- Table of Contents
-
- 05-Layer 3—IP Routing Configuration Guide
- 00-Preface
- 01-Basic IP routing configuration
- 02-Static routing configuration
- 03-RIP configuration
- 04-OSPF configuration
- 05-IS-IS configuration
- 06-BGP configuration
- 07-Policy-based routing configuration
- 08-IPv6 static routing configuration
- 09-RIPng configuration
- 10-OSPFv3 configuration
- 11-IPv6 IS-IS configuration
- 12-IPv6 policy-based routing configuration
- 13-Routing policy configuration
- Related Documents
-
| Title | Size | Download |
|---|---|---|
| 07-Policy-based routing configuration | 141.58 KB |
Contents
Restrictions and guidelines: PBR configuration
Setting match criteria for a node
Configuring actions for a node
Specifying a policy for local PBR
Specifying a policy for interface PBR
Specifying a policy for outbound PBR on a VXLAN tunnel interface
Displaying and maintaining PBR
Packet type-based local PBR configuration example
Configuring PBR
Overview
Policy-based routing (PBR) uses user-defined policies to route packets. A policy can specify the next hop for packets that match specific criteria such as ACLs.
The device forwards received packets using the following process:
1. The device uses PBR to forward matching packets.
2. If the packets do not match the PBR policy or the PBR-based forwarding fails, the device uses the routing table, excluding the default route, to forward the packets.
3. If the routing table forwarding fails, the device uses the default route to forward packets.
PBR includes the following types:
· Local PBR—Guides the forwarding of locally generated packets, such as ICMP packets generated by using the ping command.
· Interface PBR—Guides the forwarding of packets received on an interface.
· Outbound PBR on a VXLAN tunnel interface—Guides the forwarding of outgoing packets when equal-cost routes exist.
Policy
A policy includes match criteria and actions to be taken on the matching packets. A policy can have one or multiple nodes as follows:
· Each node is identified by a node number. A smaller node number has a higher priority.
· A node contains if-match and apply clauses. An if-match clause specifies a match criterion, and an apply clause specifies an action.
· A node has a match mode of permit or deny.
A policy compares packets with nodes in priority order. If a packet matches the criteria on a node, it is processed by the action on the node. If the packet does not match any criteria on the node, it goes to the next node for a match. If the packet does not match the criteria on any node, it is forwarded according to the routing table.
if-match clause
PBR supports the following types of if-match clauses:
· if-match acl—Sets an ACL match criterion.
· if-match vxlan-id—Sets a VXLAN match criterion. For more information about VXLAN, see VXLAN Configuration Guide.
· if-match service-chain—Sets a service chain match criterion. For more information about service chain, see Service Chain Configuration Guide. This clause is not supported on the S6800 switches with the LS-6800-32Q, LS-6800-2C, LS-6800-4C, LS-6800-54QF, and LS-6800-54QT product codes.
On a node, you can specify multiple types of if-match clauses, but only one if-match clause for each type. To match a node, a packet must match all types of the if-match clauses for the node but only one if-match clause for each type.
apply clause
PBR supports the following clauses.
· apply next-hop—Sets next hops.
· apply precedence—Sets IP precedence.
· apply default-next-hop—Sets default next hops.
· apply service-chain—Sets the service chain information. For this clause to take effect, make sure you have specified a reachable next hop in the apply next-hop clause. This clause is not supported on the S6800 switches with the LS-6800-32Q, LS-6800-2C, LS-6800-4C, LS-6800-54QF, and LS-6800-54QT product codes.
· apply fail-action-drop next-hop—Sets the action that drops matching packets when all next hops become invalid. If no next hops are specified on the policy node, this clause drops all packets that match the policy node. This clause is typically used in scenarios that require strict routing paths.
Relationship between the match mode and clauses on the node
|
Does a packet match all the if-match clauses on the node? |
Match mode |
|
|
Permit |
Deny |
|
|
Yes. |
· If the node contains apply clauses, PBR executes the apply clauses on the node. If the PBR-based forwarding succeeds, PBR does not compare the packet with the next node. · If the node does not contain apply clauses, the packet is forwarded according to the routing table. |
The packet is forwarded according to the routing table. |
|
No. |
PBR compares the packet with the next node. |
PBR compares the packet with the next node. |
A node that has no if-match clauses matches any packet.
