the region size. The maximum hops setting configured on the regional root bridge will be used as the maximum number of hops of the MST region.
The regional root bridge always sends a configuration BPDU with a hop count set to the maximum value. When a switch receives this configuration BPDU, it decrements the hop count by 1 and uses the new hop count as the remaining hop count in the forwarded BPDU. If the hop count of the BPDU reaches 0 at a device, the receiving device discards the BPDU. As devices beyond the reach of the maximum hop are unable to take part in spanning tree calculation, the size of the MST region is confined.
When a device becomes the root bridge of the CIST or MSTI of an MST region, the maximum hop in the configuration BPDUs generated by this device defines the network diameter of the spanning tree to define how far the spanning tree can reach in this MST region. All the devices other than the root bridge in the MST region use the maximum hop value set for the root bridge.
I. Configuration procedure
Follow these steps to configure the maximum hops of the MST region
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Configure the maximum hops of the MST region |
stp max-hops hops |
Optional 20 by default |
& Note:
A larger maximum hops setting means a larger size of the MST region. Only the maximum hops configured on the regional root bridge can restrict the size of the MST region.
II. Configuration example
# Set the maximum hops of the MST region to 30.
<Sysname> system-view
[Sysname] stp max-hops 30
1.3.6 Configuring the Network Diameter of a Switched Network
Any two stations in a switched network are interconnected through specific paths, which are composed of a series of devices. Represented by the number of devices on a path, the network diameter is the path that comprises more devices than any other among these paths.
I. Configuration procedure
Follow these steps to configure the network diameter of the switched network:
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Configure the network diameter of the switched network |
stp bridge-diameter bridgenum |
Optional 7 by default |
& Note:
l Network diameter is a parameter that indicates network size. A bigger network diameter represents a larger network size.
l Based on the network diameter you configured, MSTP automatically sets an optimal hello time, forward delay, and max age for the device.
l The configured network diameter is effective for the CIST only, and not for MSTIs.
II. Configuration example
# Set the network diameter of the switched network to 6.
<Sysname> system-view
[Sysname] stp bridge-diameter 6
1.3.7 Configuring Timers of MSTP
MSTP involves three timers: forward delay, hello time and max age. You can configure these three parameters for MSTP to calculate spanning trees.
I. Configuration procedure
Follow these steps to configure the timers of MSTP:
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Configure the forward delay timer |
stp timer forward-delay centi-seconds |
Optional 1,500 centiseconds (15 seconds) by default |
|
Configure the hello time timer |
stp timer hello centi-seconds |
Optional 200 centiseconds (2 seconds) by default |
|
Configuring the max age timer |
stp timer max-age centi-seconds |
Optional 2,000 centiseconds (20 seconds) by default |
These three timers set on the root bridge of the CIST apply on all the devices on the entire switched network.
![]() Caution:
Caution:
l The length of the forward delay time is related to the network diameter of the switched network. Typically, the larger the network diameter is, the longer the forward delay time should be. Note that if the forward delay setting is too small, temporary redundant paths may be introduced; if the forward delay setting is too big, it may take a long time for the network to resume connectivity. We recommend that you use the default setting.
l An appropriate hello time setting enables the device to timely detect link failures on the network without using excessive network resources. If the hello time is set too long, the device will take packet loss on a link for link failure and trigger a new spanning tree computing process; if the hello time is set too short, the device will send repeated configuration BPDUs frequently, which adds to the device burden and causes waste of network resources. We recommend that you use the default setting.
l If the max age time setting is too small, the network devices will frequently launch spanning tree computing and may take network congestion to a link failure; if the max age setting is too large, the network may fail to timely detect link failures and fail to timely launch spanning tree computing, thus reducing the auto-sensing capability of the network. We recommend that you use the default setting.
The setting of hello time, forward delay and max age must meet the following formulae; otherwise network instability will frequently occur.
l 2 × (forward delay – 1 second) ¦ max age
l Ma x age ¦ 2 × (hello time + 1 second)
We recommend that you specify the network diameter and the hello time using the stp bridge-diameter command by preference and let MSTP automatically calculate an optimal setting of the other two timers.
II. Configuration example
# Set the forward delay to 1,600 centiseconds, hello time to 300 centiseconds, and max age to 2,100 centiseconds.
<Sysname> system-view
[Sysname] stp timer forward-delay 1600
[Sysname] stp timer hello 300
[Sysname] stp timer max-age 2100
1.3.8 Configuring the Timeout Factor
After the network topology becomes stabilized, each non-root-bridge device forwards configuration BPDUs to the adjacent devices at the interval of hello time to check for faulty links. Typically, if a device does not receive a BPDU from the upstream device within nine times the hello time, it assumes that the upstream device has failed and starts spanning tree calculation.
In a stable network, you can avoid such unwanted spanning tree calculation by lengthening the timeout time.
I. Configuration procedure
Follow these steps to configure the timeout factor:
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Configure the timeout factor of the device |
stp timer-factor number |
Optional 3 by default |
& Note:
l Timeout time = timeout factor × hello time.
l Typically, we recommend that you set the timeout factor to 5, 6, or 7 for a stable network.
