- Table of Contents
-
- 19-Security Configuration Guide
- 00-Preface
- 01-Object group configuration
- 02-Keychain configuration
- 03-Public key management
- 04-PKI configuration
- 05-Crypto engine configuration
- 06-SSH configuration
- 07-SSL configuration
- 08-Security zone configuration
- 09-Packet filter configuration
- 10-ASPF configuration
- 11-Security policy configuration
- 12-Session management
- 13-ARP attack protection configuration
- 14-ND attack defense configuration
- 15-Attack detection and prevention configuration
- 16-mGRE configuration
- 17-Connection limit configuration
- 18-IP-based attack prevention configuration
- 19-IP source guard configuration
- 20-uRPF configuration
- 21-APR configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 13-ARP attack protection configuration | 291.29 KB |
Contents
Configuring ARP attack protection
ARP attack protection tasks at a glance
Configuring unresolvable IP attack protection
About unresolvable IP attack protection
Configuring ARP source suppression
Configuring ARP blackhole routing
Verifying and maintaining unresolvable IP attack protection
Example: Configuring unresolvable IP attack protection
Configuring ARP packet rate limit
Configuring source MAC-based ARP attack detection
About source MAC-based ARP attack detection
Verifying and maintaining source MAC-based ARP attack detection
Example: Configuring source MAC-based ARP attack detection
Configuring ARP packet source MAC consistency check
About ARP packet source MAC consistency check
Verifying and maintaining ARP packet source MAC consistency check
Configuring ARP active acknowledgement
Example: Configuring authorized ARP on a DHCP server
Example: Configuring authorized ARP on a DHCP relay agent
Configuring ARP scanning and fixed ARP
Configuring automatic ARP scanning
Configuring ARP keepalive entry scanning
About ARP keepalive entry scanning
Configuring ARP keepalive entry scanning
Verifying and maintaining ARP keepalive entry scanning
Configuring ARP gateway protection
Example: Configuring ARP gateway protection
Example: Configuring ARP filtering
Configuring ARP sender IP address checking
About ARP sender IP address checking
Example: Configuring ARP sender IP address checking
Enabling SNMP notifications for ARP
Configuring ARP attack protection
About ARP attack protection
The device can provide multiple features to detect and prevent ARP attacks and viruses in the LAN. An attacker can exploit ARP vulnerabilities to attack network devices in the following ways:
· Sends a large number of unresolvable IP packets to have the receiving device busy with resolving IP addresses until its CPU is overloaded. Unresolvable IP packets refer to IP packets for which ARP cannot find corresponding MAC addresses.
· Sends a large number of ARP packets to overload the CPU of the receiving device.
· Acts as a trusted user or gateway to send ARP packets so the receiving devices obtain incorrect ARP entries.
ARP attack protection tasks at a glance
All ARP attack protection tasks are optional.
· Preventing flood attacks
¡ Configuring unresolvable IP attack protection
¡ Configuring ARP packet rate limit
¡ Configuring source MAC-based ARP attack detection
· Preventing user and gateway spoofing attacks
¡ Configuring ARP packet source MAC consistency check
¡ Configuring ARP active acknowledgement
¡ Example: Configuring authorized ARP on a DHCP relay agent
¡ Configuring ARP scanning and fixed ARP
¡ Configuring ARP keepalive entry scanning
¡ Configuring ARP gateway protection
¡ Configuring ARP sender IP address checking
· Enabling SNMP notifications for ARP
Configuring unresolvable IP attack protection
About unresolvable IP attack protection
If a device receives a large number of unresolvable IP packets from a host, the following situations can occur:
· The device sends a large number of ARP requests, overloading the target subnets.
· The device keeps trying to resolve the destination IP addresses, overloading its CPU.
To protect the device from such IP attacks, you can configure the following features:
· ARP source suppression—Stops resolving packets from an IP address if the number of unresolvable IP packets from the IP address exceeds the upper limit within 5 seconds. The device continues ARP resolution when the interval elapses. This feature is applicable if the attack packets have the same source addresses.
· ARP blackhole routing—Creates a blackhole route destined for an unresolved IP address. The device drops all matching packets until the blackhole route is deleted. A blackhole route is deleted when its aging timer is reached or the route becomes reachable.
After a blackhole route is created for an unresolved IP address, the device immediately starts the first ARP blackhole route probe by sending an ARP request. If the resolution fails, the device continues probing according to the probe settings. If the IP address resolution succeeds in a probe, the device converts the blackhole route to a normal route. If an ARP blackhole route ages out before the device finishes all probes, the device deletes the blackhole route and does not perform the remaining probes.
This feature is applicable regardless of whether the attack packets have the same source addresses.
Configuring ARP source suppression
1. Enter system view.
system-view
2. Enable ARP source suppression.
arp source-suppression enable
By default, ARP source suppression is disabled.
3. Set the maximum number of unresolvable packets that the device can process per source IP address within 5 seconds.
arp source-suppression limit limit-value
By default, the maximum number is 10.
Configuring ARP blackhole routing
Restrictions and guidelines
Set the ARP blackhole route probe count to a big value, for example, 25. If the device fails to reach the destination IP address temporarily and the probe count is too small, all probes might finish before the problem is resolved. As a result, non-attack packets will be dropped. This setting can avoid such situation.
