- Table of Contents
-
- 14-Security Configuration Guide
- 00-Preface
- 01-ACL configuration
- 02-Time range configuration
- 03-User profile configuration
- 04-Public key management
- 05-PKI configuration
- 06-IPsec configuration
- 07-SSH configuration
- 08-SSL configuration
- 09-Session management
- 10-ARP attack protection configuration
- 11-ND attack defense configuration
- 12-Password control configuration
- 13-Crypto engine configuration
- 14-Connection limit configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 14-Connection limit configuration | 105.99 KB |
Configuring connection limits (interface-based)
Connection limit tasks at a glance
Creating a connection limit policy
Configuring the connection limit policy
About connection limit policies
Restrictions and guidelines for connection limit policy configuration
Configuring an IPv4 connection limit policy
Configuring an IPv6 connection limit policy
Applying the connection limit policy
About connection limit application
Restrictions and guidelines for connection limit application
Applying a connection limit policy to an interface
Applying a connection limit policy globally
Display and maintenance commands for connection limits
Troubleshooting connection limits
ACLs in the connection limit rules with overlapping segments
Configuring connection limits (user profile-based)
Prerequisites for connection limits
Configuring connection limits (interface-based)
About connection limits
The connection limit feature enables the device to monitor and limit the number of established connections.
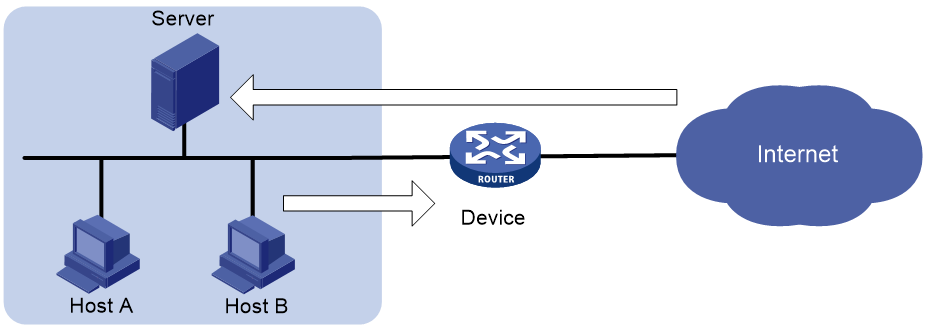
As shown in Figure 1, configure the connection limit feature to resolve the following issues:
· If Host B initiates a large number of connections in a short period of time, it might exhaust system resources and cause Host A to be unable to access the Internet.
· If the internal server receives a large number of connection requests in a short period of time, the server cannot process other requests.
Connection limit tasks at a glance
To configure connection limits, perform the following tasks:
1. Creating a connection limit policy
2. Configuring the connection limit policy
¡ Configuring an IPv4 connection limit policy
¡ Configuring an IPv6 connection limit policy
3. Applying the connection limit policy
¡ Applying a connection limit policy to an interface
¡ Applying a connection limit policy globally
Creating a connection limit policy
1. Enter system view.
system-view
2. Create a connection limit policy and enter its view.
connection-limit { ipv6-policy | policy } policy-id
Configuring the connection limit policy
About connection limit policies
To use a connection limit policy, you need to add limit rules to the policy. Each rule defines a range of connections and the criteria for limiting the connections. Connections in the range will be limited based on the criteria. The criteria include upper/lower connection limit and connection establishment rate limit. When the number of matching connections reaches the upper limit or connection rate limit in a connection limit rule based on destination IP address or service, the device accepts or rejects new connections depending on the action you configured. If the action is to reject new connections, the device does not accept new connections until the number of connections drops below the lower limit or connection rate limit due to connection aging. The device will send logs when the number of connections exceeds the upper limit or connection rate limit. The device will send logs when the number of connections drops below the lower limit or connection rate limit only if the action is to reject new connections. The connections that do not match any connection limit rules are not limited.
