- Table of Contents
-
- 14-Security Configuration Guide
- 00-Preface
- 01-ACL configuration
- 02-Time range configuration
- 03-User profile configuration
- 04-Public key management
- 05-PKI configuration
- 06-IPsec configuration
- 07-SSH configuration
- 08-SSL configuration
- 09-Session management
- 10-Attack detection and prevention configuration
- 11-ARP attack protection configuration
- 12-ND attack defense configuration
- 13-Crypto engine configuration
- 14-Connection limit configuration
- 15-Password control configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 07-SSH configuration | 429.21 KB |
Contents
Configuring the device as an SSH server
Specifying the SSH service port
Configuring the user lines for SSH login
Configuring a client's host public key
Configuring the SSH management parameters
Specifying a PKI domain for the SSH server
Configuring the device as an Stelnet client
Stelnet client tasks at a glance
Specifying the source IP address for outgoing SSH packets
Establishing a connection to an Stelnet server
Establishing a connection to an Stelnet server based on Suite B
Configuring the device as an SFTP client
Specifying the source IP address for outgoing SFTP packets
Establishing a connection to an SFTP server
Establishing a connection to an SFTP server based on Suite B
Terminating the connection with the SFTP server
Configuring the device as an SCP client
Establishing a connection to an SCP server
Establishing a connection to an SCP server based on Suite B
Specifying algorithms for SSH2
Specifying key exchange algorithms for SSH2
Specifying public key algorithms for SSH2
Specifying encryption algorithms for SSH2
Specifying MAC algorithms for SSH2
Display and maintenance commands for SSH
Stelnet configuration examples
Example: Configuring the device as an Stelnet server (publickey authentication)
Example: Configuring the device as an Stelnet client (password authentication)
Example: Configuring the device as an Stelnet client (publickey authentication)
Example: Configuring the device as an SFTP server (password authentication)
Example: Configuring the device as an SFTP client (publickey authentication)
Example: Configuring SCP with password authentication
Configuring SSH
About SSH
Secure Shell (SSH) is a network security protocol. Using encryption and authentication, SSH can implement secure remote access and file transfer over an insecure network.
SSH uses the typical client-server model to establish a channel for secure data transfer based on TCP.
SSH includes two versions: SSH1.x and SSH2.0 (hereinafter referred to as SSH1 and SSH2), which are not compatible. SSH2 is better than SSH1 in performance and security.
SSH applications
The device supports the following SSH applications:
· Secure Telnet—Stelnet provides secure and reliable network terminal access services. Through Stelnet, a user can securely log in to a remote server. Stelnet can protect devices against attacks, such as IP spoofing and plain text password interception. The device can act as an Stelnet server or an Stelnet client.
· Secure File Transfer Protocol—Based on SSH2, SFTP uses SSH connections to provide secure file transfer. The device can act as an SFTP server, allowing a remote user to log in to the SFTP server for secure file management and transfer. The device can also act as an SFTP client, enabling a user to log in from the device to a remote device for secure file transfer.
· Secure Copy—Based on SSH2, SCP offers a secure method to copy files. The device can act as an SCP server, allowing a user to log in to the device for file upload and download. The device can also act as an SCP client, enabling a user to log in from the device to a remote device for secure file transfer.
· NETCONF over SSH—Based on SSH2, it enables users to securely log in to the device through SSH and perform NETCONF operations on the device through the NETCONF-over-SSH connections. The device can act only as a NETCONF-over-SSH server. For more information about NETCONF, see Network Management and Monitoring Configuration Guide.
When acting as an SSH server or client, the device supports the following SSH versions:
· When acting as an Stelnet, SFTP, or SCP server, the device supports both SSH2 and SSH1.
· When acting as an SSH client, the device supports only SSH2.
· When acting as a NETCONF-over-SSH server, the device supports only SSH2.
How SSH works
This section uses SSH2 as an example to describe the stages to establish an SSH session.
Table 1 Stages to establish an SSH session
|
Stages |
Description |
|
Connection establishment |
The SSH server listens to connection requests on port 22. After a client initiates a connection request, the server and the client establish a TCP connection. |
|
Version negotiation |
The two parties determine a version to use. |
|
Algorithm negotiation |
SSH supports multiple algorithms. Based on the local algorithms, the two parties negotiate the following algorithms: · Key exchange algorithm for generating session keys. · Encryption algorithm for encrypting data. · Public key algorithm for the digital signature and authentication. · HMAC algorithm for protecting data integrity. |
|
Key exchange |
The two parties use the DH exchange algorithm to dynamically generate the session keys and session ID. · The session keys are used for protecting data transfer. · The session ID is used for identifying the SSH connection. In this stage, the client also authenticates the server. |
|
Authentication |
The SSH server authenticates the client in response to the client's authentication request. |
|
Session request |
After passing the authentication, the client sends a session request to the server to request the establishment of a session (or request the Stelnet, SFTP, SCP, or NETCONF service). |
|
Interaction |
After the server grants the request, the client and the server start to communicate with each other in the session. In this stage, you can paste commands in text format and execute them at the CLI. The text pasted at one time must be no more than 2000 bytes. As a best practice to ensure the correct execution of commands, paste commands that are in the same view. To execute commands of more than 2000 bytes, save the commands in a configuration file, upload the file to the server through SFTP, and use it to restart the server. |
SSH authentication methods
This section describes authentication methods that are supported by the device when it acts as an SSH server.
Password authentication
The SSH server authenticates a client through the AAA mechanism. The password authentication process is as follows:
1. The client sends the server an authentication request that includes the encrypted username and password.
2. The server performs the following operations:
a. Decrypts the request to get the username and password in plain text.
b. Verifies the username and password locally or through remote AAA authentication.
c. Informs the client of the authentication result.
If the remote AAA server requires the user to enter a password for secondary authentication, it send the SSH server an authentication response carrying a prompt. The prompt is transparently transmitted to the client to notify the user to enter a specific password. When the user enters the correct password, the AAA sever examines the password validity. If the password is valid, the SSH server returns an authentication success message to the client.
SSH1 clients do not support secondary password authentication initiated by the AAA server.
For more information about AAA, see User Access and Authentication Configuration Guide.
Publickey authentication
The server authenticates a client by verifying the digital signature of the client. The publickey authentication process is as follows:
1. The client sends the server a publickey authentication request that includes the username, public key, and public key algorithm name.
If the digital certificate of the client is required in authentication, the client also encapsulates the digital certificate in the authentication request. The digital certificate carries the public key information of the client.
2. The server verifies the client's public key.
¡ If the public key is invalid, the server informs the client of the authentication failure.
¡ If the public key is valid, the server requests the digital signature of the client. After receiving the signature, the server uses the public key to verify the signature and informs the client of the authentication result.
When acting as an SSH server, the device supports using the public key algorithms DSA, ECDSA, and RSA to verify digital signatures.
When acting as an SSH client, the device supports using the public key algorithms DSA, ECDSA, and RSA to generate digital signatures.
For more information about public key configuration, see "Managing public keys."
Password-publickey authentication
The server requires SSH2 clients to pass both password authentication and publickey authentication. However, an SSH1 client only needs to pass either authentication.
Any authentication
The server requires clients to pass password authentication or publickey authentication.
SSH support for Suite B
Suite B contains a set of encryption and authentication algorithms that meet high security requirements. Table 2 lists all algorithms in Suite B.
The SSH server and client support using the X.509v3 certificate for identity authentication in compliance with the algorithm, negotiation, and authentication specifications defined in RFC 6239.
|
Security level |
Key exchange algorithm |
Encryption algorithm and HMAC algorithm |
Public key algorithm |
|
128-bit |
ecdh-sha2-nistp256 |
AES128-GCM |
x509v3-ecdsa-sha2-nistp256 |
|
192-bit |
ecdh-sha2-nistp384 |
AES256-GCM |
x509v3-ecdsa-sha2-nistp384 |
|
Both |
ecdh-sha2-nistp256 ecdh-sha2-nistp384 |
AES128-GCM AES256-GCM |
x509v3-ecdsa-sha2-nistp256 x509v3-ecdsa-sha2-nistp384 |
Configuring the device as an SSH server
SSH server tasks at a glance
To configure an SSH server, perform the following tasks:
2. (Optional.) Specifying the SSH service port
3. Enabling the SSH server
4. Configuring the user lines for SSH login
Required only for Stelnet and NETCONF-over-SSH servers.
5. Configuring a client's host public key
Required for authentication method publickey, password-publickey, or any.
¡ Required for authentication method publickey, password-publickey, or any.
¡ Optional for the password authentication method.
7. (Optional.) Configuring the SSH management parameters
SSH management settings, such as authentication and connection control settings, help improve security of SSH connections.
8. (Optional.) Specifying a PKI domain for the SSH server
Generating local key pairs
About this task
The DSA, ECDSA, or RSA key pairs on the SSH server are required for generating the session keys and session ID in the key exchange stage. They can also be used by a client to authenticate the server. When a client authenticates the server, it compares the public key received from the server with the server's public key that the client saved locally. If the keys are consistent, the client uses the locally saved server's public key to decrypt the digital signature received from the server. If the decryption succeeds, the server passes the authentication.
