- Table of Contents
-
- 07-Wireless authentication
- 01-Local Portal Authentication Configuration Examples
- 02-HTTPS-Based Local Portal Authentication Configuration Examples
- 03-Remote Portal Authentication Configuration Examples
- 04-Local Portal Authentication through LDAP Server Configuration Examples
- 05-Local Portal Auth and SSID-based Auth Page Pushing Configuration Examples
- 06-Local Portal MAC-Trigger Authentication Configuration Examples
- 07-Portal MAC-Trigger Authentication Configuration Examples
- 08-Local Forwarding Mode and Local Portal MAC-Trigger Auth Configuration Examples
- 09-Local Portal Authentication (IPv6) Configuration Examples
- 10-Local Portal Authentication through LDAP Server (IPv6) Configuration Examples
- 11-Remote Portal Authentication (IPv6) Configuration Examples
- 12-Portal MAC-Trigger Authentication (IPv6) Configuration Example
- 13-Remote Portal Authentication with User Profile Authorization Configuration Examples
- 14-Portal Fail-Permit Configuration Examples
- 15-Local MAC Authentication Configuration Examples
- 16-Remote MAC Authentication Configuration Examples
- 17-Transparent Auth Through Remote MAC and Portal Auth Configuration Examples
- 18-Remote AP, Remote Portal, and MAC-Trigger Authentication Configuration Examples
- 19-MAC Authentication with Guest VLAN Assignment Configuration Examples
- 20-MAC Authentication with Guest VLAN Assignment (IPv6) Configuration Examples
- 21-Local MAC-And-802.1X Authentication Configuration Examples
- 22-Local 802.1X Authentication Configuration Examples
- 23-Local RADIUS-Based 802.1X Authentication in EAP Relay Mode Configuration Examples
- 24-Remote 802.1X Authentication Configuration Examples
- 25-Remote 802.1X Authentication (IPv6) Configuration Examples
- 26-Remote 802.1X Authentication in WPA3-Enterprise Mode Configuration Examples
- 27-802.1X Auth with ACL Assignment Through IMC Server Configuration Examples
- 28-802.1X Auth with User Profile Assignment Through IMC Server Configuration Examples
- 29-EAD Authentication Configuration Examples
- 30-EAD Authentication (IPv6) Configuration Examples
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 22-Local 802.1X Authentication Configuration Examples | 355.50 KB |
|
|
|
H3C Access Controllers |
|
Local 802.1X Authentication |
|
Configuration Examples |
Copyright © 2023 New H3C Technologies Co., Ltd. All rights reserved.
No part of this manual may be reproduced or transmitted in any form or by any means without prior written consent of New H3C Technologies Co., Ltd.
Except for the trademarks of New H3C Technologies Co., Ltd., any trademarks that may be mentioned in this document are the property of their respective owners.
The information in this document is subject to change without notice.
Introduction
The following information provides an example for configuring local 802.1X authentication on a wireless network.
Prerequisites
The following information applies to Comware-based access controllers and access points. Procedures and information in the examples might be slightly different depending on the software or hardware version of the access controllers and access points.
The configuration examples were created and verified in a lab environment, and all the devices were started with the factory default configuration. When you are working on a live network, make sure you understand the potential impact of every command on your network.
The following information is provided based on the assumption that you have basic knowledge of WLAN access, WLAN user access authentication, and 802.1X authentication.
Example: Configuring local 802.1X authentication for wireless clients
Network configuration
As shown in Figure 1, the switch acts as a DHCP server to assign IP addresses to the AP and the client.
Configure the AC to meet the following requirements:
· Perform local 802.1X authentication to control the network access of the client.
· Use open system authentication to authenticate the client at the data link layer. This is the default authentication method.
Restrictions and guidelines
When you configure local 802.1X authentication for wireless clients, follow these restrictions and guidelines:
· Use the serial ID labeled on the AP's rear panel to specify an AP.
