- Table of Contents
-
- 04-Network Connectivity
- 00-Preface
- 01-About the network connectivity configuration guide
- 02-MAC address table configuration
- 03-Ethernet link aggregation configuration
- 04-VLAN configuration
- 05-Loop detection configuration
- 06-Spanning tree configuration
- 07-LLDP configuration
- 08-Layer 2 forwarding configuration
- 09-Port isolation configuration
- 10-PPP configuration
- 11-ARP configuration
- 12-IP addressing configuration
- 13-DHCP configuration
- 14-DHCPv6 configuration
- 15-DNS configuration
- 16-NAT configuration
- 17-IP performance optimization configuration
- 18-IPv6 basics configuration
- 19-Basic IP routing configuration
- 20-Static routing configuration
- 21-IPv6 static routing configuration
- 22-Multicast overview
- 23-IGMP snooping configuration
- 24-MLD snooping configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 16-NAT configuration | 192.58 KB |
Contents
Restrictions and guidelines: NAT configuration
Configuring static NAT on an interface
Configuring outbound one-to-one static NAT
Configuring outbound net-to-net static NAT
Configuring inbound one-to-one static NAT
Configuring inbound net-to-net static NAT
Configuring dynamic NAT on an interface
Configuring outbound dynamic NAT
Configuring inbound dynamic NAT
Configuring NAT session logging
Enabling sending ICMP error messages for NAT failures
Display and maintenance commands for NAT
NAT overview
Network Address Translation (NAT) translates an IP address in the IP packet header to another IP address. Typically, NAT is configured on gateways to enable private hosts to access external networks and external hosts to access private network resources such as a Web server.
Basic NAT concepts
The following describes basic NAT concepts:
· NAT device—A device configured with NAT. Typically, NAT is configured on the edge device that connects the internal and external networks.
· NAT interface—An interface configured with NAT.
· NAT rule—Rules that define how to perform address translation.
· NAT address—A public IP address used for address translation, and this address is reachable from the external network. The NAT address can be manually assigned or dynamically obtained.
· NAT entry—Stores the mapping between a private IP address and a public IP address. For more information, see "NAT entries."
· Easy IP—Uses the IP address of an interface as the NAT address. The IP address of the interface can be manually assigned or be obtained through DHCP or PPPoE.
Basic NAT operating mechanism
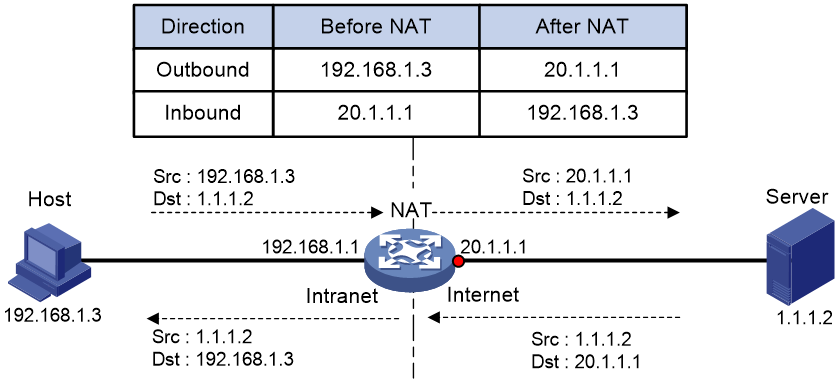
Figure 1 shows the basic NAT operating mechanism.
2. Upon receiving a response from the server, NAT translates the destination public address to the private address, and forwards the packet to the host.
The NAT operation is transparent to the terminals (the host and the server). NAT hides the private network from the external users and shows that the IP address of the internal host is 20.1.1.1.
NAT applications
Traditional NAT
Traditional NAT is configured on the interface that connects to the public network. It translates the source IP addresses of outgoing packets and destination IP addresses of incoming packets.
Twice NAT
Twice NAT translates the destination IP address on the receiving interface, and the source IP address on the sending interface. The receiving and sending interfaces are both NAT interfaces.
Twice NAT allows VPNs with overlapping addresses to access each other.
Bidirectional NAT
NAT translates the source and destination IP addresses of incoming packets on the receiving interface and outgoing packets on the sending interface.
