- Table of Contents
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 02-EVPN-DCI configuration | 232.23 KB |
Contents
Enabling route nexthop replacement and route router MAC replacement
Configuring the BGP EVPN address family and the BGP VPNv4 address family to exchange routes
Enabling BGP VPNv4 route advertisement for the BGP EVPN address family
Enabling BGP EVPN route advertisement for the BGP VPNv4 address family
EVPN-DCI configuration examples
Example: Configuring a basic EVPN-DCI network
Example: Configuring EVPN-DCI intermediate VXLAN mapping
Example: Configuring EVPN-DCI IPv4 Layer 3 communication
Configuring EVPN-DCI
About EVPN-DCI
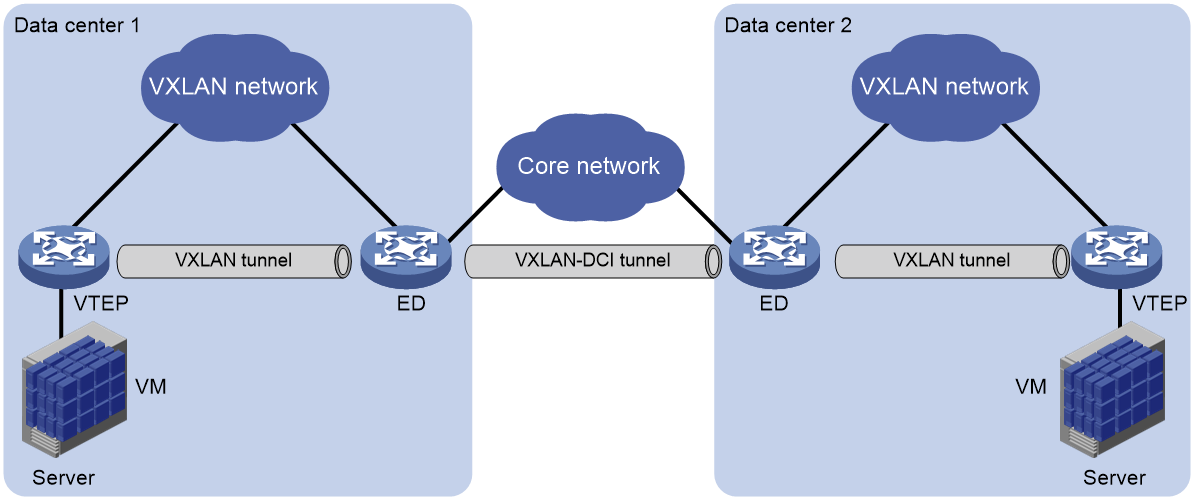
EVPN data center interconnect (EVPN-DCI) uses VXLAN-DCI tunnels to provide connectivity for data centers over an IP transport network.
EVPN-DCI network model
As shown in Figure 1, the EVPN-DCI network contains VTEPs and edge devices (EDs) located at the edge of the transport network. A VXLAN tunnel is established between a VTEP and an ED, and a VXLAN-DCI tunnel is established between two EDs. VXLAN-DCI tunnels use VXLAN encapsulation. Each ED de-encapsulates incoming VXLAN packets and re-encapsulates them based on the destination before forwarding the packets through a VXLAN or VXLAN-DCI tunnel.
Figure 1 EVPN-DCI network model
Working mechanisms
In an EVPN-DCI network, BGP EVPN peer relationships are established between EDs and between EDs and VTEPs. When advertising routes to a VTEP or another ED, an ED replaces the routes' nexthop IP address and router MAC address with its IP address and router MAC address.
In an EVPN-DCI network, a VTEP and an ED use a VXLAN tunnel to send traffic, and two EDs use a VXLAN-DCI tunnel to send traffic. An ED de-encapsulates incoming VXLAN packets and re-encapsulates them before forwarding the packets through a VXLAN or VXLAN-DCI tunnel.
EVPN-DCI tasks at a glance
To configure EVPN-DCI, perform the following tasks on EDs:
1. Enabling DCI
2. Enabling route nexthop replacement and route router MAC replacement
3. (Optional.) Configuring VXLAN mapping
Perform this task to provide Layer 2 connectivity for a tenant subnet that uses different VXLAN IDs in multiple data centers.
4. Configuring the BGP EVPN address family and the BGP VPNv4 address family to exchange routes
You must perform this task if data centers are interconnected through an MPLS L3VPN network.
Prerequisites for EVPN-DCI
Before you configure EVPN-DCI, complete basic EVPN configuration for each data center. For more information about basic EVPN configuration, see "Configuring basic EVPN features."
Enabling DCI
About this task
For EDs to automatically establish VXLAN-DCI tunnels, you must enable DCI on the Layer 3 interfaces that interconnect the EDs.
An ED establishes VXLAN-DCI tunnels based on BGP EVPN routes. If DCI is disabled on the outgoing interfaces to remote sites, EDs cannot establish VXLAN-DCI tunnels.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
Subinterfaces of a DCI-enabled interface inherit configuration of the interface.
3. Enable DCI.
dci enable
By default, DCI is disabled on an interface.
Enabling route nexthop replacement and route router MAC replacement
1. Enter system view.
system-view
2. Configure a global router ID.
router id router-id
By default, no global router ID is configured.
3. Enable a BGP instance and enter BGP instance view.
bgp as-number [ instance instance-name ]
By default, BGP is disabled, and no BGP instances exist.
4. Specify local VTEPs and remote EDs as BGP peers.
peer { group-name | ipv4-address [ mask-length ] } as-number as-number
5. Create the BGP EVPN address family and enter BGP EVPN address family view.
address-family l2vpn evpn
6. Enable BGP to exchange BGP EVPN routes with a peer or peer group.
peer { group-name | ipv4-address [ mask-length ] } enable
By default, BGP does not exchange BGP EVPN routes with peers.
7. Set the local router as the next hop for routes advertised to a peer or peer group.
peer { group-name | ipv4-address [ mask-length ] } next-hop-local
The default settings for this command are as follows:
¡ BGP sets the local router as the next hop for all routes advertised to an EBGP peer or peer group.
¡ BGP does not modify the next hop for EBGP routes advertised to an IBGP peer or peer group.
The peers specified in this task must be VTEPs in the local data center.
8. Enable route router MAC replacement for a peer or peer group.
peer { group-name | ipv4-address [ mask-length ] } router-mac-local
By default, the device does not modify the router MAC address of routes before advertising the routes.
This command enables the device to use its router MAC address to replace the router MAC address of routes received from and advertised to a peer or peer group.
The peers specified in this task must be remote EDs.
Configuring VXLAN mapping
About this task
The VXLAN mapping feature provides Layer 2 connectivity for a tenant subnet that uses different VXLAN IDs in multiple data centers.
If you map a local VXLAN to a remote VXLAN on an ED, the ED processes routes as follows:
· When the ED receives the local VXLAN's MAC/IP advertisement routes from local VTEPs, it performs the following operations:
¡ Adds the routes to the local VXLAN.