· Local 802.1X authentication does not support EAP relay.
Procedures
Configuring the AC
1. Configure interfaces on the AC:
# Create VLAN 100 and VLAN-interface 100, and assign an IP address to the VLAN interface. The AC will use this IP address to establish CAPWAP control and data tunnels with the AP.
<AC> system-view
[AC] vlan 100
[AC-vlan100] quit
[AC] interface vlan-interface 100
[AC-Vlan-interface100] ip address 2.2.2.1 24
[AC-Vlan-interface100] quit
# Create VLAN 200 and VLAN-interface 200, and assign an IP address to the VLAN interface. VLAN 200 will be used for client access.
[AC] vlan 200
[AC-vlan200] quit
[AC] interface vlan-interface 200
[AC-Vlan-interface200] ip address 2.2.1.1 24
[AC-Vlan-interface200] quit
# Configure GigabitEthernet 1/0/1 (the port connected to the switch) as a trunk port, and assign the port to VLAN 100 and VLAN 200.
[AC] interface gigabitethernet 1/0/1
[AC-GigabitEthernet1/0/1] port link-type trunk
[AC-GigabitEthernet1/0/1] port trunk permit vlan 100 200
[AC-GigabitEthernet1/0/1] quit
2. Configure a local user:
# Create a network access user named localuser and set the password to localpass in plaintext form.
[AC] local-user localuser class network
[AC-luser-network-localuser] password simple localpass
# Set the service type to lan-access.
[AC-luser-network-localuser] service-type lan-access
[AC-luser-network-localuser] quit
3. Configure a local authentication domain:
# Create ISP domain bbb and enter its view.
[AC] domain bbb
# Configure the ISP domain to use local authentication, authorization, and accounting for LAN access wireless clients.
[AC-isp-bbb] authentication lan-access local
[AC-isp-bbb] authorization lan-access local
[AC-isp-bbb] accounting lan-access local
[AC-isp-bbb] quit
4. Set the 802.1X authentication method to CHAP.
[AC] dot1x authentication-method chap
5. Configure a service template:
# Create service template service and enter its view.
[AC] wlan service-template service
# Set the SSID of the service template to service.
[AC-wlan-st-service] ssid service
# Assign VLAN 200 to the matching clients.
[AC-wlan-st-service] vlan 200
# Set the user access authentication mode to 802.1X authentication.
[AC-wlan-st-service] client-security authentication-mode dot1x
# Specify ISP domain bbb for 802.1X authentication clients in the service template.
[AC-wlan-st-service] dot1x domain bbb
# Enable the AC to forward client data traffic. If the AC forwards client data traffic by default, skip this step.
[AC-wlan-st-service] client forwarding-location ac
# Enable the service template.
[AC-wlan-st-service] service-template enable
[AC-wlan-st-service] quit
6. Configure AP settings:
|
IMPORTANT: In a large-scale network, configure AP groups as a best practice. |
# Create manual AP office, and specify the AP model and serial ID.
[AC] wlan ap office model WA6320
[AC-wlan-ap-office] serial-id 219801A28N819CE0003T
[AC-wlan-ap-office] quit
# Create AP group group1 and create an AP grouping rule by AP names to add AP office to AP group group1.
[AC] wlan ap-group group1
[AC-wlan-ap-group-group1] ap office
# Bind service template service to radio 1 in AP group group1.
[AC-wlan-ap-group-group1] ap-model WA6320
[AC-wlan-ap-group-group1-ap-model-WA6320] radio 1
[AC-wlan-ap-group-group1-ap-model-WA6320-radio-1] service-template service
# Enable radio 1.
[AC-wlan-ap-group-group1-ap-model-WA6320-radio-1] radio enable
[AC-wlan-ap-group-group1-ap-model-WA6320-radio-1] quit
[AC-wlan-ap-group-group1-ap-model-WA6320] quit
[AC-wlan-ap-group-group1] quit
Configuring the switch
# Enable the DHCP server.
<Switch> system-view
[Switch] dhcp enable
# Create VLAN 100. The switch will use this VLAN to forward the traffic on the CAPWAP tunnels between the AC and AP.
[Switch] vlan 100
[Switch-vlan100] quit
# Create VLAN 200. The switch will use this VLAN to forward packets for wireless clients.
[Switch] vlan 200
[Switch-vlan200] quit
# Configure GigabitEthernet 1/0/1 (the port connected to the AC) as a trunk port, and assign the trunk port to VLAN 100 and VLAN 200.