Bidirectional NAT supports active access to external network resources from internal users when the internal and external IP addresses overlap.
NAT control
You can use ACLs to implement NAT control. The match criteria in the ACLs include the source IP address, source port number, destination IP address, destination port number, transport layer protocol, and VPN instance. Only packets permitted by an ACL are processed by NAT.
NAT translation methods
Static NAT
Static NAT creates a fixed mapping between a private address and a public address. It supports connections initiated from internal users to external network and from external users to the internal network. Static NAT applies to regular communications.
Dynamic NAT
Dynamic NAT uses an address pool to translate addresses. It applies to the scenario where a large number of internal users access the external network.
NO-PAT
Not Port Address Translation (NO-PAT) translates a private IP address to an IP public address. The public IP address cannot be used by another internal host until it is released.
NO-PAT supports all IP packets.
PAT
Port Address Translation (PAT) translates multiple private IP addresses to a single public IP address by mapping the private IP address and source port to the public IP address and a unique port. PAT supports TCP and UDP packets, and ICMP request packets.
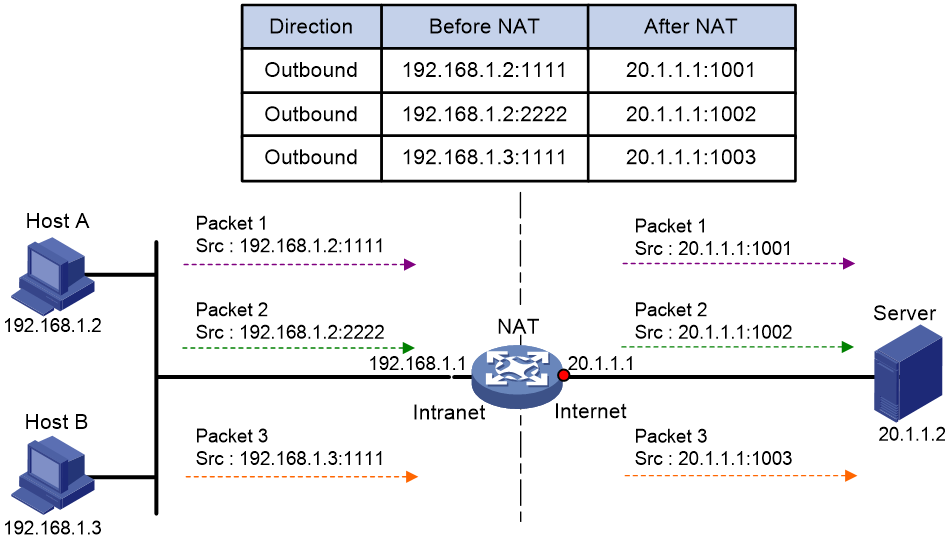
Figure 2 PAT operation
As shown in Figure 2, PAT translates the source IP addresses of the three packets to the same IP public address and translates their port numbers to different port numbers. Upon receiving a response, PAT translates the destination address and port number of the response, and forwards it to the target host.
PAT supports the following mappings:
· Endpoint-Independent Mapping (EIM)—Uses the same IP and port mapping (EIM entry) for packets from the same source IP and port to any destinations. EIM allows external hosts to initiate connections to the translated IP addresses and ports of internal hosts. It allows internal hosts behind different NAT gateways to access each other.
· Address and Port-Dependent Mapping (APDM)—Uses different IP and port mappings for packets from the same source IP and port to different destination IP addresses and ports. APDM allows an external host to initiate connections to an internal host only under the condition that the internal host has previously accessed the external host. It is secure, but it does not allow internal hosts behind different NAT gateways to access each other.
NAT entries
NAT session entry
NAT creates a NAT session entry for a session and creates an address mapping for the first packet in the session.
A NAT session entry contains extended NAT information, such as interface and translation method. Subsequent packets of the session are translated by using this entry.
· If the direction of the subsequent packets is the same as the direction of the first translated packets, NAT performs the source and destination address translation the same as the first packet.
· If the direction of the subsequent packets is the opposite direction, NAT perform reverse address translation. For example, if the source address of the first packets is translated, then the destination address of the subsequent packets is translated.
