- Table of Contents
-
- 05-Network Connectivity Configuration Guide
- 00-Preface
- 01-About the network connectivity configuration guide
- 02-MAC address table configuration
- 03-Ethernet link aggregation configuration
- 04-Port isolation configuration
- 05-VLAN configuration
- 06-Loop detection configuration
- 07-Spanning tree configuration
- 08-LLDP configuration
- 09-Layer 2 forwarding configuration
- 10-L2TP configuration
- 11-ARP configuration
- 12-IP addressing configuration
- 13-DHCP configuration
- 14-DHCP snooping configuration
- 15-DHCPv6 configuration
- 16-DHCPv6 snooping configuration
- 17-DNS configuration
- 18-HTTP configuration
- 19-HTTP redirect configuration
- 20-IP forwarding basics configuration
- 21-Fast forwarding configuration
- 22-Adjacency table configuration
- 23-IP performance optimization configuration
- 24-IPv6 basics configuration
- 25-IPv6 neighbor discovery configuration
- 26-IPv6 fast forwarding configuration
- 27-IPv6 transition technologies configuration
- 28-NAT configuration
- 29-GRE configuration
- 30-Basic IP routing configuration
- 31-Static routing configuration
- 32-OSPF configuration
- 33-Policy-based routing configuration
- 34-IPv6 static routing configuration
- 35-IPv6 policy-based routing configuration
- 36-Multicast overview
- 37-IGMP snooping configuration
- 38-MLD snooping configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 23-IP performance optimization configuration | 198.02 KB |
Contents
IP performance optimization tasks at a glance
Enabling an interface to forward directed broadcasts destined for the directly connected network
About forwarding broadcasts destined for the directly connected network
Setting the MTU of IPv4 packets sent over an interface
Configuring IPv4 virtual fragment reassembly
About IPv4 virtual fragment reassembly
Enabling IPv4 virtual fragment reassembly
Set the aging time of packet fragments cached for VFR
Enabling sending ICMP error messages
About sending ICMP error messages
Enabling sending ICMP redirect messages
Enabling sending ICMP time exceeded messages
Enable sending ICMP destination unreachable messages
Configuring rate limit for ICMP error messages
Specifying the source address for ICMP packets
Disabling sending a specific type of ICMP messages
Disabling receiving a specific type of ICMP messages
Setting TCP MSS for an interface
Configuring TCP path MTU discovery
Configuring TCP congestion control algorithm for TCP proxy
Enabling SNMP notifications for TCP events
Verifying and maintaining IP performance optimization
Displaying and clearing IP packet statistics
Displaying RawIP connection information
Displaying TCP connection information
Displaying UDP connection information
Displaying information about UDP socket load balancing
Displaying and clearing UDP traffic statistics
Optimizing IP performance
In this document, the term router refers to a routing-capable device.
IP performance optimization tasks at a glance
All IP performance optimization tasks are optional.
1. Configuring features for IP packets
¡ Enabling an interface to forward directed broadcasts destined for the directly connected network
¡ Setting the MTU of IPv4 packets sent over an interface
¡ Configuring IPv4 virtual fragment reassembly
2. Configuring features for ICMP messages
¡ Enabling sending ICMP error messages
¡ Configuring rate limit for ICMP error messages
¡ Specifying the source address for ICMP packets
¡ Disabling sending a specific type of ICMP messages
¡ Disabling receiving a specific type of ICMP messages
3. Configuring features for TCP packets
¡ Configuring TCP path MTU discovery
¡ Configuring TCP congestion control algorithm for TCP proxy
¡ Enabling SNMP notifications for TCP events
Enabling an interface to forward directed broadcasts destined for the directly connected network
About forwarding broadcasts destined for the directly connected network
A directed broadcast packet is destined for all hosts on a specific network. In the destination IP address of the directed broadcast, the network ID identifies the target network, and the host ID is made up of all ones.
You can configure this function to enable the interface to forward directed broadcast packets that are destined for directly connected network.
Procedure
system-view
2. Enter interface view.
interface interface-type interface-number
3. Enable the interface to forward directed broadcasts destined for the directly connected network.
ip forward-broadcast
By default, an interface cannot forward directed broadcasts destined for the directly connected network.