PBR and Track
PBR can work with the Track feature to dynamically adapt the availability status of an apply clause to the link status of a tracked object. The tracked object can be a next hop.
· When the track entry associated with an object changes to Negative, the apply clause is invalid.
· When the track entry changes to Positive or NotReady, the apply clause is valid.
For more information about Track-PBR collaboration, see High Availability Configuration Guide.
Restrictions and guidelines: PBR configuration
PBR configuration task list
|
Tasks at a glance |
|
(Required.) Configuring a policy: |
|
(Required.) Specifying a policy for PBR · Specifying a policy for local PBR · Specifying a policy for interface PBR · Specifying a policy for outbound PBR on a VXLAN tunnel interface |
Configuring a policy
Creating a node
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Create a node for a policy, and enter its view. |
policy-based-route policy-name [ deny | permit ] node node-number |
By default, no policy nodes exist. |
Setting match criteria for a node
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter policy node view. |
policy-based-route policy-name [ deny | permit ] node node-number |
N/A |
|
3. Set an ACL match criterion. |
if-match acl { acl-number | name acl-name } |
By default, no ACL match criterion is set. If an ACL match criterion is defined, packets are compared with the ACL rule. The permit or deny action and the time range of the specified ACL are ignored. If the specified ACL does not exist, no packet is matched. The ACL match criterion cannot match Layer 2 information. For outbound PBR on a VXLAN tunnel interface, the ACL match criterion only matches the inner IP addresses in VXLAN packets. |
|
4. Set a VXLAN match criterion. |
if-match vxlan-id vxlan-id |
By default, no VXLAN match criterion is set. This command is applicable to VXLAN networks. When equal-cost routes exist, you can configure this match criterion to select a route for packets based on VXLAN IDs. On a transport network device, you can configure PBR on the Layer 3 interface to guide the forwarding of packets based on VXLAN IDs. On a VTEP, you can configure PBR on the tunnel interface to guide the forwarding of packets based on VXLAN IDs. |
|
5. Set a service chain match criterion. |
if-match service-chain { path-id service-path-id [ path-index service-patch-index ] }&<1-2> |
By default, no service chain match criteria are set. This command is not supported on the S6800 switches with the LS-6800-32Q, LS-6800-2C, LS-6800-4C, LS-6800-54QF, and LS-6800-54QT product codes. |
Configuring actions for a node
|
IMPORTANT: If you specify a next hop or default next hop, PBR periodically performs a lookup in the FIB table to determine its availability. Temporary service interruption might occur if PBR does not update the route immediately after its availability status changes. |
To configure actions for a node:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter policy node view. |
policy-based-route policy-name [ deny | permit ] node node-number |
N/A |
|
3. Set an IP precedence. |
apply precedence { type | value } |
By default, no IP precedence is specified. |
|
4. Set next hops. |
apply next-hop [ vpn-instance vpn-instance-name ] { ip-address [ direct ] [ track track-entry-number ] }&<1-2> |
By default, no next hop is specified. You can specify multiple next hops for backup in one command line or by executing this command multiple times. You can specify a maximum of two next hops for a node. For outbound PBR on a VXLAN tunnel interface, you can specify only one next hop and the next hop must be directly connected. |
|
5. Set default next hops. |
apply default-next-hop [ vpn-instance vpn-instance-name ] { ip-address [ direct ] [ track track-entry-number ] }&<1-2> |
By default, no default next hop is specified. You can specify multiple default next hops for backup in one command line or by executing this command multiple times. You can specify a maximum of two default next hops for a node. |
|
6. Set the service chain information. |
apply service-chain path-id service-path-id [ path-index service-patch-index ] |
By default, no service chain information is set. This command is not supported on the S6800 switches with the LS-6800-32Q, LS-6800-2C, LS-6800-4C, LS-6800-54QF, and LS-6800-54QT product codes. |
|
7. Set the action that drops matching packets when all next hops specified on the policy node are invalid. |
apply fail-action-drop next-hop |
By default, the drop action is not configured. The matching packets are forwarded based on the typical packet forwarding process as described in "Overview." This command does not apply to software-forwarded packets. This command is available in R2612 and later versions. |
Specifying a policy for PBR
Specifying a policy for local PBR
Local PBR might affect local services such as ping and Telnet. When you use local PBR, make sure you fully understand its impact on local services of the device.
You can specify only one policy for local PBR and must make sure the specified policy already exists.