Procedure
1. Enter system view.
system-view
2. Enable ARP blackhole routing.
arp resolving-route enable
By default, ARP blackhole routing is enabled.
3. (Optional.) Set the number of ARP blackhole route probes for each unresolved IP address.
arp resolving-route probe-count count
The default setting is three probes.
4. (Optional.) Set the interval at which the device probes ARP blackhole routes.
arp resolving-route probe-interval interval
The default setting is 1 second.
Verifying and maintaining unresolvable IP attack protection
To display ARP source suppression configuration information, execute the following command in any view:
display arp source-suppression
Example: Configuring unresolvable IP attack protection
Network configuration
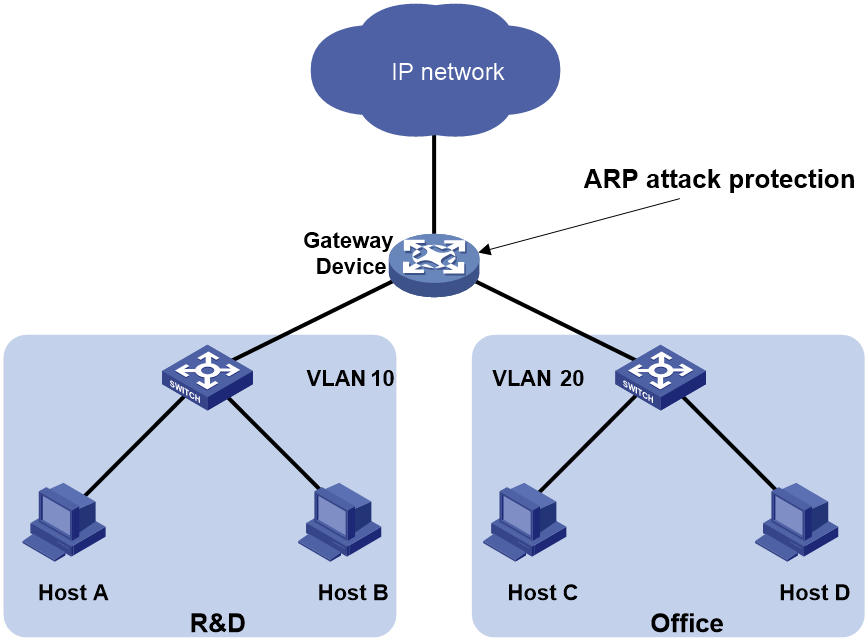
As shown in Figure 1, a LAN contains two areas: an R&D area in VLAN 10 and an office area in VLAN 20. Each area connects to the gateway (Device) through an access switch.
A large number of ARP requests are detected in the office area and are considered an attack caused by unresolvable IP packets. To prevent the attack, configure ARP source suppression or ARP blackhole routing.
Procedure
· If the attack packets have the same source address, configure ARP source suppression:
# Enable ARP source suppression.
<Device> system-view
[Device] arp source-suppression enable
# Configure the device to process a maximum of 100 unresolvable packets per source IP address within 5 seconds.
[Device] arp source-suppression limit 100
· If the attack packets have different source addresses, configure ARP blackhole routing:
# Enable ARP blackhole routing.
[Device] arp resolving-route enable
Configuring ARP packet rate limit
About this task
The ARP packet rate limit feature allows you to limit the rate of ARP packets delivered to the CPU. When the receiving rate of ARP packets on the interface exceeds the rate limit, those packets are discarded.
You can enable sending notifications to the SNMP module or enable logging for ARP packet rate limit.
· If notification sending is enabled, the device sends the highest threshold-crossed ARP packet rate within the sending interval in a notification to the SNMP module. You must use the snmp-agent target-host command to set the notification type and target host. For more information about notifications, see SNMP configuration in Network Management and Monitoring Configuration Guide.
· If logging for ARP packet rate limit is enabled, the device sends the highest threshold-crossed ARP packet rate within the sending interval in a log message to the information center. You can configure the information center module to set the log output rules. For more information about information center, see System Management Configuration Guide.
Restrictions and guidelines
As a best practice, configure this feature when ARP fast-reply or MFF is enabled, or when ARP flood attacks are detected.
If excessive notifications and log messages are sent for ARP packet rate limit, you can increase notification and log message sending interval.
If you enable notification sending and logging for ARP packet rate limit on an aggregate interface, the features apply to all aggregation member ports.
Procedure
1. Enter system view.
system-view
2. (Optional.) Enable SNMP notifications for ARP packet rate limit.
snmp-agent trap enable arp [ rate-limit ]
By default, SNMP notifications for ARP packet rate limit are disabled.
3. (Optional.) Enable logging for ARP packet rate limit.
arp rate-limit log enable
By default, logging for ARP packet rate limit is disabled.
4. (Optional.) Set the notification and log message sending interval.
arp rate-limit log interval interval
By default, the device sends notifications and log messages every 60 seconds.
5. Enter interface view.
interface interface-type interface-number
Supported interface types include Layer 2 Ethernet interface, Layer 3 Ethernet interface, Layer 3 aggregate interface, and Layer 2 aggregate interface.
6. Enable ARP packet rate limit.
arp rate-limit [ pps ]
By default, ARP packet rate limit is enabled.
