- Table of Contents
-
- 10-Security Configuration Guide
- 00-Preface
- 01-AAA Configuration
- 02-802.1X Configuration
- 03-MAC Authentication Configuration
- 04-Portal Configuration
- 05-Password Control Configuration
- 06-Public Key Configuration
- 07-IPsec Configuration
- 08-SSH Configuration
- 09-Packet-Filter Firewall Configuration
- 10-ALG Configuration
- 11-Session Management Configuration
- 12-TCP and ICMP Attack Protection Configuration
- 13-IP Source Guard Configuration
- 14-ARP Attack Protection Configuration
- 15-URPF Configuration
- 16-COPS Configuration
- 17-FIPS Configuration
- 18-PKI Configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 16-COPS Configuration | 163.07 KB |
Contents
Setting the COPS response timeout time
Setting the reconnection attempt interval
Setting the shared key for COPS packet exchange
Displaying and maintaining COPS
A COPS connection cannot be established after the COPS scheme is referenced
COPS overview
Common Open Policy Service (COPS) is a simple query and response protocol that can be used to exchange policy information between a policy server and its clients. For example, COPS can be used to perform policy-based admission control over Resource Reservation Protocol (RSVP) signaling messages. Through the interaction between the clients and the server, all RSVP signaling messages can be monitored and controlled in a centralized way. This helps realize negotiation, scheduling, and implementation of end-to-end resources on the overall network.
In addition, COPS is also a service-oriented network management protocol. It can be used to perform policy-based admission control over a variety of network applications, such as quality of service (QoS), network access, and firewall. H3C devices can act as clients to interact with the remote policy server and implement policy-based admission control over 802.1X services.
COPS defines policy decision point (PDP) and policy enforcement point (PEP) in its communication model. A PDP is a policy server, and a PEP is a client. They can exchange policy information through COPS.
COPS characteristics
A PEP and a PDP exchange COPS messages as follows. The PEP sends policy requests, policy updates, and policy deletes to the remote PDP and the PDP returns decisions back to the PEP. COPS has the following characteristics:
· Using TCP as its transport layer protocol for reliable exchange of messages between clients and the server.
· Providing extensibility to support a variety of client services without the need of modifying COPS.
· Providing message level security for authentication, replay protection, and message integrity. IP Security (IPsec) and Transport Layer Security (TLS) can be leveraged to authenticate and protect the exchanged messages between the PEP and the PDP.
· A client and a server share requests and decisions. A policy request sent by a PEP is stored in the remote PDP until the PEP requests to remove it. For a policy request, the PDP can make a solicited decision right after the request is received, or make an unsolicited decision when status changes. A PEP modifies its local decision to keep it consistent with that on the PDP after receiving the decision.
· A PDP can configure a policy for a PEP and issue decisions to the PEP according to the policy. In case the policy is not available, the PDP can notify the PEP to remove its local decisions.
COPS interaction
Figure 1 shows the COPS message interaction process.
Figure 1 COPS message interaction process
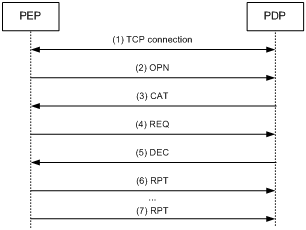
1. After startup, the PEP initiates a TCP connection request to the PDP. After the TCP connection is established, the PEP and PDP exchange COPS messages through the connection.
2. The PEP sends a Client-Open (OPN) message to the PDP to request a COPS connection. This message notifies the PDP of the client type supported by the PEP.
3. If the PDP supports the client type, it returns a Client-Accept (CAT) message to the PEP. Otherwise, it returns a Client-Close (CC) message. After the COPS connection is established, the PEP and the PDP send each other Keep-Alive (KA) messages to keep the COPS connection.
4. The PEP sends a Request (REQ) message to the PDP to request a policy for a specific service, and starts the response timeout timer. If the PEP does not receive any response from the PDP within the specified response timeout timer, it removes the REQ state immediately and notifies the PDP to remove the saved REQ state.