Example: Enabling an interface to forward directed broadcasts destined for the directly connected network
Network configuration
As shown in Figure 1, the default gateway of the host is the IP address 1.1.1.2/24 of GigabitEthernet 1/0/1 of Router A. Configure a static route destined for the host on Router B. Router B can receive directed broadcasts from the host to IP address 2.2.2.255.
Procedure
1. Configure Router A:
# Specify IP addresses for GigabitEthernet 1/0/1 and GigabitEthernet 1/0/2.
<RouterA> system-view
[RouterA] interface gigabitethernet 1/0/1
[RouterA-GigabitEthernet1/0/1] ip address 1.1.1.2 24
[RouterA-GigabitEthernet1/0/1] quit
[RouterA] interface gigabitethernet 1/0/2
[RouterA-GigabitEthernet1/0/2] ip address 2.2.2.2 24
# Enable GigabitEthernet 1/0/2 to forward directed broadcasts destined for the directly connected network.
[RouterA-GigabitEthernet1/0/2] ip forward-broadcast
2. Configure Router B:
# Configure a static route to the host.
<RouterB> system-view
[RouterB] ip route-static 1.1.1.1 24 2.2.2.2
# Specify an IP address for GigabitEthernet 1/0/2.
[RouterB] interface gigabitethernet 1/0/2
[RouterB-GigabitEthernet1/0/2] ip address 2.2.2.1 24
Verifying the configuration
After the configurations are completed, if you ping the subnet-directed broadcast address 2.2.2.255 on the host, GigabitEthernet 1/0/2 of Router B can receive the ping packets. If you delete the ip forward-broadcast configuration on any router, GigabitEthernet 1/0/2 of Router B cannot receive the ping packets.
Example: Enabling an interface to forward directed broadcasts destined for the directly connected network
Network configuration
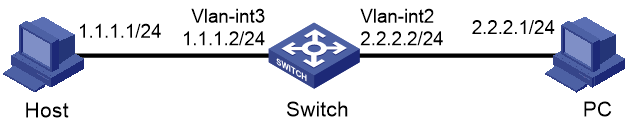
As shown in Figure 2, the default gateway of the host is 1.1.1.2/24, the IP address of VLAN-interface 3 of the switch.
The PC can receive directed broadcasts from the host to IP address 2.2.2.255.
Procedure
1. Specify IP addresses for VLAN-interface 3 and VLAN-interface 2.
<Switch> system-view
[Switch] interface vlan-interface 3
[Switch-Vlan-interface3] ip address 1.1.1.2 24
[Switch-Vlan-interface3] quit
[Switch] interface vlan-interface 2
[Switch-Vlan-interface2] ip address 2.2.2.2 24
2. Enable VLAN-interface 2 to forward directed broadcasts directed for the directly connected network.
[Switch-Vlan-interface2] ip forward-broadcast
Verifying the configuration
After the configurations are completed, if you ping the subnet-directed broadcast address 2.2.2.255 on the host, the PC can receive the ping packets. If you remove the ip forward-broadcast configuration on the switch, the PC cannot receive the ping packets.
Setting the MTU of IPv4 packets sent over an interface
About this task
When a packet exceeds the MTU of IPv4 packets sent over an interface, the device processes the packet in one of the following ways:
· If the packet disallows fragmentation, the device discards it.
· If the packet allows fragmentation, the device fragments it and forwards the fragments.
Fragmentation and reassembling consume system resources, so set the MTU based on the network environment to avoid fragmentation.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Set the MTU of IPv4 packets sent over the interface.
ip mtu mtu-size
By default, the MTU of IPv4 packets sent over an interface is not set.
Configuring IPv4 virtual fragment reassembly
About IPv4 virtual fragment reassembly
To prevent each service module from processing packet fragments that do not arrive in order, you can enable the virtual fragment reassembly (VFR) feature. This feature virtually reassembles the fragments of a datagram through fragment check, sequencing, and caching, ensuring fragments arrive at each service module in order.
Enabling IPv4 virtual fragment reassembly
About this task
In addition to fragment check, sequencing, and caching, VFR can detect and prevent the following types of attacks:
· Tiny fragment attack—The first fragment size is too small to hold the Layer 4 (such as TCP and UDP) header field, which is forced into the second fragment. VFR discards all tiny fragments.
· Overlapping fragment attack—Two consecutive incoming fragments are identical or overlap with each other. If an overlapping fragment is detected, VFR discards all fragments within a fragment chain.