[Switch] interface gigabitethernet 1/0/1
[Switch-GigabitEthernet1/0/1] port link-type trunk
[Switch-GigabitEthernet1/0/1] port trunk permit vlan 100 200
[Switch-GigabitEthernet1/0/1] quit
# Configure GigabitEthernet 1/0/2 (the port connected to the AP) as a trunk port, assign the port to VLAN 100 and VLAN 200, and set the PVID of the port to 100.
[Switch] interface gigabitethernet 1/0/2
[Switch-GigabitEthernet1/0/2] port link-type trunk
[Switch-GigabitEthernet1/0/2] port trunk permit vlan 100 200
[Switch-GigabitEthernet1/0/2] port trunk pvid vlan 100
# Enable PoE on GigabitEthernet 1/0/2.
[Switch-GigabitEthernet1/0/2] poe enable
[Switch-GigabitEthernet1/0/2] quit
# Assign IP address 2.2.2.100/24 to VLAN-interface 100.
[Switch] interface vlan-interface 100
[Switch-Vlan-interface100] ip address 2.2.2.100 255.255.255.0
[Switch-Vlan-interface100] quit
# Assign IP address 2.2.1.2/24 to VLAN-interface 200.
[Switch] interface vlan-interface 200
[Switch-Vlan-interface200] ip address 2.2.1.2 255.255.255.0
[Switch-Vlan-interface200] quit
# Create a DHCP address pool named 100, and specify subnet 2.2.2.0/24 and gateway IP address 2.2.2.1 in the DHCP address pool.
[Switch] dhcp server ip-pool 100
[Switch-dhcp-pool-100] network 2.2.2.0 mask 255.255.255.0
[Switch-dhcp-pool-100] gateway-list 2.2.2.1
[Switch-dhcp-pool-100] option 138 ip-address 2.2.2.1
[Switch-dhcp-pool-100] quit
# Create a DHCP address pool named 200, and specify subnet 2.2.1.0/24 and gateway IP address 2.2.1.1 in the DHCP address pool.
[Switch] dhcp server ip-pool 200
[Switch-dhcp-pool-200] network 2.2.1.0 mask 255.255.255.0
[Switch-dhcp-pool-200] gateway-list 2.2.1.1
[Switch-dhcp-pool-200] quit
Configuring the iNode client
Prerequisites
In this example, the client version is iNode PC 7.1.