5. After receiving the REQ message from the PEP, the PDP replies a Decision (DEC) message containing decision content to the PEP.
6. After receiving the DEC message, the PEP conducts service processing according to the decision defined in the DEC message, and sends a Report (RPT) message to notify the PDP of the processing result. The PDP can update and remove the decision at any time. If the PEP receives a DEC message after the response timeout timer expires, the PEP does not process the message.
7. If the PDP specifies the interval for reporting accounting information when the PDP and the PEP establish the COPS connection, the PEP periodically sends RPT messages containing accounting information to the PDP after the PEP receives the DEC message.
COPS applications
COPS can be applied to 802.1X authentication to implement authorization policy control over 802.1X users. Figure 2 shows a typical network diagram.
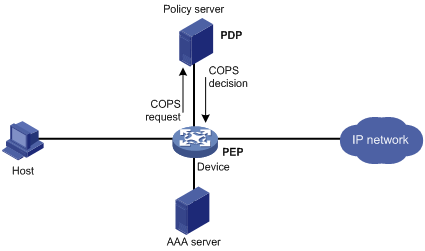
After the PEP starts, it establishes a COPS connection with the PDP according to the COPS configuration. After a 802.1X user passes authentication and gets online, the PEP and the PDP interact as follows:
· As the PEP, the device sends the PDP a REQ message containing the online user information (username, host IP address, host MAC address, access port number), to request authorization information for the user (such as VLAN and ACL) from the PDP.
· According to the submitted user information and the PDP’s policy configuration, the PDP sends the PEP a DEC message containing the authorization information. When the user is online, the PDP can update the authorization information for the user at any time.
· If the accounting interval is specified on the PDP, the PEP periodically sends RPT messages containing accounting information to the PDP when the user is online.
· After the user gets offline, the PEP notifies the PDP to remove the policy request for the user.
|
|
NOTE: If both COPS and another protocol such as RADIUS are configured on the access device for user authorization, only COPS is effective. For more information about other authorization schemes, see the chapter “Configuring AAA.” |
Protocols and standards
· RFC 2748, Common Open Policy Service
COPS configuration task list
COPS configuration includes configuring the COPS client ID and configuring a COPS scheme. A COPS scheme takes effect after being referenced by a service module. Only 802.1X can reference COPS schemes. For more information, see the chapter “Configuring 802.1X.”
Complete the following tasks to configure COPS:
|
Task |
Remarks |
|
|
Required |
||
|
Required |
||
|
Required |
||
|
Optional |
||
|
Optional |
||
|
Optional |
||
|
|
NOTE: After a COPS scheme is referenced by a service module, modifications to the COPS scheme do not take effect immediately. To bring them into effect, cancel the reference of the COPS scheme for the service module and then reference the COPS scheme again. |
Setting the COPS client id
As a PEP, the device uses a COPS client ID to identify itself. The COPS client ID and the interface information of the COPS service compose the PEP ID in the OPN packet sent to the PDP. The PDP uses the PEP ID to identify the PEP.
To set the COPS client ID:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Set the COPS client ID. |
cops id pep-id |
By default, no COPS client ID is configured. |
|
|
NOTE: · One device can be configured with only one COPS client ID. · If multiple PEPs communicate with the same PDP, make sure that the COPS client ID configured on each PEP is unique. |
Configuring a COPS scheme
Creating a COPS scheme
To create a COPS scheme:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Create a COPS scheme, and enter its view. |
cops scheme scheme-name |
By default, no COPS scheme exists. |
|
|
NOTE: The device supports up to 16 COPS schemes. |
Specifying a PDP
Up to two PDPs can be specified in a COPS scheme, and they function as the primary PDP and backup PDP according to the order they are specified.
To specify a PDP:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter COPS scheme view. |
cops scheme cops-scheme-name |
N/A |
|
3. Specify a PDP. |
server ipv4 ipv4-address [ port port-number ] |
By default, no PDP is specified. |
|
|
NOTE: The PEP first tries to establish a TCP connection to the primary PDP. If the attempt fails, the PEP contacts the backup PDP. The PEP will not stop until a connection is successfully established or the reference of the COPS scheme is cancelled. |
Setting the COPS response timeout time
After the PEP sends a REQ message to the PDP, the PEP starts the response timeout timer. If the PEP does not receive any response from the PDP before the timer expires, it directly removes the REQ message and notifies the service module.