The session management module maintains the updating and aging of NAT session entries. For information about session management, see Security Configuration Guide.
EIM entry
If EIM is configured on the NAT device, the PAT mode will first create a NAT session entry, and then an EIM entry. The EIM entry is a 3-tuple entry, and it maps a private address/port to a public address/port. The EIM entry ensures:
· Subsequent new connections originating from the same source IP and port uses the same translation as the initial connection.
· Translates the address for new connections initiated from external hosts to the NAT address and port number based on the EIM entry.
An EIM entry ages out after all related NAT session entries age out.
NO-PAT entry
A NO-PAT entry maps a private address to a public address. The same mapping applies to subsequent connections originating from the same source IP.
A NO-PAT entry can also be created during the ALG process for NAT. For information about NAT ALG, see "NAT ALG."
A NO-PAT entry ages out after all related NAT session entries age out.
NAT ALG
NAT ALG (Application Level Gateway) translates address or port information in the application layer payloads to ensure connection establishment.
For example, an FTP application includes a data connection and a control connection. The IP address and port number for the data connection depend on the payload information of the control connection. This requires NAT ALG to translate the address and port information for data connection establishment.
Configuring NAT
Restrictions and guidelines: NAT configuration
The general restrictions and guidelines are as follows:
· Configure an ACL to identify the IP addresses to be translated. The match criteria include the source IP address, source port number, destination IP address, destination port number, and transport layer protocol.
· If you perform all the translation methods on an interface, the NAT rules are sorted in the following descending order:
a. Static NAT.
b. Dynamic NAT.
NAT sorts rules of the same type in descending order of NAT priority values. A NAT rule with a smaller priority value represents a higher priority for packet translation. You can move the NAT rules of the same type to change their priority for packet matching.
After you move a rule to the line before or after a reference NAT rule, the priority of the moved rule is changed, but the priority of the reference NAT rule is not.
· If the rule is moved to the line before the reference NAT rule, the priority of the moved rule equals the priority value of the reference rule minus one.
· If the rule is moved to the line after the reference NAT rule, the priority of the moved rule equals the priority value of the reference rule plus one.
NAT tasks at a glance
To configure NAT, perform the following tasks:
1. Configuring an address translation method
¡ Configuring static NAT on an interface
¡ Configuring dynamic NAT on an interface
2. (Optional.) Configuring NAT ALG
3. (Optional.) Configuring NAT logging
4. (Optional.) Enabling sending ICMP error messages for NAT failures
Configuring static NAT on an interface
Restrictions and guidelines
Typically, configure inbound static NAT with outbound dynamic NAT or outbound static NAT to implement bidirectional NAT.
Prerequisites
Before configuring static NAT, you must perform the following tasks:
· Configure an ACL to identify the IP addresses to be translated. For more information about ACLs, see Security Configuration Guide.
· Manually add a route for inbound static NAT. Use local-ip or local-network as the destination address, and use global-ip, an address in global-network, or the next hop directly connected to the output interface as the next hop.
Configuring outbound one-to-one static NAT
About this task
For address translation from a private IP address to a public IP address, configure outbound one-to-one static NAT on the interface connected to the external network.
· When the source IP address of an outgoing packet matches the local-ip, the source IP address is translated into the global-ip.
· When the destination IP address of an incoming packet matches the global-ip, the destination IP address is translated into the local-ip.
Procedure
1. Enter system view.
system-view
2. Configure a one-to-one mapping for outbound static NAT.
nat static outbound local-ip global-ip [ acl { ipv4-acl-number | name ipv4-acl-name } [ reversible ] ] [ rule rule-name ] [ priority priority ] [ disable ] [ counting ]
3. (Optional.) Rearrange outbound one-to-one mapping NAT rules to adjust their priorities.
nat static outbound rule move nat-rule-name1 { after | before } nat-rule-name2
4. Enter interface view.
interface interface-type interface-number
5. Enable static NAT on the interface.
nat static enable
By default, static NAT is disabled.
Configuring outbound net-to-net static NAT
About this task
For address translation from a private network to a public network, configure outbound net-to-net static NAT on the interface connected to the external network.
· When the source IP address of an outgoing packet matches the private address range, the source IP address is translated into a public address in the public address range.