To support SSH clients that use different types of key pairs, generate DSA, ECDSA, and RSA key pairs on the SSH server.
· RSA key pairs—The SSH server generates a server key pair and a host key pair for RSA. The RSA server key pair is only used in SSH1 to encrypt the session key for secure transmission of the session key. It is not used in SSH2, because no session key transmission is required in SSH2.
· DSA key pair—The SSH server generates only one DSA host key pair. SSH1 does not support the DSA algorithm.
· ECDSA key pair—The SSH server generates only one ECDSA host key pair.
Restrictions and guidelines
Local DSA, ECDSA, and RSA key pairs for SSH use default names. You cannot assign names to the key pairs.
If the device does not have RSA key pairs with default names, it automatically generates one RSA server key pair and one RSA host key pair when SSH starts. Both key pairs use their default names. The SSH application starts when you execute an SSH server command on the device.
The key modulus length must be less than 2048 bits when you generate the DSA key pair on the SSH server.
When you generate an ECDSA key pair, you can generate only a secp256r1 or secp384r1 ECDSA key pair.
Procedure
1. Enter system view.
system-view
2. Generate local key pairs.
public-key local create { dsa | ecdsa { secp256r1 | secp384r1 } | rsa }
Specifying the SSH service port
About this task
The default port of the SSH service is 22. You can specify another port for the SSH service to improve security of SSH connections.
Restrictions and guidelines
If you modify the SSH port number when the SSH server is enabled, the SSH service is restarted and all SSH connections are terminated after the modification. SSH users must reconnect to the SSH server to access the server.
If you set the SSH port to a well-known port number, the service that uses the well-known port number might fail to start. Well-known port numbers are in the range of 1 to 1024.
Procedure
1. Enter system view.
system-view
2. Specify the SSH service port.
ssh server port port-number
By default, the SSH service port is 22.
Enabling the Stelnet server
About this task
After you enable the Stelnet server on the device, a client can log in to the device through Stelnet.
Procedure
1. Enter system view.
system-view
2. Enable the Stelnet server.
ssh server enable
By default, the Stelnet server is disabled.
Enabling the SFTP server
About this task
After you enable the SFTP server on the device, a client can log in to the device through SFTP.
Restrictions and guidelines
When acting as an SFTP server, the device does not support SFTP connections initiated by SSH1 clients.
Procedure
1. Enter system view.
system-view
2. Enable the SFTP server.
sftp server enable
By default, the SFTP server is disabled.
Enabling the SCP server
About this task
After you enable the SCP server on the device, a client can log in to the device through SCP.
Restrictions and guidelines
When acting as an SCP server, the device does not support SCP connections initiated by SSH1 clients.
Procedure
1. Enter system view.
system-view
2. Enable the SCP server.
scp server enable
By default, the SCP server is disabled.
Enabling NETCONF over SSH
About this task
After you enable NETCONF over SSH on the device, a client can perform NETCONF operations on the device through a NETCONF-over-SSH connection.
Restrictions and guidelines
When acting as a server in the NETCONF-over-SSH connection, the device does not support connection requests initiated by SSH1 clients.
Procedure
1. Enter system view.
system-view
2. Enable NETCONF over SSH.
netconf ssh server enable
By default, NETCONF over SSH is disabled.
For more information about NETCONF over SSH commands, see Network Management and Monitoring Command Reference.
Configuring the user lines for SSH login
About this task
Depending on the SSH application, an SSH client can be an Stelnet client, SFTP client, SCP client, or NETCONF-over-SSH client.
Only Stelnet and NETCONF-over-SSH clients require the user line configuration. The user line configuration takes effect on the clients at the next login.
Procedure
1. Enter system view.
system-view
2. Enter VTY user line view.
line vty number [ ending-number ]
3. Set the login authentication mode to scheme.
authentication-mode scheme
By default, the authentication mode is password.
For more information about this command, see Fundamentals Command Reference.
Configuring a client's host public key
About this task
In publickey authentication, the server compares the SSH username and the client's host public key received from the client with the locally saved SSH username and the client's host public key. If they are the same, the server checks the digital signature that the client sends. The client generates the digital signature by using the private key that is paired with the client's host public key.
For publickey authentication, password-publickey authentication, or any authentication, you must perform the following tasks:
1. Configure the client's DSA, ECDSA, or RSA host public key on the server.
2. Specify the associated host private key on the client to generate the digital signature.
If the device acts as an SSH client, specify the public key algorithm on the client. The algorithm determines the associated host private key for generating the digital signature.
Client public key configuration methods
You can configure the client host public key by using the following methods:
· Manually enter the content of a client's host public key on the server.
a. Display the host public key on the client and record the key.
b. Type the client's host public key character by character on the server, or use the copy and paste method.
The manually entered key must be in DER format without being converted. For the displayed key to meet the requirement when the client is an H3C device, use the display public-key local public command. The format of the public key displayed in any other way (for example, by using the public-key local export command) might be incorrect. If the key is not in correct format, the system discards the key.
· Import the client host public key from a public key file.
a. Save the client public key file to the server. For example, transfer the client public key file to the server in binary mode through FTP or TFTP.
b. Import the client public key from the locally saved public key file.
During the import process, the server automatically converts the host public key to a string in PKCS format.
Restrictions and guidelines
As a best practice, configure no more than 20 SSH client's host public keys on an SSH server.
Import the client's host public key as a best practice.
Entering a client's host public key
1. Enter system view.
system-view
2. Enter public key view.
public-key peer keyname
3. Configure a client's host public key.
Enter the content of the client's host public key character by character, or use the copy and paste method.
When you enter the content of a client's host public key, you can use spaces and carriage returns between characters but the system does not save them. For more information, see "Managing public keys."
4. Exit public key view and save the key.
peer-public-key end
Importing a client's host public key from the public key file
1. Enter system view.
system-view
2. Import a client's public key from the public key file.
public-key peer keyname import sshkey filename
Configuring an SSH user
About this task
Configure an SSH user and a local user depending on the authentication method.
· If the authentication method is publickey, you must create an SSH user and a local user on the SSH server. The two users must have the same username, so that the SSH user can be assigned the correct working directory and user role.
· If the authentication method is password, you must perform one of the following tasks:
¡ For local authentication, configure a local user on the SSH server.
¡ For remote authentication, configure an SSH user on a remote authentication server, for example, a RADIUS server.
You do not need to create an SSH user by using the ssh user command. However, if you want to display all SSH users, including the password-only SSH users, for centralized management, you can use this command to create them. If such an SSH user has been created, make sure you have specified the correct service type and authentication method.
· If the authentication method is password-publickey or any, you must create an SSH user on the SSH server and perform one of the following tasks:
¡ For local authentication, configure a local user on the SSH server.
¡ For remote authentication, configure an SSH user on a remote authentication server, for example, a RADIUS server.
In either case, the local user or the SSH user configured on the remote authentication server must have the same username as the SSH user.
Restrictions and guidelines
If you change the authentication parameters for a logged-in SSH user, the change takes effect on the user at the next login.
For an SFTP or SCP user, the working directory depends on the authentication method.
· If the authentication method is password, the working directory is authorized by AAA.
· If the authentication method is publickey or password-publickey, the working folder is specified by the authorization-attribute command in the associated local user view.
For an SSH user, the user role also depends on the authentication method.
· If the authentication method is password, the user role is authorized by AAA.
· If the authentication method is publickey or password-publickey, the user role is specified by the authorization-attribute command in the associated local user view.
For all authentication methods except password authentication, you must specify a client's host public key or digital certificate.
· For a client that sends the user's public key information directly to the server, specify the client's host public key on the server. The specified public key must already exist. For more information about public keys, see "Configuring a client's host public key."
· For a client that sends the user's public key information to the server through a digital certificate, specify the PKI domain on the server. This PKI domain verifies the client's digital certificate. For successful verification, the specified PKI domain must have the correct CA certificate. To specify the PKI domain, use the ssh user or ssh server pki-domain command. For more information about configuring a PKI domain, see "Configuring PKI."
For information about configuring local users and remote authentication, see AAA configuration in User Access and Authentication Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Create an SSH user, and specify the service type and authentication method.
ssh user username service-type { all | netconf | scp | sftp | stelnet } authentication-type { password | { any | password-publickey | publickey } [ assign { pki-domain domain-name | publickey keyname } ] }
An SSH server supports up to 1024 SSH users.
Configuring the SSH management parameters
Enabling the SSH server to support SSH1 clients
1. Enter system view.
system-view
2. Enable the SSH server to support SSH1 clients.
ssh server compatible-ssh1x enable
By default, the SSH server does not support SSH1 clients.
Setting the minimum interval for updating the RSA server key pair
1. Enter system view.
system-view
2. Set the minimum interval for updating the RSA server key pair.
ssh server rekey-interval interval
By default, the device does not update the RSA server key pair.
This configuration takes effect only on SSH1 clients.
Setting the SSH user authentication timeout timer
1. Enter system view.
system-view
2. Set the SSH user authentication timeout timer.
ssh server authentication-timeout time-out-value
The default setting is 60 seconds.
