- Released At: 12-05-2025
- Page Views:
- Downloads:
- Table of Contents
- Related Documents
-
|
|
|
RIPng Technology White Paper |
|
|
|
|
|
|
Copyright © 2021 New H3C Technologies Co., Ltd. All rights reserved.
No part of this manual may be reproduced or transmitted in any form or by any means without prior written consent of New H3C Technologies Co., Ltd.
Except for the trademarks of New H3C Technologies Co., Ltd., any trademarks that may be mentioned in this document are the property of their respective owners.
This document provides generic technical information, some of which might not be applicable to your products.
The information in this document is subject to change without notice.
Contents
Differences between RIPng and RIP
Compatibility with network layer protocols
Accelerating route convergence through suboptimal routing
Overview
RIP is a distance-vector Interior Gateway Protocol (IGP) developed by the IETF. Easy to configure and manage, RIP is widely used in small-sized IPv4 networks.
To route IPv6 packets, the IETF developed RIPng based on RIP. RIPng has become an important routing protocol used on IPv6 networks.
RIPng implementation
RIPng operates the same way as RIP except that RIPng contains some modifications to support IPv6.
Introduction to RIP
Mechanism
RIP uses UDP and port 520 to exchange route information.
RIP uses a hop count to measure the distance to a destination. The hop count is known as a metric. The hop count from a router to a directly connected network is 0. The hop count from a router to a directly connected router is 1. To limit convergence time, RIP uses a metric range of 0 to 15. A metric value of 16 (or greater) is considered infinite, which means the destination network is unreachable.
The following describes how the routers on a RIP network learn the latest routing information from each other:
1. Each RIP router sends request messages to its neighboring routers, and listens for RIP request or response messages from neighboring routers.
2. Upon receiving response messages, the router processes the routing update information in the messages, updates its local routing table, and sends triggered update messages to its neighbors.
3. Upon receiving the triggered update, the neighboring routers send triggered updates to their respective neighbors.
By default, a RIP router sends its routing table to neighbors every 30 seconds. RIP uses an aging mechanism to retain only valid routes.
RIP versions
RIP has two versions: RIPv1 and RIPv2.
RIPv1 is a classful routing protocol. It advertises messages only through broadcast. Because RIPv1 messages do not carry mask information, RIPv1 can only recognize natural networks such as Classes A, B, and C, and it does not support non-contiguous subnets.
RIPv2 is a classless routing protocol. It has the following advantages over RIPv1:
· Supports route tags for flexible route control through routing policies.
· Supports masks, route summarization, and Classless Inter-Domain Routing (CIDR).
· Supports designated next hops on broadcast networks.
· Supports multicast route updates to reduce resource consumption.
· Supporting plaintext authentication and MD5 authentication by adding an authentication route entry (RTE) into updates to enhance security.
Differences between RIPng and RIP
Packets
IP address lengths
RIPng uses 128-bit IPv6 addresses. RIPv2 uses 32-bit IPv4 addresses.
Packet lengths
A RIPv2 packet can carry a maximum of 25 RTEs. The maximum number of RTEs in a RIPng packet depends on the IPv6 MTU of the sending interface.
Packet formats
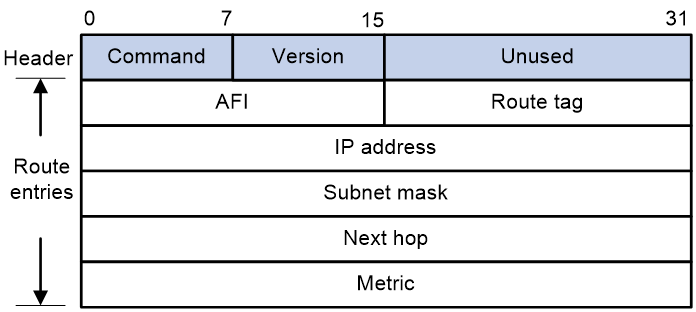
As shown in Figure 1, a RIPv2 packet contains a header and multiple RTEs.
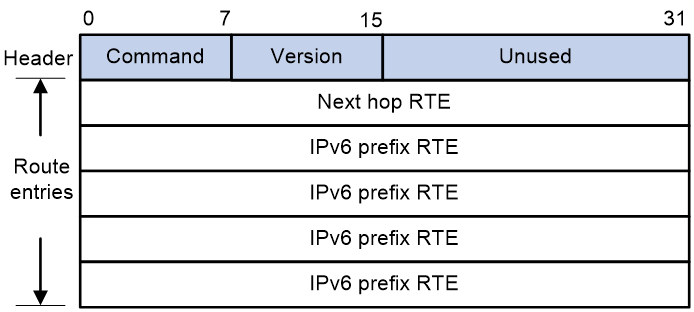
As shown in Figure 2, a RIPng packet contains a header and the following types of RTEs:
· Next hop RTE—Defines the IPv6 address of a next hop.
· IPv6 prefix RTE—A next hop RTE can be followed by multiple IPv6 prefix RTEs. An IPv6 prefix RTE describes the destination IPv6 address, route tag, prefix length, and metric in a RIPng route entry.