· When the destination IP address of an incoming packet matches the public address range, the destination IP address is translated into a private address in the private address range.
Procedure
1. Enter system view.
system-view
2. Configure a net-to-net mapping for outbound static NAT.
nat static outbound net-to-net local-start-address local-end-address global global-network { mask-length | mask } [ acl { ipv4-acl-number | name ipv4-acl-name } [ reversible ] ] [ rule rule-name ] [ priority priority ] [ disable ] [ counting ]
3. Enter interface view.
interface interface-type interface-number
4. Enable static NAT on the interface.
nat static enable
By default, static NAT is disabled.
Configuring inbound one-to-one static NAT
About this task
For address translation from a public IP address to a private IP address, configure inbound one-to-one static NAT.
· When the source IP address of an incoming packet matches the global-ip, the source IP address is translated into the local-ip.
· When the destination IP address of an outgoing packet matches the local-ip, the destination IP address is translated into the global-ip.
Procedure
1. Enter system view.
system-view
2. Configure a one-to-one mapping for inbound static NAT.
nat static inbound global-ip local-ip [ acl { ipv4-acl-number | name ipv4-acl-name } [ reversible ] ] [ rule rule-name ] [ priority priority ] [ disable ] [ counting ]
3. Enter interface view.
interface interface-type interface-number
4. Enable static NAT on the interface.
nat static enable
By default, static NAT is disabled.
Configuring inbound net-to-net static NAT
About this task
For address translation from a public network to a private network, configure inbound net-to-net static NAT.
· When the source IP address of an incoming packet matches the public address range, the source IP address is translated into a private address in the private address range.
· When the destination IP address of an outgoing packet matches the private address range, the destination IP address is translated into a public address in the public address range.
Procedure
1. Enter system view.
system-view
2. Configure a net-to-net mapping for inbound static NAT.
nat static inbound net-to-net global-start-address global-end-address local local-network { mask-length | mask } [ acl { ipv4-acl-number | name ipv4-acl-name } [ reversible ] ] [ rule rule-name ] [ priority priority ] [ disable ] [ counting ]
3. Enter interface view.
interface interface-type interface-number
4. Enable static NAT on the interface.
nat static enable
By default, static NAT is disabled.
Configuring dynamic NAT on an interface
Restrictions and guidelines
You can configure multiple inbound or outbound dynamic NAT rules.
· A NAT rule with an ACL takes precedence over a rule without any ACL.
· If two ACL-based dynamic NAT rules are configured, the rule with the higher ACL number has higher priority.
Prerequisites
Before configuring dynamic NAT, you must perform the following tasks:
· Configure an ACL to identify the IP addresses to be translated. For more information about ACLs, see Security Configuration Guide.
· Determine whether to enable the Easy IP feature. If you use the IP address of an interface as the NAT address, you are configuring Easy IP.
· Determine a public IP address pool for address translation.
· Determine whether to translate port numbers. Use NO-PAT to translate only IP addresses and PAT to translate both IP addresses and port numbers.
Configuring outbound dynamic NAT
About this task
To translate private IP addresses into public IP addresses, configure outbound dynamic NAT on the interface connected to the external network.
Procedure
1. Enter system view.
system-view
2. Create a NAT address group and enter its view.
nat address-group group-id
3. Add an address range to the address group.
address start-address end-address [ name group-name ]
You can add multiple address ranges to an address group.
The address ranges must not overlap.
4. Return to system view.
quit
5. Enter interface view.
interface interface-type interface-number
6. Configure outbound dynamic NAT. Choose the options to configure as needed:
¡ Configure NO-PAT.
nat outbound [ ipv4-acl-number | name ipv4-acl-name ] address-group { group-id | name group-name } no-pat [ reversible ] [ rule rule-name ] [ priority priority ] [ disable ] [ description text ] [ counting ]
¡ Configure PAT.
nat outbound [ ipv4-acl-number | name ipv4-acl-name ][ address-group { group-id | name group-name } ] [ port-preserved ] [ rule rule-name ] [ priority priority ] [ disable ] [ description text ] [ counting ]
You can configure multiple outbound dynamic NAT rules on an interface.
|
Parameter |
Description |
|
address-group |
If you do not specify this keyword, the IP address of the interface is used as the NAT address. Easy IP is implemented. |
|
no-pat reversible |
If you specify these keywords, you enable reverse address translation. Reverse address translation uses existing NO-PAT entries to translate the destination address for connections actively initiated from the external network to the internal network. The destination address is translated into the private IP address in the matching NO-PAT entry. |
7. (Optional.) Configure a PAT mapping mode.
a. Return to system view.
quit
b. Configure a PAT mapping mode.
nat mapping-behavior endpoint-independent [ acl { ipv4-acl-number | name ipv4-acl-name } ]
The default mapping mode is Address and Port-Dependent Mapping.