In each connection limit rule, an ACL is used to define the connection range. In addition, the rule also uses the following filtering methods to further limit the connections:
· per-destination—Limits user connections by destination IP address.
· per-service—Limits user connections by service (transport layer protocol and service port).
· per-source—Limits user connections by source IP address.
You can select more than one filtering method, and the selected methods take effect at the same time. For example, if you specify both per-destination and per-service, the user connections using the same service and destined to the same IP address are limited. If you do not specify any filtering methods in a limit rule, all user connections in the range are limited.
Restrictions and guidelines for connection limit policy configuration
When a connection limit policy is applied, connections on the device match all limit rules in the policy in ascending order of rule IDs. As a best practice, specify a smaller range and more filtering methods in a rule with a smaller ID.
Configuring an IPv4 connection limit policy
1. Enter system view.
system-view
2. Create an IPv4 connection limit policy and enter its view.
connection-limit policy policy-id
3. Configure a connection limit rule.
limit limit-id acl { acl-number | name acl-name } [ per-destination | per-service | per-source ] * { amount max-amount min-amount | rate rate } * [ description text | permit-new ] *
4. (Optional.) Configure a description for the connection limit policy.
description text
By default, an IPv4 connection limit policy does not have a description.
Configuring an IPv6 connection limit policy
1. Enter system view.
system-view
2. Create an IPv6 connection limit policy and enter its view.
connection-limit ipv6-policy policy-id
3. Configure a connection limit rule.
limit limit-id acl ipv6 { acl-number | name acl-name } [ per-destination | per-service | per-source ] * { amount max-amount min-amount | rate rate } * [ description text | permit-new ] *
4. (Optional.) Configure a description for the connection limit policy.
description text
By default, an IPv6 connection limit policy does not have a description.
Applying the connection limit policy
About connection limit application
To make a connection limit policy take effect, apply it globally or to an interface. The connection limit policy applied to an interface takes effect only on the specified connections on the interface. The connection limit policy applied globally takes effect on all the specified connections on the device.
Different connection limit policies can be applied to individual interfaces as well as globally on the device. In this case, the device matches connections against these policies in the order of the policy on the inbound interface, the global policy, and the policy on the outbound interface. It cannot accept new connections as long as the number of connections reaches the smallest upper connection limit defined by these policies.
Restrictions and guidelines for connection limit application
A connection limit policy or any modification to it takes effect only on new connections. It does not take effect on existing connections.
On an IRF fabric where session synchronization is enabled, connection limit policies applied to a subordinate device do not take effect on sessions switched from the master device.
Applying a connection limit policy to an interface
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Apply a connection limit policy to the interface.
connection-limit apply { ipv6-policy | policy } policy-id
By default, no connection limit policy is applied to an interface.
Only one IPv4 connection limit policy and one IPv6 connection limit policy can be applied to an interface. A new IPv4 or IPv6 connection limit policy overwrites the old policy.
Applying a connection limit policy globally
1. Enter system view.
system-view
2. Apply a connection limit policy globally.
connection-limit apply global { ipv6-policy | policy } policy-id
By default, no connection limit policy is applied globally.
Only one IPv4 connection limit policy and one IPv6 connection limit policy can be applied globally. A new IPv4 or IPv6 connection limit policy overwrites the old policy.
Display and maintenance commands for connection limits
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display the connection limit policy information. |
display connection-limit { ipv6-policy | policy } { all | policy-id } |
|
Display the connection limit statistics globally or on an interface. |
display connection-limit statistics { global | interface interface-type interface-number } |
|
Display statistics about IPv4 connections matching connection limit rules globally or on an interface. |
display connection-limit stat-nodes { global | interface interface-type interface-number } [ { deny-new | permit-new } | destination destination-ip | service-port port-number | source source-ip ] * [ count ] |
|
Display statistics about IPv6 connections matching connection limit rules globally or on an interface. |
display connection-limit ipv6-stat-nodes { global | interface interface-type interface-number } [ { deny-new | permit-new } | destination destination-ip | service-port port-number | source source-ip ] * [ count ] |
|
Clear the connection limit statistics globally or on an interface. |
reset connection-limit statistics { global | interface interface-type interface-number } |
Troubleshooting connection limits
ACLs in the connection limit rules with overlapping segments
Symptom
A connection limit policy has two rules. Rule 1 sets the upper limit to 10 for the connections from each host on segment 192.168.0.0/24. Rule 2 sets the upper limit to 100 for the connections from 192.168.0.100/24.