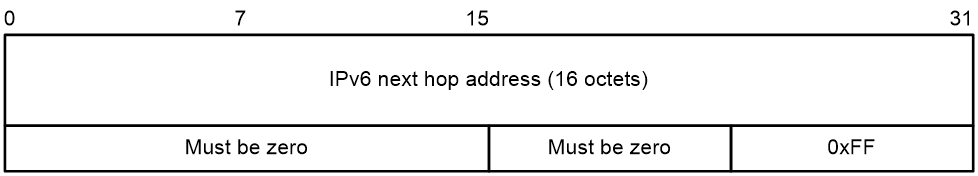
Figure 3 shows the format of a next hop RTE.
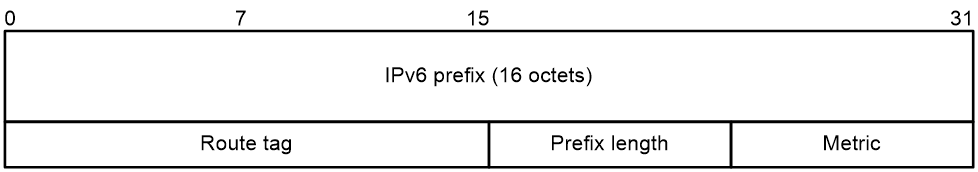
Figure 4 shows the format of an IPv6 prefix RTE:
· IPv6 prefix—Destination IPv6 address prefix.
· Route tag—Route tag.
· Prefix length—Length of the IPv6 address prefix.
· Metric—Cost of the route.
Figure 4 IPv6 prefix RTE format
Packet sending modes
RIPv2 can periodically send routing information through broadcast or multicast as configured. RIPng periodically sends routing information only through multicast.
Authentication
RIPv2 uses authentication RTEs for packet authentication. RIPng uses the authentication mechanism of IPv6 for packet authentication.
Compatibility with network layer protocols
RIP can run in IP networks and IPX networks. RIPng can run in IPv6 networks only.
Accelerating route convergence through suboptimal routing
When the device receives routes with the same destination from multiple neighbors, the device selects an optimal route and one or more suboptimal routes from among all routes by route cost. Suboptimal routing takes effect as follows:
· When the optimal route is deleted because of link failure, suboptimal routing immediately takes effect.
· When the garbage-collect timer for the optimal route (in suppressed state) expires, the suboptimal routes immediately take effect if they have not been withdrawn. The suboptimal routes can take effect without waiting for an update from their senders.
Using suboptimal routes can help accelerate RIP or RIPng route convergence in various scenarios. Routing loops will not occur because suboptimal routing takes effect only after the optimal route becomes unavailable.
Application scenarios
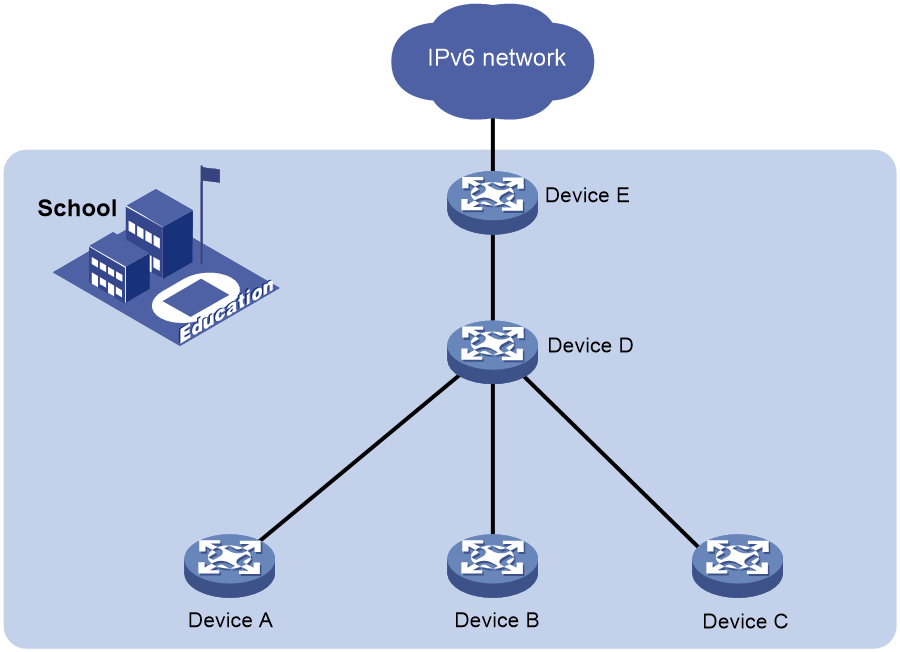
As shown in Figure 5, a school deploys a small-sized IPv6 network. All routers and hosts on the network run IPv6.
On this small-sized network, run RIPng between the nodes on the network for them to automatically adapt to topology changes.
Figure 5 Typical RIPng application scenario
References
· RFC 2080, RIPng for IPv6
· RFC 2081, RIPng Protocol Applicability Statement
· RFC 1058, Routing Information Protocol
· RFC 1721, RIP Version 2 Protocol Analysis
· RFC 2082, RIP-2 MD5 Authentication
· RFC 2453, RIP Version 2