To set the COPS response timeout time
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter COPS scheme view. |
cops scheme scheme-name |
N/A |
|
3. Set the COPS response timeout time. |
timer response timeout time |
Optional. 5 seconds by default. |
Setting the reconnection attempt interval
If the PEP fails to establish a COPS connection with a PDP, or the COPS connection willrn down because the keep-alive (KA) timer times out, the PEP tries to establish a COPS connection with the other PDP if two PDPs are specified. The attempt to establish a connection with either of the PDPs will not stop until a connection is successfully established or the reference of the COPS scheme is cancelled. If only one PDP is specified, the PEP tries to establish a COPS connection with the PDP repeatedly until the connection is successfully established or the reference of the COPS scheme is cancelled. The reconnection attempt interval specifies the time interval from when the current connection attempt fails to when the next connection attempt is initiated.
To set the reconnection attempt interval
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter COPS scheme view. |
cops scheme scheme-name |
N/A |
|
3. Set the reconnection attempt interval. |
timer reconnect interval interval |
Optional. 60 seconds by default. |
Setting the shared key for COPS packet exchange
A shared key helps verify the integrity of the COPS packets transferred between a PEP and a PDP and make sure that the PEP communicates with the correct PDP. The sender uses the specified algorithm and shared key to generate a digest carried in COPS packets. After receiving the COPS packets, the receiver uses the same algorithm and shared key to generate a digest and compare it against the digest in the received packets. If they are the same, the packets pass the integrity check. Otherwise, the receiver drops the packets.
To set the shared key for COPS packet exchange:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter COPS scheme view. |
cops scheme scheme-name |
N/A |
|
3. Set the shared key for COPS packet exchange. |
key key-string [ algorithm hmac-md5-96 ] |
Optional. By default, no shared key is configured. |
|
|
NOTE: The configuration of shared key on the PEP must be consistent with that on the PDP. That is, if a shared key is configured on the PEP, the same one must be configured on the PDP. If no shared key is configured on the PEP, do not configure a shared key on the PDP either. |
Displaying and maintaining COPS
|
Task |
Command |
Remarks |
|
Display COPS connection information. |
display cops connection [ slot slot-number ] [ | { begin | exclude | include } regular-expression ] |
Available in any view |
|
|
NOTE: The COPS connection information is available only after the COPS scheme is referenced by a service module. |
COPS configuration example
Network requirements
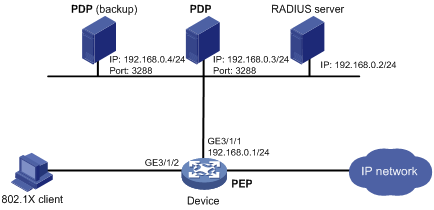
As shown in Figure 3, the 802.1X client connects to GigabitEthernet 3/1/2 of the device, and the device connects to two PDPs and one RADIUS server. The requirements are as follows:
· The device uses the RADIUS server to perform authentication and accounting for the 802.1X user.
· After the 802.1X user passes authentication, the device functions as the PEP to request user authorization attributes from the PDP.
· The two PDPs back up each other. The IP address of the primary PDP is 192.168.0.3/24, and the IP address of the backup PDP is 192.168.0.4/24.
· The reconnection attempt interval is 30 seconds, the response timeout time is 10 seconds, the shared key is abcdefg, and the HMAC-MD5-96 algorithm is adopted.