¡ Replaces the VXLAN ID of the routes with the remote VXLAN ID and advertises the routes to remote EDs.
· When the ED receives the remote VXLAN's MAC/IP advertisement routes from a remote data center, it adds the routes to the local VXLAN.
VXLAN mapping includes the following types:
· Non-intermediate VXLAN mapping—When two data centers use different VXLAN IDs for a subnet, map the local VXLAN to the remote VXLAN on the ED of one data center. For example, for VXLAN 10 of data center 1 to communicate with VXLAN 20 of data center 2, map VXLAN 10 to VXLAN 20 on the ED of data center 1.
· Intermediate VXLAN mapping—When multiple data centers use different VXLAN IDs for a subnet, map the VXLANs to an intermediate VXLAN on all EDs. For example, data center 1 uses VXLAN 10, data center 2 uses VXLAN 20, and data center 3 uses VXLAN 30. To provide connectivity for the VXLANs, map them to intermediate VXLAN 500 on EDs of the data centers. You must use intermediate VXLAN mapping if more than two data centers use different VXLAN IDs. The intermediate VXLAN can be used only for VXLAN mapping, and it cannot be used for common VXLAN services.
Restrictions and guidelines
You must create mapped remote VXLANs on the device, create an EVPN instance for each remote VXLAN, and configure RD and route target settings for the EVPN instances.
When you use VXLAN mapping, follow these route target restrictions:
· EVPN instances and EVPN address family of VPN instances do not have the same export targets.
· EVPN instances and EVPN address family of the public instance do not have the same export targets.
Procedure
1. Enter system view.
system-view
2. Enter VSI view.
vsi vsi-name
3. Enter EVPN instance view.
evpn encapsulation vxlan
4. Map the local VXLAN to a remote VXLAN.
mapping vni vxlan-id
By default, a local VXLAN is not mapped to any remote VXLAN.
The remote VXLAN ID cannot be the reserved VXLAN ID specified by using the reserved vxlan command or the L3 VXLAN ID specified by using the l3-vni command. For more information about the reserved vxlan command, see VXLAN Command Reference.
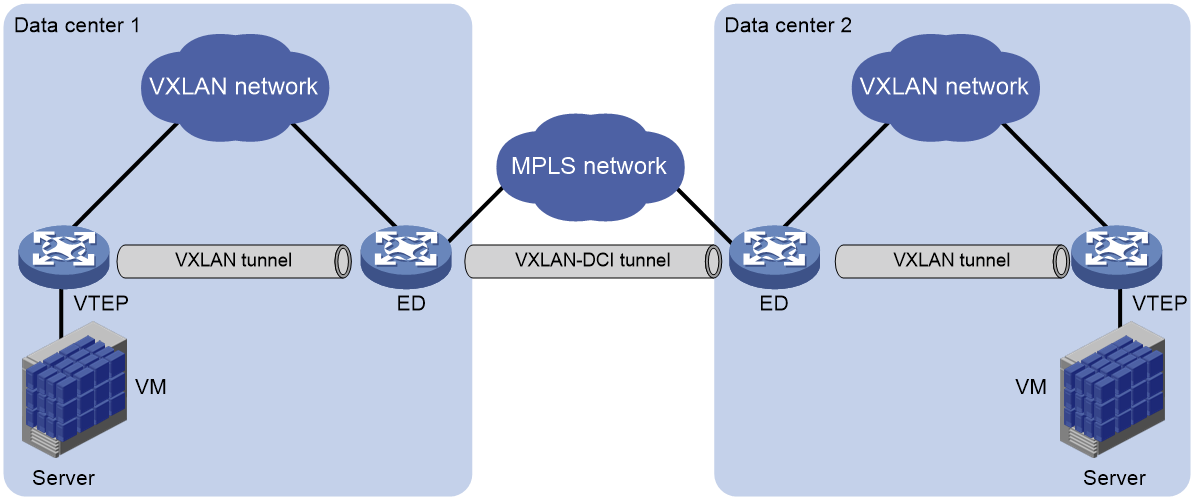
Configuring the BGP EVPN address family and the BGP VPNv4 address family to exchange routes
About route exchange
When data centers are interconnected through an MPLS L3VPN network, EVPN EDs also act as MPLS L3VPN PEs. To enable communication between the data centers, you must perform the following tasks on the EDs:
· Configure both MPLS L3VPN and EVPN.
· Configure the BGP EVPN address family and the BGP VPNv4 address family to exchange routes.
Figure 2 Data centers interconnected through an MPLS L3VPN network
Enabling BGP VPNv4 route advertisement for the BGP EVPN address family
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP EVPN address family view.
address-family l2vpn evpn
4. Enable BGP VPNv4 route advertisement for the BGP EVPN address family.
advertise l3vpn route [ replace-rt ][ advertise-policy policy-name ]
By default, BGP VPNv4 routes are not advertised through the BGP EVPN address family.
After you execute this command, the device advertises BGP VPNv4 routes as IP prefix advertisement routes through the BGP EVPN address family.
Enabling BGP EVPN route advertisement for the BGP VPNv4 address family
1. Enter system view.
system-view
2. Enter BGP instance view.
bgp as-number [ instance instance-name ]
3. Enter BGP VPNv4 address family view.
address-family vpnv4
4. Enable BGP EVPN route advertisement for the BGP VPNv4 address family.
advertise evpn route [ replace-rt ][ advertise-policy policy-name ]
By default, BGP EVPN routes are not advertised through the BGP VPNv4 address family.
After you execute this command, the device advertises IP prefix advertisement routes and MAC/IP advertisement routes that contain host route information through the BGP VPNv4 address family.
EVPN-DCI configuration examples
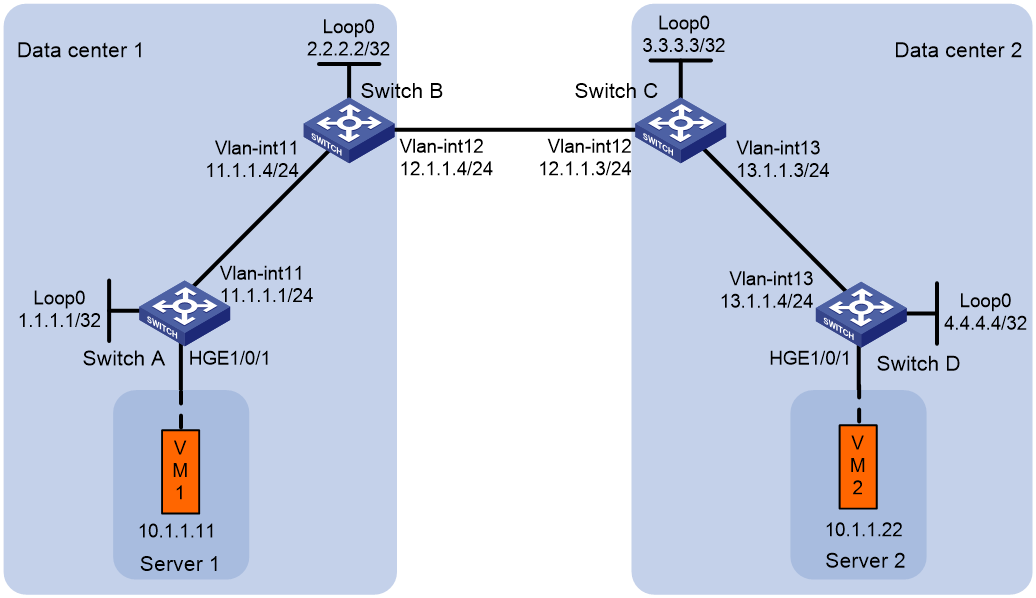
Example: Configuring a basic EVPN-DCI network
Network configuration
As shown in Figure 3:
· Configure VXLAN 10 on Switch A through Switch D to provide connectivity for the VMs in the data centers.
