- Table of Contents
-
- H3C S6116 Ultra-Low Latency Switch Series Configuration Guide-Release 671x-6W101
- 00-Preface
- 01-Interface forwarding configuration
- 02-CLI configuration
- 03-RBAC configuration
- 04-Login management configuration
- 05-FTP and TFTP configuration
- 06-File system management configuration
- 07-Configuration file management configuration
- 08-Software upgrade configuration
- 09-Device management configuration
- 10-Tcl configuration
- 11-Bulk interface configuration
- 12-IP addressing configuration
- 13-IPv6 basics configuration
- 14-Static routing configuration
- 15-IPv6 static routing configuration
- 16-AAA configuration
- 17-Public key management
- 18-SSH configuration
- 19-System maintenance and debugging configuration
- 20-NTP configuration
- 21-SNMP configuration
- 22-RMON configuration
- 23-Event MIB configuration
- 24-Information center configuration
- 25-PTP configuration
- 26-Network synchronization configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 09-Device management configuration | 233.21 KB |
Device management tasks at a glance
Restrictions and guidelines for configuring the system time
System time configuration tasks at a glance
Setting the system time at the CLI
Obtaining the UTC time through a time protocol
Setting the daylight saving time
Configuring delay compensation duration for obtaining time
Enabling displaying the copyright statement
Disabling password recovery capability
Setting memory alarm thresholds
Setting the temperature alarm thresholds
Verifying and diagnosing transceiver modules
Diagnosing transceiver modules
Disabling transceiver module source alarm
Restrictions and guidelines for device reboot
Rebooting the device immediately at the CLI
Restoring the factory-default configuration
Display and maintenance commands for device management configuration
Managing the device
This chapter describes how to configure basic device parameters and manage the device.
Device management tasks at a glance
All device management tasks are optional. You can perform any of the tasks in any order.
· Configuring basic parameters
¡ Configuring delay compensation duration for obtaining time
¡ Enabling displaying the copyright statement
· Configuring security parameters
¡ Disabling password recovery capability
· Monitoring the device
¡ Setting memory alarm thresholds
¡ Setting the temperature alarm thresholds
· Managing resources
Verifying and diagnosing transceiver modules
· Maintaining the device
¡ Restoring the factory-default configuration
Configuring the device name
About this task
A device name (also called hostname) identifies a device in a network and is used in CLI view prompts. For example, if the device name is Sysname, the user view prompt is <Sysname>.
Procedure
1. Enter system view.
system-view
sysname sysname
By default, the device name is H3C.
Configuring the system time
About the system time
Correct system time is essential to network management and communication. Configure the system time correctly before you run the device on the network.
The device can use one of the following methods to obtain the system time:
· Uses the locally set system time, and then uses the clock signals generated by its built-in crystal oscillator to maintain the system time.
· Periodically obtains the UTC time from an NTP source, and uses the UTC time, time zone, and daylight saving time to calculate the system time. For more information about NTP, see ''Configuring NTP.''
The system time calculated by using the UTC time from a time source is more precise.
Restrictions and guidelines for configuring the system time
After you execute the clock protocol none command, the clock datetime command determines the system time, whether or not the time zone or daylight saving time has been configured.
If you configure or change the time zone or daylight saving time after the device obtains the system time, the device recalculates the system time. To view the system time, execute the display clock command.
System time configuration tasks at a glance
To configure the system time, perform the following tasks:
1. Configuring the system time
Choose one of the following tasks:
¡ Setting the system time at the CLI
¡ Obtaining the UTC time through a time protocol
2. (Optional.) Setting the time zone
Make sure each network device uses the time zone of the place where the device resides.
3. (Optional.) Setting the daylight saving time
Make sure each network device uses the daylight saving time parameters of the place where the device resides.
Setting the system time at the CLI
1. Enter system view.
system-view
2. Configure the device to use the local system time.
clock protocol none
By default, the device uses the NTP time source.
If you execute the clock protocol command multiple times, the most recent configuration takes effect.
3. Return to user view.
quit
4. Set the local system time.
clock datetime time date
By default, the factory-default system time is used.
|
CAUTION: Change of the system time affects execution of system time-related features (such as scheduled tasks) and cooperative operation with other devices (such as log reporting and statistics collection). Before using this command, make sure you understand its impact on the live network. |
Obtaining the UTC time through a time protocol
1. Enter system view.
system-view
2. Specify the system time source.
clock protocol ntp
By default, the device uses the NTP time source.
If you execute this command multiple times, the most recent configuration takes effect.
3. Configure time protocol parameters.
For more information about NTP configuration, see ''Configuring NTP.''
Setting the time zone
1. Enter system view.
system-view
2. Set the time zone.
clock timezone zone-name { add | minus } zone-offset
By default, the system uses the UTC time zone.
