- Table of Contents
- Related Documents
-
01-Text
Download Book (891.46 KB)Assignment of traffic to VXLANs
Configuring basic VXLAN features
Configuration restrictions and guidelines
Setting the forwarding mode for VXLANs
Configuration restrictions and guidelines
Assigning VXLAN tunnels to a VXLAN
Mapping an Ethernet service instance to a VSI
Enabling local-MAC change logging
Configuring static remote-MAC address entries
Disabling remote-MAC address learning
Enabling software-based MAC learning on an interface
Configuring a multicast-mode VXLAN
Configuring a VTEP using the PIM method
Configuring a VTEP using the IGMP host method
Confining floods to the local site
Confining the flood traffic of an Ethernet service instance
Setting the destination UDP port number of VXLAN packets
Configuring VXLAN packet check
Enabling ARP flood suppression
Disabling remote ARP learning for VXLANs
Enabling VXLAN packet statistics
Enabling packet statistics for a VSI
Enabling packet statistics for an Ethernet service instance
Setting the VXLAN hardware resource allocation mode
Testing the reachability of a remote VM
Displaying and maintaining VXLANs
Unicast-mode VXLAN configuration example
Multicast-mode VXLAN configuration example
VXLAN IP gateways separated from VTEPs
Centralized VXLAN IP gateway deployment
Centralized VXLAN gateway group deployment
Distributed VXLAN IP gateway deployment
Configuration restrictions and guidelines
Configuring a centralized VXLAN IP gateway
Configuring a centralized VXLAN IP gateway group
Configuration restrictions and guidelines
Specifying a VTEP group as the gateway for an access layer VTEP
Configuring a distributed VXLAN IP gateway
Enabling packet statistics for a VSI interface
Displaying and maintaining VXLAN IP gateway
VXLAN IP gateway configuration examples
Centralized VXLAN IP gateway configuration example
Centralized VXLAN IP gateway group configuration example
Distributed VXLAN IPv4 gateway configuration example
Configuring the VTEP as an OVSDB VTEP
OVSDB VTEP configuration task list
Setting up an OVSDB connection to a controller
Configuration restrictions and guidelines
Configuring active TCP connection settings
Configuring passive TCP connection settings
Enabling the OVSDB VTEP service
Specifying a global source address for VXLAN tunnels
Enabling flood proxy on multicast VXLAN tunnels
OVSDB VTEP configuration examples
Unicast-mode VXLAN configuration example
Flood proxy VXLAN configuration example
VXLAN overview
Virtual eXtensible LAN (VXLAN) is a MAC-in-UDP technology that provides Layer 2 connectivity between distant network sites across an IP network. VXLAN is typically used in data centers for multitenant services.
VXLAN provides the following benefits:
· Support for more virtual switched domains than VLANs—Each VXLAN is uniquely identified by a 24-bit VXLAN ID. The total number of VXLANs can reach 16777216 (224). This specification makes VXLAN a better choice than 802.1Q VLAN to isolate traffic for VMs.
· Easy deployment and maintenance—VXLAN requires deployment only on the edge devices of the transport network. Devices in the transport network perform typical Layer 3 forwarding.
The device supports only IPv4-based VXLAN. IPv6-based VXLAN is not supported.
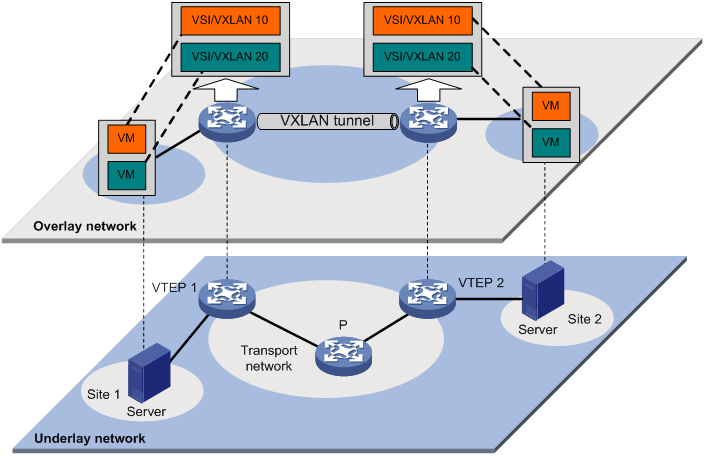
VXLAN network model
As shown in Figure 1, a VXLAN is a virtual Layer 2 network (known as the overlay network) built on top of an existing physical Layer 3 network (known as the underlay network). The overlay network encapsulates inter-site Layer 2 frames into VXLAN packets and forwards the packets to the destination along the Layer 3 forwarding paths provided by the underlay network. The underlay network is transparent to tenants, and geographically dispersed sites of a tenant are merged into a Layer 2 network.
The transport edge devices assign VMs to different VXLANs, and then forward traffic between sites for VMs by using VXLAN tunnels.
The transport edge devices are VXLAN tunnel endpoints (VTEP). They can be servers that host VMs or independent network devices.
An H3C VTEP uses VSIs and VXLAN tunnels to provide VXLAN services.
· VSI—A virtual switch instance is a virtual Layer 2 switched domain. Each VSI provides switching services only for one VXLAN. VSIs learn MAC addresses and forward frames independently of one another. VMs in different sites have Layer 2 connectivity if they are in the same VXLAN.
· VXLAN tunnel—Logical point-to-point tunnels between VTEPs over the transport network. Each VXLAN tunnel can trunk multiple VXLANs.
VTEPs encapsulate VXLAN traffic in the VXLAN, outer UDP, and outer IP headers. The devices in the transport network forward VXLAN traffic only based on the outer IP header.
Figure 1 VXLAN network model
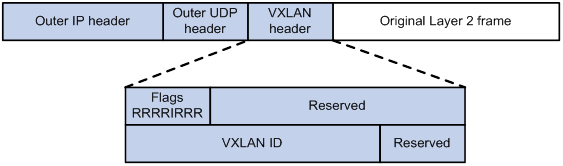
VXLAN packet format
As shown in Figure 2, a VTEP encapsulates a frame in the following headers:
· 8-byte VXLAN header—VXLAN information for the frame.
? Flags—If the I bit is 1, the VXLAN ID is valid. If the I bit is 0, the VXLAN ID is invalid. All other bits are reserved and set to 0.
? 24-bit VXLAN ID—Identifies the VXLAN of the frame. It is also called the virtual network identifier (VNI).
· 8-byte outer UDP header for VXLAN—The default VXLAN destination UDP port number is 4789.
· 20-byte outer IP header—Valid addresses of VTEPs or VXLAN multicast groups on the transport network. Devices in the transport network forward VXLAN packets based on the outer IP header.
Figure 2 VXLAN packet format
Working mechanisms
The VTEP uses the following process to forward an inter-site frame:
1. Assigns the frame to its matching VXLAN if the frame is sent between sites.
2. Performs MAC learning on the VXLAN's VSI.
3. Forwards the frame through VXLAN tunnels.
This section describes this process in detail. For intra-site frames in a VSI, the system performs typical Layer 2 forwarding, and it processes 802.1Q VLAN tags as described in "Access modes of VSIs."
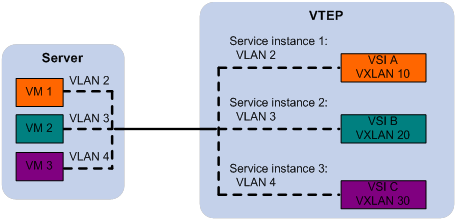
Assignment of traffic to VXLANs
Traffic from the local site to a remote site
The VTEP uses an Ethernet service instance to match a list of VLANs on a site-facing interface. The VTEP assigns customer traffic to a VXLAN by mapping the Ethernet service instance to a VSI. An Ethernet service instance is identical to an attachment circuit (AC) in L2VPN.
As shown in Figure 3, Ethernet service instance 1 matches VLAN 2 and is mapped to VSI A (VXLAN 10). When a frame from VLAN 2 arrives, the VTEP assigns the frame to VXLAN 10, and looks up VSI A's MAC address table for the outgoing interface.
Figure 3 Identifying traffic from the local site
Traffic from a remote site to the local site
When a frame arrives at a VXLAN tunnel, the VTEP uses the VXLAN ID in the frame to identify its VXLAN.
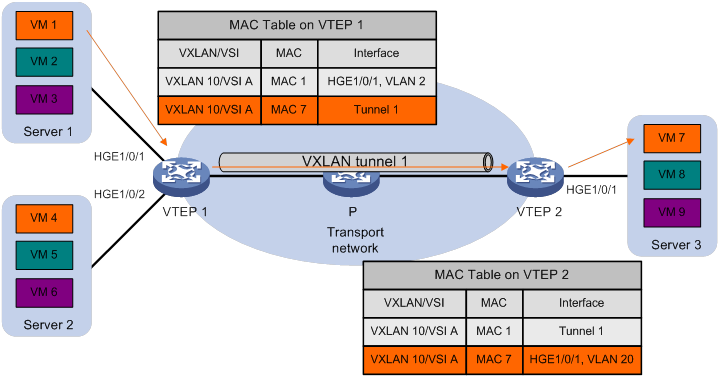
MAC learning
The VTEP performs source MAC learning on the VSI as a Layer 2 switch.
· For traffic from the local site to the remote site, the VTEP learns the source MAC address before VXLAN encapsulation.
· For traffic from the remote site to the local site, the VTEP learns the source MAC address after removing the VXLAN header.
A VSI's MAC address table includes the following types of MAC address entries:
· Local MAC—Dynamic MAC entries learned from the local site. The outgoing interfaces are site-facing interfaces on which the MAC addresses are learned. VXLAN does not support manual local-MAC entries.
· Remote MAC—MAC entries learned from a remote site, including static and dynamic MAC entries. The outgoing interfaces for the MAC addresses are VXLAN tunnel interfaces.
? Static—Manually added MAC entries.
? Dynamic—MAC entries learned in the data plane from incoming traffic on VXLAN tunnels. The learned MAC addresses are contained in the inner Ethernet header.
? OpenFlow—MAC entry issued by a remote controller through OpenFlow.
? OVSDB—MAC entry issued by a remote controller through OVSDB.
For a remote address, the manual static entry has higher priority than the dynamic entry.
Traffic forwarding
A VTEP uses the following processes to forward traffic at Layer 2:
· Unicast process—Applies to destination-known unicast traffic.
· Flood process—Applies to multicast, broadcast, and unknown unicast traffic.
When the VTEP forwards VXLAN traffic, it processes the 802.1Q tag in the inner Ethernet header depending on the VSI access mode (VLAN or Ethernet mode). In VLAN access mode, sites can use different VLANs to provide the same service. For more information, see "Access modes of VSIs."
Unicast
The following process (see Figure 4) applies to a known unicast frame between sites:
1. The source VTEP encapsulates the Ethernet frame in the VXLAN/UDP/IP header.
In the outer IP header, the source IP address is the source VTEP's VXLAN tunnel source IP address. The destination IP address is the VXLAN tunnel destination IP address.
2. The source VTEP forwards the encapsulated packet out of the outgoing VXLAN tunnel interface found in the VSI's MAC address table.
3. The intermediate transport devices (P devices) forward the frame to the destination VTEP by using the outer IP header.
4. The destination VTEP removes the headers on top of the inner Ethernet frame. It then performs MAC address table lookup in the VXLAN's VSI to forward the frame out of the matching outgoing interface.
Flood
The VTEP floods a broadcast, multicast, or unknown unicast frame to all site-facing interfaces and VXLAN tunnels in the VXLAN, except for the incoming interface.
VXLAN supports the following modes for flood traffic:
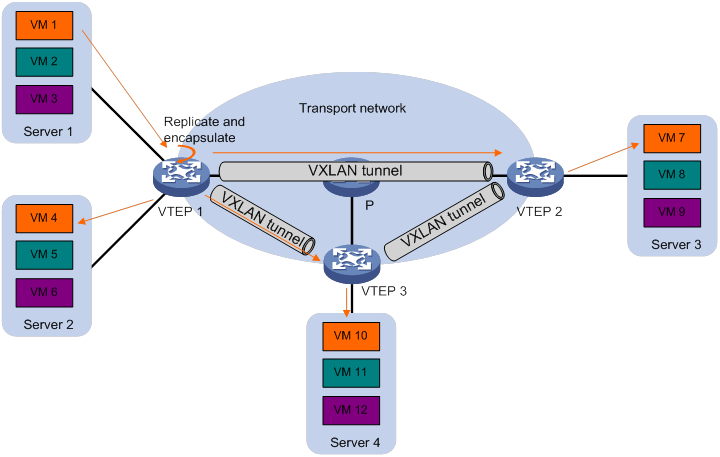
· Unicast mode—Also called head-end replication. The source VTEP replicates the flood frame, and then sends one replica to the destination IP address of each VXLAN tunnel in the VXLAN. See Figure 5.
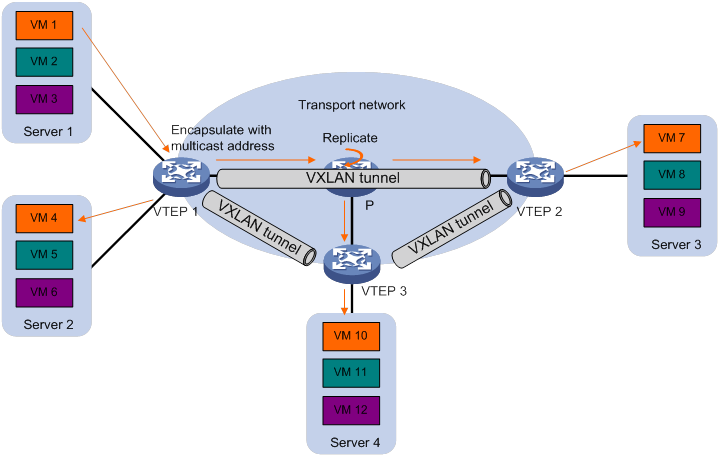
· Multicast mode—Also called tandem replication. The source VTEP sends the flood frame in a multicast VXLAN packet destined for a multicast group address. Transport network devices replicate and forward the packet to remote VTEPs based on their multicast forwarding entries. See Figure 6.
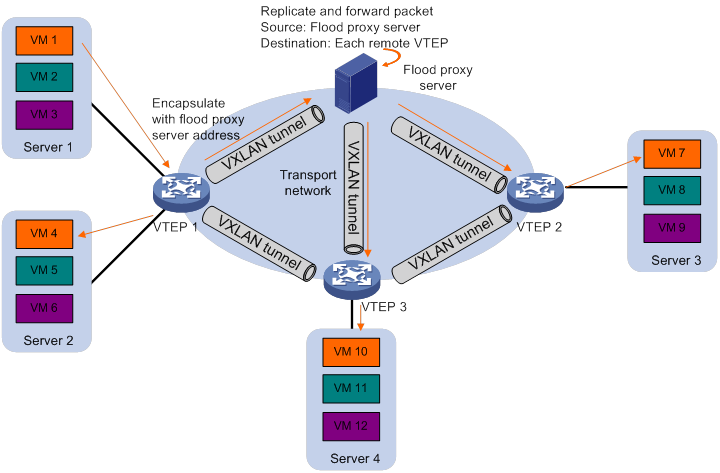
· Flood proxy mode—The source VTEP sends the flood frame in a VXLAN packet over a VXLAN tunnel to a flood proxy server. The flood proxy server replicates and forwards the packet to each remote VTEP through its VXLAN tunnels. See Figure 7.
The flood proxy mode applies to VXLANs that have many sites. This mode reduces flood traffic in the transport network without using a multicast protocol. To use a flood proxy server, you must set up a VXLAN tunnel to the server on each VTEP.
|
|
NOTE: The flood proxy mode is typically used in SDN transport networks that have a flood proxy server. For VTEPs to forward packets based on the MAC address table issued by an SDN controller, you must perform the following tasks on the VTEPs: · Disable remote-MAC address learning by using the vxlan tunnel mac-learning disable command. · Disable source MAC check on all transport-facing interfaces by using the undo mac-address static source-check enable command. If the VTEP is an IRF fabric, you must also disable the feature on all IRF ports. |
Each destination VTEP floods the inner Ethernet frame to all the site-facing interfaces in the VXLAN. To avoid loops, the destination VTEPs do not flood the frame to VXLAN tunnels.
Access modes of VSIs
The access mode of a VSI determines how the VTEP processes the 802.1Q VLAN tags in the Ethernet frames.
· VLAN access mode—Ethernet frames received from or sent to the local site must contain 802.1Q VLAN tags.
? For an Ethernet frame received from the local site, the VTEP removes all its 802.1Q VLAN tags before forwarding the frame.
? For an Ethernet frame destined for the local site, the VTEP adds 802.1Q VLAN tags to the frame before forwarding the frame.
In VLAN access mode, VXLAN packets sent between sites do not contain 802.1Q VLAN tags. You can use different 802.1Q VLANs to provide the same service in different sites.
· Ethernet access mode—The VTEP does not process the 802.1Q VLAN tags of Ethernet frames received from or sent to the local site.
? For an Ethernet frame received from the local site, the VTEP forwards the frame with the 802.1Q VLAN tags intact.
? For an Ethernet frame destined for the local site, the VTEP forwards the frame without adding 802.1Q VLAN tags.
In Ethernet access mode, VXLAN packets sent between VXLAN sites contain 802.1Q VLAN tags. You must use the same VLAN to provide the same service between sites.
ARP flood suppression
ARP flood suppression reduces ARP request broadcasts by enabling the VTEP to reply to ARP requests on behalf of VMs.
As shown in Figure 8, this feature snoops ARP packets to populate the ARP flood suppression table with local and remote MAC addresses. If an ARP request has a matching entry, the VTEP replies to the request on behalf of the VM. If no match is found, the VTEP floods the request to both local and remote sites.
Figure 8 ARP flood suppression
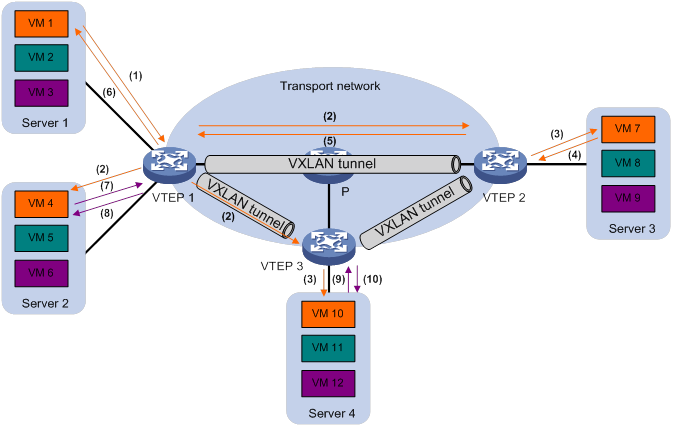
ARP flood suppression uses the following workflow:
1. VM 1 sends an ARP request to obtain the MAC address of VM 7.
2. VTEP 1 creates a suppression entry for VM 1, and floods the ARP request in the VXLAN.
3. VTEP 2 and VTEP 3 de-encapsulate the ARP request. The VTEPs create a suppression entry for VM 1, and broadcast the request in the local site.
4. VM 7 sends an ARP reply.
5. VTEP 2 creates a suppression entry for VM 7 and forwards the ARP reply to VTEP 1.
6. VTEP 1 de-encapsulates the ARP reply, creates a suppression entry for VM 7, and forwards the ARP reply to VM 1.
7. VM 4 sends an ARP request to obtain the MAC address of VM 1 or VM 7.
8. VTEP 1 creates a suppression entry for VM 4 and replies to the ARP request.
9. VM 10 sends an ARP request to obtain the MAC address of VM 1.
10. VTEP 3 creates a suppression entry for VM 10 and replies to the ARP request.
VXLAN IP gateways
A VXLAN IP gateway provides Layer 3 forwarding services for VMs in VXLANs. A VXLAN IP gateway can be an independent device or be collocated with a VTEP. For more information about VXLAN IP gateway placement, see "Configuring VXLAN IP gateways."
Protocols and standards
RFC 7348, Virtual eXtensible Local Area Network (VXLAN): A Framework for Overlaying Virtualized Layer 2 Networks over Layer 3 Networks
Configuring basic VXLAN features
Configuration restrictions and guidelines
Before you can configure VXLANs, you must perform the following tasks:
1. Set the system operating mode to standard or advanced by using the system-working-mode command in system view.
2. Save the configuration.
3. Reboot the device.
For more information about setting the system operating mode, see device management in Fundamentals Configuration Guide.