· Fragment flooding attack—The maximum number of concurrent preassemblies or the number of fragments per datagram exceeds the upper limits. VFR discards subsequent fragments if the upper limit is reached.
Restrictions and guidelines
The enabling status of VFR can be managed through CLI or controlling the enabling status of a service module that can call VFR. VRF is enabled in either of the following conditions:
· A service module that can call it is enabled.
· The ip virtual-reassembly enable command is executed.
If fragment reassembly is required, but a service module cannot call it, execute this command at CLI.
Procedure
1. Enter system view.
system-view
2. Enable IPv4 virtual fragment reassembly.
ip virtual-reassembly enable
By default, IPv4 virtual fragment reassembly is disabled.
Set the aging time of packet fragments cached for VFR
About this task
With virtual fragment reassembly enabled, the device sets an aging timer for each cached fragment. When the timer of a packet fragment expires, the device discards the fragment. You can perform this task to set the aging time as needed.
Fragments of different packets in the cache queue might have the same packet ID, especially when the device has cached a large number of packet fragments. If a fragment is lost, the system might mistakenly use a fragment of a later received packet that has the same packet ID to substitute for the lost one, causing reassembly errors. To resolve this issue, set a short aging time as a best practice to reduce cached fragments if a large number of packets are cached for a service and packet loss occurs.
Restrictions and guidelines
This task takes effect only when IPv4 virtual fragment reassembly is enabled.
Procedure
1. Enter system view.
system-view
2. Set the aging time for cached packet fragments.
ip virtual-reassembly aging aging-milliseconds
By default, the aging time for cached packet fragments is 3000 milliseconds.
Enabling sending ICMP error messages
About sending ICMP error messages
ICMP messages are used by network layer and transport layer protocols to communicate updates and errors with other devices, facilitating network management.
Sending excessive ICMP messages increases network traffic. The device performance degrades if it receives a lot of malicious ICMP messages that cause it to respond with ICMP error messages. To prevent such problems, the sending of ICMP error messages is disabled by default. You can enable sending ICMP error messages of different types as needed.
ICMP error messages include redirect messages, time exceeded messages, and destination unreachable messages.
Enabling sending ICMP redirect messages
About this task
A host that has only one default route sends all packets to the default gateway. The default gateway sends an ICMP redirect message (packet type field set to 5) to inform the host of a correct next hop by following these rules:
· The receiving and sending interfaces are the same.
· The packet source IP address and the IP address of the packet receiving interface are on the same segment.
· There is no source route option in the received packet.
ICMP redirect messages simplify host management and enable hosts to gradually optimize their routing table.
For more information about the packet type field, see RFC792.
Procedure
1. Enter system view.
system-view
2. Enable sending ICMP redirect messages.
ip redirects enable
By default, the device does not send ICMP redirect messages.
Enabling sending ICMP time exceeded messages
About this task
A device sends ICMP time exceeded messages (packet type field set to 11) by following these rules:
· The device sends the source an ICMP TTL exceeded in transit message (packet type field set to 0) when the following conditions are met:
¡ The received packet is not destined for the device.
¡ The TTL field of the packet is 1.
· When the device receives the first fragment of an IP datagram destined for it, it starts a timer. If the timer expires before all the fragments of the datagram are received, the device sends an ICMP fragment reassembly time exceeded message (packet type field set to 1) to the source.
For more information about the packet type field, see RFC792.
Restrictions and guidelines
If the ICMP time exceeded message sending is disabled, the device does not send ICMP TTL exceeded in transit messages. However, it can still send ICMP fragment reassembly time exceeded messages.
Procedure
1. Enter system view.
system-view
2. Enable sending ICMP time exceeded messages.
ip ttl-expires enable
By default, the device does not send ICMP time exceeded messages.
Enable sending ICMP destination unreachable messages
About this task
A device sends ICMP destination unreachable messages (packet type field set to 3) by following these rules:
· The device sends the source an ICMP network unreachable message when the following conditions are met:
¡ The packet does not match any route.
¡ No default route exists in the routing table.
· The device sends the source an ICMP protocol unreachable message when the following conditions are met:
¡ The packet is destined for the device.
¡ The transport layer protocol of the packet is not supported by the device.
· The device sends the source an ICMP port unreachable message when the following conditions are met:
¡ The UDP packet is destined for the device.