Setting the daylight saving time
1. Enter system view.
system-view
2. Set the daylight saving time.
clock summer-time name start-time start-date end-time end-date add-time
By default, the daylight saving time is not set.
Configuring delay compensation duration for obtaining time
About this task
For devices that obtains time through coaxial cables or external antennas, the time obtained by the device clock chip will experience a delay. The length of the coaxial cable or external antenna determines the length of this delay. This feature configures the delay compensation duration for the device's time obtaining. The compensation duration needs to be determined based on the actual length of the coaxial cable or external antenna.
Hardware and feature compatibility
Only the S6116-48X-M switch supports this feature.
Restrictions and guidelines
When you configure this feature, you need to determine the delay compensation duration based on the actual length of the external antenna or coaxial cable.
Procedure
1. Enter system view.
system-view
2. Configure the delay compensation duration for obtaining time.
clock delay-compensation { 1pps | gps } timer
By default, the delay compensation duration for obtaining time is 0.
Enabling displaying the copyright statement
About this task
This feature enables the device to display the copyright statement in the following situations:
· When a Telnet or SSH user logs in.
· When a console user quits user view. This is because the device automatically tries to restart the user session.
If you disable displaying the copyright statement, the device does not display the copyright statement in any situations.
Procedure
1. Enter system view.
system-view
2. Enable displaying the copyright statement.
copyright-info enable
By default, displaying the copyright statement is enabled.
Configuring banners
About this task
Banners are messages that the system displays when a user logs in.
The system supports the following banners:
· Legal banner—Appears after the copyright statement.
· Message of the Day (MOTD) banner—Appears after the legal banner and before the login banner.
· Login banner—Appears only when password or scheme authentication is configured.
· Shell banner—Appears when a user accesses user view.
The system displays the banners in the following order: legal banner, MOTD banner, login banner, and shell banner.
Banner input methods
You can configure a banner by using one of the following methods:
· Input the entire command line in a single line.
The banner cannot contain carriage returns. The entire command line, including the command keywords, the banner, and the delimiters, can have a maximum of 511 characters. The delimiters for the banner can be any printable character but must be the same. You cannot press Enter before you input the end delimiter.
For example, you can configure the shell banner "Have a nice day." as follows:
<System> system-view
[System] header shell %Have a nice day.%
· Input the command line in multiple lines.
The banner can contain carriage returns. A carriage return is counted as two characters.
To input a banner configuration command line in multiple lines, use one of the following methods:
¡ Press Enter after the final command keyword, type the banner, and end the final line with the delimiter character %. The banner plus the delimiter can have a maximum of 1999 characters.
For example, you can configure the banner "Have a nice day." as follows:
<System> system-view
[System] header shell
Please input banner content, and quit with the character '%'.
Have a nice day.%
¡ After you type the final command keyword, type any printable character as the start delimiter for the banner and press Enter. Then, type the banner and end the final line with the same delimiter. The banner plus the end delimiter can have a maximum of 1999 characters.
For example, you can configure the banner "Have a nice day." as follows:
<System> system-view
[System] header shell A
Please input banner content, and quit with the character 'A'.
Have a nice day.A
¡ After you type the final command keyword, type the start delimiter and part of the banner. Make sure the final character of the final string is different from the start delimiter. Then, press Enter, type the rest of the banner, and end the final line with the same delimiter. The banner plus the start and end delimiters can have a maximum of 2002 characters.
For example, you can configure the banner "Have a nice day." as follows:
<System> system-view
[System] header shell AHave a nice day.
Please input banner content, and quit with the character 'A'.
A
Procedure
1. Enter system view.
system-view
2. Configure the legal banner.
header legal text
3. Configure the MOTD banner.
header motd text
4. Configure the login banner.
header login text
5. Configure the shell banner.
header shell text
Disabling password recovery capability
About this task
Password recovery capability controls console user access to the device configuration and SDRAM from BootWare menus. For more information about BootWare menus, see the release notes.
If password recovery capability is enabled, a console user can access the device configuration without authentication to configure a new password.
If password recovery capability is disabled, console users must restore the factory-default configuration before they can configure new passwords. Restoring the factory-default configuration deletes the next-startup configuration files.
To enhance system security, disable password recovery capability.
Restrictions and guidelines
To access the device configuration without authentication, you must connect to the device and access the BootWare menu while the device is starting up.
Procedure
1. Enter system view.
system-view
2. Disable password recovery capability.
undo password-recovery enable
By default, password recovery capability is enabled.