II. Configuration example
# Set the timeout factor to 6.
<Sysname> system-view
[Sysname] stp timer-factor 6
1.3.9 Configuring the Maximum Transmission Rate of Ports
The maximum transmission rate of a port refers to the maximum number of MSTP packets that the port can send within each hello time.
The maximum transmission rate of an Ethernet port is related to the physical status of the port and the network structure.
I. Configuration procedure
Following these steps to configure the maximum transmission rate of a port or a group of ports:
|
To do... |
Use the command... |
Remarks |
|
|
Enter system view |
system-view |
— |
|
|
Enter Ethernet interface view or port group view |
Enter Ethernet interface view |
interface interface-type interface-number |
User either command Configured in Ethernet interface view, the setting is effective on the current port only; configured in port group view, the setting is effective on all ports in the port group |
|
Enter port group view |
port-group { manual port-group-name | aggregation agg-id } |
||
|
Configure the maximum transmission rate of the port(s) |
stp transmit-limit packet-number |
Optional 10 by default |
|
& Note:
If the maximum transmission rate setting of a port is too big, the port will send a large number of MSTP packets within each hello time, thus using excessive network resources. We recommend that you use the default setting.
II. Configuration example
# Set the maximum transmission rate of port Ethernet 1/1/1 to 5.
<Sysname> system-view
[Sysname] interface ethernet 1/1/1
[Sysname-Ethernet1/1/1] stp transmit-limit 5
1.3.10 Configuring Ports as Edge Ports
If a port directly connects to a user terminal rather than another device or a shared LAN segment, this port is regarded as an edge port. When a network topology change occurs, an edge port will not cause a temporary loop. Therefore, if you specify a port as an edge port, this port can transition rapidly from the blocked state to the forwarding state without delay.
I. Configuration procedure
Following these steps to specify a port or a group of ports as edge port(s):
|
To do... |
Use the command... |
Remarks |
|
|
Enter system view |
system-view |
— |
|
|
Enter Ethernet interface view or port group view |
Enter Ethernet interface view |
interface interface-type interface-number |
User either command Configured in Ethernet interface view, the setting is effective on the current port only; configured in port group view, the setting is effective on all ports in the port group |
|
Enter port group view |
port-group { manual port-group-name | aggregation agg-id } |
||
|
Configure the port(s) as edge port(s) |
stp edged-port enable |
Required All Ethernet ports are non-edge ports by default |
|
& Note:
l With BPDU guard disabled, when a port set as an edge port receives a BPDU from another port, it will become a non-edge port again.
l If a port directly connects to a user terminal, configure it to be an edge port and enable BPDU guard for it. This enables the port to transition to the forwarding state while ensuring network security.
II. Configuration example
# Configure Ethernet 1/1/1 to be an edge port.
<Sysname> system-view
[Sysname] interface ethernet 1/1/1
[Sysname-Ethernet1/1/1] stp edged-port enable
1.3.11 Configuring Whether Ports Connect to Point-to-Point Links
A point-to-point link is a link directly connecting with two devices. If the roles of two ports directly connected by a point-to-point link meet specific requirements, the ports can rapidly transition to the forwarding state after a proposal-agreement handshake process.
I. Configuration procedure
Following these steps to configure whether a port or a group of ports connect to point-to-point links:
|
To do... |
Use the command... |
Remarks |
|
|
Enter system view |
system-view |
— |
|
|
Enter Ethernet interface view or port group view |
Enter Ethernet interface view |
interface interface-type interface-number |
User either command Configured in Ethernet interface view, the setting is effective on the current port only; configured in port group view, the setting is effective on all ports in the port group |
|
Enter port group view |
port-group { manual port-group-name | aggregation agg-id } |
||
|
Configure whether the port(s) connect to point-to-point links |
stp point-to-point { force-true | force-false | auto } |
Optional The default setting is auto; namely the device automatically detects whether an Ethernet port connects to a point-to-point link |
|
& Note:
l As for aggregated ports, all ports can be configured as connecting to point-to-point links. If a port works in auto-negotiation mode and the negotiation result is full duplex, this port can be configured as connecting to a point-to-point link.
l If a port is configured as connecting to a point-to-point link, the setting takes effect for the port in all MSTIs. If the physical link to which the port connects is not a point-to-point link and you force it to be a point-to-point link by configuration, the configuration may incur a temporary loop.
II. Configuration example
# Configure port Ethernet 1/1/1 as connecting to a point-to-point link.
<Sysname> system-view
[Sysname] interface ethernet 1/1/1
[Sysname-Ethernet1/1/1] stp point-to-point force-true
1.3.12 Configuring the Mode a Port Uses to Recognize/Send MSTP Packets
A port can send/recognize MSTP packets in two formats:
l 802.1s-compliant standard format
l Compatible format
By default, the packet format recognition mode of a port is auto. In auto mode, the port automatically distinguishes the two MSTP packet formats, and sends packets in the format the same as that of received MSTP packets. You can configure the MSTP packet format to be used by a port. After the configuration, when working in MSTP mode, the port sends and receives only MSTP packets in the configured format to communicate with devices that adopt the same format.