Perform this task to prevent malicious occupation of TCP connections. If a user does not finish the authentication when the timeout timer expires, the connection cannot be established.
Setting the maximum number of SSH authentication attempts
1. Enter system view.
system-view
2. Set the maximum number of SSH authentication attempts.
ssh server authentication-retries retries
The default setting is 3.
Perform this task to prevent malicious hacking of usernames and passwords. If the authentication method is any, the total number of publickey authentication attempts and password authentication attempts cannot exceed the upper limit.
Specifying an SSH login control ACL
1. Enter system view.
system-view
2. Specify an SSH login control ACL.
IPv4:
ssh server acl { advanced-acl-number | basic-acl-number | mac mac-acl-number }
IPv6:
ssh server ipv6 acl { ipv6 { advanced-acl-number | basic-acl-number } | mac mac-acl-number }
This feature uses an ACL to filter SSH clients that initiate SSH connections to the server. By default, no ACLs are specified and all SSH users can initiate SSH connections to the server.
Enabling logging for SSH login attempts that are denied by the SSH login control ACL
1. Enter system view.
system-view
2. Enable logging for SSH login attempts that are denied by the SSH login control ACL.
ssh server acl-deny-log enable
By default, logging is disabled for login attempts that are denied by the SSH login control ACL.
This command enables SSH to generate log messages for SSH login attempts that are denied by the SSH login control ACL and send the messages to the information center.
Setting the DSCP value in the packets that the SSH server sends to SSH clients
1. Enter system view.
system-view
2. Set the DSCP value in the packets that the SSH server sends to the SSH clients.
IPv4:
ssh server dscp dscp-value
IPv6:
ssh server ipv6 dscp dscp-value
By default, the DSCP value of SSH packets is 48.
The DSCP value of a packet defines the priority of the packet and affects the transmission priority of the packet. A bigger DSCP value represents a higher priority.
Setting the SFTP connection idle timeout timer
1. Enter system view.
system-view
2. Set the SFTP connection idle timeout timer.
sftp server idle-timeout time-out-value
By default, the SFTP connection idle timeout is 10 minutes.
When the SFTP connection idle timeout timer expires, the system automatically tears the connection down and releases the connection resources.
Setting the maximum number of online SSH users
1. Enter system view.
system-view
2. Set the maximum number of online SSH users.
aaa session-limit ssh max-sessions
The default setting is 32.
When the number of online SSH users reaches the upper limit, the system denies new SSH connection requests. Changing the upper limit does not affect online SSH users.
For more information about this command, see AAA commands in User Access and Authentication Command Reference.
Specifying a PKI domain for the SSH server
About this task
The PKI domain specified for the SSH server has the following functions:
· The SSH server uses the PKI domain to send its certificate to the client in the key exchange stage.
· The SSH server uses the PKI domain to authenticate the client's certificate if no PKI domain is specified for the client authentication by using the ssh user command.
Procedure
1. Enter system view.
system-view
2. Specify a PKI domain for the SSH server.
ssh server pki-domain domain-name
By default, no PKI domain is specified for the SSH server.
Configuring the device as an Stelnet client
Stelnet client tasks at a glance
To configure an Stelnet client, perform the following tasks:
Only required for authentication method publickey, password-publickey, or any.
2. (Optional.) Specifying the source IP address for outgoing SSH packets
3. Establishing a connection to an Stelnet server
4. (Optional.) Establishing a connection to an Stelnet server based on Suite B
Generating local key pairs
About this task
You must generate local key pairs on Stelnet clients when the Stelnet server uses the publickey, password-publickey, or any authentication method.
Restrictions and guidelines
Local DSA, ECDSA, and RSA key pairs for SSH use default names. You cannot assign names to the key pairs.
The key modulus length must be less than 2048 bits when you generate a DSA key pair.
When you generate an ECDSA key pair, you can generate only a secp256r1 or secp384r1 ECDSA key pair.
Procedure
1. Enter system view.
system-view
2. Generate local key pairs.
public-key local create { dsa | ecdsa { secp256r1 | secp384r1 } | rsa }
Specifying the source IP address for outgoing SSH packets
About this task
After you specify the source IP address for outgoing SSH packets on an Stelnet client, the client uses the specified IP address to communicate with the Stelnet server.
Restrictions and guidelines
As a best practice, specify a loopback interface as the source interface or specify the IP address of a loopback or dialer interface as the source address of outgoing SSH packets for the following purposes:
· Ensuring the communication between the Stelnet client and the Stelnet server.
· Improving the manageability of Stelnet clients in authentication service.
Procedure
1. Enter system view.
system-view
2. Specify the source address for outgoing SSH packets.
IPv4:
ssh client source { interface interface-type interface-number | ip ip-address }
By default, an IPv4 Stelnet client uses the primary IPv4 address of the output interface in the matching route as the source address of the outgoing SSH packets.
IPv6:
ssh client ipv6 source { interface interface-type interface-number | ipv6 ipv6-address }
By default, an IPv6 Stelnet client automatically selects a source IPv6 address for outgoing SSH packets in compliance with RFC 3484.
Establishing a connection to an Stelnet server
About this task
Perform this task to enable the Stelnet client feature on the device and establish a connection to the Stelnet server. You can specify the public key algorithm and the preferred encryption, HMAC, and key exchange algorithms to be used during the connection.
To access the server, a client must use the server's host public key to authenticate the server. As a best practice, configure the server's host public key on the device in an insecure network. If the server's host public key is not configured on the client, the client will notify you to confirm whether to continue with the access.
· If you choose to continue, the client accesses the server and downloads the server's host public key. The downloaded public key will be used to authenticate the server in subsequent accesses.
· If you choose to not continue, the connection cannot be established.
Restrictions and guidelines for establishing a connection to an Stelnet server
An Stelnet client cannot establish connections to both IPv4 and IPv6 Stelnet servers.
Establishing a connection to an IPv4 Stelnet server
Execute the following command in user view to establish a connection with an IPv4 Stelnet server:
ssh2 server [ port-number ] [ identity-key { dsa | ecdsa-sha2-nistp256 | ecdsa-sha2-nistp384 | rsa | { x509v3-ecdsa-sha2-nistp256 | x509v3-ecdsa-sha2-nistp384 } pki-domain domain-name } | prefer-compress zlib | prefer-ctos-cipher { 3des-cbc | aes128-cbc | aes128-ctr | aes128-gcm | aes192-ctr | aes256-cbc | aes256-ctr | aes256-gcm | des-cbc } | prefer-ctos-hmac { md5 | md5-96 | sha1 | sha1-96 | sha2-256 | sha2-512 } | prefer-kex { dh-group-exchange-sha1 | dh-group1-sha1 | dh-group14-sha1 | ecdh-sha2-nistp256 | ecdh-sha2-nistp384 } | prefer-stoc-cipher { 3des-cbc | aes128-cbc | aes128-ctr | aes128-gcm | aes192-ctr | aes256-cbc | aes256-ctr | aes256-gcm | des-cbc } | prefer-stoc-hmac { md5 | md5-96 | sha1 | sha1-96 | sha2-256 | sha2-512 } ] * [ dscp dscp-value | escape character | { public-key keyname | server-pki-domain domain-name } | source { interface interface-type interface-number | ip ip-address } ] *
Establishing a connection to an IPv6 Stelnet server
Execute the following command in user view to establish a connection to an IPv6 Stelnet server:
ssh2 ipv6 server [ port-number ] [ -i interface-type interface-number ] [ identity-key { dsa | ecdsa-sha2-nistp256 | ecdsa-sha2-nistp384 | rsa | { x509v3-ecdsa-sha2-nistp256 | x509v3-ecdsa-sha2-nistp384 } pki-domain domain-name } | prefer-compress zlib | prefer-ctos-cipher { 3des-cbc | aes128-cbc | aes128-ctr | aes128-gcm | aes192-ctr | aes256-cbc | aes256-ctr | aes256-gcm | des-cbc } | prefer-ctos-hmac { md5 | md5-96 | sha1 | sha1-96 | sha2-256 | sha2-512 } | prefer-kex { dh-group-exchange-sha1 | dh-group1-sha1 | dh-group14-sha1 | ecdh-sha2-nistp256 | ecdh-sha2-nistp384 } | prefer-stoc-cipher { 3des-cbc | aes128-cbc | aes128-ctr | aes128-gcm | aes192-ctr | aes256-cbc | aes256-ctr | aes256-gcm | des-cbc } | prefer-stoc-hmac { md5 | md5-96 | sha1 | sha1-96 | sha2-256 | sha2-512 } ] * [ dscp dscp-value | escape character | { public-key keyname | server-pki-domain domain-name } | source { interface interface-type interface-number | ipv6 ipv6-address } ] *
Establishing a connection to an Stelnet server based on Suite B
Execute the following command in user view to establish a connection to an Stelnet server based on Suite B:
IPv4:
ssh2 server [ port-number ] suite-b [ 128-bit | 192-bit ] pki-domain domain-name [ server-pki-domain domain-name ] [ prefer-compress zlib ] [ dscp dscp-value | escape character | source { interface interface-type interface-number | ip ip-address } ] *
IPv6:
ssh2 ipv6 server [ port-number ] [ -i interface-type interface-number ] suite-b [ 128-bit | 192-bit ] pki-domain domain-name [ server-pki-domain domain-name ] [ prefer-compress zlib ] [ dscp dscp-value | escape character | source { interface interface-type interface-number | ipv6 ipv6-address } ] *
Configuring the device as an SFTP client
SFTP client tasks at a glance
To configure an SFTP client, perform the following tasks:
Only required for authentication method publickey, password-publickey, or any.