Connecting to the wireless network
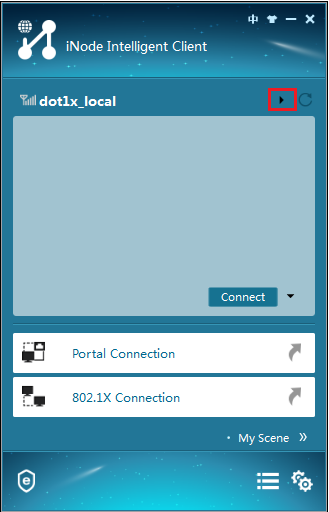
1. Run the iNode client, and then click Wireless Connection, as shown in Figure 2.
2. Click triangle icon in the wireless connection title bar, as shown in Figure 3.
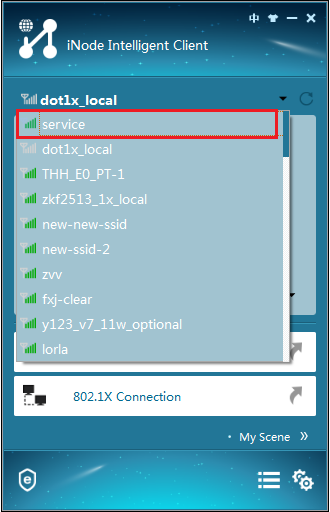
3. Double-click the wireless service with SSID service, as shown in Figure 4.
Figure 4 Selecting a wireless service
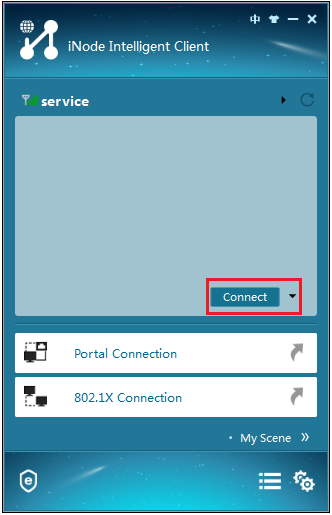
4. Click Connect, as shown in Figure 5.
Figure 5 Connecting to the wireless network
Configuring 802.1X authentication
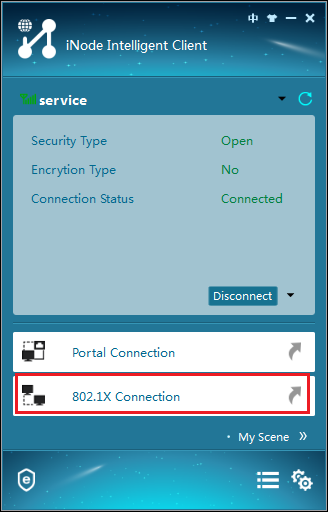
1. Click 802.1X Connection, as shown in Figure 6.
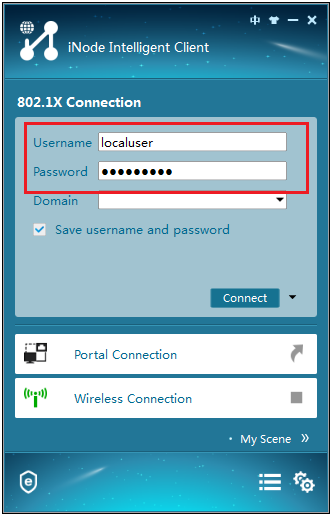
2. Enter username localuser and password localpass, as shown in Figure 7.
Figure 7 Entering the username and password
3. Click the inverted triangle icon next to Connect and select Properties.
4. In the dialog box that opens, select a wireless NIC and clear the option for uploading the client version.
5. Return to the iNode 802.1X connection screen.
6. Click Connect.
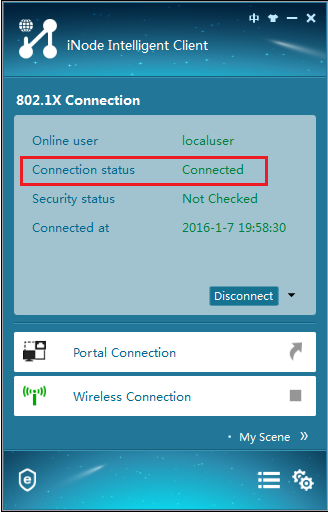
The iNode client displays the connection state as shown in Figure 8.