· Configure Switch A and Switch D as VTEPs, and configure Switch B and Switch C as EDs.
Procedure
|
IMPORTANT: By default, interfaces on the device are operating in Layer 3 mode. Before you configure Ethernet service instances on an interface, you must use the port link-mode command to configure the interface to operate in Layer 2 mode. |
1. Configure IP addresses and unicast routing settings:
# Assign IP addresses to interfaces, as shown in Figure 3. (Details not shown.)
# Configure OSPF on the transport network for the switches to reach one another. (Details not shown.)
2. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Configure Layer 2 forwarding for VXLAN tunnels.
[SwitchA] undo vxlan ip-forwarding
# Disable remote MAC address learning.
[SwitchA] vxlan tunnel mac-learning disable
# Create VXLAN 10 on VSI vpna.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
# Create an EVPN instance on VSI vpna. Configure the switch to automatically generate an RD, and manually configure a route target for the EVPN instance.
[SwitchA-vsi-vpna] evpn encapsulation vxlan
[SwitchA-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchA-vsi-vpna-evpn-vxlan] vpn-target 123:456
[SwitchA-vsi-vpna-evpn-vxlan] quit
[SwitchA-vsi-vpna] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchA] bgp 100
[SwitchA-bgp-default] peer 2.2.2.2 as-number 100
[SwitchA-bgp-default] peer 2.2.2.2 connect-interface loopback 0
[SwitchA-bgp-default] address-family l2vpn evpn
[SwitchA-bgp-default-evpn] peer 2.2.2.2 enable
[SwitchA-bgp-default-evpn] quit
[SwitchA-bgp-default] quit
# On HundredGigE 1/0/1, create Ethernet service instance 1000 to match VLAN 100.
[SwitchA] interface hundredgige 1/0/1
[SwitchA-HundredGigE1/0/1] service-instance 1000
[SwitchA-HundredGigE1/0/1-srv1000] encapsulation s-vid 100
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-HundredGigE1/0/1-srv1000] xconnect vsi vpna
[SwitchA-HundredGigE1/0/1-srv1000] quit
3. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Configure Layer 2 forwarding for VXLAN tunnels.
[SwitchB] undo vxlan ip-forwarding
# Disable remote MAC address learning.
[SwitchB] vxlan tunnel mac-learning disable
# Enable DCI on the Layer 3 interface that connects Switch B to Switch C for the switches to establish a VXLAN-DCI tunnel.
[SwitchB] interface vlan-interface 12
[SwitchB-Vlan-interface12] dci enable
[SwitchB-Vlan-interface12] quit
# Create VXLAN 10 on VSI vpna.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] quit
# Create an EVPN instance on VSI vpna. Configure the switch to automatically generate an RD, and manually configure a route target for the EVPN instance.
[SwitchB-vsi-vpna] evpn encapsulation vxlan
[SwitchB-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchB-vsi-vpna-evpn-vxlan] vpn-target 123:456
[SwitchB-vsi-vpna-evpn-vxlan] quit
[SwitchB-vsi-vpna] quit
# Configure BGP to advertise BGP EVPN routes. Enable nexthop replacement for routes advertised to Switch A, and enable router MAC replacement for routes advertised to and received from Switch C.
[SwitchB] bgp 100
[SwitchB-bgp-default] peer 3.3.3.3 as-number 200
[SwitchB-bgp-default] peer 3.3.3.3 connect-interface loopback 0
[SwitchB-bgp-default] peer 3.3.3.3 ebgp-max-hop 64
[SwitchB-bgp-default] peer 1.1.1.1 as-number 100
[SwitchB-bgp-default] peer 1.1.1.1 connect-interface loopback 0
[SwitchB-bgp-default] address-family l2vpn evpn
[SwitchB-bgp-default-evpn] peer 3.3.3.3 enable
[SwitchB-bgp-default-evpn] peer 3.3.3.3 router-mac-local
[SwitchB-bgp-default-evpn] peer 1.1.1.1 enable
[SwitchB-bgp-default-evpn] peer 1.1.1.1 next-hop-local
[SwitchB-bgp-default-evpn] quit
[SwitchB-bgp-default] quit
4. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Configure Layer 2 forwarding for VXLAN tunnels.
[SwitchC] undo vxlan ip-forwarding
# Disable remote MAC address learning.
[SwitchC] vxlan tunnel mac-learning disable
# Enable DCI on the Layer 3 interface that connects Switch C to Switch B for the switches to establish a VXLAN-DCI tunnel.
[SwitchC] interface vlan-interface 12
[SwitchC-Vlan-interface12] dci enable
[SwitchC-Vlan-interface12] quit
# Create VXLAN 10 on VSI vpna.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] vxlan 10
[SwitchC-vsi-vpna-vxlan-10] quit
# Create an EVPN instance on VSI vpna. Configure the switch to automatically generate an RD, and manually configure a route target for the EVPN instance.
[SwitchC-vsi-vpna] evpn encapsulation vxlan
[SwitchC-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchC-vsi-vpna-evpn-vxlan] vpn-target 123:456
[SwitchC-vsi-vpna-evpn-vxlan] quit
[SwitchC-vsi-vpna] quit
# Configure BGP to advertise BGP EVPN routes. Enable nexthop replacement for routes advertised to Switch D, and enable router MAC replacement for routes advertised to and received from Switch B.