2. (Optional.) Specifying the source IP address for outgoing SFTP packets
3. Establishing a connection to an SFTP server
4. (Optional.) Establishing a connection to an SFTP server based on Suite B
5. (Optional.) Working with SFTP directories
6. (Optional.) Working with SFTP files
7. (Optional.) Displaying help information
8. (Optional.) Terminating the connection with the SFTP server
Generating local key pairs
About this task
You must generate local key pairs on SFTP clients when the SFTP server uses the publickey, password-publickey, or any authentication method.
Restrictions and guidelines
Local DSA, ECDSA, and RSA key pairs for SSH use default names. You cannot assign names to the key pairs.
The key modulus length must be less than 2048 bits when you generate a DSA key pair.
When you generate an ECDSA key pair, you can generate only a secp256r1 or secp384r1 ECDSA key pair.
Procedure
1. Enter system view.
system-view
2. Generate local key pairs.
public-key local create { dsa | ecdsa { secp256r1 | secp384r1 } | rsa }
Specifying the source IP address for outgoing SFTP packets
About this task
After you specify the source IP address for outgoing SFTP packets on an SFTP client, the client uses the specified IP address to communicate with the SFTP server.
Restrictions and guidelines
As a best practice, specify a loopback interface as the source interface or specify the IP address of a loopback or dialer interface as the source address of outgoing SFTP packets for the following purposes:
· Ensuring the communication between the SFTP client and the SFTP server.
· Improving the manageability of SFTP clients in authentication service.
Procedure
1. Enter system view.
system-view
2. Specify the source address for outgoing SFTP packets.
IPv4:
sftp client source { ip ip-address | interface interface-type interface-number }
By default, an SFTP client uses the primary IPv4 address of the output interface in the matching route as the source address of the outgoing SFTP packets.
IPv6:
sftp client ipv6 source { ipv6 ipv6-address | interface interface-type interface-number }
By default, an IPv6 SFTP client automatically selects a source IPv6 address for the outgoing SFTP packets in compliance with RFC 3484.
Establishing a connection to an SFTP server
About this task
Perform this task to enable the SFTP client feature on the device and establish a connection to the SFTP server. You can specify the public key algorithm and the preferred encryption, HMAC, and key exchange algorithms to be used during the connection.
To access the server, a client must use the server's host public key to authenticate the server. As a best practice, configure the server's host public key on the device in an insecure network. If the server's host public key is not configured on the client, the client will notify you to confirm whether to continue with the access.
· If you choose to continue, the client accesses the server and downloads the server's host public key. The downloaded public key will be used to authenticate the server in subsequent accesses.
· If you choose to not continue, the connection cannot be established.
Restrictions and guidelines for establishing a connection to an SFTP server
An SFTP client cannot establish connections to both IPv4 and IPv6 SFTP servers.
Establishing a connection to an IPv4 SFTP server
Execute the following command in user view to establish a connection to an IPv4 SFTP server:
sftp server [ port-number ] [ identity-key { dsa | ecdsa-sha2-nistp256 | ecdsa-sha2-nistp384 | rsa | { x509v3-ecdsa-sha2-nistp256 | x509v3-ecdsa-sha2-nistp384 } pki-domain domain-name } | prefer-compress zlib | prefer-ctos-cipher { 3des-cbc | aes128-cbc | aes128-ctr | aes128-gcm | aes192-ctr | aes256-cbc | aes256-ctr | aes256-gcm | des-cbc } | prefer-ctos-hmac { md5 | md5-96 | sha1 | sha1-96 | sha2-256 | sha2-512 } | prefer-kex { dh-group-exchange-sha1 | dh-group1-sha1 | dh-group14-sha1 | ecdh-sha2-nistp256 | ecdh-sha2-nistp384 } | prefer-stoc-cipher { 3des-cbc | aes128-cbc | aes128-ctr | aes128-gcm | aes192-ctr | aes256-cbc | aes256-ctr | aes256-gcm | des-cbc } | prefer-stoc-hmac { md5 | md5-96 | sha1 | sha1-96 | sha2-256 | sha2-512 } ] * [ dscp dscp-value | { public-key keyname | server-pki-domain domain-name } | source { interface interface-type interface-number | ip ip-address } ] *
Establishing a connection to an IPv6 SFTP server
Execute the following command in user view to establish a connection to an IPv6 SFTP server:
sftp ipv6 server [ port-number ] [ -i interface-type interface-number ] [ identity-key { dsa | ecdsa-sha2-nistp256 | ecdsa-sha2-nistp384 | rsa | { x509v3-ecdsa-sha2-nistp256 | x509v3-ecdsa-sha2-nistp384 } pki-domain domain-name } | prefer-compress zlib | prefer-ctos-cipher { 3des-cbc | aes128-cbc | aes128-ctr | aes128-gcm | aes192-ctr | aes256-cbc | aes256-ctr | aes256-gcm | des-cbc } | prefer-ctos-hmac { md5 | md5-96 | sha1 | sha1-96 | sha2-256 | sha2-512 } | prefer-kex { dh-group-exchange-sha1 | dh-group1-sha1 | dh-group14-sha1 | ecdh-sha2-nistp256 | ecdh-sha2-nistp384 } | prefer-stoc-cipher { 3des-cbc | aes128-cbc | aes128-ctr | aes128-gcm | aes192-ctr | aes256-cbc | aes256-ctr | aes256-gcm | des-cbc } | prefer-stoc-hmac { md5 | md5-96 | sha1 | sha1-96 | sha2-256 | sha2-512 } ] * [ dscp dscp-value | { public-key keyname | server-pki-domain domain-name } | source { interface interface-type interface-number | ipv6 ipv6-address } ] *
Establishing a connection to an SFTP server based on Suite B
Execute the following command in user view to establish a connection to an SFTP server based on Suite B:
IPv4:
sftp server [ port-number ] suite-b [ 128-bit | 192-bit ] pki-domain domain-name [ server-pki-domain domain-name ] [ prefer-compress zlib ] [ dscp dscp-value | source { interface interface-type interface-number | ip ip-address } ] *
IPv6:
ssh2 ipv6 server [ port-number ] [ -i interface-type interface-number ] suite-b [ 128-bit | 192-bit ] pki-domain domain-name [ server-pki-domain domain-name ] [ prefer-compress zlib ] [ dscp dscp-value | escape character | source { interface interface-type interface-number | ipv6 ipv6-address } ] *
Working with SFTP directories
About this task
After you establish a connection to an SFTP server, you can operate directories of the SFTP server.
Changing the working directory on the SFTP server
1. Enter SFTP client view.
For more information, see "Establishing a connection to an SFTP server."
2. Change the working directory on the SFTP server.
cd [ remote-path ]
3. (Optional.) Return to the upper-level directory.
cdup
Displaying the current working directory on the SFTP server
1. Enter SFTP client view.
For more information, see "Establishing a connection to an SFTP server."
2. Display the current working directory on the SFTP server.
pwd
Displaying files under a directory
1. Enter SFTP client view.
For more information, see "Establishing a connection to an SFTP server."
2. Display files under a directory.
¡ dir [ -a | -l ] [ remote-path ]
¡ ls [ -a | -l ] [ remote-path ]
The dir command has the same function as the ls command.
Changing the name of a directory on the SFTP server
1. Enter SFTP client view.
For more information, see "Establishing a connection to an SFTP server."
2. Change the name of a directory on the SFTP server.
rename oldname newname
Creating a new directory on the SFTP server
1. Enter SFTP client view.
For more information, see "Establishing a connection to an SFTP server."
2. Create a new directory on the SFTP server.
mkdir remote-path
Deleting directories on the SFTP server
1. Enter SFTP client view.
For more information, see "Establishing a connection to an SFTP server."
2. Delete one or more directories from the SFTP server.
rmdir remote-path
Working with SFTP files
About this task
After you establish a connection to an SFTP server, you can operate files on the SFTP server.
Changing the name of a file on the SFTP server
1. Enter SFTP client view.
For more information, see "Establishing a connection to an SFTP server."
2. Change the name of a file on the SFTP server.
rename old-name new-name
Downloading a file from the SFTP server and save it locally
1. Enter SFTP client view.
For more information, see "Establishing a connection to an SFTP server."
2. Download a file from the SFTP server and save it locally.
get remote-file [ local-file ]
Uploading a local file to the SFTP server
1. Enter SFTP client view.
For more information, see "Establishing a connection to an SFTP server."
2. Upload a local file to the SFTP server.
put local-file [ remote-file ]
Display files under a directory
1. Enter SFTP client view.
For more information, see "Establishing a connection to an SFTP server."