VXLAN configuration task list
|
Tasks at a glance |
Remarks |
|
(Required.) Setting the forwarding mode for VXLANs |
N/A |
|
(Required.) Creating a VXLAN on a VSI |
N/A |
|
(Required.) Configuring a VXLAN tunnel |
N/A |
|
(Required.) Assigning VXLAN tunnels to a VXLAN |
To extend a VXLAN to remote sites, you must assign VXLAN tunnels to the VXLAN. |
|
(Required.) Mapping an Ethernet service instance to a VSI |
Perform this task to assign customer traffic to VXLANs. |
|
(Optional.) Managing MAC address entries |
N/A |
|
(Optional.) Configuring a multicast-mode VXLAN |
By default, the VTEP floods VXLAN traffic in unicast mode. If the network is multicast dense, configure the VTEP to flood VXLAN traffic in multicast mode. |
|
(Optional.) Confining floods to the local site |
N/A |
|
(Optional.) Confining the flood traffic of an Ethernet service instance |
Perform this task to prevent broadcast storms within a VSI. |
|
(Optional.) Setting the destination UDP port number of VXLAN packets |
N/A |
|
(Optional.) Configuring VXLAN packet check |
Perform this task to check incoming VXLAN packets, including the following items: · UDP checksum. · 802.1Q VLAN tags in the inner Ethernet header. |
|
(Optional.) Enabling ARP flood suppression |
N/A |
|
(Optional.) Disabling remote ARP learning for VXLANs |
N/A |
|
(Optional.) Enabling VXLAN packet statistics |
N/A |
|
(Optional.) Setting the VXLAN hardware resource allocation mode |
N/A |
|
(Optional.) Testing the reachability of a remote VM |
N/A |
Setting the forwarding mode for VXLANs
Enable Layer 3 forwarding mode if you want to use the device as a VXLAN IP gateway. Enable Layer 2 or Layer 3 forwarding mode if you want to use the device as a VTEP. For more information about VXLAN IP gateways, see "Configuring VXLAN IP gateways."
Configuration restrictions and guidelines
When you set the VXLAN forwarding mode, follow these restrictions and guidelines:
· If you enable Layer 3 forwarding for VXLANs, the tagging status of VXLAN packets is not determined by the link type of the outgoing interface. You must set the tagging mode of VXLAN packets.
? Set the tagging mode to untagged if the following requirements are met:
- The link type of the outgoing interface is access, trunk, or hybrid.
- VXLAN packets are transmitted to the next hop through the PVID of the outgoing interface.
? Set the tagging mode to tagged if the following requirements are met:
- The link type of the outgoing interface is trunk or hybrid.
- VXLAN packets are transmitted to the next hop through a VLAN other than the PVID of the outgoing interface.
· You must delete all VSIs, VSI interfaces, and VXLAN tunnel interfaces before you can change the forwarding mode.
· You must delete all VXLAN tunnel interfaces before you can change the tagging mode of VXLAN packets.
Configuration procedure
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable Layer 2 or Layer 3 forwarding for VXLANs. |
·
Enable Layer 2 forwarding: ·
Enable Layer 3 forwarding: |
By default, Layer 3 forwarding is enabled for VXLANs. If you do not set the tagging mode, the untagged mode is used. |
Creating a VXLAN on a VSI
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable L2VPN. |
l2vpn enable |
By default, L2VPN is disabled. |
|
3. Create a VSI and enter VSI view. |
vsi vsi-name |
By default, no VSIs exist. |
|
4. (Optional.) Configure a VSI description. |
description text |
By default, a VSI does not have a description. |
|
5. Enable the VSI. |
undo shutdown |
By default, a VSI is enabled. |
|
6. Create a VXLAN and enter VXLAN view. |
vxlan vxlan-id |
By default, no VXLANs exist. You can create only one VXLAN on a VSI. The VXLAN ID must be unique for each VSI. |
Configuring a VXLAN tunnel
This task provides basic VXLAN tunnel configuration. For more information about tunnel configuration and commands, see Layer 3—IP Services Configuration Guide and Layer 3—IP Services Command Reference.
To ensure correct traffic forwarding, do not use an interface as both a traffic outgoing interface of VXLAN tunnels and site-facing interface configured with ACs.
Make sure the following VXLAN tunnels are not associated with the same VXLAN when they have the same tunnel destination IP address:
· A VXLAN tunnel automatically created by EVPN.
· A manually created VXLAN tunnel.
For more information about EVPN, see EVPN Configuration Guide.
To configure a VXLAN tunnel:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Specify a global source address for VXLAN tunnels. |
tunnel global source-address ip-address |
By default, no global source address is specified for VXLAN tunnels. A VXLAN tunnel uses the global source address if you do not specify a source interface or source address for the tunnel. |
|
3. Create a VXLAN tunnel interface and enter tunnel interface view. |
interface tunnel tunnel-number mode vxlan |
By default, no tunnel interfaces exist. The endpoints of a tunnel must use the same tunnel mode. ECMP is supported by the first 2048 manually created VXLAN tunnels. |
|
4. Specify a source IP address or source interface for the tunnel. |
source { ipv4-address | interface-type interface-number } |
Do not perform this step if you are using OVSDB for VXLAN tunnel management. By default, no source IP address or source interface is specified for a tunnel. This step specifies the source IP address in the outer IP header of tunneled VXLAN packets. If an interface is specified, its primary IP address is used. For a multicast-mode VXLAN, the source IP address cannot be a loopback interface's address, and the source interface cannot be a loopback interface. |
|
5. Specify a destination IP address for the tunnel. |
destination ipv4-address |
By default, no destination IP address is specified for a tunnel. Specify the remote VTEP's IP address. This IP address will be the destination IP address in the outer IP header of tunneled VXLAN packets. As a best practice, do not configure multiple VXLAN tunnels to use the same source and destination IP addresses. |
|
6. (Optional.) Enable BFD on the tunnel. |
tunnel bfd enable destination-mac mac-address |
By default, BFD is disabled on a tunnel. For BFD sessions to come up, you must reserve a VXLAN by using the reserved vxlan command. |
|
7. (Optional.) Return to system view. |
quit |
N/A |
|
8. (Optional.) Specify the reserved VXLAN. |
reserved vxlan vxlan-id |
By default, no VXLAN has been reserved. You can specify only one reserved VXLAN on the VTEP. The reserved VXLAN cannot be the VXLAN created on any VSI. |
Assigning VXLAN tunnels to a VXLAN
To provide Layer 2 connectivity for a VXLAN between two sites, you must assign the VXLAN tunnel between the sites to the VXLAN.
You can assign multiple VXLAN tunnels to a VXLAN, and configure a VXLAN tunnel to trunk multiple VXLANs. For a unicast-mode VXLAN, the system floods unknown unicast, multicast, and broadcast traffic to each tunnel associated with the VXLAN. If a flood proxy server is used, the VTEP sends flood traffic to the server through the flood proxy tunnel. The flood proxy server replicates and forwards flood traffic to remote VTEPs.
To assign VXLAN tunnels to a VXLAN:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VSI view. |
vsi vsi-name |
N/A |
|
3. Enter VXLAN view. |
vxlan vxlan-id |
N/A |
|
4. Assign VXLAN tunnels to the VXLAN. |
tunnel { tunnel-number [ flooding-proxy ] | all } |
By default, a VXLAN does not contain any VXLAN tunnels. For full Layer 2 connectivity in the VXLAN, make sure the VXLAN contains the VXLAN tunnel between each pair of sites in the VXLAN. Enable flood proxy on the tunnel for the VTEP to send flood traffic to the flood proxy server. The flood proxy server replicates and forwards flood traffic to remote VTEPs. |
Mapping an Ethernet service instance to a VSI
An Ethernet service instance matches a list of VLANs on a site-facing interface. The VTEP assigns customer traffic from the VLANs to a VXLAN by mapping the Ethernet service instance to a VSI.
An Ethernet service instance can contain only one match criterion. To change the match criterion, you must remove the original criterion first. When you remove the match criterion in an Ethernet service instance, the mapping between the service instance and the VSI is removed automatically.
If an Ethernet service instance contains the encapsulation default match criterion, traffic is matched as follows:
· The service instance matches any frames if it is the only instance on the interface.
· The service instance matches frames that do not match any other service instance if multiple instances exist on the interface.
To map an Ethernet service instance to a VSI:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter Layer 2 Ethernet interface view or Layer 2 aggregate interface view. |
· interface interface-type interface-number · interface bridge-aggregation interface-number |
N/A |
|
3. Create an Ethernet service instance and enter Ethernet service instance view. |
service-instance instance-id |
By default, no Ethernet service instances exist. |
|
4. Configure a frame match criterion. |
·
Match frames that do not match any other
service instance on the interface: ·
Match untagged frames: ·
Match frames tagged with the specified outer
802.1Q VLAN IDs: ·
Match frames tagged with the specified outer
and inner 802.1Q VLAN IDs: |
By default, an Ethernet service instance does not contain a frame match criterion. You can specify multiple SVLAN IDs or CVLAN IDs only in Ethernet access mode. |
|
5. (Optional.) Configure the VLAN tag processing rule for incoming traffic. |
rewrite inbound tag { nest { c-vid vlan-id | s-vid vlan-id [ c-vid vlan-id ] } | remark { { 1-to-1 | 2-to-1 } { c-vid vlan-id | s-vid vlan-id } | { 1-to-2 | 2-to-2 } s-vid vlan-id c-vid vlan-id } | strip { c-vid | s-vid [ c-vid ] } } [ symmetric ] |
By default, VLAN tags of incoming traffic are not processed. |
|
6. (Optional.) Configure the VLAN tag processing rule for outgoing traffic. |
rewrite outbound tag { nest { c-vid vlan-id | s-vid vlan-id [ c-vid vlan-id ] } | remark { { 1-to-1 | 2-to-1 } { c-vid vlan-id | s-vid vlan-id } | { 1-to-2 | 2-to-2 } s-vid vlan-id c-vid vlan-id } | strip { c-vid | s-vid [ c-vid ] } } |
By default, VLAN tags of outgoing traffic are not processed. |
|
7. Map the Ethernet service instance to a VSI. |
xconnect vsi vsi-name [ access-mode { ethernet | vlan } ] [ track track-entry-number&<1-3> ] |
By default, an Ethernet service instance is not mapped to any VSI. |
Managing MAC address entries
With VXLAN, local MAC addresses are learned dynamically. You can log MAC changes, but you cannot manually add local MAC addresses.
Remote-MAC address entries include the following types:
· Manually created static entries.
· Dynamic entries learned in the data plane.
· Entries issued by a remote controller through OpenFlow or OVSDB.
Enabling local-MAC change logging
Local-MAC change logging enables the VXLAN module to send a log message to the information center when a local MAC address is added or removed.
With the information center, you can set log message filtering and output rules, including output destinations. For more information about configuring the information center, see Network Management and Monitoring Configuration Guide.
To enable local-MAC change logging:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable local-MAC change logging. |
vxlan local-mac report |
By default, local-MAC change logging is disabled. |
Configuring static remote-MAC address entries
Do not configure static remote-MAC entries for VXLAN tunnels that are automatically established by using EVPN.
· EVPN re-establishes VXLAN tunnels if the transport-facing interface goes down and then comes up. If you have configured static remote-MAC entries, the entries are deleted when the tunnels are re-established.
· EVPN re-establishes VXLAN tunnels if you perform configuration rollback. If the tunnel IDs change during tunnel re-establishment, configuration rollback fails, and static remote-MAC entries on the tunnels cannot be restored.
For more information about EVPN, see EVPN Configuration Guide.
To configure a static remote-MAC address entry:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Add a static remote-MAC address entry. |
mac-address static mac-address interface tunnel tunnel-number vsi vsi-name |
By default, VXLAN VSIs do not have static remote-MAC address entries. For the setting to take effect, make sure the VSI's VXLAN has been created and specified on the VXLAN tunnel. |
Disabling remote-MAC address learning
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Disable remote-MAC address learning. |
vxlan tunnel mac-learning disable |
By default, remote-MAC address learning is enabled. When network attacks occur, disable remote-MAC address learning to prevent the device from learning incorrect remote MAC addresses. You can manually add static remote-MAC address entries. |
Enabling software-based MAC learning on an interface
This feature is applicable to SDN networks.
To reduce broadcast traffic in an SDN network, the controller synchronizes the MAC addresses that each VTEP learns among all VTEPs. On a VTEP, an interface can learn MAC addresses in hardware or software.
· In hardware-based learning mode, the software periodically obtains new MAC addresses from the hardware and advertises the MAC addresses to the controller.
· In software-based learning mode, the software instantly issues new MAC addresses to the hardware and the controller as soon as they are learned.
Software-based MAC learning shortens the interval at which the VTEP advertises MAC address reachability information to the controller. However, this mode is resource intensive. When you use this mode, you must fully understand its impact on the device performance.
Software-based MAC learning consumes more resources than the hardware learning method. As a best practice to ensure device performance, do not enable software-based MAC learning if MAC addresses change frequently in the network.
To enable software-based MAC learning on the interface:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter Layer 2 Ethernet interface view or Layer 2 aggregate interface view. |
· interface interface-type interface-number · interface bridge-aggregation interface-number |
N/A |
|
3. Enable software-based MAC learning on the interface. |
l2vpn mac-address software-learning enable |
By default, hardware-based MAC learning is used. |
Configuring a multicast-mode VXLAN
A multicast-mode VXLAN supports the following multicast methods:
· PIM—VTEPs and transport network devices run PIM to generate multicast forwarding entries. On a VTEP, you can use the IP address of a loopback interface as the source IP address for multicast VXLAN packets. If the VTEP has multiple transport-facing interfaces, PIM dynamically selects the outgoing interfaces for multicast VXLAN packets.
· IGMP host—VTEPs and transport network devices run PIM and IGMP to generate multicast forwarding entries.
? Transport-facing interfaces of VTEPs act as IGMP hosts.
? Transport network devices connected to a VTEP run IGMP.
? All transport network devices run PIM.
On a VTEP, you must use the IP address of the transport-facing interface as the source IP address for multicast VXLAN packets. If the VTEP has multiple transport-facing interfaces, multicast VXLAN packets are sent to the transport network through the interface that provides the source IP address for multicast VXLAN packets.
VTEPs in a multicast-mode VXLAN can use different multicast methods.
For a multicast-mode VXLAN to flood traffic, you must perform the following tasks in addition to multicast-mode configuration:
· Enable IP multicast routing on all VTEPs and transport network devices.
· Configure a multicast routing protocol on transport network devices. A VTEP can be both a multicast source and multicast group member. As a best practice, use BIDIR-PIM.
· Enable IGMP on transport network devices that are connected to an IGMP host-enabled VTEP.
Configuring a VTEP using the PIM method
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VSI view. |
vsi vsi-name |
N/A |
|
3. Enter VXLAN view. |
vxlan vxlan-id |
N/A |
|
4. Assign a multicast group address for flood traffic, and specify a source IP address for multicast VXLAN packets. |
group group-address source source-address |
By default, a VXLAN uses unicast mode for flood traffic. No multicast group address or source IP address is specified for multicast VXLAN packets. You must assign all VTEPs in a multicast-mode VXLAN to the same multicast group. You can specify the IP address of a loopback interface as the source IP address for multicast VXLAN packets. For multicast traffic to be forwarded correctly, you must use the source IP address of an up VXLAN tunnel as the source IP address for multicast VXLAN packets. |
|
5. Enter the view of the transport-facing interface. |
interface interface-type interface-number |
N/A |
|
6. Enable PIM. |
·
Enable PIM-SM ·
Enable PIM-DM |
By default, PIM is disabled on an interface. |
Configuring a VTEP using the IGMP host method
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VSI view. |
vsi vsi-name |
N/A |
|
3. Enter VXLAN view. |
vxlan vxlan-id |
N/A |
|
4. Assign a multicast group address for flood traffic, and specify a source IP address for multicast VXLAN packets. |
group group-address source source-address |
By default, a VXLAN uses unicast mode for flood traffic. No multicast group address or source IP address is specified for multicast VXLAN packets. You must assign all VTEPs in a multicast-mode VXLAN to the same multicast group. |
|
5. Enter the view of the transport-facing interface. |
interface interface-type interface-number |
N/A |
|
6. Enable the IGMP host feature. |
igmp host enable |
By default, the IGMP host feature is disabled on an interface. The IGMP host feature enables the interface to send IGMP reports in response to IGMP queries before it can receive traffic from the multicast group. The igmp host enable command takes effect after you execute the multicast routing command. |
Confining floods to the local site
By default, the VTEP floods broadcast, unknown unicast, and unknown multicast frames received from the local site to the following interfaces in the frame's VXLAN:
· All site-facing interfaces except for the incoming interface.
· All VXLAN tunnel interfaces.
To confine a kind of flood traffic to the site-facing interfaces, disable flooding for that kind of flood traffic on the VSI bound to the VXLAN. The VSI will not flood the corresponding frames to VXLAN tunnel interfaces.
To confine floods to site-facing interfaces for a VXLAN:
|
Step |
Command |
Remarks |
|
|
1. Enter system view. |
system-view |
N/A |
|
|
2. Enter VSI view. |
vsi vsi-name |
N/A |
|
|
3. Disable flooding for the VSI. |
flooding disable { all | { broadcast | unknown-multicast | unknown-unicast } * } |
By default, flooding is enabled for a VSI. The unknown-multicast or unknown-unicast keyword cannot be used alone. You must specify both of them. |
|
|
4. (Optional.) Enable selective flood for a MAC address. |
selective-flooding mac-address mac-address |
By default, selective flood is disabled. Use this feature to exclude a remote unicast or multicast MAC address from the flood suppression done by using the flooding disable command. The VTEP will flood the frames destined for the specified MAC address to remote sites when floods are confined to the local site. |
|
Confining the flood traffic of an Ethernet service instance
By default, an Ethernet service instance sends flood traffic to the other Ethernet service instances of the same VSI. To prevent broadcast storms, you can confine the flood traffic of Ethernet service instances.
You can use one of the following modes for confining flood traffic:
· all-port—Disables an Ethernet service instance from flooding traffic to all the other Ethernet service instances of the same VSI.
· source-port—Disables an Ethernet service instance from flooding traffic to the other Ethernet service instances of the same VSI on the local port.
To confine the flood traffic of an Ethernet service instance:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter Layer 2 Ethernet interface view or Layer 2 aggregate interface view. |
· interface interface-type interface-number · interface bridge-aggregation interface-number |
N/A |
|
3. Enter Ethernet service instance view. |
service-instance instance-id |
N/A |
|
4. Confine the flood traffic of the Ethernet service instance. |
flooding disable { all-port | source-port } |
By default, an Ethernet service instance sends flood traffic to the other Ethernet service instances of the same VSI. |
Setting the destination UDP port number of VXLAN packets
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Set a destination UDP port for VXLAN packets. |
vxlan udp-port port-number |
By default, the destination UDP port number is 4789 for VXLAN packets. You must configure the same destination UDP port number on all VTEPs in a VXLAN. |
Configuring VXLAN packet check
The device can check the UDP checksum and 802.1Q VLAN tags of each received VXLAN packet.
· UDP checksum check—The device always sets the UDP checksum of VXLAN packets to zero. For compatibility with third-party devices, a VXLAN packet can pass the check if its UDP checksum is zero or correct. If its UDP checksum is incorrect, the VXLAN packet fails the check and is dropped.
· VLAN tag check—The device checks the inner Ethernet header of each VXLAN packet for 802.1Q VLAN tags. If the header contains 802.1Q VLAN tags, the device drops the packet.
If a remote VTEP uses the Ethernet access mode, its VXLAN packets might contain 802.1Q VLAN tags. To prevent the local VTEP from dropping the VXLAN packets, do not execute the vxlan invalid-vlan-tag discard command on the local VTEP.
The access mode is configurable by using the xconnect vsi command.
To configure VXLAN packet check:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable the VTEP to drop VXLAN packets that fail UDP checksum check. |
vxlan invalid-udp-checksum discard |
By default, the VTEP does not check the UDP checksum of VXLAN packets. |
|
3. Enable the VTEP to drop VXLAN packets that have 802.1Q VLAN tags in the inner Ethernet header. |
vxlan invalid-vlan-tag discard |
By default, the VTEP does not check the inner Ethernet header for 802.1Q VLAN tags. |
Enabling ARP flood suppression
Use ARP flood suppression to reduce ARP request broadcasts.
The aging timer is fixed at 25 minutes for ARP flood suppression entries. If the suppression table is full, the VTEP stops learning new entries. For the VTEP to learn new entries, you must wait for old entries to age out, or use the reset arp suppression vsi command to clear the table.
If the flooding disable command is configured, set the MAC aging timer to a higher value than the aging timer for ARP flood suppression entries on all VTEPs. This setting prevents the traffic blackhole that occurs when a MAC address entry ages out before its ARP flood suppression entry ages out. To set the MAC aging timer, use the mac-address timer command.
When remote ARP learning is disabled for VXLANs, the device does not use ARP flood suppression entries to respond to ARP requests received on VXLAN tunnels.
To enable ARP flood suppression:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VSI view. |
vsi vsi-name |
N/A |
|
3. Enable ARP flood suppression. |
arp suppression enable |
By default, ARP flood suppression is disabled. |
Disabling remote ARP learning for VXLANs
By default, the device learns ARP information of remote VMs from packets received on VXLAN tunnel interfaces. To save resources on VTEPs in an SDN transport network, you can temporarily disable remote ARP learning when the controller and VTEPs are synchronizing entries. After the entry synchronization is completed, use the undo vxlan tunnel arp-learning disable command to enable remote ARP learning.
As a best practice, disable remote ARP learning for VXLANs only when the controller and VTEPs are synchronizing entries.
To disable remote ARP learning for VXLANs:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Disable remote ARP learning for VXLANs. |
vxlan tunnel arp-learning disable |
By default, remote ARP learning is enabled for VXLANs. |
Enabling VXLAN packet statistics
You can collect packet statistics for a VXLAN VSI or AC.