[SwitchC] bgp 200
[SwitchC-bgp-default] peer 2.2.2.2 as-number 100
[SwitchC-bgp-default] peer 2.2.2.2 connect-interface loopback 0
[SwitchC-bgp-default] peer 2.2.2.2 ebgp-max-hop 64
[SwitchC-bgp-default] peer 4.4.4.4 as-number 200
[SwitchC-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchC-bgp-default] address-family l2vpn evpn
[SwitchC-bgp-default-evpn] peer 2.2.2.2 enable
[SwitchC-bgp-default-evpn] peer 2.2.2.2 router-mac-local
[SwitchC-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchC-bgp-default-evpn] peer 4.4.4.4 next-hop-local
[SwitchC-bgp-default-evpn] quit
[SwitchC-bgp-default] quit
5. Configure Switch D:
# Enable L2VPN.
<SwitchD> system-view
[SwitchD] l2vpn enable
# Configure Layer 2 forwarding for VXLAN tunnels.
[SwitchD] undo vxlan ip-forwarding
# Disable remote MAC address learning.
[SwitchD] vxlan tunnel mac-learning disable
# Create VXLAN 10 on VSI vpna.
[SwitchD] vsi vpna
[SwitchD-vsi-vpna] vxlan 10
[SwitchD-vsi-vpna-vxlan-10] quit
# Create an EVPN instance on VSI vpna. Configure the switch to automatically generate an RD, and manually configure a route target for the EVPN instance.
[SwitchD-vsi-vpna] evpn encapsulation vxlan
[SwitchD-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchD-vsi-vpna-evpn-vxlan] vpn-target 123:456
[SwitchD-vsi-vpna-evpn-vxlan] quit
[SwitchD-vsi-vpna] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchD] bgp 200
[SwitchD-bgp-default] peer 3.3.3.3 as-number 200
[SwitchD-bgp-default] peer 3.3.3.3 connect-interface Loopback 0
[SwitchD-bgp-default] address-family l2vpn evpn
[SwitchD-bgp-default-evpn] peer 3.3.3.3 enable
[SwitchD-bgp-default-evpn] quit
[SwitchD-bgp-default] quit
# On HundredGigE 1/0/1, create Ethernet service instance 1000 to match VLAN 200.
[SwitchD] interface hundredgige 1/0/1
[SwitchD-HundredGigE1/0/1] service-instance 1000
[SwitchD-HundredGigE1/0/1-srv1000] encapsulation s-vid 200
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchD-HundredGigE1/0/1-srv1000] xconnect vsi vpna
[SwitchD-HundredGigE1/0/1-srv1000] quit
Verifying the configuration
1. Verify the configuration on EDs. (This example uses Switch B.)
# Verify that the ED has discovered Switch A and Switch C through IMET routes and has established VXLAN and VXLAN-DCI tunnels to the switches.
[SwitchB] display evpn auto-discovery imet
Total number of automatically discovered peers: 2
VSI name: vpna
RD PE_address Tunnel_address Tunnel mode VXLAN ID
1:10 1.1.1.1 1.1.1.1 VXLAN 10
1:10 3.3.3.3 3.3.3.3 VXLAN-DCI 10
# Verify that the VXLAN and VXLAN-DCI tunnels on the ED are up.
[SwitchB] display interface tunnel
Tunnel0
Current state: UP
Line protocol state: UP
Description: Tunnel0 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 2.2.2.2, destination 1.1.1.1
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
Tunnel1
Current state: UP
Line protocol state: UP
Description: Tunnel1 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 2.2.2.2, destination 3.3.3.3
Tunnel protocol/transport UDP_VXLAN-DCI/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
# Verify that the VXLAN and VXLAN-DCI tunnels have been assigned to the VXLAN.
[SwitchB] display l2vpn vsi name vpna verbose
VSI Name: vpna
VSI Index : 0
VSI State : Up
MTU : -
Bandwidth : -
Broadcast Restrain : -
Multicast Restrain : -
Unknown Unicast Restrain: -
MAC Learning : -
MAC Table Limit : -
MAC Learning rate : -
Drop Unknown : -
Flooding : Enabled
Statistics : Disabled
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel0 0x5000000 UP Auto Disabled
Tunnel1 0x5000001 UP Auto Disabled
# Verify that the ED has generated EVPN MAC address entries for the VMs.
[SwitchB] display evpn route mac
Flags: D - Dynamic B - BGP L - Local active
G - Gateway S - Static M - Mapping
VSI name: vpna
MAC address Link ID/Name Flags Next hop
0001-0001-0011 Tunnel0 B 1.1.1.1
0001-0001-0033 Tunnel1 B 3.3.3.3
2. Verify that VM 1 and VM 2 can communicate. (Details not shown.)
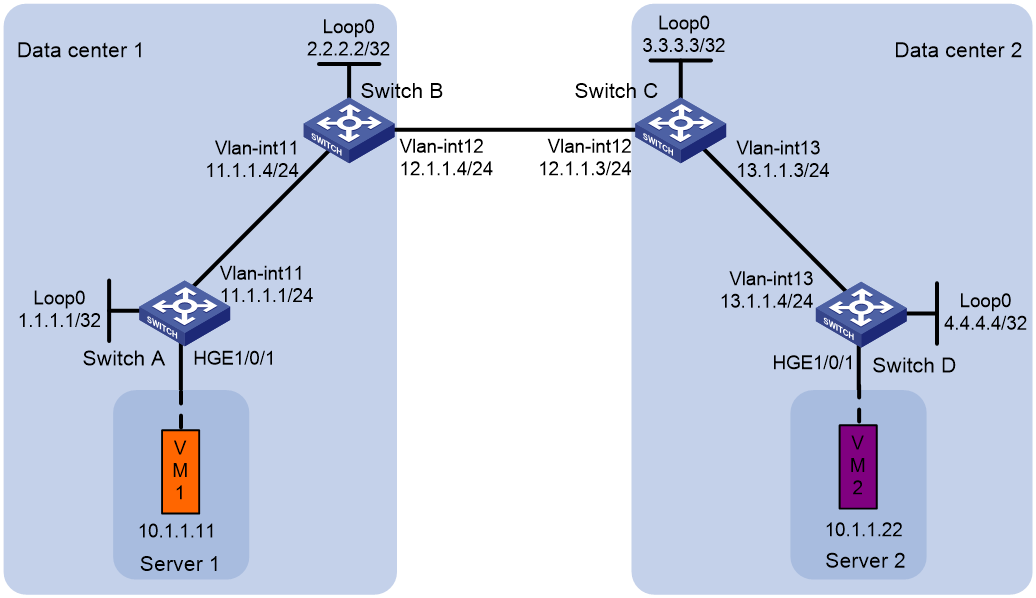
Example: Configuring EVPN-DCI intermediate VXLAN mapping
Network configuration
As shown in Figure 4:
· Configure VXLAN 10 on VTEP Switch A and ED Switch B, and configure VXLAN 30 on VTEP Switch D and ED Switch C.
· Configure intermediate VXLAN mapping for VXLAN 10 and VXLAN 30 to have Layer 2 connectivity:
¡ Map VXLAN 10 to intermediate VXLAN 500 on Switch B.
¡ Map VXLAN 30 to intermediate VXLAN 500 on Switch C.
Procedure
|
IMPORTANT: By default, interfaces on the device are operating in Layer 3 mode. Before you configure Ethernet service instances on an interface, you must use the port link-mode command to configure the interface to operate in Layer 2 mode. |
1. Configure IP addresses and unicast routing settings:
# Assign IP addresses to interfaces, as shown in Figure 4. (Details not shown.)
# Configure OSPF on the transport network for the switches to reach one another. (Details not shown.)
2. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Configure Layer 2 forwarding for VXLAN tunnels.