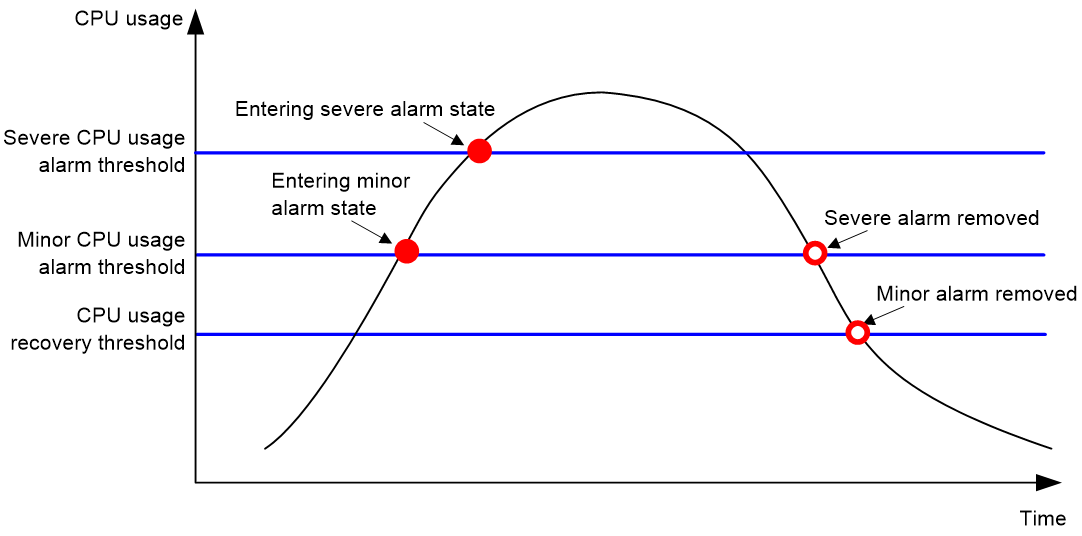
Monitoring CPU usage
About this task
To monitor CPU usage, the device performs the following operations:
· Samples CPU usage at 1-minute intervals, and compares the samples with CPU usage thresholds to identify the CPU usage status and send alarms or notifications accordingly.
· Samples and saves CPU usage at a configurable interval if CPU usage tracking is enabled. You can use the display cpu-usage history command to display the historical CPU usage statistics in a coordinate system.
The device supports the following CPU usage thresholds:
· Minor threshold—If the CPU usage increases to or above the minor threshold but is less than the severe threshold, the CPU usage enters minor alarm state. The device sends minor alarms periodically until the CPU usage increases above the severe threshold or the minor alarm is removed.
· Severe threshold—If the CPU usage increases above the severe threshold, the CPU usage enters severe alarm state. The device sends severe alarms periodically until the severe alarm is removed.
· Recovery threshold—If the CPU usage decreases below the recovery threshold, the CPU usage enters recovered state. The device sends a recovery notification.
CPU usage alarms and notifications can be sent to SNMP and the information center to be encapsulated as SNMP traps and informs and log messages. For more information about SNMP and information center, see ''Configuring SNMP'' and ''Configuring the information center.''
Figure 1 CPU alarms and alarm-removed notifications
Procedure
1. Enter system view.
system-view
2. Set the CPU usage alarm thresholds.
monitor cpu-usage threshold severe-threshold { minor-threshold minor-threshold recovery-threshold recovery-threshold [ slot slot-number [ cpu cpu-number ] ] }
The default settings are as follows:
¡ Severe CPU usage alarm threshold—99%.
¡ Minor CPU usage alarm threshold—90%.
¡ CPU usage recovery threshold—60%.
|
CAUTION: If you set the severe CPU usage alarm threshold to a too low value, the device will reach the threshold easily. Normal service processing will be affected. |
3. Set CPU usage alarm resending intervals.
monitor resend cpu-usage { minor-interval minor-interval | severe-interval severe-interval } * [ slot slot-number [ cpu cpu-number ] ]
By default, the minor alarm resending interval is 300 seconds and the severe alarm resending interval is 60 seconds.
4. Set the sampling interval for CPU usage tracking.
monitor cpu-usage interval interval [ slot slot-number [ cpu cpu-number ] ]
By default, the sampling interval for CPU usage tracking is 1 minute.
5. Enable CPU usage tracking.
monitor cpu-usage enable [ slot slot-number [ cpu cpu-number ] ]
By default, CPU usage tracking is enabled.
6. (Optional.) Enable periodic CPU usage logging.
monitor cpu-usage logging interval interval-time
By default, periodic CPU usage logging is disabled.