Configuration procedure
|
|
NOTE: · Configure the RADIUS server to make sure that authentication and accounting operate normally. · Configure the PDPs, including COPS connection parameters, usernames, and their authorization attributes (such as VLAN and ACL). · The following involves part of AAA and RADIUS configurations. For more information, see the chapter “Configuring AAA.” |
1. Configure the RADIUS scheme.
<Device> system-view
# Create RADIUS scheme radius1 and enter its view.
[Device] radius scheme radius1
# Specify the primary authentication server, the primary accounting server, and the authentication and accounting keys.
[Device-radius-radius1] primary authentication 192.168.0.2
[Device-radius-radius1] primary accounting 192.168.0.2
[Device-radius-radius1] key authentication name
[Device-radius-radius1] key accounting money
# Configure the scheme to exclude the domain names from usernames sent to the RADIUS server. (optional, keep this configuration consistent with that configured on the server)
[Device-radius-radius1] user-name-format without-domain
[Device-radius-radius1] quit
2. Configure the authentication domain.
# Create ISP domain bbb and enter its view.
[Device] domain bbb
# Configure the authentication and accounting methods for the domain.
[Device-isp-bbb] authentication lan-access radius-scheme radius1
[Device-isp-bbb] accounting lan-access radius-scheme radius1
[Device-isp-bbb] quit
3. Configure COPS.
# Set the COPS client ID as 192.168.0.1.
[Device] cops id 192.168.0.1
# Create COPS scheme cops1x and enter its view.
[Device] cops scheme cops1x
# Specify the primary PDP with IP address 192.168.0.3 and port number 3288.
[Device-cops-cops1x] server ipv4 192.168.0.3 port 3288
# Specify the backup PDP with IP address 192.168.0.4 and port number 3288.
[Device-cops-cops1x] server ipv4 192.168.0.4 port 3288
# Set the COPS reconnection attempt interval to 30 seconds.
[Device-cops-cops1x] timer reconnect interval 30
# Set the COPS response timeout timer to 10 seconds.
[Device-cops-cops1x] timer response timeout 10
# Set the shared key for COPS message exchange to abcdefg, and specify the HMAC-MD5-96 algorithm.
[Device-cops-cops1x] key abcdefg algorithm hmac-md5-96
[Device-cops-copa1x] quit
4. Configure 802.1X.
# Enable 802.1X globally.
[Device] dot1x
# Enable 802.1X on GigabitEthernet 3/1/2.
[Device] dot1x interface GigabitEthernet 3/1/2
# Configure 802.1X to reference COPS scheme cops1x.
[Device] dot1x cops cops1x
Verifying the configuration
After 802.1X references the COPS scheme, the device establishes a COPS connection with the primary PDP. To view COPS connection information, use the display cops connection command:
[Device] display cops connection
PEP ID: 192.168.0.1-s0
Client Type: COPS-1X Status: UP
Connection Losts: 2 Reconnections: 4
KA Timer: 30s ACCT Timer: 600s
Reconnect Interval: 30s Response Timeout: 10s
Current TCP Connection:
PEP: 192.168.0.1/1031
PDP: 192.168.0.3/3288
Last TCP Connection:
PEP: 192.168.0.1/1031
PDP: 192.168.0.4/3288
TX:
REQ: Succ 101, Fail 4
RPT: Succ 100, Fail 1
OPN: Succ 1, Fail 0
KA: Succ 5, Fail 0
DRQ: Succ 1, Fail 0
SSC: Succ 3, Fail 0
RX:
CAT: 1 KA: 5
S-DEC: 100 UNS-DEC: 2 SSQ: 3
After the user passes 802.1X authentication, the PDP assigns the authorization attributes to the 802.1X user. To view online user connection information, use the display connection command.
Troubleshooting COPS
A COPS connection cannot be established after the COPS scheme is referenced
Symptom:
After the PEP initiates a policy request, the PDP does not return any response.
Analysis:
· The COPS client ID is not configured for the PEP device.
· The COPS scheme referenced by the service module is not configured.
· No PDP is specified or a wrong PDP is specified in the COPS scheme referenced by the service module.
· The shared key set in the COPS scheme referenced by the service module is not consistent with that configured on the specified PDP in the scheme.
Solution:
· Set the COPS client ID for the PEP device.
· Reference the COPS scheme for the service module.
· Specify the correct PDP in the COPS scheme.
· Make sure that the shared key in the COPS scheme is consistent with that configured on the specified PDP.