[SwitchA] undo vxlan ip-forwarding
# Disable remote MAC address learning.
[SwitchA] vxlan tunnel mac-learning disable
# Create VXLAN 10 on VSI vpna.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
# Create an EVPN instance on VSI vpna. Configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchA-vsi-vpna] evpn encapsulation vxlan
[SwitchA-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchA-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchA-vsi-vpna-evpn-vxlan] quit
[SwitchA-vsi-vpna] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchA] bgp 100
[SwitchA-bgp-default] peer 2.2.2.2 as-number 100
[SwitchA-bgp-default] peer 2.2.2.2 connect-interface loopback 0
[SwitchA-bgp-default] address-family l2vpn evpn
[SwitchA-bgp-default-evpn] peer 2.2.2.2 enable
[SwitchA-bgp-default-evpn] quit
[SwitchA-bgp-default] quit
# On HundredGigE 1/0/1, create Ethernet service instance 1000 to match VLAN 100.
[SwitchA] interface hundredgige 1/0/1
[SwitchA-HundredGigE1/0/1] service-instance 1000
[SwitchA-HundredGigE1/0/1-srv1000] encapsulation s-vid 100
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-HundredGigE1/0/1-srv1000] xconnect vsi vpna
[SwitchA-HundredGigE1/0/1-srv1000] quit
3. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Configure Layer 2 forwarding for VXLAN tunnels.
[SwitchB] undo vxlan ip-forwarding
# Disable remote MAC address learning.
[SwitchB] vxlan tunnel mac-learning disable
# Enable DCI on the Layer 3 interface that connects Switch B to Switch C for the switches to establish a VXLAN-DCI tunnel.
[SwitchB] interface vlan-interface 12
[SwitchB-Vlan-interface12] dci enable
[SwitchB-Vlan-interface12] quit
# Create VXLAN 10 on VSI vpna.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] quit
# Create an EVPN instance on VSI vpna. Configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchB-vsi-vpna] evpn encapsulation vxlan
[SwitchB-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchB-vsi-vpna-evpn-vxlan] vpn-target auto
# Map local VXLAN 10 to intermediate VXLAN 500.
[SwitchB-vsi-vpna-evpn-vxlan] mapping vni 500
[SwitchB-vsi-vpna-evpn-vxlan] quit
[SwitchB-vsi-vpna] quit
# Create VXLAN 500 on VSI vpnb. The switch will replace the VXLAN ID of VXLAN 10's traffic with VXLAN ID 500 when performing Layer 2 forwarding.
[SwitchB] vsi vpnb
[SwitchB-vsi-vpnb] vxlan 500
[SwitchB-vsi-vpnb-vxlan-500] quit
# Create an EVPN instance on VSI vpnb. Configure the switch to automatically generate an RD, and manually configure a route target for the EVPN instance.
[SwitchB-vsi-vpnb] evpn encapsulation vxlan
[SwitchB-vsi-vpnb-evpn-vxlan] route-distinguisher auto
[SwitchB-vsi-vpnb-evpn-vxlan] vpn-target 123:456
[SwitchB-vsi-vpnb-evpn-vxlan] quit
[SwitchB-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes. Enable nexthop replacement for routes advertised to Switch A, and enable router MAC replacement for routes advertised to and received from Switch C.
[SwitchB] bgp 100
[SwitchB-bgp-default] peer 3.3.3.3 as-number 200
[SwitchB-bgp-default] peer 3.3.3.3 connect-interface loopback 0
[SwitchB-bgp-default] peer 3.3.3.3 ebgp-max-hop 64
[SwitchB-bgp-default] peer 1.1.1.1 as-number 100
[SwitchB-bgp-default] peer 1.1.1.1 connect-interface loopback 0
[SwitchB-bgp-default] address-family l2vpn evpn
[SwitchB-bgp-default-evpn] peer 3.3.3.3 enable
[SwitchB-bgp-default-evpn] peer 3.3.3.3 router-mac-local
[SwitchB-bgp-default-evpn] peer 1.1.1.1 enable
[SwitchB-bgp-default-evpn] peer 1.1.1.1 next-hop-local
[SwitchB-bgp-default-evpn] quit
[SwitchB-bgp-default] quit
4. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Configure Layer 2 forwarding for VXLAN tunnels.
[SwitchC] undo vxlan ip-forwarding
# Disable remote MAC address learning.
[SwitchC] vxlan tunnel mac-learning disable
# Enable DCI on the Layer 3 interface that connects Switch C to Switch B for the switches to establish a VXLAN-DCI tunnel.
[SwitchC] interface vlan-interface 12
[SwitchC-Vlan-interface12] dci enable
[SwitchC-Vlan-interface12] quit
# Create VXLAN 30 on VSI vpna.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] vxlan 30
[SwitchC-vsi-vpna-vxlan-30] quit
# Create an EVPN instance on VSI vpna. Configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchC-vsi-vpna] evpn encapsulation vxlan
[SwitchC-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchC-vsi-vpna-evpn-vxlan] vpn-target auto
# Map local VXLAN 30 to intermediate VXLAN 500.
[SwitchC-vsi-vpna-evpn-vxlan] mapping vni 500
[SwitchC-vsi-vpna-evpn-vxlan] quit
[SwitchC-vsi-vpna] quit
# Create VXLAN 500 on VSI vpnb. The switch will replace the VXLAN ID of VXLAN 30's traffic with VXLAN ID 500 when performing Layer 2 forwarding.
[SwitchC] vsi vpnb
[SwitchC-vsi-vpnb] vxlan 500
[SwitchC-vsi-vpnb-vxlan-500] quit
# Create an EVPN instance on VSI vpnb. Configure the switch to automatically generate an RD, and manually configure a route target for the EVPN instance.
[SwitchC-vsi-vpnb] evpn encapsulation vxlan
[SwitchC-vsi-vpnb-evpn-vxlan] route-distinguisher auto
[SwitchC-vsi-vpnb-evpn-vxlan] vpn-target 123:456
[SwitchC-vsi-vpnb-evpn-vxlan] quit
[SwitchC-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes. Enable nexthop replacement for routes advertised to Switch D, and enable router MAC replacement for routes advertised to and received from Switch B.