This command takes effect only on outbound dynamic NAT for PAT.
8. (Optional.) Rearrange outbound dynamic NAT rules to adjust their priorities.
nat outbound rule move nat-rule-name1 { after | before } nat-rule-name2
Configuring inbound dynamic NAT
Restrictions and guidelines
Do not configure inbound dynamic NAT alone. Typically, inbound dynamic NAT functions with outbound dynamic NAT, or outbound static NAT to implement bidirectional NAT.
As a best practice, manually create a route because it takes time to automatically add routes.
Procedure
1. Enter system view.
system-view
2. Create a NAT address group and enter its view.
nat address-group group-id
3. Add an address range to the address group.
address start-address end-address [ name group-name ]
You can add multiple address ranges to an address group.
The address ranges in address groups must not overlap.
4. Return to system view.
quit
5. Enter interface view.
interface interface-type interface-number
6. Configure inbound dynamic NAT.
nat inbound { ipv4-acl-number | name ipv4-acl-name } address-group { group-id | name group-name } [ no-pat [ reversible ] [ add-route ] ] [ rule rule-name ] [ priority priority ] [ disable ] [ description text ] [ counting ]
You can configure multiple inbound dynamic NAT rules on an interface.
|
Parameter |
Description |
|
no-pat reversible |
If you specify these keywords, you enable reverse address translation. Reverse address translation uses existing NO-PAT entries to translate the destination address for connections actively initiated from the external network to the internal network. The destination address is translated into the private IP address in the matching NO-PAT entry. |
|
add-route |
This keyword enables the device to automatically add a route destined for the private address when an inbound dynamic NAT rule is matched. The output interface is the NAT interface, and the next hop is the source address before translation. If you do not specify this keyword, you must manually add the route. |
7. (Optional.) Rearrange inbound dynamic NAT rules to adjust their priorities.
nat inbound rule move nat-rule-name1 { after | before } nat-rule-name2
Configuring NAT ALG
About this task
NAT ALG translates address or port information in the application layer payload to ensure connection establishment.
For example, an FTP application includes a data connection and a control connection. The IP address and port number for the data connection depend on the payload information of the control connection. This requires NAT ALG to translate the address and port information to establish the data connection.
Procedure
1. Enter system view
system-view
2. Configure NAT ALG for a protocol or all protocols.
nat alg { all | dns | ftp | icmp-error | ils | mgcp | nbt | pptp | rsh | rtsp | sccp | sqlnet | tftp | xdmcp }
By default, NAT ALG is enabled for DNS, FTP, ICMP error messages, RTSP, and PPTP, and is disabled for the other supported protocols.
Configuring NAT logging
Configuring NAT session logging
About this task
NAT session logging records NAT session information, including translation information and access information.
A NAT device generates NAT session logs for the following events:
· NAT session establishment.
· NAT session removal. This event occurs when you add a configuration with a higher priority, remove a configuration, change ACLs, when a NAT session ages out, or when you manually delete a NAT session.
· Active NAT session logging.
Procedure
1. Enter system view.
system-view
2. Enable NAT logging.
nat log enable [ acl { ipv4-acl-number | name ipv4-acl-name } ]
By default, NAT logging is disabled.
3. Enable NAT session logging.
¡ For NAT session establishment events:
nat log flow-begin
¡ For NAT session removal events:
nat log flow-end
¡ For active NAT flows:
nat log flow-active minutes
By default, NAT session logging is disabled.