2. Display files under a directory.
¡ dir [ -a | -l ] [ remote-path ]
¡ ls [ -a | -l ] [ remote-path ]
The dir command has the same function as the ls command.
Deleting a file from the SFTP server
1. Enter SFTP client view.
For more information, see "Establishing a connection to an SFTP server."
2. Delete a file from the SFTP server.
¡ delete remote-file
¡ remove remote-file
The delete command has the same function as the remove command.
Displaying help information
About this task
After you establish a connection to the SFTP server, you can display the help information of SFTP client commands, including the command syntax and parameter configuration.
Procedure
1. Enter SFTP client view.
For more information, see "Establishing a connection to an SFTP server."
2. Display SFTP client command help information.
¡ help
¡ ?
The help command has the same function as the ? command.
Terminating the connection with the SFTP server
1. Enter SFTP client view.
For more information, see "Establishing a connection to an SFTP server."
2. Terminate the connection with the SFTP server and return to user view.
¡ bye
¡ exit
¡ quit
The three commands have the same function.
Configuring the device as an SCP client
SCP client tasks at a glance
To configure an SCP client, perform the following tasks:
Only required for the publickey, password-publickey, or any authentication method.
2. Establishing a connection to an SCP server
3. (Optional.) Establishing a connection to an SCP server based on Suite B
Generating local key pairs
About this task
You must generate local key pairs on SCP clients when the SCP server uses the publickey, password-publickey, or any authentication method.
Restrictions and guidelines
Local DSA, ECDSA, and RSA key pairs for SSH use default names. You cannot assign names to the key pairs.
The key modulus length must be less than 2048 bits when you generate a DSA key pair.
When you generate an ECDSA key pair, you can generate only a secp256r1 or secp384r1 ECDSA key pair.
Procedure
1. Enter system view.
system-view
2. Generate local key pairs.
public-key local create { dsa | ecdsa { secp256r1 | secp384r1 } | rsa }
Establishing a connection to an SCP server
About this task
Perform this task to enable the SCP client feature on the device, establish a connection to the SCP server, and transfer files with the server. You can specify the public key algorithm and the preferred encryption, HMAC, and key exchange algorithms to be used during the connection.
To access the server, a client must use the server's host public key to authenticate the server. As a best practice, configure the server's host public key on the device in an insecure network. If the server's host public key is not configured on the client, the client will notify you to confirm whether to continue with the access.
· If you choose to continue, the client accesses the server and downloads the server's host public key. The downloaded public key will be used to authenticate the server in subsequent accesses.
· If you choose to not continue, the connection cannot be established.
Restrictions and guidelines for establishing a connection to an SCP server
An SCP client cannot establish connections to both IPv4 and IPv6 SCP servers.
Establishing a connection to an IPv4 SCP server
Execute the following command in user view to connect to an IPv4 SCP server, and transfer files with the server:
scp server [ port-number ] { get | put } source-file-name [ destination-file-name ] [ identity-key { dsa | ecdsa-sha2-nistp256 | ecdsa-sha2-nistp384 | rsa | { x509v3-ecdsa-sha2-nistp256 | x509v3-ecdsa-sha2-nistp384 } pki-domain domain-name } | prefer-compress zlib | prefer-ctos-cipher { 3des-cbc | aes128-cbc | aes128-ctr | aes128-gcm | aes192-ctr | aes256-cbc | aes256-ctr | aes256-gcm | des-cbc } | prefer-ctos-hmac { md5 | md5-96 | sha1 | sha1-96 | sha2-256 | sha2-512 } | prefer-kex { dh-group-exchange-sha1 | dh-group1-sha1 | dh-group14-sha1 | ecdh-sha2-nistp256 | ecdh-sha2-nistp384 } | prefer-stoc-cipher { 3des-cbc | aes128-cbc | aes128-ctr | aes128-gcm | aes192-ctr | aes256-cbc | aes256-ctr | aes256-gcm | des-cbc } | prefer-stoc-hmac { md5 | md5-96 | sha1 | sha1-96 | sha2-256 | sha2-512 } ] * [ { public-key keyname | server-pki-domain domain-name } | source { interface interface-type interface-number | ip ip-address } ] *
Establishing a connection to an IPv6 SCP server
Execute the following command in user view to connect to an IPv6 SCP server, and transfer files with the server.
scp ipv6 server [ port-number ] [ -i interface-type interface-number ] { get | put } source-file-name [ destination-file-name ] [ identity-key { dsa | ecdsa-sha2-nistp256 | ecdsa-sha2-nistp384 | rsa | { x509v3-ecdsa-sha2-nistp256 | x509v3-ecdsa-sha2-nistp384 } pki-domain domain-name } | prefer-compress zlib | prefer-ctos-cipher { 3des-cbc | aes128-cbc | aes128-ctr | aes128-gcm | aes192-ctr | aes256-cbc | aes256-ctr | aes256-gcm | des-cbc } | prefer-ctos-hmac { md5 | md5-96 | sha1 | sha1-96 | sha2-256 | sha2-512 } | prefer-kex { dh-group-exchange-sha1 | dh-group1-sha1 | dh-group14-sha1 | ecdh-sha2-nistp256 | ecdh-sha2-nistp384 } | prefer-stoc-cipher { 3des-cbc | aes128-cbc | aes128-ctr | aes128-gcm | aes192-ctr | aes256-cbc | aes256-ctr | aes256-gcm | des-cbc } | prefer-stoc-hmac { md5 | md5-96 | sha1 | sha1-96 | sha2-256 | sha2-512 } ] * [ { public-key keyname | server-pki-domain domain-name } | source { interface interface-type interface-number | ipv6 ipv6-address } ] *
Establishing a connection to an SCP server based on Suite B
Execute the following command in user view to establish a connection to an SCP server based on Suite B:
IPv4:
scp server [ port-number ] { get | put } source-file-name [ destination-file-name ] suite-b [ 128-bit | 192-bit ] pki-domain domain-name [ server-pki-domain domain-name ] [ prefer-compress zlib ] [ source { interface interface-type interface-number | ip ip-address } ] *
IPv6:
scp ipv6 server [ port-number ] [ -i interface-type interface-number ] { get | put } source-file-name [ destination-file-name ] suite-b [ 128-bit | 192-bit ] pki-domain domain-name [ server-pki-domain domain-name ] [ prefer-compress zlib ] [ source { interface interface-type interface-number | ipv6 ipv6-address } ] *
Specifying algorithms for SSH2
About algorithms for SSH2
The SSH2 client and server use the following types of algorithms for algorithm negotiation during the Stelnet, SFTP, or SCP session establishment:
· Key exchange algorithms.
· Public key algorithms.
· Encryption algorithms.
· MAC algorithms.
If you specify algorithms, SSH2 uses only the specified algorithms for algorithm negotiation. The client uses the specified algorithms to initiate the negotiation, and the server uses the matching algorithms to negotiate with the client. If multiple algorithms of the same type are specified, the algorithm specified earlier has a higher priority during negotiation.
Specifying key exchange algorithms for SSH2
1. Enter system view.
system-view
2. Specify key exchange algorithms for SSH2.
ssh2 algorithm key-exchange { dh-group-exchange-sha1 | dh-group1-sha1 | dh-group14-sha1 | ecdh-sha2-nistp256 | ecdh-sha2-nistp384 } *
By default, SSH2 uses the ecdh-sha2-nistp256, ecdh-sha2-nistp384, dh-group-exchange-sha1, dh-group14-sha1, and dh-group1-sha1 key exchange algorithms in descending order of priority for algorithm negotiation.
Specifying public key algorithms for SSH2
1. Enter system view.
system-view
2. Specify public key algorithms for SSH2.
:
ssh2 algorithm public-key { dsa | ecdsa-sha2-nistp256 | ecdsa-sha2-nistp384 | rsa | x509v3-ecdsa-sha2-nistp256 | x509v3-ecdsa-sha2-nistp384 } *
By default, SSH2 uses the x509v3-ecdsa-sha2-nistp256, x509v3-ecdsa-sha2-nistp384, ecdsa-sha2-nistp256, ecdsa-sha2-nistp384, rsa, and dsa public key algorithms in descending order of priority for algorithm negotiation.
Specifying encryption algorithms for SSH2
1. Enter system view.
system-view
2. Specify encryption algorithms for SSH2.
ssh2 algorithm cipher { 3des-cbc | aes128-cbc | aes128-ctr | aes128-gcm | aes192-ctr | aes256-cbc | aes256-ctr | aes256-gcm | des-cbc } *
By default, SSH2 uses the aes128-ctr, aes192-ctr, aes256-ctr, aes128-gcm, aes256-gcm, aes128-cbc, 3des-cbc, aes256-cbc, and des-cbc encryption algorithms in descending order of priority for algorithm negotiation.
Specifying MAC algorithms for SSH2
1. Enter system view.
system-view
2. Specify MAC algorithms for SSH2.
ssh2 algorithm mac { md5 | md5-96 | sha1 | sha1-96 | sha2-256 | sha2-512 } *
By default, SSH2 uses the sha2-256, sha2-512, sha1, md5, sha1-96, and md5-96 MAC algorithms in descending order of priority for algorithm negotiation.