I. Configuration procedure
Follow these steps to configure the MSTP packet format that a port or a group of ports can recognize:
|
To do... |
Use the command... |
Remarks |
|
|
Enter system view |
system-view |
— |
|
|
Enter Ethernet interface view or port group view |
Enter Ethernet interface view |
interface interface-type interface-number |
User either command Configured in Ethernet interface view, the setting is effective on the current port only; configured in port group view, the setting is effective on all ports in the port group |
|
Enter port group view |
port-group { manual port-group-name | aggregation agg-id } |
||
|
Configure the mode the port uses to recognize/send MSTP packets |
stp compliance { auto | dot1s | legacy } |
Optional auto by default |
|
& Note:
l In MSTP mode, if a port is configured to recognize/send MSTP packets in a mode other than auto, and if it receives a packet in the format other than as configured, that port will become a designated port, and the port will remain in the discarding state to prevent the occurrence of a loop.
l If a port receives MSTP packets of different formats frequently, this means that the MSTP packet formation configuration contains error. In this case, if the port is working in MSTP mode, it will be shut down for protection.
II. Configuration example
# Configure Ethernet 1/0 to receive and send standard-format MSTP packets.
<Sysname> system-view
[Sysname] interface ethernet 1/1/1
[Sysname-Ethernet1/1/1] stp compliance dot1s
1.3.13 Enabling the MSTP Feature
I. Configuration procedure
Follow these steps to enable the MSTP feature:
|
To do... |
Use the command... |
Remarks |
|
|
Enter system view |
system-view |
— |
|
|
Enable the MSTP feature for the device |
stp enable |
Optional By default, the MSTP feature is enabled globally. |
|
|
Enter Ethernet interface view or port group view |
Enter Ethernet interface view |
interface interface-type interface-number |
User either command Configured in Ethernet interface view, the setting is effective on the current port only; configured in port group view, the setting is effective on all ports in the port group |
|
Enter port group view |
port-group { manual port-group-name | aggregation agg-id } |
||
|
Enable the MSTP feature for the port(s) |
stp enable |
Optional By default, MSTP is enabled for all ports after it is enabled for the device globally |
|
& Note:
l You must enable MSTP for the device before any other MSTP-related configuration can take effect.
l To control MSTP flexibly, you can use the stp disable or undo stp command to disable the MSTP feature for specific ports so that they will not take part in spanning tree computing and thus to save the device’s CPU resources.
II. Configuration example
# Enable MSTP for the device and disable MSTP for port Ethernet 1/1/1.
<Sysname> system-view
[Sysname] stp enable
[Sysname] interface ethernet 1/1/1
[Sysname-Ethernet1/1/1] stp disable
1.4 Configuring Leaf Nodes
Perform the following configurations for a device operating as a leaf node.
1.4.1 Configuring an MST Region
Refer to section Configuring an MST Region.
1.4.2 Configuring the Work Mode of MSTP
Refer to section Configuring the Work Mode of MSTP Device.
1.4.3 Configuring the Timeout Factor
Refer to section Configuring the Timeout Factor.
1.4.4 Configuring the Maximum Transmission Rate of Ports
Refer to section Configuring the Maximum Transmission Rate of Ports.
1.4.5 Configuring Ports as Edge Ports
Refer to section Configuring Ports as Edge Ports.
1.4.6 Configuring Path Costs of Ports
Path cost is a parameter related to the rate of port-connected links. On an MSTP-compliant device, ports can have different priorities in different MSTIs. Setting an appropriate path cost allows VLAN traffic flows to be forwarded along different physical links, thus to enable per-VLAN load balancing.
The device can automatically calculate the path cost; alternatively, you can also configure the path cost for ports.
I. Specifying a standard that the device uses when calculating the path cost
You can specify a standard for the device to use in automatic calculation for the path cost. The device supports the following standards:
l dot1d-1998: The device calculates the default path cost for ports based on IEEE 802.1D-1998.
l dot1t: The device calculates the default path cost for ports based on IEEE 802.1t.
l legacy: The device calculates the default path cost for ports based on a private standard.
Follow these steps to specify a standard for the device to use when calculating the default path cost:
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Specify a standard for the device to use when calculating the default path cost of the link connected with the device |
stp pathcost-standard { dot1d-1998 | dot1t | legacy } |
Optional The device uses the private standard by default. |
Table 1-7 Link speed vs. path cost
|
Link speed |
Duplex state |
802.1D-1998 |
802.1t |
Private standard |
|
0 |
— |
65535 |
200,000,000 |
200,000 |
|
10 Mbps |
Single Port Aggregated Link 2 Ports Aggregated Link 3 Ports Aggregated Link 4 Ports |
100 100 100 100 |
2,000,000 1,000,000 666,666 500,000 |
2,000 1,800 1,600 1,400 |
|
100 Mbps |
Single Port Aggregated Link 2 Ports Aggregated Link 3 Ports Aggregated Link 4 Ports |
19 19 19 19 |
200,000 100,000 66,666 50,000 |
200 180 160 140 |
|
1000 Mbps |
Single Port Aggregated Link 2 Ports Aggregated Link 3 Ports Aggregated Link 4 Ports |
4 4 4 4 |
20,000 10,000 6,666 5,000 |
20 18 16 14 |
|
10 Gbps |
Single Port Aggregated Link 2 Ports Aggregated Link 3 Ports Aggregated Link 4 Ports |
2 2 2 2 |
2,000 1,000 666 500 |
2 1 1 1 |
& Note:
In the calculation of the path cost value of an aggregated link, 802.1D-1998 does not take into account the number of ports in the aggregated link. Whereas, 802.1T takes the number of ports in the aggregated link into account. The calculation formula is: Path Cost = 200,000,000/link speed (in 100 kbps), where link speed is the sum of the link speed values of the non-blocked ports in the aggregated link.