Configuring source MAC-based ARP attack detection
About source MAC-based ARP attack detection
This feature checks the number of ARP packets delivered to the CPU. If the number of packets from the same MAC address within 5 seconds exceeds a threshold, the device generates an ARP attack entry for the MAC address. If the ARP logging feature is enabled, the device handles the attack by using either of the following methods before the ARP attack entry ages out:
· Monitor—Only generates log messages.
· Filter—Generates log messages and filters out subsequent ARP packets from the MAC address.
When an ARP attack entry ages out, ARP packets sourced from the MAC address in the entry can be processed correctly.
To enable the ARP logging feature, use the arp check log enable command. For information about the ARP logging feature, see ARP in Layer 3—IP Services Configuration Guide.
Source MAC-based ARP attack detection checks the number of ARP packets delivered to the CPU in one of the following modes:
· Layer 3 interface-based mode—Checks the number of ARP packets on a per-interface basis. If the number of ARP packets received from the same MAC address within 5 seconds on a Layer 3 interface (excluding the VLAN interface) exceeds the threshold, the device determines that an attack has occurred.
· VLAN interface-based mode—Checks the number of ARP packets on a per-slot basis. If the number of ARP packets received from the same MAC address within 5 seconds on the slot to which the VLAN interface belongs exceeds the threshold, the device determines that an attack has occurred. It records the first physical interface that receives such an ARP packet in the ARP attack entry.
Restrictions and guidelines
If you change the attack handling method from monitor to filter, the configuration takes effect immediately.
If you change the attack handling method from filter to monitor, the device works as follows:
· Uses the filter attack handling method to process the ARP packets that match the existing ARP attack entries before the entries age out.
· Uses the monitor attack handling method to process the ARP packets that match the newly-generated ARP attack entries.
You can exclude the MAC addresses of some gateways and servers from this detection. This feature does not inspect ARP packets from those devices even if they are attackers.
Procedure
1. Enter system view.
system-view
2. Enable source MAC-based ARP attack detection and specify the handling method.
arp source-mac { filter | monitor }
By default, this feature is disabled.
3. Set the threshold.
arp source-mac threshold threshold-value
By default, the threshold is 30.
4. Set the aging timer for ARP attack entries.
arp source-mac aging-time time
By default, the lifetime is 300 seconds.
5. (Optional.) Exclude specific MAC addresses from this detection.
arp source-mac exclude-mac mac-address&<1-n>
By default, no MAC address is excluded.
Verifying and maintaining source MAC-based ARP attack detection
Displaying source MAC-based ARP attack detection entries
To display ARP attack entries detected by source MAC-based ARP attack detection, execute the following commands in any view:
display arp source-mac { interface interface-type interface-number [ slot slot-number ] | slot slot-number }
Maintaining statistics for source MAC-based ARP attack packets
To display statistics for packets dropped by source MAC-based ARP attack detection, execute the following commands in any view:
display arp source-mac statistics slot slot-number
To clear statistics of packets dropped by source MAC-based ARP attack detection, execute the following commands in user view:
reset arp source-mac statistics { all | [ slot slot-number ] }
Example: Configuring source MAC-based ARP attack detection
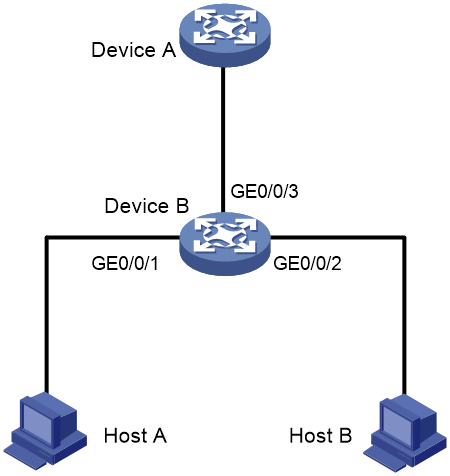
Network configuration
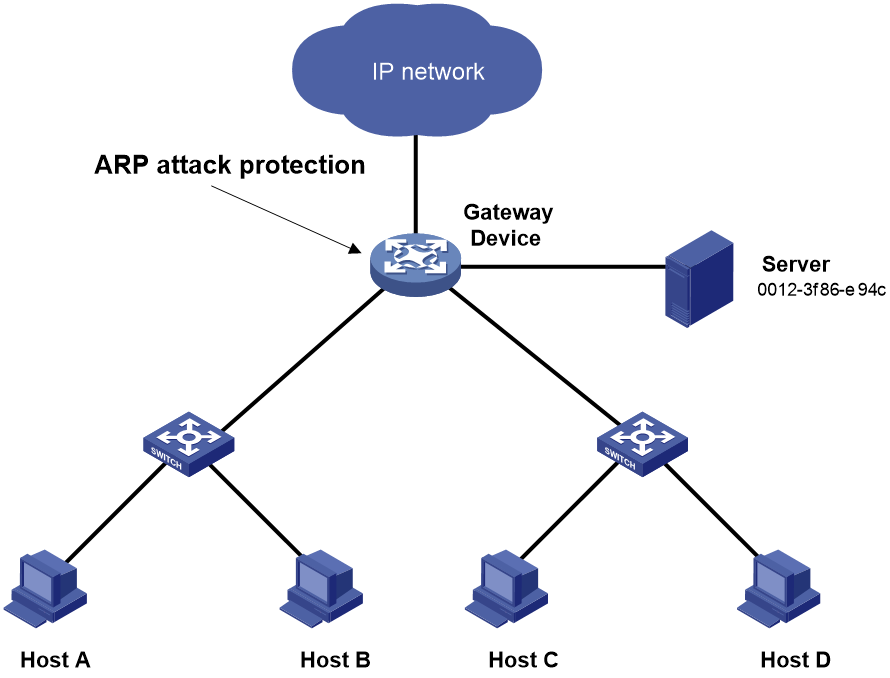
As shown in Figure 2, the hosts access the Internet through a gateway (Device). If malicious users send a large number of ARP requests to the gateway, the gateway might crash and cannot process requests from the clients. To solve this problem, configure source MAC-based ARP attack detection on the gateway.