Display and maintenance commands for SSH
Execute display commands in any view.
|
Task |
Command |
|
Display the public keys of the local key pairs. |
display public-key local { dsa | ecdsa | rsa } public [ name publickey-name ] |
|
Display information about peer public keys. |
display public-key peer [ brief | name publickey-name ] |
|
Display the source IP address configuration of the SFTP client. |
display sftp client source |
|
Display the source IP address configuration of the Stelnet client. |
display ssh client source |
|
Display SSH server status or sessions. |
display ssh server { session | status } |
|
Display SSH user information on the SSH server. |
display ssh user-information [ username ] |
|
Display algorithms used by SSH2 in the algorithm negotiation stage. |
display ssh2 algorithm |
For more information about the display public-key local and display public-key peer commands, see public key management commands in Security Command Reference.
Stelnet configuration examples
Example: Configuring the device as an Stelnet server (publickey authentication)
Network configuration
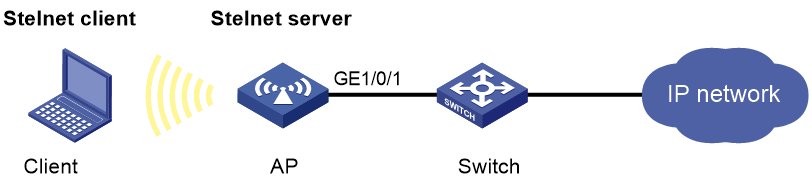
As shown in Figure 1:
· The AP acts as the Stelnet server, and it uses publickey authentication and the RSA public key algorithm.
· The wireless client acts as the Stelnet client, using Stelnet client software (SSH2). After the user on the client logs in to the AP through Stelnet, the user can configure and manage the AP as a network administrator.
Procedure
In the server configuration, the client's host public key is required. Use the client software to generate RSA key pairs on the client before configuring the Stelnet server.
There are different types of Stelnet client software, such as PuTTY and OpenSSH. This example uses an Stelnet client that runs PuTTY version 0.58.
The configuration procedure is as follows:
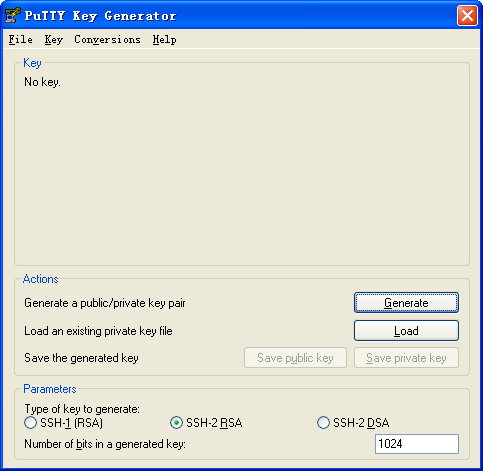
1. Generate RSA key pairs on the Stelnet client:
a. Run PuTTYGen.exe on the client, select SSH-2 RSA, and click Generate.
Figure 2 Generating a key pair on the client
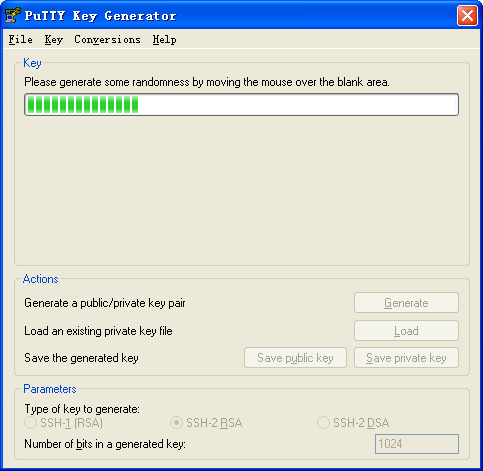
b. Continuously move the mouse and do not place the mouse over the green progress bar shown in Figure 3. Otherwise, the progress bar stops moving and the key pair generating progress stops.
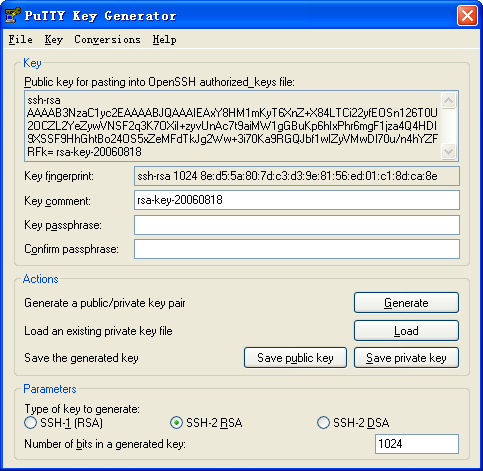
c. After the key pair is generated, click Save public key to save the public key.
A file saving window appears.
Figure 4 Saving a key pair on the client
d. Enter a file name (key.pub in this example), and click Save.
e. On the page shown in Figure 4, click Save private key to save the private key.
A confirmation dialog box appears.
f. Click Yes.
A file saving window appears.
g. Enter a file name (private.ppk in this example), and click Save.
h. Transmit the public key file to the server through FTP or TFTP. (Details not shown.)
2. Configure the Stelnet server:
# Generate RSA key pairs.
<AP> system-view
[AP] public-key local create rsa
The range of public key modulus is (512 ~ 2048).
If the key modulus is greater than 512, it will take a few minutes.
Press CTRL+C to abort.
Input the modulus length [default = 1024]:
Generating Keys...
.
Create the key pair successfully.
# Enable the Stelnet server.
[AP] ssh server enable
# Assign an IP address to VLAN-interface 2. The Stelnet client uses this IP address as the destination for SSH connection.
[AP] vlan 2
[AP-vlan2] quit
[AP] interface vlan-interface 2
[AP-Vlan-interface2] ip address 192.168.1.40 255.255.255.0
[AP-Vlan-interface2] quit
# Set the authentication mode to AAA for the user lines.
[AP] line vty 0 4
[AP-ui-vty0-4] authentication-mode scheme
# Specify SSH as the login protocol.
[AP-ui-vty0-4] protocol inbound ssh
[AP-ui-vty0-4] quit
# Import the client's public key from file key.pub and name it AP001.
[AP] public-key peer AP001 import sshkey key.pub
# Create a local user named client002.
[AP] local-user client002
# Authorize local user client002 to use the SSH service.
[AP-luser-manage-client002] service-type ssh
# Assign the network-admin user role to local user client002.
[AP-luser-manage-client002] authorization-attribute user-role network-admin
[AP-luser-manage-client002] quit
# Create an SSH user named client002. Specify the authentication method as publickey for the user, and assign the public key AP001 to the user.
[AP] ssh user client002 service-type stelnet authentication-type publickey assign publickey AP001
3. Specify the private key file and establish a connection to the Stelnet server:
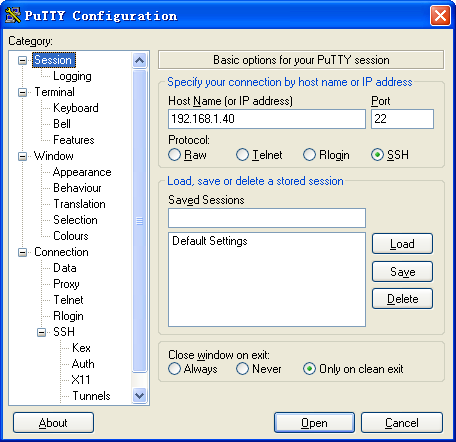
a. Launch PuTTY.exe on the Stelnet client to enter the interface shown in Figure 5.
b. In the Host Name (or IP address) field, enter the IP address (192.168.1.40) of the Stelnet server.
Figure 5 Specifying the host name (or IP address)
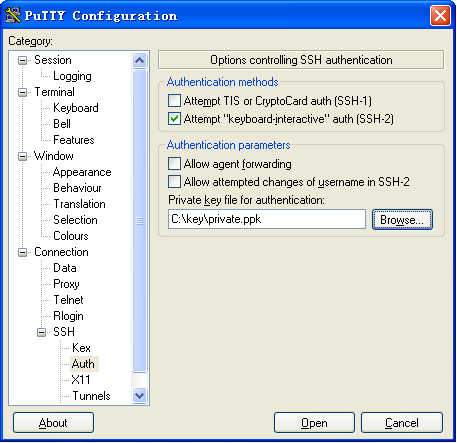
c. Select Connection > SSH > Auth from the navigation tree.
The window shown in Figure 6 appears.
d. Click Browse… and select the private key file (private.ppk in this example).
e. Click Open.
Figure 6 Selecting the private key file
f. Entering username client002 to log in to the Stelnet server.
Example: Configuring the device as an Stelnet client (password authentication)
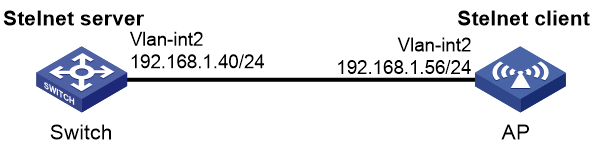
Network configuration
As shown in Figure 7:
· The switch acts as the Stelnet server and uses password authentication to authenticate the Stelnet client. The username and password of the client are saved on the switch.