¡ The packet's port number does not match the corresponding process.
· The device sends the source an ICMP source route failed message when the following conditions are met:
¡ The source uses Strict Source Routing to send packets.
¡ The intermediate device finds that the next hop specified by the source is not directly connected.
· The device sends the source an ICMP fragmentation needed and DF set message when the following conditions are met:
¡ The MTU of the sending interface is smaller than the packet.
¡ The packet has DF set.
For more information about the packet type field, see RFC792.
Restrictions and guidelines
If a DHCP-enabled device does not send any ICMP echo requests, but receives an ICMP echo reply, the device will not send any ICMP protocol unreachable messages to the source. To enable DHCP, use the dhcp enable command. For more information about this command, see DHCP commands in Network Connectivity Command Reference.
Procedure
1. Enter system view.
system-view
2. Enable sending ICMP destination unreachable messages.
ip unreachables enable
By default, the device does not send ICMP destination unreachable messages.
Configuring rate limit for ICMP error messages
About this task
To avoid sending excessive ICMP error messages within a short period that might cause network congestion, you can limit the rate at which ICMP error messages are sent. A token bucket algorithm is used with one token representing one ICMP error message.
A token is placed in the bucket at intervals until the maximum number of tokens that the bucket can hold is reached.
A token is removed from the bucket when an ICMP error message is sent. When the bucket is empty, ICMP error messages are not sent until a new token is placed in the bucket.
Procedure
1. Enter system view.
system-view
2. Set the interval for tokens to arrive in the bucket and the bucket size for ICMP error messages.
ip icmp error-interval interval [ bucketsize ]
By default, a token is placed in the bucket at intervals of 100 milliseconds and the bucket allows a maximum of 10 tokens.
To disable the ICMP rate limit, set the interval to 0 milliseconds.
Specifying the source address for ICMP packets
About this task
Specifying the source IP address for outgoing ping echo requests and ICMP error messages (including Time Exceeded, Port Unreachable, and Parameter Problem messages) helps users locate the sending device easily. As a best practice, specify the IP address of the loopback interface as the source IP address.
Restrictions and guidelines
For ICMP echo requests, the source IP address specified in the ping command has higher priority than the source IP address specified in the ip icmp source command.
Procedure
1. Enter system view.
system-view
2. Specify the source address for outgoing ICMP packets.
ip icmp source ip-address
By default, no source address is specified for outgoing ICMP packets. The default source IP addresses for different types of ICMP packets vary as follows:
¡ For an ICMP error message, the source IP address is the IP address of the receiving interface of the packet that triggers the ICMP error message. ICMP error messages include Time Exceeded, Port Unreachable, and Parameter Problem messages.
¡ For an ICMP echo request, the source IP address is the IP address of the sending interface.
¡ For an ICMP echo reply, the source IP address is the destination IP address of the ICMP echo request specific to this reply.
Disabling sending a specific type of ICMP messages
About this task
By default, the device sends all types of ICMP messages except Destination Unreachable, Time Exceeded, and Redirect messages. Attackers might obtain information from specific types of ICMP messages, causing security issues.
For security purposes, you can perform this task to disable sending ICMP messages of specific types.
Restrictions and guidelines
Disabling sending ICMP messages of a specific type might affect network operation. Please use this feature with caution.
To enable sending Destination Unreachable, Time Exceeded, or Redirect messages, you can perform one of the following tasks:
· Execute the ip icmp send enable command.
· Execute one of the following commands as needed:
¡ ip unreachables enable
¡ ip ttl-expires enable
¡ ip redirects enable
Procedure
1. Enter system view.
system-view
2. Disable the device from sending a specific type of ICMP messages.
undo ip icmp { name icmp-name | type icmp-type code icmp-code } send enable
By default, the device can send all types of ICMP messages except Destination Unreachable, Time Exceeded, and Redirect messages.
Disabling receiving a specific type of ICMP messages
About this task
By default, the device receives all types of ICMP messages. Such a setting might affect device performance if a large number of ICMP responses are received within a short time. To solve this issue, you can perform this task to disable the device from receiving a specific type of ICMP messages.
Restrictions and guidelines
Disabling receiving ICMP messages of a specific type might affect network operation. Please use this feature with caution.