II. Configuring Path Costs of Ports
Follow these steps to configure the path cost of ports:
|
To do... |
Use the command... |
Remarks |
|
|
Enter system view |
system-view |
— |
|
|
Enter Ethernet interface view or port group view |
Enter Ethernet interface view |
interface interface-type interface-number |
User either command Configured in Ethernet interface view, the setting is effective on the current port only; configured in port group view, the setting is effective on all ports in the port group |
|
Enter port group view |
port-group { manual port-group-name | aggregation agg-id } |
||
|
Configure the path cost of the port(s) |
stp [ instance instance-id ] cost cost |
Optional By default, MSTP automatically calculates the path cost of each port |
|
& Note:
l When the path cost of a port is changed, MSTP will re-compute the role of the port and initiate a state transition. If you use 0 as instance-id, you are setting the path cost of the CIST.
l If you change the standard that the device uses in calculating the default path cost, the port path cost value set through the stp cost command will be out of effect.
III. Configuration example I
# Configure the path cost of Ethernet 1/1/1 in MSTI 1 to 2000.
<Sysname> system-view
[Sysname] interface ethernet 1/1/1
[Sysname-Ethernet1/1/1] stp instance 1 cost 2000
IV. Configuration example II
# Configure MSTP to automatically calculate the path cost of Ethernet 1/1/1 based on the IEEE 802.1D-1998 standard.
<Sysname> system-view
[Sysname] interface ethernet 1/1/1
[Sysname-Ethernet1/1/1] undo stp instance 1 cost
[Sysname-Ethernet1/1/1] quit
[Sysname] stp pathcost-standard dot1d-1998
1.4.7 Configuring Port Priority
The priority of a port is an import basis that determines whether the port can be elected as the root port of device. If all other conditions are the same, the port with the highest priority will be elected as the root port.
On an MSTP-compliant device, a port can have different priorities in different MSTIs, and the same port can play different roles in different MSTIs, so that data of different VLANs can be propagated along different physical paths, thus implementing per-VLAN load balancing. You can set port priority values based on the actual networking requirements.
I. Configuration procedure
Follow these steps to configure the priority of a port or a group of ports:
|
To do... |
Use the command... |
Remarks |
|
|
Enter system view |
system-view |
— |
|
|
Enter Ethernet interface view or port group view |
Enter Ethernet interface view |
interface interface-type interface-number |
User either command Configured in Ethernet interface view, the setting is effective on the current port only; configured in port group view, the setting is effective on all ports in the port group |
|
Enter port group view |
port-group { manual port-group-name | aggregation agg-id } |
||
|
Configure port priority |
stp [ instance instance-id ] port priority priority |
Optional 128 for all Ethernet ports by default |
|
& Note:
l When the priority of a port is changed, MSTP will re-compute the role of the port and initiate a state transition.
l Generally, a lower configured value priority indicates a higher priority of the port. If you configure the same priority value for all the Ethernet ports on the a device, the specific priority of a port depends on the index number of that port. Changing the priority of an Ethernet port triggers a new spanning tree computing process.
II. Configuration example
# Set the priority of port Ethernet 1/1/1 to 16 in MSTI 1.
<Sysname> system-view
[Sysname] interface ethernet 1/1/1
[Sysname-Ethernet1/1/1] stp instance 1 port priority 16
1.4.8 Configuring Whether Ports Connect to Point-to-Point Links
Refer to Configuring Whether Ports Connect to Point-to-Point Links.
1.4.9 Configuring the Mode a Port Uses to Recognize/Send MSTP Packets
Refer to section Configuring the Mode a Port Uses to Recognize/Send MSTP Packets.
1.4.10 Enabling the MSTP Feature
Refer to Enabling the MSTP Feature.
1.5 Performing mCheck
Ports on an MSTP-compliant device have three working modes: STP compatible mode, RSTP mode, and MSTP mode.
In a switched network, if a port on the device running MSTP (or RSTP) connects to a device running STP, this port will automatically migrate to the STP-compatible mode. However, if the device running STP is removed, this will not be able to migrate automatically to the MSTP (or RSTP) mode, but will remain working in the STP-compatible mode. In this case, you can perform an mCheck operation to force the port to migrate to the MSTP (or RSTP) mode.
You can perform mCheck on a port through two approaches, which lead to the same result.
I. Configuration prerequisites
l MSTP has been correctly configured on the device.
l MSTP has been configured to operate in MSTP mode or RSTP-compatible mode.