Figure 2 Network diagram
Procedure
# Enable source MAC-based ARP attack detection, and specify the handling method as filter.
<Device> system-view
[Device] arp source-mac filter
# Set the threshold to 30.
[Device] arp source-mac threshold 30
# Set the lifetime for ARP attack entries to 60 seconds.
[Device] arp source-mac aging-time 60
# Exclude MAC address 0012-3f86-e94c from this detection.
[Device] arp source-mac exclude-mac 0012-3f86-e94c
Configuring ARP packet source MAC consistency check
About ARP packet source MAC consistency check
This feature enables a gateway to filter out ARP packets whose source MAC address in the Ethernet header is different from the sender MAC address in the message body. This feature allows the gateway to learn correct ARP entries.
Procedure
1. Enter system view.
system-view
2. Enable ARP packet source MAC address consistency check.
arp valid-check enable
By default, ARP packet source MAC address consistency check is disabled.
Verifying and maintaining ARP packet source MAC consistency check
display arp valid-check statistics slot slot-number
To clear statistics for packets dropped by ARP packet source MAC consistency check, execute the following command in user view:
reset arp valid-check statistics { all | slot slot-number }
Configuring ARP active acknowledgement
About this task
Use the ARP active acknowledgement feature on gateways to prevent user spoofing.
This feature enables the device to perform active acknowledgement before creating an ARP entry.
· Upon receiving an ARP request that requests the MAC address of the device, the device sends an ARP reply. Then, it sends an ARP request for the sender IP address in the received ARP request to determine whether to create an ARP entry for the sender IP address.
¡ If the device receives an ARP reply within the probe interval, it creates the ARP entry.
¡ If the device does not receive an ARP reply within the probe interval, it does not create the ARP entry.
· Upon receiving an ARP reply, the device examines whether it was the reply to the request that the device has sent.
¡ If it was, the device creates an ARP entry for the sender IP address in the ARP reply.
¡ If it was not, the device sends an ARP request for the sender IP address to determine whether to create an ARP entry for the sender IP address.
- If the device receives an ARP reply within the probe interval, it creates the ARP entry.
- If the device does not receive an ARP reply within the probe interval, it does not create the ARP entry.
To improve validity and reliability of ARP entries, you can enable ARP active acknowledgement in strict mode. In this mode, the device creates ARP entries only for the IP addresses that the device actively initiates the ARP resolution.
Procedure
1. Enter system view.
system-view
2. Enable ARP active acknowledgement.
arp active-ack [ strict ] enable
By default, ARP active acknowledgement is disabled.
For ARP active acknowledgement to take effect in strict mode, make sure ARP blackhole routing is enabled.
Configuring authorized ARP
About authorized ARP
Authorized ARP entries are generated based on the DHCP clients' address leases on the DHCP server or dynamic client entries on the DHCP relay agent. For more information about DHCP server and DHCP relay agent, see Layer 3—IP Services Configuration Guide.
Use this feature to prevent user spoofing and to allow only authorized clients to access network resources.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
Supported interface types include Layer 3 Ethernet interface, Layer 3 Ethernet subinterface, Layer 3 aggregate interface, Layer 3 aggregate subinterface, VSI interface, and VLAN interface.
3. Enable authorized ARP on the interface.
arp authorized enable
By default, authorized ARP is disabled.
Example: Configuring authorized ARP on a DHCP server
Network configuration
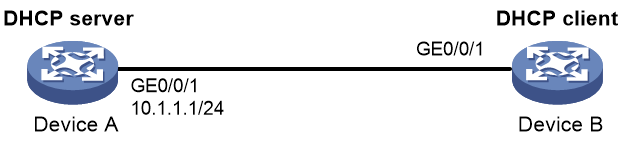
As shown in Figure 3, configure authorized ARP on GigabitEthernet 0/0/1 of Device A (a DHCP server) to ensure user validity.