· The AP acts as the Stelnet client. After the user on the AP logs in to the switch through Stelnet, the user can configure and manage the switch as a network administrator.
Procedure
1. Configure the Stelnet server:
# Generate RSA key pairs.
<Switch> system-view
[Switch] public-key local create rsa
The range of public key modulus is (512 ~ 2048).
If the key modulus is greater than 512, it will take a few minutes.
Press CTRL+C to abort.
Input the modulus length [default = 1024]:
Generating Keys...
.
Create the key pair successfully.
# Enable the Stelnet server.
[Switch] ssh server enable
# Assign an IP address to VLAN-interface 2. The Stelnet client uses this address as the destination address of the SSH connection.
[Switch] interface vlan-interface 2
[Switch-Vlan-interface2] ip address 192.168.1.40 255.255.255.0
[Switch-Vlan-interface2] quit
# Set the authentication mode to AAA for the user lines.
[Switch] line vty 0 4
[Switch-ui-vty0-4] authentication-mode scheme
# Specify SSH as the login protocol.
[Switch-ui-vty0-4] protocol inbound ssh
[Switch-ui-vty0-4] quit
# Create a local user named client001.
[Switch] local-user client001
# Set the password to aabbcc in plain text for local user client001.
[Switch-luser-manage-client001] password simple aabbcc
# Authorize local user client001 to use the SSH service.
[Switch-luser-manage-client001] service-type ssh
# Assign the network-admin user role to local user client001.
[Switch-luser-manage-client001] authorization-attribute user-role network-admin
[Switch-luser-manage-client001] quit
# Create an SSH user named client001. Specify the service type as stelnet and the authentication method as password for the user.
[Switch] ssh user client001 service-type stelnet authentication-type password
2. Establish a connection to the Stelnet server:
# Assign an IP address to VLAN-interface 2.
<AP> system-view
[AP] interface vlan-interface 2
[AP-Vlan-interface2] ip address 192.168.1.56 255.255.255.0
[AP-Vlan-interface2] quit
[AP] quit
# Establish an SSH connection to the server.
<AP> ssh2 192.168.1.40
Username: client001
Trying 192.168.1.40 ...
Press CTRL+K to abort
Connected to 192.168.1.40 ...
The Server is not authenticated. Continue? [Y/N]:y
Do you want to save the server public key? [Y/N]:n
Enter password:
After you enter the correct password, you successfully log in to the switch.
Example: Configuring the device as an Stelnet client (publickey authentication)
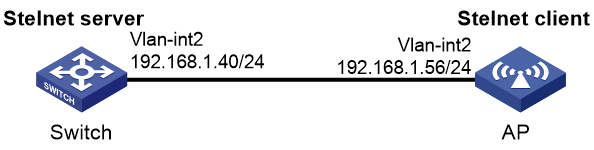
Network configuration
As shown in Figure 8:
· The switch acts as the Stelnet server, and it uses publickey authentication and the RSA public key algorithm.
· The AP acts as the Stelnet client. After the user on the AP logs in to the switch through Stelnet, the user can configure and manage the switch as a network administrator.
Procedure
In the server configuration, the client's host public key is required. Generate RSA key pairs on the client before configuring the Stelnet server.
1. Configure the Stelnet client:
# Assign an IP address to VLAN-interface 2.
<AP> system-view
[AP] interface vlan-interface 2
[AP-Vlan-interface2] ip address 192.168.1.56 255.255.255.0
[AP-Vlan-interface2] quit
# Generate RSA key pairs.
[AP] public-key local create rsa
The range of public key modulus is (512 ~ 2048).
If the key modulus is greater than 512, it will take a few minutes.
Press CTRL+C to abort.
Input the modulus length [default = 1024]:
Generating Keys...
.
Create the key pair successfully.
# Export the RSA host public key to file key.pub.
[AP] public-key local export rsa ssh2 key.pub
[AP] quit
# Transmit the public key file key.pub to the server through FTP or TFTP. (Details not shown.)
2. Configure the Stelnet server:
# Generate RSA key pairs.
<Switch> system-view
[Switch] public-key local create rsa
The range of public key modulus is (512 ~ 2048).
If the key modulus is greater than 512, it will take a few minutes.
Press CTRL+C to abort.
Input the modulus length [default = 1024]:
Generating Keys...
.
Create the key pair successfully.
# Enable the Stelnet server.
[Switch] ssh server enable
# Assign an IP address to VLAN-interface 2. The Stelnet client uses this address as the destination address for SSH connection.
[Switch] interface vlan-interface 2
[Switch-Vlan-interface2] ip address 192.168.1.40 255.255.255.0
[Switch-Vlan-interface2] quit
# Set the authentication mode to AAA for the user lines.
[Switch] line vty 0 4
[Switch-ui-vty0-4] authentication-mode scheme
# Specify SSH as the login protocol.
[Switch-ui-vty0-4] protocol inbound ssh
[Switch-ui-vty0-4] quit
# Import the peer public key from the file key.pub, and name it AP001.
[Switch] public-key peer AP001 import sshkey key.pub
# Create a local user named client002.
[Switch] local-user client002
# Authorize local user client002 to use the SSH service.
[Switch-luser-manage-client002] service-type ssh
# Assign the network-admin user role to local user client002.
[Switch-luser-manage-client002] authorization-attribute user-role network-admin
[Switch-luser-manage-client002] quit
# Create an SSH user named client002. Specify the authentication method as publickey for the user. Assign the public key AP001 to the user.
[Switch] ssh user client002 service-type stelnet authentication-type publickey assign publickey AP001
3. Establish an SSH connection to the Stelnet server.
<AP> ssh2 192.168.1.40
Username: client002
Trying 192.168.1.40 ...
Press CTRL+K to abort
Connected to 192.168.1.40 ...
The Server is not authenticated. Continue? [Y/N]:y
Do you want to save the server public key? [Y/N]:n
After you enter username client002 and then enter y to continue accessing the server, you can log in to the server successfully.
SFTP configuration examples
Example: Configuring the device as an SFTP server (password authentication)
Network configuration
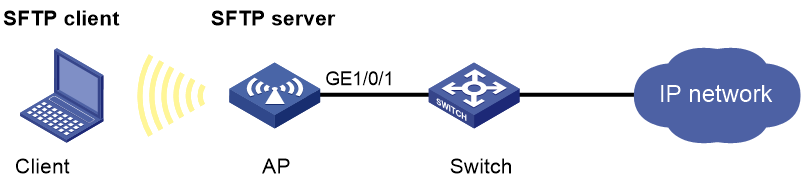
As shown in Figure 9:
· The AP acts as the SFTP server and uses password authentication to authenticate the SFTP client. The username and password of the client are saved on the AP.
· After the user on the SFTP client logs in to the AP through SFTP, the user can perform file management and transfer operations on the AP as a network administrator.
Procedure
1. Configure the SFTP server:
# Generate RSA key pairs.
<AP> system-view
[AP] public-key local create rsa
The range of public key modulus is (512 ~ 2048).
If the key modulus is greater than 512, it will take a few minutes.
Press CTRL+C to abort.
Input the modulus length [default = 1024]:
Generating Keys...
.
Create the key pair successfully.
# Enable the SFTP server.
[AP] sftp server enable
# Assign an IP address to VLAN-interface 2. The client uses this address as the destination for SSH connection.
[AP] interface vlan-interface 2
[AP-Vlan-interface2] ip address 192.168.1.45 255.255.255.0
[AP-Vlan-interface2] quit
# Create a local user named client002.
[AP] local-user client002
# Set the password to aabbcc in plain text for local user client002.
[AP-luser-manage-client002] password simple aabbcc
# Authorize local user client002 to use the SSH service.
[AP-luser-manage-client002] service-type ssh
# Assign the network-admin user role and working directory flash:/ to local user client002.
[AP-luser-manage-client002] authorization-attribute user-role network-admin work-directory flash:/
[AP-luser-manage-client002] quit
# Create an SSH user named client002. Specify the authentication method as password and service type as sftp for the user.
[AP] ssh user client002 service-type sftp authentication-type password
2. Establish a connection between the SFTP client and the SFTP server:
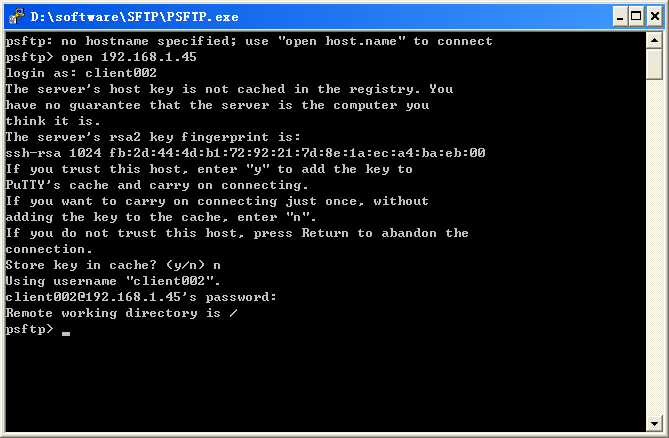
The device supports different types of SFTP client software. This example uses an SFTP client that runs PSFTP of PuTTy version 0.58.
|
|
NOTE: PSFTP supports only password authentication. |
To establish a connection to the SFTP server:
a. Run the psftp.exe to launch the client interface shown in Figure 10, and enter the following command:
open 192.168.1.45
b. Enter username client002 and password aabbcc as prompted to log in to the SFTP server.
