Country / Region
Equipped with New Intelligent Engine, H3C Upgrades its Active Security Strategy
On April 24, NAVIGATE 2020 is heating up. At the long-anticipated forum with the theme of active security, H3C unveiled the evolution of active security strategy and its key technological achievements to online guests. By combining its own practice, H3C gave an in-depth analysis on the intelligence development path of active security, and released a batch of AI-powered new products and technologies. At the same time, based on the concepts of active security, H3C gave an emphasis on sharing its ideas and solutions on zero-trust security, which will provide support for the business security of hundreds of industries and safeguard security of the digital economy.
Five Key Technologies Drive Intelligent Evolution of Active Security
Digital transformation drives technological evolution. When conventional IT architectures are overturned, unknown threats will be deeply hidden. To address this issue, intelligent and strong security systems are urgently required. To satisfy network security requirements of enterprises during transformation, H3C has released a series of new security products equipped with active security systems characterized by all-stack, intention, and enabling. Specifically, new detection systems and AI security device series provide all-domain awareness to the underlying layer, boosting intelligent management and analysis capabilities of SDN security controllers and Big Data platforms. Consequently, H3C will be able to empower the cloud, build cloud security management platforms and capability centers based on in-depth AI algorithms and model, and provide comprehensive support for cloud security, IoT, industrial control computer and other scenarios.
Sun Songer, President of H3C's Security Product Line and Vice President of H3C, said that by focusing on active detection, intelligent analysis, pre-warning, and timely response, H3C was forging ahead intelligent evolution of active security strategy from five technological directions. They were security AI powered by hardware and software, multi-scenario software-defined security, people-centered zero trust security, fully-revolutionized 5G security, and open & integrated active security eco-system.

Sun Songer, President of H3C's Security Product Line and Vice President of H3C
Application Upgrades of Security AI Accurately Tackle New Security Challenges
Dr. Gu Chengjie, President of H3C Security Research Institute, said that confronted with new security challenges in digital revolution, such as AI attacks, new application detection, encrypted traffic recognition, diversified attacked targets, etc., AI technologies could be used to address network security problems more effectively, accurately, quickly, and intelligently.
Dr. Gu Chengjie, President of H3C Security Research Institute
Therefore, H3C focuses on application upgrades of security AI. Firstly, it expands sources of data collection and achieves intelligent processing of a massive volume of security data by introducing self-developed GPU service PCBs. Secondly, it continuously optimizes AI algorithms through identifying malicious/encrypted traffic, detecting DNS hidden channels, and spotting security knowledge maps. Thirdly, H3C builds a knowledge-centered intelligent analysis system through a security business model involving malicious/encrypted traffic analysis, traffic/behavior analysis, network intrusion detection, and correlated security protection.
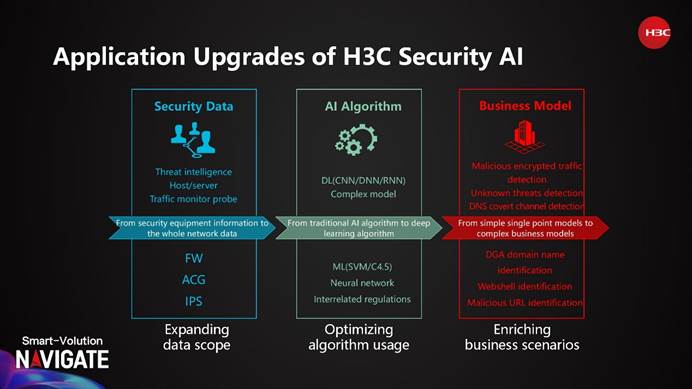
Application Upgrades of H3C Security AI
Transforming Security Concepts and Taking the Road of Zero-Trust Security
Conventional security concepts deem intranets as trustworthy and therefore intranets are weak in security defense. Once the conventional defense boundary is breached, the most sensitive and important network and data assets will be in high risk. To address this issue, zero-trust security is proposed. Under the zero-trust model, all devices, identities, and permissions are verified in all sections.
Facing intelligence revolution, Zhao Jiawei, Deputy Director of Security Product Development Department of H3C, introduced H3C’s zero-trust security solution. The solution consists of unified security management systems, trusted business control systems, identity authentication and permission management systems, and trusted terminal systems. On this basis, it implements key concepts of the zero-trust security architecture including non-interrupted analysis and detection, dynamic access control, and minimized permissions. Consequently, the zero-trust security solution can substantially protect users’ key assets.

Zhao Jiawei, Deputy Director of Security Product Development Department of H3C
The core advantage of the zero-trust security solution lies in that it establishes a trusted network based on identity security and AI-powered dynamic granting of permissions, which enables real-time monitoring of abnormal behaviors. In addition, the attack defense perspective helps improve all-round integrated security defense, and facilitates timely detection and handling of security problems. The solution can thus form a unified strategy correlation with the overall security defense system.
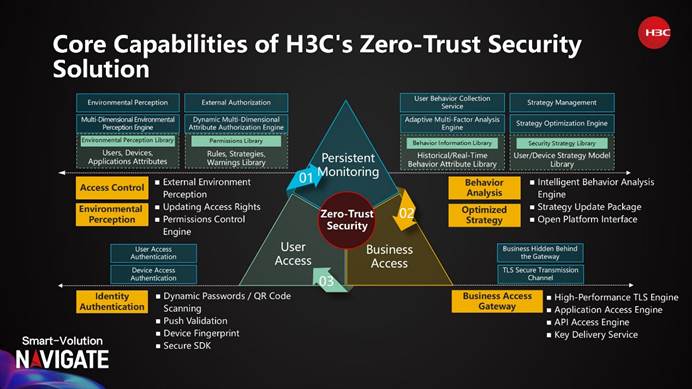
Core Capabilities of H3C’s Zero-Trust Security Solution
H3C Takes the Initiative on the Intelligent Application Practice of Active Security
To forge an actively secure world where people and data are put first, H3C takes the initiative to apply the active security system into its four business scenarios to verify and optimize the entire architecture and technologies. The four scenarios are security resource management in cloud environment, security situation analysis in groups, unknown threat identification in data centers, and remote work management of R&D personnel.
Dr. James Chen, CIO and Senior Vice President of H3C elaborated on this topic by using the company’s own practice. He said that H3C had taken visual analysis of the security situations from different dimensions of assets, business, and users in the whole company. Furthermore, to facilitate security management of remote work of R&D personnel, H3C established a mechanism of detecting, alerting, responding to, and handling security events through cloud, network, and terminal collaboration.
For instance, in its Beijing headquarter, H3C has set the security threat model as the benchmark and performed associated analysis and in-depth exploration of Big Data by using the Big Data platform. While at the headquarter in Hangzhou, H3C has transformed various security capabilities from pure product configuration to service configuration, enabling full-lifecycle management on security resources stored on the cloud, and significantly improving utilization of security resources, he said.

Dr. James Chen, CIO and Senior Vice President of H3C
Apart from the application practice by H3C itself, the active security system has also seen a large number of successful cases in rich fields ranging from governments at the province level, top universities, top-grade hospitals, to carriers, power & energy and transportation. H3C will continue to explore and practice the evolution of the active security system, build a reliable and controllable active defense system for network security, and escort the development of China’s digital economy.