Procedure
1. Configure Device A:
# Specify the IP address for GigabitEthernet 0/0/1.
<DeviceA> system-view
[DeviceA] interface gigabitethernet 0/0/1
[DeviceA-GigabitEthernet0/0/1] ip address 10.1.1.1 24
[DeviceA-GigabitEthernet0/0/1] quit
# Configure DHCP.
[DeviceA] dhcp enable
[DeviceA] dhcp server ip-pool 1
[DeviceA-dhcp-pool-1] network 10.1.1.0 mask 255.255.255.0
[DeviceA-dhcp-pool-1] quit
# Enter Layer 3 Ethernet interface view.
[DeviceA] interface gigabitethernet 0/0/1
# Enable authorized ARP.
[DeviceA-GigabitEthernet0/0/1] arp authorized enable
[DeviceA-GigabitEthernet0/0/1] quit
2. Configure Device B:
<DeviceB> system-view
[DeviceB] interface gigabitethernet 0/0/1
[DeviceB-GigabitEthernet0/0/1] ip address dhcp-alloc
[DeviceB-GigabitEthernet0/0/1] quit
Verifying the configuration
# Display authorized ARP entry information on Device A.
[DeviceA] display arp all
Type: S-Static D-Dynamic O-Openflow R-Rule M-Multiport I-Invalid
IP address MAC address VLAN/VSI name Interface Aging Type
10.1.1.2 0012-3f86-e94c -- GE0/0/1 960 D
The output shows that IP address 10.1.1.2 has been assigned to Device B.
Device B must use the IP address and MAC address in the authorized ARP entry to communicate with Device A. Otherwise, the communication fails. Thus user validity is ensured.
Example: Configuring authorized ARP on a DHCP relay agent
Network configuration
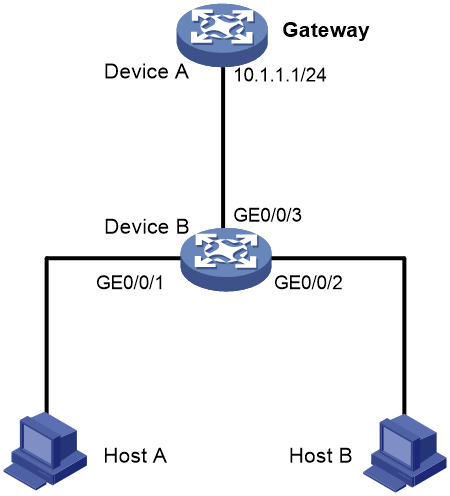
As shown in Figure 4, configure authorized ARP on GigabitEthernet 0/0/2 of Device B (a DHCP relay agent) to ensure user validity.
Procedure
1. Configure Device A:
# Specify the IP address for GigabitEthernet 0/0/1.
<DeviceA> system-view
[DeviceA] interface gigabitethernet 0/0/1
[DeviceA-GigabitEthernet0/0/1] ip address 10.1.1.1 24
[DeviceA-GigabitEthernet0/0/1] quit
# Configure DHCP.
[DeviceA] dhcp enable
[DeviceA] dhcp server ip-pool 1
[DeviceA-dhcp-pool-1] network 10.10.1.0 mask 255.255.255.0
[DeviceA-dhcp-pool-1] gateway-list 10.10.1.1
[DeviceA-dhcp-pool-1] quit
[DeviceA] ip route-static 10.10.1.0 24 10.1.1.2
2. Configure Device B:
# Enable DHCP.
<DeviceB> system-view
[DeviceB] dhcp enable
# Specify the IP addresses of GigabitEthernet 0/0/1 and GigabitEthernet 0/0/2.
[DeviceB] interface gigabitethernet 0/0/1
[DeviceB-GigabitEthernet0/0/1] ip address 10.1.1.2 24
[DeviceB-GigabitEthernet0/0/1] quit
[DeviceB] interface gigabitethernet 0/0/2
[DeviceB-GigabitEthernet0/0/2] ip address 10.10.1.1 24
# Enable DHCP relay agent on GigabitEthernet 0/0/2.
[DeviceB-GigabitEthernet0/0/2] dhcp select relay
# Add the DHCP server 10.1.1.1 to DHCP server group 1.
[DeviceB-GigabitEthernet0/0/2] dhcp relay server-address 10.1.1.1
# Enable authorized ARP.
[DeviceB-GigabitEthernet0/0/2] arp authorized enable
[DeviceB-GigabitEthernet0/0/2] quit
# Enable recording of relay entries on the relay agent.
[DeviceB] dhcp relay client-information record
3. Configure Device C:
<DeviceC> system-view
[DeviceC] ip route-static 10.1.1.0 24 10.10.1.1
[DeviceC] interface gigabitethernet 0/0/2
[DeviceC-GigabitEthernet0/0/2] ip address dhcp-alloc
[DeviceC-GigabitEthernet0/0/2] quit
Verifying the configuration
# Display authorized ARP information on Device B.
[DeviceB] display arp all
Type: S-Static D-Dynamic O-Openflow R-Rule M-Multiport I-Invalid
IP address MAC address VLAN/VSI name Interface Aging Type
10.10.1.2 0012-3f86-e94c -- GE0/0/2 960 D
The output shows that Device A assigned the IP address 10.10.1.2 to Device C.
Device C must use the IP address and MAC address in the authorized ARP entry to communicate with Device B. Otherwise, the communication fails. Thus the user validity is ensured.
Configuring ARP scanning and fixed ARP
About this task
ARP scanning is typically used together with the fixed ARP feature in small-scale and stable networks.
ARP scanning automatically creates ARP entries for devices in an address range. The device performs ARP scanning in the following steps:
1. Sends ARP requests for each IP address in the address range.
2. Obtains their MAC addresses through received ARP replies.
3. Creates dynamic ARP entries.
Enabled with automatic ARP scanning, the device periodically sends ARP requests to all IP addresses in the specified scanning range at the rate set by using the arp scan auto send-rate command.