Before you apply a new policy, you must first remove the current policy.
To specify a policy for local PBR:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Specify a policy for local PBR. |
ip local policy-based-route policy-name |
By default, local PBR is not enabled. |
Specifying a policy for interface PBR
You can specify only one policy for interface PBR and must make sure the specified policy already exists.
Before you can apply a new policy to an interface, you must first remove the current policy from the interface.
You can apply a policy to multiple interfaces.
In a VXLAN IP gateway or EVPN gateway deployment, when you apply a policy to an interface on a border gateway, follow these restrictions and guidelines:
· If the interface is a Layer 3 Ethernet interface, the policy is also applied to its subinterfaces. For more information about VXLAN IP gateway deployment, see VXLAN Configuration Guide.
· If the interface is a Layer 3 aggregate interface, the policy is also applied to its subinterfaces. For more information about EVPN gateway deployment, see EVPN Configuration Guide.
To specify a policy for interface PBR on an interface:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Enter interface view. |
interface interface-type interface-number |
N/A |
|
3. Specify a policy for interface PBR. |
ip policy-based-route policy-name |
By default, no interface policy is applied to an interface. |
Specifying a policy for outbound PBR on a VXLAN tunnel interface
In a VXLAN network, equal-cost routes might exist between two endpoints of a VXLAN tunnel. The device cannot route VXLAN packets to the exact next hop. To choose the desired next hop for outgoing VXLAN packets, use outbound PBR on the VXLAN tunnel interface.
The outbound PBR configuration takes effect only on VTEPs.
You can specify only one policy for interface PBR and must make sure the specified policy already exists.
Before you can apply a new policy to an interface, you must first remove the current policy from the interface.
In a VXLAN IP gateway group network, Layer 3 interface-based PBR on VTEPS or VXLAN IP gateways cannot match the outer source and destination IP addresses in VXLAN packets. This restriction is not applied if the interface is a VSI interface. In addtion, the restriction does not apply to the S6800 switches labeled with the following product codes:
· LS-6800-32Q.
· LS-6800-2C.
· LS-6800-4C.
· LS-6800-54QF.
· LS-6800-54QT.
The policy specified for outbound PBR on a VXLAN tunnel interface supports only the if-match acl, if-match vxlan-id, and apply next-hop clauses.
To specify a policy for outbound PBR on a VXLAN tunnel interface:
|
Step |
Command |
Remarks |
|
1. Enter system view. |
system-view |
N/A |
|
2. Create a VXLAN tunnel interface and enter tunnel interface view. |
interface tunnel tunnel-number mode vxlan |
By default, no tunnel interfaces exist. The endpoints of a tunnel must use the same tunnel mode to correctly transmit packets. |
|
3. Specify a policy for outbound PBR. |
ip policy-based-route policy-name egress |
By default, no policy is specified for outbound PBR on a VXLAN tunnel interface. |
Displaying and maintaining PBR
Execute display commands in any view and reset commands in user view.
|
Task |
Command |
|
Display PBR policy information. |
display ip policy-based-route [ policy policy-name ] |
|
Display PBR configuration. |
display ip policy-based-route setup |
|
Display the outbound PBR configuration and statistics for a VXLAN tunnel interface. |
display ip policy-based-route egress interface interface-type interface-number [ slot slot-number ] |
|
Display local PBR configuration and statistics. |
display ip policy-based-route local [ slot slot-number ] |
|
Display interface PBR configuration and statistics. |
display ip policy-based-route interface interface-type interface-number [ slot slot-number ] |
|
Clear PBR statistics. |
reset ip policy-based-route statistics [ policy policy-name ] |
PBR configuration examples
Packet type-based local PBR configuration example
Network requirements
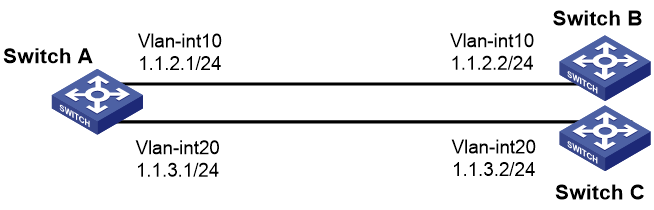
As shown in Figure 1, Switch B and Switch C cannot reach each other.
Configure PBR on Switch A to forward all TCP packets to the next hop 1.1.2.2 (Switch B).