<Device> system-view
[Device] acl basic 2001
[Device-acl-ipv4-basic-2001] rule permit source 192.168.0.0 0.0.0.255
[Device-acl-ipv4-basic-2001] quit
[Device] acl basic 2002
[Device-acl-ipv4-basic-2002] rule permit source 192.168.0.100 0
[Device-acl-ipv4-basic-2002] quit
[Device] connection-limit policy 1
[Device-connlmt-policy-1] limit 1 acl 2001 per-destination amount 10 5
[Device-connlmt-policy-1] limit 2 acl 2002 per-destination amount 100 10
As a result, the host at 192.168.0.100 can only initiate a maximum of 10 connections to the external network.
Solution
To resolve the issue:
1. Rearrange the two connection limit rules by exchanging their rule IDs.
2. If the issue persists, contact H3C Support.
Configuring connection limits (user profile-based)
About connection limits
The connection limit feature enables the device to assign user profiles to control the number of established connections and establishment rate on a per-user basis. This feature facilitates accurate allocation of system resources and improves access efficiency when multiple users are present.
After the user passes authentication, the device checks the associated user profile, and performs either of the following actions:
· If the user profile exists and has a connection limit policy in its view, the device restricts user access according to the connection limit policy.
· If no user profile exists or the user profile does not have a connection limit policy, the device allows user access without limiting the connections initiated by the user.
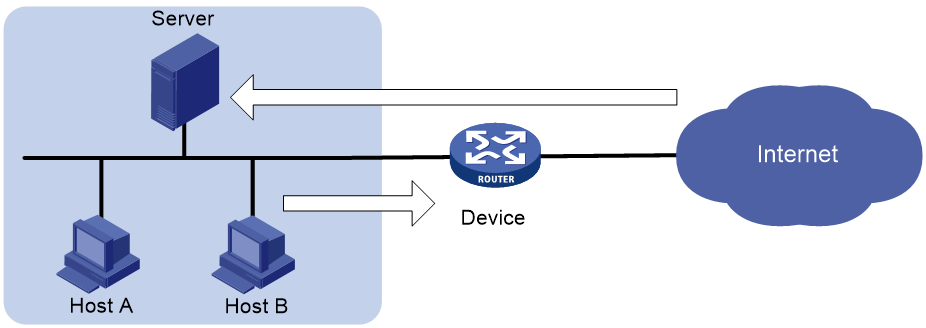
As shown in Figure 2, configure the connection limit feature to resolve the following issues:
· If Host B initiates a large number of connections in a short period of time, it might exhaust system resources and cause Host A to be unable to access the Internet.
· If the internal server receives a large number of connection requests in a short period of time, the server cannot process other requests.
Prerequisites for connection limits
The connection limit feature must work with an authentication server.
Before configuring connection limits, complete either of the following tasks:
· For remote authentication, specify the user profile to be associated with the user's account on the remote server.
· For local authentication, specify the user's authorized user profile in local user view on the device. For information about configuring local users, see AAA configuration in User Access and Authentication Configuration Guide.
Configuring connection limits
1. Enter system view.
system-view
2. Create a user profile and enter user profile view.
user-profile profile-name
For more information about this command, see Security Command Reference.
3. Set the maximum number of user connections.
connection-limit amount amount
By default, the number of user connections is not limited.
4. Set the maximum connection establishment rate.
connection-limit rate rate
By default, the connection establishment rate is not limited.
5. (Optional.) Display user profile configuration and online user information.
display user-profile [ session-group ] [ name profile-name ]
For more information about this command, see Security Command Reference.