You can limit the ARP packet sending rate if the scanning range has a large number of IP addresses. to avoid high CPU usage and heavy network load caused by a burst of ARP traffic.
If you specify the scanning range and source address for the sending ARP requests, the interface scans all IP addresses in the scanning range. If you only specify the scanning range, the interface scans the IP addresses that belong to both the scanning range and the subnet addresses of the interface.
Fixed ARP converts existing dynamic ARP entries (including those generated through ARP scanning) to static ARP entries. These static ARP entries are of the same attributes as the ARP entries that are manually configured. This feature prevents ARP entries from being modified by attackers.
Restrictions and guidelines
IP addresses in existing ARP entries are not scanned.
If you trigger ARP scanning and enable automatic ARP scanning, both of them take effect. As a best practice, use automatic ARP scanning only on networks where users come online and go offline frequently.
Due to the limit on the total number of static ARP entries, some dynamic ARP entries might fail the conversion.
The arp fixup command is a one-time operation. You can use this command again to convert the dynamic ARP entries learned later to static.
To delete a static ARP entry converted from a dynamic one, use the undo arp ip-address [ vpn-instance-name ] command. You can also use the reset arp all command to delete all ARP entries or the reset arp static command to delete all static ARP entries.
You can use the arp scan auto enable [ start-ip-address to end-ip-address [ source-addr source-ip-address ] ] command to specify a maximum of 16 scanning ranges for different subnets. The subnet addresses for each scanning range cannot overlap with each other.
Triggering an ARP scanning
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
3. Trigger an ARP scanning.
arp scan [ start-ip-address to end-ip-address ]
|
CAUTION: ARP scanning will take some time. To stop an ongoing scan, press Ctrl + C. Dynamic ARP entries are created based on ARP replies received before the scan is terminated. |
Configuring automatic ARP scanning
1. Enter system view.
system-view
2. Set the ARP packet sending rate for automatic ARP scanning.
arp scan auto send-rate { ppm ppm | pps }
By default, the device sends ARP packets at the rate of 48 pps during automatic ARP scanning.
3. Enter interface view.
interface interface-type interface-number
4. Enable automatic ARP scanning.
arp scan auto enable [start-ip-address to end-ip-address [ source-addr source-ip-address ] ]
By default, automatic ARP scanning is disabled.
Configuring fixed ARP
1. Enter system view.
system-view
2. Convert existing dynamic ARP entries to static ARP entries.
arp fixup
Configuring ARP keepalive entry scanning
About ARP keepalive entry scanning
In a large-scale network, it takes a long time for ARP scanning to identify the hosts that go offline abnormally if you specify a large scanning range. After you enable ARP keepalive entry scanning, the system can quickly locate those hosts and monitor the host status within the aging time.
You can set the aging time for ARP keepalive entries in both system view and interface view. The aging time set in interface view takes precedence over the aging time set in system view. In interface view, the default aging time for ARP keepalive entries is the aging time set in system view.
When users come online, the system generates dynamic APR entries and IPSG binding entries. Enabled with ARP keepalive entry scanning, the system also creates online keepalive entries when users come online. If users go offline, the corresponding APR entries are deleted and the status of the keepalive entries is set to offline. The device sends ARP requests at intervals to the IP addresses in the offline keepalive entries until the keepalive entries become online again or are deleted when the aging time expires. The interval varies with the number of ARP requests that have been sent to the IP address in an offline keepalive entry. For more information about IP source guard configuration, see Security Configuration Guide.
Configuring ARP keepalive entry scanning
1. Enter system view.
system-view
2. (Optional.) Set the ARP request sending rate for keepalive entry scanning.
arp scan keepalive send-rate pps
By default, the device sends ARP requests at a rate of 48 pps during keepalive entry scanning.
3. (Optional.) Set the aging time for ARP keepalive entries.
arp scan keepalive aging-time time
By default, the aging time for ARP keepalive entries in system view is 60 minutes. The aging time for ARP keepalive entries in interface view is the aging time set in system view.
4. Enter interface view.
interface interface-type interface-number
5. Enable the ARP keepalive entry scanning feature.
arp scan keepalive enable
By default, the ARP keepalive entry scanning is disabled on an interface.
Verifying and maintaining ARP keepalive entry scanning
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display ARP keepalive entries. |
display arp scan keepalive entry [ interface interface-type interface-number ] [ count ] |
|
Display statistics about ARP requests sent to the IP addresses in offline keepalive entries for an interface. |
display arp scan keepalive statistics [ slot slot-number ] [ interface interface-type interface-number ] |
|
Clear statistics about ARP requests sent to the IP addresses in offline keepalive entries. |
reset arp scan keepalive statistics [ slot slot-number ] |
Configuring ARP gateway protection
About ARP gateway protection
Configure this feature on interfaces not connected with a gateway to prevent gateway spoofing attacks.
When such an interface receives an ARP packet, it checks whether the sender IP address in the packet is consistent with that of any protected gateway. If yes, it discards the packet. If not, it handles the packet correctly.
Restrictions and guidelines
You can enable ARP gateway protection for a maximum of eight gateways on an interface.
Do not configure both the arp filter source and arp filter binding commands on an interface.