Enabling packet statistics for a VSI
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Set the packet statistic collection mode to VSI. |
statistic mode vsi |
The default packet statistic collection mode is VSI. You can use the statistic mode ac, statistic mode queue, or statistic mode vsi command to set the packet statistic collection mode. If you execute the statistic mode command multiple times, the most recent configuration takes effect. |
|
3. Enter VSI view. |
vsi vsi-name |
N/A |
|
4. Enable packet statistics for the VSI. |
statistics enable |
By default, the packet statistics feature is disabled for all VSIs. |
|
5. (Optional.) Display packet statistics for VSIs. |
display l2vpn vsi verbose |
This command is available in any view. |
Enabling packet statistics for an Ethernet service instance
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Set the packet statistic collection mode to AC. |
statistic mode ac |
The default packet statistic collection mode is VSI. You can use the statistic mode ac, statistic mode queue, or statistic mode vsi command to set the packet statistic collection mode. If you execute the statistic mode command multiple times, the most recent configuration takes effect. For more information about the statistic mode queue command, see QoS commands in ACL and QoS Command Reference. |
|
3. Enter interface view. |
·
Enter Layer 2 Ethernet interface view: ·
Enter Layer 2 aggregate interface view: |
N/A |
|
4. Enter Ethernet service instance view. |
service-instance instance-id |
N/A |
|
5. Enable packet statistics for the Ethernet service instance. |
statistics enable |
By default, the packet statistics feature is disabled for all Ethernet service instances. For the statistics enable command to take effect, you must configure a frame match criterion for the Ethernet service instance and map it to a VSI. If you modify the frame match criterion or VSI mapping, packet statistics of the instance is cleared. |
|
6. (Optional.) Display packet statistics for Ethernet service instances. |
display l2vpn service-instance [ interface interface-type interface-number [ service-instance instance-id ] ] [ verbose ] |
This command is available in any view. |
Setting the VXLAN hardware resource allocation mode
The creation of VXLAN tunnels and MAC address entries requires hardware resources. The hardware resources on the device are limited. You can use this command to set the hardware resource allocation mode for VXLANs.
· MAC address mode—Assigns more hardware resources to MAC address entries.
· Normal mode—Assigns more hardware resources to VXLAN tunnels. In this mode, a VXLAN tunnel interface can be the outgoing interface of a network route.
To set the VXLAN hardware resource allocation mode:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Set the VXLAN hardware resource allocation mode. |
hardware-resource vxlan { mac | normal } |
By default, the VXLAN hardware resource allocation mode is normal. |
Testing the reachability of a remote VM
This feature enables the device to test the reachability of a remote VM by simulating a local VM to send ICMP echo requests. The requests are encapsulated in Layer 2 data frames and then sent to the remote VM in the specified VXLAN. The device determines the reachability of the remote VM based on the response time and number of received ICMP echo replies.
To test the reachability of a remote VM:
|
Task |
Command |
Remarks |
|
Test the reachability of a remote VM. |
emulate-ping vxlan [ -c count | -m interval | -s packet-size | -t time-out ] * vxlan-id vxlan-id source-mac mac-address destination-mac mac-address |
Execute this command in any view. |
Displaying and maintaining VXLANs
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
(In standalone mode.) Display ARP flood suppression entries on VSIs. |
display arp suppression vsi [ name vsi-name ] [ slot slot-number ] [ count ] |
|
(In IRF mode.) Display ARP flood suppression entries on VSIs. |
display arp suppression vsi [ name vsi-name ] [ chassis chassis-number slot slot-number ] [ count ] |
|
Display MAC address entries for VSIs. |
display l2vpn mac-address [ vsi vsi-name ] [ dynamic ] [ count ] |
|
Display information about Ethernet service instances. |
display l2vpn service-instance [ interface interface-type interface-number [ service-instance instance-id ] ] [ verbose ] |
|
Display information about VSIs. |
display l2vpn vsi [ name vsi-name ] [ verbose ] |
|
Display information about the multicast groups that contain IGMP host-enabled interfaces. |
display igmp host group [ group-address | interface interface-type interface-number ] [ verbose ] |
|
Display information about tunnel interfaces. |
display interface [ tunnel [ number ] ] [ brief [ description | down ] ] |
|
Display the VXLAN hardware resource allocation mode. |
display hardware-resource [ vxlan ] |
|
Display the current packet statistic collection mode. |
display statistic mode |
|
Display VXLAN tunnel information for VXLANs. |
display vxlan tunnel [ vxlan vxlan-id ] |
|
Clear ARP flood suppression entries on VSIs. |
reset arp suppression vsi [ name vsi-name ] |
|
Clear dynamic MAC address entries on VSIs. |
reset l2vpn mac-address [ vsi vsi-name ] |
|
Clear packet statistics on VSIs. |
reset l2vpn statistics vsi [ name vsi-name ] |
|
Clear packet statistics on ACs. |
reset l2vpn statistics ac [ interface interface-type interface-number service-instance instance-id ] |
|
|
NOTE: For more information about the display interface tunnel command, see tunneling commands in Layer 3—IP Services Command Reference. |
VXLAN configuration examples
Unicast-mode VXLAN configuration example
Network requirements
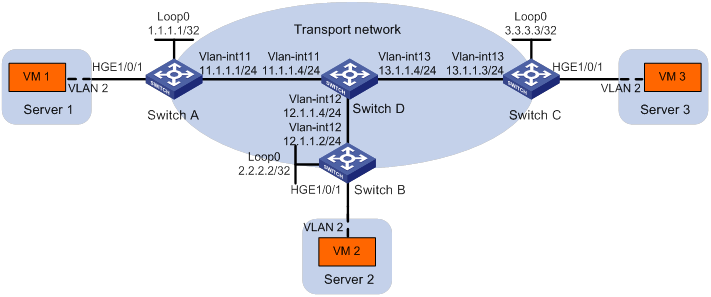
As shown in Figure 9:
· Configure VXLAN 10 as a unicast-mode VXLAN on Switch A, Switch B, and Switch C to provide Layer 2 connectivity for the VMs across the network sites.
· Manually establish VXLAN tunnels and assign the tunnels to VXLAN 10.
· Enable remote-MAC address learning.
Configuration procedure
1. Configure IP addresses and unicast routing settings:
# Assign IP addresses to interfaces, as shown in Figure 9. (Details not shown.)
# Configure OSPF on all transport network switches (Switches A through D). (Details not shown.)
2. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Enable Layer 2 forwarding for VXLANs.
[SwitchA] undo vxlan ip-forwarding
# Create VSI vpna and VXLAN 10.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# Assign an IP address to Loopback 0. The IP address will be used as the source IP address of the VXLAN tunnels to Switch B and Switch C.
[SwitchA] interface loopback 0
[SwitchA-Loopback0] ip address 1.1.1.1 255.255.255.255
[SwitchA-Loopback0] quit
# Create a VXLAN tunnel to Switch B. The tunnel interface name is Tunnel 1.
[SwitchA] interface tunnel 1 mode vxlan
[SwitchA-Tunnel1] source 1.1.1.1
[SwitchA-Tunnel1] destination 2.2.2.2
[SwitchA-Tunnel1] quit
# Create a VXLAN tunnel to Switch C. The tunnel interface name is Tunnel 2.
[SwitchA] interface tunnel 2 mode vxlan
[SwitchA-Tunnel2] source 1.1.1.1
[SwitchA-Tunnel2] destination 3.3.3.3
[SwitchA-Tunnel2] quit
# Assign Tunnel 1 and Tunnel 2 to VXLAN 10.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] tunnel 1
[SwitchA-vsi-vpna-vxlan-10] tunnel 2
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# On HundredGigE 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchA] interface hundredgige 1/0/1
[SwitchA-HundredGigE1/0/1] service-instance 1000
[SwitchA-HundredGigE1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-HundredGigE1/0/1-srv1000] xconnect vsi vpna
[SwitchA-HundredGigE1/0/1-srv1000] quit
[SwitchA-HundredGigE1/0/1] quit
3. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Enable Layer 2 forwarding for VXLANs.
[SwitchB] undo vxlan ip-forwarding
# Create VSI vpna and VXLAN 10.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Assign an IP address to Loopback 0. The IP address will be used as the source IP address of the VXLAN tunnels to Switch A and Switch C.
[SwitchB] interface loopback 0
[SwitchB-Loopback0] ip address 2.2.2.2 255.255.255.255
[SwitchB-Loopback0] quit
# Create a VXLAN tunnel to Switch A. The tunnel interface name is Tunnel 2.
[SwitchB] interface tunnel 2 mode vxlan
[SwitchB-Tunnel2] source 2.2.2.2
[SwitchB-Tunnel2] destination 1.1.1.1
[SwitchB-Tunnel2] quit
# Create a VXLAN tunnel to Switch C. The tunnel interface name is Tunnel 3.
[SwitchB] interface tunnel 3 mode vxlan
[SwitchB-Tunnel3] source 2.2.2.2
[SwitchB-Tunnel3] destination 3.3.3.3
[SwitchB-Tunnel3] quit
# Assign Tunnel 2 and Tunnel 3 to VXLAN 10.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] tunnel 2
[SwitchB-vsi-vpna-vxlan-10] tunnel 3
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# On HundredGigE 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchB] interface hundredgige 1/0/1
[SwitchB-HundredGigE1/0/1] service-instance 1000
[SwitchB-HundredGigE1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchB-HundredGigE1/0/1-srv1000] xconnect vsi vpna
[SwitchB-HundredGigE1/0/1-srv1000] quit
[SwitchB-HundredGigE1/0/1] quit
4. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Enable Layer 2 forwarding for VXLANs.
[SwitchC] undo vxlan ip-forwarding
# Create VSI vpna and VXLAN 10.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] vxlan 10
[SwitchC-vsi-vpna-vxlan-10] quit
[SwitchC-vsi-vpna] quit
# Assign an IP address to Loopback 0. The IP address will be used as the source IP address of the VXLAN tunnels to Switch A and Switch B.
[SwitchC] interface loopback 0
[SwitchC-Loopback0] ip address 3.3.3.3 255.255.255.255
[SwitchC-Loopback0] quit
# Create a VXLAN tunnel to Switch A. The tunnel interface name is Tunnel 1.
[SwitchC] interface tunnel 1 mode vxlan
[SwitchC-Tunnel1] source 3.3.3.3
[SwitchC-Tunnel1] destination 1.1.1.1
[SwitchC-Tunnel1] quit
# Create a VXLAN tunnel to Switch B. The tunnel interface name is Tunnel 3.
[SwitchC] interface tunnel 3 mode vxlan
[SwitchC-Tunnel3] source 3.3.3.3
[SwitchC-Tunnel3] destination 2.2.2.2
[SwitchC-Tunnel3] quit
# Assign Tunnel 1 and Tunnel 3 to VXLAN 10.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] vxlan 10
[SwitchC-vsi-vpna-vxlan-10] tunnel 1
[SwitchC-vsi-vpna-vxlan-10] tunnel 3
[SwitchC-vsi-vpna-vxlan-10] quit
[SwitchC-vsi-vpna] quit
# On HundredGigE 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchC] interface hundredgige 1/0/1
[SwitchC-HundredGigE1/0/1] service-instance 1000
[SwitchC-HundredGigE1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchC-HundredGigE1/0/1-srv1000] xconnect vsi vpna
[SwitchC-HundredGigE1/0/1-srv1000] quit
[SwitchC-HundredGigE1/0/1] quit
Verifying the configuration
1. Verify the VXLAN settings on the VTEPs. This example uses Switch A.
# Verify that the VXLAN tunnel interfaces on the VTEP are up.
[SwitchA] display interface tunnel 1
Tunnel1
Current state: UP
Line protocol state: UP
Description: Tunnel1 Interface
Bandwidth: 64kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 1.1.1.1, destination 2.2.2.2
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
# Verify that the VXLAN tunnels have been assigned to the VXLAN.
[SwitchA] display l2vpn vsi verbose
VSI Name: vpna
VSI Index : 0
VSI State : Up
MTU : 1500
Bandwidth : -
Broadcast Restrain : -
Multicast Restrain : -
Unknown Unicast Restrain: -
MAC Learning : Enabled
MAC Table Limit : -
MAC Learning rate : -
Drop Unknown : -
Flooding : Enabled
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel1 0x5000001 Up Manual Disabled
Tunnel2 0x5000002 Up Manual Disabled
ACs:
AC Link ID State
HGE1/0/1 srv1000 0 Up
# Verify that the VTEP has learned the MAC addresses of remote VMs.
<SwitchA> display l2vpn mac-address
MAC Address State VSI Name Link ID/Name Aging
cc3e-5f9c-6cdb Dynamic vpna Tunnel1 Aging
cc3e-5f9c-23dc Dynamic vpna Tunnel2 Aging
--- 2 mac address(es) found ---
2. Verify that VM 1, VM 2, and VM 3 can ping each other. (Details not shown.)
Multicast-mode VXLAN configuration example
Network requirements
As shown in Figure 10:
· Configure VXLAN 10 as a multicast-mode VXLAN on Switch A, Switch B, and Switch C to provide Layer 2 connectivity for the VMs across the network sites.
· Manually establish VXLAN tunnels and assign the tunnels to VXLAN 10.
· Enable remote-MAC address learning.
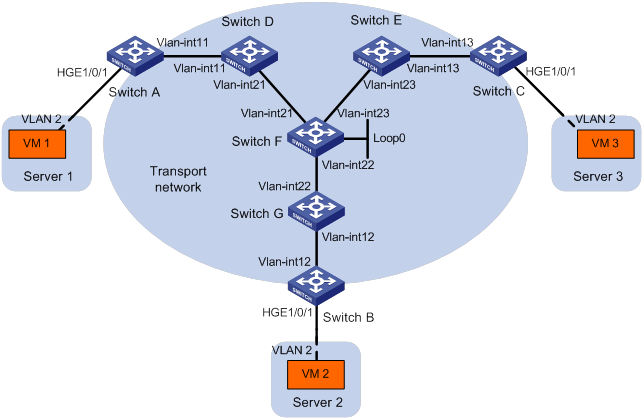
Table 1 IP address assignment
|
Device |
Interface |
IP address |
Device |
Interface |
IP address |
|
Switch A: |
|
|
Switch C: |
|
|
|
|
VLAN-interface 11 |
11.1.1.1/24 |
|
VLAN-interface 13 |
13.1.1.3/24 |
|
Switch D: |
|
|
Switch E: |
|
|
|
|
VLAN-interface 11 |
11.1.1.4/24 |
|
VLAN-interface 13 |
13.1.1.5/24 |
|
|
VLAN-interface 21 |
21.1.1.4/24 |
|
VLAN-interface 23 |
23.1.1.5/24 |
|
Switch F: |
|
|
Switch G: |
|
|
|
|
VLAN-interface 21 |
21.1.1.6/24 |
|
VLAN-interface 12 |
12.1.1.7/24 |
|
|
VLAN-interface 22 |
22.1.1.6/24 |
|
VLAN-interface 22 |
22.1.1.7/24 |
|
|
VLAN-interface 23 |
23.1.1.6/24 |
Switch B: |
|
|
|
|
Loop 0 |
6.6.6.6/32 |
|
VLAN-interface 12 |
12.1.1.2/24 |
Configuration procedure
1. Configure IP addresses and unicast routing settings:
# Assign IP addresses to interfaces, as shown in Figure 10. (Details not shown.)
# Configure OSPF on all transport network switches (Switches A through G). (Details not shown.)
2. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Enable IP multicast routing.
[SwitchA] multicast routing
[SwitchA-mrib] quit
# Enable Layer 2 forwarding for VXLANs.
[SwitchA] undo vxlan ip-forwarding
# Create VSI vpna and VXLAN 10.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# Assign an IP address to VLAN-interface 11, and enable the IGMP host feature on the interface. This interface's IP address will be the source IP address of VXLAN packets sent by the VTEP.
[SwitchA] interface vlan-interface 11
[SwitchA-Vlan-interface11] ip address 11.1.1.1 24
[SwitchA-Vlan-interface11] igmp host enable
[SwitchA-Vlan-interface11] quit
# Create a VXLAN tunnel to Switch B. The tunnel interface name is Tunnel 1.
[SwitchA] interface tunnel 1 mode vxlan
[SwitchA-Tunnel1] source 11.1.1.1
[SwitchA-Tunnel1] destination 12.1.1.2
[SwitchA-Tunnel1] quit
# Create a VXLAN tunnel to Switch C. The tunnel interface name is Tunnel 2.
[SwitchA] interface tunnel 2 mode vxlan
[SwitchA-Tunnel2] source 11.1.1.1
[SwitchA-Tunnel2] destination 13.1.1.3
[SwitchA-Tunnel2] quit
# Assign Tunnel 1 and Tunnel 2 to VXLAN 10.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] tunnel 1
[SwitchA-vsi-vpna-vxlan-10] tunnel 2
# Configure the multicast group address and source IP address for multicast VXLAN packets.
[SwitchA-vsi-vpna-vxlan-10] group 225.1.1.1 source 11.1.1.1
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# On HundredGigE 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchA] interface hundredgige 1/0/1
[SwitchA-HundredGigE1/0/1] service-instance 1000
[SwitchA-HundredGigE1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-HundredGigE1/0/1-srv1000] xconnect vsi vpna
[SwitchA-HundredGigE1/0/1-srv1000] quit
[SwitchA-HundredGigE1/0/1] quit
3. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Enable IP multicast routing.
[SwitchB] multicast routing
[SwitchB-mrib] quit
# Enable Layer 2 forwarding for VXLANs.
[SwitchB] undo vxlan ip-forwarding
# Create VSI vpna and VXLAN 10.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Assign an IP address to VLAN-interface 12, and enable the IGMP host feature on the interface. This interface's IP address will be the source IP address of VXLAN packets sent by the VTEP.
[SwitchB] interface vlan-interface 12
[SwitchB-Vlan-interface12] ip address 12.1.1.2 24
[SwitchB-Vlan-interface12] igmp host enable
[SwitchB-Vlan-interface12] quit
# Create a VXLAN tunnel to Switch A. The tunnel interface name is Tunnel 2.
[SwitchB] interface tunnel 2 mode vxlan
[SwitchB-Tunnel2] source 12.1.1.2
[SwitchB-Tunnel2] destination 11.1.1.1
[SwitchB-Tunnel2] quit
# Create a VXLAN tunnel to Switch C. The tunnel interface name is Tunnel 3.
[SwitchB] interface tunnel 3 mode vxlan
[SwitchB-Tunnel3] source 12.1.1.2
[SwitchB-Tunnel3] destination 13.1.1.3
[SwitchB-Tunnel3] quit
# Assign Tunnel 2 and Tunnel 3 to VXLAN 10.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] tunnel 2
[SwitchB-vsi-vpna-vxlan-10] tunnel 3
# Configure the VXLAN multicast group address and the source IP address for VXLAN packets.
[SwitchB-vsi-vpna-vxlan-10] group 225.1.1.1 source 12.1.1.2
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# On HundredGigE 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchB] interface hundredgige 1/0/1
[SwitchB-HundredGigE1/0/1] service-instance 1000
[SwitchB-HundredGigE1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchB-HundredGigE1/0/1-srv1000] xconnect vsi vpna
[SwitchB-HundredGigE1/0/1-srv1000] quit
[SwitchB-HundredGigE1/0/1] quit
4. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Enable IP multicast routing.
[SwitchC] multicast routing
[SwitchC-mrib] quit
# Enable Layer 2 forwarding for VXLANs.
[SwitchC] undo vxlan ip-forwarding
# Create VSI vpna and VXLAN 10.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] vxlan 10
[SwitchC-vsi-vpna-vxlan-10] quit
[SwitchC-vsi-vpna] quit
# Assign an IP address to VLAN-interface 13, and enable the IGMP host feature on the interface. This interface's IP address will be the source IP address of VXLAN packets sent by the VTEP.