Configuring NAT alarm logging
About this task
Packets that need to be translated are dropped if the NAT resources are not enough. In NO-PAT, the NAT resources refer to the public IP addresses. In EIM PAT, the NAT resources refer to public IP addresses and ports. NAT alarm logging monitors the usage of NAT resources and outputs logs if the NAT resources are not enough.
Restrictions and guidelines
The nat log alarm command take effect only after you use the nat log enable command to enable NAT logging.
Prerequisites
Before configuring NAT alarm logging, you must configure the custom NAT log generation and outputting features. For more information, see the information center in System Management Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enable NAT logging.
nat log enable [ acl { ipv4-acl-number | name ipv4-acl-name } ]
By default, NAT logging is disabled.
The acl keyword does not take effect on NAT alarm logging.
3. Enable NAT alarm logging.
nat log alarm
By default, NAT alarm logging is disabled.
An NAT alarm log is output when NAT resources run out.
Enabling sending ICMP error messages for NAT failures
About this task
By default, the device does not send ICMP error messages when NAT fails. Disabling sending ICMP error messages for NAT failures reduces useless packets, saves bandwidth, and avoids exposing the firewall IP address to the public network.
Restrictions and guidelines
Enable this feature for traceroute because the traceroute function requires ICMP error packets.
Procedure
1. Enter system view.
system-view
2. Enable sending ICMP error messages for NAT failures.
nat icmp-error reply
By default, no ICMP error messages are sent for NAT failures.
Display and maintenance commands for NAT
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display the NAT ALG status for all supported protocols |
display nat alg |
|
Display all NAT configuration information. |
display nat all |
|
Display NAT address group information. |
display nat address-group [ group-id ] |
|
Display information about NAT EIM entries. |
display nat eim |
|
Display inbound dynamic NAT configuration. |
display nat inbound |
|
Display NAT logging configuration. |
display nat log |
|
Display information about NAT NO-PAT entries. |
display nat no-pat |
|
Display outbound dynamic NAT configuration. |
display nat outbound |
|
Display NAT sessions. |
display nat session [ [ responder ] { source-ip source-ip | destination-ip destination-ip } * ] [ verbose ] |
|
Display static NAT mappings. |
display nat static |
|
Display NAT statistics. |
display nat statistics [ summary ] |
|
clear NAT counting statistics |
reset nat count statistics { all | dynamic | static } |
|
Clear NAT sessions. |
reset nat session |
NAT configuration examples
Example: Configuring outbound one-to-one static NAT
Network configuration
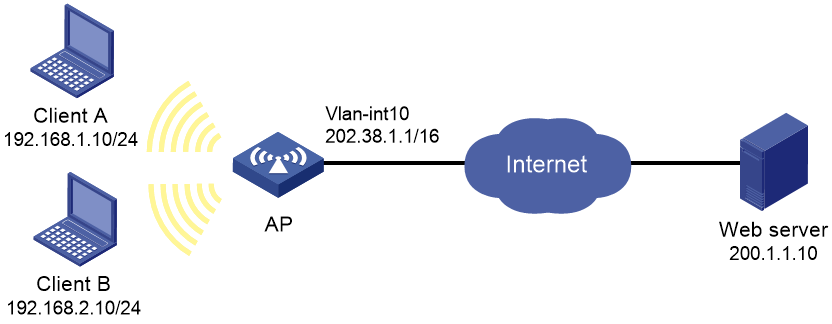
As shown in Figure 3, configure static NAT to allow the client at 192.168.1.10/24 to access the Internet.
Procedure
# Assign IP addresses to interfaces. (Details not shown.)
# Configure a one-to-one static NAT mapping between private address 192.168.1.10 and public address 202.38.1.100.
<AP> system-view
[AP] nat static outbound 192.168.1.10 202.38.1.100
# Enable static NAT on VLAN-interface 10.
[AP] interface vlan-interface 10
[AP-Vlan-interface10] nat static enable
[AP-Vlan-interface10] quit
Verifying the configuration
# Verify that the client at 192.168.1.10 can access the server on the Internet. (Details not shown.)
# Display static NAT configuration.
[AP] display nat static
Static NAT mappings:
Totally 1 outbound static NAT mappings.
IP-to-IP:
Local IP : 192.168.1.10
Global IP : 202.38.1.100
Config status: Active
Interfaces enabled with static NAT:
Totally 1 interfaces enabled with static NAT.