If ARP gateway protection works with ARP attack detection, MFF, ARP snooping, and ARP fast-reply, ARP gateway protection applies first.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
Supported interface types include Layer 2 Ethernet interface and Layer 2 aggregate interface.
3. Enable ARP gateway protection for the specified gateway.
arp filter source ip-address
By default, ARP gateway protection is disabled.
Example: Configuring ARP gateway protection
Network configuration
As shown in Figure 5, Host B launches gateway spoofing attacks to Device B. As a result, traffic that Device B intends to send to Device A is sent to Host B.
Configure Device B to block such attacks.
Procedure
# Configure ARP gateway protection on Device B.
<DeviceB> system-view
[DeviceB] interface gigabitethernet 0/0/1
[DeviceB-GigabitEthernet0/0/1] arp filter source 10.1.1.1
[DeviceB-GigabitEthernet0/0/1] quit
[DeviceB] interface gigabitethernet 0/0/2
[DeviceB-GigabitEthernet0/0/2] arp filter source 10.1.1.1
Verifying the configuration
# Verify that GigabitEthernet 0/0/1 and GigabitEthernet 0/0/2 discard the incoming ARP packets whose sender IP address is the IP address of the gateway.
Configuring ARP filtering
ARP filtering
The ARP filtering feature can prevent gateway spoofing and user spoofing attacks.
An interface enabled with this feature checks the sender IP and MAC addresses in a received ARP packet against permitted entries. If a match is found, the packet is handled correctly. If not, the packet is discarded.
Restrictions and guidelines
You can configure a maximum of eight permitted entries on an interface.
Do not configure both the arp filter source and arp filter binding commands on an interface.
If ARP filtering works with ARP attack detection, MFF, ARP snooping, and ARP fast-reply, ARP filtering applies first.
Procedure
1. Enter system view.
system-view
2. Enter interface view.
interface interface-type interface-number
Supported interface types include Ethernet interface and Layer 2 aggregate interface.
3. Enable ARP filtering and configure a permitted entry.
arp filter binding ip-address mac-address
By default, ARP filtering is disabled.
Example: Configuring ARP filtering
Network configuration
As shown in Figure 6, the IP and MAC addresses of Host A are 10.1.1.2 and 000f-e349-1233, respectively. The IP and MAC addresses of Host B are 10.1.1.3 and 000f-e349-1234, respectively.
Configure ARP filtering on GigabitEthernet 0/0/1 and GigabitEthernet 0/0/2 of Device B to permit ARP packets from only Host A and Host B.
Procedure
# Configure ARP filtering on Device B.
<DeviceB> system-view
[DeviceB] interface gigabitethernet 0/0/1
[DeviceB-GigabitEthernet0/0/1] arp filter binding 10.1.1.2 000f-e349-1233
[DeviceB-GigabitEthernet0/0/1] quit
[DeviceB] interface gigabitethernet 0/0/2
[DeviceB-GigabitEthernet0/0/2] arp filter binding 10.1.1.3 000f-e349-1234
Verifying the configuration
# Verify that GigabitEthernet 0/0/1 permits ARP packets from Host A and discards other ARP packets.
# Verify that GigabitEthernet 0/0/2 permits ARP packets from Host B and discards other ARP packets.
Configuring ARP sender IP address checking
About ARP sender IP address checking
This feature allows a gateway to check the sender IP address of an ARP packet in a VLAN before ARP learning. If the sender IP address is within the allowed IP address range, the gateway continues ARP learning. If the sender IP address is out of the range, the gateway determines the ARP packet as an attack packet and discards it.
Restrictions and guidelines
If the VLAN is a sub-VLAN and is associated with a super VLAN, configure this checking feature only in the sub-VLAN.
If Layer 3 communication is configured between the secondary VLANs associated with a primary VLAN, configure this feature in the primary VLAN. If Layer 3 communication is not configured between the secondary VLANs associated with a primary VLAN, configure this feature in the intended VLAN.
Procedure
1. Enter system view.
system-view
2. Enter VLAN view.
vlan vlan-id
3. Enable the ARP sender IP address checking feature and specify the IP address range.
arp sender-ip-range start-ip-address end-ip-address
By default, the ARP sender IP address checking feature is disabled.
Example: Configuring ARP sender IP address checking
Network configuration
As shown in Figure 7, perform the following tasks:
· Create a super VLAN and associate it with VLANs 2, 3, and 4. VLANs 2, 3, and 4 are isolated at Layer 2 but interoperable at Layer 3. All hosts in VLANs 2, 3, and 4 use the gateway IP address 10.1.1.1/24 for Layer 3 communication.
· Configure the ARP sender IP address checking feature in VLAN 2 and specify the sender IP address range 10.1.1.1 to 10.1.1.10.