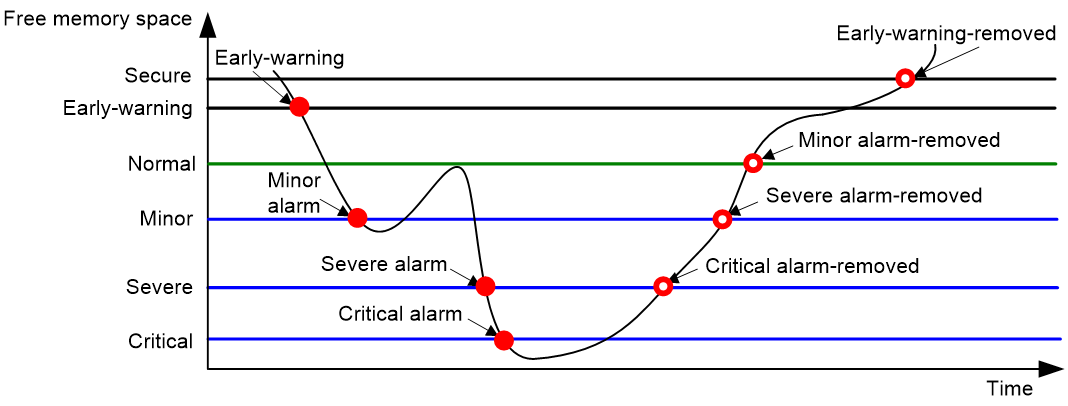
Setting memory alarm thresholds
About this task
To ensure correct operation and improve memory efficiency, the system monitors the amount of free memory space in real time. If the amount of free memory space reaches the minor, severe, or critical alarm threshold, the system issues an alarm to affected service modules and processes.
The system can also issue an early warning to warn you of an approaching insufficient-memory condition.
You can use the display memory command to display memory usage information.
As shown in the following table and figure, the system supports these free-memory thresholds:
· Sufficient-memory threshold.
· Early-warning threshold.
· Normal state threshold.
· Minor alarm threshold.
· Severe alarm threshold.
· Critical alarm threshold.
Table 1 Memory alarm notifications and memory alarm-removed notifications
|
Notification |
Triggering condition |
Remarks |
|
Early-warning notification |
The amount of free memory space decreases below the early-warning threshold. |
After generating and sending an early-warning notification, the system does not generate and send any additional early-warning notifications until the early warning is removed. |
|
Minor alarm notification |
The amount of free memory space decreases below the minor alarm threshold. |
After generating and sending a minor alarm notification, the system does not generate and send any additional minor alarm notifications until the minor alarm is removed. |
|
Severe alarm notification |
The amount of free memory space decreases below the severe alarm threshold. |
After generating and sending a severe alarm notification, the system does not generate and send any additional severe alarm notifications until the severe alarm is removed. |
|
Critical alarm notification |
The amount of free memory space decreases below the critical alarm threshold. |
After generating and sending a critical alarm notification, the system does not generate and send any additional critical alarm notifications until the critical alarm is removed. |
|
Critical alarm-removed notification |
The amount of free memory space increases above the severe alarm threshold. |
N/A |
|
Severe alarm-removed notification |
The amount of free memory space increases above the minor alarm threshold. |
N/A |
|
Minor alarm-removed notification |
The amount of free memory space increases above the normal state threshold. |
N/A |
|
Early-warning-removed notification |
The amount of free memory space increases above the sufficient-memory threshold. |
N/A |
Figure 2 Memory alarm notifications and alarm-removed notifications
Restrictions and guidelines
If a memory alarm occurs, delete unused configuration items or disable some features to increase the free memory space. Because the memory space is insufficient, some configuration items might not be able to be deleted.
Procedure
1. Enter system view.
system-view
2. Set the memory usage threshold.
memory-threshold [ slot slot-number [ cpu cpu-number ] ] usage memory-threshold
By default, the memory usage threshold is 100%.
3. Set the free-memory thresholds.
memory-threshold [ slot slot-number [ cpu cpu-number ] ] [ ratio ] minor minor-value severe severe-value critical critical-value normal normal-value [ early-warning early-warning-value secure secure-value ]
The default settings are as follows:
¡ Minor alarm threshold—448 MB.
¡ Severe alarm threshold—224 MB.
¡ Critical alarm threshold—128 MB.
¡ Normal state threshold—496 MB.
¡ Early-warning threshold—512 MB.
¡ Sufficient-memory threshold—576 MB.
4. Set memory depletion alarm resending intervals.
monitor resend memory-threshold { critical-interval critical-interval | early-warning-interval early-warning-interval | minor-interval minor-interval | severe-interval severe-interval } * [ slot slot-number [ cpu cpu-number ] ]
The following are the default settings:
¡ Early warning resending interval—1 hour.
¡ Minor alarm resending interval—12 hours.
¡ Severe alarm resending interval—3 hours.