II. Perform global mCheck
Follow these steps to perform global mCheck:
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Perform mCheck |
stp mcheck |
Required |
III. Perform mCheck in Ethernet interface view
Follow these steps to perform mCheck in Ethernet interface view:
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Enter Ethernet interface view |
interface interface-type interface-number |
— |
|
Perform mCheck |
stp mcheck |
Required |
![]() Caution:
Caution:
The stp mcheck command is meaningful only when MSTP is configured to operate in MSTP mode or RSTP-compatible mode, not in the STP-compatible mode.
IV. Configuration example
# Perform mCheck on port Ethernet 1/1/1.
1) Perform mCheck globally
<Sysname> system-view
[Sysname] stp mcheck
2) Perform mCheck in Ethernet interface view
<Sysname> system-view
[Sysname] interface ethernet 1/1/1
[Sysname-Ethernet1/1/1] stp mcheck
1.6 Configuring the VLAN Ignore Feature
1.6.1 Introduction to the VLAN Ignore Feature
Traffic on a VLAN in a complex network may be blocked by spanning tree.

Figure 1-6 VLAN connectivity blocked by MSTP
As shown in Figure 1-6, port A on Switch A allows VLAN 1 to pass, C allows VLAN 2 to pass; port B on Switch B allows VLAN 1 to pass, port D allows VLAN 2 to pass. Switch A and Switch B run MSTP. Switch A is the root bridge, and port A and port C on it are designated ports. Port B on Switch B is the root port, and port D is a blocked port. In this case, traffic on VLAN 2 is blocked.
Enabling the VLAN Ignore feature for a VLAN can make ports of the VLAN forward packets normally rather than comply with the calculated result of MSTP.
1.6.2 Configuration Procedure
Follow these steps to configure VLAN Ignore:
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Enable VLAN Ignore for a VLAN |
stp ignored vlan vlan-list |
Required By default, VLAN Ignore is disabled in a VLAN. |
|
Display VLAN Ignore enabled VLANs |
display stp ignored-vlan |
Optional Available in any view |
1.6.3 Configuration Examples
I. Network requirements
l Switch A and B are in direct connection;
l Ethernet 1/1/1 on Switch A and Ethernet 1/1/2 on Switch B allow VLAN 1 to pass. Ethernet 1/1/3 on Switch A and Ethernet 1/1/4 on Switch B allow VLAN 2 to pass.
l Switch A is the root bridge, and both Switch A and Switch B run MSTP. Ethernet 1/1/4 on Switch B is blocked, causing traffic block on VLAN 2.
l Configure VLAN Ignore to keep the ports in VLAN 2 on Switch B in the forwarding state.
II. Network diagram
Figure 1-7 Network diagram for VLAN Ignore configuration
III. Configuration procedure
1) Enable VLAN Ignore on Switch B.
# Enable VLAN Ignore on VLAN 2.
<SysnameB> system-view
[SysnameB] stp ignored vlan 2
2) Verify the configuration
# Display the VLAN Ignore-enabled VLANs.
[SysnameB] display stp ignored-vlan
STP-Ignored VLAN: 2
1.7 Configuring Digest Snooping
As defined in IEEE 802.1s, interconnected devices are in the same region only when the region related configuration (domain name, revision level, VLAN-to-MSTI mappings) on them is identical. An MSTP enabled device identifies devices in the same MST region via checking the configuration ID in BPDU packets. The configuration ID includes the region name, revision level, configuration digest that is in 16-byte length and is the result computed via the HMAC-MD5 algorithm based on VLAN-to-MSTI mappings.
In practical networking implementations, since MSTP implementations differ with vendors, the configuration digest computed using private keys is different; hence different vendors’ devices in the same MST region can not communicate with each other.
Enabling the Digest Snooping feature on the associated port can make a device communicate with another vendor’s device in the same MST region.
1.7.1 Configuration Prerequisites
Associated devices of different vendors are interconnected and run MSTP.
1.7.2 Configuration Procedure
Follow these steps to configure Digest Snooping:
|
To do... |
Use the command... |
Remarks |
|
|
Enter system view |
system-view |
— |
|
|
Enter Ethernet interface or port group view |
Enter Ethernet interface view |
interface interface-type interface-number |
Choose either |
|
Enter port group view |
port-group { manual port-group-name | aggregation agg-id } |
||
|
Enable digest snooping on the interface or port group |
stp config-digest-snooping |
Required Not enabled by default |
|
|
Return to system view |
quit |
— |
|
|
Enable global digest snooping |
stp config-digest-snooping |
Required Not enabled by default |
|
![]() Caution:
Caution:
l You can only enable the Digest Snooping feature on the device connected to another vendor’s device that use private key to compute the configuration digest.
l With the Digest Snooping feature enabled, comparison of configuration digest is not needed for in-the-same-region check, so the VLAN-to-MSTI mappings must be the same on associated ports.
l With global Digest Snooping enabled, modification of VLAN-to-MSTI mappings and removing of the current region configuration using the undo stp region-configuration command are not allowed. You can only modify the region name and revision level.
l You need to enable this feature both globally and on associated ports to make it take effect. It is recommended to enable the feature on all associated ports first and then globally, making all configured ports take effect, and disable the feature globally to disable it on all associated ports.
l It is not recommended to enable Digest Snooping on the MST region edge port to avoid loops.
l Do not enable Digest Snooping when the network works well to avoid traffic interruption.