[SwitchC] interface vlan-interface 13
[SwitchC-Vlan-interface13] ip address 13.1.1.3 24
[SwitchC-Vlan-interface13] igmp host enable
[SwitchC-Vlan-interface13] quit
# Create a VXLAN tunnel to Switch A. The tunnel interface name is Tunnel 1.
[SwitchC] interface tunnel 1 mode vxlan
[SwitchC-Tunnel1] source 13.1.1.3
[SwitchC-Tunnel1] destination 11.1.1.1
[SwitchC-Tunnel1] quit
# Create a VXLAN tunnel to Switch B. The tunnel interface name is Tunnel 3.
[SwitchC] interface tunnel 3 mode vxlan
[SwitchC-Tunnel3] source 13.1.1.3
[SwitchC-Tunnel3] destination 12.1.1.2
[SwitchC-Tunnel3] quit
# Assign Tunnel 1 and Tunnel 3 to VXLAN 10.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] vxlan 10
[SwitchC-vsi-vpna-vxlan-10] tunnel 1
[SwitchC-vsi-vpna-vxlan-10] tunnel 3
# Configure the multicast group address and source IP address for VXLAN multicast packets.
[SwitchC-vsi-vpna-vxlan-10] group 225.1.1.1 source 13.1.1.3
[SwitchC-vsi-vpna-vxlan-10] quit
[SwitchC-vsi-vpna] quit
# On HundredGigE 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchC] interface hundredgige 1/0/1
[SwitchC-HundredGigE1/0/1] service-instance 1000
[SwitchC-HundredGigE1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchC-HundredGigE1/0/1-srv1000] xconnect vsi vpna
[SwitchC-HundredGigE1/0/1-srv1000] quit
[SwitchC-HundredGigE1/0/1] quit
5. Configure Switch D:
# Enable IP multicast routing.
<SwitchD> system-view
[SwitchD] multicast routing
[SwitchD-mrib] quit
# Enable IGMP and PIM-SM on VLAN-interface 11.
[SwitchD] interface vlan-interface 11
[SwitchD-Vlan-interface11] igmp enable
[SwitchD-Vlan-interface11] pim sm
[SwitchD-Vlan-interface11] quit
# Enable PIM-SM on VLAN-interface 21.
[SwitchD] interface vlan-interface 21
[SwitchD-Vlan-interface21] pim sm
[SwitchD-Vlan-interface21] quit
# Enable BIDIR-PIM.
[SwitchD] pim
[SwitchD-pim] bidir-pim enable
[SwitchD-pim] quit
6. Configure Switch E:
# Enable IP multicast routing.
<SwitchE> system-view
[SwitchE] multicast routing
[SwitchE-mrib] quit
# Enable IGMP and PIM-SM on VLAN-interface 13.
[SwitchE] interface vlan-interface 13
[SwitchE-Vlan-interface13] igmp enable
[SwitchE-Vlan-interface13] pim sm
[SwitchE-Vlan-interface13] quit
# Enable PIM-SM on VLAN-interface 23.
[SwitchE] interface vlan-interface 23
[SwitchE-Vlan-interface23] pim sm
[SwitchE-Vlan-interface23] quit
# Enable BIDIR-PIM.
[SwitchE] pim
[SwitchE-pim] bidir-pim enable
[SwitchE-pim] quit
7. Configure Switch F:
# Enable IP multicast routing.
<SwitchF> system-view
[SwitchF] multicast routing
[SwitchF-mrib] quit
# Enable PIM-SM on VLAN-interface 21, VLAN-interface 22, VLAN-interface 23, and Loopback 0.
[SwitchF] interface vlan-interface 21
[SwitchF-Vlan-interface21] pim sm
[SwitchF-Vlan-interface21] quit
[SwitchF] interface vlan-interface 22
[SwitchF-Vlan-interface22] pim sm
[SwitchF-Vlan-interface22] quit
[SwitchF] interface vlan-interface 23
[SwitchF-Vlan-interface23] pim sm
[SwitchF-Vlan-interface23] quit
[SwitchF] interface loopback 0
[SwitchF-LoopBack0] pim sm
[SwitchF-LoopBack0] quit
# Enable BIDIR-PIM.
[SwitchF] pim
[SwitchF-pim] bidir-pim enable
# Configure VLAN-interface 22 as a candidate-BSR, and configure Loopback 0 as a candidate-RP for BIDIR-PIM.
[SwitchF-pim] c-bsr 22.1.1.6
[SwitchF-pim] c-rp 6.6.6.6 bidir
[SwitchF-pim] quit
8. Configure Switch G:
# Enable IP multicast routing.
<SwitchG> system-view
[SwitchG] multicast routing
[SwitchG-mrib] quit
# Enable IGMP and PIM-SM on VLAN-interface 12.
[SwitchG] interface vlan-interface 12
[SwitchG-Vlan-interface12] igmp enable
[SwitchG-Vlan-interface12] pim sm
[SwitchG-Vlan-interface12] quit
# Enable PIM-SM on VLAN-interface 22.
[SwitchG] interface vlan-interface 22
[SwitchG-Vlan-interface22] pim sm
[SwitchG-Vlan-interface22] quit
# Enable BIDIR-PIM.
[SwitchG] pim
[SwitchG-pim] bidir-pim enable
[SwitchG-pim] quit
Verifying the configuration
1. Verify the VXLAN settings on the VTEPs. This example uses Switch A.
# Verify that the VXLAN tunnel interfaces on the VTEP are up.
[SwitchA] display interface tunnel 1
Tunnel1
Current state: UP
Line protocol state: UP
Description: Tunnel1 Interface
Bandwidth: 64kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 11.1.1.1, destination 12.1.1.2
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
# Verify that the VXLAN tunnels have been assigned to the VXLAN.
[SwitchA] display l2vpn vsi verbose
VSI Name: vpna
VSI Index : 0
VSI State : Up
MTU : 1500
Bandwidth : -
Broadcast Restrain : -
Multicast Restrain : -
Unknown Unicast Restrain: -
MAC Learning : Enabled
MAC Table Limit : -
MAC Learning rate : -
Drop Unknown : -
Flooding : Enabled
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel1 0x5000001 Up Manual Disabled
Tunnel2 0x5000002 Up Manual Disabled
MTunnel0 0x6000000 Up Auto Disabled
ACs:
AC Link ID State
HGE1/0/1 srv1000 0 Up
# Verify that the VTEP has learned the MAC addresses of remote VMs.
<SwitchA> display l2vpn mac-address
MAC Address State VSI Name Link ID/Name Aging
cc3e-5f9c-6cdb Dynamic vpna Tunnel1 Aging
cc3e-5f9c-23dc Dynamic vpna Tunnel2 Aging
--- 2 mac address(es) found ---
# Verify that the VTEP has joined the VXLAN multicast group on VLAN-interface 11.
<SwitchA> display igmp host group
IGMP host groups in total: 1
Vlan-interface11(11.1.1.1):
IGMP host groups in total: 1
Group address Member state Expires
225.1.1.1 Idle Off
2. Verify that VM 1, VM 2, and VM 3 can ping each other. (Details not shown.)
Configuring VXLAN IP gateways
Overview
The following are available IP gateway placement designs for VXLANs:
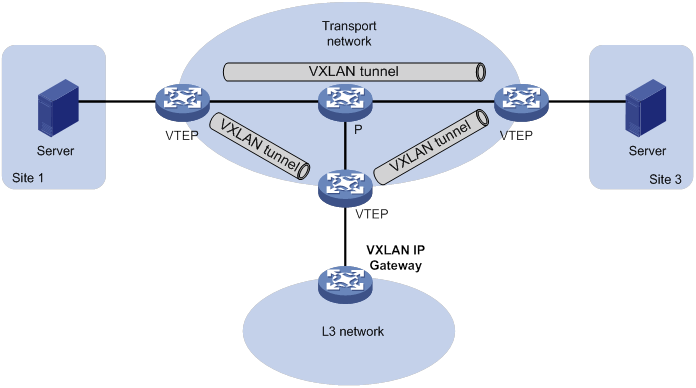
· VXLAN IP gateways separated from VTEPs—Use a VXLAN-unaware device as a gateway to the external network for VXLANs. On the gateway, you do not need to configure VXLAN settings.
· VXLAN IP gateways collocated with VTEPs—Include the following placement designs:
? Centralized VXLAN IP gateway deployment—Use one VTEP to provide Layer 3 forwarding for VXLANs. Typically, the gateway-collocated VTEP connects to other VTEPs and the external network. To use this design, make sure the IP gateway has sufficient bandwidth and processing capability. Centralized VXLAN IP gateways provide services only for IPv4 networks.
? Centralized VXLAN gateway group deployment—Use one VTEP group that contains redundant centralized VXLAN IP gateways to provide reliable gateway services for VXLANs.
? Distributed VXLAN IP gateway deployment—Deploy one VXLAN IP gateway on each VTEP to provide Layer 3 forwarding for VXLANs at their respective sites. This design distributes the Layer 3 traffic load across VTEPs. However, its configuration is more complex than the centralized VXLAN IP gateway design.
In a collocation design, the VTEPs use virtual Layer 3 VSI interfaces as gateway interfaces to provide services for VXLANs.
VXLAN IP gateways separated from VTEPs
As shown in Figure 11, an independent VXLAN IP gateway connects a Layer 3 network to a VTEP. VMs send Layer 3 traffic in Layer 2 frames to the gateway through VXLAN tunnels. When the tunneled VXLAN packets arrive, the VTEP terminates the VXLANs and forwards the inner frames to the gateway. In this gateway placement design, the VTEP does not perform Layer 3 forwarding for VXLANs.
Figure 11 VXLAN IP gateway separated from VTEPs
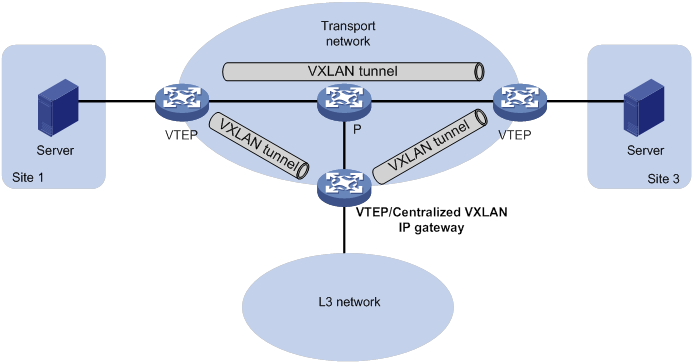
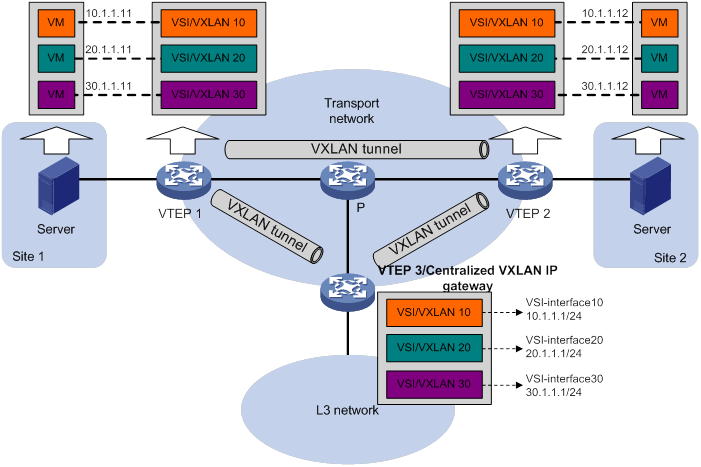
Centralized VXLAN IP gateway deployment
As shown in Figure 12, a VTEP acts as a gateway for VMs in the VXLANs. The VTEP both terminates the VXLANs and performs Layer 3 forwarding for the VMs.
Figure 12 Centralized VXLAN IP gateway placement design
As shown in Figure 13, the network uses the following process to forward Layer 3 traffic from VM 10.1.1.11 to the Layer 3 network:
1. The VM sends an ARP request to obtain the MAC address of the gateway (VTEP 3) at 10.1.1.1.
2. VTEP 1 floods the ARP request to all remote VTEPs.
3. VTEP 3 de-encapsulates the ARP request, creates an ARP entry for the VM, and sends an ARP reply to the VM.
4. VTEP 1 forwards the ARP reply to the VM.
5. The VM learns the MAC address of the gateway, and sends the Layer 3 traffic to the gateway.
6. VTEP 3 removes the VXLAN encapsulation and inner Ethernet header for the traffic, and forwards the traffic to the destination node.
Inter-VXLAN forwarding is the same as this process except for the last step. At the last step of inter-VLAN forwarding, the gateway replaces the source-VXLAN encapsulation with the destination-VXLAN encapsulation, and then forwards the traffic.
Figure 13 Example of centralized VXLAN IP gateway deployment
Centralized VXLAN gateway group deployment
As shown in Figure 14, a VTEP group uses redundant centralized VXLAN IP gateways to provide reliable gateway services for VMs in the VXLANs. All member VTEPs in the group participate in Layer 3 forwarding and load share traffic between the Layer 3 network and the VXLANs. This design distributes processing among multiple VTEPs and prevents single points of failure.
Figure 14 Example of centralized VXLAN IP gateway group deployment
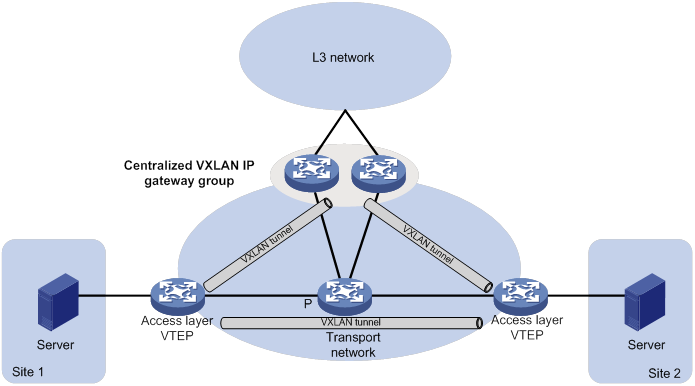
The VTEP group is a virtual gateway that provides services at a group IP address. Access layer VTEPs set up VXLAN tunnels to the group IP address for data traffic forwarding. Each VTEP in the group automatically uses its member IP address to set up tunnels to the other member VTEPs and access layer VTEPs. The tunnels are used to transmit protocol packets and synchronize ARP entries.
Distributed VXLAN IP gateway deployment
As shown in Figure 15, each site's VTEP acts as a gateway to perform Layer 3 forwarding for the VXLANs of the local site. A VTEP acts as a border gateway to the Layer 3 network for the VXLANs. The VTEPs perform Layer 3 forwarding based on ARP entries.
|
|
IMPORTANT: The site-connected gateways are called distributed gateways. On the distributed gateways, you must enable local proxy ARP. |
Figure 15 Distributed VXLAN IP gateway placement design
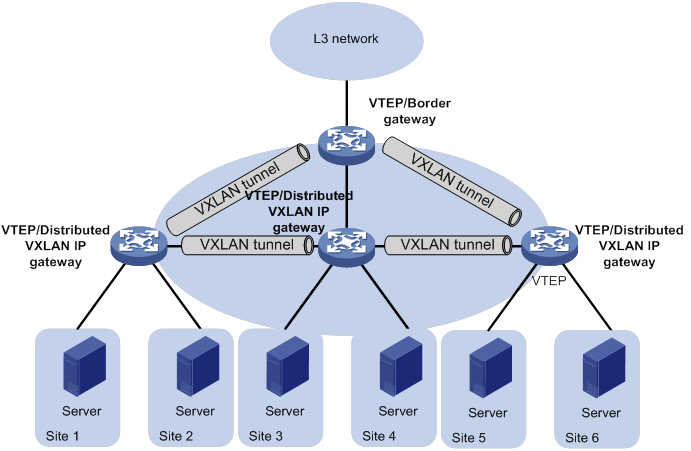
Figure 16 shows an example of distributed VXLAN IP gateway deployment. This section uses this figure to describe the forwarding processes for intra-VXLAN traffic, inter-VXLAN traffic, and traffic from a VXLAN to an external network. In these processes, VTEPs use dynamically learned ARP entries.
Figure 16 Example of distributed VXLAN IP gateway deployment
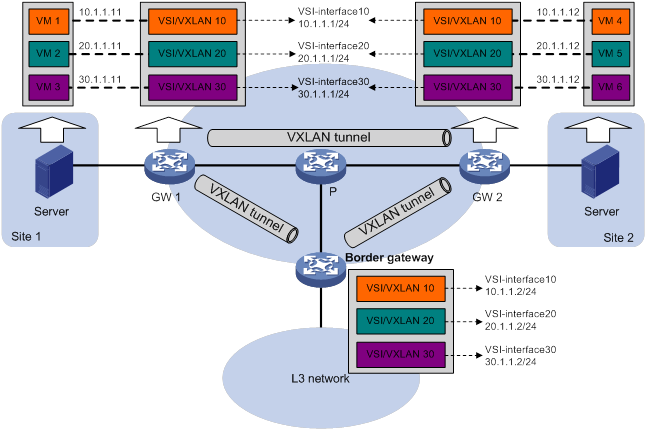
Intra-VXLAN traffic forwarding between sites
As shown in Figure 16, the network uses the following process to forward traffic in a VXLAN between sites (for example, from VM 1 to VM 4 in VXLAN 10):
1. VM 1 sends an ARP request to obtain the MAC address of VM 4.
2. GW 1 performs the following operations:
a. Creates an ARP entry for VM 1 and replies with the MAC address of VSI-interface 10 (the gateway interface for VXLAN 10).
b. Replaces the sender MAC address of the ARP request with the MAC address of VSI-interface 10, and then floods the request to all remote VTEPs.
3. VM 1 creates an ARP entry for VM 4. The MAC address in the entry is the MAC address of VSI-interface 10 on GW 1.
4. GW 2 (the VTEP for VM 4) performs the following operations:
a. De-encapsulates the ARP request and creates an ARP entry for VM 1. The entry contains VM 1's IP address (10.1.1.11), the MAC address of VSI-interface 10 on GW 1, and the incoming tunnel interface.
b. Replaces the sender MAC address of the request with the MAC address of VSI-interface 10 on GW 2, and then floods the request to the local site in VXLAN 10.
5. VM 4 creates an ARP entry for VM 1, and then sends a reply to GW 2. The MAC address in the ARP entry is the MAC address of VSI-interface 10 on GW 2.
6. GW 2 performs the following operations:
a. Creates an ARP entry for VM 4.
b. Replaces the sender MAC address of the request with the MAC address of VSI-interface 10 on GW 2, and sends the reply to GW 1.
7. GW 1 de-encapsulates the ARP request and creates an ARP entry for VM 4. The entry contains VM 4's IP address (10.1.1.12), the MAC address of VSI-interface 10 on GW 2, and the incoming tunnel interface.
8. For subsequent traffic between VM 1 and VM 4, GW 1 and GW 2 use their respective ARP tables to make the forwarding decision.
Inter-VXLAN traffic forwarding between sites
As shown in Figure 16, the network uses the following process to forward traffic between VXLANs (for example, from VM 1 in VXLAN 10 to VM 5 in VXLAN 20):
1. VM 1 sends an ARP request to obtain the MAC address of the gateway at 10.1.1.1.
2. GW 1 creates an ARP entry for VM 1 and replies with the MAC address of VSI-interface 10 (the gateway interface for VXLAN 10).
3. VM 1 sends the packet destined for VM 5 to GW 1.
4. GW 1 sends an ARP request to the local site and remote sites to obtain the MAC address of VM 5. In the ARP request, the sender IP address is 20.1.1.1, and the sender MAC address is the MAC address of VSI-interface 20 on GW 1.
5. GW 2 performs the following operations:
a. De-encapsulates the ARP request and creates an ARP entry for VM 1. The entry contains VM 1's IP address (20.1.1.1), the MAC address of VSI-interface 20 on GW 1, and the incoming tunnel interface.
b. Replaces the sender MAC address of the request with the MAC address of VSI-interface 20 on GW 2, and then floods the request to the local site in VXLAN 20.
6. VM 5 creates an ARP entry for GW 2, and then sends a reply to GW 2. The entry contains the IP address (20.1.1.1) and MAC address of VSI-interface 20 on GW 2).
7. GW 2 performs the following operations:
a. Creates an ARP entry for VM 5.
b. Replaces the sender MAC address in the request with the MAC address of VSI-interface 20 on GW 2, and then sends the reply to GW 1.
8. GW 1 de-encapsulates the ARP request and creates an ARP entry for VM 5. The entry contains VM 5's IP address 20.1.1.12, the MAC address of VSI-interface 20 on GW 2, and the incoming tunnel interface.
9. For subsequent traffic between VM 1 and VM 5, GW 1 and GW 2 use their respective ARP tables to make the forwarding decision.
VXLAN-to-external network traffic forwarding
As shown in Figure 16, the network uses the following process to forward traffic from a VXLAN to the Layer 3 network (for example, from VM 1 to the host at 50.1.1.1):
1. VM 1 sends an ARP request to obtain the MAC address of the gateway at 10.1.1.1.
2. GW 1 creates an ARP entry for VM 1 and replies with the MAC address of VSI-interface 10 (the gateway interface for VXLAN 10).
3. VM 1 sends a packet destined for the host to GW 1.
4. GW 1 performs the following operations:
a. Searches the IP routing policies or routing table for the next hop. In this example, the next hop for the packet is 10.1.1.2 (the border gateway).
b. Floods an ARP request to the local and remote sites in VXLAN 10 to obtain the MAC address of 10.1.1.2.
5. The border gateway de-encapsulates the ARP request, creates an ARP entry for GW 1, and tunnels a reply to GW 1.
6. GW 1 de-encapsulates the ARP reply and creates an ARP entry for 10.1.1.2.
7. GW 1 sends the packet destined for the host to the border gateway.
8. The border gateway de-encapsulates the packet and forwards it to the host.
Configuration restrictions and guidelines
As a best practice, deploy Layer 2 Ethernet interfaces of the access link type or Layer 3 Ethernet interfaces as the outgoing interfaces of VXLAN packets on a VXLAN IP gateway. To use Layer 2 Ethernet interfaces of the trunk link type or Layer 3 Ethernet subinterfaces, you must execute the vxlan ip-forwarding tagged command.
Do not configure centralized gateway settings and centralized gateway group settings together on a device.
Configuration prerequisites
Before you configure a centralized or distributed VXLAN IP gateway, you must perform the following tasks on VTEPs:
· Enable Layer 3 forwarding for VXLANs.
· Create VSIs and VXLANs.
· Configure VXLAN tunnels and assign them to VXLANs.
Configuring a centralized VXLAN IP gateway
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Create a VSI interface and enter VSI interface view. |
interface vsi-interface vsi-interface-id |
By default, no VSI interfaces exist. |
|
3. Assign an IPv4 address to the VSI interface. |
ip address ip-address { mask | mask-length } |
By default, no IPv4 address is assigned to a VSI interface. |
|
4. Return to system view. |
quit |
N/A |
|
5. Enter VSI view. |
vsi vsi-name |
N/A |
|
6. Specify a gateway interface for the VSI. |
gateway vsi-interface vsi-interface-id |
By default, no gateway interface is specified for a VSI. |
Configuring a centralized VXLAN IP gateway group
Configuration restrictions and guidelines
A centralized VXLAN IP gateway group is exclusive with the VSI flood confining feature in some conditions. When you use the features together, follow these restrictions and guidelines:
· A gateway group can work correctly only when flooding is enabled for VSIs or when both unknown unicast and unknown multicast floods are suppressed.