¡ Critical alarm resending interval—1 hour.
5. (Optional.) Enable periodic memory usage logging.
monitor memory-usage logging interval interval-time
By default, periodic memory usage logging is disabled.
Setting the temperature alarm thresholds
About this task
The device monitors its temperature based on the following thresholds:
· Low-temperature threshold.
· High-temperature warning threshold.
· High-temperature alarming threshold.
When the device temperature drops below the low-temperature threshold or reaches the high-temperature warning or alarming threshold, the device performs the following operations:
· Sends log messages and traps.
· Sets LEDs on the device panel.
Procedure
1. Enter system view.
system-view
2. Configure the temperature alarm thresholds.
temperature-limit slot slot-number { hotspot } sensor-number lowlimit warninglimit [ alarmlimit ]
The defaults vary by temperature sensor model. To view the defaults, execute the undo temperature-limit and display environment commands in turn.
The high-temperature alarming threshold must be higher than the high-temperature warning threshold, and the high-temperature warning threshold must be higher than the low-temperature threshold.
Verifying and diagnosing transceiver modules
Verifying transceiver modules
About this task
You can use one of the following methods to verify the genuineness of a transceiver module:
· Display the key parameters of a transceiver module, including its transceiver type, connector type, central wavelength of the transmit laser, transfer distance, and vendor name.
· Display its electronic label. The electronic label is a profile of the transceiver module and contains the permanent configuration, including the serial number, manufacturing date, and vendor name. The data was written to the transceiver module or the device's storage component during debugging or testing of the transceiver module or device.
The device regularly checks transceiver modules for their vendor names. If a transceiver module does not have a vendor name or the vendor name is not H3C, the device repeatedly outputs traps and log messages. For information about logging rules, see ''Configuring the information center.''
Procedure
To verify transceiver modules, execute the following commands in any view:
· Display the key parameters of transceiver modules.
display transceiver interface [ interface-type interface-number ]
· Display the electrical label information of transceiver modules.
display transceiver manuinfo interface [ interface-type interface-number ]
Diagnosing transceiver modules
About this task
The device provides the alarm and digital diagnosis functions for transceiver modules. When a transceiver module fails or is not operating correctly, you can perform the following tasks:
· Check the alarms that exist on the transceiver module to identify the fault source.
· Examine the key parameters monitored by the digital diagnosis function, including the temperature, voltage, laser bias current, TX power, and RX power.
Procedure
To diagnose transceiver modules, execute the following commands in any view:
· Display transceiver alarms.
display transceiver alarm interface [ interface-type interface-number ]
· Display the current values of the digital diagnosis parameters on transceiver modules.
display transceiver diagnosis interface [ interface-type interface-number ]
Disabling transceiver module source alarm
About this task
The device regularly checks transceiver modules for their vendor names. If a transceiver module does not have a vendor name or the vendor name is not HPE, the device repeatedly outputs traps and log messages. If the transceiver modules were manufactured or sold by HPE, you can disable transceiver module source alarm.
Restrictions and guidelines
To view the vendor information, use the display transceiver manuinfo command.
Procedure
1. Enter system view.
system-view
2. Disable transceiver module source alarm.
transceiver phony-alarm-disable
By default, transceiver module source alarm is enabled.
Scheduling a task
About task scheduling
You can schedule the device to automatically execute a command or a set of commands without administrative interference.
You can configure a periodic schedule or a non-periodic schedule. A non-periodic schedule is not saved to the configuration file and is lost when the device reboots. A periodic schedule is saved to the startup configuration file and is automatically executed periodically.
Restrictions and guidelines
· The default system time is always restored at reboot. To make sure a task schedule can be executed as expected, reconfigure the system time or configure NTP after you reboot the device. For more information about NTP, see ''Configuring NTP.''
· To assign a command (command A) to a job, you must first assign the job the command or commands for entering the view of command A.
· Make sure all commands in a schedule are compliant to the command syntax. The system does not check the syntax when you assign a command to a job.
· A schedule cannot contain any one of these commands: telnet, ftp, ssh2, and monitor process.
· A schedule does not support user interaction. If a command requires a yes or no answer, the system always assumes that a Y or Yes is entered. If a command requires a character string input, the system assumes that either the default character string (if any) or a null string is entered.
· A schedule is executed in the background, and no output (except for logs, traps, and debug information) is displayed for the schedule.
Procedure
1. Enter system view.
system-view
2. Create a job.
scheduler job job-name
3. Assign a command to the job.
command id command
By default, no command is assigned to a job.
You can assign multiple commands to a job. A command with a smaller ID is executed first.
4. Exit to system view.
quit
5. Create a schedule.
scheduler schedule schedule-name
6. Assign a job to the schedule.
job job-name
By default, no job is assigned to a schedule.