1.7.3 Configuration Examples
I. Network requirements
l Switch A and Switch B connect to a third-party’s device and all the devices are in the same region.
l Enable Digest Snooping on Switch A and Switch B so that the three devices can communicate with one another.
II. Network diagram

Figure 1-8 Network diagram for Digest Snooping configuration
III. Configuration procedure
1) Enable Digest Snooping on Switch A
# Enable Digest Snooping on Ethernet 1/1/2.
<SysnameA> system-view
[SysnameA] interface ethernet 1/1/2
[SysnameA-Ethernet1/1/2] stp config-digest-snooping
# Enable global Digest Snooping.
[SysnameA-Ethernet1/1/2] quit
[SysnameA] stp config-digest-snooping
2) Enable Digest Snooping on Switch B (the same as the configuration procedure of Switch A, omitted)
1.8 Configuring No Agreement Check
Two types of packet are used for rapid state transition on designated RSTP and MSTP ports:
l Proposal: Packets sent by designated ports to request rapid transition
l Agreement: Packets used to acknowledge rapid transition requests
Both RSTP and MSTP switches can perform rapid transition operation on a designated port only when the port receives an agreement packet from the downstream switch. The differences between RSTP and MSTP switches are:
l For MSTP, the downstream device’s root port sends an agreement packet only after it receives an agreement packet from the upstream device.
l For RSTP, the down stream device sends an agreement packet regardless of whether an agreement packet from the upstream device is received.
Figure 1-9 and Figure 1-10 show the rapid state transition mechanism on MSTP and RSTP designated ports.

Figure 1-9 Rapid state transition mechanism on the MSTP designated port

Figure 1-10 Rapid state transition mechanism on the RSTP designated port
If the upstream device comes from another vendor, the rapid state transition implementation may be limited. For example, when the upstream device adopts RSTP, the downstream device adopts MSTP and does not support RSTP mode, the root port on the downstream device receives no agreement packet from the upstream device and thus sends no agreement packets to the upstream device. As a result, the designated port of the upstream switch fails to transit rapidly and can only change to the Forwarding state after a period twice the Forward Delay.
In this case, you can enable the No Agreement Check feature on the downstream device’s port to perform rapid state transition.
1.8.1 Configuration Prerequisites
l A device is the upstream one that is connected to another vendor’s MSTP supported device via a point-to-point link.
l Configure the same region name, revision level and VLAN-to-MSTI mappings on the two devices, making them in the same region.
1.8.2 Configuration Procedure
Following these steps to configure No Agreement Check:
|
To do... |
Use the command... |
Remarks |
|
|
Enter system view |
system-view |
— |
|
|
Enter Ethernet interface or port group view |
Enter Ethernet interface view |
interface interface-type interface-number |
Choose either |
|
Enter port group view |
port-group { manual port-group-name | aggregation agg-id } |
||
|
Enable No Agreement Check |
stp no-agreement-check |
Required Not enabled by default |
|
& Note:
The No Agreement Check feature can take effect only when it is enabled on the root port.
1.8.3 Configuration Examples
I. Network requirements
l Switch A connects to a third-party’s device that has different MSTP implementation. Both switches are in the same region.
l Another vendor’s device is the regional root bridge, and Switch A is the downstream device.
II. Network diagram
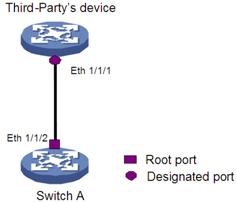
Figure 1-11 No Agreement Check configuration
III. Configuration procedure
# Enable No Agreement Check on Ethernet 1/1/2 of Switch A.
<Sysname> system-view
[Sysname] interface ethernet 1/1/2
[Sysname-Ethernet1/1/2] stp no-agreement-check
1.9 Configuring Protection Functions
An MSTP-compliant device supports the following protection functions:
l BPDU guard
l Root guard
l Loop guard
l TC-BPDU attack guard
& Note:
Among loop guard, root guard and edge port setting, only one function can take effect on the same port at the same time.
These protection functions function as follows:
l BPDU guard
For access layer devices, the access ports generally have user terminals (such as PCs) or file servers directly connected to them. These ports are usually configured as edge ports to allow rapid transition. However, these ports become non-edge ports when they receive configuration BPDUs, which triggers a new round of spanning tree computing process and causes changes of network topology. Under normal conditions, these ports are not supposed to receive configuration BPDUs. However, if someone forges configuration BPDUs maliciously to attack the devices, network may become instable.
MSTP provides the BPDU guard function to protect the system against such attacks. With the BPDU guard function enabled on the devices, edge ports receiving configuration BPDUs are shut down and the NMS is informed. Those ports closed thereby can be restored only by the network administrators.
l Root guard
The root bridge and its secondary root bridges of a spanning tree must reside in the same MST region. Especially for the CIST, the root bridge and its secondary root bridges are generally put in a high-bandwidth core region during network design. However, due to possible configuration errors or attacks in the network, the root bridge may receive a configuration BPDU with a higher priority. In this case, the current, legal root bridge will be superseded by another device, causing undesired change of the network topology. As a result of this kind of illegal topology change, the traffics that are to travel along high-speed links may be led to low-speed links, resulting in network congestion.