[SwitchC] bgp 200
[SwitchC-bgp-default] peer 2.2.2.2 as-number 100
[SwitchC-bgp-default] peer 2.2.2.2 connect-interface loopback 0
[SwitchC-bgp-default] peer 2.2.2.2 ebgp-max-hop 64
[SwitchC-bgp-default] peer 4.4.4.4 as-number 200
[SwitchC-bgp-default] peer 4.4.4.4 connect-interface loopback 0
[SwitchC-bgp-default] address-family l2vpn evpn
[SwitchC-bgp-default-evpn] peer 2.2.2.2 enable
[SwitchC-bgp-default-evpn] peer 2.2.2.2 router-mac-local
[SwitchC-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchC-bgp-default-evpn] peer 4.4.4.4 next-hop-local
[SwitchC-bgp-default-evpn] quit
[SwitchC-bgp-default] quit
5. Configure Switch D:
# Enable L2VPN.
<SwitchD> system-view
[SwitchD] l2vpn enable
# Configure Layer 2 forwarding for VXLAN tunnels.
[SwitchD] undo vxlan ip-forwarding
# Disable remote MAC address learning.
[SwitchD] vxlan tunnel mac-learning disable
# Create VXLAN 30 on VSI vpna.
[SwitchD] vsi vpna
[SwitchD-vsi-vpna] vxlan 30
[SwitchD-vsi-vpna-vxlan-30] quit
# Create an EVPN instance on VSI vpna. Configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchD-vsi-vpna] evpn encapsulation vxlan
[SwitchD-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchD-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchD-vsi-vpna-evpn-vxlan] quit
[SwitchD-vsi-vpna] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchD] bgp 200
[SwitchD-bgp-default] peer 3.3.3.3 as-number 200
[SwitchD-bgp-default] peer 3.3.3.3 connect-interface Loopback 0
[SwitchD-bgp-default] address-family l2vpn evpn
[SwitchD-bgp-default-evpn] peer 3.3.3.3 enable
[SwitchD-bgp-default-evpn] quit
[SwitchD-bgp-default] quit
# On HundredGigE 1/0/1, create Ethernet service instance 1000 to match VLAN 200.
[SwitchD] interface hundredgige 1/0/1
[SwitchD-HundredGigE1/0/1] service-instance 1000
[SwitchD-HundredGigE1/0/1-srv1000] encapsulation s-vid 200
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchD-HundredGigE1/0/1-srv1000] xconnect vsi vpna
[SwitchD-HundredGigE1/0/1-srv1000] quit
Verifying the configuration
1. Verify the configuration on EDs. (This example uses Switch B.)
# Verify that the ED has discovered Switch A and Switch C through IMET routes and has established VXLAN and VXLAN-DCI tunnels to the switches.
[SwitchB] display evpn auto-discovery imet
Total number of automatically discovered peers: 2
VSI name: vpna
RD PE_address Tunnel_address Tunnel mode VXLAN ID
1:10 1.1.1.1 1.1.1.1 VXLAN 10
1:500 3.3.3.3 3.3.3.3 VXLAN-DCI 500
# Verify that the VXLAN and VXLAN-DCI tunnels on the ED are up.
[SwitchB] display interface tunnel
Tunnel0
Current state: UP
Line protocol state: UP
Description: Tunnel0 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 2.2.2.2, destination 1.1.1.1
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
Tunnel1
Current state: UP
Line protocol state: UP
Description: Tunnel1 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 2.2.2.2, destination 3.3.3.3
Tunnel protocol/transport UDP_VXLAN-DCI/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
# Verify that the VXLAN and VXLAN-DCI tunnels have been assigned to VXLAN 10, and that no tunnels are assigned to intermediate VXLAN 500.
[SwitchB] display l2vpn vsi verbose
VSI Name: vpna
VSI Index : 0
VSI State : Up
MTU : -
Bandwidth : -
Broadcast Restrain : -
Multicast Restrain : -
Unknown Unicast Restrain: -
MAC Learning : -
MAC Table Limit : -
MAC Learning rate : -
Drop Unknown : -
Flooding : Enabled
Statistics : Disabled
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel0 0x5000000 UP Auto Disabled
Tunnel1 0x5000001 UP Auto Disabled
VSI Name: vpnb
VSI Index : 1
VSI State : Down
MTU : -
Bandwidth : -
Broadcast Restrain : -
Multicast Restrain : -
Unknown Unicast Restrain: -
MAC Learning : -
MAC Table Limit : -
MAC Learning rate : -
Drop Unknown : -
Flooding : Enabled
Statistics : Disabled
VXLAN ID : 500
# Verify that the ED has generated EVPN MAC address entries for the VMs, and the remote MAC address entry has the M flag.
[SwitchB] display evpn route mac
Flags: D - Dynamic B - BGP L - Local active
G - Gateway S - Static M - Mapping
VSI name: vpna
MAC address Link ID/Name Flags Next hop
0001-0001-0011 Tunnel0 B 1.1.1.1
0001-0001-0033 Tunnel1 BM 3.3.3.3
2. Verify that VM 1 and VM 2 can communicate. (Details not shown.)
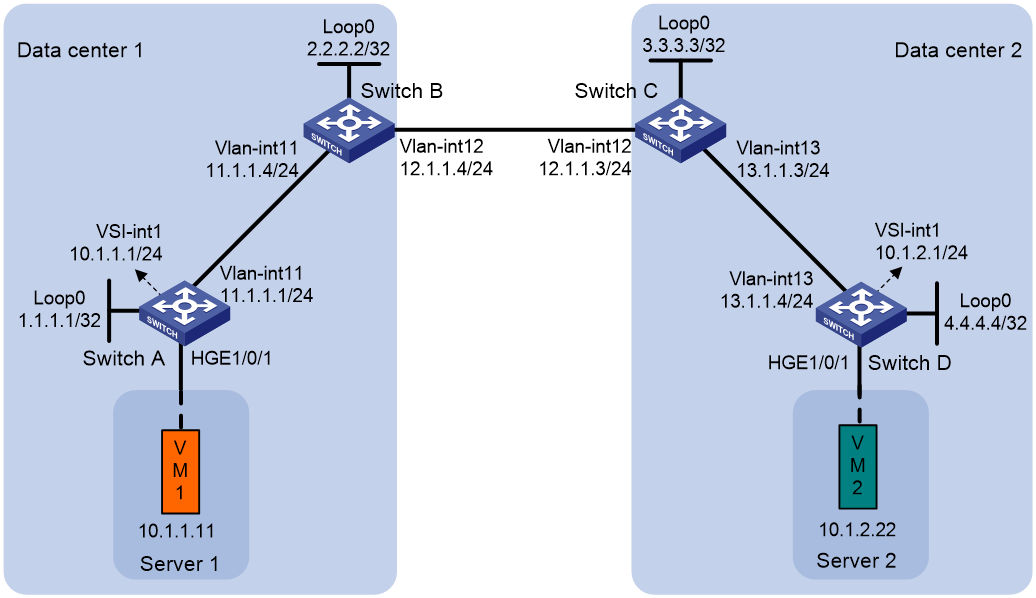
Example: Configuring EVPN-DCI IPv4 Layer 3 communication
Network configuration
As shown in Figure 5:
· Configure VXLAN 10 for data center 1, and configure VXLAN 20 for data center 2.
· Configure Switch A and Switch D as distributed EVPN gateways to perform Layer 3 forwarding between VXLAN 10 and VXLAN 20.
· Configure Switch B and Switch C as EDs.