Configuration procedure
1. Configure Switch A:
# Create VLAN 10 and VLAN 20.
<SwitchA> system-view
[SwitchA] vlan 10
[SwitchA-vlan10] quit
[SwitchA] vlan 20
[SwitchA-vlan20] quit
# Configure the IP addresses of VLAN-interface 10 and VLAN-interface 20.
[SwitchA] interface vlan-interface 10
[SwitchA-Vlan-interface10] ip address 1.1.2.1 24
[SwitchA-Vlan-interface10] quit
[SwitchA] interface vlan-interface 20
[SwitchA-Vlan-interface20] ip address 1.1.3.1 24
[SwitchA-Vlan-interface20] quit
# Configure ACL 3101 to match TCP packets.
[SwitchA] acl advanced 3101
[SwitchA-acl-ipv4-adv-3101] rule permit tcp
[SwitchA-acl-ipv4-adv-3101] quit
# Configure Node 5 for the policy aaa to forward TCP packets to next hop 1.1.2.2.
[SwitchA] policy-based-route aaa permit node 5
[SwitchA-pbr-aaa-5] if-match acl 3101
[SwitchA-pbr-aaa-5] apply next-hop 1.1.2.2
[SwitchA-pbr-aaa-5] quit
# Configure local PBR by applying the policy aaa to Switch A.
[SwitchA] ip local policy-based-route aaa
2. Configure Switch B:
# Create VLAN 10.
<SwitchB> system-view
[SwitchB] vlan 10
[SwitchB-vlan10] quit
# Configure the IP address of VLAN-interface 10.
[SwitchB] interface vlan-interface 10
[SwitchB-Vlan-interface10] ip address 1.1.2.2 24
3. Configure Switch C:
# Create VLAN 20.
<SwitchC> system-view
[SwitchC] vlan 20
[SwitchC-vlan20] quit
# Configure the IP address of VLAN-interface 20.
[SwitchC] interface vlan-interface 20
[SwitchC-Vlan-interface20] ip address 1.1.3.2 24
Verifying the configuration
# Telnet to Switch B on Switch A. The operation succeeds. (Details not shown.)
# Telnet to Switch C on Switch A. The operation fails. (Details not shown.)
# Ping Switch C from Switch A. The operation succeeds. (Details not shown.)
Telnet uses TCP, and ping uses ICMP. The results show the following:
· All TCP packets sent from Switch A are forwarded to the next hop 1.1.2.2.
· Other packets are forwarded through VLAN-interface 20.
· The local PBR configuration is effective.
Packet type-based interface PBR configuration example
Network requirements
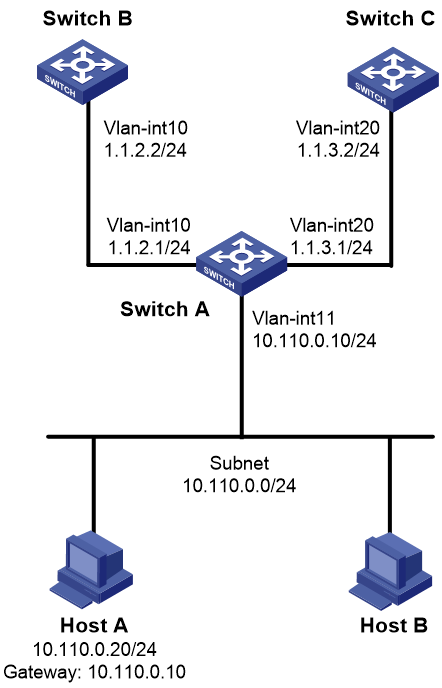
As shown in Figure 2, Switch B and Switch C cannot reach each other.
Configure PBR on Switch A to forward all TCP packets received on VLAN-interface 11 to the next hop 1.1.2.2 (Switch B).