· As a best practice, finish gateway group configuration before you configure VSI flood confining. The system will display prompts when the VSI flood confining setting conflicts with the gateway group configuration.
Configuring a VTEP group
Make sure the member VTEPs use the same VXLAN settings.
Configure a VTEP group on a member VTEP:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Create a VSI interface and enter VSI interface view. |
interface vsi-interface vsi-interface-id |
By default, no VSI interfaces exist. You must create the same VSI interface on all VTEPs in the VTEP group. |
|
3. Assign an IP address to the VSI interface. |
ip address ip-address { mask | mask-length } |
By default, no IP address is assigned to a VSI interface. You must assign the same IP address to the VSI interface on each VTEP in the VTEP group. |
|
4. Assign a MAC address to the VSI interface. |
mac-address mac-address |
The default MAC address of VSI interfaces is the bridge MAC address + 1. You must assign the same MAC address to the VSI interface on each VTEP in the VTEP group. If the specified MAC address has the same higher 36 bits as the device's bridge MAC address, the specified MAC address is used as the source MAC address of the packets sent by the VSI interface. If the specified MAC address does not meet this requirement, the default MAC address is used as the source MAC address of the packets sent by the VSI interface. The device supports a maximum of 16 VSI interface MAC addresses if the higher 36 bits of the MAC addresses are different than the device's bridge MAC address. As a best practice, assign VSI interfaces the MAC addresses that have the same higher 36 bits as the device's bridge MAC address if more than 16 MAC addresses are required. |
|
5. Return to system view. |
quit |
N/A |
|
6. Enter VSI view. |
vsi vsi-name |
N/A |
|
7. Specify a gateway interface for the VSI. |
gateway vsi-interface vsi-interface-id |
By default, no gateway interface is specified for a VSI. |
|
8. Return to system view. |
quit |
N/A |
|
9. Assign the local VTEP to a VTEP group and specify the member IP address for the VTEP. |
vtep group group-ip member local member-ip |
By default, a VTEP is not assigned to any VTEP group. Perform this task on all member VTEPs in the VTEP group. The IP address specified by the member-ip argument must already exist on the local VTEP. You must configure a routing protocol to advertise the IP address in the transport network. Member VTEPs in a VTEP group cannot use the group IP address or share an IP address. |
|
10. Specify all the other VTEPs in the VTEP group. |
vtep group group-ip member remote member-ip&<1-8> |
By default, no VTEP group is specified. Perform this task on all member VTEPs in the VTEP group. |
Specifying a VTEP group as the gateway for an access layer VTEP
Before you specify a VTEP group on an access layer VTEP, perform the following tasks on the VTEP:
· Configure VSIs and VXLANs.
· Set up VXLAN tunnels to remote sites and the VTEP group, and assign the tunnels to VXLANs.
To specify a VTEP group as the gateway for an access layer VTEP:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Specify a VTEP group and all its member VTEPs. |
vtep group group-ip member remote member-ip&<1-8> |
By default, no VTEP group is specified. |
Configuring a distributed VXLAN IP gateway
For a VXLAN that requires access to the external network, specify the VXLAN's VSI interface on the border gateway as the next hop by using one of the following methods:
· Configure a static route.
· Configure a routing policy, and apply the policy by using the apply default-next-hop or apply next-hop command. For more information about configuring routing policies, see routing policy configuration in Layer 3—IP Routing Configuration Guide.
If both ARP flood suppression and local proxy ARP are enabled on a distributed VXLAN IP gateway, only local proxy ARP takes effect. As a best practice, do not use these features together on distributed VXLAN IP gateways. For more information about ARP flood suppression, see "Enabling ARP flood suppression."
To configure a distributed VXLAN IP gateway:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Create a VSI interface and enter VSI interface view. |
interface vsi-interface vsi-interface-id |
By default, no VSI interfaces exist. |
|
3. Assign an IPv4 address to the VSI interface. |
ip address ip-address { mask | mask-length } [ sub ] |
By default, no IPv4 address is assigned to a VSI interface. This interface will be used as a gateway for VXLANs. On an IPv4 network, you can assign one primary IP address and multiple secondary IP addresses. |
|
4. Specify the VSI interface as a distributed gateway. |
distributed-gateway local |
By default, a VSI interface is not a distributed gateway. |
|
5. Enable local proxy ARP. |
local-proxy-arp enable [ ip-range startIP to endIP ] |
By default, local proxy ARP is disabled. For more information about the commands, see Layer 3—IP Services Command Reference. |
|
6. Return to system view. |
quit |
N/A |
|
7. (Optional.) Enable dynamic ARP entry synchronization for distributed VXLAN IP gateways. |
arp distributed-gateway dynamic-entry synchronize |
By default, dynamic ARP entry synchronization is disabled for distributed VXLAN IP gateways. When local proxy ARP is enabled on distributed VXLAN IP gateways, each gateway learns ARP information independently. A gateway does not forward ARP packets destined for it to other gateways. For distributed VXLAN IP gateways to have the same ARP entries, you must enable dynamic ARP entry synchronization. A controller or the EVPN feature can also synchronize ARP entries among distributed VXLAN IP gateways. When you use a controller or the EVPN feature, do not enable dynamic ARP entry synchronization. |
|
8. Enter VSI view. |
vsi vsi-name |
N/A |
|
9. Specify the VSI interface as the gateway interface for the VSI. |
gateway vsi-interface vsi-interface-id |
By default, no gateway interface is specified for a VSI. |
|
10. Assign a subnet to the VSI. |
gateway subnet ipv4-address wildcard-mask |
By default, no subnet exists on a VSI. You must configure this command on VSIs that share a gateway interface. This command enables the VSI interface to identify the VSI of a packet. You can assign a maximum of eight IPv4 subnets to a VSI. Make sure these subnets are on the same network as one of the IP addresses on the gateway interface. For VSIs that share a gateway interface, the subnets must be unique. If you remove the gateway interface from the VSI, the VSI's subnet settings are automatically deleted. |
Configuring a VSI interface
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter VSI interface view. |
interface vsi-interface vsi-interface-id |
N/A |
|
3. Assign a MAC address to the VSI interface. |
mac-address mac-address |
The default MAC address of VSI interfaces is the bridge MAC address + 1. If the specified MAC address has the same higher 36 bits as the device's bridge MAC address, the specified MAC address is used as the source MAC address of the packets sent by the VSI interface. If the specified MAC address does not meet this requirement, the default MAC address is used as the source MAC address of the packets sent by the VSI interface. The device supports a maximum of 16 VSI interface MAC addresses if the higher 36 bits of the MAC addresses are different than the device's bridge MAC address. As a best practice, assign VSI interfaces the MAC addresses that have the same higher 36 bits as the device's bridge MAC address if more than 16 MAC addresses are required. |
|
4. Configure the description of the VSI interface. |
description text |
The default description of a VSI interface is interface-name plus Interface (for example, Vsi-interface100 Interface). |
|
5. Set the MTU for the VSI interface. |
mtu mtu-value |
The default MTU of a VSI interface is 1444 bytes. |
|
6. Set the expected bandwidth for the VSI interface. |
bandwidth bandwidth-value |
The default expected bandwidth (in kbps) equals the interface baud rate divided by 1000. |
|
7. Restore the default settings on the interface. |
default |
N/A |
|
8. Set an ARP packet sending rate limit for the VSI interface. |
arp send-rate pps |
By default, the ARP packet sending rate is not limited for a VSI interface. |
|
9. Bring up the interface. |
undo shutdown |
By default, a VSI interface is up. |
Enabling packet statistics for a VSI interface
To enable packet statistics for a VSI and its associated VSI interface, set the packet statistic collection mode to VSI and execute the statistics enable command in VSI view.
The statistic mode vsi command takes effect only if the VSI interface is associated with only one VSI.
You can use the statistic mode ac, statistic mode queue, or statistic mode vsi command to set the packet statistic collection mode. If you execute the statistic mode command multiple times, the most recent configuration takes effect.
To enable packet statistics for a VSI interface:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Set the packet statistic collection mode to VSI. |
statistic mode vsi |
The default packet statistic collection mode is VSI. |
|
3. Enter VSI view. |
vsi vsi-name |
N/A |
|
4. Enable packet statistics for the VSI. |
statistics enable |
By default, the packet statistics feature is disabled for all VSIs. |
Displaying and maintaining VXLAN IP gateway
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display information about VSI interfaces. |
display interface [ vsi-interface [ vsi-interface-id ] ] [ brief [ description | down ] ] |
|
Clear statistics on VSI interfaces. |
reset counters interface [ vsi-interface [ vsi-interface-id ] ] |
VXLAN IP gateway configuration examples
Centralized VXLAN IP gateway configuration example
Network requirements
As shown in Figure 17:
· Configure VXLAN 10 as a unicast-mode VXLAN on Switch A, Switch B, and Switch C to provide connectivity for the VMs across the network sites.
· Configure a centralized VXLAN IP gateway on Switch B to provide gateway services for VXLAN 10.
· Manually establish VXLAN tunnels and assign the tunnels to VXLAN 10.
· Enable remote-MAC address learning.
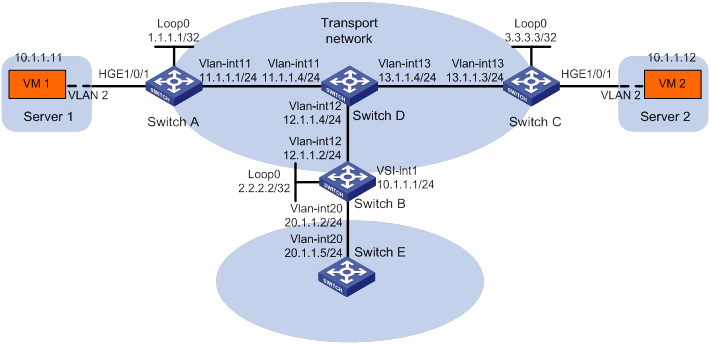
Configuration procedure
1. On VM 1 and VM 2, specify 10.1.1.1 as the gateway address. (Details not shown.)
2. Configure IP addresses and unicast routing settings:
# Assign IP addresses to interfaces, as shown in Figure 17. (Details not shown.)
# Configure OSPF on all transport network switches (Switches A through D). (Details not shown.)
# Configure OSPF to advertise routes to networks 10.1.1.0/24 and 20.1.1.0/24 on Switch B and Switch E. (Details not shown.)
3. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Enable Layer 2 forwarding for VXLANs.
[SwitchA] undo vxlan ip-forwarding
# Create VSI vpna and VXLAN 10.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# Assign an IP address to Loopback 0. The IP address will be used as the source IP address of the VXLAN tunnels to Switch B and Switch C.
[SwitchA] interface loopback 0
[SwitchA-Loopback0] ip address 1.1.1.1 255.255.255.255
[SwitchA-Loopback0] quit
# Create a VXLAN tunnel to Switch B. The tunnel interface name is Tunnel 1.
[SwitchA] interface tunnel 1 mode vxlan
[SwitchA-Tunnel1] source 1.1.1.1
[SwitchA-Tunnel1] destination 2.2.2.2
[SwitchA-Tunnel1] quit
# Create a VXLAN tunnel to Switch C. The tunnel interface name is Tunnel 2.
[SwitchA] interface tunnel 2 mode vxlan
[SwitchA-Tunnel2] source 1.1.1.1
[SwitchA-Tunnel2] destination 3.3.3.3
[SwitchA-Tunnel2] quit
# Assign Tunnel 1 and Tunnel 2 to VXLAN 10.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] tunnel 1
[SwitchA-vsi-vpna-vxlan-10] tunnel 2
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# On HundredGigE 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchA] interface hundredgige 1/0/1
[SwitchA-HundredGigE1/0/1] service-instance 1000
[SwitchA-HundredGigE1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-HundredGigE1/0/1-srv1000] xconnect vsi vpna
[SwitchA-HundredGigE1/0/1-srv1000] quit
[SwitchA-HundredGigE1/0/1] quit
4. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Create VSI vpna and VXLAN 10.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Assign an IP address to Loopback 0. The IP address will be used as the source IP address of the VXLAN tunnels to Switch A and Switch C.
[SwitchB] interface loopback 0
[SwitchB-Loopback0] ip address 2.2.2.2 255.255.255.255
[SwitchB-Loopback0] quit
# Create a VXLAN tunnel to Switch A. The tunnel interface name is Tunnel 2.
[SwitchB] interface tunnel 2 mode vxlan
[SwitchB-Tunnel2] source 2.2.2.2
[SwitchB-Tunnel2] destination 1.1.1.1
[SwitchB-Tunnel2] quit
# Create a VXLAN tunnel to Switch C. The tunnel interface name is Tunnel 3.
[SwitchB] interface tunnel 3 mode vxlan
[SwitchB-Tunnel3] source 2.2.2.2
[SwitchB-Tunnel3] destination 3.3.3.3
[SwitchB-Tunnel3] quit
# Assign Tunnel 2 and Tunnel 3 to VXLAN 10.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] tunnel 2
[SwitchB-vsi-vpna-vxlan-10] tunnel 3
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Create VSI-interface 1 and assign the interface an IP address. The IP address will be used as the gateway address for VXLAN 10.
[SwitchB] interface vsi-interface 1
[SwitchB-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchB-Vsi-interface1] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] gateway vsi-interface 1
[SwitchB-vsi-vpna] quit
5. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Enable Layer 2 forwarding for VXLANs.
[SwitchC] undo vxlan ip-forwarding
# Create VSI vpna and VXLAN 10.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] vxlan 10
[SwitchC-vsi-vpna-vxlan-10] quit
[SwitchC-vsi-vpna] quit
# Assign an IP address to Loopback 0. The IP address will be used as the source IP address of the VXLAN tunnels to Switch A and Switch B.
[SwitchC] interface loopback 0
[SwitchC-Loopback0] ip address 3.3.3.3 255.255.255.255
[SwitchC-Loopback0] quit
# Create a VXLAN tunnel to Switch A. The tunnel interface name is Tunnel 1.
[SwitchC] interface tunnel 1 mode vxlan
[SwitchC-Tunnel1] source 3.3.3.3
[SwitchC-Tunnel1] destination 1.1.1.1
[SwitchC-Tunnel1] quit
# Create a VXLAN tunnel to Switch B. The tunnel interface name is Tunnel 3.
[SwitchC] interface tunnel 3 mode vxlan
[SwitchC-Tunnel3] source 3.3.3.3
[SwitchC-Tunnel3] destination 2.2.2.2
[SwitchC-Tunnel3] quit
# Assign Tunnel 1 and Tunnel 3 to VXLAN 10.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] vxlan 10
[SwitchC-vsi-vpna-vxlan-10] tunnel 1
[SwitchC-vsi-vpna-vxlan-10] tunnel 3
[SwitchC-vsi-vpna-vxlan-10] quit
[SwitchC-vsi-vpna] quit
# On HundredGigE 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchC] interface hundredgige 1/0/1
[SwitchC-HundredGigE1/0/1] service-instance 1000
[SwitchC-HundredGigE1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchC-HundredGigE1/0/1-srv1000] xconnect vsi vpna
[SwitchC-HundredGigE1/0/1-srv1000] quit
[SwitchC-HundredGigE1/0/1] quit
Verifying the configuration
1. Verify the VXLAN IP gateway settings on Switch B:
# Verify that the VXLAN tunnel interfaces are up on Switch B.
[SwitchB] display interface tunnel 2
Tunnel2
Current state: UP
Line protocol state: UP
Description: Tunnel2 Interface
Bandwidth: 64kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 2.2.2.2, destination 1.1.1.1
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
# Verify that VSI-interface 1 is up.
[SwitchB] display interface vsi-interface 1
Vsi-interface1
Current state: UP
Line protocol state: UP
Description: Vsi-interface1 Interface
Bandwidth: 1000000kbps
Maximum transmission unit: 1444
Internet address: 10.1.1.1/24 (primary)
IP packet frame type: Ethernet II, hardware address: 0011-2200-0102
IPv6 packet frame type: Ethernet II, hardware address: 0011-2200-0102
Physical: Unknown, baudrate: 1000000 kbps
Last clearing of counters: Never
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
# Verify that the VXLAN tunnels have been assigned to the VXLAN, and VSI-interface 1 is the gateway interface of VSI vpna.
[SwitchB] display l2vpn vsi verbose
VSI Name: vpna
VSI Index : 0
VSI State : Up
MTU : 1500
Bandwidth : -
Broadcast Restrain : -
Multicast Restrain : -
Unknown Unicast Restrain: -
MAC Learning : Enabled
MAC Table Limit : -
MAC Learning rate : -
Drop Unknown : -
Flooding : Enabled
Gateway interface : VSI-interface 1
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel2 0x5000002 Up Manual Disabled
Tunnel3 0x5000003 Up Manual Disabled
# Verify that Switch B has created ARP entries for the VMs.
[SwitchB] display arp
Type: S-Static D-Dynamic O-Openflow R-Rule M-Multiport I-Invalid
IP address MAC address VID Interface/Link ID Aging Type
20.1.1.5 000c-29c1-5e46 N/A Vlan20 19 D
10.1.1.11 0000-1234-0001 N/A Vsi1 20 D
10.1.1.12 0000-1234-0002 N/A Vsi1 19 D
# Verify that Switch B has created FIB entries for the VMs.
[SwitchB] display fib 10.1.1.11
Destination count: 1 FIB entry count: 1
Flag:
U:Useable G:Gateway H:Host B:Blackhole D:Dynamic S:Static
R:Relay F:FRR
Destination/Mask Nexthop Flag OutInterface/Token Label
10.1.1.11/32 10.1.1.11 UH Vsi1 Null
2. Verify that the VMs can access the WAN:
# Verify that VM 1 and VM 2 can ping each other. (Details not shown.)
# Verify that VM 1, VM 2, and VLAN-interface 20 (20.1.1.5) on Switch E can ping each other. (Details not shown.)
Centralized VXLAN IP gateway group configuration example
Network requirements
As shown in Figure 18:
· Configure VXLAN 10 as a unicast-mode VXLAN on Switch A, Switch B, and Switch C.
· Manually establish VXLAN tunnels and assign the tunnels to VXLAN 10.
· Assign Switch B and Switch C to a VTEP group to provide gateway services for VXLAN 10.
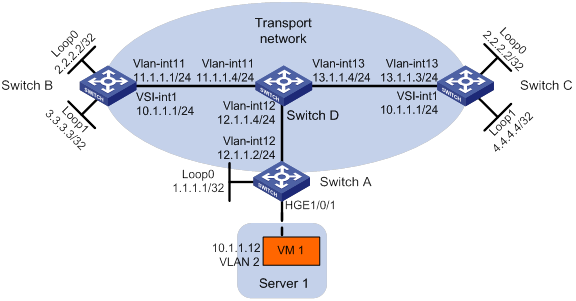
Configuration procedure
1. On VM 1, specify 10.1.1.1 as the gateway address. (Details not shown.)
2. Configure IP addresses and unicast routing settings:
# Assign IP addresses to interfaces, as shown in Figure 18. (Details not shown.)
# Configure OSPF on all transport network switches (Switches A through D). (Details not shown.)
3. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Enable Layer 2 forwarding for VXLANs.
[SwitchA] undo vxlan ip-forwarding
# Create VSI vpna and VXLAN 10.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# Assign an IP address to Loopback 0. The IP address will be used as the source IP address of the VXLAN tunnel to the VTEP group.
[SwitchA] interface loopback 0
[SwitchA-Loopback0] ip address 1.1.1.1 255.255.255.255
[SwitchA-Loopback0] quit
# Create a VXLAN tunnel to the VTEP group. The tunnel interface name is Tunnel 1.
[SwitchA] interface tunnel 1 mode vxlan
[SwitchA-Tunnel1] source 1.1.1.1
[SwitchA-Tunnel1] destination 2.2.2.2
[SwitchA-Tunnel1] quit
# Assign Tunnel 1 to VXLAN 10.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] tunnel 1
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# On HundredGigE 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchA] interface hundredgige 1/0/1
[SwitchA-HundredGigE1/0/1] service-instance 1000
[SwitchA-HundredGigE1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-HundredGigE1/0/1-srv1000] xconnect vsi vpna
[SwitchA-HundredGigE1/0/1-srv1000] quit
[SwitchA-HundredGigE1/0/1] quit
# Specify VTEP group 2.2.2.2 and its member VTEPs at 3.3.3.3 and 4.4.4.4.
[SwitchA] vtep group 2.2.2.2 member remote 3.3.3.3 4.4.4.4
4. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Create VSI vpna and VXLAN 10.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Assign IP address 2.2.2.2/32 to Loopback 0. The IP address will be used as the IP address of the VTEP group.