Procedure
|
IMPORTANT: By default, interfaces on the device are operating in Layer 3 mode. Before you configure Ethernet service instances on an interface, you must use the port link-mode command to configure the interface to operate in Layer 2 mode. |
1. Configure IP addresses and unicast routing settings:
# On VM 1, specify 10.1.1.1 as the gateway address. On VM 2, specify 10.1.2.1 as the gateway address. (Details not shown.)
# Assign IP addresses to interfaces, as shown in Figure 5. (Details not shown.)
# Configure OSPF on the transport network for the switches to reach one another. (Details not shown.)
2. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchA] vxlan tunnel mac-learning disable
[SwitchA] vxlan tunnel arp-learning disable
# Create VXLAN 10 on VSI vpna.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
# Create an EVPN instance on VSI vpna. Configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchA-vsi-vpna] evpn encapsulation vxlan
[SwitchA-vsi-vpna-evpn-vxlan] route-distinguisher auto
[SwitchA-vsi-vpna-evpn-vxlan] vpn-target auto
[SwitchA-vsi-vpna-evpn-vxlan] quit
[SwitchA-vsi-vpna] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchA] bgp 100
[SwitchA-bgp-default] peer 2.2.2.2 as-number 100
[SwitchA-bgp-default] peer 2.2.2.2 connect-interface loopback 0
[SwitchA-bgp-default] address-family l2vpn evpn
[SwitchA-bgp-default-evpn] peer 2.2.2.2 enable
[SwitchA-bgp-default-evpn] quit
[SwitchA-bgp-default] quit
# On HundredGigE 1/0/1, create Ethernet service instance 1000 to match VLAN 100.
[SwitchA] interface hundredgige 1/0/1
[SwitchA-HundredGigE1/0/1] service-instance 1000
[SwitchA-HundredGigE1/0/1-srv1000] encapsulation s-vid 100
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-HundredGigE1/0/1-srv1000] xconnect vsi vpna
[SwitchA-HundredGigE1/0/1-srv1000] quit
# Configure RD and route target settings for VPN instance vpn1.
[SwitchA] ip vpn-instance vpn1
[SwitchA-vpn-instance-vpn1] route-distinguisher 1:1
[SwitchA-vpn-instance-vpn1] address-family ipv4
[SwitchA-vpn-ipv4-vpn1] vpn-target 2:2
[SwitchA-vpn-ipv4-vpn1] quit
[SwitchA-vpn-instance-vpn1] address-family evpn
[SwitchA-vpn-evpn-vpn1] vpn-target 1:1
[SwitchA-vpn-evpn-vpn1] quit
[SwitchA-vpn-instance-vpn1] quit
# Configure VSI-interface 1 as a distributed gateway.
[SwitchA] interface vsi-interface 1
[SwitchA-Vsi-interface1] ip binding vpn-instance vpn1
[SwitchA-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchA-Vsi-interface1] mac-address 1-1-1
[SwitchA-Vsi-interface1] distributed-gateway local
[SwitchA-Vsi-interface1] quit
# Create VSI-interface 2. Associate VSI-interface 2 with VPN instance vpn1, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchA] interface vsi-interface 2
[SwitchA-Vsi-interface2] ip binding vpn-instance vpn1
[SwitchA-Vsi-interface2] l3-vni 1000
[SwitchA-Vsi-interface2] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] gateway vsi-interface 1
[SwitchA-vsi-vpna] quit
3. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchB] vxlan tunnel mac-learning disable
[SwitchB] vxlan tunnel arp-learning disable
# Enable DCI on the Layer 3 interface that connects Switch B to Switch C for the switches to establish a VXLAN-DCI tunnel.
[SwitchB] interface vlan-interface 12
[SwitchB-Vlan-interface12] dci enable
[SwitchB-Vlan-interface12] quit
# Configure BGP to advertise BGP EVPN routes. Enable nexthop replacement for routes advertised to Switch A, and enable router MAC replacement for routes advertised to and received from Switch C.
[SwitchB] bgp 100
[SwitchB-bgp-default] peer 3.3.3.3 as-number 200
[SwitchB-bgp-default] peer 3.3.3.3 connect-interface loopback 0
[SwitchB-bgp-default] peer 3.3.3.3 ebgp-max-hop 64
[SwitchB-bgp-default] peer 1.1.1.1 as-number 100
[SwitchB-bgp-default] peer 1.1.1.1 connect-interface loopback 0
[SwitchB-bgp-default] address-family l2vpn evpn
[SwitchB-bgp-default-evpn] peer 3.3.3.3 enable
[SwitchB-bgp-default-evpn] peer 3.3.3.3 router-mac-local
[SwitchB-bgp-default-evpn] peer 1.1.1.1 enable
[SwitchB-bgp-default-evpn] peer 1.1.1.1 next-hop-local
[SwitchB-bgp-default-evpn] quit
[SwitchB-bgp-default] quit
# Configure RD and route target settings for VPN instance vpn1.
[SwitchB] ip vpn-instance vpn1
[SwitchB-vpn-instance-vpn1] route-distinguisher 1:2
[SwitchB-vpn-instance-vpn1] address-family ipv4
[SwitchB-vpn-ipv4-vpn1] vpn-target 2:2
[SwitchB-vpn-ipv4-vpn1] quit
[SwitchB-vpn-instance-vpn1] address-family evpn
[SwitchB-vpn-evpn-vpn1] vpn-target 1:1
[SwitchB-vpn-evpn-vpn1] quit
[SwitchB-vpn-instance-vpn1] quit
# Create VSI-interface 2. Associate VSI-interface 2 with VPN instance vpn1, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchB] interface vsi-interface 2
[SwitchB-Vsi-interface2] ip binding vpn-instance vpn1
[SwitchB-Vsi-interface2] l3-vni 1000
[SwitchB-Vsi-interface2] quit
4. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchC] vxlan tunnel mac-learning disable
[SwitchC] vxlan tunnel arp-learning disable
# Enable DCI on the Layer 3 interface that connects Switch C to Switch B For the switches to establish a VXLAN-DCI tunnel.
[SwitchC] interface vlan-interface 12
[SwitchC-Vlan-interface12] dci enable
[SwitchC-Vlan-interface12] quit
# Configure BGP to advertise BGP EVPN routes. Enable nexthop replacement for routes advertised to Switch D, and enable router MAC replacement for routes advertised to and received from Switch B.