Procedure
1. Enter system view.
system-view
2. Disable the device from receiving a specific type of ICMP messages.
undo ip icmp { name icmp-name | type icmp-type code icmp-code } receive enable
By default, the device can receive all types of ICMP messages.
Setting TCP MSS for an interface
About this task
The maximum segment size (MSS) option informs the receiver of the largest segment that the sender can accept. Each end announces its MSS during TCP connection establishment. If the size of a TCP segment is smaller than the MSS of the receiver, TCP sends the TCP segment without fragmentation. If not, it fragments the segment according to the receiver's MSS.
Restrictions and guidelines
· If you set the TCP MSS on an interface, the size of each TCP segment received or sent on the interface cannot exceed the MSS value.
· This configuration takes effect only for TCP connections established after the configuration rather than the TCP connections that already exist.
· This configuration is effective only for IP packets.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Set the TCP MSS for the interface.
tcp mss value
By default, the TCP MSS is not set.
Configuring TCP path MTU discovery
About this task
TCP path MTU discovery (in RFC 1191) discovers the path MTU between the source and destination ends of a TCP connection. The device uses the path MTU to calculate the MSS to avoid IP fragmentation. The path MTU uses an aging mechanism to ensure that the source device can increase the path MTU when the minimum link MTU on the path increases.
TCP path MTU discovery works as follows:
1. A TCP source device sends a packet with the Don't Fragment (DF) bit set.
2. A router discards the packet that exceeds the MTU of the outgoing interface and returns an ICMP error message. The error message contains the MTU of the outgoing interface.
3. Upon receiving the ICMP message, the TCP source device calculates the current path MTU of the TCP connection.
4. The TCP source device sends subsequent TCP segments that are smaller than the MSS (MSS = path MTU – IP header length – TCP header length).
If the TCP source device still receives ICMP error messages when the MSS is smaller than 32 bytes, the TCP source device will fragment packets.
An ICMP error message received from a router that does not support RFC 1191 has the MTU of the outgoing interface set to 0. Upon receiving the ICMP message, the TCP source device selects the path MTU smaller than the current path MTU from the MTU table as described in RFC 1191. Based on the selected path MTU, the TCP source device calculates the TCP MSS. The MTU table contains MTUs of 68, 296, 508, 1006, 1280, 1492, 2002, 4352, 8166, 17914, 32000, and 65535 bytes. Because the minimum TCP MSS specified by the system is 32 bytes, the actual minimum MTU is 72 bytes.
The aging mechanism of the path MTU is as follows:
· When the TCP source device receives an ICMP error message, it reduces the path MTU and starts an aging timer for the path MTU.
· After the aging timer expires, the source device uses a larger MSS in the MTU table, as described in RFC 1191.
· If no ICMP error message is received within two minutes, the source device increases the MSS again until the MSS negotiated during TCP three-way handshake is reached.
Prerequisites
Make sure all devices on a TCP connection are enabled to send ICMP error messages by using the ip unreachables enable command.
Procedure
1. Enter system view.
system-view
2. Enable TCP path MTU discovery.
tcp path-mtu-discovery [ aging age-time | no-aging ]
By default, TCP path MTU discovery is disabled.
Enabling SYN Cookie
About this task
A TCP connection is established through a three-way handshake. An attacker can exploit this mechanism to mount SYN Flood attacks. The attacker sends a large number of SYN packets, but does not respond to the SYN ACK packets from the server. As a result, the server establishes a large number of TCP semi-connections and can no longer handle normal services.
SYN Cookie can protect the server from SYN Flood attacks. When the server receives a SYN packet, it responds with a SYN ACK packet without establishing a TCP semi-connection. The server establishes a TCP connection and enters ESTABLISHED state only when it receives an ACK packet from the client.
Procedure
1. Enter system view.
system-view
2. Enable SYN Cookie.
tcp syn-cookie enable
By default, SYN Cookie is disabled.
Setting the TCP buffer size
1. Enter system view.
system-view
2. Set the size of TCP receive/send buffer.
tcp window window-size
The default buffer size is 63 KB.
Setting TCP timers
About this task
You can set the following TCP timers:
· SYN wait timer—TCP starts the SYN wait timer after sending a SYN packet. Within the SYN wait timer if no response is received or the upper limit on TCP connection tries is reached, TCP fails to establish the connection.