You can assign multiple jobs to a schedule. The jobs will be executed concurrently.
7. Assign user roles to the schedule.
user-role role-name
By default, a schedule has the user role of the schedule creator.
You can assign a maximum of 64 user roles to a schedule. A command in a schedule can be executed if it is permitted by one or more user roles of the schedule.
8. Specify the execution time for the schedule.
Choose one option as needed:
¡ Execute the schedule at specific points of time.
time at time date
time once at time [ month-date month-day | week-day week-day&<1-7> ]
¡ Execute the schedule after a period of time.
time once delay time
¡ Execute the schedule at the specified time on every specified day in a month or week.
time repeating at time [ month-date [ month-day | last ] | week-day week-day&<1-7> ]
¡ Execute the schedule periodically from the specified time on.
time repeating [ at time [date ] ] interval interval
By default, no execution time is specified for a schedule.
The time commands overwrite each other. The most recently executed command takes effect.
9. (Optional.) Set the schedule log file size limit.
scheduler logfile size value
By default, the schedule log file size limit is 16 KB.
The schedule log file stores log messages for execution results of commands in jobs. After the limit is reached, the system deletes the oldest log messages to store the new log messages. If the remaining space of the log file is not enough for a single log message, the system truncates the message and does not store the extra part.
Example: Scheduling a task
Network configuration
As shown in Figure 3, two interfaces of the device are connected to users.
To save energy, configure the device to perform the following operations:
· Enable the interfaces at 8:00 a.m. every Monday through Friday.
· Disable the interfaces at 18:00 every Monday through Friday.
Procedure
# Enter system view.
<Sysname> system-view
# Configure a job for disabling interface Ten-GigabitEthernet 1/0/1.
[Sysname] scheduler job shutdown-Ten-GigabitEthernet1/0/1
[Sysname-job-shutdown-Ten-GigabitEthernet1/0/1] command 1 system-view
[Sysname-job-shutdown-Ten-GigabitEthernet1/0/1] command 2 interface ten-gigabitethernet 1/0/1
[Sysname-job-shutdown-Ten-GigabitEthernet1/0/1] command 3 shutdown
[Sysname-job-shutdown-Ten-GigabitEthernet1/0/1] quit
# Configure a job for enabling interface Ten-GigabitEthernet 1/0/1.
[Sysname] scheduler job start-Ten-GigabitEthernet1/0/1
[Sysname-job-start-Ten-GigabitEthernet1/0/1] command 1 system-view
[Sysname-job-start-Ten-GigabitEthernet1/0/1] command 2 interface ten-gigabitethernet 1/0/1
[Sysname-job-start-Ten-GigabitEthernet1/0/1] command 3 undo shutdown
[Sysname-job-start-Ten-GigabitEthernet1/0/1] quit
# Configure a job for disabling interface Ten-GigabitEthernet 1/0/2.
[Sysname] scheduler job shutdown-Ten-GigabitEthernet1/0/2
[Sysname-job-shutdown-Ten-GigabitEthernet1/0/2] command 1 system-view
[Sysname-job-shutdown-Ten-GigabitEthernet1/0/2] command 2 interface ten-gigabitethernet 1/0/2
[Sysname-job-shutdown-Ten-GigabitEthernet1/0/2] command 3 shutdown
[Sysname-job-shutdown-Ten-GigabitEthernet1/0/2] quit
# Configure a job for enabling interface Ten-GigabitEthernet 1/0/2.
[Sysname] scheduler job start-Ten-GigabitEthernet1/0/2
[Sysname-job-start-Ten-GigabitEthernet1/0/2] command 1 system-view
[Sysname-job-start-Ten-GigabitEthernet1/0/2] command 2 interface ten-gigabitethernet 1/0/2
[Sysname-job-start-Ten-GigabitEthernet1/0/2] command 3 undo shutdown
[Sysname-job-start-Ten-GigabitEthernet1/0/2] quit
# Configure a periodic schedule for enabling the interfaces at 8:00 a.m. every Monday through Friday.
[Sysname] scheduler schedule START-pc1/pc2
[Sysname-schedule-START-pc1/pc2] job start-Ten-GigabitEthernet1/0/1
[Sysname-schedule-START-pc1/pc2] job start-Ten-GigabitEthernet1/0/2
[Sysname-schedule-START-pc1/pc2] time repeating at 8:00 week-day mon tue wed thu fri