[SwitchB] interface loopback 0
[SwitchB-Loopback0] ip address 2.2.2.2 255.255.255.255
[SwitchB-Loopback0] quit
# Assign an IP address to Loopback 1. The IP address will be used as the member IP address of the VTEP.
[SwitchB] interface loopback 1
[SwitchB-Loopback1] ip address 3.3.3.3 255.255.255.255
[SwitchB-Loopback1] quit
# Create a VXLAN tunnel to Switch A. The tunnel source IP address is 2.2.2.2, and the tunnel interface name is Tunnel 2.
[SwitchB] interface tunnel 2 mode vxlan
[SwitchB-Tunnel2] source 2.2.2.2
[SwitchB-Tunnel2] destination 1.1.1.1
[SwitchB-Tunnel2] quit
# Assign Tunnel 2 to VXLAN 10.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] tunnel 2
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Create VSI-interface 1 and assign the interface an IP address. The IP address will be used as the gateway address for VXLAN 10. Assign a MAC address to the interface.
[SwitchB] interface vsi-interface 1
[SwitchB-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchB-Vsi-interface1] mac-address 2-2-2
[SwitchB-Vsi-interface1] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] gateway vsi-interface 1
[SwitchB-vsi-vpna] quit
# Assign the local VTEP to VTEP group 2.2.2.2, and specify the member IP address of the local VTEP.
[SwitchB] vtep group 2.2.2.2 member local 3.3.3.3
# Specify the other member VTEP Switch C.
[SwitchB] vtep group 2.2.2.2 member remote 4.4.4.4
5. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Create VSI vpna and VXLAN 10.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] vxlan 10
[SwitchC-vsi-vpna-vxlan-10] quit
[SwitchC-vsi-vpna] quit
# Assign IP address 2.2.2.2/32 to Loopback 0. The IP address will be used as the IP address of the VTEP group.
[SwitchC] interface loopback 0
[SwitchC-Loopback0] ip address 2.2.2.2 255.255.255.255
[SwitchC-Loopback0] quit
# Assign an IP address to Loopback 1. The IP address will be used as the member IP address of the VTEP.
[SwitchC] interface loopback 1
[SwitchC-Loopback1] ip address 4.4.4.4 255.255.255.255
[SwitchC-Loopback1] quit
# Create a VXLAN tunnel to Switch A. The tunnel source IP address is 2.2.2.2, and the tunnel interface name is Tunnel 2.
[SwitchC] interface tunnel 2 mode vxlan
[SwitchC-Tunnel2] source 2.2.2.2
[SwitchC-Tunnel2] destination 1.1.1.1
[SwitchC-Tunnel2] quit
# Assign Tunnel 2 to VXLAN 10.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] vxlan 10
[SwitchC-vsi-vpna-vxlan-10] tunnel 2
[SwitchC-vsi-vpna-vxlan-10] quit
[SwitchC-vsi-vpna] quit
# Create VSI-interface 1 and assign the interface an IP address. The IP address will be used as the gateway address for VXLAN 10. Assign a MAC address to the interface.
[SwitchC] interface vsi-interface 1
[SwitchC-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchC-Vsi-interface1] mac-address 2-2-2
[SwitchC-Vsi-interface1] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] gateway vsi-interface 1
[SwitchC-vsi-vpna] quit
# Assign the local VTEP to VTEP group 2.2.2.2, and specify the member IP address of the local VTEP.
[SwitchC] vtep group 2.2.2.2 member local 4.4.4.4
# Specify the other member VTEP Switch B.
[SwitchC] vtep group 2.2.2.2 member remote 3.3.3.3
Distributed VXLAN IPv4 gateway configuration example
Network requirements
As shown in Figure 19:
· Configure VXLAN 10, VXLAN 20, and VXLAN 30 as unicast-mode VXLANs on Switch A, Switch B, and Switch C to provide connectivity for the VMs across the network sites.
· Manually establish VXLAN tunnels and assign the tunnels to the VXLANs.
· Configure distributed VXLAN IP gateways on Switch A and Switch C to forward traffic between the VXLANs.
· Configure Switch B as a border gateway to forward traffic between the VXLANs and the WAN connected to Switch E.
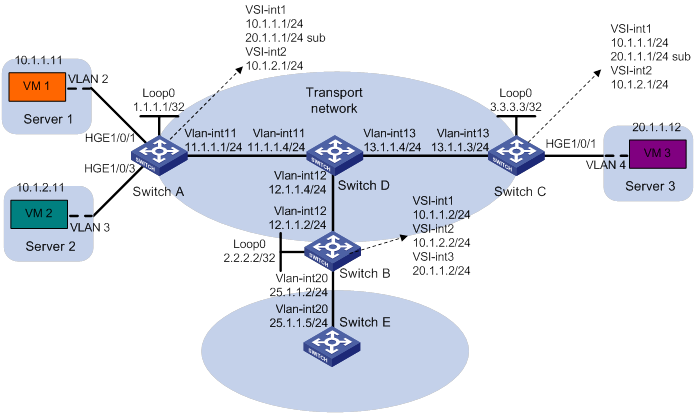
Configuration procedure
1. On VM 1, VM 2, and VM 3, specify 10.1.1.1, 10.1.2.1, and 20.1.1.1 as the gateway address, respectively. (Details not shown.)
2. Configure IP addresses and unicast routing settings:
# Assign IP addresses to interfaces, as shown in Figure 19. (Details not shown.)
# Configure OSPF on all transport network switches (Switches A through D). (Details not shown.)
# Configure OSPF to advertise routes to networks 10.1.1.0/24, 10.1.2.0/24, 20.1.1.0/24, and 25.1.1.0/24 on Switch B and Switch E. (Details not shown.)
3. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Create VSI vpna and VXLAN 10.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# Create VSI vpnb and VXLAN 20.
[SwitchA] vsi vpnb
[SwitchA-vsi-vpnb] vxlan 20
[SwitchA-vsi-vpnb-vxlan-20] quit
[SwitchA-vsi-vpnb] quit
# Create VSI vpnc and VXLAN 30.
[SwitchA] vsi vpnc
[SwitchA-vsi-vpnc] vxlan 30
[SwitchA-vsi-vpnc-vxlan-30] quit
[SwitchA-vsi-vpnc] quit
# Assign an IP address to Loopback 0. The IP address will be used as the source IP address of the VXLAN tunnels to Switch B and Switch C.
[SwitchA] interface loopback 0
[SwitchA-Loopback0] ip address 1.1.1.1 255.255.255.255
[SwitchA-Loopback0] quit
# Create a VXLAN tunnel to Switch B. The tunnel interface name is Tunnel 1.
[SwitchA] interface tunnel 1 mode vxlan
[SwitchA-Tunnel1] source 1.1.1.1
[SwitchA-Tunnel1] destination 2.2.2.2
[SwitchA-Tunnel1] quit
# Create a VXLAN tunnel to Switch C. The tunnel interface name is Tunnel 2.
[SwitchA] interface tunnel 2 mode vxlan
[SwitchA-Tunnel2] source 1.1.1.1
[SwitchA-Tunnel2] destination 3.3.3.3
[SwitchA-Tunnel2] quit
# Assign Tunnel 1 and Tunnel 2 to VXLAN 10.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] tunnel 1
[SwitchA-vsi-vpna-vxlan-10] tunnel 2
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# Assign Tunnel 1 and Tunnel 2 to VXLAN 20.
[SwitchA] vsi vpnb
[SwitchA-vsi-vpnb] vxlan 20
[SwitchA-vsi-vpnb-vxlan-20] tunnel 1
[SwitchA-vsi-vpnb-vxlan-20] tunnel 2
[SwitchA-vsi-vpnb-vxlan-20] quit
[SwitchA-vsi-vpnb] quit
# Assign Tunnel 2 to VXLAN 30.
[SwitchA] vsi vpnc
[SwitchA-vsi-vpnc] vxlan 30
[SwitchA-vsi-vpnc-vxlan-30] tunnel 2
[SwitchA-vsi-vpnc-vxlan-30] quit
[SwitchA-vsi-vpnc] quit
# On HundredGigE 1/0/1, create Ethernet service instance 1000 to match VLAN 2.
[SwitchA] interface hundredgige 1/0/1
[SwitchA-HundredGigE1/0/1] service-instance 1000
[SwitchA-HundredGigE1/0/1-srv1000] encapsulation s-vid 2
# Map Ethernet service instance 1000 to VSI vpna.
[SwitchA-HundredGigE1/0/1-srv1000] xconnect vsi vpna
[SwitchA-HundredGigE1/0/1-srv1000] quit
[SwitchA-HundredGigE1/0/1] quit
# On HundredGigE 1/0/3, create Ethernet service instance 1000 to match VLAN 3.
[SwitchA] interface hundredgige 1/0/3
[SwitchA-HundredGigE1/0/3] service-instance 1000
[SwitchA-HundredGigE1/0/3-srv1000] encapsulation s-vid 3
# Map Ethernet service instance 1000 to VSI vpnb.
[SwitchA-HundredGigE1/0/3-srv1000] xconnect vsi vpnb
[SwitchA-HundredGigE1/0/3-srv1000] quit
[SwitchA-HundredGigE1/0/3] quit
# Create VSI-interface 1 and assign the interface an IP address and a MAC address. The IP address will be used as the gateway address for VXLAN 10.
[SwitchA] interface vsi-interface 1
[SwitchA-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchA-Vsi-interface1] mac-address 1-1-1
# Specify VSI-interface 1 as a distributed gateway and enable local proxy ARP on the interface.
[SwitchA-Vsi-interface1] distributed-gateway local
[SwitchA-Vsi-interface1] local-proxy-arp enable
[SwitchA-Vsi-interface1] quit
# Create VSI-interface 2 and assign the interface an IP address and a MAC address. The IP address will be used as the gateway address for VXLAN 20.
[SwitchA] interface vsi-interface 2
[SwitchA-Vsi-interface2] ip address 10.1.2.1 255.255.255.0
[SwitchA-Vsi-interface2] mac-address 2-2-2
# Specify VSI-interface 2 as a distributed gateway and enable local proxy ARP on the interface.
[SwitchA-Vsi-interface2] distributed-gateway local
[SwitchA-Vsi-interface2] local-proxy-arp enable
[SwitchA-Vsi-interface2] quit
# Enable dynamic ARP entry synchronization for distributed VXLAN IP gateways.
[SwitchA] arp distributed-gateway dynamic-entry synchronize
# Specify VSI-interface 1 as the gateway interface for VSI vpna. Assign subnet 10.1.1.0/24 to the VSI.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] gateway vsi-interface 1
[SwitchA-vsi-vpna] gateway subnet 10.1.1.0 0.0.0.255
[SwitchA-vsi-vpna] quit
# Specify VSI-interface 2 as the gateway interface for VSI vpnb.
[SwitchA] vsi vpnb
[SwitchA-vsi-vpnb] gateway vsi-interface 2
[SwitchA-vsi-vpnb] quit
# Assign a secondary IP address to VSI-interface 1. The IP address will be used as the gateway address for VXLAN 30.
[SwitchA] interface vsi-interface 1
[SwitchA-Vsi-interface1] ip address 20.1.1.1 255.255.255.0 sub
[SwitchA-Vsi-interface1] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpnc. Assign subnet 20.1.1.0/24 to the VSI.
[SwitchA] vsi vpnc
[SwitchA-vsi-vpnc] gateway vsi-interface 1
[SwitchA-vsi-vpnc] gateway subnet 20.1.1.0 0.0.0.255
[SwitchA-vsi-vpnc] quit
# Configure a routing policy for VXLAN 10. Set the policy name to vxlan10, and set the default next hop to 10.1.1.2 (VSI-interface 1 on Switch B).
[SwitchA] acl advanced 3000
[SwitchA-acl-ipv4-adv-3000] rule 0 permit ip
[SwitchA-acl-ipv4-adv-3000] quit
[SwitchA] policy-based-route vxlan10 permit node 5
[SwitchA-pbr-vxlan10-5] if-match acl 3000
[SwitchA-pbr-vxlan10-5] apply default-next-hop 10.1.1.2
[SwitchA-pbr-vxlan10-5] quit
# Configure a routing policy for VXLAN 20. Set the policy name to vxlan20, and set the default next hop to 10.1.2.2 (VSI-interface 2 on Switch B).
[SwitchA] policy-based-route vxlan20 permit node 5
[SwitchA-pbr-vxlan20-5] if-match acl 3000
[SwitchA-pbr-vxlan20-5] apply default-next-hop 10.1.2.2
[SwitchA-pbr-vxlan20-5] quit
# Apply policies vxlan10 and vxlan20 to VSI-interface 1 and VSI-interface 2, respectively.
[SwitchA] interface vsi-interface 1
[SwitchA-Vsi-interface1] ip policy-based-route vxlan10
[SwitchA-Vsi-interface1] quit
[SwitchA] interface vsi-interface 2
[SwitchA-Vsi-interface2] ip policy-based-route vxlan20
[SwitchA-Vsi-interface2] quit
4. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Create VSI vpna and VXLAN 10.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Create VSI vpnb and VXLAN 20.
[SwitchB] vsi vpnb
[SwitchB-vsi-vpnb] vxlan 20
[SwitchB-vsi-vpnb-vxlan-20] quit
[SwitchB-vsi-vpnb] quit
# Create VSI vpnc and VXLAN 30.
[SwitchB] vsi vpnc
[SwitchB-vsi-vpnc] vxlan 30
[SwitchB-vsi-vpnc-vxlan-30] quit
[SwitchB-vsi-vpnc] quit
# Assign an IP address to Loopback 0. The IP address will be used as the source IP address of the VXLAN tunnels to Switch A and Switch C.
[SwitchB] interface loopback 0
[SwitchB-Loopback0] ip address 2.2.2.2 255.255.255.255
[SwitchB-Loopback0] quit
# Create a VXLAN tunnel to Switch A. The tunnel interface name is Tunnel 2.
[SwitchB] interface tunnel 2 mode vxlan
[SwitchB-Tunnel2] source 2.2.2.2
[SwitchB-Tunnel2] destination 1.1.1.1
[SwitchB-Tunnel2] quit
# Create a VXLAN tunnel to Switch C. The tunnel interface name is Tunnel 3.
[SwitchB] interface tunnel 3 mode vxlan
[SwitchB-Tunnel3] source 2.2.2.2
[SwitchB-Tunnel3] destination 3.3.3.3
[SwitchB-Tunnel3] quit
# Assign Tunnel 2 to VXLAN 10.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] tunnel 2
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Assign Tunnel 2 to VXLAN 20.
[SwitchB] vsi vpnb
[SwitchB-vsi-vpnb] vxlan 20
[SwitchB-vsi-vpnb-vxlan-20] tunnel 2
[SwitchB-vsi-vpnb-vxlan-20] quit
[SwitchB-vsi-vpnb] quit
# Assign Tunnel 3 to VXLAN 30.
[SwitchB] vsi vpnc
[SwitchB-vsi-vpnc] vxlan 30
[SwitchB-vsi-vpnc-vxlan-30] tunnel 3
[SwitchB-vsi-vpnc-vxlan-30] quit
[SwitchB-vsi-vpnc] quit
# Create VSI-interface 1 and assign the interface an IP address.
[SwitchB] interface vsi-interface 1
[SwitchB-Vsi-interface1] ip address 10.1.1.2 255.255.255.0
[SwitchB-Vsi-interface1] quit
# Create VSI-interface 2 and assign the interface an IP address.
[SwitchB] interface vsi-interface 2
[SwitchB-Vsi-interface2] ip address 10.1.2.2 255.255.255.0
[SwitchB-Vsi-interface2] quit
# Create VSI-interface 3 and assign the interface an IP address.
[SwitchB] interface vsi-interface 3
[SwitchB-Vsi-interface3] ip address 20.1.1.2 255.255.255.0
[SwitchB-Vsi-interface3] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpna.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] gateway vsi-interface 1
[SwitchB-vsi-vpna] quit
# Specify VSI-interface 2 as the gateway interface for VSI vpnb.
[SwitchB] vsi vpnb
[SwitchB-vsi-vpnb] gateway vsi-interface 2
[SwitchB-vsi-vpnb] quit
# Specify VSI-interface 3 as the gateway interface for VSI vpnc.
[SwitchB] vsi vpnc
[SwitchB-vsi-vpnc] gateway vsi-interface 3
[SwitchB-vsi-vpnc] quit
5. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Create VSI vpna and VXLAN 10.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] vxlan 10
[SwitchC-vsi-vpna-vxlan-10] quit
[SwitchC-vsi-vpna] quit
# Create VSI vpnb and VXLAN 20.
[SwitchC] vsi vpnb
[SwitchC-vsi-vpnb] vxlan 20
[SwitchC-vsi-vpnb-vxlan-20] quit
[SwitchC-vsi-vpnb] quit
# Create VSI vpnc and VXLAN 30.
[SwitchC] vsi vpnc
[SwitchC-vsi-vpnc] vxlan 30
[SwitchC-vsi-vpnc-vxlan-30] quit
[SwitchC-vsi-vpnc] quit
# Assign an IP address to Loopback 0. The IP address will be used as the source IP address of the VXLAN tunnels to Switch A and Switch B.
[SwitchC] interface loopback 0
[SwitchC-Loopback0] ip address 3.3.3.3 255.255.255.255
[SwitchC-Loopback0] quit
# Create a VXLAN tunnel to Switch A. The tunnel interface name is Tunnel 1.
[SwitchC] interface tunnel 1 mode vxlan
[SwitchC-Tunnel1] source 3.3.3.3
[SwitchC-Tunnel1] destination 1.1.1.1
[SwitchC-Tunnel1] quit
# Create a VXLAN tunnel to Switch B. The tunnel interface name is Tunnel 3.
[SwitchC] interface tunnel 3 mode vxlan
[SwitchC-Tunnel3] source 3.3.3.3
[SwitchC-Tunnel3] destination 2.2.2.2
[SwitchC-Tunnel3] quit
# Assign Tunnel 1 to VXLAN 10.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] vxlan 10
[SwitchC-vsi-vpna-vxlan-10] tunnel 1
[SwitchC-vsi-vpna-vxlan-10] quit
[SwitchC-vsi-vpna] quit
# Assign Tunnel 1 to VXLAN 20.
[SwitchC] vsi vpnb
[SwitchC-vsi-vpnb] vxlan 20
[SwitchC-vsi-vpnb-vxlan-20] tunnel 1
[SwitchC-vsi-vpnb-vxlan-20] quit
[SwitchC-vsi-vpnb] quit
# Assign Tunnel 1 and Tunnel 3 to VXLAN 30.
[SwitchC] vsi vpnc
[SwitchC-vsi-vpnc] vxlan 30
[SwitchC-vsi-vpnc-vxlan-30] tunnel 1
[SwitchC-vsi-vpnc-vxlan-30] tunnel 3
[SwitchC-vsi-vpnc-vxlan-30] quit
[SwitchC-vsi-vpnc] quit
# On HundredGigE 1/0/1, create Ethernet service instance 1000 to match VLAN 4.
[SwitchC] interface hundredgige 1/0/1
[SwitchC-HundredGigE1/0/1] service-instance 1000
[SwitchC-HundredGigE1/0/1-srv1000] encapsulation s-vid 4
# Map Ethernet service instance 1000 to VSI vpnc.
[SwitchC-HundredGigE1/0/1-srv1000] xconnect vsi vpnc
[SwitchC-HundredGigE1/0/1-srv1000] quit
[SwitchC-HundredGigE1/0/1] quit
# Create VSI-interface 1 and assign the interface an IP address and a MAC address. The IP address will be used as the gateway address for VXLAN 10.
[SwitchC] interface vsi-interface 1
[SwitchC-Vsi-interface1] ip address 10.1.1.1 255.255.255.0
[SwitchC-Vsi-interface1] mac-address 1-1-1
# Specify VSI-interface 1 as a distributed gateway and enable local proxy ARP on the interface.
[SwitchC-Vsi-interface1] distributed-gateway local
[SwitchC-Vsi-interface1] local-proxy-arp enable
[SwitchC-Vsi-interface1] quit
# Create VSI-interface 2 and assign the interface an IP address and a MAC address. The IP address will be used as the gateway address for VXLAN 20.
[SwitchC] interface vsi-interface 2
[SwitchC-Vsi-interface2] ip address 10.1.2.1 255.255.255.0
[SwitchC-Vsi-interface2] mac-address 2-2-2
# Specify VSI-interface 2 as a distributed gateway and enable local proxy ARP on the interface.
[SwitchC-Vsi-interface2] distributed-gateway local
[SwitchC-Vsi-interface2] local-proxy-arp enable
[SwitchC-Vsi-interface2] quit
# Enable dynamic ARP entry synchronization for distributed VXLAN IP gateways.
[SwitchC] arp distributed-gateway dynamic-entry synchronize
# Specify VSI-interface 1 as the gateway interface for VSI vpna. Assign subnet 10.1.1.0/24 to the VSI.
[SwitchC] vsi vpna
[SwitchC-vsi-vpna] gateway vsi-interface 1
[SwitchC-vsi-vpna] gateway subnet 10.1.1.0 0.0.0.255
[SwitchC-vsi-vpna] quit
# Specify VSI-interface 2 as the gateway interface for VSI vpnb.
[SwitchC] vsi vpnb
[SwitchC-vsi-vpnb] gateway vsi-interface 2
[SwitchC-vsi-vpnb] quit
# Assign a secondary IP address to VSI-interface 1. The IP address will be used as the gateway address for VXLAN 30.
[SwitchC] interface vsi-interface 1
[SwitchC-Vsi-interface1] ip address 20.1.1.1 255.255.255.0 sub
[SwitchC-Vsi-interface1] quit
# Specify VSI-interface 1 as the gateway interface for VSI vpnc. Assign subnet 20.1.1.0/24 to the VSI.
[SwitchC] vsi vpnc
[SwitchC-vsi-vpnc] gateway vsi-interface 1
[SwitchC-vsi-vpnc] gateway subnet 20.1.1.0 0.0.0.255
[SwitchC-vsi-vpnc] quit
# Configure a routing policy for the VXLANs. Set the policy name to vxlan, and set the default next hop to 20.1.1.2 (VSI-interface 1 on Switch B).