Configuration procedure
1. Make sure Switch B and Switch C can reach Host A. (Details not shown.)
2. Configure Switch A:
# Create VLAN 10 and VLAN 20.
<SwitchA> system-view
[SwitchA] vlan 10
[SwitchA-vlan10] quit
[SwitchA] vlan 20
[SwitchA-vlan20] quit
# Configure the IP addresses of VLAN-interface 10 and VLAN-interface 20.
[SwitchA] interface vlan-interface 10
[SwitchA-Vlan-interface10] ip address 1.1.2.1 24
[SwitchA-Vlan-interface10] quit
[SwitchA] interface vlan-interface 20
[SwitchA-Vlan-interface20] ip address 1.1.3.1 24
[SwitchA-Vlan-interface20] quit
# Configure ACL 3101 to match TCP packets.
[SwitchA] acl advanced 3101
[SwitchA-acl-ipv4-adv-3101] rule permit tcp
[SwitchA-acl-ipv4-adv-3101] quit
# Configure Node 5 for the policy aaa to forward TCP packets to next hop 1.1.2.2.
[SwitchA] policy-based-route aaa permit node 5
[SwitchA-pbr-aaa-5] if-match acl 3101
[SwitchA-pbr-aaa-5] apply next-hop 1.1.2.2
[SwitchA-pbr-aaa-5] quit
# Configure interface PBR by applying the policy aaa to VLAN-interface 11.
[SwitchA] interface vlan-interface 11
[SwitchA-Vlan-interface11] ip address 10.110.0.10 24
[SwitchA-Vlan-interface11] ip policy-based-route aaa
[SwitchA-Vlan-interface11] quit
Verifying the configuration
# On Host A, Telnet to Switch B that is directly connected to Switch A. The operation succeeds. (Details not shown.)
# On Host A, Telnet to Switch C that is directly connected to Switch A. The operation fails. (Details not shown.)
# Ping Switch C from Host A. The operation succeeds. (Details not shown.)
Telnet uses TCP, and ping uses ICMP. The results show the following:
· All TCP packets arriving on VLAN-interface 11 of Switch A are forwarded to next hop 1.1.2.2.
· Other packets are forwarded through VLAN-interface 20.
· The interface PBR configuration is effective.
VXLAN ID-based outbound PBR configuration example
Network requirements
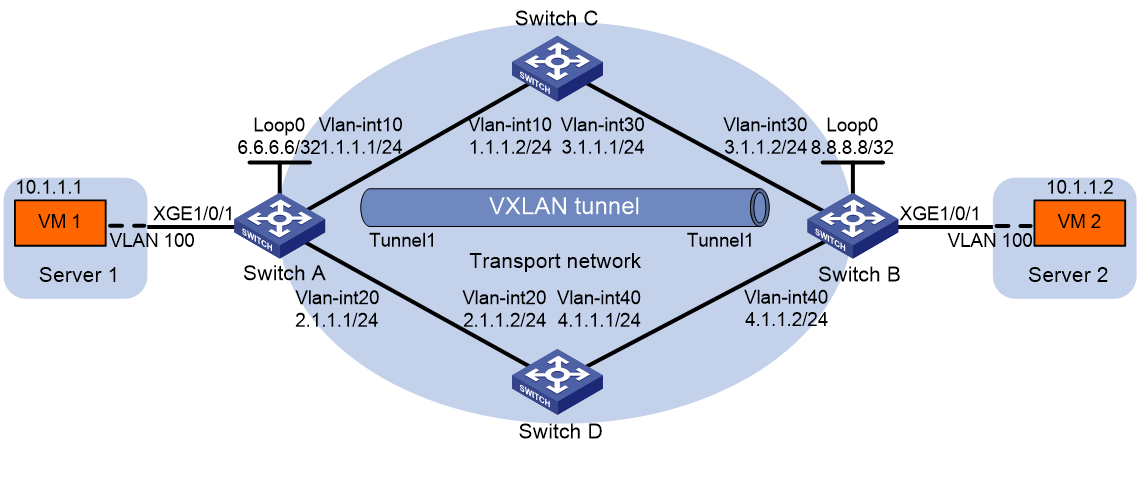
As shown in Figure 3, Switch C and Switch D are Layer 3 switches in the transport network. VXLAN 10 is configured on Switch A and Switch B (as VTEPs) to provide Layer 2 connectivity for VM 1 and VM 2 across the network sites.
· A VXLAN tunnel between the VTEPs is manually established.
· The tunnel is assigned to the VXLAN.
· Remote MAC address learning is enabled.
· The VTEPs flood VXLAN traffic in unicast mode (head-end replication).
Traffic from VM 1 to VM 2 enters the VXLAN tunnel through one of the equal-cost routes (with the next hop 2.1.1.2) between the VXLAN endpoints.