[Sysname-schedule-START-pc1/pc2] quit
# Configure a periodic schedule for disabling the interfaces at 18:00 every Monday through Friday.
[Sysname] scheduler schedule STOP-pc1/pc2
[Sysname-schedule-STOP-pc1/pc2] job shutdown-Ten-GigabitEthernet1/0/1
[Sysname-schedule-STOP-pc1/pc2] job shutdown-Ten-GigabitEthernet1/0/2
[Sysname-schedule-STOP-pc1/pc2] time repeating at 18:00 week-day mon tue wed thu fri
[Sysname-schedule-STOP-pc1/pc2] quit
Verifying the configuration
# Display the configuration information of all jobs.
[Sysname] display scheduler job
Job name: shutdown-Ten-GigabitEthernet1/0/1
system-view
interface ten-gigabitethernet 1/0/1
shutdown
Job name: shutdown-Ten-GigabitEthernet1/0/2
system-view
interface ten-gigabitethernet 1/0/2
shutdown
Job name: start-Ten-GigabitEthernet1/0/1
system-view
interface ten-gigabitethernet 1/0/1
undo shutdown
Job name: start-Ten-GigabitEthernet1/0/2
system-view
interface ten-gigabitethernet 1/0/2
undo shutdown
# Display the schedule information.
[Sysname] display scheduler schedule
Schedule name : START-pc1/pc2
Schedule type : Run on every Mon Tue Wed Thu Fri at 08:00:00
Start time : Wed Sep 28 08:00:00 2011
Last execution time : Wed Sep 28 08:00:00 2011
Last completion time : Wed Sep 28 08:00:03 2011
Execution counts : 1
-----------------------------------------------------------------------
Job name Last execution status
start-Ten-GigabitEthernet1/0/1 Successful
start-Ten-GigabitEthernet1/0/2 Successful
Schedule name : STOP-pc1/pc2
Schedule type : Run on every Mon Tue Wed Thu Fri at 18:00:00
Start time : Wed Sep 28 18:00:00 2011
Last execution time : Wed Sep 28 18:00:00 2011
Last completion time : Wed Sep 28 18:00:01 2011
Execution counts : 1
-----------------------------------------------------------------------
Job name Last execution status
shutdown-Ten-GigabitEthernet1/0/1 Successful
shutdown-Ten-GigabitEthernet1/0/2 Successful
# Display schedule log information.
[Sysname] display scheduler logfile
Job name : start-Ten-GigabitEthernet1/0/1
Schedule name : START-pc1/pc2
Execution time : Wed Sep 28 08:00:00 2011
Completion time : Wed Sep 28 08:00:02 2011
--------------------------------- Job output -----------------------------------
<Sysname>system-view
System View: return to User View with Ctrl+Z.
[Sysname]interface ten-gigabitethernet 1/0/1
[Sysname-Ten-GigabitEthernet1/0/1]undo shutdown
Job name : start-Ten-GigabitEthernet1/0/2
Schedule name : START-pc1/pc2
Execution time : Wed Sep 28 08:00:00 2011
Completion time : Wed Sep 28 08:00:02 2011
--------------------------------- Job output -----------------------------------
<Sysname>system-view
System View: return to User View with Ctrl+Z.
[Sysname]interface ten-gigabitethernet 1/0/2
[Sysname-Ten-GigabitEthernet1/0/2]undo shutdown
Job name : shutdown-Ten-GigabitEthernet1/0/1
Schedule name : STOP-pc1/pc2
Execution time : Wed Sep 28 18:00:00 2011
Completion time : Wed Sep 28 18:00:01 2011
--------------------------------- Job output -----------------------------------
<Sysname>system-view
System View: return to User View with Ctrl+Z.
[Sysname]interface ten-gigabitethernet 1/0/1
[Sysname-Ten-GigabitEthernet1/0/1]shutdown
Job name : shutdown-Ten-GigabitEthernet1/0/2
Schedule name : STOP-pc1/pc2
Execution time : Wed Sep 28 18:00:00 2011
Completion time : Wed Sep 28 18:00:01 2011
--------------------------------- Job output -----------------------------------
<Sysname>system-view
System View: return to User View with Ctrl+Z.
[Sysname]interface ten-gigabitethernet 1/0/2
[Sysname-Ten-GigabitEthernet1/0/2]shutdown
Rebooting the device
About device reboot
The following device reboot methods are available:
· Schedule a reboot at the CLI, so the device automatically reboots at the specified time or after the specified period of time.
· Immediately reboot the device at the CLI.
During the reboot process, the device performs the following operations:
a. Resets all of its chips.
b. Uses the BootWare to verify the startup software package, decompress the package, and load the images.
c. Initializes the system.
· Power off and then power on the device. This method might cause data loss, and is the least-preferred method.
Using the CLI, you can reboot the device from a remote host.
Restrictions and guidelines for device reboot
For data security, the device does not reboot while it is performing file operations.