[SwitchC] acl advanced 3000
[SwitchC-acl-ipv4-adv-3000] rule 0 permit ip
[SwitchC-acl-ipv4-adv-3000] quit
[SwitchC] policy-based-route vxlan permit node 5
[SwitchC-pbr-vxlan-5] if-match acl 3000
[SwitchC-pbr-vxlan-5] apply default-next-hop 20.1.1.2
[SwitchC-pbr-vxlan-5] quit
# Apply policy vxlan to VSI-interface 1.
[SwitchC] interface vsi-interface1
[SwitchC-Vsi-interface1] ip policy-based-route vxlan
[SwitchC-Vsi-interface1] quit
Verifying the configuration
1. Verify the VXLAN IP gateway settings on Switch A:
# Verify that the VXLAN tunnel interfaces are up on Switch A.
[SwitchA] display interface tunnel 2
Tunnel2
Current state: UP
Line protocol state: UP
Description: Tunnel2 Interface
Bandwidth: 64kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 1.1.1.1, destination 3.3.3.3
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
# Verify that VSI-interface 1 is up.
[SwitchA] display interface vsi-interface 1
Vsi-interface1
Current state: UP
Line protocol state: UP
Description: Vsi-interface1 Interface
Bandwidth: 1000000kbps
Maximum transmission unit: 1444
Internet address: 10.1.1.1/24 (primary)
IP packet frame type: Ethernet II, hardware address: 0001-0001-0001
IPv6 packet frame type: Ethernet II, hardware address: 0001-0001-0001
Physical: Unknown, baudrate: 1000000 kbps
Last clearing of counters: Never
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
# Verify that the VXLAN tunnels have been assigned to VXLAN 10, and VSI-interface 1 is the gateway interface for VSI vpna.
[SwitchA] display l2vpn vsi name vpna verbose
VSI Name: vpna
VSI Index : 0
VSI State : Up
MTU : 1500
Bandwidth : -
Broadcast Restrain : -
Multicast Restrain : -
Unknown Unicast Restrain: -
MAC Learning : Enabled
MAC Table Limit : -
MAC Learning rate : -
Drop Unknown : -
Flooding : Enabled
Gateway Interface : VSI-interface 1
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel1 0x5000001 Up Manual Disabled
Tunnel2 0x5000002 Up Manual Disabled
ACs:
AC Link ID State
HGE1/0/1 srv1000 0 Up
# Verify that Switch A has created ARP entries for the VMs.
[SwitchA] display arp
Type: S-Static D-Dynamic O-Openflow R-Rule M-Multiport I-Invalid
IP address MAC address VID Interface/Link ID Aging Type
11.1.1.4 000c-29c1-5e46 11 Vlan11 19 D
10.1.1.2 0003-0000-0000 N/A Vsi1 20 D
10.1.1.11 0cda-41b5-cf09 N/A Vsi1 20 D
10.1.2.2 0004-0000-0000 N/A Vsi2 20 D
10.1.2.11 0cda-41b5-cf89 N/A Vsi2 20 D
20.1.1.12 0000-fc00-0b01 N/A Vsi1 19 D
2. Verify the configuration on the border gateway Switch B:
# Verify that the VXLAN tunnel interfaces are up on Switch B.
[SwitchB] display interface tunnel 2
Tunnel2
Current state: UP
Line protocol state: UP
Description: Tunnel2 Interface
Bandwidth: 64kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 2.2.2.2, destination 1.1.1.1
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
# Verify that VSI-interface 1 is up.
[SwitchB] display interface vsi-interface 1
Vsi-interface1
Current state: UP
Line protocol state: UP
Description: Vsi-interface1 Interface
Bandwidth: 1000000kbps
Maximum transmission unit: 1444
Internet address: 10.1.1.2/24 (primary)
IP packet frame type: Ethernet II, hardware address: 0011-2200-0102
IPv6 packet frame type: Ethernet II, hardware address: 0011-2200-0102
Physical: Unknown, baudrate: 1000000 kbps
Last clearing of counters: Never
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
# Verify that the VXLAN tunnels have been assigned to VXLAN 10, and VSI-interface 1 is the gateway interface for VSI vpna.
[SwitchB] display l2vpn vsi name vpna verbose
VSI Name: vpna
VSI Index : 0
VSI State : Up
MTU : 1500
Bandwidth : -
Broadcast Restrain : -
Multicast Restrain : -
Unknown Unicast Restrain: -
MAC Learning : Enabled
MAC Table Limit : -
MAC Learning rate : -
Drop Unknown : -
Flooding : Enabled
Gateway interface : VSI-interface 1
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel1 0x5000001 Up Manual Disabled
Tunnel2 0x5000002 Up Manual Disabled
# Verify that Switch B has created ARP entries for the VMs.
[SwitchB] display arp
Type: S-Static D-Dynamic O-Openflow R-Rule M-Multiport I-Invalid
IP address MAC address VID Interface/Link ID Aging Type
12.1.1.4 0000-fc00-00ab 12 Vlan12 14 D
25.1.1.5 4431-9234-24bb 20 Vlan20 17 D
10.1.1.1 0000-fc00-00ab N/A Vsi1 17 D
10.1.1.11 0000-fc00-00ab N/A Vsi1 20 D
10.1.2.1 0000-fc00-00bc N/A Vsi2 17 D
10.1.1.11 0000-fc00-00bc N/A Vsi2 20 D
20.1.1.1 0000-fc00-00aa N/A Vsi3 17 D
20.1.1.12 0000-fc00-00aa N/A Vsi3 20 D
# Verify that Switch B has created FIB entries for the VMs.
[SwitchB] display fib 10.1.1.11
Destination count: 1 FIB entry count: 1
Flag:
U:Useable G:Gateway H:Host B:Blackhole D:Dynamic S:Static
R:Relay F:FRR
Destination/Mask Nexthop Flag OutInterface/Token Label
10.1.1.11/32 10.1.1.11 UH Vsi1 Null
[SwitchB] display fib 20.1.1.12
Destination count: 1 FIB entry count: 1
Flag:
U:Useable G:Gateway H:Host B:Blackhole D:Dynamic S:Static
R:Relay F:FRR
Destination/Mask Nexthop Flag OutInterface/Token Label
20.1.1.12/32 20.1.1.12 UH Vsi1 Null
3. Verify that the network connectivity for VMs meets the requirements:
# Verify that VM 1, VM 2, and VM 3 can ping each other. (Details not shown.)
# Verify that VM 1, VM 2, and VM 3 can ping VLAN-interface 20 (25.1.1.5) on Switch E for WAN access. (Details not shown.)
Configuring the VTEP as an OVSDB VTEP
Overview
An H3C network virtualization controller can use the Open vSwitch Database (OVSDB) management protocol to deploy and manage VXLANs on VTEPs. To work with a controller, you must configure the VTEP as an OVSDB VTEP.
As shown in Figure 20, an OVSDB VTEP stores all of its VXLAN settings in the form of entries in an OVSDB database. The OVSDB database, OVSDB VTEP service, and the controller interact through the OVSDB server. The controller communicates with the OVSDB server through the OVSDB protocol to manage the OVSDB database. The OVSDB VTEP service reads and writes data in the OVSDB database through the OVSDB server.
The OVSDB VTEP service performs the following operations to manage the VXLAN settings on the VTEP:
· Converts data in the OVSDB database into VXLAN configuration and deploys the configuration to the VTEP. For example, create or remove a VXLAN or VXLAN tunnel.
· Adds site-facing interface information and the global source address of VXLAN tunnels to the OVSDB database. The information is reported to the controller by the OVSDB server.
You can configure a VTEP both at the CLI and through a controller. As a best practice, do not manually remove the VXLAN configuration issued by the controller.
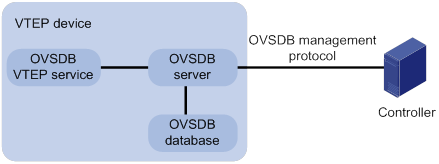
Protocols and standards
RFC 7047, The Open vSwitch Database Management Protocol
OVSDB VTEP configuration task list
|
Tasks at a glance |
|
(Required.) Setting up an OVSDB connection to a controller: |
|
(Required.) Enabling the OVSDB server |
|
(Required.) Enabling the OVSDB VTEP service |
|
(Required.) Specifying a global source address for VXLAN tunnels |
|
(Required.) Specifying a VTEP access port |
|
(Optional.) Enabling flood proxy on multicast VXLAN tunnels |
Configuration prerequisites
Before you configure the VTEP as an OVSDB VTEP, enable L2VPN by using the l2vpn enable command.
Setting up an OVSDB connection to a controller
The OVSDB server supports the following types of OVSDB connections:
· Active TCP connection—The OVSDB server initiates a TCP connection to the controller.
· Passive TCP connection—The OVSDB server accepts the TCP connection from the controller.
Configuration restrictions and guidelines
You can set up multiple OVSDB connections. For the device to establish the connections, you must enable the OVSDB server. You must disable and then re-enable the OVSDB server if it has been enabled.
Configuring active TCP connection settings
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Set up an active TCP connection. |
ovsdb server tcp ip ip-address port port-number |
By default, the device does not have active OVSDB TCP connections. You can set up a maximum of eight active OVSDB TCP connections. |
Configuring passive TCP connection settings
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable the device to listen for TCP connection requests. |
ovsdb server ptcp [ port port-number ] |
By default, the device does not listen for TCP connection requests. You can specify only one port to listen for OVSDB TCP connection requests. Port 6640 is used if you do specify a port when you execute the command. |
Enabling the OVSDB server
Make sure you have complete OVSDB connection setup before you enable the OVSDB server. If you change OVSDB connection settings after the OVSDB server is enabled, you must disable and then re-enable the OVSDB server for the change to take effect.
To enable the OVSDB server:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable the OVSDB server. |
ovsdb server enable |
By default, the OVSDB server is disabled. |
Enabling the OVSDB VTEP service
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable the OVSDB VTEP service. |
vtep enable |
By default, the OVSDB VTEP service is disabled. |
Specifying a global source address for VXLAN tunnels
|
|
IMPORTANT: For correct VXLAN deployment and VTEP management, do not manually specify tunnel-specific source addresses for VXLAN tunnels if OVSDB is used. |
The VTEP reports the global VXLAN tunnel source address to the controller for VXLAN tunnel setup.
To specify a global source address for VXLAN tunnels:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Specify a global source address for VXLAN tunnels. |
tunnel global source-address ip-address |
By default, no global source address is specified for VXLAN tunnels. |
Specifying a VTEP access port
For the controller to manage a site-facing interface, you must specify the interface as a VTEP access port.
To specify a VTEP access port:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
·
Enter Layer 2 Ethernet interface view: ·
Enter Layer 2 aggregate interface view: |
N/A |
|
3. Specify the interface as a VTEP access port. |
vtep access port |
By default, an interface is not a VTEP access port. |
Enabling flood proxy on multicast VXLAN tunnels
If you use a flood proxy server, you must enable flood proxy globally on multicast tunnels. Then the multicast tunnels are converted into flood proxy tunnels. The VTEP sends broadcast, multicast, and unknown unicast traffic for a VXLAN to the flood proxy server through the tunnels. The flood proxy server then replicates and forwards flood traffic to remote VTEPs.
To enable flood proxy on multicast VXLAN tunnels:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enable flood proxy on multicast VXLAN tunnels. |
vxlan tunnel flooding-proxy |
By default, flood proxy is disabled on multicast VXLAN tunnels. |
OVSDB VTEP configuration examples
Unicast-mode VXLAN configuration example
Network requirements
As shown in Figure 21, configure the controller cluster to deploy unicast-mode VXLAN 10 to Switch A, Switch B, and Switch C to provide Layer 2 connectivity for the VMs across the network sites.
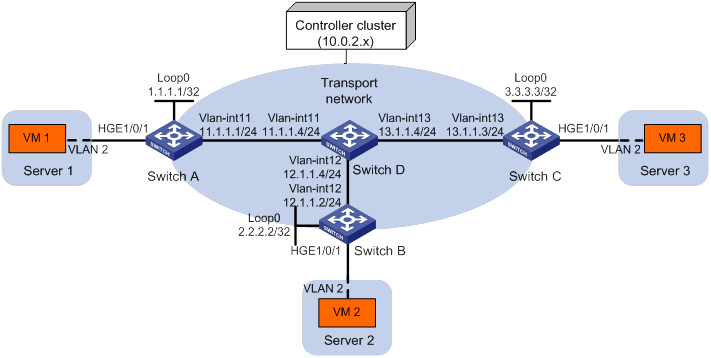
Configuration procedure
1. Configure IP addresses and unicast routing settings:
# Assign IP addresses to interfaces, as shown in Figure 21. (Details not shown.)
# Configure OSPF on all transport network switches (Switches A through D). (Details not shown.)
2. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Configure active TCP connection settings.
[SwitchA] ovsdb server tcp ip 10.0.2.15 port 6632
# Enable the OVSDB server.
[SwitchA] ovsdb server enable
# Enable the OVSDB VTEP service.
[SwitchA] vtep enable
# Assign an IP address to Loopback 0. Specify the IP address as the global source address for VXLAN tunnels.
[SwitchA] interface loopback 0
[SwitchA-LoopBack0] ip address 1.1.1.1 255.255.255.255
[SwitchA-LoopBack0] quit
[SwitchA] tunnel global source-address 1.1.1.1
# Specify site-facing interface HundredGigE 1/0/1 as a VTEP access port.
[SwitchA] interface hundredgige 1/0/1
[SwitchA-HundredGigE1/0/1] vtep access port
[SwitchA-HundredGigE1/0/1] quit
3. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Configure active TCP connection settings.
[SwitchB] ovsdb server tcp 10.0.2.15 port 6632
# Enable the OVSDB server.
[SwitchB] ovsdb server enable
# Enable the OVSDB VTEP service.
[SwitchB] vtep enable
# Assign an IP address to Loopback 0. Specify the IP address as the global source address for VXLAN tunnels.
[SwitchB] interface loopback 0
[SwitchB-LoopBack0] ip address 2.2.2.2 255.255.255.255
[SwitchB-LoopBack0] quit
[SwitchB] tunnel global source-address 2.2.2.2
# Specify site-facing interface HundredGigE 1/0/1 as a VTEP access port.
[SwitchB] interface hundredgige 1/0/1
[SwitchB-HundredGigE1/0/1] vtep access port
[SwitchB-HundredGigE1/0/1] quit
4. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Configure active TCP connection settings.
[SwitchC] ovsdb server tcp ip 10.0.2.15 port 6632
# Enable the OVSDB server.
[SwitchC] ovsdb server enable
# Enable the OVSDB VTEP service.
[SwitchC] vtep enable
# Assign an IP address to Loopback 0. Specify the IP address as the global source address for VXLAN tunnels.
[SwitchC] interface loopback 0
[SwitchC-LoopBack0] ip address 3.3.3.3 255.255.255.255
[SwitchC-LoopBack0] quit
[SwitchC] tunnel global source-address 3.3.3.3
# Specify site-facing interface HundredGigE 1/0/1 as a VTEP access port.
[SwitchC] interface hundredgige 1/0/1
[SwitchC-HundredGigE1/0/1] vtep access port
[SwitchC-HundredGigE1/0/1] quit
5. Configure VXLAN settings on the controller. (Details not shown.)
Verifying the configuration
1. Verify the VXLAN settings on the VTEPs. This example uses Switch A.
# Verify that the VXLAN tunnel interfaces on the VTEP are up.
[SwitchA] display interface tunnel 1
Tunnel1
Current state: UP
Line protocol state: UP
Description: Tunnel1 Interface
Bandwidth: 64kbps
Maximum transmission unit: 1464
Internet protocol processing: Disabled
Last clearing of counters: Never
Tunnel source 1.1.1.1, destination 2.2.2.2
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
# Verify that the VXLAN tunnels have been assigned to the VXLAN.
[SwitchA] display l2vpn vsi verbose
VSI Name: evpn2014
VSI Index : 0
VSI State : Up
MTU : 1500
Bandwidth : -
Broadcast Restrain : -
Multicast Restrain : -
Unknown Unicast Restrain: -
MAC Learning : Enabled
MAC Table Limit : -
MAC Learning rate : -
Drop Unknown : -
Flooding : Enabled
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel1 0x5000001 Up Manual Disabled
Tunnel2 0x5000002 Up Manual Disabled
ACs:
AC Link ID State
HGE1/0/1 srv2 0 Up
# Verify that the VTEP has learned the MAC addresses of remote VMs.
<SwitchA> display l2vpn mac-address
MAC Address State VSI Name Link ID/Name Aging
cc3e-5f9c-6cdb Dynamic evpn2014 Tunnel1 Aging
cc3e-5f9c-23dc Dynamic evpn2014 Tunnel2 Aging
--- 2 mac address(es) found ---
2. Verify that VM 1, VM 2, and VM 3 can ping each other. (Details not shown.)
Flood proxy VXLAN configuration example
Network requirements
As shown in Figure 22:
· Configure the controller cluster to deploy VXLAN 10 to Switch A, Switch B, and Switch C to provide Layer 2 connectivity for the VMs across the network sites.
· Enable flood proxy for VXLAN 10.
· Use the MAC address entries issued by the controller to direct traffic forwarding on Switch A, Switch B, and Switch C.
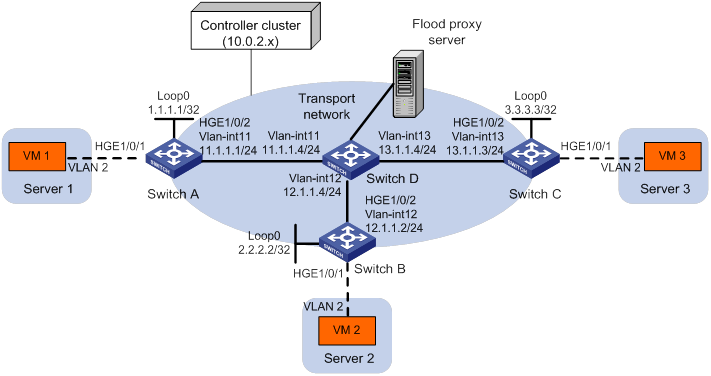
Configuration procedure
1. Configure IP addresses and unicast routing settings:
# Assign IP addresses to interfaces, as shown in Figure 22. (Details not shown.)
# Configure OSPF on all transport network switches (Switches A through D). (Details not shown.)
2. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Configure active TCP connection settings.
[SwitchA] ovsdb server tcp ip 10.0.2.15 port 6632
# Enable the OVSDB server.
[SwitchA] ovsdb server enable
# Enable the OVSDB VTEP service.
[SwitchA] vtep enable
# Assign an IP address to Loopback 0.
[SwitchA] interface loopback 0
[SwitchA-LoopBack0] ip address 1.1.1.1 255.255.255.255
[SwitchA-LoopBack0] quit
# Specify the IP address of Loopback 0 as the global source address for VXLAN tunnels.
[SwitchA] tunnel global source-address 1.1.1.1
# Specify site-facing interface HundredGigE 1/0/1 as a VTEP access port.
[SwitchA] interface hundredgige 1/0/1
[SwitchA-HundredGigE1/0/1] vtep access port
[SwitchA-HundredGigE1/0/1] quit
# Disable source MAC check on transport-facing interface HundredGigE 1/0/2.
[SwitchA] interface hundredgige 1/0/2
[SwitchA-HundredGigE1/0/2] undo mac-address static source-check enable
[SwitchA-HundredGigE1/0/2] quit
# Disable remote-MAC address learning.
[SwitchA] vxlan tunnel mac-learning disable
# Enable flood proxy on multicast VXLAN tunnels.
[SwitchA] vxlan tunnel flooding-proxy
3. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Configure active TCP connection settings.