· FIN wait timer—TCP starts the FIN wait timer when TCP changes the connection state to FIN_WAIT_2. If no FIN packet is received within the timer interval, TCP terminates the connection. If a FIN packet is received, TCP changes the connection state to TIME_WAIT. If a non-FIN packet is received, TCP restarts the timer, and tears down the connection when the timer expires.
Procedure
1. Enter system view.
system-view
2. Set the TCP SYN wait timer.
tcp timer syn-timeout time-value
By default, the TCP SYN wait timer is 75 seconds.
3. Set the TCP FIN wait timer.
tcp timer fin-timeout time-value
By default, the TCP FIN wait timer is 675 seconds.
Configuring TCP congestion control algorithm for TCP proxy
About this task
When you perform this task, you can configure one of the following TCP congestion control algorithms:
· Reno—Use this algorithm in scenarios with low latency and low bandwidth. In scenarios with high latency and high bandwidth, the speed of data transmission takes a long time to reach the maximum and thus the bandwidth utilization rate is low.
Reno is an early TCP congestion control algorithm that increases the number of congestion windows on receipt of ACK messages.
· BIC—Use this algorithm in scenarios with high bandwidth and low packet loss ratio.
BIC can make good use of remaining bandwidth resources and improve throughput, because this algorithm does not slow down packet sending as long as no packet loss occurs. However, the transmission latency of this algorithm is high. This algorithm will reduce the number of congestion windows when transmission errors cause packet loss.
· BBR—Use this algorithm in scenarios with high bandwidth, high latency, and packet loss.
BBR does not use packet loss as a congestion signal. In a scenario with high packet loss ratio, this algorithm can ensure high throughput and reduce transmission latency effectively. BBRv2 improves intra-protocol fairness by balancing aggressiveness.
Restrictions and guidelines
This task does not take effect on the modules that support TCP congestion control algorithm configuration. The TCP congestion control algorithm used by such a module depends on its configuration.
The modules that do not support TCP congestion control algorithm configuration use the same algorithm as the TCP proxy module.
Procedure
1. Enter system view.
system-view
2. Specify a TCP congestion control algorithm for TCP proxy.
tcp-proxy congestion-method { bbrv1 | bbrv2 | bic | reno }
By default, the TCP congestion control algorithm is Reno for TCP proxy.
Enabling SNMP notifications for TCP events
About this task
This feature enables the TCP module to generate SNMP notifications for critical TCP events, such as MD5 authentication failure in TCP connection. The SNMP notifications are sent to the SNMP module. For the SNMP notifications to be sent correctly, you must also configure SNMP. For more information about SNMP configuration, see SNMP configuration in Network Management and Monitoring Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enable SNMP notifications for TCP events.
snmp-agent trap enable tcp
By default, SNMP notifications for TCP events are enabled.
Verifying and maintaining IP performance optimization
Displaying and clearing IP packet statistics
To display IP packet statistics, execute the following command in any view:
display ip statistics [ slot slot-number ]
To clear IP packet statistics, execute the following command in user view:
reset ip statistics
reset ip statistics [ slot slot-number ]
Displaying ICMP statistics
To display ICMP statistics, execute the following command in any view:
display icmp statistics
display icmp statistics [ slot slot-number ]
Displaying RawIP connection information
Perform display tasks in any view.
· Display brief information about RawIP connections.
display rawip [ slot slot-number ]
· Display detailed information about RawIP connections.
display rawip verbose [ slot slot-number ]
Displaying TCP connection information
Perform display tasks in any view.
· Display brief information about TCP connections.
display tcp [ slot slot-number ]
· Display detailed information about TCP connections.
display tcp verbose [ slot slot-number ]
Displaying UDP connection information
Perform display tasks in any view.
· Display brief information about UDP connections.
display udp [ slot slot-number ]
· Display detailed information about UDP connections.
display udp verbose [ slot slot-number ]
Displaying information about UDP socket load balancing
Perform display tasks in any view.
· Display brief information about UDP socket load balancing.
display udp socket-loadbalance [ slot slot-number ]
· Display detailed information about UDP socket load balancing.
display udp socket-loadbalance verbose [ slot slot-number ] [ port port-number ]
Displaying and clearing UDP traffic statistics
To display UDP traffic statistics, execute the following command in any view:
display udp statistics
display udp statistics [ slot slot-number ]
To clear UDP traffic statistics, execute the following command in user view:
reset udp statistics