Rebooting the device immediately at the CLI
Prerequisites
Perform the following steps in any view:
1. Verify that the next-startup configuration file is correctly specified.
display startup
For more information about the display startup command, see configuration file management commands in the command reference for the device.
2. Verify that the startup image files are correctly specified.
display boot-loader
If one main startup image file is damaged or does not exist, you must specify another main startup image file before rebooting the device.
For more information about the display boot-loader command, see software upgrade commands in the command reference for the device.
3. Save the running configuration to the next-startup configuration file.
save
To avoid configuration loss, save the running configuration before a reboot.
For more information about the save command, see configuration file management commands in the command reference for the device.
Procedure
To reboot the device immediately at the CLI, execute one of the following commands in user view:
reboot [ slot slot-number ] [ force ]
|
CAUTION: · A device reboot might result in a service outage. Before using this command, make sure you understand its impact on the live network. · Use the force keyword to reboot the device only when the system is faulty or fails to start up normally. A forced device reboots might cause file system damage. Before using the force keyword to reboot the device, make sure you understand its impact. |
Scheduling a device reboot
Restrictions and guidelines
The device supports only one device reboot schedule. If you execute the scheduler reboot command multiple times, the most recent configuration takes effect.
Procedure
To schedule a reboot, execute one of the following commands in user view:
· scheduler reboot at time [ date ]
· scheduler reboot delay time
By default, no device reboot time is specified.
|
CAUTION: This task enables the device to reboot at a scheduled time, resulting in service interruption. Before using this command, make sure you understand its impact on the live network. |
Restoring the factory-default configuration
About this task
If you want to use the device in a different scenario or you cannot troubleshoot the device by using other methods, use this task to restore the factory-default configuration.
This task does not delete .bin files and license files.
Restrictions and guidelines
This feature is disruptive.
Procedure
1. Execute the following command in user view to restore the factory-default configuration for the device:
restore factory-default
2. Reboot the device.
reboot
|
CAUTION: This command restores the device to the factory default settings. Before using this command, make sure you understand its impact on the live network. |
When the command prompts you to choose whether to save the running configuration, enter N. If you choose to save the running configuration, the device loads the saved configuration at startup.
Display and maintenance commands for device management configuration
Execute display commands in any view. Execute the reset scheduler logfile command in user view. Execute reset version-update-record in system view.
|
Task |
Command |
|
Display device alarm information. |
display alarm [ slot slot-number ] |
|
Display the system time, date, time zone, and daylight saving time. |
display clock |
|
Display the copyright statement. |
display copyright |
|
Display CPU usage statistics. The core keyword is mutually exclusive with the control-plane and data-plane keywords. |
display cpu-usage [ control-plane | data-plane ] [ summary ] [ slot slot-number [ cpu cpu-number [ core { core-number | all } ] ] ] |
|
Display CPU usage monitoring settings. |
display cpu-usage configuration [ slot slot-number [ cpu cpu-number ] ] |
|
Display the historical CPU usage statistics in a coordinate system. |
display cpu-usage history [ job job-id ] [ slot slot-number [ cpu cpu-number ] ] |
|
Display hardware information. |
display device [flash | usb ] [ slot slot-number | verbose ] |
|
Display electronic label information for the device. |
display device manuinfo [ slot slot-number [ subslot subslot-number ] ] |
|
Display electronic label information for a fan tray. |
display device manuinfo slot slot-number fan fan-id |
|
Display electronic label information for a power module. |
display device manuinfo slot slot-number power power-id |
|
Display or save operating information for features and hardware modules. |
display diagnostic-information [ hardware | ifmgr | infrastructure | l2 | l3 | service ] [ key-info ] [ filename ] |
|
Display device temperature information. |
display environment [ slot slot-number ] |
|
Display the operating states of fan trays. |
display fan [ slot slot-number [ fan-id ] ] [ verbose ] |
|
Display memory usage statistics. |
display memory [ summary ] [ slot slot-number [ cpu cpu-number ] ] |
|
Display memory alarm thresholds and statistics. |
display memory-threshold [ slot slot-number [ cpu cpu-number ] ] |
|
Display power module information. |
display power [ slot slot-number [ power-id | verbose ] ] |
|
Display job configuration information. |
display scheduler job [ job-name ] |
|
Display job execution log information. |
display scheduler logfile |
|
Display the automatic reboot schedule. |
display scheduler reboot |
|
Display schedule information. |
display scheduler schedule [ schedule-name ] |
|
Display system stability and status information. |
display system stable state [ summary ] |
|
Display system version information. |
display version |
|
Display startup software image upgrade records. |
display version-update-record |
|
Clear job execution log information. |
reset scheduler logfile |
|
Clear startup software image upgrade records. |
reset version-update-record |