Configure PBR for Tunnel 1 on Switch A to forward the outgoing traffic through the route with the next hop 1.1.1.2.
Configuration procedure
1. Configure IP addresses and unicast routing settings:
# Assign IP address to interfaces, as shown in Figure 3. (Details not shown.)
# Configure OSPF on all switches in the transport network. (Details not shown.)
2. Configure Switch A:
# Enable L2VPN.
<SwitchA> system-view
[SwitchA] l2vpn enable
# Create the VSI vpna and VXLAN 10.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# Assign an IP address to Loopback 0. The IP address will be used as the source IP address of the VXLAN tunnel.
[SwitchA] interface loopback 0
[SwitchA-Loopback0] ip address 6.6.6.6 255.255.255.255
[SwitchA-Loopback0] quit
# Create a VXLAN tunnel to Switch B. The tunnel interface is Tunnel 1. The tunnel destination is Loopback 0 at 8.8.8.8 on Switch B.
[SwitchA] interface tunnel 1 mode vxlan
[SwitchA-Tunnel1] source 6.6.6.6
[SwitchA-Tunnel1] destination 8.8.8.8
[SwitchA-Tunnel1] quit
# Assign Tunnel 1 to VXLAN 10.
[SwitchA] vsi vpna
[SwitchA-vsi-vpna] vxlan 10
[SwitchA-vsi-vpna-vxlan-10] tunnel 1
[SwitchA-vsi-vpna-vxlan-10] quit
[SwitchA-vsi-vpna] quit
# Create Ethernet service instance 1000 on Ten-GigabitEthernet 1/0/1 to match frames from VLAN 10.
[SwitchA] interface ten-gigabitethernet 1/0/1
[SwitchA-Ten-GigabitEthernet1/0/1] service-instance 1000
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] encapsulation s-vid 10
# Map Ethernet service instance 1000 to the VSI vpna.
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] xconnect vsi vpna
[SwitchA-Ten-GigabitEthernet1/0/1-srv1000] quit
[SwitchA-Ten-GigabitEthernet1/0/1] quit
# Configure node 5 for the policy aaa, and configure a VXLAN match criterion for the policy to forward packets with the VXLAN ID 10 to 1.1.1.2.
[SwitchA] policy-based-route aaa permit node 5
[SwitchA-pbr-aaa-5] if-match vxlan 10
[SwitchA-pbr-aaa-5] apply next-hop 1.1.1.2
[SwitchA-pbr-aaa-5] quit
# Apply the policy to Tunnel 1 to guide the forwarding of outgoing packets.
[SwitchA] interface tunnel 1
[SwitchA-Tunnel1] ip policy-based-route aaa egress
[SwitchA-Tunnel1] quit
3. Configure Switch B:
# Enable L2VPN.
<SwitchB> system-view
[SwitchB] l2vpn enable
# Create the VSI vpna and VXLAN 10.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Assign an IP address to Loopback 0. The IP address will be used as the source IP address of the VXLAN tunnel.
[SwitchB] interface loopback 0
[SwitchB-Loopback0] ip address 8.8.8.8 255.255.255.255
[SwitchB-Loopback0] quit
# Create a VXLAN tunnel to Switch A. The tunnel interface is Tunnel 1. The tunnel destination is Loopback 0 at 6.6.6.6 on Switch A.
[SwitchB] interface tunnel 1 mode vxlan
[SwitchB-Tunnel1] source 8.8.8.8
[SwitchB-Tunnel1] destination 6.6.6.6
[SwitchB-Tunnel1] quit
# Assign Tunnel 1 to VXLAN 10.
[SwitchB] vsi vpna
[SwitchB-vsi-vpna] vxlan 10
[SwitchB-vsi-vpna-vxlan-10] tunnel 1
[SwitchB-vsi-vpna-vxlan-10] quit
[SwitchB-vsi-vpna] quit
# Create Ethernet service instance 1000 on Ten-GigabitEthernet 1/0/1 to match frames from VLAN 10.
[SwitchB] interface ten-gigabitethernet 1/0/1
[SwitchB-Ten-GigabitEthernet1/0/1] service-instance 1000
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] encapsulation s-vid 10
# Map Ethernet service instance 1000 to the VSI vpna.
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] xconnect vsi vpna
[SwitchB-Ten-GigabitEthernet1/0/1-srv1000] quit
[SwitchB-Ten-GigabitEthernet1/0/1] quit