[SwitchB] ovsdb server tcp ip 10.0.2.15 port 6632
# Enable the OVSDB server.
[SwitchB] ovsdb server enable
# Enable the OVSDB VTEP service.
[SwitchB] vtep enable
# Assign an IP address to Loopback 0.
[SwitchB] interface loopback 0
[SwitchB-LoopBack0] ip address 2.2.2.2 255.255.255.255
[SwitchB-LoopBack0] quit
# Specify the IP address of Loopback 0 as the global source address for VXLAN tunnels.
[SwitchB] tunnel global source-address 2.2.2.2
# Specify site-facing interface HundredGigE 1/0/1 as a VTEP access port.
[SwitchB] interface hundredgige 1/0/1
[SwitchB-HundredGigE1/0/1] vtep access port
[SwitchB-HundredGigE1/0/1] quit
# Disable source MAC check on transport-facing interface HundredGigE 1/0/2.
[SwitchB] interface hundredgige 1/0/2
[SwitchB-HundredGigE1/0/2] undo mac-address static source-check enable
[SwitchB-HundredGigE1/0/2] quit
# Disable remote-MAC address learning.
[SwitchB] vxlan tunnel mac-learning disable
# Enable flood proxy on multicast VXLAN tunnels.
[SwitchB] vxlan tunnel flooding-proxy
4. Configure Switch C:
# Enable L2VPN.
<SwitchC> system-view
[SwitchC] l2vpn enable
# Configure active TCP connection settings.
[SwitchC] ovsdb server tcp 10.0.2.15 port 6632
# Enable the OVSDB server.
[SwitchC] ovsdb server enable
# Enable the OVSDB VTEP service.
[SwitchC] vtep enable
# Assign an IP address to Loopback 0.
[SwitchC] interface loopback 0
[SwitchC-LoopBack0] ip address 3.3.3.3 255.255.255.255
[SwitchC-LoopBack0] quit
# Specify the IP address of Loopback 0 as the global source address for VXLAN tunnels.
[SwitchC] tunnel global source-address 3.3.3.3
# Specify site-facing interface HundredGigE 1/0/1 as a VTEP access port.
[SwitchC] interface hundredgige 1/0/1
[SwitchC-HundredGigE1/0/1] vtep access port
[SwitchC-HundredGigE1/0/1] quit
# Disable source MAC check on transport-facing interface HundredGigE 1/0/2.
[SwitchC] interface hundredgige 1/0/2
[SwitchC-HundredGigE1/0/2] undo mac-address static source-check enable
[SwitchC-HundredGigE1/0/2] quit
# Disable remote-MAC address learning.
[SwitchC] vxlan tunnel mac-learning disable
# Enable flood proxy on multicast VXLAN tunnels.
[SwitchC] vxlan tunnel flooding-proxy
5. Configure VXLAN settings on the controller, and configure the flood proxy server. (Details not shown.)
Verifying the configuration
1. Verify the VXLAN settings on the VTEPs. This example uses Switch A.
# Verify that the VXLAN tunnel interfaces on the VTEP are up.
[SwitchA] display interface tunnel
Tunnel1
Current state: UP
Line protocol state: UP
Description: Tunnel1 Interface
Bandwidth: 64kbps
Maximum transmission unit: 1464
Internet protocol processing: disabled
Last clearing of counters: Never
Tunnel source 1.1.1.1, destination 2.2.2.2
Tunnel protocol/transport UDP_VXLAN/IP
Last 300 seconds input rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Last 300 seconds output rate: 0 bytes/sec, 0 bits/sec, 0 packets/sec
Input: 0 packets, 0 bytes, 0 drops
Output: 0 packets, 0 bytes, 0 drops
# Verify that the VXLAN tunnels have been assigned to the VXLAN, and flood proxy has been enabled on the multicast VXLAN tunnel.
[SwitchA] display l2vpn vsi verbose
VSI Name: evpn2014
VSI Index : 0
VSI State : Up
MTU : 1500
Bandwidth : -
Broadcast Restrain : -
Multicast Restrain : -
Unknown Unicast Restrain: -
MAC Learning : Enabled
MAC Table Limit : -
MAC Learning rate : -
Drop Unknown : -
Flooding : Enabled
VXLAN ID : 10
Tunnels:
Tunnel Name Link ID State Type Flood proxy
Tunnel1 0x5000001 Up Manual Disabled
Tunnel2 0x5000002 Up Manual Disabled
Tunnel3 0x5000003 Up Manual Enabled
ACs:
AC Link ID State
HGE1/0/1 srv2 0 Up
# Verify that the VTEP has obtained the MAC addresses of remote VMs from the controller.
<SwitchA> display l2vpn mac-address
MAC Address State VSI Name Link ID/Name Aging
cc3e-5f9c-6cdb OVSDB evpn2014 Tunnel1 NotAging
cc3e-5f9c-23dc OVSDB evpn2014 Tunnel2 NotAging
--- 2 mac address(es) found ---
2. Verify that VM 1, VM 2, and VM 3 can ping each other. (Details not shown.)
A
access port
VXLAN VTEP access port, 70
active
VXLAN OVSDB TCP connection, 69
address
VXLAN MAC address entry management, 15
ARP
VXLAN ARP flood suppression, 7, 20
VXLAN flood confine (Ethernet service instance), 19
VXLAN local flood confine, 18
assigning
VXLAN traffic assignment, 3
VXLAN tunnel, 13
C
changing
VXLAN local MAC change logging, 15
checking
VXLAN packet check, 20
configuring
VXLAN (multicast mode), 16, 28
VXLAN (unicast mode), 24
VXLAN basics, 10, 24
VXLAN IP gateway, 36, 47
VXLAN IP gateway (centralized), 42, 47
VXLAN IP gateway (distributed), 45
VXLAN IP gateway group (centralized), 52
VXLAN IP gateway VTEP group (centralized), 43
VXLAN IPv4 gateway (distributed), 56
VXLAN OVSDB TCP connection (active), 69
VXLAN OVSDB TCP connection (passive), 69
VXLAN OVSDB VTEP, 68, 68, 71
VXLAN OVSDB VTEP (flood proxy), 74
VXLAN OVSDB VTEP (unicast mode), 71
VXLAN packet check, 20
VXLAN packet statistics, 21
VXLAN static remote-MAC address entry, 15
VXLAN tunnel, 12
VXLAN VSI interface, 46
VXLAN VTEP (IGMP host method), 18
VXLAN VTEP (PIM method), 17
VXLAN VTEP IP gateway group (centralized), 43
confining
VXLAN flood (Ethernet service instance), 19
VXLAN local flood, 18
connecting
VXLAN OVSDB controller connection, 69
VXLAN OVSDB TCP connection (active), 69
VXLAN OVSDB TCP connection (passive), 69
creating
VXLAN on VSI, 11
D
disabling
VXLAN remote ARP learning, 21
VXLAN remote-MAC address learning, 16
displaying
VXLAN, 23
VXLAN IP gateway, 47
E
enabling
multicast VXLAN tunnel flood proxy, 71
VXLAN ARP flood suppression, 20
VXLAN local MAC change logging, 15
VXLAN OVSDB service, 70
VXLAN OVSDB VTEP service, 70
VXLAN packet statistics (Ethernet service instance), 21
VXLAN packet statistics (VSI), 21
VXLAN software-based MAC learning, 16
VXLAN VSI interface packet statistics, 47
Ethernet
VXLAN Ethernet service instance > VSI mapping, 13
VXLAN network model, 1
VXLAN overview, 1
VXLAN packet statistics (Ethernet service instance), 21
VXLAN VSI access mode, 7
F
flooding
multicast VXLAN tunnel flood proxy, 71
VXLAN ARP flood suppression, 7, 20
VXLAN flood confine (Ethernet service instance), 19
VXLAN local flood confine, 18
VXLAN OVSDB VTEP configuration (flood proxy), 74
VXLAN traffic forwarding flood process, 4, 5
format
VXLAN packet format, 2
forwarding
VXLAN forwarding mode, 11
VXLAN traffic forwarding, 4
VXLAN tunnel assignment, 13
frame
VXLAN flood confine (Ethernet service instance), 19
VXLAN local flood confine, 18, 18
G
gateway
VXLAN IP gateway, 8
VXLAN IP gateway configuration, 36, 47
VXLAN IP gateway configuration (centralized), 42, 47
VXLAN IP gateway configuration (distributed), 45
VXLAN IP gateway group configuration (centralized), 52
VXLAN IPv4 gateway configuration (distributed), 56
VXLAN VTEP IP gateway group configuration (centralized), 43
global
VXLAN tunnel global source address, 70
I
IGMP
VXLAN multicast mode configuration, 16
VXLAN VTEP configuration (IGMP host method), 18
IP routing
VXLAN ARP flood suppression, 7
VXLAN IP gateway, 8
VXLAN IP gateway (centralized), 37
VXLAN IP gateway (distributed), 39
VXLAN IP gateway (separated from VTEP), 36
VXLAN IP gateway configuration, 36, 47
VXLAN IP gateway configuration (centralized), 42, 47
VXLAN IP gateway configuration (distributed), 45
VXLAN IP gateway group configuration (centralized), 52
VXLAN IPv4 gateway configuration (distributed), 56
VXLAN VSI interface configuration, 46
VXLAN VTEP IP gateway group (centralized), 38
VXLAN VTEP IP gateway group configuration (centralized), 43
IPv4
VXLAN IPv4 gateway configuration (distributed), 56
VXLAN network model, 1
VXLAN overview, 1
L
Layer 2
VXLAN network model, 1
VXLAN overview, 1
Layer 3
VXLAN IP gateway (centralized), 37
VXLAN IP gateway (distributed), 39
VXLAN IP gateway (separated from VTEP), 36
VXLAN IP gateway configuration, 36, 47
VXLAN IP gateway configuration (centralized), 42, 47
VXLAN IP gateway configuration (distributed), 45
VXLAN IP gateway group configuration (centralized), 52
VXLAN IPv4 gateway configuration (distributed), 56
VXLAN VSI interface configuration, 46
VXLAN VTEP IP gateway group (centralized), 38
VXLAN VTEP IP gateway group configuration (centralized), 43
learning
VXLAN MAC address learning, 3
VXLAN remote ARP learning, 21
VXLAN remote-MAC address learning, 16
VXLAN software-based MAC learning, 16
local
VXLAN local MAC change logging, 15
logging
VXLAN local MAC change logging, 15
M
MAC
VXLAN remote ARP learning, 21
MAC addressing
VXLAN local MAC change logging, 15
VXLAN MAC address entry management, 15
VXLAN MAC address learning, 3
VXLAN remote-MAC address learning, 16
VXLAN software-based MAC learning, 16
VXLAN static remote-MAC address entry, 15
MAC-in-UDP
VXLAN ARP flood suppression, 7
VXLAN basic configuration, 10, 24
VXLAN configuration (multicast mode), 28
VXLAN configuration (unicast mode), 24
VXLAN flood confine (Ethernet service instance), 19
VXLAN local flood confine, 18
VXLAN network model, 1
VXLAN overview, 1
VXLAN OVSDB VTEP configuration, 68, 68, 71
maintaining
VXLAN, 23
VXLAN IP gateway, 47
managing
VXLAN MAC address entries, 15
VXLAN packet statistics (VSI), 21
manual
VXLAN tunnel configuration, 12
mapping
VXLAN Ethernet service instance > VSI, 13
mode
VXLAN configuration (multicast), 16
VXLAN forwarding, 11
VXLAN hardware resource allocation mode, 22
VXLAN OVSDB VTEP configuration (unicast mode), 71
VXLAN VSI access, 7
multicast
VXLAN configuration (multicast mode), 28
VXLAN mode configuration, 16
VXLAN traffic forwarding flood process, 5
VXLAN tunnel flood proxy, 71
N
network
multicast VXLAN tunnel flood proxy, 71
VXLAN ARP flood suppression, 7, 20
VXLAN basic configuration, 10, 24
VXLAN configuration (multicast mode), 16, 28
VXLAN configuration (unicast mode), 24
VXLAN creation on VSI, 11
VXLAN Ethernet service instance > VSI mapping, 13
VXLAN flood confine (Ethernet service instance), 19
VXLAN IP gateway, 8
VXLAN IP gateway (centralized), 37
VXLAN IP gateway (distributed), 39
VXLAN IP gateway (separated from VTEP), 36
VXLAN IP gateway configuration, 47
VXLAN IP gateway configuration (centralized), 42, 47
VXLAN IP gateway configuration (distributed), 45
VXLAN IP gateway group configuration (centralized), 52
VXLAN IPv4 gateway configuration (distributed), 56
VXLAN local flood confine, 18
VXLAN MAC address entry management, 15
VXLAN model, 1
VXLAN OVSDB server enable, 70
VXLAN OVSDB VTEP configuration, 68, 68, 71
VXLAN OVSDB VTEP configuration (flood proxy), 74
VXLAN OVSDB VTEP configuration (unicast mode), 71
VXLAN packet statistics, 21
VXLAN remote VM reachability test, 23
VXLAN tunnel assignment, 13
VXLAN tunnel configuration, 12
VXLAN tunnel global source address, 70
VXLAN VSI interface configuration, 46
VXLAN VSI interface packet statistics, 47
VXLAN VTEP configuration (IGMP host method), 18
VXLAN VTEP configuration (PIM method), 17
VXLAN VTEP IP gateway group (centralized), 38
VXLAN VTEP IP gateway group configuration (centralized), 43
network management
VXLAN IP gateway configuration, 36
VXLAN overview, 1
VXLAN OVSDB VTEP configuration, 68, 68, 71
NMM
VXLAN basic configuration, 10, 24
O
Open vSwitch Database. Use OVSDB
controller connection setup, 69
controller connection setup restrictions, 69
protocols and standards, 68
server enable, 70
TCP connection (active), 69
TCP connection (passive), 69
VTEP access port, 70
VTEP configuration, 68, 68, 71
VTEP configuration (flood proxy), 74
VTEP configuration (unicast mode), 71
VTEP service enable, 70
P
packet
VXLAN packet check, 20
VXLAN packet destination UDP port, 19
VXLAN packet format, 2
VXLAN packet statistics, 21
VXLAN packet statistics (VSI), 21
VXLAN traffic forwarding, 4
VXLAN VSI access mode, 7
VXLAN VSI interface packet statistics, 47
passive
VXLAN OVSDB TCP connection, 69
PIM
VXLAN multicast mode configuration, 16
VXLAN VTEP configuration (PIM method), 17
port
VXLAN packet destination UDP port, 19
VXLAN VTEP access port, 70
procedure
assigning VXLAN tunnel, 13
configuring VXLAN (multicast mode), 16, 28
configuring VXLAN (unicast mode), 24
configuring VXLAN basics, 10
configuring VXLAN IP gateway (centralized), 42, 47
configuring VXLAN IP gateway (distributed), 45
configuring VXLAN IP gateway group (centralized), 52
configuring VXLAN IP gateway VTEP group (centralized), 43
configuring VXLAN IPv4 gateway (distributed), 56
configuring VXLAN OVSDB TCP connection (active), 69
configuring VXLAN OVSDB TCP connection (passive), 69
configuring VXLAN OVSDB VTEP, 68, 68, 68
configuring VXLAN OVSDB VTEP (flood proxy), 74
configuring VXLAN OVSDB VTEP (unicast mode), 71
configuring VXLAN packet check, 20
configuring VXLAN packet statistics, 21
configuring VXLAN static remote-MAC address entry, 15
configuring VXLAN tunnel, 12
configuring VXLAN VSI interface, 46
configuring VXLAN VTEP (IGMP host method), 18
configuring VXLAN VTEP (PIM method), 17
configuring VXLAN VTEP IP gateway group (centralized), 43
confining VXLAN flood (Ethernet service instance), 19
confining VXLAN local flood, 18
creating VXLAN on VSI, 11
disabling VXLAN remote ARP learning, 21
disabling VXLAN remote-MAC address learning, 16
displaying VXLAN, 23
displaying VXLAN IP gateway, 47
enabling multicast VXLAN tunnel flood proxy, 71
enabling VXLAN ARP flood suppression, 20
enabling VXLAN local MAC change logging, 15
enabling VXLAN OVSDB service, 70
enabling VXLAN OVSDB VTEP service, 70
enabling VXLAN packet statistics (Ethernet service instance), 21
enabling VXLAN packet statistics (VSI), 21
enabling VXLAN software-based MAC learning, 16
enabling VXLAN VSI interface packet statistics, 47
maintaining VXLAN, 23
maintaining VXLAN IP gateway, 47
managing VXLAN MAC address entries, 15
mapping VXLAN Ethernet service instance > VSI, 13
setting up VXLAN OVSDB controller connection, 69
setting VXLAN forwarding mode, 11
setting VXLAN hardware resource allocation mode, 22
setting VXLAN packet destination UDP port, 19
specifying VXLAN tunnel global source address, 70
specifying VXLAN VTEP access port, 70
specifying VXLAN VTEP group IP gateway (centralized), 44
testing VXLAN remote VM reachability, 23
protocols and standards
OVSDB, 68
VXLAN, 9
proxying
multicast VXLAN tunnel flood proxy, 71
VXLAN OVSDB VTEP configuration (flood proxy), 74
VXLAN traffic forwarding flood proxy mode, 5
R
reachability
VXLAN remote VM reachability test, 23
remote
VXLAN remote-MAC address learning, 16
VXLAN static remote-MAC address entry, 15
restrictions
OVSDB controller connection setup, 69
VXLAN configuration, 10
VXLAN IP gateway configuration, 42
S
server
VXLAN OVSDB server enable, 70
service instance
VXLAN Ethernet service instance > VSI mapping, 13
setting
VXLAN forwarding mode, 11
VXLAN hardware resource allocation mode, 22
VXLAN packet destination UDP port, 19
setting up
VXLAN OVSDB controller connection, 69
specifying
VXLAN tunnel global source address, 70
VXLAN VTEP access port, 70
VXLAN VTEP group IP gateway (centralized), 44
static
VXLAN static remote-MAC address entry, 15
statistics
VXLAN packet statistics, 21
VXLAN packet statistics (VSI), 21
VXLAN VSI interface packet statistics, 47
suppressing
VXLAN ARP flood suppression, 7, 20
T
TCP
VXLAN OVSDB TCP connection (active), 69
VXLAN OVSDB TCP connection (passive), 69
testing
VXLAN remote VM reachability, 23
traffic
VXLAN basic configuration, 10, 24
VXLAN forwarding mode, 11
VXLAN MAC address learning, 3
VXLAN traffic assignment, 3
VXLAN traffic forwarding, 4
tunneling
VXLAN basic configuration, 10, 24
VXLAN network model, 1
VXLAN tunnel assignment, 13
VXLAN tunnel configuration, 12
VXLAN tunnel global source address, 70
U
UDP
VXLAN packet check, 20
VXLAN packet destination UDP port, 19
unicast
VXLAN configuration (unicast mode), 24
VXLAN OVSDB VTEP configuration (unicast mode), 71
VXLAN traffic forwarding, 4, 4
VXLAN traffic forwarding flood process, 5
V
Virtual eXtensible LAN. Use VXLAN
virtual machine
VXLAN remote VM reachability test, 23
VLAN
VXLAN packet check, 20
VXLAN VSI access mode, 7
VSI
VXLAN creation on VSI, 11
VXLAN Ethernet service instance > VSI mapping, 13
VXLAN network model, 1
VXLAN VSI access mode, 7
VXLAN VSI interface configuration, 46
VXLAN VSI interface packet statistics, 47
VTEP
access port, 70
VXLAN IP gateway (centralized), 37
VXLAN IP gateway (distributed), 39
VXLAN IP gateway (separated from VTEP), 36
VXLAN IP gateway configuration, 47
VXLAN IP gateway configuration (centralized), 42, 47
VXLAN IP gateway configuration (distributed), 45
VXLAN IP gateway group configuration (centralized), 52
VXLAN IP gateway VTEP group configuration (centralized), 43
VXLAN IPv4 gateway configuration (distributed), 56
VXLAN OVSDB controller connection, 69
VXLAN OVSDB VTEP configuration, 68, 68, 71
VXLAN OVSDB VTEP service enable, 70
VXLAN VTEP configuration (IGMP host method), 18
VXLAN VTEP configuration (PIM method), 17
VXLAN VTEP group IP gateway (centralized), 44
VXLAN VTEP IP gateway group (centralized), 38
VXLAN VTEP IP gateway group configuration (centralized), 43
ARP flood suppression, 7
ARP flood suppression enable, 20
basic configuration, 10, 24
configuration (multicast mode), 16, 28
configuration (unicast mode), 24
configuration restrictions, 10
creation on VSI, 11
display, 23
Ethernet service instance > VSI mapping, 13
flood confine (Ethernet service instance), 19
forwarding mode, 11
how it works, 3
IP gateway, 8
IP gateway (centralized), 37
IP gateway (distributed), 39
IP gateway (separated from VTEP), 36
IP gateway configuration, 36, 47
IP gateway configuration (centralized), 42, 47
IP gateway configuration (distributed), 45
IP gateway configuration restrictions, 42
IP gateway display, 47
IP gateway group configuration (centralized), 52
IP gateway maintain, 47
IP gateway VTEP group configuration (centralized), 43
IPv4 gateway configuration (distributed), 56
local flood confine, 18
local MAC change logging, 15
MAC address entry management, 15
MAC address learning, 3
maintain, 23
multicast tunnel flood proxy, 71
network model, 1
overview, 1
OVSDB controller connection, 69
OVSDB controller connection setup restrictions, 69
OVSDB protocols and standards, 68
OVSDB server enable, 70
OVSDB TCP connection (active), 69
OVSDB TCP connection (passive), 69
OVSDB VTEP configuration, 68, 68, 71
OVSDB VTEP configuration (flood proxy), 74
OVSDB VTEP configuration (unicast mode), 71
OVSDB VTEP service enable, 70
packet check configuration, 20
packet destination UDP port, 19
packet format, 2
packet statistics (Ethernet service instance), 21
packet statistics (VSI), 21
packet statistics configuration, 21
protocols and standards, 9
remote VM reachability test, 23
remote-MAC address learning, 16
software-based MAC learning, 16
static remote-MAC address entry, 15
traffic assignment, 3
traffic forwarding, 4
tunnel assignment, 13
tunnel configuration, 12
tunnel global source address, 70
VSI access mode, 7
VSI interface configuration, 46
VTEP access port, 70
VTEP configuration (IGMP host method), 18
VTEP configuration (PIM method), 17
VTEP group IP gateway (centralized), 44
VTEP IP gateway group (centralized), 38
VTEP IP gateway group configuration (centralized), 43