Figure 8 Successful 802.1X authentication
Verifying the configuration
# Display online 802.1X user information.
[AC] display dot1x connection
User MAC address : 0015-00bf-e84d
AP name : office
Radio ID : 1
SSID : service
BSSID : 741f-4ad4-1fe0
Username : localuser
Authentication domain : bbb
IPv4 address : 2.2.1.3
Authentication method : CHAP
Initial VLAN : 200
Authorization VLAN : 200
Authorization ACL number : N/A
Authorization user profile : N/A
Termination action : N/A
Session timeout period : N/A
Online from : 2019/12/04 17:37:55
Online duration : 0h 4m 20s
# Display service template information.
[AC] display wlan service-template service
Service template name : service
SSID : service
SSID-hide : Disabled
User-isolation : Disabled
Service template status : Enabled
Maximum clients per BSS : Not configured
Frame format : Dot3
Seamless roam status : Disabled
Seamless roam RSSI threshold : 50
Seamless roam RSSI gap : 20
VLAN ID : 200
AKM mode : Not configured
Security IE : Not configured
Cipher suite : Not configured
TKIP countermeasure time : 0 sec
PTK lifetime : 43200 sec
GTK rekey : Enabled
GTK rekey method : Time-based
GTK rekey time : 86400 sec
GTK rekey client-offline : Disabled
User authentication mode : 802.1X
Intrusion protection : Disabled
Intrusion protection mode : Temporary-block
Temporary block time : 180 sec
Temporary service stop time : 20 sec
Fail VLAN ID : Not configured
802.1X handshake : Disabled
802.1X handshake secure : Disabled
802.1X domain : bbb
MAC-auth domain : Not configured
Max 802.1X users : 4096
Max MAC-auth users : 4096
802.1X re-authenticate : Disabled
Authorization fail mode : Online
Accounting fail mode : Online
Authorization : Permitted
Key derivation : SHA1
PMF status : Disabled
Hotspot policy number : Not configured
Forwarding policy status : Disabled
Forwarding policy name : Not configured
FT status : Disabled
QoS trust : Port
QoS priority : 0
Configuration files
· AC:
#
vlan 100
#
vlan 200
#
wlan service-template service
ssid service
vlan 200
client forwarding-location ac
client-security authentication-mode dot1x
dot1x domain bbb
service-template enable
#
interface Vlan-interface100
ip address 2.2.2.1 255.255.255.0
#
interface Vlan-interface200
ip address 2.2.1.1 255.255.255.0
#
interface GigabitEthernet1/0/1
port link-mode bridge
port link-type trunk
port trunk permit vlan 1 100 200
#
domain bbb
authentication lan-access local
authorization lan-access local
accounting lan-access local
#
local-user localuser class network
password cipher $c$3$+5Yra0KsaLci/RxEa4lyYKxxiw6jwMCcOg==
service-type lan-access
#
wlan ap-group group1
ap office
ap-model WA6320
radio 1
radio enable
service-template service
radio 2
#
wlan ap office model WA6320
serial-id 219801A28N819CE0003T
#
· Switch:
#
dhcp enable
#
vlan 100
#
vlan 200
#
dhcp server ip-pool 100
network 2.2.2.0 mask 255.255.255.0
gateway-list 2.2.2.1
option 138 ip-address 2.2.2.1
#
dhcp server ip-pool 200
network 2.2.1.0 mask 255.255.255.0
gateway-list 2.2.1.1
#
interface Vlan-interface100
ip address 2.2.2.100 255.255.255.0
#
interface Vlan-interface200
ip address 2.2.1.2 255.255.255.0
#
interface GigabitEthernet1/0/1
port link-type trunk
port trunk permit vlan 1 100 200
#
interface GigabitEthernet1/0/2
port link-type trunk
port access permit vlan 100 200
port trunk pvid vlan 100
poe enable
#
Related documentation
· AP and WT Management Configuration Guide in H3C Access Controllers Configuration Guides
· AP and WT Management Command Reference in H3C Access Controllers Command References
· Network Connectivity Configuration Guide in H3C Access Controllers Configuration Guides
· Network Connectivity Command Reference in H3C Access Controllers Command References
· User Access and Authentication Configuration Guide in H3C Access Controllers Configuration Guides
· User Access and Authentication Command Reference in H3C Access Controllers Command References
· WLAN Access Configuration Guide in H3C Access Controllers Configuration Guides
· WLAN Access Command Reference in H3C Access Controllers Command References