Interface: Vlan-interface2
Config status: Active
# Display NAT session information.
[AP] display nat session verbose
Initiator:
Source IP/port: 192.168.1.10/42496
Destination IP/port: 202.38.1.111/2048
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: ICMP(1)
Inbound interface: Vlan-interface1
Responder:
Source IP/port: 202.38.1.111/42496
Destination IP/port: 202.38.1.100/0
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: ICMP(1)
Inbound interface: Vlan-interface10
State: ICMP_REPLY
Application: INVALID
Rule ID: -/-/-
Rule name:
Start time: 2017-08-16 09:30:49 TTL: 27s
Initiator->Responder: 5 packets 420 bytes
Responder->Initiator: 5 packets 420 bytes
Total sessions found: 1
Example: Configuring outbound dynamic NAT
Network configuration
As shown in Figure 4, a company has a private subnet address 192.168.0.0/16 and two public IP addresses 202.38.1.2 and 202.38.1.3. Configure outbound dynamic NAT to allow only internal users on subnet 192.168.1.0/24 to access the Internet.
Procedure
# Assign IP addresses to interfaces. (Details not shown.)
# Configure address group 0, and add addresses 202.38.1.2 and 202.38.1.3 to the group.
<AP> system-view
[AP] nat address-group 0
[AP-address-group-0] address 202.38.1.2 202.38.1.3
[AP-address-group-0] quit
# Configure ACL 2000, and create a rule to permit packets only from subnet 192.168.1.0/24 to pass through.
[AP] acl basic 2000
[AP-acl-ipv4-basic-2000] rule permit source 192.168.1.0 0.0.0.255
[AP-acl-ipv4-basic-2000] quit
# Enable outbound dynamic PAT on VLAN-interface 10. The source IP addresses of the packets permitted by the ACL rule is translated into the addresses in address group 0.
[AP] interface vlan-interface 10
[AP-Vlan-interface10] nat outbound 2000 address-group 0
[AP-GigabitEthernet1/0/2] quit
Verifying the configuration
# Verify that Client A can access the WWW server, but Client B cannot. (Details not shown.)
# Display all NAT configuration and statistics.
[AP] display nat all
NAT address group information:
Totally 1 NAT address groups.
Address group ID: 0:
Port range: 1-65535
Address information:
Start address End address
202.38.1.2 202.38.1.3
NAT outbound information:
Totally 1 NAT outbound rules.
Interface: Vlan-interface10
ACL: 2000
Address group ID: 0
Port-preserved: N NO-PAT: N Reversible: N
Config status: Active
NAT logging:
Log enable : Disabled
Flow-begin : Disabled
Flow-end : Disabled
Flow-active : Disabled
Port-block-assign : Disabled
Port-block-withdraw : Disabled
Alarm : Disabled
NAT mapping behavior:
Mapping mode : Address and Port-Dependent
ACL : ---
Config status: Active
NAT ALG:
DNS : Enabled
FTP : Enabled
H323 : Enabled
ICMP-ERROR : Enabled
ILS : Enabled
MGCP : Enabled
NBT : Enabled
PPTP : Enabled
RTSP : Enabled
RSH : Enabled
SCCP : Enabled
SIP : Enabled
SQLNET : Enabled
TFTP : Enabled
XDMCP : Enabled
Static NAT load balancing: Disabled
# Display NAT session information generated when Client A accesses the WWW server.
[AP] display nat session verbose
Initiator:
Source IP/port: 192.168.1.10/52992
Destination IP/port: 200.1.1.10/2048
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: ICMP(1)
Inbound interface: Vlan-interface1
Responder:
Source IP/port: 200.1.1.10/4
Destination IP/port: 202.38.1.3/0
DS-Lite tunnel peer: -
VPN instance/VLAN ID/Inline ID: -/-/-
Protocol: ICMP(1)
Inbound interface: Vlan-interface10
State: ICMP_REPLY
Application: INVALID
Rule ID: -/-/-
Rule name:
Start time: 2017-08-15 14:53:29 TTL: 12s
Initiator->Responder: 1 packets 84 bytes
Responder->Initiator: 1 packets 84 bytes
Total sessions found: 1