Figure 10 SFTP client interface
Example: Configuring the device as an SFTP client (publickey authentication)
Network configuration
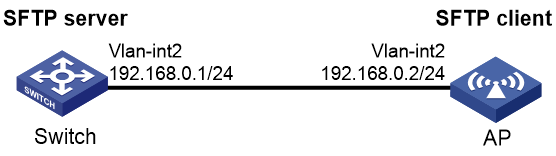
As shown in Figure 11:
· The switch acts as the SFTP server, and it uses publickey authentication and the RSA public key algorithm.
· The AP acts as the SFTP client. After the user on the AP logs in to the switch through SFTP, the user can perform file management and transfer operations on the switch as a network administrator.
Procedure
In the server configuration, the client's host public key is required. Generate RSA key pairs on the client before configuring the SFTP server.
1. Configure the SFTP client:
# Assign an IP address to VLAN-interface 2.
<AP> system-view
[AP] interface vlan-interface 2
[AP-Vlan-interface2] ip address 192.168.0.2 255.255.255.0
[AP-Vlan-interface2] quit
# Generate RSA key pairs.
[AP] public-key local create rsa
The range of public key modulus is (512 ~ 2048).
If the key modulus is greater than 512, it will take a few minutes.
Press CTRL+C to abort.
Input the modulus length [default = 1024]:
Generating Keys...
.
Create the key pair successfully.
# Export the host public key to the file pubkey.
[AP] public-key local export rsa ssh2 pubkey
[AP] quit
# Transmit the public key file pubkey to the server through FTP or TFTP. (Details not shown.)
2. Configure the SFTP server:
# Generate RSA key pairs.
<Switch> system-view
[Switch] public-key local create rsa
The range of public key modulus is (512 ~ 2048).
If the key modulus is greater than 512, it will take a few minutes.
Press CTRL+C to abort.
Input the modulus length [default = 1024]:
Generating Keys...
.
Create the key pair successfully.
# Enable the SFTP server.
[Switch] sftp server enable
# Assign an IP address to VLAN-interface 2. The SSH client uses this address as the destination for SSH connection.
[Switch] interface vlan-interface 2
[Switch-Vlan-interface2] ip address 192.168.0.1 255.255.255.0
[Switch-Vlan-interface2] quit
# Import the peer public key from the file pubkey, and name it AP001.
[Switch] public-key peer AP001 import sshkey pubkey
# Create a local user named client001.
[Switch] local-user client001
# Set the password to aabbcc in plain text for local user client001.
[Switch-luser-manage-client001] password simple aabbcc
# Authorize local user client001 to use the SSH service.
[Switch-luser-manage-client001] service-type ssh
# Assign the network-admin user role and working directory flash:/ to local user client001.
[Switch-luser-manage-client001] authorization-attribute user-role network-admin work-directory flash:/
[Switch-luser-manage-client001] quit
# Create an SSH user named client001. Specify the service type as sftp and the authentication method as publickey for the user. Assign the public key AP001 to the user.
[Switch] ssh user client001 service-type sftp authentication-type publickey assign publickey AP001
3. Establish a connection to the SFTP server:
# Establish a connection to the SFTP server and enter SFTP client view.
<AP> sftp 192.168.0.1 identity-key rsa
Input Username: client001
Trying 192.168.0.1 ...
Press CTRL+K to abort
Connected to 192.168.0.1 ...
The Server is not authenticated. Continue? [Y/N]:y
Do you want to save the server public key? [Y/N]:n
sftp-client>
# Display files under the current directory of the server, delete the file z, and verify the result.
sftp-client> dir
-rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg
-rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2
-rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey
drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new
-rwxrwxrwx 1 noone nogroup 225 Sep 01 06:55 pub
-rwxrwxrwx 1 noone nogroup 0 Sep 01 08:00 z
sftp-client> delete z
The following File will be deleted:
/z
Are you sure to delete it? [Y/N]:y
This operation may take a long time.Please wait...
File successfully Removed
sftp-client> dir
-rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg
-rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2
-rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey
drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new
-rwxrwxrwx 1 noone nogroup 225 Sep 01 06:55 pub
# Add directory new1 and verify the result.
sftp-client> mkdir new1
New directory created
sftp-client> dir
-rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg
-rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2
-rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey
drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new
-rwxrwxrwx 1 noone nogroup 225 Sep 01 06:55 pub
drwxrwxrwx 1 noone nogroup 0 Sep 02 06:30 new1
# Rename directory new1 to new2 and verify the result.
sftp-client> rename new1 new2
File successfully renamed
sftp-client> dir
-rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg
-rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2
-rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey
drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new
-rwxrwxrwx 1 noone nogroup 225 Sep 01 06:55 pub
drwxrwxrwx 1 noone nogroup 0 Sep 02 06:33 new2
# Download the file pubkey2 from the server and save it as a local file public.
sftp-client> get pubkey2 public
Remote file:/pubkey2 ---> Local file: public
Downloading file successfully ended
# Upload the local file pu to the server, save it as puk, and verify the result.
sftp-client> put pu puk
Local file:pu ---> Remote file: /puk
Uploading file successfully ended
sftp-client> dir
-rwxrwxrwx 1 noone nogroup 1759 Aug 23 06:52 config.cfg
-rwxrwxrwx 1 noone nogroup 225 Aug 24 08:01 pubkey2
-rwxrwxrwx 1 noone nogroup 283 Aug 24 07:39 pubkey
drwxrwxrwx 1 noone nogroup 0 Sep 01 06:22 new
drwxrwxrwx 1 noone nogroup 0 Sep 02 06:33 new2
-rwxrwxrwx 1 noone nogroup 283 Sep 02 06:35 pub
-rwxrwxrwx 1 noone nogroup 283 Sep 02 06:36 puk
sftp-client>
# Exit SFTP client view.
sftp-client> quit
Bye
Connection closed.
<AP>
SCP configuration examples
Example: Configuring SCP with password authentication
Network configuration
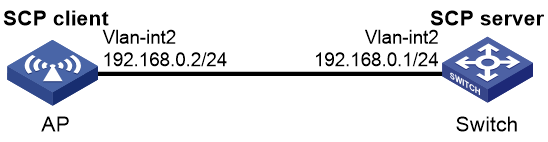
As shown in Figure 12:
· The switch acts as the SCP server and uses password authentication to authenticate the SCP client. The client's username and password are saved on the switch.
· The AP acts as the SCP client. After the user on the AP logs in to the switch through SCP, the user can transfer files between the AP and the switch as a network administrator.
Procedure
1. Configure the SCP server:
# Generate RSA key pairs.
<Switch> system-view
[Switch] public-key local create rsa
The range of public key modulus is (512 ~ 2048).
If the key modulus is greater than 512, it will take a few minutes.
Press CTRL+C to abort.
Input the modulus length [default = 1024]:
Generating Keys...
.
Create the key pair successfully.
# Enable the SCP server.
[SwitchB] scp server enable
# Configure an IP address for VLAN-interface 2. The client uses this address as the destination for SCP connection.
[Switch] interface vlan-interface 2
[Switch-Vlan-interface2] ip address 192.168.0.1 255.255.255.0
[Switch-Vlan-interface2] quit
# Create a local user named client001.
[Switch] local-user client001
# Set the password to aabbcc in plain text for local user client001.
[Switch-luser-manage-client001] password simple aabbcc
# Authorize local user client001 to use the SSH service.
[Switch-luser-manage-client001] service-type ssh
# Assign the network-admin user role to local user client001.
[Switch-luser-manage-client001] authorization-attribute user-role network-admin
[Switch-luser-manage-client001] quit
# Create an SSH user named client001. Specify the service type as scp and the authentication method as password for the user.
[Switch] ssh user client001 service-type scp authentication-type password
2. Configure an IP address for VLAN-interface 2 on the SCP client.
<AP> system-view
[AP] interface vlan-interface 2
[AP-Vlan-interface2] ip address 192.168.0.2 255.255.255.0
[AP-Vlan-interface2] quit
[AP] quit
3. Connect to the SCP server, download the file remote.bin from the server, and save it locally with the name local.bin.
<AP> scp 192.168.0.1 get remote.bin local.bin
Username: client001
Press CTRL+C to abort.
Connecting to 192.168.0.1 port 22.
The server is not authenticated. Continue? [Y/N]:y
Do you want to save the server public key? [Y/N]:n
[email protected]’s password:
remote.bin 100% 2875 2.8KB/s 00:00