Procedure
# Create VLAN 10.
<Device> system-view
[Device] vlan 10
[Device-vlan10] quit
# Create VLAN-interface 10, and assign IP address 10.1.1.1/24 to it.
[Device] interface vlan-interface 10
[Device-Vlan-interface10] ip address 10.1.1.1 255.255.255.0
[Device] quit
# Create VLAN 2, and assign GigabitEthernet 0/0/1 and GigabitEthernet 0/0/2 to the VLAN.
[Device] vlan 2
[Device-vlan2] port gigabitethernet 0/0/1 gigabitethernet 0/0/2
[Device-vlan2] quit
# Create VLAN 3, and assign GigabitEthernet 0/0/3 and GigabitEthernet 0/0/4 to the VLAN.
[Device] vlan 3
[Device-vlan3] port gigabitethernet 0/0/3 gigabitethernet 0/0/4
[Device-vlan3] quit
# Create VLAN 4, and assign GigabitEthernet 0/0/5 and GigabitEthernet 0/0/6 to the VLAN.
[Device] vlan 4
[Device-vlan4] port gigabitethernet 0/0/5 gigabitethernet 0/0/6
[Device-vlan4] quit
# Configure VLAN 10 as a super VLAN, and associate sub-VLANs 2, 3, and 4 with the super VLAN.
[Device] vlan 10
[Device-vlan10] supervlan
[Device-vlan10] subvlan 2 3 4
[Device-vlan10] quit
# Enable the ARP sender IP address checking feature in VLAN 2 and specify the IP address range 10.1.1.1 to 10.1.1.10.
[Device] vlan 2
[Device-vlan2] arp sender-ip-range 10.1.1.1 10.1.1.10
Verifying the configuration
# Verify that the device accepts only ARP packets whose sender IP addresses are within the specified address range 10.1.1.1 to 10.1.1.10. The device discards the ARP packets with the sender IP addresses that are out of the range.
Enabling SNMP notifications for ARP
About this task
Enable SNMP notifications for ARP as required.
· If you enable ARP active acknowledgement notifications, the device sends a notification to the SNMP module when it does not establish an ARP entry due to active acknowledgement. The notification includes the sender IP address in the received ARP packet and the interface that receives the ARP packet.
· If you enable rate limit notifications for sending ARP Miss messages or ARP packets, the device sends the highest threshold-crossed rate as a notification to the SNMP module when the sending rate exceeds the custom threshold.
· If you enable notifications for packet dropping due to ARP attack detection, the device sends a notification to the SNMP module when a packet is dropped by ARP attack detection. The notification includes the VLAN ID, service ID, and VSI for the dropped packet and packet drop reason.
· If you enable ARP entry modification notifications, the device sends a notification to the SNMP module when it detects that the ARP entry for a user might be changed to the attacker's ARP entry. The notification includes the sender IP and MAC addresses in the ARP attack packet.
· If you enable ARP entry limit notifications, the device sends the current number of ARP entries as a notification to the SNMP module when the number of global ARP entries exceeds the alarm threshold.
· If you enable ARP gateway protection notifications, the device sends a notification to the SNMP module when it is attacked by gateway spoofing attacks. The notification includes the sender IP and MAC addresses in the ARP attack packet dropped by ARP gateway protection, and index of the interface that receives the ARP attack packet. When an ARP packet with the same sender IP address triggers the SNMP notification again within 3 minutes, the device sends a recovery notification to the SNMP module.
· If you enable endpoint and local device conflict notifications, the device sends a notification to the SNMP module when an endpoint and local device conflict occurs. The notification includes the sender IP address, sender MAC address, target IP address, and target MAC address in the conflicting ARP packet.
· If you enable MAC address inconsistency notifications, the device sends a notification to the SNMP module when the MAC address in the configured static ARP entry and user's actual MAC address are inconsistent. The notification includes the IP address, VPN instance, and MAC address in the ARP entry.
· An invalid ARP packet contains an invalid hardware address type, protocol address type, hardware address length, protocol address length, operation code, or VLAN. For example, when the operation code value is not 1 (ARP request) or 2 (ARP reply), the operation code is invalid and the ARP packet is invalid. If you enable invalid ARP packet check notifications, the device sends a notification to the SNMP module when it receives an invalid ARP packet. The notification includes the name of the interface that receives the ARP packet, sender MAC and IP addresses, user VLAN ID, and VLAN ID of the service provider.
· If you enable rate limit notifications for receiving ARP packets, the device sends the highest threshold-crossed rate as a notification to the SNMP module. For more information about ARP packet rate limit, see "Configuring ARP packet rate limit."
· If you enable user IP address conflict notifications, the device sends a notification to the SNMP module when a user IP address conflict occurs. The notification includes the sender IP and MAC addresses in the conflicting ARP packet, and MAC address in the corresponding local ARP entry. For more information about enabling recording user IP address conflicts, see ARP configuration in Layer 3—IP Services Configuration Guide.
· If you enable user port migration notifications, the device sends a notification to the SNMP module when a user port changes. The notification includes the IP address, MAC address, port before migration, and port after migration of the user. For more information about enabling recording user port migrations, see ARP configuration in Layer 3—IP Services Configuration Guide.
For ARP event notifications to be sent correctly, you must also configure SNMP on the device. For more information about SNMP configuration, see Network Management and Monitoring Configuration Guide.
Procedure
1. Enter system view.
system-view
2. Enable SNMP notifications for ARP.
snmp-agent trap enable arp [ active-ack | arp-miss | detection-drop | entry-check | entry-limit | gateway-check | local-conflict | mac-mismatch | packet-check | rate-limit | user-ip-conflict | user-move ] *
By default, SNMP notifications for ARP are disabled.
If you do not specify any keywords, this command enables all SNMP notifications for ARP.