To prevent this situation from happening, MSTP provides the root guard function to protect the root bridge. Ports with root guard function enabled can only be designated ports in all MSTIs. Once a port of this type receives a configuration BPDU with a higher priority from an MSTI, it turns to the listening state in the MSTI and stops forwarding packets (as if it is disconnected from the link). If the port receives no BPDUs with higher priorities within twice the forwarding delay, the port reverts to its original state.
l Loop guard
A device maintains the states of its root port and blocked ports by receiving and processing BPDUs from the upstream device. However, due to link congestion or unidirectional link failures, these ports may fail to receive BPDUs from the upstream device. In this case, the downstream device will reselect the port roles (for example, ports failing to receive upstream BPDUs become designated ports and the blocked ports transition to the forwarding state), resulting in loops in the switched network. The loop guard function can suppress the occurrence of such loops.
& Note:
A loop guard–enabled port that fails to receive BPDUs from the upstream device remains in the discarding state in all the MSTIs in the process of STP computing, regardless of the role it plays.
l TC-BPDU attack guard
A device removes the corresponding forwarding entries upon receiving a TC-BPDU (a PDU notifying of a topology change). If a malicious user forges large amount of TC-BPDUs and sends them to a device in a short period, the device may be busy removing the forwarding entries, decreasing the performance of the switch and introducing potential stability risks.
The TC-BPDU attack guard function can relieve a switch from this dilemma. With this function enabled, the device removes the forwarding address entries only once within a specific period (10 seconds) after it receives a TC-BPDU. At the same time, the system monitors whether other TC-BPDUs are received within that period. If so, the device will perform another removing operation after the period elapses. This prevents removing forwarding address entries frequently.
1.9.1 Configuration Prerequisites
MSTP has been correctly configured on the device.
1.9.2 Enabling the BPDU Guard Function
& Note:
We recommend that you enable the BPDU guard function.
I. Configuration procedure
Following these steps to enable the BPDU guard function:
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Enable the BPDU guard function for the device |
stp bpdu-protection |
Required Disabled by default |
II. Configuration example
# Enable the BPDU guard function.
<Sysname> system-view
[Sysname] stp bpdu-protection
1.9.3 Enabling the Root Guard Function
& Note:
We recommend that you enable the root guard function.
I. Configuration procedure
Follow these steps to enable the root guard function:
|
To do... |
Use the command... |
Remarks |
|
|
Enter system view |
System-view |
— |
|
|
Enter Ethernet interface view or port group view |
Enter Ethernet interface view |
interface interface-type interface-number |
User either command Configured in Ethernet interface view, the setting is effective on the current port only; configured in port group view, the setting is effective on all the ports in the port group |
|
Enter port group view |
port-group { manual port-group-name | aggregation agg-id } |
||
|
Enable the root guard function for the ports(s) |
stp root-protection |
Required Disabled by default |
|
II. Configuration example
# Enable the root guard function for Ethernet 1/1/1.
<Sysname> system-view
[Sysname] interface ethernet 1/1/1
[Sysname-Ethernet1/1/1] stp root-protection
1.9.4 Enabling the Loop Guard Function
& Note:
We recommend that you enable the loop guard function.
I. Configuration procedure
Follow these steps to enable the loop guard function:
|
To do... |
Use the command... |
Remarks |
|
|
Enter system view |
system-view |
— |
|
|
Enter Ethernet interface view or port group view |
Enter Ethernet interface view |
interface interface-type interface-number |
User either command Configured in Ethernet interface view, the setting is effective on the current port only; configured in port group view, the setting is effective on all the ports in the port group |
|
Enter port group view |
port-group { manual port-group-name | aggregation agg-id } |
||
|
Enable the loop guard function for the ports(s) |
stp loop-protection |
Required Disabled by default |
|
II. Configuration example
# Enable the loop guard function for Ethernet 1/1/1.
<Sysname> system-view
[Sysname] interface ethernet 1/1/1
[Sysname-Ethernet1/1/1] stp loop-protection
1.9.5 Enabling the TC-BPDU Attack Guard Function
& Note:
We recommend that you keep this function enabled.