[SwitchC] bgp 200
[SwitchC-bgp-default] peer 2.2.2.2 as-number 100
[SwitchC-bgp-default] peer 2.2.2.2 connect-interface Loopback 0
[SwitchC-bgp-default] peer 2.2.2.2 ebgp-max-hop 64
[SwitchC-bgp-default] peer 4.4.4.4 as-number 200
[SwitchC-bgp-default] peer 4.4.4.4 connect-interface Loopback 0
[SwitchC-bgp-default] address-family l2vpn evpn
[SwitchC-bgp-default-evpn] peer 2.2.2.2 enable
[SwitchC-bgp-default-evpn] peer 2.2.2.2 router-mac-local
[SwitchC-bgp-default-evpn] peer 4.4.4.4 enable
[SwitchC-bgp-default-evpn] peer 4.4.4.4 next-hop-local
[SwitchC-bgp-default-evpn] quit
[SwitchC-bgp-default] quit
# Configure RD and route target settings for VPN instance vpn1.
[SwitchC] ip vpn-instance vpn1
[SwitchC-vpn-instance-vpn1] route-distinguisher 1:3
[SwitchC-vpn-instance-vpn1] address-family ipv4
[SwitchC-vpn-ipv4-vpn1] vpn-target 2:2
[SwitchC-vpn-ipv4-vpn1] quit
[SwitchC-vpn-instance-vpn1] address-family evpn
[SwitchC-vpn-evpn-vpn1] vpn-target 1:1
[SwitchC-vpn-evpn-vpn1] quit
[SwitchC-vpn-instance-vpn1] quit
# Create VSI-interface 2. Associate VSI-interface 2 with VPN instance vpn1, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchC] interface vsi-interface 2
[SwitchC-Vsi-interface2] ip binding vpn-instance vpn1
[SwitchC-Vsi-interface2] l3-vni 1000
[SwitchC-Vsi-interface2] quit
5. Configure Switch D:
# Enable L2VPN.
<SwitchD> system-view
[SwitchD] l2vpn enable
# Disable remote MAC address learning and remote ARP learning.
[SwitchD] vxlan tunnel mac-learning disable
[SwitchD] vxlan tunnel arp-learning disable
# Create an EVPN instance on VSI vpnb. Configure the switch to automatically generate an RD and a route target for the EVPN instance.
[SwitchD] vsi vpnb
[SwitchD-vsi-vpnb] evpn encapsulation vxlan
[SwitchD-vsi-vpnb-evpn-vxlan] route-distinguisher auto
[SwitchD-vsi-vpnb-evpn-vxlan] vpn-target auto
[SwitchD-vsi-vpnb-evpn-vxlan] quit
# Create VXLAN 20 on VSI vpnb.
[SwitchD-vsi-vpnb] vxlan 20
[SwitchD-vsi-vpnb-vxlan-20] quit
[SwitchD-vsi-vpnb] quit
# Configure BGP to advertise BGP EVPN routes.
[SwitchD] bgp 200
[SwitchD-bgp-default] peer 3.3.3.3 as-number 200
[SwitchD-bgp-default] peer 3.3.3.3 connect-interface Loopback 0
[SwitchD-bgp-default] address-family l2vpn evpn
[SwitchD-bgp-default-evpn] peer 3.3.3.3 enable
[SwitchD-bgp-default-evpn] quit
[SwitchD-bgp-default] quit
# On HundredGigE 1/0/1, create Ethernet service instance 3000 to match VLAN 3.
[SwitchD] interface hundredgige 1/0/1
[SwitchD-HundredGigE1/0/1] service-instance 3000
[SwitchD-HundredGigE1/0/1-srv3000] encapsulation s-vid 3
# Map Ethernet service instance 3000 to VSI vpnb.
[SwitchD-HundredGigE1/0/1-srv3000] xconnect vsi vpnb
[SwitchD-HundredGigE1/0/1-srv3000] quit
# Configure RD and route target settings for VPN instance vpn1.
[SwitchD] ip vpn-instance vpn1
[SwitchD-vpn-instance-vpn1] route-distinguisher 1:4
[SwitchD-vpn-instance-vpn1] address-family ipv4
[SwitchD-vpn-ipv4-vpn1] vpn-target 2:2
[SwitchD-vpn-ipv4-vpn1] quit
[SwitchD-vpn-instance-vpn1] address-family evpn
[SwitchD-vpn-evpn-vpn1] vpn-target 1:1
[SwitchD-vpn-evpn-vpn1] quit
[SwitchD-vpn-instance-vpn1] quit
# Configure VSI-interface 1 as a distributed gateway.
[SwitchD] interface vsi-interface 1
[SwitchD-Vsi-interface1] ip binding vpn-instance vpn1
[SwitchD-Vsi-interface1] ip address 10.1.2.1 255.255.255.0
[SwitchD-Vsi-interface1] mac-address 1-2-1
[SwitchD-Vsi-interface1] distributed-gateway local
[SwitchD-Vsi-interface1] quit
# Create VSI-interface 2. Associate VSI-interface 2 with VPN instance vpn1, and configure the L3 VXLAN ID as 1000 for the VPN instance.
[SwitchD] interface vsi-interface 2
[SwitchD-Vsi-interface2] ip binding vpn-instance vpn1
[SwitchD-Vsi-interface2] l3-vni 1000
[SwitchD-Vsi-interface2] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpnb.
[SwitchD] vsi vpnb
[SwitchD-vsi-vpnb] gateway vsi-interface 1
[SwitchD-vsi-vpnb] quit
Verifying the configuration
1. Verify the configuration on EDs. (This example uses Switch B.)
# Verify that the ED has discovered Switch A and Switch C through MAC/IP advertisement routes and IP prefix advertisement routes, and has established VXLAN and VXLAN-DCI tunnels to the switches.
[SwitchB] display evpn auto-discovery macip-prefix
Destination IP Source IP L3VNI Tunnel mode OutgoingInterface
1.1.1.1 2.2.2.2 1000 VXLAN Vsi-interface2
3.3.3.3 2.2.2.2 1000 VXLAN-DCI Vsi-interface2
# Verify that the VXLAN and VXLAN-DCI tunnels on the ED are up.
[SwitchB] display interface tunnel
Tunnel0
Current state: UP
Line protocol state: UP
Description: Tunnel0 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 2.2.2.2, destination 1.1.1.1
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
Tunnel1
Current state: UP
Line protocol state: UP
Description: Tunnel1 Interface
Bandwidth: 64 kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 2.2.2.2, destination 3.3.3.3
Tunnel protocol/transport UDP_VXLAN-DCI/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
# Verify that the ED has EVPN ARP entries and EVPN routes for the VMs.
[SwitchB] display arp vpn-instance vpn1
Type: S-Static D-Dynamic O-Openflow R-Rule I-Invalid
IP address MAC address VLAN/VSI name Interface Aging Type
1.1.1.1 0031-1900-0000 0 Tunnel0 N/A R
3.3.3.3 0031-3900-0000 0 Tunnel1 N/A R
[SwitchB] display ip routing-table vpn-instance vpn1
Destinations : 4 Routes : 4
Destination/Mask Proto Pre Cost NextHop Interface
10.1.1.0/24 BGP 255 0 1.1.1.1 Vsi2
10.1.1.11/32 BGP 255 0 1.1.1.1 Vsi2
10.1.2.0/24 BGP 255 0 3.3.3.3 Vsi2
10.1.2.22/32 BGP 255 0 3.3.3.3 Vsi2
2. Verify that VM 1 and VM 2 can communicate. (Details not shown.)