I. Configuration procedure
Follow these steps to enable the TC-BPDU attack guard function
|
To do... |
Use the command... |
Remarks |
|
Enter system view |
system-view |
— |
|
Enable the TC-BPDU attack guard function |
stp tc-protection enable |
Optional Enabled by default |
II. Configuration example
# Enable the TC-BPDU attack guard function.
<Sysname> system-view
[Sysname] stp tc-protection enable
1.10 Displaying and Maintaining MSTP
|
To do... |
Use the command... |
Remarks |
|
View the MSTP status information and statistics information |
display stp [ instance instance-id ] [ interface interface-list | slot slot-id ] [ brief ] |
Available in any view |
|
View the MST region configuration information |
display stp region-configuration |
Available in any view |
|
View the list of the VLANs with VLAN Ignore enabled |
display stp ignored-vlan |
Available in any view |
|
Clear the MSTP statistics information |
reset stp [ interface interface-list ] |
Available in user view |
1.11 MSTP Configuration Examples
I. Network requirements
Configure MSTP so that packets of different VLANs are forwarded along different spanning trees. The specific configuration requirements are as follows:
l All devices on the network are in the same MST region.
l Packets of VLAN 10 are forwarded along MSTI 1, those of VLAN 30 are forwarded along MSTI 3, those of VLAN 40 are forwarded along MSTI 4, and those of VLAN 20 are forwarded along MSTI 0.
l Switch A and Switch B are convergence layer devices, while Switch C and Switch D are access layer devices. VLAN 10 and VLAN 30 are terminated on the convergence layer devices, and VLAN 40 is terminated on the access layer devices, so the root bridges of MSTI 1 and MSTI 3 are Switch A and Switch B, while the root bridge of MSTI 4 is Switch C.
II. Network diagram
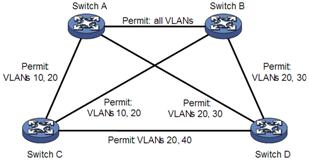
Figure 1-12 Network diagram for MSTP configuration
& Note:
“Permit:” beside each link in the figure is followed by the VLANs the packets of which are permitted to pass this link.
III. Configuration procedure
1) Configuration on Switch A
# Configure an MST region.
<SysnameA> system-view
[SysnameA] stp region-configuration
[SysnameA-mst-region] region-name example
[SysnameA-mst-region] instance 1 vlan 10
[SysnameA-mst-region] instance 3 vlan 30
[SysnameA-mst-region] instance 4 vlan 40
[SysnameA-mst-region] revision-level 0
# Activate MST region configuration manually.
[SysnameA-mst-region] active region-configuration
[SysnameA-mst-region] quit
# Configure Switch A as the root bridge of MSTI 1.
[SysnameA] stp instance 1 root primary
# Enable MSTP on the device
[SysnameA] stp enable
# View the MST region configuration information that has taken effect.
[SysnameA] display stp region-configuration
Oper configuration
Format selector :0
Region name :example
Revision level :0
Instance Vlans Mapped
0 1 to 9, 11 to 29, 31 to 39, 41 to 4094
1 10
3 30
4 40
2) Configuration on Switch B
# Configure an MST region.
<SysnameB> system-view
[SysnameB] stp region-configuration
[SysnameB-mst-region] region-name example
[SysnameB-mst-region] instance 1 vlan 10
[SysnameB-mst-region] instance 3 vlan 30
[SysnameB-mst-region] instance 4 vlan 40
[SysnameB-mst-region] revision-level 0
# Activate MST region configuration manually.
[SysnameB-mst-region] active region-configuration
[SysnameB-mst-region] quit
# Configure Switch B as the root bridge of MSTI 3.
[SysnameB] stp instance 3 root primary
# Enable MSTP on the device
[SysnameB] stp enable
# View the MST region configuration information that has taken effect.
[SysnameB] display stp region-configuration
Oper configuration
Format selector :0
Region name :example
Revision level :0
Instance Vlans Mapped
0 1 to 9, 11 to 29, 31 to 39, 41 to 4094
1 10
3 30
4 40
3) Configuration on Switch C
# Configure an MST region.
<SysnameC> system-view
[SysnameC] stp region-configuration
[SysnameC-mst-region] region-name example
[SysnameC-mst-region] instance 1 vlan 10
[SysnameC-mst-region] instance 3 vlan 30
[SysnameC-mst-region] instance 4 vlan 40
[SysnameC-mst-region] revision-level 0
# Activate MST region configuration manually.
[SysnameC-mst-region] active region-configuration
[SysnameC-mst-region] quit
# Configure Switch C as the root bridge of MSTI 4.
[SysnameC] stp instance 4 root primary
# Enable MSTP on the device
[SysnameC] stp enable
# View the MST region configuration information that has taken effect.
[SysnameC] display stp region-configuration
Oper configuration
Format selector :0
Region name :example
Revision level :0
Instance Vlans Mapped
0 1 to 9, 11 to 29, 31 to 39, 41 to 4094
1 10
3 30
4 40
4) Configuration on Switch D
# Configure an MST region.
<SysnameD> system-view
[SysnameD] stp region-configuration
[SysnameD-mst-region] region-name example
[SysnameD-mst-region] instance 1 vlan 10
[SysnameD-mst-region] instance 3 vlan 30
[SysnameD-mst-region] instance 4 vlan 40
[SysnameD-mst-region] revision-level 0
# Activate MST region configuration manually.
[SysnameD-mst-region] active region-configuration
[SysnameD-mst-region] quit
# Enable MSTP on the system
[SysnameD] stp enable
# View the MST region configuration information that has taken effect.
[SysnameD] display stp region-configuration
Oper configuration
Format selector :0
Region name :example
Revision level :0
Instance Vlans Mapped
0 1 to 9, 11 to 29, 31 to 39, 41 to 4094
1 10
3 30
4 40

